The Evolution of Cyber Security and What to Expect Next
Show transcript [en]
thank you for the opportunity to be here today in beautiful Athens so Dr Greg and I have had an opportunity to work together for the last six seven years in Abu Dhabi and so I appreciate the opportunity to come here today and talk a little bit about my history in the business so what Greg did say is basically I'm old I've been doing this for a long time I've been fortunate enough to be able to do this in uh three different continents United States Europe and now in the Middle East um and I've had an interesting career that uh has worked some very interesting cyber cases around Espionage counter terrorism Counter Intelligence criminal activity um and so what I wanted to
highlight today is basically some of the lessons learned that I have gained over the years and it's amazing looking back on things 25 30 years ago uh that are still relevant today there're the same challenges that we're dealing with and so I want to kind of give you some insights into into uh the things that I've learned over the years to hopefully give you some of that knowledge that you can take into your careers and hopefully uh avoid some of the mistakes that I've made be able to leverage some of the lessons learned and hopefully be able to take those into your own careers uh going forward so as a good Air Force officer I have to give you a nice agenda
slide so I'm going to talk a little bit about myself and then really focus on some of the the pivotal cases that I had the opportunity to work uh and give you some lessons into uh what you should apply today as well as going into the future um talk about some of the more recent cases over the last couple years that have been interesting and then end with kind of I wouldn't call it a prediction but some of the things that I start to see emerging that we'll have to deal with in the next kind of 5 to 10 years um and then I'll kind of summarize everything and kind of talk through uh what to focus on so a little bit about
my background uh I start off within the United States Air Force I was fortunate enough to be recruited uh to become a special agent with what we call the Air Force office of special investigations uh if anybody's seen the the United States show NCIS same thing but that's for the Navy so we investigate uh felony level crimes counterterrorism uh intelligence Espionage type activities so I was brought in as a computer crime investigator where I got to work uh on intrusions into Air Force and DOD systems a lot of computer forensics and able to work information operations and a number of different things um since then I've been focused on building Security operation centers so the last probably 15 years uh both in
the United States and over in the Middle East uh have been building and operating Security operation centers uh most recently I built what we call a combined security operations center for the Baraka nuclear power plant in UAE which is a combination of operational Technologies and it systems so it's been fascinating to kind of work in that converged area of of OT IC as well as it um I'm now working part-time in Austria in Vienna as a security researcher where it's actually really interesting to look at digital twins um kind of the convergence of it and OT uh looking at Next Generation Security operation centers and then really how Insider threats have evolved over the last 30
years and how we still need to focus on that is a challenge so I want to talk a little bit about the past so so the first case um was before my time but one of the agents that recruited to be into OSI a guy named Jim Christie heavily worked on this case and uh we had many beers kind of talking about the nuances uh so what happened here is very interesting there's actually a book and a movie on it uh so there's a guy named cliff sto who was an astronomer working at Berkley and he was basically a system administrator kind of managing the help desk and and his boss uh came to him and
said hey there's a a discrepancy of. 75 cents in the basically there's an accounting system where if people wanted to use the computer main frames uh they had to log their time and they would have to pay for the amount of time they used well there was an actual discrepancy of 75 so Cliff started looking into it and uh what he identified was there was uh remote connections to modems that ultimately would allow access for a very short period of time until it pivoted and went somewhere else so he was very curious he started investigating and he basically started he basically took a bunch of equipment from his his co-workers and all their modems to create a modem bank so
whenever the next time the dialing happened he'd able connect where it was and so uh he was able to see that the bad guy he he called it a hacker pivoted and would go into different uh place in the United States so he reached out the FBI and said hey FBI we got some hacker breaking into our system and then migrating over to other us systems uh and what the FBI focused on was the 75 they're like our threshold is $10,000 so if you can't show that there is theft of $10,000 we don't care and so he kept investigating uh identified that they they were breaking into US government contractors that had contracts with the
US Air Force and so that's how he got in touch with OSI and Jim Christie was assigned the case and he started investigating and realized it was basically the first cyber Espionage case that we had come across FBI had never worked these cases especially on an international level and and so OSI got heavily involved and started inves and ultimately it got traced back to Germany and because the Air Force had bases in Germany and OSI had offices on those bases we have a relationship with uh federal law enforcement within in West Germany in this case uh and we were able to work with them and's Telecom to ultimately find the suspect which was Marcus H and
he was a German citizen uh we tracked him down with help of the the local authorities he was arrested uh charged and convicted of Espionage and during that interrogation he basically revealed that he was working for the KGB and the KGB had specific requirements that they lever upon him for different technology that they wanted him to find and they ultimately paid him $54,000 for all the data that he stole and so it was interesting is that multiple agencies were involved uh we did finally get uh support from some of the other local law enforcement to help identify uh the connections uh but what what was interesting to me and I've seen that even today that very minor discrepancies
or anomalies can actually lead to pretty significant um identification of compromises also that in this case typical unpatched systems and worse was default passwords and and even uh easily guess passwords and still amazed me today that there's default passwords being deployed with different technology iot technology that gets compromised on a regular basis the other interesting thing and I've seen this throughout my career is nation state foreign intelligence often use third- party threat actors hackers to to do their business and so uh it happened very early in in this case and we see it today that that adversaries often leverage uh the community to to break in and steal on their behalf and then also uh International cooperation in this
case was extremely necessary there's no way we would have been able to identify the suspect in this case without that the uh German authorities so now the first case I really got involved in uh was working at headquarters OSI at Bing Air Force base in Washington DC and uh there was a a task force created for what we call uh Moonlight Ms and so in this case there was a massive data breach within NASA and Military contractors which is why once again the Air Force got allall because we typically investigate uh intelligence Counter Intelligence activities with our contractors and so this case uh the initial compromise was really low security environments universities schools libraries and that really LED
that to allow them to Pivot to some of the the actual targets uh they exploited uh vulnerabilities and software that it was a known vulnerability and at this time the manufacturers the software man ufacturers were really slow to even put a patch out so now you see patches coming out pretty frequently whether or not they're applied a different story but in this case the patches were very slow to even be produced by the actual manufacturers so that window of vulnerability was far more extensive so in this case we uh identified that it was Russian foreign intelligence that was behind this and we classified this as an advanced persistent threat the reason I highlight this is Kevin Mandy
and I work together on this case um and so when he went to Mand created Mand and came up with the AP uh monitor it was based on this case uh back in the late or mate9 uh once again us classified information was stolen but more importantly what was stolen was what we call sensitive but unclassified information so by itself as an individual document it was unclassified if you aggregate all this sensitive but unclassified information together it becomes classified so it became a real challenge where we were investigating things that technically were unclassified but as an aggregate was actually very classified and then because of this all this information stolen so we did kind of a a a loss identification and damage
assessment and it was pretty significant um so that kind of leads to that not just classified information systems but also sensitive but unclassified information systems are extremely susceptible and vulnerable and you have to apply the right security controls around them and so one of the other interesting things is the adversary because they would hop through different countries and different kind of lower security environments that had zero logging in place it really delayed the investigation because we had to basically obtain a subpoena go to the location install a network sniffer wait for the adversary to come through again find out what location they came through off in a foreign country which made it challenging to then get International
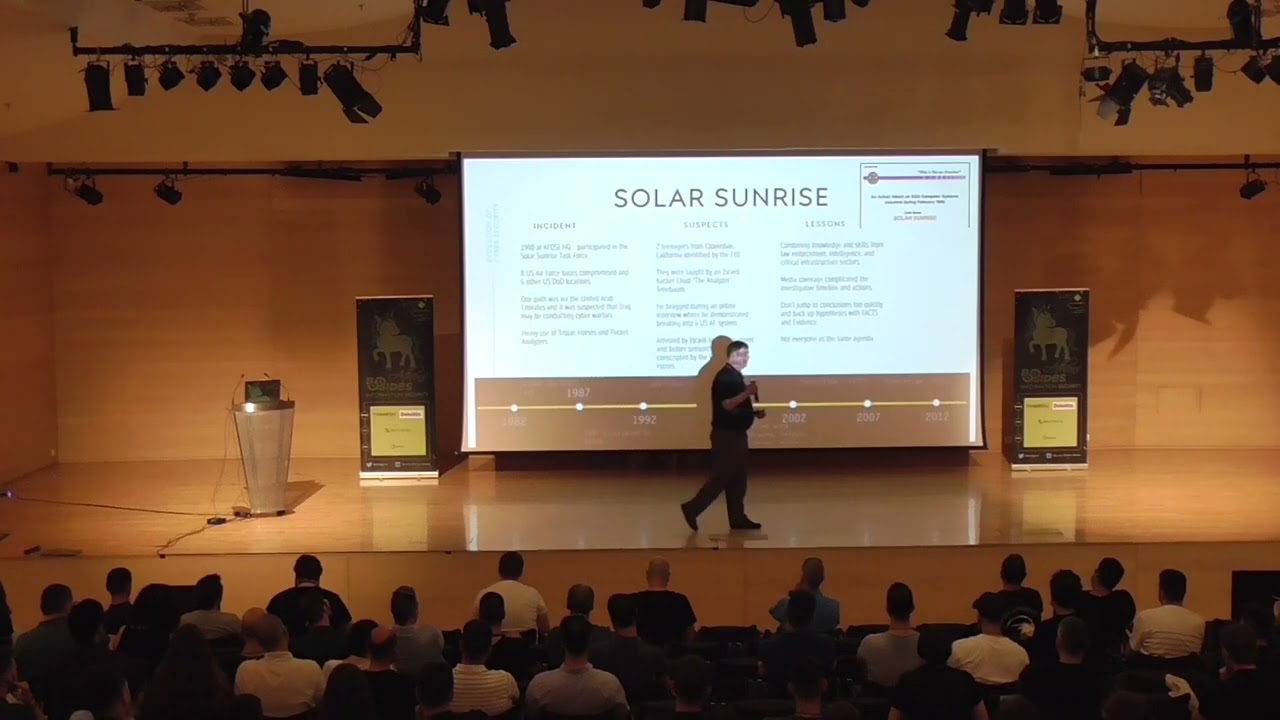
cooperation so these types of Investigations can last years because you go through the step-by-step process to really ident ify the adversaries um the other thing was having this is the first time that we actually brought together a task force we had uh investigators from NASA the FBI OSI other military investigative agencies and it was cool to see all these different agencies together because they have different authorities they have different skill sets and having this type of task force really helped us investigate this type of opportunity the next one which was a couple years later was uh solar sunrise this was more of an Air Force specific investigation because they targeted eight Air Force bases and a couple other
DOD facilities the challenge with this one was we saw traffic routed through the UAE and at that time uh the United States and the International Community was putting a lot of pressure on Iraq to open up for nuclear inspections and they were refusing so we were planning different battle campaigns to go in there and force compliance and so the concern that leadership had in the United States was this was our Iraq launching a Cyber attack through one of the only conduits out of Iraq which was through the United Arab Emirates and so there's heavy use of Trojan horses uh a lot of network packet capture and Analysis and so as we started investigate uh in this case the FBI had
learned their lesson and they were very supportive in this type of investigation and we actually found out there was two individuals in California uh that were part of the case a part of the the intrusions the challenge with this was the media got a hold of the story and started reporting on it and when we do investigations we like to take our time we like to make sure all the eyes are dotted and teas are crossed and so because this became public we had to scramble and get the search warrant um done very rapidly because we didn't want the the individuals involved to get wind of what we were doing and and stop their activity so fortunately the kids didn't
watch the news and we raided their their house um and because we were able to catch them in the act uh we able to see actual intrusion activity happening and more importantly they had a chat dialogue up with this uh hacker from Israel called analyzer and so at the time we didn't know who he was but we knew he was from Israel and he knew he had the the code name analyzer um and so after we arrested the kids he was training in the United States uh he actually did an online interview and very blatantly broke into an Air Force system while he was on the interview uh so fortunately we were able to track him back once again working
closely with Israeli law enforcement and the interesting part of that was we actually sent one of our agents over there um to help with the interrogation and he was arrested convicted and right prior to S sentencing he was conscripted into the the the military which was surprising by us because we we thought he should have been put in jail uh but obviously they had other agenda for for his skills within the IDF um so in this case we expand the task force where it was not just law enforcement we brought in the intelligence Community we brought in National Labs we brought in other um talented people to help with this case which is one of the kind of Lessons
Learned of when you have an opportunity to bring in different people from different backgrounds different authorities different skill sets it really gives you greater power to do these types of Investigations um once again the media coverage was not helpful normally we don't like to uh let people know what we're doing until it is all adjudicated uh but in this case it accelerated the timeline because we didn't want the adversaries to really know what was going on the other big one and and I use this today don't jump to conclusions it was amazing how much time and effort was spent briefing the Pentagon briefing the White House on the potential that Iraq was launching a Cyber attack against the United States
was farthest from the truth you had two Punk kids from California doing it with some mentorship from a 19-year-old in in Israel um but we spent a tremendous amount of time trying to kind of brief a lot of people that really didn't need to know what was going on because they immediately jumped to conclusions that were not correct and then once again not everybody has the same agenda from a law enforcement perspective we like to investigate prosecute and arrest or in uh prison uh in this case the half of the Israelis so the Israeli law enforcement was very helpful but when it came to the intelligence community and the military they had other plans for Mr
T so fast forward to uh now we're being stationed in Germany and there was a little issue in in Yugoslavia in 1999 Air Force was asked to support NATO from a cyber perspective so we launched the first undercover cyber operation which was very cool um we embedded ourselves in different uh anti-nato hacking groups uh and this is really from a intelligence collection standpoint so um if you think about threat intelligence today I mean we were doing this a long time ago embedding people within these communities to understand their capabilities who they're targeting um and really look at how we can bring that intelligence to the community so they can kind of have as as much for warning
as possible and so we also were involved in a lot of Investigations into um a lot of it was denial surface attacks and defacing websites but there was some legitimate cyber activity against NATO and the United States Air Forces in Europe um and so that all changed on the 7th of May so what happened on 7th of May uh NATO and I'll hate to say this but the United States dropped seven uh guided Munitions in Belgrade on a building that just so happened to be the Chinese Embassy it was an accident um and what happened in the Cyber war was overnight hundreds of thousands of Chinese hackers started to fight on behalf of uh Serbia against nato in the
United States and so that could a huge amount of noise uh they did a lot of Deni surface attacks um more importantly they would get onto these dark web forums and offer tools training uh to the the kind of anti-nato contingent which was fascinating and we did not plan for this and so we actually had to Pivot and a lot of interesting discussion around how to deal with this new threat actor that was not anticipated not planned for um and and it really created some interesting Lessons Learned one was that cyber warfare is very Dynamic things change all the time um I'll talk about a modern case that we have that just came up this
year that we didn't plan for expect and and are dealing with on a daily basis now activists can be extremely sophisticated uh we see that back then and even now that the tools that they use are are equal to uh nation state sponsor tools they have zero days uh they have the techniques that that are well uh organized they have good plan and then one of the other interesting things there's a thing called law of armed conflict Lo and not well defined in cyers space and the reason this was a problem was we had a new adversary involved in this war that were civilians they were leveraging civilian infrastructure they were Le leveraging infrastructure in a country not a part
of the war and so what we realized was there was no good Rules of Engagement on how to deal with this so it was less of a how do we counter this from a offens of cyber capability and more of about how do we tolerate it how do we become resilient to it because they're not a part of the conflict uh from a legal standpoint and we couldn't actually do any kinde of type of counter offenses um and then we also learned that geopolitical and historical Alliance uh have to be factored in not just in in regular Warfare but also modern cyber warfare um we saw a lot of interesting activity even within the NATO partners that that were more
supportive of B than the NATO alliance so it was interesting to understand all these things and factor that into any type of conflict that you're dealing with so I made my way back to the United States and uh started working at the Federal Bureau of Investigations in the Enterprise Security operation Center um why that was created was because of this guy guy named Robert Hansen so Robert Hansen was a special agent with the FBI and he was actually a Counter Intelligence agent and so he was spying for the KGB and and then the Russian Federation from 1979 to when he was arrested in 2001 so I got back to the states in 2001 started working for the
FBI in 2003 after they started building the eso and what happened here was Hansen uh for financial reasons decided to start spying uh for the Russians and because he was a c intelligence agent he knew all the trade craft so his Handler in Russia had no clue who he was and he would use both traditional and modern cyber trade craft to extra exchange information for money and he would do use dead drops uh he would use he'd basically take some chalk mark it on a a light pole that would tell his Handler that there was a package under a bridge and then they would retrieve the package and then replace it with a bunch of cash
and so what was interesting is very damaging to the United States so he would compromise what we call Double agents or people SP spying for a foreign country but are actually spying for the United States uh he compromised FBI investigations into Russian spies um and he would divulge a lot of classified information so extremely damaged to the United States um he actually passed away this month uh a couple weeks ago in his prison cell of theoretically natural causes um so the postmortem on this is the doj Inspector General basically looked at what the challenge was and how to detect the next Robert Hansen so what they realized was they had very little um internal monitoring they had plenty
of external monitoring no problem but they had very little in regards to internal monitoring of of data of behavior and all that stuff so what they created was this Enterprise Security operation Center that was really focused on Insider threat and what that meant was they needed to deploy tools and back then basically we we bastardized a data loss intervention tool that that the financial sector used and turned it into a Counter Intelligence a cyber Counter Intelligence tool and so what we were able to do is basically started with data classification so we had to tag all the data and then we monitored everything if somebody were to go to a shared file we logged it if somebody
were to plug in uh a USB key we log it if somebody went and did email we log it so um the challenging part here was you have authorized people with authorized access doing unauthorized things so it it's extremely difficult to figure out the unauthorized things part of it and so we basically had to bring in additional data sources so we work closely with the physical uh law enforcement part of the bureau to bring in Access Control information CCTV footage we interfaced with uh HR so any type of disciplinary actions from an HR standpoint brought in and so allowed us to really kind of create these thresholds and identify behavior and activity that was suspicious and so interesting thing
about this was so the lesson learn and I still use it today is having that Enterprise uh cyber situation awareness and Enterprise visibility is critical not just from a cyber security standpoint but also from an Insider threat detection standpoint uh being able to understand your data what's critical who should have access to it how's it encrypted uh being able to look at your security policies both cyber security policies and and physical security policies and not just have them in place but are you monitoring any violations how do you keep track if people are not adhering to those those policy violations um so bringing all that together and we're using that today in the UA is you need to be able to
track this stuff record it and then investigate these things and then we had some fun with our our polygraphs uh so the polygraph world has a has a phrase in In God We Trust all all else we polyr so I've kind of adapted that for us us where in God we trust but all else we monitor I don't care if you're a system administrator or you're the CEO you need to monitor that activity because they could be an unwitting Insider and without having that knowledge and and those monitoring capabilities in place you'll never know so let's talk a little B about K and so uh mandans put out AP1 uh which highlighted in this case
Chinese counterintelligence and so um I worked with Kevin on a couple of the cases that Manny worked on but we actually had several others that we worked on independently but a lot of the information that he reported in AP1 was mirrored in in our investigations so I'll talk a little bit about kind of the investigations that that I ran um that was consistent with what Kevin had in his report if you haven't read it it's a great report um highly recommend you kind of look at kind of the tradecraft that's used things that we came across was um the the shift in focus from Perimeter devices to the user and and the Chinese in this case were extremely
good at doing their own open source intelligence collection to the point that we had one instance where they would break into uh their intended targets home system compromise the wife's email and then create a fishing attack from his wife's email to him at work with a malicious payload and so it was the first time I saw how invested another nation state sponsor attacker was in in getting to a hard target and so being able to compromise a home system and ultimately uh get to the intended target at work uh was fascina I had never seen that before uh and this case they used both published and unpublished uh exploits so zero days and and once again they they
really knew the environment so they once they got in they would uh escalate the Privileges move laterally expand and then just suck as much data as they could and they would send that data out through common ports so if you're you're in a security Operation Center uh you typically wouldn't spend a lot of time looking at outb communication there and it was encrypted anyway um the thing that failed them on this case was that they got greedy and they they launched their attack um at midnight on Friday on a 3-day weekend so Monday was a holiday in the United States they knew this government agency did not have 24x7 security operations and so they started
pumping out terabytes of data over the weekend because they knew nobody was there to watch it and they got caught because when the sck came in on on Tuesday uh they saw a whole bunch of traffic going out uh Port 443 uh to the terabytes and obviously that was suspicious and that kind of launched the investigation and then they also used some pretty interesting anti forensic techniques so uh the initial uh compromise was through a malicious uh Word document and what happened is they they probably targeted four people and when you opened up the word document it would run a shell script uh to compromise the the user count but then it would delete the actual malicious
code in the word document so when we got there and started doing forensics we we saw the the what we thought was the carrier file but it was a legitimate word document that had a bunch of uh blank space in it and so we were fortunate that one of the four victims uh wasn't working that week and so the intact document was still in his inbox so we were able to ver engineer it identify ioc's and then uh expand the investigation throughout the agency and so in this case uh what was clear was state sponsored threat actor uh they had plenty of time they had plenty of uh capabilities and motivation and then over a series of
probably six months they did everything they need to do and that last weekend is when they're like okay we got everything we need let's just pull out as much as possible and then move on and so they do have a deep understanding of of the capabilities of the environment so they knew which exploits to use that would not trigger an alert so that tells me that they had a lab that had all the defensive Technologies this agency had and then practiced and ran their tools against this environment uh to be able to do that so defensive tools are great but it's not the only thing you have to look at Behavior you have to look at um
data flows you have to really look at the the entirety of the picture to understand potential malicious activity we also found out so in this case Microsoft was the victim and and it was a heap overflow uh and so we brought it to them and and within a day they came back said Yep this is this is bad this is a serious zero day um and then we didn't hear from them for 6 weeks and then they said okay we created a patch it's going to be out of uh standard Patch Tuesday no poping circumstance no we're fixing a major flaw in our system it was under the wire it was released with normal Patch Tuesday stuff what was
interesting from our perspective was it took 6 weeks a major flaw in their operating system or one of their services um and it took 6 weeks to fix so uh once again it highlights that your window of vulnerability is often far greater than you think because state sponsored threed actors that have zero days um have several months to to execute their tools before uh the software vendor is able to fix them and then once again uh it was the first time I experienced that that the threat landscape is far greater than just the organization that you're responsible for protecting so understanding that that the employees their homes their mobile devices uh those things are all
susceptible to state sponsored well and any other type of threat so now fast forward to to d8 so I get to du8 and one of the first interesting cases to come across is a cyber extortion case so the company that got victimized was a ride share company called kareim they ultimately got bought by Uber but uh Kareem had had been operating in the UA at headquartered in the UA for 5 six years um they had basically uh 78 cities across 13 countries of coverage uh with 14 million customers and about 560,000 they call them captains but drivers and so a fairly significant uh Workforce and client base and so what happened was the adversary uh broke in without the
knowledge of the company stole their source code stole all their clients and stole their driver information and then what they did is they basically left a message in the system telling the leadership basically the CEO and the board hey I broke into your system I took all your source code I took all your customers and your driver information and if you don't want me to release it publicly you'll pay me 10 Bitcoin and so uh the company obviously brought in its Response Team like us um and we started investigating the challenge was that that these guys were based in Dubai and their entire infrastructure structure was AWS out of Dublin uh fortunately uh one of the agents that
that worked the solar Sunrise case with me was now the chief security officer for for Amazon and so I was able to call him up and ask him hey here's the situation he's like yep I'm aware of it yeah Irish law enforcement won't do anything so that's a dead end good luck in Dubai and unfortunately the Dubai law enforcement cyber community is is is not very robust so we really were on our own and what okay this was uh Kareem had a global Workforce I mean it was a still in kind of startup mode had been startup mode for for 5 years and because everything was in the cloud all their developers were from all over the world
and they had no real Access Control they had no real security controls and it really complicated kind of an in response and what I was able to do was uh we had kind of the timeline of of when the adversary uh put the communication on the system and the only only real logs I had were were VPC logs or virtual private Cloud uh flow logs and what I was able to deduce from that was okay we know how how large of uh the source code repository is and some math was able to determine when it was exfiltrated and where and under what account it was used and so the account that was used uh was a legitimate
account we contacted the owner of the account and they said they hadn't used the account during that time frame so at least we're able to identify that it was stolen credentials that the adversary did in fact take the source code did in fact take the the repository and now the focus was on how do we close all the vulnerabilities and limit the damage as much as possible so they engaged a crisis communication team that uh started negotiating with the threat actor trying to buy more time they did make some incremental payments but really it was to delay uh to to close up any of the vulnerabilities they had and then they put together a communication
plan to communicate both internally with the the employees as well as externally with the client base and so uh what happened was from a lesson learned standpoint in these types of cases where you have a global environment law enforcement jurisdiction is extremely difficult to to narrow down and and once again if I was the Irish law enforcer yeah the server's here but you're in Dubai I mean there's no motivation for me to support this type of investigation and so it was very Challen ing to get law enforcement involved at all uh one thing that that I took away from this case was having a crisis communication team for stuff like this was invaluable because they actually were able to
communicate with all the different shareholders and stakeholders the board of directors the SE suite and then ultimately craft the right message for both internal and external communication uh that helped limit the the perception damage limit the the reputational damage uh and ultimately prepare them to be bought by which was was very interesting so now let's talk about the present um so this is probably within the last couple years the first one uh Dr Greg and I had the the great pleasure of working for uh Dubai Expo 2020 which actually happened in 2021 because of the pandemic but we uh were fortunate to be able to build probably one of the more modern Security operation centers uh
because it was a smart City built from the sand um 6 years prior to Expo starting it literally was the desert and so it was very interesting to to have to deal with that um what we came across was several different challenges um one was there was uh several different groups uh that would create fake social media accounts of Expo Executives and use it any anywhere from scamming to um information operation campaigns against Expo UAE as a whole and the leadership of the country another interesting thing that we came across was fake job postings so this was was run up to Expo uh and Expo had a legitimate job site and and bad guys basically would scrape
the job postings and then repost it with uh charging applicants for Visa processing fees um potentially relocation fees we even had two instances where people showed up to Expo say I'm here to start my job and we're like who are you and they had got scammed by this recruiting agency they paid money then they flew themselves and they showed up on on the front door of Expo wait for their to um there's also a fake news out about a covid-19 outbreak um we kind of identified that that was linked to a a state sponsored uh information campaign against the United Arab Emirates and then we also came across during the construction phase several very peculiar physical security
incidents um that showed long-term planning uh potential implant of of cyber devices and stuff like that so uh this was another instance where there was kind of a blend of physical security and cyber security that had to work together um so like I said it was a a brand new city so it was one of the more modern cities ever to be built uh huge amount of space over a th000 Acres over 2 million square meters of new buildings so when I say new buildings it had all the latest 5G it had all the latest building management systems a lot of iot sensors a lot of industrial iot sensors um everything had to be sustainable and
green so a lot of uh uh energy uh savings systems in place um so it was a real challenge for us because we needed to be able to monitor systems that that were very very new and and not well understood um and so the other one interesting challenge was the way these Mega events work is you get sponsors so in this case Cisco was the network sponsor and so the security Operation Center had to use all Cisco stuff which some of it's good other stuff I would prefer a better best debr thing but we are limited to the technology stack that the sponsors provideed so we had to kind of work through some of those challenges
um interesting thing on if you work in threat intelligence or utilize threat intelligence there's these things called takeown services and takedown Services where if if you're working for a company and somebody tries to create a URL that's consistent with that company using different words you can use a takedown service to basically take down that domain and so we brought on a service like that for Expo specifically and what we didn't realize is it's not conducive to Mega events we were challenged with uh some of the social media because they would make us prove that Her Excellency uh the minister did not have this fake uh Facebook account and and it was really cumbersome to to
have them ultimately work with the social media providers to D down accounts without extensive proof that it wasn't uh from the person that should have it we also saw an interesting convergence of iot iot and the cloud so in this case seens was one of the partners so they deployed their Billy management system um which was all these iot sensors and then they pushed it all to their own cloud uh management system so ultimately all the building management systems within the entire site was managed through a cloud portal and that was the first time come across really iot and Cloud convergence which created a huge Challenge on use case development because in a sock you have
use cases you have correlation rules and you have in the iot space everything is very bespoke so you have different manufacturers you have their own way of doing things and and there was not a lot of kind of available use cases we could leverage so we had to work very closely with seens to come up with a few of the use cases that were most relevant and to them they they had never done use case development so it's a little bit of a challenge to work with seens to understand kind of their world and then have them understand our world to actually create um use cases that were were available for us in the S and then
once again uh I attempted to integrate physical security with cyber security I've been trying to do this for almost 30 years and once again it didn't work and part of it is the the physical security system is a separate network uh they don't understand cyber security their Protocols are different and so it was very challenging to to integrate I would want to be able to leverage facial recognition software and if we see some cyber activity pivot to a camera to see if there's any physical activity there wasn't able to do it unfortunately it was it was very challenging so one of the the recent cases we're working on is anonymous Sudan didn't know about these guys until
last month uh but apparently they targeted Sweden and Denmark back in January 2023 uh and then they hit Israel and took down uh some power substations and then we got involved because they attacked three banks in the UA um denal service attack took them down for about a day um but it was uh something that the country got very concerned about because once again three major banks in the country should be resilient to denial service attacks uh but they Wen they went down and then most recently this month they targeted Microsoft and some other us uh organizations so they uh created a telegram in January 18th uh so very recent if you look at the
telegram and look at any of the kind of Open Source information appears to be motivated by religious and political um activities there is a strong relationship with with Russian activist groups and they actually joined uh the pro-russian activist group uh Kil net and when we look a little bit deeper uh the language is always either um Russian English or or uh Arabic and so surprisingly Global targets so so it wasn't isolated to I mean what's going on in Sudan or or stuff like that it's it's kind of a very diverse Target base um and so a couple lessons that that I learned is how amazed we're it's 2023 and we're still getting hit by Doos
attacks and all the banks in the UA had DS mitigation services and they fell down they recovered rapidly so you're not out for a week now it's limited a couple hours or at most a day but still I'm amazed that that dos attacks are are effective against certain uh critical infrastructure attribution is extremely difficult there's a lot of O out there but also there's a lot of things we call false flags and false flags are uh organizations intelligence organizations that that want the perception that it's somebody else so they will intentionally put information out there where intelligence collection capabilities will interpret that as real and ultimately divert the attention away from from who is really behind this um
we've also noticed that that a lot of these activist groups are infiltrated by nation state uh threat actors and that way they can have plausible deniability they can influence the targeting and it's a great way for for them to kind of meet their own mission requirements but in an anonymous way with misattribution and then I'm amazed the amount of of kind of response and time taken away from other things to deal with this type of of attack so uh not just within the UA but obviously globally with the the types of targets I have so case that I'm currently working um is interesting and this kind of goes back to the very first uh case where
there was analysis of building access information and basically uh they were using this to corroborate HR um pan cards and so an HR person was looking at the access control logs and realized that her badge was used uh over the weekend and she's like I didn't come to work over the weekend so that discrepancy started this investigation and what was hampering this investigation was Legacy physical security information so cameras were no longer functioning so we didn't have any CCT footage um the access control system was OB L compromise so we couldn't rely on that the thing that allowed us to catch the bad guy was from Co So Co created a need for a thermal imaging
system at the front of the building and nobody knew that this thermal imaging system also had a camera and was not only taking the temperature of people but also a picture of the person and so we were able to correlate when uh the misuse of this credential gained access we then had a very clear picture of who's responsible and so what was interesting was this employee another Insider had been working for this organization for 28 years and so similar to the Hansen case we have a a trusted Insider that had been working for the organization for a very long time now doing unauthorized activity and so we then looked at how the adversary was doing certain things uh he was able
to penetrate the aircraft and air gap is something that we talk about within critical infrastructure classified environments where it's it's a network isolated from the rest of the world and there are now techniques that that can very easily bypass the air gap so it's no longer the the protection that we used to enjoy um so what ultimately happened was a complete failure of both people process and Technology um and that was underlying a poor security culture uh when we start we started the investigation we we did what we call a technical surveillance countermeasure so bug me we were concerned that this individual was Implement imple implanting actual listing devices and other uh surveillance devices so we did a a TSM
sweep of the entire building and part of that is a physical inspection and dude we saw so many passwords on stickies on on keyboards on the the monitors we had uh mobile devices all over place um we unfortunately opened up a drawer and there's a bunch of sexual paraphernalia in there um so and in the UAE that's illegal so um we confiscated all this stuff which was very interesting because we sent an email out to people we we grabbed the stuff from saying hey uh we had an investigation we took a bunch of stuff uh if you want to claim your property come claim your property person that had the drawer full of sex stuff
did not reach out to us and say stuff back um but it was interesting and so once again uh highlighted the need for kind of physical security and cyber security to work together once again very difficult um they don't have a cyber security culture in this case with all the Legacy technology it was extremely difficult to actually get any useful information out of them to help with the investigation and that really forced some things so um if you see on the some of the graphics um what's interesting is uh there are modern tools we got BH bunnies we got rubber duckies we got the flipper zero and interesting thing about the flipper zero was it was a GoFundMe
project and uh it's amazing how some of these very inexpensive uh tools are used now for modern day aspon um once again uh there was no Insider threat capability no Insider threat detection capability and so uh obviously it doesn't have to be limited to classified or very sensitive environments this was a critical infrastructure client um so having an entire threat program for critical infrastructure is also uh recommended and then we did engage with the ababi police um and unfortunately there was no collaboration uh Cross of information they basically took all the stuff that we did and then they did go to the guy's house and searched the house but we got no results on uh if any
of the the client data or uh equipment was in his house so very little communication with law enforcement in this case so now the future so uh what do we do when we talk about the future we talk about chat gbt so I asked chat gbt what does the Future Hope and and as expected came up with some relevant topics but very generic stuff so I will say what Eric says about the chat gbt topics um obviously there is a increased sophistication um AI is is now useful I would say it's more than just machine learning and and what I see now is a combination of artificial intelligence and machine learning uh to help bad guys
be more productive uh be quicker so uh my old team did a lot of vulnerability research take months and now with machine learning vulnerability research to identify potential zero days is going to be far quicker it's going to be automated uh and then couple that with machine with artificial intelligence to actually create exploits dynamically quickly in a semi-automated fashion is what I see so uh we no longer have the luxury of okay when a vulnerability is discovered we have 3 days a week uh to make sure the patches is deployed within seconds I would say that exploits will be created once vulnerabilities are discovered and when those if those are zero days discovered by an adversary
then obviously there there's a larger window window of vulnerability that we need to be concerned about we look at targeted tax and critical infrastructure um working in the nuclear sector and some of the other critical sectors in the UA 100% there is going to be a convergence of it and OT Wireless technology for ease of monitoring ease of uh Administration there's a lot of remote sites that uh they don't have the Personnel to go to these remote sites and do activities so you're going to see this convergence it's already happening but I see it accelerating um as new OT devices uh programable logic controllers plcs there are now virtualized plc's there are plc's that that have operating systems so it's no
longer just a static thing that that opens and closes a valve you actually can program stuff which can be beneficial for cyber Defenders because you can now put um host base intrusion detection systems on the plcs where before you couldn't um but still that that convergence is quickly going to expand the the threat landscape and make it very challenging uh iot devices so I think that will be mitigated as the global Community consolidates kind of security controls and recommendations where uh they will control the Gateway they will force authentication encryption stuff like that so I'm less concerned about iot um but I am definitely concerned about uh ransomware Evolution where we've already seen cyber extortion but I'm predic that there'll
be cyber hes taking let's look at medical devices with that are implanted in your body if an adversary can say hey I can kill your dad tomorrow unless you pay me a ransom that's more motivation than than less supply chain attacks um I definitely see that uh everybody can be victimized so if there are hard targets out there um individuals would be targeted we've already seen individual targeted to to Pivot to get to the hard targets that will continue supply chain we've already seen that with solar winds that will uh continue to expand evolution of emerging Technologies like I mentioned uh wearables and Ved medical devices uh I'm concerned about because once again we it can kill people and so
if you look at autonomous vehicles anybody that can get into these types of systems that can cause uh death is a is a concern a lot and then obviously State sponsor attacks I think because of how the technology and the attack vectors have expanded um is no longer limited to state sponsored uh threat ACS you have religious groups you have political groups you have threat intelligence companies basically the capabilities that were limited to threat or nation states threat actors has now expanded tremendously so some of the final thoughts um I I'm still going to footstop insid threats I see that as one of the major concerns because as I mentioned they have authorized access um
but they're doing author unauthorized things and it's extreme extremely difficult to detect that most organizations that I come across are still having challenges with the block and tackling of patch management multiactor authentication and so to to implement an inside threat program is very difficult um you need different technology different Human Resources um and there's always privacy concerns that you have to deal with uh cyber threat actors are embracing technology and so should we and so when we look at um chat gbt an example we can use that to leverage the defensive Technologies I hope it will allow me to write use cases I hope that it will help me uh create correlation RS so I don't need a spunk
s&v that cost me $250,000 I can leverage technology to be able to do that much quicker information sharing and exchange I'm a big fan of I've seen this throughout my investigative career that uh having liaison with International Partners the security Community is very helpful so I want to reiterate thanks for being here uh the conferences like this are extremely valuable to share information to share lessons learned to share challenges and ultimately increase kind of the security posture of the entire Community with with your collaboration uh technology advancements are great and UA is really pushing the bounds of of of Technology but I caveat that also apply sound security practices when those new technologies are deployed
test them make sure that you actually can defend and protect and monitor against those we're definitely entering into a new phase of cyber security where human life will be impacted and in the past okay data stolen uh services are disabled that's recoverable um but now when you're talking about human life and how a Cyber attack can actually kill somebody that's a concern and that's what I'm more concerned about now going into the future that how do we take our industry and now have it as a way to protect human life and finally um I would like people from to learn from the past read as much as you can all the information I presented I should say
everything on the slide uh you can verify through open sources um everything I took about or talk talked about uh you can not um but definitely look at the past look at case studies um what I find challenging within the cyber community is is we're trying to mitigate all possible risks and that's just not feasible so my recommendation is mitigate the risks that are most relevant to you and that often is based on real incidents so if you can do postmortem on incidents within your sector within your community within your country and then deild build your kind of uh defensive posture your detection capability around that that'll be the best thank you for your
time