The Dangers of Working in Cyber Security
Show original YouTube description
Show transcript [en]
hello there everyone how you doing thank you very much for coming along to to my my talk I've called this the snappily titled keeping yourself safe when working in cybersecurity I tried to come up with a better title things like when that time the police made me want to cry help I want to cry things like that but it just didn't work out it just so I've gone for the very very boring but descriptive keeping yourself safe when working in cybersecurity and just as a little bit of interest what sort of people have we got in the river we've got people who make applications makers developers yeah very gear breakers people who bust lots of stuff excellent
researchers malware researchers that sort of thing yes excellent stuff very good well just a little bit about me I'm a director of a local company vertical structure and it's about the only time you're gonna hear me mention my my company name and the rest of the time it's just a story really about me not here to sell anything I'm not here to kind of make you come and buy my fantastic services or products or anything like that but you are very welcome to do so I'm a security and penetration tester and a trainer and the consultant security control consultant contractor and I've been working in the IT industry I suppose since about 2002 and working
in this this new seemingly new world of cyber security I suppose for the last I suppose about six or seven years something like that so just a little bit about me just because I'm up on stage and you have to listen to me I'm going to tell you a little bit about Who I am and how I got to where I am now and I started off in a very different profession maybe like some of the other people I'm not sure I started off as a stage manager in the theatre industry I have an honors diploma from the Royal Academy of Dramatic Arts in stage management and theatre production and so you know my background wasn't originally
an IT and or in any way shape or form after about two years of working in the theatre in I realized that I wasn't that fond of actors and I didn't really like directors very much either which is kind of a kind of a limiting factor when you're in that in that industry so I started doing some open university courses started retraining started to to come in to my second career and I'm very proud of the fact that I have had that I have a second career I like working with people who have second careers as well I find that they they tend to be very very focused on their second career my adage is that when you've done a job that you
hate and you find a job you love you will you will never go want to go back to the job you hate and therefore you will work very very bloody hard to make sure that you don't so I managed to blog myself a job as a developer I was working in PHP originally and don't judge me for that but you know I was working as a PHP developer company I was working for went belly-up and thankfully they not thankfully they didn't pay us for about three months two months something like that but in that time before they went belly-up managed to blog another job I'm quite good at quite good at interviews and talking the talk
and in that role I stayed there for ten years I learned an awful lot of stuff I worked for a local company that developed software for oil and gas and oil and gas industry I had a number of titles I was a web applications developer I was a systems administrator I was a network administrator I was a Technical Sales I was after sales technical and my last title before I left was something like management information systems applications infrastructure architect if you can say that after a couple of beers later on then you'll be doing really really well and worked with a lot of different oil companies lots of companies based in mostly in the u.s. did a lot of work
around the world went to see an awful lot of places an awful lot of hotel rooms and and meeting rooms in airport lounges in different parts of the world and we worked with a lot of different oil companies as I say one of the companies that we started working with was a Russian oil and gas company who I believe no longer exists and one of the things that Russians take very seriously maybe one of the very many things that Russian Russian people take very seriously is oil and gas and security around that oil and gas and we started working with them and they started it was in about 2005 and they insisted on on these on penetration and security
tests starting to happen now as developer and sysadmin and network administrator it was fascinating absolutely fascinating to watch what was happening as within about we kicked off at 9 o'clock by 9:03 they were uploading malware to our service they were they were completely pillaging everything that we'd worked so hard to to put in place they were performing basic sequined floors I found it fascinating I was tailing the logs and just watching and understanding and you know seeing how they'd broken into our applications and how they were doing this stuff and that was when I started to really think yeah that's that's that's really cool that's what I want to that's what I want to date so cut a long story short after
a short while and working that that company also went went under after a while and but after a while I started a company with a friend of mine and we wanted to not work for anybody else we wanted to work for ourselves do fun things and to you know to never have never have another boss again but those of you who work for yourselves will realize that actually when you are self-employed or you contract into places instead of one boss in a in your in your world you actually now have ten bosses who all want you all the time and it makes things a lot more interesting makes things a lot more fun and you know
we do we do some we do some really cool stuff and very proud of what we do but well the way the where this story is going is that I started contracting with a security company with a company developing some really interesting software it was after the the London riots and before the before the the Olympics in London and I started doing a bit of work it was one of those pieces of work where you you initially get called in for mine was a ten day attend a job that was in May 2012 and I have been consistently working with them since then so it's you know it's it's a nice a nice thing and I said before you
know the the term cyber security I think wasn't was kind of in its infancy at that point you know we were wasn't really a cyber security company and now every email I received seems to have cyber in it in some way shape or form either cyber or gdpr I don't know if you are receiving those emails as well and so we and we were working on this company we went a little bit outside of what we normally do but we we provide some services we provided some installation work some security testing a few sysadmin roles a few services VPNs a couple of dev environments a bit of a assistance here and there lots of lots
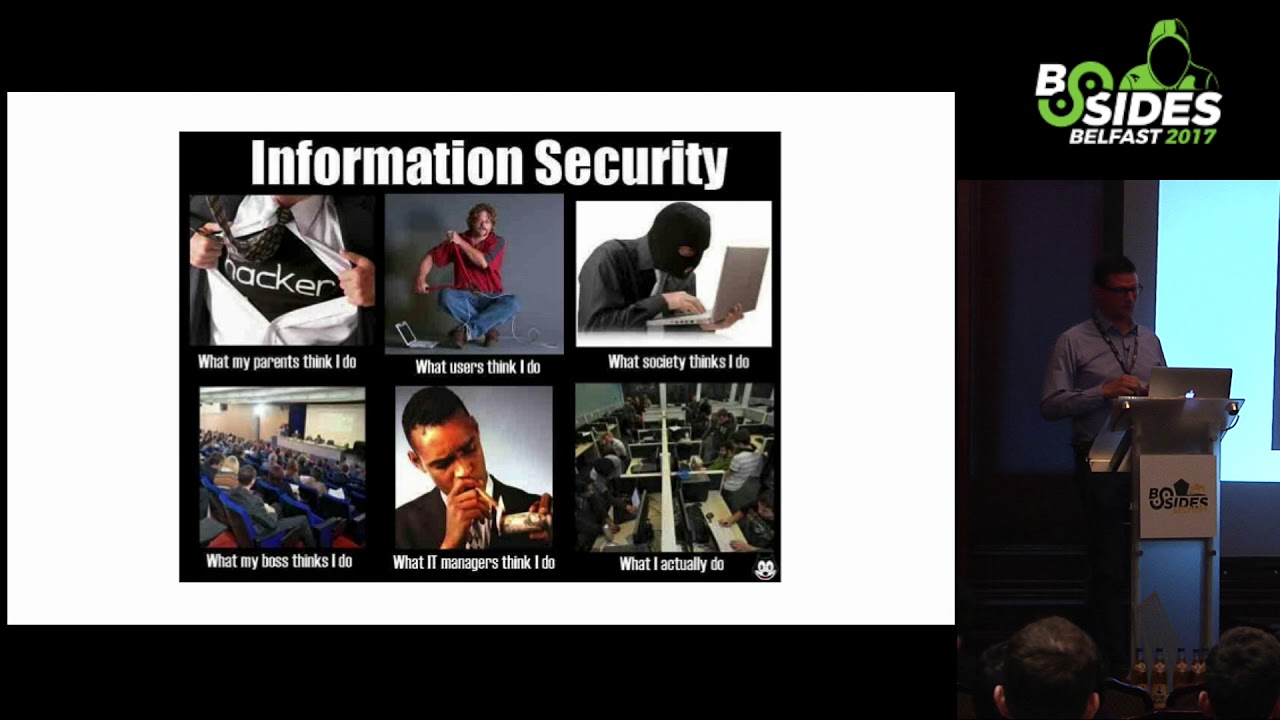
and lots of bits and pieces it's been really gratifying to see that company grow from you know literally three people above a garage and to I think it's around about 40 people now and we're still involve for them and still do a lot of work as I say it was initially a short-term job and it stretched into into so far a 5 and 1/2 year engagement but back to me and and that's what stories about is it's me and I'm not here to say to sell anything so I'm sure you've all seen this before not sure how it scales but you know it's the typical you know what my parents think I do what users think I do
what society etc this is a story about how I nearly how I very nearly went from bottom right to top right although I'm never sure in that infographic way sorry in that stock image why the the guy behind the computer has felt to have about it was required to have a balaclava on and maybe it's cold in the room or I don't know and so my my journey it from from bottom right to top right so has anyone heard of this this thing called wanna cry anyone did you hear about it at all it was this small thing earlier on in the year and it was it started around about the 12th of May and encrypt your data on your hard drive
basically just just encrypted everything and there was a long long list of documents and file file suffixes that it that it that it encrypted it then used the one of the shallow brokers SMB vulnerabilities to to spread around the network initially it was thought obviously and you know I'm preaching to the choir here initially of thought it was it was all the older machines and of a massive stories about Windows XP being the you know the the biggest worst thing in the whole wide world and you know all everyone is going to be completely ruined because they were they were still running these Windows XP s and actually it was really interesting when you know
when researching about it that wanna cry affected mostly Windows 7 versions as you see from the far left that's taken from a burski report there so what we had was a jump on page of details about about this new ransomware it could be the biggest ransomware offensive in history was it targeted at the NHS know why the wanna cry malware caused chaos for the National Health Service in the UK they seek to recover from global cyber attack as security concerns resurfaced and then I love this one here the ransomware meltdown experts warned about is here let's get all end of the world II I was going to put either a Carmina Burana or the 28 days later
music on what I put that those slides up but I think the words do it for themselves and then there's a message obviously you know that what happens after any of these events is that the inquest begins the story the next story happens you know what happens after the ransomware has happened so I've been reading about the the new outbreak with you know with great interest same as probably everybody else in the room had avoided managing to touch it in any way shape or form we'd made sure that the everything possible was was patched that everything had been rebooted everything was was looking pretty good from our point of view we're discussing it with our clients and you
know giving them advice about how to fix it you know how to prevent it from happening and you know we're wondering at the same time you know actually the previous slide you know was this the global ransomware meltdown though we all heard about we're expecting and I'd been to a great talk as anyone anyone come along to the OWASP Belfast meetups every so often yet there's a great talk last week last year from porec Donnelly and and had been about ransomware and I'd pulled out a few more of his slides and started having a look through and trying to understand a little bit more about you know the process that people use for for for
launching these ransomware attacks so where do I come into this you know I'm Northern Irish security consultant tester trainer English living in Northern Ireland but during the weekend of the 12th of May to the Monday the 15th of May and in the eyes of the NCAA the PSNI cybercrime unit and probably a few other agencies that I'm not aware of or I'm not permitted to be aware of and myself my business party and sorry my business partner and one of the people we work with were apparently apparently prime suspects with involvement in the NHS ransomware attack that was called wanna cry devastated obviously a number of NHS trusts in the UK as well as other
organizations around the world people had telefónica you know things things like that so I received this I learnt of my involvement in this using air quotes when I was at work one day and I received a call from my father-in-law who never phones me he never talked to me but I received a phone call from my father-in-law and he used to was very scary used the words there are some very serious gentlemen here who want to speak to you and I thought right okay he handed his phone over to a very stern sounding police officer who informed me that they would need to meet urgently to discuss my potential involvement in the NHS ransomware outbreak they informed me that they were
serving a warrant at my home which entitled them to search the house doesn't scale hugely well apologies and I've also had to blank out my address and people who signed it address all that sort of stuff and they were serving a warrant at my home which entitles them to search the house and investigate all electronic goods within the house later discovered there was a warrant against my business partners home address and also our office address and when they came in they they entered there's the premises search record and they specify general wear and tear on my my devices I think that some of them are probably got more than general wear and tear on them
but yeah they they they inventoried every piece of electronics in my house which as with most of you was quite a significant undertaking you know I have devices here there and everywhere and they did that over the course of the next few hours and did the same and my in my business partners home as well when I received the phone call I didn't know what what we were facing you know I just was told we need to meet to discuss your involvement or potential involvement so I was wondering you know had had one of our service been compromised was it was it being used as a bot whether it was there something that was you know kind of analyte you
know was being used to send out messages or to you know commander control service or you know something like that that's what I was wondering so arranged to meet officers the the officers on the phone at our office we don't advertise where our physical offices and so nobody was kind of aware of it which was quite good because it gave us a bit of breathing space during that breathing space I firstly phoned a very lovely local solicitors firm and Ford Campbell and the brilliant Cathy Matthews from Fort Campbell if you're looking for a solicitor let me tell you she is absolutely brilliant I never thought I would need to keep a solicitors card in my wallet but I do now I also phoned my
wife to explain what was going on when I say explain what was going on I phoned her to explain that I was going to meet the police officers of my office and I didn't know what it was for and I don't know if I'll be picking the kids up from school and I don't know what you know I don't I don't know so I failed in explaining to her what was going on because I didn't even know myself and she sounded confused irritated she actually asked me at one point is there anything you need to tell me which was nice I thought so I went to the office I met the officers who were very nice
very very professional very focused I think it's probably the right word and I explained that my solicitor would be joining us shortly sitting in an office in a small office with with three police officers in absolute silence waiting for a solicitor to arrive it's one of the scariest experiences of my life and I never I never hope to have that experience again and I didn't need to call a solicitor I wasn't under arrest I wasn't kind of I wasn't you know kind of been charged with anything but I felt it was a good idea to help us to to make sure that we that we all knew what was going on so you had ten minutes sitting
around waiting for waiting in absolute silence for the for for things to start for my solicitor to get there and for things to to to kick off and I'd worked with her with one of the officers on a previous case and spoken to another one on sis and so we all knew who each other were we you know we all come across each other in some way shape or form and as I say they were they were they were there and they were investigating they were doing their jobs and they were keen to get asked questions though and get and get things going and from my point of view I was very great I was very glad
that you know they were firstly that they thought that this was suitable for us to do it in an office rather than I don't know if they slapped handcuffs on but you know escorting me to a police station in the back of a police car I don't know if that would have happened but I'm very glad they gave us the opportunity to talk then so our solicitor came along and and it all began and it was there was nothing like this it was it was all very it was you know they didn't they didn't take me outside and you put my hand on a photocopier and tell me it was a lie detector or anything like that
there was no no tricks no games nothing like that questions ask me what was what was going on so when the interview began we were told our involvement in the NHS ransomware outbreak was that a paste bin had been discovered which had apparently originated from an IP belonging to us and another one which mentioned the words NHS ransomware sorry and another one which stated NHS leaked ransomware test as shown in these images again apologies for the scale up here these are the to paste pin so you can see NHS ransomware and you can see NHS ransomware a test NHS leak ransomware test so what's that one two three four I've lured out two words there five six
seven eight words in a in a couple of anonymous paste bins as you'll see there are 159 views on this one 74 views on this one and they're posted as a guest and as a guest so they're anonymous they're not comment from any account they were posted on Tuesday the 9th of May 2017 the wanna cry outbreak started Nerdist on Friday the 12th of May from these the from these there was an investigation which led to the warrants that we saw previously which led to the search and seizure warrants being issued for this there were eight police officers at my house and three of whom came to our office so there are 5 then 5 of my house and 3 at my
colleagues house and 3 at the office I had no recognition of these pastes but I did have a faint idea of where things may have gone awry awry I got slightly less concerned because things started to fall in place I thought I could I could start to solve their issue one of the things I was very cautious about I didn't want to be just kind of saying yeah it's to do with this and it's there and if you're an insert you know it's a client and it's this and it bla bla bla so I wanted to make sure that we got the answers out nice and carefully and honestly so I believe they can solve it
within a few minutes so the two IPS they mentioned ap1 and ap2 an IP one in question belonged to a server which was set up to provide a VPN service and for a particular client who do a lot of work in the realm of cyber security and breach alerts so that was IP one it's not used for anonymization in any way shape or form it's designed as a corporate VPN it's designed as a place to access certain IP restricted and sources IP 2 belongs to our client who had been posting something on pastebin one of the salespeople for our client had been doing a demonstration of breach alert capabilities on Wednesday the 10th of May in response to requirement from a
trust and then a chess trust regarding a ransomware issue that had taken place earlier on in the year in 27 January 2017 so one of those posts that we saw previously had been from our VPN server one post had been from the user in England's home IP address so those nine words post over to paste pins one post had come from AP and went back to us and one post had come from another and from another IP obviously once they had the IP it was a quick jump to do a you know very very basic who is on the IP who owns it oh it must be these chaps over here here's my name there's the other
details and so that's how they were able to to get to us and so quickly so before I get to what we learned what the the warrant that we were served with gave the police the right to extract information from and retain all electronic devices for examination in relation to home and work if required so that would have been our that would've been everything laptops phones hard drives at home backup drives modems Reuters Smart TVs potentially you know anything that they felt was was appropriate and as it was in the course of the in the course of the the the interview with them we were able to identify I was able to call out the IP
address of the VPN server to say to them yes I think it's this IP address is that correct they're able to look on their notes and say yes it is that's exactly correct so we're able to to identify what happened but in the meantime the police were in my house they went through every single one of our they gave a full and proper search of the house and they took logs of every piece of equipment in the house and they I believe took notes of serial numbers and so now at least if I ever get burgled and the insurance company asked me for a list of everything electronic device they'll be able to provide that and I don't know if you can
get that under freedom to information during so the warrant basically gave them the right to extract information from everything so they that that nazar solicitor advised us that compels us to provide provide the police with the connection logs for the VPN and an image of the server for their examination we were able to we again one of the signs that we weren't you know things weren't going to go the worst for us after being able to explain what we thought had happened was that we were permitted to to get them access to the logs and show them the grepping of the logs that we were doing so we're able to show them the logs and say there's a user
connecting there to see that string that's the sign of the user connecting then we're able to go back and try and find dates and times and it was some of the most the fastest and most efficient graphing I've ever done and you know I managed to do it without any man pages or you know googling which sometimes it's quite an achievement with with some of them and we did have a bit of a disaster we were attempting to prove our innocence we're attempting to prove what was going on openvpn truncates andrey and and overwrites logs when it restarts okay so you're using Oviatt OpenVPN it truncates your logs when it begin when it restarts depending on configuration
obviously we didn't we we didn't have this in we didn't have this this knowledge at the beginning and had a bit of a code Brown Brown trails a time as it were and the last restart on the open VPN server had which which was on a Windows hyper-v hosts had been when do you think just after the patches for the wanna cry issue had been released by Microsoft so therefore we didn't have the exact connection logs for the day that the pastes were posted on paste bin at that particular time so then we had to you know heigh-ho heigh-ho and off to backups we go and once again my I have a bit of advice here next time you're
doing a restore exercise for any of your service imagine you have policemen standing over your shoulder watching everything that you type and do another one standing there getting very nervous and clicking his pen and another one over there with a piece of forensic software who you know with the forensic drive trying to you know wanting to wanting to start examine examining stuff it will make you work faster it will make you work better you know try to try to think of that so we retrieved the logs brought them onto the same server we're able to prove that they were you know they were accurate showing the process of getting the logs from the backup server added another hour to what
we were doing and all the one all the while you know you're wondering what's going to happen are they gonna seize our stuff what would we be it would I you know the the same issue would I be able to leave in time to pick up my children that I had said to my wife I would do earlier in the day and while we were talking about this as well there was a there was a bit of a discussion of snatch of a discussion that I overheard that we were talking that they were that they mentioned that there but also been a raid launched against someone in England and that had been performed by the NCAA the National Crime Agency later
discovered that the guy in England who post the pastebin posts his house was raided at 7:30 on a Monday morning they seized all of his electronic goods and devices it just went hell-for-leather and they didn't return them for and they you know they imaged them and they did what they had to do and it took them about three weeks to get all the stuff back - so for our point of view the next four and a half hours were spent proving our case you know proving that we'd done it proving that we'd you know we could we had evidence that this person was connected at this time we provided evidence of the application that you
know and why they would have been posting this stuff up online we spent the next four and a half hours or so proving our case retrieving a server image and getting it downloaded and which wasn't it was a not inconsiderable task on its own and considering I was I was working off my the hot spot on my foot on my you know there I was working tethered off my phone and downloading a 12 gig disc image from a from from a remote source that really helps with the the monthly bill when it comes in and let me tell you that nothing downloads our slowly like with the the grepping and with the backup and restore nothing
downloads as slowly as when a policeman is watching you downloaded and so we then had so this was our warrant sorry this was the back of the warrant again apologies for the quality of the picture there but and we were compelled to provide logs for examination image of the server and as I say not a not a not insignificant task in itself so what did we learn we learnt that paste big paste bin log everything you put up there they logged location they log IP they log lots and lots of bits of information about what you're doing and they give up the data very quickly if for a legitimate law enforcement request that's what they you know Terms of
Service say it's what they should be doing in our case the investigation starts on a Friday from what we understood they found this on the Friday and appears nice saber crime unit had a warrant ready to go apparently on on Sunday evening so that was quite a rapid you know quite a rapid step what else did we learn we learned the law enforcement agencies talk a lot and can be very efficient so in our case the NCA spoke to some people some people we found out that you know some information had come from various agencies in the UK and further afield and the NCA scoped to their US counterparts came back to the NCA came back to the PSNI cybercrime
unit went to a County Court Judge for signing of our warrants and then went to me it was a County Court Judge I have the signature on my warrant to prove it apparently the you in in Northern Ireland there's special that part of the legislation requires that instead of a magistrate to sign it there's a County Court Judge is required to sign it which means that there are county court judges out there who get their their golf interrupted at least once a week to sign warrants for these raids for things like this and we also learned that you know if you look at that there was a lot of time and money spent tracking us down
you know that's a request from the you confirm the the UK wide NCA to somewhere in the states to somewhere to back to the NCA back to the PS and I back to the county court back to us eight officers in our house three and in the office three in my colleagues house a lot of people a lot of time a lot of money and it's it's you know it seems like a very it seemed it seems like the that that there shouldn't have been that we shouldn't have caused that to happen in the first place what else did we learn we learned that a search and seizure warrant can be obtained on the basis of
an IP address posting a relatively nonspecific text message to a public forum we were unlucky to get involved I think those those messages they're just text they're not malware nobody's uploading you know sharing malware like people are doing in this room I'm sure you know sharing it to mega or one of those one of those services to share it around your colleagues or your research you know associates but the search or seizure warrant can be obtained on the basis of an IP address on a very very nonspecific text message now this was an you know this was a bit of a bigger deal because wanna cry was being investigated in in a very very stringent manner
because it had to be because it had nearly brought the NHS to a standstill so we heard earlier you know we're talking about you know malware research you know looking at ransomware and looking at this malware that comes in and you know the involvement can be can be accidental you upload a a command-and-control script to paste bin which is later used by somebody else you upload something to a public forum that is then used or adapted in another in another forum does that make that does that then make you the original author of that malware all of that of that issue you've got to be very very careful how do you upload and share that information
with others does it link back to you in any way it probably should do but you know you've got to be very very careful what about new exploits and vulnerabilities when you're sharing them to or working out if they're if they're accurate or if they're true you know if they work you know how do you share that amongst your group of researchers and friends without being you know being caught up in something like this and wasting police's the you know the police's time some organizations will be more protected than others there'll be there'll be universities you know people from university here people from CSIS if people from UCD or something like or other places where you have a little bit
more leeway because your IP addresses will always come back to you know to a security research part of the university and they're able to talk to they talk to you have a look at some of the other content posted on pasted in and once again apologies I searched on paste bin for docs trying to see if there was information about people being docstore how to Doc's or what you know what was going on there's loads I searched for the words you had on Facebook sorry on paste bin see if there's more info if there's information about about that there's tons and tons and tons of pieces of information once again I believe we were unlucky to get involved in this we
were you know it was the wrong place at the wrong time what else did we learn we learned that seizure of all electronic goods for imaging and catalytic imaging and cataloging would have been completely within scope thankfully it wasn't actioned in our case because they they list the police were great you know they listen to the story they believed the story they proved the story we were able to prove the story to them and prove that you know we haven't we hadn't done anything wrong but this would have included as I mentioned before laptops phones hard drives encryption keys give up your encryption keys for your GPG or your you know your your hard drives at
home and passwords servers tablets everything would have been would have been brought in imaged in taken away apparently the image of our VPN server which is now dead will never never come back again and the VPN server it will be kept forever as well so that's gone into storage somewhere in somewhere in somewhere and it'll never be it'll it'll never be deleted will always always be kept as a as a I suppose a reminder of for us of what what happened so if the consider your company how long could your company operate without these things without your laptop without your phone could you afford to go out and purchase new laptops phones whatever is for your for your staff in some cases
bail conditions state that you're not allowed to use electronic devices for a period of time and things like that you know can your company operate without those bits and pieces consider your business continuity plan you know it's a it's a very very important thing so what else did we learn probably wouldn't have looked like that but and but the police could and they would have completed a forced entry including breaking down the door if my father-in-law hadn't been in the house thankfully doing some painting so that would have meant that my my father and already thinks that I'm now at the top right of my my image at the beginning and but you know they they
would have affected a forcible entry which probably would have made things worse you know if we if we if they probably wouldn't have listened to the story so much if they hadn't had free access to the house and being able to get in and get you know and see stuff if we'd been there my family including my two small kids and my wife would have been removed from the house while the police searched catalogued and questioned and what else did we learn we learned that this is the rights of the occupier an owner of property seized and what this says is and I will read it to you here it's the section in red section
ten if premises have been searched by force every attempt will be made to secure them under the police and Criminal Evidence ni order 1989 compensation is not payable for damage during a properly conducted search so if you're raided by the police and they have to cause damage to enter then you are not covered for any costs so I'd have been out for a not only a solicitor's bill but a new front door the respect and love of my father-in-law and a few other you know bits and pieces incidental bits and pieces what else did we learn I'm not sure what we would have done if we hadn't been able to provide the logs I don't know I don't know what
what state things would have got to and would have that this have been when the seizure of all of our stuff would have started thankfully we didn't have to find out but you know that's the you know that's the state in which we we presume it can feel sometimes like you're having to prove your innocence this slight there's a bit different to how I imagined it would be but you know when the police come with a you know even a slightly compelling case you have to prove that you didn't you didn't do that and the punishment of having our stuff seized would probably have been a considerable setback for our business you know we wouldn't be able to claim
insurance for police grabbed our stuff but I mean you know I'm not sure there's a there's a thing magic for that but keep your logs it may help to prove your innocence back up your lungs take them off your off your service if you're if you're providing services in this way or you know just provide if you're if you're doing stuff around you know with sensitive material back up your logs test your backed up logs send your logs to another location and then test them again use a different use some some some some software to help you understand those logs and to to make sure that you've got them we've got clients using Cabana we've seen people
using and using Splunk you know things like that just make sure you have your logs you know it's a very very very bad situation to get into what else did we learn solicitous and used a gold plated background there for a reason solicitors can be very expensive but they are also work they were also worth every penny for us and they made sure everything was done the right way they made me feel confident about speaking to the police about providing everything that I needed to provide about understanding the warrant and what it innate what it meant I'm longer in the tooth than you know some of the more junior you know some of the junior
people that we work with I didn't I didn't have code Brown immediately and there are some you know junior researchers who you know they might not have known what to do they might not have realized that calling a solicitor would help them they might not have had the funds to be able to just you know to call someone in to to spend six hours just sit you know sitting there listening and making sure things were done right so they are expensive but they're worth every penny I was a Ford Campbell that's their details there they're not sponsoring this event in any way shape or form or anything like that if you have any problems I would I
thoroughly recommend speaking to them they are they they are brilliant we love them they now get there they're top of our Christmas card list every year now and you know we're very grateful to to them for their for their help more loaning don't work from home or perform research from home without a connection to the office if you are sharing stuff from from office you know sorry if you're if you're sharing stuff and your home of IP address pops up on a list somewhere it's you that's gonna be you know that's gonna have the problem your IP address is not anonymized your IP address is it's obviously logged by these telcos in various in various places using tor you
know you're gonna you're going to find yourself a level of anonymization but you know if our M if if the you know for instance if our client had been using tor and and and also posted one from our our IP address and then you know we might found ourselves in a different situation the question why we're using tor you know why was somebody using tor to post exactly that message why was somebody doing this what if you got to hide why using an anonymous Asian software questions that shouldn't be you know shouldn't really be difficult to answer but which are things that you've got to be aware of working from home or from a relative's home imagine working from
your mum's house so your address gets and her IP address get your mom or dad's house so your IP address gets logged against something like this you you do not want that phone call from your mom or dad saying you know there's police at the police here and they want to speak to you trust me it's not nice and it'll be a waste of time and money for everyone concerned I dislike the fact that we wasted you know the police time was wasted looking for tui jets in Northern Ireland and one in England about you know about something that you know shouldn't have shouldn't have got to that stage protect yourself don't force the police
to investigate don't do something that's going to make the police investigate they don't have many tools at their disposal apart from warrants and searches don't waste their time by you know by uploading something stupid to a you know to a public resource you know public space like that and it's expensive and time-consuming and as I said they don't have many tools at their disposal apart from these warrants and searches so just just be aware of them protect yourself your office IP or your you know a known IP is always a better thing to be to be to be caught up in something like this then your personal IP address and there's potentially some brand recognition for law enforcement say you
know black duck or you know Liberty or you know BT are doing some you know malware research or you know some investigation then you know that's that's a that's a different thing to some idiot on a ntl virtual media connection at home you know that's a different whole different world so what have we learn the officers we met were a lot more pleasant professional willing to listen than I imagine this chap would have been I imagine the the actions and those of your clients and employees both online and offline have consequences warrants and events like this may may have may cause you issues so for instance I have a security clearance and I have everyone a code code for which
like they're young people in Hollywood we're looking for volunteers if anyone would like to come along and join in by the way and I run a code Club so now when I go to fill in my clearance forms for either that or the other bits and pieces you know will the fact that a warrants been issued in my name in my company's name against my home address will that will that feature will that be an issue I I don't know you know other repercussions that I'm not you know I'm not aware of yet I tell you one thing my my neighbors were fascinated and very interested to know why there was a marked police car sitting outside my
house and lots of strange gentlemen with backpacks on walking in and out of were walking in and out the house and I think some of them even popped over to say hi just so that they could understand who it was because they're like that we were definitely the talk of the road and got invited to a few drinks parties to explain ourselves afterwards which was which was kind of cool so what else did we learn my father knows I say thinks I'm some sort of crime boss and and I wouldn't rush to another meeting with these officers in a similar circumstances they were fair as I say they were very courteous very professional very very pleasant and
willing to listen which was the key thing you know they were willing to listen and but I'm not sure I would like to be you know in a room with them waiting for a solicitor for another you know for another for another ten minutes or even the rest of the four hours so from now on what have I learned I would like to stay more as a cubicle junkie down the bottom here or a you know standing up talking giving training sessions or breaking people's stuff after we've made them sign a pieces of paper that big we've learned don't provide VPN service to to people that go back to our own IP addresses we're learning about we're learning to make
sure that we stay more bottom-right than going anywhere near the top right from now on and what else did we learn we learned the Hollywood County down is a very very long way from Pyongyang so that's my story my my takeaways that I would say is just be careful look after yourselves when you're researching when you're understanding what's what's out there be very aware of the fact that you and that you don't want to cause the police to have to come and knock on your door either in a friendly way or an unfriendly way so apart from that if there are there any questions as anyone they'd like to ask yes mark it's almost like I placed you there that's pretty
good isn't it if a more explicit paced yeah well I think yes that that would have been a very beneficial thing you know that you know in this case the organization they were looking for specific terms and keywords and I think in this case you know having a you know I know the the solution that they've they've come up with is that they put a hash in into each paste which is a you know an md5 reversal which to break you know an md5 River in an md5 hash of the words this is a test post by company X for any more details please contact blah blah blah blah you know and it's a you
know they've been very careful to to kind of watermark posts so yes you know watermarking what you do don't be flagging up saying you know don't be trying to to hide yes hello
it was more than that was more than that so it's more it was it was it was more than that and so when we add up the cost of me and my business partners day away from work because we were in separate rooms it solicitor and the day after to kind of recover from the hangover of all of this stuff and then you know and then Lister's bills it was it was a it was an expensive Monday sort of Monday that we don't like to we don't like to repeat and it would have been more expensive if they if they'd change toward my door apart which they probably which would have happened if
anybody else know brilliant well I'll be around about for a wee while if anyone has any questions if there's any anything pops up thank you very much for coming and listening





