How to Manage DevSecOps
Show transcript [en]
hello everyone I am going to talk about the application security team of terraneo and what we're doing to ensure security before we get started let me introduce triangle a little bit General is the leading e-commerce company in Turkey it was founded in 2010 with a dynamic and agile startup Spirit since then we have grown into a difficult back by Alibaba General Atlantic salt Bank Prince Royal capital and several wealth funds our application security team has eight members as you can see let's talk about scope of the application security these are the current metrics of your annual the environment search so in order to secure it we have to work hard to implement some application secured standards
we're responsible for application security tests and vulnerability management product security mobile application security kubernetes and container security and also their setups first step of our application security implementation is the security gate CI CD pipeline security gates is responsible for handling automated application secured tests security gates is triggered every time anybody pushes a commit into their gitlab repositories all of the applications are tested in these steps static application security software composition analysis software bills of materials infrastructure s code and also container security our developers can go to the application security orchestration platform to examine their vulnerabilities here's an example vulnerable to list of a project the vulnerabilities of every project can be seen on the application
security orchestration platform in detail here's an example vulnerability that was identified by gitlix that we used in security cicd pipeline step you can also check out vulnerabilities that are identified in manual application secure tests the secretion shows the manual identified SQL injection vulnerables there all valid vulnerabilities are issued on related gitlab repositories by a member of the application security here's an example template for application security issues on gitlab manual test issues must be closed on gitlab but automated test issues are closed when pipelines are triggered after issues are fixed each identified vulnerability has to be fixed properly to make sure everything fix is correct at light the abstract team retests each other when developers lost issues on
gitlab will get notified about their situations and closed issues are moved to the absecon's retest issuable we check if vulnerabilities are properly fixed according to our suggestions in case of improper fixes we reopen closed issues and their statuses get updated on the application secured orchestration platform note that the studies of vulnerabilities that are identified by automated tools are updated directly by the application security orchestration software if there is a proper fix one of the other applications we developed is the issue reporter every Thursday the issue report pulls open issues from the application security orchestration platform and notifies their responsible teams about open issues on absec tribe channels the second sequence chart shows an example f-set vulnerable to reporter
message or an abstract wrap Channel on Slack even if the issue reporter helps teams to know what vulnerabilities they have we decided that we should have developed an application that sends open issues where comes are pushed into the gitlab repositories then the abstract pipeline vulnerable to notify your idea came to our minds the absec pipeline vulnerable to Notifier is triggered by security cicd pipeline step after that it sends open vulnerable things to responsible developers as a notification via direct messages on Slack establishing Partnerships with development teams is a critical step in application security that's why we developed our own partnership automation system with this system we can quickly respond to application security test requests the partnership automation listens to
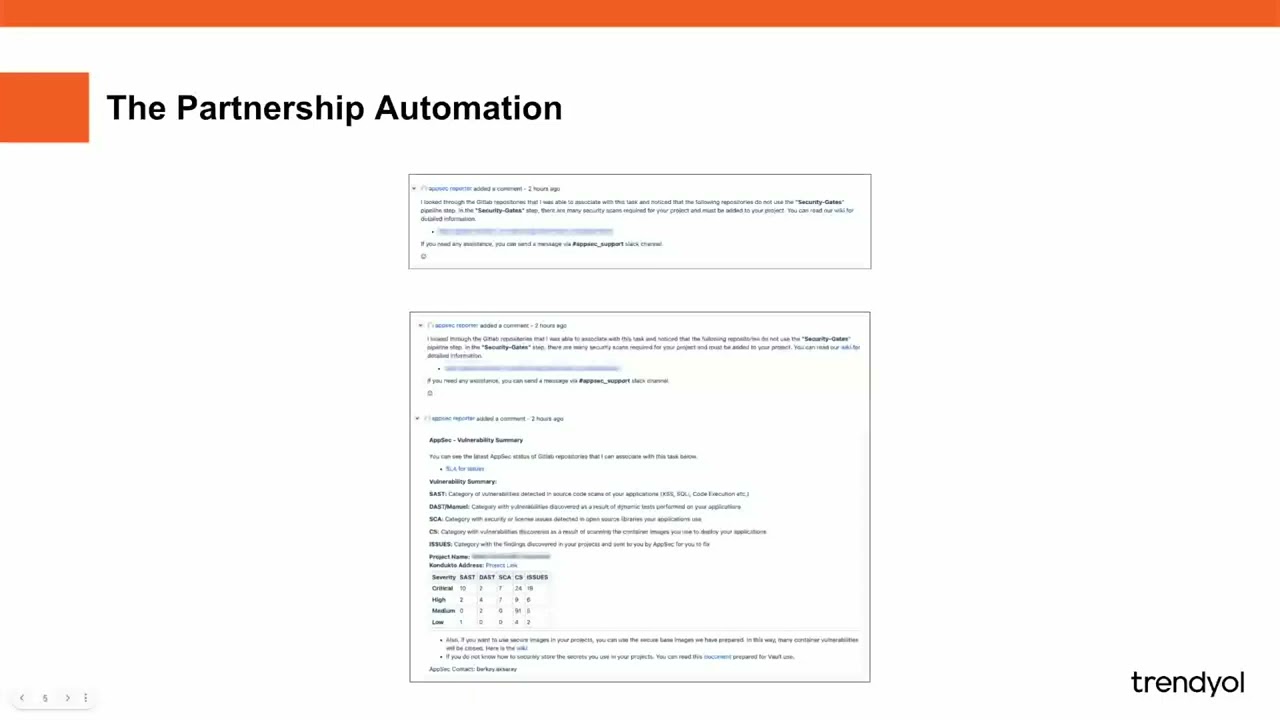
jira for every task that comes to the F6 state then it notifies the objective via select and creates a gitlab test for the objective then it checks the contacts of the jira cards if it finds a commit link it says previous identified vulnerabilities otherwise it modifies the team advantage in case it finds a commenting but the project is not integrated into security pipeline it notifies the team to add teams to the absec partnership automation nfsec state has to be created on jira boards here's an example card that was moved to the F6 state the first sequential shows the response from the partnership automation mentioning that security case was not integrated into the Project's pipeline if the partnership automation finds a
commit link and security gets the ICD pipeline step is integrated into the specific project the responsible team will get a similar response from the automation as shown in the second screenshots deploying applications in Secure environments is important in order to build secure container images we have to be picky about base images here is an example project that uses a vulnerable business as you can clearly see there are a lot of critical vulnerabilities inside the container the app section crates maintains and releases secure container based images depending on the common technologies that are used in trundle the other problem with containers is shell usage shall use it in containers is an insecure approach from a security
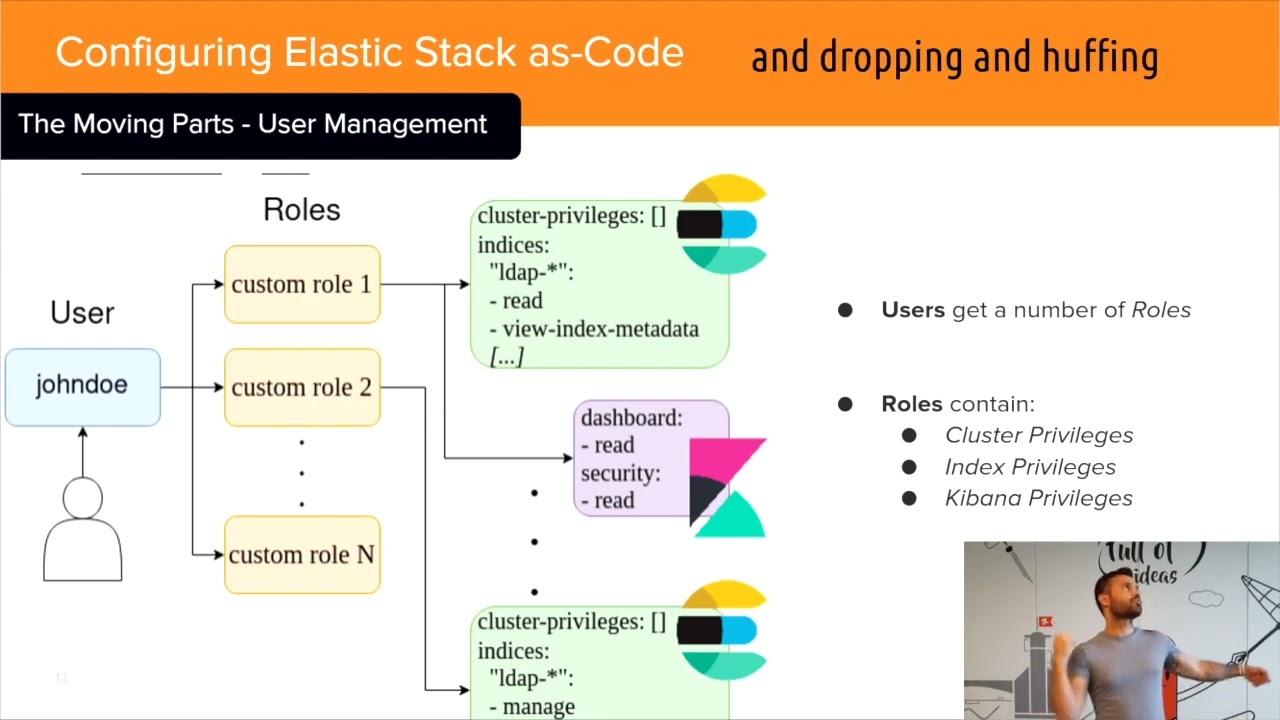
perspective that's why we strongly recommend images that don't have shells however some of our applications need to use shell commands at runtime so we created and release Dev images that contain sharp pictures we currently support Java noches python Theory .net nginx call internal we mostly use new Reddit for log management so in order to support New Relic agents in our secure container images DP container team prepare the pipeline for creating Java 11 and 17 images that contain new related agents the best proactive approach to prioritize an application security goes through secure application development trainings for Developers we record application secure trainings and organize periodic application secure strains addition we collaborate on training platforms such as supercon
Warrior and invite our developers to the trains for example in secure code Warrior we have four different courses for our developers back-end developers triangle not just developers to random mobile developers and also triangle front-end Developers secret management is important in application security because applications rely on sensitive information such as the API Keys usernames passwords and other credentials if these credentials are not properly secured they can be easily accessed by unauthorized parties leading to serious security breaches and data leaks effective secret management practices involve storing secrets in Secure encrypted storage locations and use and access control statistics who can access them this helps ensure that sensitive information is protected from unauthorized access or exposure here's an example lack of script management
issue in detail we care about script Management in trundle and we want our teams to store their credentials in Secure environments such as steroids the other thing that you care about is service service Authentication service service authentication is important in modern software architectures because it tells different services to securely communicate with each other over a network in microservice architecture for example a single application may be exposed on multiple services each responsible for handling a specific function these Services often need to communicate with each other to exchange data or platform tasks and this communication needs to be secured and trusted Services authentication provides a way to ensure that only transit services can communicate with each other
by using secure authentication mechanisms such as API keys or art tokens or digital certificates Services can verify each other's identity and ensure that they are communicating with authorized services without search Source authentication sources may be vulnerable to unauthorized access by administrative actor we're planning to be a listing service in Trend use we want our teams to implement S2s authentication to their projects and the last but not the least important thing for us is the rate limiting read anything is a strategy for limiting Network traffic on how often someone can repeat an action within a certain time frame for instance trying to login into an account rate limiting can have stopped certain kinds of mailshot activity you can also
reduce strain on web servers however rate limiting is not a complete solution for managing both activity we strongly use rate limiting on most of our applications many of the applications straight vulnerabilities occur due to either improper or no input sensation so in order to centralize inputs and help our developers easily mitigate these issues we developed a few methods that can be used in Java project each method has different use cases for example SQL injection method should be used when you put user inputs directly or indirectly into SQL queries if we don't synthesize or filter user inputs in this case SQL injection vulnerabilities may occur the track model and application utilizes the application monitoring tool to fetch
metrics for all services including Network traffic metrics and dependent service information this information is not used to obtain the gitlab reposter links and issue configuration data for each service then a thread modeling application searches the application security orchestration platform for all vulnerabilities associated with each service the search results include a number of open vulnerabilities and open gitlab issues the number of days that have passed since the SLA times for each form of reality is an essential metric too based on this information the threat model and application calculates the risk score for each service thank you all for listening to our presentation