BSidesNCL (Newcastle) 2022 - MFA - A Golden Attack Vector by Parth Shukla
Show transcript [en]
okay hi everyone i hope you all are doing good so yeah as the screen says my topic is golden attack weapon which is multi-factor authentication system and we are going to figure it out that did it to work efficiently or not also this is my first night stop so forgive me for any mistake that i make during the talk yes to introduce myself i'm part i'm a community leader at bug access which you can share my shirt as well i'm a reader i am a bug bounty hunter and i code in bastion python last but not the least i am security analyst international security so at sequence we work at do we work at api security
and some of our plans are t-mobile verizon tinder victoria secret not this all brand you have heard of at the end of this presentation i'm going to give you a qr code which can help you to find the attacker's perspective of your organization so stay tuned uh let's get started yeah okay so what is multi-factor authentication system so that's a method which requires more than one verification that is when you give password you have to give some personalized information which can help a system or a server to detect that it's actually you who are accessing the account so what do you think did it work till you're not i guess no because uh some some of the new functionalities
rise gives rise to some of new vulnerabilities some of them will see road is as well uh recently like around two years ago there was a account take over one liberty on facebook like the instagram thing with the help of multi-picture authentication bypass so i'm going to discuss about certain uh ways to bypass multi-factor authentication system i also have live levels for you for around three to four ways to bypass so you can see that real things in action so yeah so the first thing i want to discuss is the checkmate which is the direct bypass that how do attacker get easily easily access the system without changing literally anything okay one of the bypass the mitigation of checkmate is
changing the referral header which can be discussed later yeah but this is how the checkmate or direct bypass box so the normal user will have the route like web app signing multi-factor authentication system and resources but what does attacker do he will go to the signing page and without with entering password and username he will bypass the mfa by directly accessing slash dashboard so this way the attacker can really not bypass the mfn access that he shows but the thing that server checked is the referral header that from which uh website the slash dashboard is coming from and that a developer said says slash mfa or slash mdp verify okay now this can be changed when you access the
slash dashboard you can just put the referral header which which i have mentioned in the third point to the target dot com slash otp verify or whatever uh you can find like the slash thing when you request it originally okay so yeah so now i have a poc for this and it's really fun to see this but okay so next thing is the bypassing mf using true force this thing is also known as trial and error method and how do we do this using intruder so those who are bounty hunters know what is included so you can put multiple requests on the only within 10 to 15 seconds you can put 100 requests so you can literally try each
and every otp sequence that our user might be getting like starting from one one one one two nine nine nine nine and use the market otp like three five zero nine and that would be in that way so you can get a bypass by checking this data support so there are total three type of status quo 3x 2x and 4x 2x this is successful 3x is the redirection port and 4x is the error okay so with the help of this you can figure out that if you are getting the success for or the rejection code of the directory okay uh now i'll be showing you the live poc that how this thing is working so it's just too many views you guys
will enjoy this okay so i am putting my for the uh victims username so mfa was used to decide that if even if the attacker has used element password they can still not access the account because they do not have the 2fa code or something okay so here it is asking for 2fa but as an attacker i'll just deselect the 2fps
so i'll wait for the core or the right phone so usually we don't have this this is just for poc so the right four is seven triple two okay now in this functionality we were having the array which was passed as a 2x so i could literally pass any number of 2f record i want to try in this reset mfa and then with the help and if the if the 1 2f record is right i would get the correct response [Music] so here i will put 7 2 in one of the array data [Music] so i pass that long otp capture the request [Music] you can see here in the otp parameter there was a area object which
was path which was one one one one which we pass which is the wrong otp so i'll paste the my payload here which was having pretty much many otps that i would try [Music] you can see as one otp was correct i could get the correct response from the server so this is known as style and error method that i am trying multiple otps i don't know the true otp right but i'm just putting as plc7 so here i could just face uh from one one one one two nine nine nine and if one of them is correct then i can just uh have the access to the victim's account and also the uh was disabled i reset it
the 2fa so every time i need to access now i don't need the two ff you can just access with username and password yes so this was awarded 200 of bounty it was pretty serious because i could if i have a password which they can access from any social engineering attack or a click checking thing called like getting access to password is pretty easy so you could just do social engineering on the employee or the victim once i get password i don't even need to write 2x4 i'll just put from 111 to 99999 and otp is correct [Music] yeah the third one is a default open now this you won't find it many times on the
backpack because developer are pretty smart now all your time back in 2017-18 we used to find this or not because as a developer you don't want to enter the correct odp every time that you receive one sms or time based utp but that would be that the testing purpose so they created something known as default tokens which means that every time for a tester or development is zero zero zero zero that is just an example uh you will get the output correct because that was allowed it was a 200 okay status okay so this you won't find it every time but yeah it's still out there many developers forget to remove the default otp and the most common default otp in
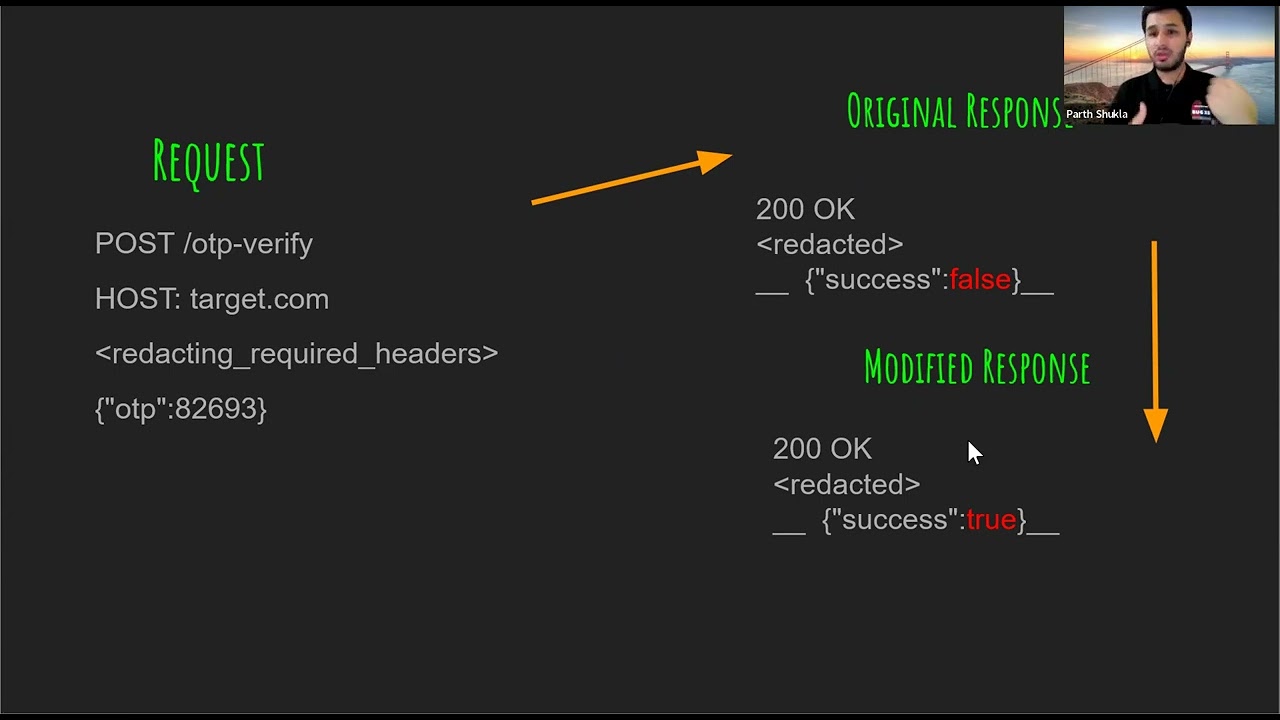
my experience which i found is zero zero zero zero and nine nine nine nine because developers don't want to write the correct opinion every time okay the next important and the most most expensive thing is response manipulation one suit is once a software which can help you to manipulate the response you are getting from servants which is pretty nice pretty pretty amazing so as i told you before there are three common responses for 2x6 3xx and 4xx 2x is okay 3x6 is 3d direction and 4x axis error i have found this vulnerability last week one day on one of the biggest it company uh i i was not sure that it would be out there on this big company
but it was that i could literally take over any account in you now it was serious in this case because these guys actually removed the password field and what they did was while you registered you gave a phone number and an email account now every time while documenting you put that email account you'll get otp on your phone number which is registered and then that you have entered so the biggest mistake that i was i did was that i directly reported it what i should have done was i could have literally taken the email id of any person who is high up in the ladder like maybe a senior director or vice president you can get that on contra dot
io okay so once you have that you don't even need their phone numbers you can just put their email address 150 otp just put on wrong otp and a play with the response folder and that is how we can bypass the one impedance so i got around dollar 1500 for this because i could literally do accounting for any users that were on their website i have a live demo for this also which i'll show in a while so this is not the request
response would be success is false because [Music] but when i modify the request which is true then server won't check the thing it will get that okay i'm getting this access to i'll just pass out the resources or the related resources on our our true parameter okay now there is a motivation to this as well which i mentioned at the end when we discuss the mitigation part okay so this is the uh poc which i would like to show you guys it's little poc but uh it's like really really important you can find this bug as soon as this presentation is what it's out there everywhere
[Music] so i do simple yeah so i get the confirmation code so first what i'm doing is as an editor i am uh getting my correct response like i would first get the correct response for my account and then i'll copy paste the response or the correct response for the invalid response of the victims account okay so right now i'm collecting my correct response that access i have on my account request
okay so this is the correct response that we will be getting which is the account that i have accessed
and let's wait for the correct yeah so this is the correct response that is 200 okay
yeah so copy paste that correct response which i cannot show because i don't have the disclosure permission [Music] yeah so i can i'll get the set new password okay which i don't have to do because that's my account now we don't use that response and we go to the victim segment directly yeah so we change the username to wikipin
i have to continue address that works
yeah so we put any random confirmation for because we don't need that we are playing with the response here so we capture response to this request
and now we paste the correct response that report caught for our account okay which was 200 okay
so with this matter also you can take over any account you want or this was awarded bounty as well because no end user interaction is needed so you can just change the password
yeah put any password to sheets so they won't know that they will get an email that password is changed but till they do the reset password again you will have access to the listings account which is pretty nice but without any user interaction you can do account over with this one so that is why i feel that mfa if not configured properly can bring huge huge huge attack vector for your convention yeah so hence you can see i was able to change the user password and gain access to the user account without any interaction so now this is an unusual way to find bypass you won't find this um like this is not even a bypass this is a
basic logic flaw that you would be getting so it's like you would create an account and you turn off the multi-factor authentication system now log out from the account go to forget password page and you will change your password and if you're not ask the mf report that means that you are able to bypass it now how you can able to find or why this is an issue now you if you are forgetting a password that doesn't mean that you don't have a access to your unique otp device if that's an sms or a time-based authentication system it shouldn't be like okay i forgot the password then the system need to change the multi-factor authentication system as well which
should not be the case so if an attacker even tried to change your password in the earlier case if it changed the password then it should not have disabled the mfa okay so this is a way to find a part this is a simple logic flaw that the server might be about the organization might be having and you should try so many times but bounty hurts for synchronity and unless forget this type of bypasses this type of business logic flow that if a victim is for the if the user is just resetting a password then you don't need to disable the mf8 and it doesn't mean that uh user does not have a mfa device
okay now this is a good good vulnerability definitely as an attacker it will take time for you to expect this vulnerability because but you have to create a csr responsible which is not the responsible csrf webpage which is very easy to make using purposes uh but yeah csrf is used for the cross site request policy is used to bypass a certain restriction and it forces the user to accept executed action they do not intend to means adding a product to a card or resetting mf or designing password deleting the account all these type of vulnerabilities can be exploited with csr okay so now let's check this bypass in action
there you can see when you scan the barcode you get a this is a time based otp like google authenticator
so time expired when i was trying this
so when it is time i should be you need to be pretty quick because every 60 seconds or every 30 seconds the code expires okay so you can see now 2fa is enabled
yeah so if i want to disable i'll capture the csrf request which are sent to the attacker so without any authentication if if the attacker clicks on submit button then the 2fa would be disabled automatically
so this is that accuracy form
will get access to the pocs as well and i have removed the target name uh because of the disclosure permission and each of this vulnerability is insane transfer so you can try to find a bypass then please report that in security so you can see now 2fa is enabled and i have the request to disable the 2fa you all can see from plc that how can i uh make the csr form immediately from the headphones
so i open this and i'll submit the request so technically it should give me the error but in this case it won't because i have logged into my account and if i click the submit request i'll get data and when i check it here when i replace the page you can see the tool is disabled so if i have the password for the account and i want that victim should disable the 2fs i can gain access i just put a csrf form with the help of social engineering has sent him by me because i have the email already and as soon as he clicks on submit request and if the account is locked in the 2fp will be
disabled or what will happen if the user clicks on supplement request and if he or she is not logged in the login page would appear they will log in and as soon as the lock in the 2f would be disabled and that is how i can gain access to the themes account
you can see it's enabled okay so yeah nutrition yeah so how to mitigate this appropriately now this is there is bypass to everything i believe that no system is perfect there is always a bypass to each mitigation that a developer made so some of the uh mitigation are that ensuring that otp verification is happening on is not happening on clients it is happening on the server side so attackers cannot play with the server side if it is happening on the client side you can easily bypass it just like the first thing which is that checkmate that if if it is happening our client said you can directly access the resource and you can bypass it
the second thing is otp is not written response point now what happens is that sometimes when you capture the send code button request and when you uh capture the sponsored request you will get a message saying that okay xxx would potentially was sent to the moment about this which is a bad bad implementation okay now it might happen that when you are uh capturing that request you will find that the gs file is being ruled any temporary dot gs5 and when you capture that request you'll find that the 2fa is leaking in the gs body as well so in any response body otp should not be linked and if you use otp should not be used
that is how does it how does that work so or you might have known the term shoulder support so if i'm just passing by and if i know that okay this is my target and i know the otp or the otp which was used before the that otp should be expired in the second case which we saw the error thing so even if the otp was used and it is present in that array the response would be to include okay because you are allowing the reusation of otp and there should be a proper expiration time um which is generally should be 15 minutes because you don't know the delay of a legitimate user is giving
so yeah these are the some of the mitigation that you should work on okay now any questions then i'll be by taking any questions which you have and yes this is the qr code i was talking about to gain a attacker's perspective of your account you can just put out you can just go to this qr code and register and you'll get everything what are the wonderfulities that you want to have and yeah that's all thank you so much for joining in and you can visit any of these this is my personal website departure.com and my community and stuff so if there are any questions i don't know if you could hear it i suspect you cannot but there was a nice
pause does anybody have questions at um there are no questions so okay thank you very much thank you so much





