Secrets No More: Quantum State of the Art and Advances in Codebreaking | Alexey Bocharnikov
Show transcript [en]
our first Speaker after lunch break is Alexa bonov Alexa has been at the Forefront of Technology Innovation for over 15 years he brings a unique mix of quantum techn knowledge and cyber security strategy expertise to his work at Accenture currently he's an Asia Pacific Regional leader for Quantum security and director of cyber security strategy presenting a talk titled Secrets no more Quantum state of the art and advances in code breaking breaking please invite Alexi to the
stage everyone let me open my nails quickly so Quantum in this talk I see as my primary objective to to talk you through this topic so you can make better decisions there are so many misconceptions you you all heard this term you read about it you watched YouTube videos and through all the discussions I've been involved into I rarely see a person that has you know blocks aligned in the right way usually there are so many things that are not right and that's what I want to help you here I hope after this presentation you know what to ask what to look for where not to to get trapped so let's go straight into that the first
one or I should say probably my presentation is built like on those most common questions I see and they are in the order as they come so first one there are two really different things one is quantum Computing and another one is quantum risk so when you hear Quantum Computing what people refer to is they refer to a problem that they want to solve and they want to solve it with a quantum computer which is a physical device and what they hope to do they hope to do it much better than you can do classically whereas when you refer to Quantum risk you don't need a quantum computer at all like the whole thing is
very classical like the solution to this problem is classical all the things you're going to do to remediate it are classical you don't need a quantum computer at any shape or form in any of the steps where you remediate Quantum risk it's all about cryptography it just happens that quantum computer launch the discussion and probably because of that Quantum get attached to this word risk but it has nothing to do with Quantum so I just want to underscore it once again Quantum Computing a device itself an algorithm an algorithm and the belief to do it much much faster the risk is very classical now going to the next one uh that's I like a lot so look these are
nine terms people like word Quantum they attach it to all the words when they name things and it does not automatically put that term into the same bucket I just put nine of them and you are free to think about any other things and you'll ask me in a moment so before I go and explain let me ask the audience so guys how many of you just rise your hand think that all nine of them are related to Quantum Computing so a quantum computer is implied there to do something all nine of them anyone hands the next question seven yeah take your time read it I'm not rushing no one I see the whole audience I'm saying no one because those
who are on the front rows don't see those that are in the back rows five half of them one two three roughly five awesome five then three okay roughly half of the audience one uh another three and no one like none of the related to Quantum Computing okay so the right answer is just one let's go one by one through each of them so Quantum magazine is just like a paper people decided Quantum is a fancy word and named that a magazine also I like very much when in presentations when people want to name articles they bring the word Quantum and attach it and sometimes they even use Quantum Leap implying that they'll jump so fast and
so forward word so no one will see how fast they move so you should keep in mind Quantum the word itself means like very very small minuscal whenever you hear Quantum lip or Quantum jum what they say is that they'll jump so small that you won't even notice how far they jumped then Quantum Internet that's a complicated one so whenever you hear Quantum Internet what people imply they refer usually to a thing where they aim to build a network that allow to distribute in t fent between quantum computers so you do kind of distributed computation it's not our classical internet that becomes better it's not like any other thing it is just a distributed computation on a quantum
computer though this term like is not yet well defined sometimes people refer to Quantum key distribution and we'll speak about it later but in most cases like whenever we speak with academics what is implied is that you have one computer in Melbourne another one in Sydney and you somehow wire them so you like have one device then Quantum terminal that's a physical place here in Sydney next to the Central Station where government invested and they built like four story building three story thing where they brought all the startups with Quantum and they just called it quantum terminal obviously nothing to have with Quantum Computing then Quantum sensing so whenever you hear that one what you
should think about that's like you have a box a chest maybe of a different size smaller or bigger and something happens inside you don't care what happens inside as an outcome you receive a classical bit of strings strings like like a reading of a some parameter magnetic field gravitational force whatever you want to read and you just process it on your laptop or on a server so you don't need a quantum computer neither inside nor after nor before to do that stuff it's like a an advanced measurement device quantum optimization so that's like I like one of the most things all this one because that's the cheekiest one so what people imply here is that someone was aiming to
build a Quantum algorithm that's hard so he started resarch the field thought thoroughly how can he apply things that Quantum can do to his problem and then came up with a classical algorithm which is not Quantum but because he s a lot he was inspired by quantum physics by things how the work he literally called this Quantum inspired and in this case optimization so there are many other things apart of optimization so Quantum inspired no Quantum Computing Insight it's just someone learn the field and become inspired and do did something classically Quantum Leap we discussed Quantum Computing obviously you need a quantum computer to do something better you hope it will be better not necessarily always but you hope that
Quantum risk that's the one that we're going to speak here about cyber security problem cryptography no quantum computer needed to solve it and the last one Quantum cryptography so Quantum cryptography this is a common thing that people in cyber security tend to kind of throw and what they imply is that there's some cryptography that exists and you need the quantum computer to run that cryptography algorithms on a quantum computer and that's the only way how you can get protected from Quantum risk so that's not true Quantum cry cryptography as a term just does not almost does not exist it is some sort of an academic research that's in its infancy where people try to build
Advanced cryptography algorithms that are not anywhere close to production where they try to use quantum computers to do some Advanced cryptographic manipulations but in today World in our day-to-day jobs whatever and whenever you think about cyber security and here term quantum cryptography it is not in any shape of form related to Quantum Computing now with that knowledge I'm sure now you craw much better through things where people try to kind of trick you and bring Quantum Computing where there's none like if anyone wants to ask any other term you have in my mind in your mind right now let's just try and see if I can help you if no we can just wait until the end and bring it to the
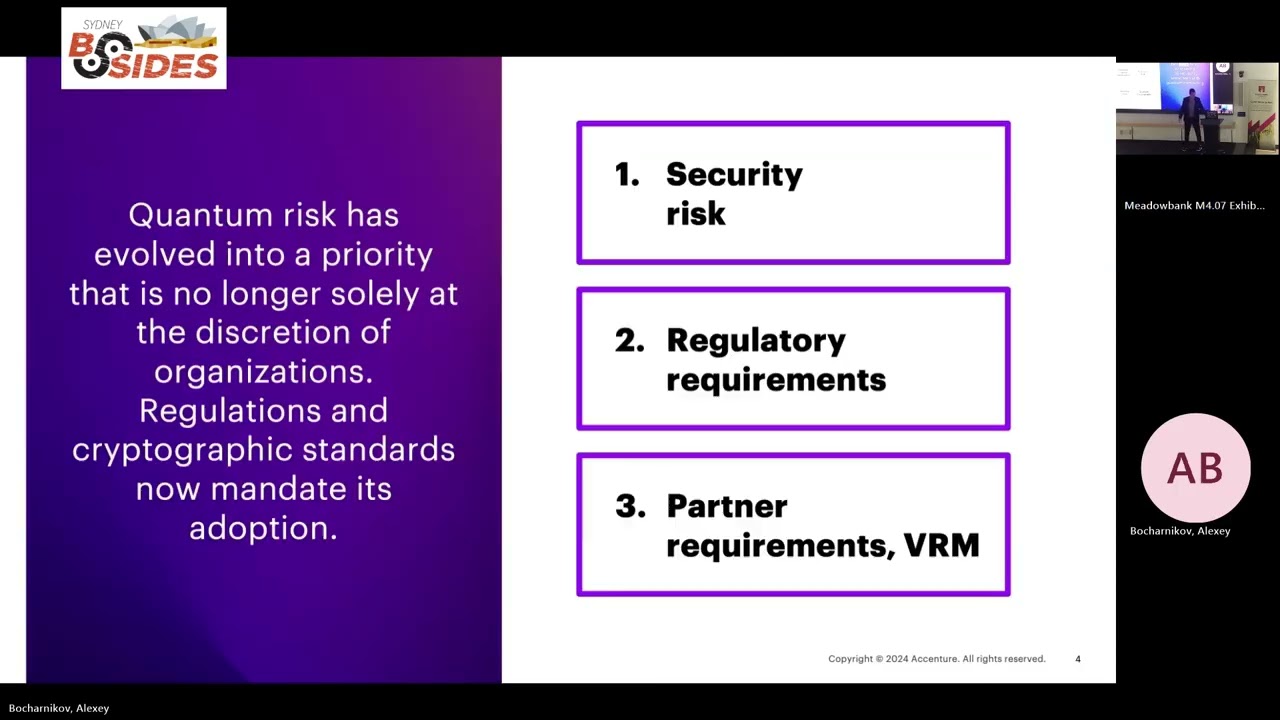
end no fine next one now we're going into Quantum risk and the rest of the presentation will be just about the quantum risk and I wanted to start by bringing to you the recent change like not that recent but on the scale of world like a recent change uh and that is about force that drives adoption of the solutions the remediation of the quantum risk so before that it was the security risk itself cryptography is vulnerable my data is not well protected does and need to go and fix it and whenever you go you need to speak with your executive with your CER with anyone and try to convince them this this is a real problem this is
the real threat I need to fix it that was hard like you needed people to believe you to understand technically what's going on and that didn't work very well so that was understood by many governments and what they came up with they came up with with some sort of help with the ultimate prioritization technique that they use which is regulations so today whenever you go and speak about Quantum risk you probably will use another approach which is there are regulations there like whether you like it or not whether you agree with my statement that Quantum risk is a real thing or not like doesn't matter there are standards and regulations and now you need to go and make things work now
also there's the third force that I think a lot of people underestimate but it's super powerful now whenever your organization works it has a lot of communication with counterparties across the globe from us whatever other parts of the globe now they have their own data security data privacy officers cyber security functions and whenever they adopt the tool set that makes in Quantum safe they will demand that from their partners because from that point they won't accept that their data that they consider something they need to protect is protected by means that they consider insecure so soon and it happens today but the more we go into the future the higher will be the force the stronger will be
the force Partners will demand from everyone that guys you to go and build things Quantum safe because that's we think what's the only way to make data secure I just want to spend one slide speaking about regulations uh I recently found an awesome resource it was just the day before yesterday which the link is at the bottom that outlines all the regulations that government has government across the world issued like there are so many lines so there are regulations and guidelines so there's only one country in the world that made regulations a mandatory thing that you must follow and that is us there is just two here but in fact they have many more and in us there is an obligation for
companies from different sectors to start doing some steps that make them Quantum safe like all other countries and then my example those are Australia South K Singapore and Europe in general those are just guidelines so they either in their strategy or in whatever other document that they make public someone who is a trusted party in that dialogue acknowledges that this is a risk must all think about it there are ways how you can remediate it but it's not yet a regulation now there is another site which is the right side where we have cryptography regulatory bodies you know there are bdes in the world that everyone tends to listen to and what they do the only thing not the only
thing like one of the most important things they do they Define what cryptography algorithms and with what configurations you're allowed to use and what is considered safe today so their job is to look after the different attacks after the growth of compute power development in the academics about ways how you can break cryptographic algorithms different crypto analytic methods absorb that and come up with a guideline that tells you like today that's the key length you want to use and that's the algorithm that you are allowed to use now this is the four most common one and recently uh in US n issued their guideline it probably was one month ago and in that guideline they
depreciated the usage of asmatic cryptography algorithms we'll speak a moment about them starting from 2030 and going forward they allowed to use only the postquantum cryptography algorithms now what it means practically it means that whenever you have next audit coming to you uh they'll come up and they'll take those guidelines not regulations they'll take those guidelines and assess you against those guidelines and if you're not compliant if you're using something outdated you'll have an audit Point whatever uh compliance requirement uh process you would need to follow in your environment to remediate it that's all about regulations all the rest is about the the risk itself like the security risk itself so I wanted to start from a
little bit distant and speak about what's the difference in how you protect data that's my interpretation it's not written in a book or I'm not aware about the statements in a book so you have matter like sometimes some things that you want to protect like physical elements like a gold or a paper or a letter and recently we added information to that like digital information like ultimately when you think about physical representation of an of of something the only way how you can protect it is by physically securing it you add guards you put it in a safe on theground and the way how it can break in is through physical penetration so if I have more power if I have like
stronger people I can eventually come up to you and get that data it may work with the information too right you can put it un encrypted on the server into the save and and you have the same but it wasn't the best thing you can do and thus we have this other points here another way how you can do things is you can do something with the information and do not disclose what you've done with that and hope that unless people found the way how you manipulate it with your information it remains secure so this level of security is based on the absess of knowledge how things work so you can can do it in a matter World in a
physical world but you can do it with an information and it's okay so a lot of people fail back to those mod where the top one doesn't work they assume that while I keep obscured like the processes I use to secure my information I'm safe so it is kind of a good to have thing but that's not the position where you want to be you want to be on the right hand side and that's where you use Mass like or other scientific tools to provide security there no matter how strong you are even more there's like a famous cryptography principles written by kov where he explicitly states that the internal mechanics of a cryptography algorithm must be known and security
must not rely on the knowledge about how cryptography algorithm works so you want to be there all the security levels all the standards every time you refer to cryptography that's this right hand side now what happens today with the quantum Computing Evolution and what I fortunately hear more and more is that people in their response in their initial intent and impulse to make things Quantum safe they're telling okay fine I won't be using algorithms that are considered secure but I have other things like no one can get to my environments because I have you know defense and depths in general like there are so many other things accounts are properly controlled like I have firewalls properly set up that's fine
like you're right it helps but you need to clearly keep in mind that you move from this right hand side to this kind of middle point where you imply and absence of knowledge to your environment next one I found it very fascinating uh so this is the the explanation why things are secure this is very interesting to understand it will make at least it made my life easier once you get it uh and that is computational hardness assumption so have you ever thought that the algorithms to use today do they provide like absolute security there is no way anyone can break them or do they provide reasonable security meaning sometime in the future maybe someone can break it so
there are these two big Realms in cryptography and one is called information secure or in my initial sentence it was absolute secure and this reasonably secure now you can build an algorithm that provides like this absolute security but that is so unpractical like they exist but they are so unpractical no one ever uses them so this information security it implies that no matter what resources do you use like this you have a computer size of a universe like no matter how big is it you have all the resources in the world you cannot break the message there's just no way you can do it and that exists but not practical all the algorithms we use today you pick any one
of them they are built on assumptions and the main of them is the computational hardness assumption what it effectively means is that when they were designed someone came up with an assumption like sort of a ceiling that defines how how much of computational resources an attacker a would be attacker could have when he attacks an algorithm so those are strong assumptions but don't take me WR those are great assumptions it worked with us how those algorithms that we've built 40 30 years ago they're still today they're still secure those were the right assumptions so unfortunately what when those SGS were developed what wasn't taken into account that at some point the new way of compute will appear in that case
today we know it's Quantum Computing that will break those assumptions and that's what happened today in essence you can say this assumption based flaw was baked into every algorithms when they were designed and it's still the case when we build postquantum secure algorithms we still build them on assumptions and there's no guarantee that someday in the future someone will come up with another computational Paradigm whatever it will be or with a novel crypto analytical methods with the noval algorithms how to break things and those assumptions won't hold if you're lucky enough to be on the first row and to observe what happens when assumption fails that didn't happen before uh in the past we had algorithms that were
depreciated but it never was at the scale that we see today where like the whole class of cryptography algorithms fails because underlying assumptions were essentially the same and they are no longer valid so keep in mind computational hardness assumption very fancy thing just tells you that ini assumed things will be secure given that amount of resources but those were just assumptions and they tend to fail now in cryptography there are so many different Primitives like a lot of them that's not a comprehensive that's just to give you an intuition what happens there are different ways you can do cryptography usually when you take any one system that you use in your production environment you never use any
one of them independently usually you combine them build them three four at least two of them to do anything useful so for example the most basic example whenever whenever you want to sense a data from point A to point B and you want to make it secure you want to do two things so first one you want to agree on a key you want to have a way how over the open Channel when you imply that anyone can listen to the channel you can exchange some information between two parties and at the end have two strings one on the site a another one on the side B and be sure that only those uh participants in the
communication know that secret this is a symetri primitive called public key cers so use it once at the beginning of the session you establish the key and then when you start encrypting when you start sending the messages you're not using that then you go into the symmetric key Primitives and you use one of those blog ciphers or stream ciphers and that's where you continuously apply that key and encrypt data so this key is used while the session is active and then you need to establish it again so you always have a combination of those things quantum computer didn't break all of them like there are so many and they're all secure what has happened is that
asymmetric Primitives which are here at the bottom they happen to be rely on mathematical problems ionic example is the factorization problem where you're easy to multiply hard to reverse factor and everyone believed that this factorization problem will stay hard for a much longer time but just happened that one of the first algorithm that was developed for quantum computers allowed to solve that problem and also what happens that you can can effectively bring other mathematical foundations that are used for other public key ciphers to the same problem and that's the whole class of asymmetric Primitives was relying on the same mathematical construct where Quantum confusion happened to be effective and thus it's no longer considered secure sometimes
you may hear that symmetric Primitives are are not secure anymore so this is the wrong assumption it's a little bit Shady but in general whenever you speak with cryptographers or with academics the T to say and all those cryptography agencies from the previous slide and there official Publications they never say that cryptography symmetric key Primitives are vulnerable the reason being is that in general symmetric Primitives are not built on mathematical problems you do not multiply things there you do not do any complex M the only thing you do there you just substitute and Shuffle things and you substitute and shuffle them in such a complicated way that you assume that if someone intercepts that and they don't
know how to reverse that they will never figure out how to do it and thus the message is secure there the problem the assumption is that this substitution permutation method is secure on its own now Quantum Computing that's another famous algorithm which is a Quantum search by grer it from the first glance may seem like gives you advance advantage in conducting attacks through unstructured search meaning just you can Brute Force things and and use quantum computer it allows you to find symmetric key faster and thus it is vulnerable but that's not the case because the consensus is that once you build that search algorithm the complexity of that algorithm becomes so big so it's exponentially complex in fact and that
it outweighs the advantage it gives so the end you have zero Advantage so symmetric key Primitives are okay as algorithm iconic example is fine we still use it asymmetric Primitives all of them are done so they need to be replaced and there are a lot of other things that we use and they are still secure now I want to stop for a moment and speak like why is it a problem why can't I just go and replace I have this old algorithms and now I have this new algorithms that need standardized that are called post Quantum cryptography algorithms they built on assumptions that include quantum computer that means that the problems they have chosen are complex even for quantum computers
and we believe they're secure like what's the problem what's the issue the issue is in one sentence is that they're not compatible with what you use today so this table represents digital signatures uh not the algorithms that we used to establish key remember there were two blocks here one was digital signature another one was key agreement protocols so this is just digital signatures and why I want to speak about digital signatures because because it happens they have more problems than another block and the primary reason for that is as you see there are two kind columns one relates to size another one shows relative time none of the finalists that become now standards have even close numbers to what we have today
so if you take slh DSA the kind of third row in the second part its public key size is 17 kilobytes this is insane because for RSA is just 256 bytes so it's 50 times more like none of the systems that we use today and think about it devices where have a lot of restrictions on computational resources and in general like network devices none of them was developed to handle that a big key then you can say okay I'll trace the length of the key and we'll kind of use more power to do computations there's some thread off possible that's like the second line you see there you used the key to 7 kilobytes but now your
relative time in signing is just 3,000 times more than it was before that's again insane that's so complicated and this is the primary reason why we speak so much now about Quantum risk is because those algorithms that were introduced is post Quantum safe they are just not compatible with technology hardware and software that we use today and will cause so many issues taking past experience it took forever to remediate algorithms like the the the basic example from my experience is that one day we wanted to change hhen for passwords that we used in a database and we wanted to use another hash function that was better like more secure and the problem the obvious problem we faced is
that you cannot do it on your own you need a user to log in and then you tell him like please change and then he changes so for three years you have the old old old password using old hash because users are just not coming to you every day they're not changing that so with that in mind migration to new cryptography algorithms will be painful now on this slide I wanted to bring like one data point there are many data points you can find I want to bring why one data point that defines the timeline whenever you go and speak internally you eventually will come up to a discussion about how much time do I
have and the iconic question is when someone will break cryptography like no one can say no one has a crystal ball but what what you can do you can bring different facts that allow you to kind of Judge make a better decision about where things are going to happen now people when they discuss that tend to focus on the right side so here is just number of cubits and quantum computers of different modalities throw on one graph so that's not the right way to compare quantum computers with each other they're built using different principles they very different there's in the industry no one metric that you can use to equally compare them but for the sake of this slide just the number
of cubits is okay you see their capacity is growing they're becoming bigger and bigger and bigger and that's usually when the discussion ends but there's a second part which is the left side that's the algorithms that exist to actually break cryptography sure developed his initial idea what 25 years ago now if not more and then there were so many improvements to that like 2009 there was an algorithm that required 1 billion physical cubits to execute an attack and the note again measuring algorithm requirements just in cubits is wrong there are so many other things you need to keep in mind but for the sake of explanation to show the trends we're using just number of cubits there was
one billion cubits to actually execute an attack that was a lot we had one cubit and there was one billion cubits like I have a lot of time to wait now 2019 there was another elation that require now 20 million cubits to execute an attack this is two orders of magnitude drop that's still a lot I have two 20 million cubits and at the time I have whatever 10 20 Cubit device still Gap is huge now 2022 from the top of my head there's another class of algorithms appear that are called that are called herotic those are the previous algorithms for proven algorithms which means they will work every time you launch them heuristic on
the opposite they work sometimes like usually it means that in Practical situations when I do root optimization when I use Google Maps there's no graph that complex that will break my algorithm and it just works but I can construct a situation when this algorithm fails that what her istic means so the C zapa came with an idea where they converted the problem of breaking a cryptographic algorithm into optimization problem and thus it became herois and in their approach they required just 6,000 cubits then 2023 January Chinese scientists come up with an algorithm that require 400 cubits Which is less than we had at that point in time it didn't scale it didn't work they applied the same idea
of translating the problem into optimization problem they just used another technique it just didn't work didn't scale now one month ago there were two other papers from Chinese scientists and you know just outlining them in a few sentences they did the same they found another way how to rub problem and translate it into optimization problem and again they claim they can do it with less than with the capacity that we have today with Quantum compus that we can use right now but it didn't work again once you apply it and try to uh use them on algorithms with the sizes of a keys that we use in production it just didn't work so the bottom line here is the development in
the algorithms area is an active space of research it's not that we have Shore that was 25 years ago and it's it no there are so many progress made in that space and it's much closer than it may think from the distance to the capacity of quantum computers that we have today now uh if you ever read or heard about Quantum risk probably heard about this equation that's a MOS equation I can skip it but I'll be very quick the idea is that that's the second Factor we can use like how to understand where do I need to start should it be quick for ml8 the idea is that you compare your best estimate of when a quantum computer
will be able to break a cryptography algorithm with two other factors which is how long do I need to protect my data and how long it takes to change my environment how long it takes to R your environment so when once you do that when you have the gap which is small not necessarily negative or positive but small that means that your estimates are they obviously estimates they're close to each other and that's where you need to worry obviously if you have a huge negative Gap then that's a huge problem if you have huge positive Gap then you have some time to actually think about it and work on that so that requires some estimates uh and I found that a lot
of companies are moving in the direction that they want to have a position so whenever board comes or a regulator comes in the future and asks like they were news you heard about it why didn't you do anything companies tend to make a safe move to protect them and come up with some statements saying guys in 20124 in November we did our homework we understood there is an emerging risk or current risk and based on our estimates we consulted with abnc and came up that we're fine or we're in a risk Zone and thus we started the remediation program now of course everyone heard about haris now decrypt later attack and at some point I realized that uh I
assumed that this is a known fact what it is but there were people in the audience that didn't know and from that moment I decided to add one quick slide to explain what happens so data keeps value over time whenever you created a data probably it will be valuable to you for more than a year but sometimes it SPS to like decades think about your medical data or some other data about HR records that needs to be kept for years not decades now it may mean nothing but an attacker attackers found a way how to use it against you and that's not a noble thing it's not connected to quantum computers that was with us for ages and the idea
is that you intercept data you sit on it you don't do anything you intercept it in encrypted form then you wait for something to happen like maybe maybe someone will come up with a much bigger super computer maybe someone will find a flow in the implementation of the algorithm maybe someone will find a way how to break like the foundational Concepts that form security of the algorithm you just sit and wait and that was 30 years ago that is now the only thing that you remember this computational hardness assumption this baked in flaw was always in all the algorithms now what changed with the development of botum computers is that the tool that will allow you to break
messages encrypted today just became known and now any government like anyone tells you that and even associate this attack with quantum computers because they know I can intercept it and there's a good chance before data loses value before time lapses someone will come up with an algorithm and a quantum computer big enough that they can use so I decrypted I think it's important to outline that there are two interesting assumptions that people make when they think about threats and they always map them to this Harvest now replate their attack but they don't hold so first assumption is that whenever attack happens whenever someone attacks your environment you live under impression that you can do something like I can
hire a company I can shut off the server I can do something to stop it no that doesn't work with this Harvest a cry lator thing if someone intercepted your data today you've lost control today you cannot reencrypt it you can do anything if you are unlucky and in the future someone decrypts your data and starts whatever trading it on the black market to do something against your will you can do anything you just sit in the front row and observe and the second one is usually people build complicate complicated uh detection capabilities they try to get sign signs of things happening in their environment and from that understand is there any attack happening like what's going on so this
type of attack is a passive sniffing attack like it's the hardest one to detect you will never know it happened especially if it happened somewhere where you don't have control over the environment okay now we're coming almost to the end of the uh slides that I wanted to speak with you about so here I wanted to try and outline like a canvas for you what does it mean to become Quantum safe I'm not aiming to explain in all the details all the bullet points but what I wanted to do with you is to show you how big is it there are so many things to care about so you start from Quantum safe components we discussed
post Quantum cryptography algorithms now there is another one Quantum key distribution that I didn't speak about so this is the technique where you take like a huge box a hardware piece you put it inside a you put it in inside B and then you connect them using the fiber optics they most likely will be using the existing one and the only thing those devices do in this point-to-point communication they establish a key and a string of bits that is known only to these devices and then you can consume those keys to actually encrypt data between those sites so never ever Quantum key distribution is number one solution to your Quantum safe problems like never ever there are special use
cases for this technology it has other flaws other problems that you need to carefully wait before you go into the implementation of quantum key distribution setup so I just wanted to warn and that's such a misconception and probably again because Quantum the word itself is used in the name of this technology you have Quantum risk you have Quantum key distribution one much another and I solve the problem no you are not that's a niche technology with very specific applications and also there are Economy based methods so there are other things you can do remember on that one of the slides with two lines you can drop from the point where you want to be to have this cryptography
based security to one point below where it's built on the methods that you know someone don't know or Economy based methods the iconic example here would be if you think about a database and you apply a key to encrypt a database if someone steals your database it will just need to find one key to get access to all the records there to one million records in my example but if you C every row with a separate key you effectively increase the cost of attack and it may be just economically unviable to make this attack you can come up with other ideas how to economically protect your data make it less interesting for an attacker to go after your after your
environment now once you have that if you have it on your table it's like nothing it doesn't make things Quantum safe just the fact of existence of a qqd device doesn't make things Quantum safe you need to actually put it in action you need to incorporate it into your environment and there are many things where it should happen I tend to ask the audience one question and I've never heard anyone answer like can anyone name anyone tool or service or middleware or anything that is modern not 20 years old that is modern where you don't use cryptography so there is none you pick anything and inside you'll have cryptography used for at least something usually you start whenever you
think about your environment from cryptography Services which are internal pki and HSM systems this is the tools that deliver cryptography services to other internal consumers and that's like the most critical asset you want to remediate them first those are obviously non- compliant today with the implementation of new pqc with the announce ment of new pqc algorithms and with a huge question mark will your existing tools support that migration then you go to network like you pick any network protocol on the OC layer just anyone there will be cryptography there most likely here you'll be waiting for vendors to come for standardization agencies to make changes to how Network protocols communicate there's nothing you can do but you can use some wrappers
like tools that allow you to wrap your traffic into the pqc traffic and let make it safe this a mix of work with the vendors and decisions for most critical use cases whether they want to use third party Solutions then you go to this is like the most general term you can think of it environment elements like everything you have there should be a way how you prioritize things because cryptography is omnipresent you cannot go and remediate everything you start one by one and come up with some metrics how you can do that usually here we come to the discussion of the discovery process I want to know what cryptography they use where what data is protected with
what cryptography algorithms and having that said I will make informed decisions about what they want to remediate and then it may be surprising but Cyber Solutions require work too so take identity management like this whole thing identity management it's just cryptography wrapped with a workflow nothing more nothing less you have crypto craphy sitting there to authenticate users to prove their identity like for every step there's a cryptography your identity systems would need to become pqc compliant which require a lot of efforts and then now you see that's a huge huge undertaking you come to a here it's called strategy plane governance plane like how do I do it and that's one of the most complicated one from my experience you
need to convince people around you various stakeholders people looking after your infrastructure CA product owners like eventually coo to invest into the remediation that's a costly Endeavor recently I heard a very interesting kind of comparison how people describe how long it takes and I'll share it with you it takes three sizes or two cosos to actually solve this problem it it spans through so many years that average term of an executive person is less than the time this problem takes to solve so this is a four size of Problem whatever your actual you know average time or to see your problem okay now because of the time it is 45 minutes now I have other things to speak
about but do you want to have questions now we can stop and I'll take any questions from the audience and then if we have whatever any more time I can speak about other topics





