A Brief History of Spyware in Mexico: A Civil Society Perspective

Show transcript [en]
Okay, who am I? I am Paul Aguilar. I work in an organization called Social TIC. Social TIC sees technology issues in human rights contexts, journalism, activism. I studied engineering in computing at UNAM and now I am the coordinator of the digital security area at Social TIC. So if you want to look for me on the internet, that's how I am. "Pencer Bjorn" is a little difficult to remember or say, but you can find me anywhere. Next. And as I was saying, Social TIC focuses on technology in human rights contexts. We provide training, workshops, quick response to incidents, forensic analysis, all of this dedicated to the band that is doing activism, journalism, incidents in the country, so they can continue doing their
work without being attacked digitally, which is a very big trend in our country and in the region in general. So, today I'm going to talk to you about the work we do there. This is focused on spyware issues, which are the most complicated things that happen, but quite interesting. And, next please. Just as a disclaimer, does anyone here work in the government, in the police, in Sedena or something like that? No? Operan Pegasus or something like that? No? We're good to go, nothing's wrong, this is neutral land, we're in the B-Sides, it's a good space, we're in community, we can talk later, with a calm, a coffee or something. So, well, here it's just going to be that, this talk
is going to be full of some social political elements, so if someone works in government, don't be afraid, please. Okay, okay. SPEAKER 1: SPEAKER 2: SPEAKER 1: This access is usually silent. It is based on quite advanced attacks, for example, vulnerability attacks from day 0 or vulnerabilities already known but in outdated devices. And when the software is implemented, it has access to a lot of information. Depending on the software's capacity, it can access basically everything on the device. So, for example, that image you see there is a report that was filtered from NSO. which is the company that develops Pegasus. So, there you can see how in the technical manual they promote that they have access to everything on the device. Calls,
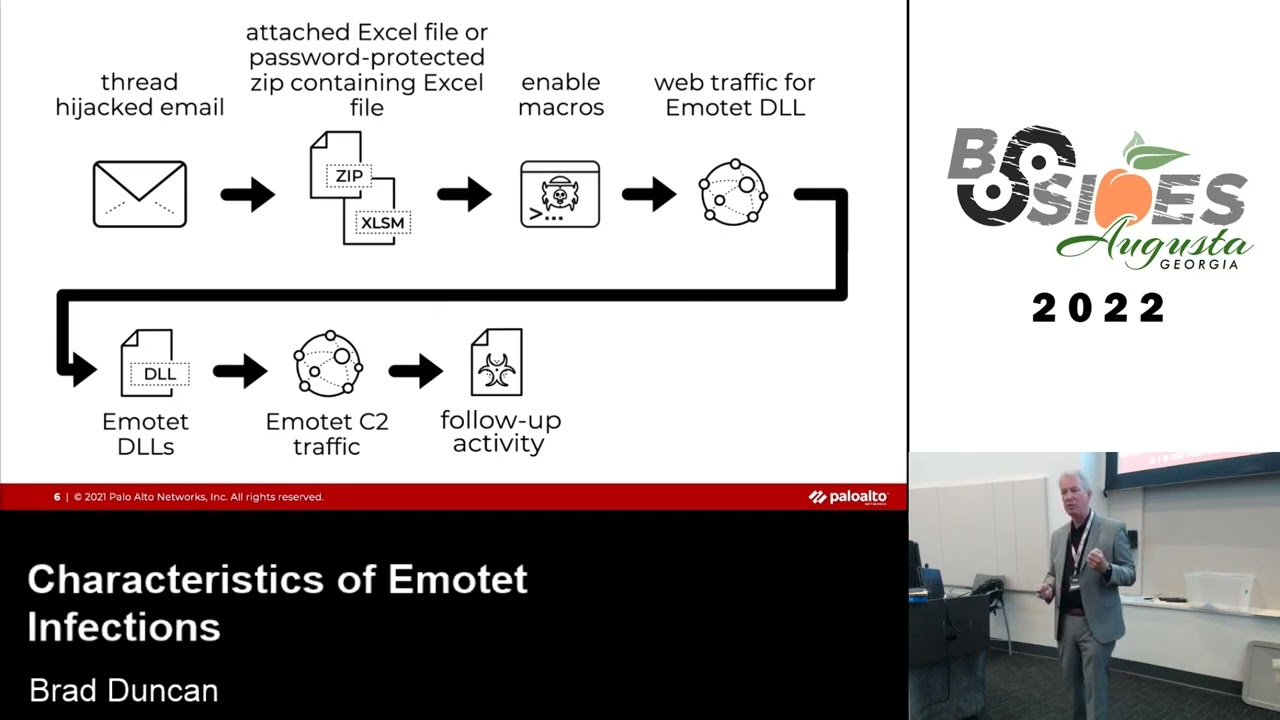
messages, emails, files, contacts, real-time location, etc. Nothing surprising for these times, 2024, but this was filtered approximately in 2016. So, if you remember the time in mobile, in that time, it was very different. Mobile devices were very different, right? But, well, when we are talking about... When we are talking about spyware, we refer to this type of technology. Now, spyware is not only the software that is installed, but it is a whole suite of tools. For example, here you can see that this is part of the infrastructure that is used to perform an attack with spyware. So you can see that, for example, So, you have the target, which is here, and there are different types of attacks. There can be an
attack by installing a middle box, which is a tool that modifies network traffic when the person is connected to that network, and therefore can make a malicious traffic injection. There can be complementary tools that allow, let's say, a part of monitoring, of recognition of the victim, and from there, be able to design the attack in a more sophisticated way. So, for these spyware-san attacks to work, Now Who sells these tools? Globally, there are different security tools suppliers. There are some focused specifically on tactical tools, offensive tools, like these Spyware. And here are some of the companies a little more well-known. For example, Candiru is one of the ones that became famous, more or less, in the pandemic, because a spyware was being developed in the
Middle East. In the case of Mexico, we have been frequent customers of NSO Group, Hacking Team, and here you can see the products they sell and some of the countries they sell them to. In the case of Mexico, Mexico is one of the main customers, since Felipe Calderon's time, software of this type has been bought, although previously there were other tools, for example, for telecommunications intervention, things like MCCatcher, tools to monitor the telephone network, etc. But this, as you are already seeing, is in the device and has access to information. In Mexico, this is just a map so you can see where the main companies are based. In Mexico, as I was saying, NSO Group
is the main provider currently. It's in Israel. And FinFisher is a company that was German-English and Hacking Team in Italy. I mention these names because they are the ones that are known here, but they have already changed their name for things that we are going to talk about right now. And well, in Mexico, how do you sell this? Well, you have resellers. You have local companies that make, let's say, a listing to be able to earn the license, and then the official suppliers in Mexico become. So, in the end, we have companies that here in Mexico resell these products to the fiscal authorities or governments. This is interesting because over the years we have realized,
and I mean civil society in general, that many of these companies are ghost companies, for example, and that they are linked to relatives, to people who work in the government, who have connections, for example, in Israel, and therefore have, through this partnership, if we want to call it that, access to licenses, they give them licenses to put a company in Mexico, and then they sell it to the government, right? But it's a closed circle, economic, political, and power. There have been cases where even these companies, when their physical home has been searched, it doesn't exist. I mean, here, Torre Diana is very beautiful, but these companies say that it's foreign And, well, in Mexico, in theory, there are very few entities that can buy this
type of technology. In theory, they only sell to organizations in particular. For example, security and intelligence agencies, like CISEN, they are in theory enabled to buy this type of tool. Security forces, like, for example, the SEDENA or the SEMAT, the Navy Secretariat, the Defense Secretariat, - is Or Okay. Okay, so this is just context to warm up the engines. In Mexico, there are many technologies for surveillance and espionage, but the three most well-known are: Fin Spy, from the company Fin Fisher, Remote Control System, from the company Hacking Team, which was made up of the tools Galileo and Da Vinci, and Pegasus, which is from the company NSO Group, and the one that you've probably heard the most about. So, these
are the three main families, because they are the ones that have invested the most money. But there are many other solutions from smaller companies that continue to take advantage of these exploits or vulnerabilities to develop solutions. These, in general, have been bought, for example, by the federal government, but we know that there are smaller entities, states, that have also bought other solutions. In the case of Finn Fisher, this tool was used in the time of Felipe Calderón and Peña Nieto, more or less between 2011 and 2014. So it was one of the first tools that was documented here in Mexico that was used, for example, against activists. And then there was the remote control system
that was used on similar dates, also in the sexenio of Calderón and Peña Nieto. And here there is a political justification to say, well, the fight against organized crime, which I think we all grew up in that time, at least because I can see, we know that it was complicated, a lot of violence, a lot of talking about criminal drug trafficking. Organized, then there was a justification to use these technologies and later at the same time it was used Pegasus but it is also still used today, so currently these two tools do not have evidence that it is still used but only Pegasus and this is interesting because you can see that more or less
in the same states they stopped using and we are going to talk a little about why but currently the most used is Pegasus and something relevant is that in the current government foreign But they have continued to spy. So that's interesting because in the end we have the three political blocs of Mexico using the same tools. We have the conservative side of PAN, the PRI side, and the black side. And all governments have used these tools with the same objectives, and they are not to capture organized crime. Spoiler. Okay, so who has used these tools? Well, in the case of FinSpy, more or less around 2014, it is documented that four entities used them. The Public Security Secretariat, the
PR, the CISEN, and the Major Presidential State, which belongs to the military. So these four entities are confirmed to have been used. Oops, something happened. Okay, well, while you read, nothing happens. Okay, good, thanks. Then we have Hacking Team, which with the Remote Control System tool was used in 14 entities. Here we can see a brutal growth in the use of this tool in a similar period. And something interesting that I wanted to highlight here is that we are already talking about state entities: the State of Durango, Querétaro, Puebla, Mexico City, and the Federal District. We have some federal entities, such as Sedena, Semar, the Federal Police, the State of Campeche. So we started to
see that it is not only used at the federal level, but also at the state level and by local governments. And this talks a little about the uncontrolled and the unmeasured use of these tools at the local level. In the case of Pegasus, when it starts to be investigated, this decreases a lot, but it only decreases in the use of Pegasus. This is important to mention because Pegasus is currently operated by Kerl Cisen and PGR, and currently it is operated by Sedena and the Navy Secretariat. There are suspicions that in other states at the local level other tools are still being used, other solutions that are not so powerful because the form of attack is
different, but they are still being used. In the case of Pegasus, it's only at the federal level. And here's something interesting, because if you see here, it says "Center of Military Intelligence". Has anyone heard of the Center of Military Intelligence? Raise your hand. Okay, one person. Okay, just one. The Center of Military Intelligence is a group foreign to the CDNA, using a tool of espionage of military degree, without an order of a judge operated by a group that in theory does not exist within the current military structure. So this sounds like a movie, but that's how it is. So that's how it happens. And here the problem is not that these tools are used, but
against whom they are being used, which is a bit crazy. the Fin Fisher. Están documentados, pero no a este nivel. Estos de Pegaso ya tienen un nivel de documentación y colaboración mucho más amplio. Entonces, los primeros que se documentan son en 2016 y se ponen en 2017. Y están enfocados a personas que trabajaban en el sector salud. ¿Sí? ¿Alguien de aquí ha visto esos sellitos que están en la comida que dice alto en grasa, alto en azúcar? ¿Sí? Bueno, ese grupo que puso esos sellitos, lo cual es bueno, les prometo que es bueno, ayuda a su salud, aunque se enojen. Son los mismos que pusieron impuestos al azúcar, por eso la Coca-Cola. But that has a public health logic, that if you put an tax on sugar,
sugar goes up and therefore it is consumed less, in theory. So when all this development of public health was happening, there was an interest, let's say, between a company that sells soda and the government, and they said, well, these activists are going to give us problems economically, let's see what they are doing. And they were spied on. So the first case of espionage with pedophiles, well documented in Mexico, is of people who were trying to put taxes on sugar. And this is also important, and I emphasize this case a lot, because it is the only case worldwide where there is evidence that there is a link between companies like the sugar industry, or the soda
industry, and the government. So, when we talk about particular political theories, we should use these tools, because these lines begin to be drawn. After that, many of these cases focused on issues that were directly related to private interests of the government. For example, the White House of Enrique Peña Nieto. That was a case in which Enrique Peña Nieto and his family took a house with a lot of money. It was not possible to prove where they bought it. And well, the Carmen Arcegui team, which I think everyone here knows, began to investigate and boom, they were espied. Also, there was talk about the Rancho del Sol massacre, which was a perfect massacre. perpetrated by the
army, in collusion with organized crime, and the people who were investigating and documenting that, when they became public, they were, ah, spied. Panama Papers, Panama Papers, it has to do with corruption issues, the people who invested in the Panama Papers, ah, spied. And, well, Ayotzinapa, I think that most of us here also grew up in the context of the disappeared students, who at that time didn't have much information, now they have a lot more information, especially what happened in Iguala at that time, but the family members of the disappeared students of Ayotzinapa were spied on for being asking the government to do their job. And more anti-corruption issues, right? So this is 2017, here is
the full picture. All these images can be found in the CITIES and LAB reports, which is one of the organizations we collaborate with to do this type of work, and they are public, they are very good reports. If you are interested in the subject of spyware in Mexico, I recommend you read it. It has forensic methodologies, topics of context, and everything that has been found in these years. Then, espionage cases continued to appear, specifically the G.A. was attacked, the G.A. was the group of experts that came to Mexico to do all the forensic and legal analysis of the Ayotzinapa case. They were people from other countries that came to Mexico to support as a specialized
commission that did not have a conflict of interest between local governments, federal governments and family members. So they were espionaged, because they came to work and obviously things were going to come out that the government did not want to come out. Other cases that came out, for example, was the Narvarte case, which if you don't remember, the Narvarte case has to do with a Veracruz journalist who was investigating the nexus of Duarte, the former governor of there, the same one who gave water to children with cancer instead of medication against cancer, that same one. This journalist had conflicts with Duarte. And well, he came running to Mexico because he suspected that they wanted to kill
him. And when he arrived in Mexico City, they killed him in the Narvártico colony. That's why the case is called like that. A whole topic was elaborated there to say that he was not assassinated. The evidence says the opposite. But just the lawyers who were carrying the case of the involved people in that case were espied. Okay? So it's very complicated not to suspect why these people are being espied when you see the topics that they are investigating or working on, right? - And then he tried to spy on his collaborators from the media called Rio 12. So there is evidence that the murder of the journalist along with the espionage of the media is quite linked. And he also tried to spy on his wife. So
this is quite interesting. If you pay attention to the images, we can talk about how all these attacks were implemented through phishing. So here someone is going to give a phishing talk. We can go to... um The person enters, through phishing, the vulnerability is activated and the device is infected. When they don't click on this, they start sending messages a little more focused on their intimacy, right? Making friends, family members say, "Hey, how do you like this report?" When the words are missing, we can receive a single attack, as a reference to the murder. So the person says, "Well, what are you saying?" They get in, click, and they're infected. So this was one of the main media of Pegasus attacks a few
years ago, phishing. Right now it's evolving, I'll talk a little more about it. But well, we can talk about the case of Javier Valdés, who was murdered. There's another journalist named Cecilio Pineda, who was also murdered and who later, in the forensic analysis of his devices, it was revealed that they used real-time monitoring tools to know his location a few hours before his assassination. It wasn't Pegasus, it was a tool called Circle, which is for telecommunications, for the SS7 protocol. If anyone knows about that, they'll understand. So they relocated him and, well, things happened. So, as you can see, it's a pretty complicated context, right? The list continues to grow. There are even people, I
don't like to say this, but there is Ricardo Anaya. Ricardo Anaya was also espied, opposition like Claudio X, who I mention a lot today. So there is a fairly indiscriminate use and control of these tools, but the evidence points to the use of more against journalists and activists. Everything I mention right now is included in something called government espionage. foreign This investigation revolved around a 50,000 phone numbers leak of possible objectives of NSO Group, which develops Pegasus. And in that list of 50,000 numbers, 15,000 were Mexican. So, in terms of proportion, we can see that the list was quite large. Not half of the users, but a fairly high percentage, probably almost a third of phone numbers. So,
that reveals that there are still many numbers that have not been identified, many people have not been identified, and a search for this type of thing begins again. And voila, more cases come out. So, since 2021, more cases have been coming out. For example, the young man, well, the cowboy up there, his name is Raymundo. Raymundo investigated massacres that took place in the north of the country, perpetrated by military, that is, state crimes, and espionage. We have journalists like Ricardo Rafael, or the political animal media, who also investigated violations perpetrated by the military, by the state, and who were also espionaged. So, there is a pattern again, there is a use against issues that bother
the government, but specifically in this case, that have to do with military. They are spying on the Centro Pro, which is an organization that provides legal support in defense of human rights. They advised the families of the missing people in Ayotzinapa. So they are being spied on again and again for all the work they are doing with the families and other types of investigations. So, well, there are still cases. The last thing I will say is when they spy on these people. Does anyone know who the person up there is? No They proved that this happened. There were state crimes perpetrated in the military bases here in Mexico City and other places. They start finding all this and start writing reports
to tell the public what is happening. And obviously that is uncomfortable because you have people from the government with the capacity to do these investigations that will reveal new state crimes. Well, you have to spy on them. So spy on Encinas, spy on the team that does these investigations from within the government. And, well, all this leads us to the fact that, in theory, these tools are being used, yes, by those who could use them, but there is a lot of evidence of cases where there are strange things, organized crime, personal interests of certain politicians, of parties, very strange things from the sugar industry. So, really, this, although the final operator is a criminal, a
There are no judicial orders and the issue of national security is very diffuse because then it is understood that a threat to national security is all that person from civil society who is looking to make things transparent, who is looking to evidence things that are wrong in our country and that, therefore, are a danger to the government. So that national security part becomes problematic, that speech, right? Even AMLO, one of the morning hours when these cases were revealed, I don't know if you heard, said, we don't spy, we do intelligence. So there is a lot of play with that speech and I think that you will understand it very well, you know the difference between
the two. is From SocialTIC we are part of a coalition, the Coalition of Digital Rights here in Mexico, and it is a work that we have been documenting between several organizations. There is the PRO Center, which offers support for human rights. There is Article 19, which offers support to journalists on issues of freedom of expression. SocialTIC, which we support in the technical part. And R3D, Network for the Defense of Digital Rights, many people know it only as RET, so we call it R3D, which is legal and would be like an electronic frontier Mexican foundation. So, they are some of the "cracks". You can follow all the organizations if you are interested in these topics. And well, these organizations
are the ones who have been documenting these cases, generating evidence, providing all the legal, technical, human rights support that is needed. And we have also made international alliances. For example, Citizen Lab. Citizen Lab is a laboratory that is in the University of Toronto, in the Monk School. And well, they are pioneers in the whole issue of forensic analysis. They did the first analysis of Pegasus and Finn Fisher almost 10 years ago. It was interesting because they published a report of a journalist who was spying in the Middle East. And when they publish the report we say, hey, that message looks very similar to the one this journalist colleague received, Rafa Cabrera from the Aristeia team.
So it looks very similar. Let's see, let's review. So it starts to be reviewed, the analysis begins to be done and it turns out that it was the same, that it was the same infrastructure, the same attack methodology, the same technology. So from there we started to scratch. but it was thanks to this type of international collaborations. Also with Amnesty International, they have a team called Security Lab, which is a security laboratory that does forensic analysis for journalists and activists. We collaborate with them a lot. And Access Now, which is an organization that defends digital rights. For those who don't know, digital rights are human rights on the internet. So they are human rights, they
have to be respected. And AccessNow does a lot of this work. They have a global helpline where they can receive cases and derive them locally. For example, SocialTik is a contact point for any of these three organizations to do the local triage, do the early detection and, in case necessary, scale the analyses and investigations. And as I mentioned, we launched the spy government campaign in 2016-2017, where the first cases were documented that were linked to phishing attacks. Much of what is known is about Phineas Fisher. Has anyone here heard of Phineas Fisher? So Thanks to the hacking that this wonderful entity did, many documents, emails, contracts, technical manuals were leaked. And many transparency reviews could be made that the government did not want
to deliver. For example, if a transparency request was made, hey, what did you spend this money on? It did not respond. But here there were emails and contracts where that money, that transaction, matched with a purchase. There were assistance emails to help them install and configure the tools. So much of what is technically known in the first cases started from this. Because there was information that was leaked. Phineas Fisher has some guides called Do It Yourself Guide, Hack Pack. So you can look for them. And they have a methodology to do hacktivism. How to identify a target, do the recognition, enter, do the pivoting, extract the information, how to share it safely, etc. etc. SocialTik
does not approve of hacktivism as such, but if someone accepts hacktivism, we thank them very much. Because they help humanity a lot. So, well, Finas Fisher did this. He has done other wonderful things. He hacked the police in Spain. He hacked banks in the Canary Islands. He gave money to NGOs. He has a hacktivist manifesto with very Zapatista tints. Very indigenous communities, Latin American, with - So, if a hacker of this level has it in mind, I think we can have it in mind. So, check out their manuals, they have very good tutorials. And, well, that's for the first case. For the second case, which is the spy army, here we found that the final operator
was the SEDENA. The SEDENA and all the cases that were documented, like the ones I told you about, only have to do with investigations that revolved around organized crime or the military. So, it makes sense that the SEDENA is doing intelligence actions, but, well, it ends up spying and things happen. A lot of what is known also comes from the Wakamaya Leaks. This is important and it is a very cool quimio because if you review, if you are going to say that on the weekend I will look for who is Finesse Fisher and then if you say now I'm going to look for who is Wakamaya, you will see that the attack methodology is very
similar. Even the political statement that Wakamaya makes when it makes its tutorials, its videos of how it accesses certain infrastructures, has the same touch. So I have a dream, Guajiro, in which Finesse Fisher and Wakamaya collaborate. But well, a lot of what is also known about the Sedena is from the Wakamaya Leaks, which I think most people heard about. And well, what happened here is that they infiltrate the server of the LACEDENA, they extract private communications, and from those private communications it is identified that it is the CMI, the Military Intelligence Center. Why? Because the CMI was already suspected, we already said, let's see, here is an operator, here are some strange things, there is
something that says CMI, but we don't know what that is. So when this information is filtered and the analysis of the documents is done, it is already found, Military Intelligence Center. its organigram, its logo, its operations, tactical intelligence reports. What did we say? Let's see, we have a forensic analysis of this device that says it was spied on a certain date. But we have the forensic analysis, we lack the context. So when these documents were found, there were reports with the same dates where a report was delivered to the superior command. So they said, well, there is a forensic analysis with dates, there is a report with dates, well, everything makes sense, right? And it
already has the context. So much of what is known at the contextual level and that was complementary to the forensic analysis comes from the Wacom and Alexa. And well, just to finish, In case there are questions. There are some things that are being requested, right? For example, that there is regulation and transparency in the use of these tools. Nobody is saying that they don't use them. Just use them for what it is. If they buy them to fight organized crime, terrorism, or whatever it is that is against national security, but that is a real danger and not that they are parents of babies. Well, I'm not going to make that comment. If you read the
Guacamayalix, you know that they identified groups of feminists, of parents, of missing people, of babies that died burned in the battery, sometimes. All of that is being monitored and spied on. So, let's see, if these tools exist, cool, but use them for what they are. So, for that, regulation and transparency are required on who buys it, who uses it, why they use it, for what. It's the only thing that is asked. So, also for that, it is asked that there are internal installation rules, use criteria, and technology disposition. So, again, we just want it to be used for what it is. And something very specific that Poland started to innovate in the last year is
guaranteeing the right to know and have access to your file. If you follow the Spyware issue, you will know that Poland had a change of government recently and that it is making public that it spied on certain people, they are being notified, they are being given access to their file, and well, that is a fairly useful transparency exercise. So that is what we have been asking here since 2016, which has not been achieved, but which is being implemented in other countries and which is good, it is good to know. Again, this is illegal. As you can imagine, all the cases we mentioned have nothing to do with national security threats. It is done under the
expected legal framework. There is nothing else to say to defend them. There are some things that are also asked to be clarified because they have been going on for many years. I was in the train when I was very young, I'm still young, but I don't feel that much. So, many of these things are already being resolved, because there are people who were my age at that time and who are not so young anymore. So, we simply want the General Prosecutor's Office to do its research, its job. For example, the case of Carmen Aristegui has been going on for years, there are many other cases that have not been moved forward. We want transparency responsibilities
to be respected, which would come from all the lines I mentioned. And above all, that there is no repetition of human rights violations. For example, the Pro Center has been deported twice. There are journalists like Raimundo who have been deported three times in a period of a year and a half, two years. So, simply, let this not continue to be repeated against the actors who should not be. And for the gang that is here, let's not be mercenaries, okay? There are very smart people in our community, those people are the ones who end up building these exploits, finding these vulnerabilities, developing the command and control, the interfaces, the operational manuals, so let's not be mercenaries,
okay? We have to use our knowledge, our wisdom, our superpowers, hackers if you want to call them that, for a good, okay? If your good is to work in a company and have a good economic life, good! But while you're not investigating people who are investigating why they gave water to some children instead of giving them drugs against cancer, for example, okay? So use your superpowers for good. If you want to talk to Social Tick, you can find me. You can look for me directly. And well, don't be mercenaries, work for good or work to be happy, but let's not hurt anyone else. And well, that's all. I don't know if there are any questions.
That was a GIF, but we're posting a PDF, so you can imagine that it turned around. And that's it.