Milenko Starcik - Cybersecurity for Space Systems (BSidesFrankfurt 2024)
Show transcript [en]
Guys, our next talk. Yeah. Our next talk is about cyber security for space station with Mileno Star. He works for vision space system in Dharmmstat from threat modeling to pentesting and R&D stuff. Take it away. Thank you for the introduction. [Applause] Thank you. So I think the bar has been set pretty high with the first two talks saying it's not rocket science. So I guess now I have to deliver. Um but my my the the point of this talk is to show you that it's it's not rocket science even if it's rocket science. So cyber security across all domains is is pretty similar and we see the same problems as in every other industry especially when
it goes into the OT direction. We we have pretty much the same the same problems. Um one of the factors um is that space systems are pretty expensive by nature. So they are pretty extensive in the development. Takes a long time to build a spacecraft to launch it. It's very expensive. And then operation requires like trained personnel. The software is specialized. Um but at the same time the impact of a failure of one of these systems for example uh weather data. Even though yesterday someone said like yeah the weather is anyway wrong the prediction for tomorrow. Um but for like uh air traffic management it's very important to have accurate weather weather data for like maritime
transportation. Uh the weather data actually matters. It's uh it's not just about your daily use to know if it's will be tomorrow sunny or not. Um and also in a in a military context, it's very very important for your uh country to know how the weather will be um in a certain location. Next is imaging capabilities. Um of course it's nice to have a Google Maps view of uh the venue here like you can see where the building is. Um but at the same time like high frequency updates of images are actively used in in military context as well. Um so this is very valuable information. Uh for example like planet labs um does this. Um then we have of course
telecommunications. Uh you have of course like your more traditional services. Um but then there is now also for example for the new iPhone you can send emergency messages with your iPhone. So what happens if you want to send an emergency message and it's not going through? Uh that's that's a pretty high risk. Now with every new new new new new new telephone out there um there's the new 5G NTN standards coming out so non-aterrestrial networks for 5G. So you will see in the very near future more and more providers like Doa Telecom, Starink providing you with mobile phone access over satellite. Um and then we have position navigation and timing services. So GNSS, GPS very well known again used by by
almost everyone but again very critical if it fails. A lot of systems fail that are based on it. Often you don't know that these systems are actually using for example GPS to to synchronize the timing. So they use GPS for retrieving timing information from the signal as an external source because maybe you don't have an atomic clock in your infrastructure. But if the GPS fails, you you're in in real trouble. Um because systems cannot sync anymore. Um so this is like a high level overview of of how space systems usually work. So you have a ground segment which is by nature on the ground. It includes the the control center. So this is where you operate your s satellite. Also
operate your payload which is usually separated. So you do the operation of the satellite and you do the operation um of the payload or payloads for larger satellites often separately often even done by other companies. Um you have of course launch facilities so like rockets. Um then comes the more obvious part. You have spacecrafts. Um so one or multiple now with like most people know about like SpaceX for example deploying like thousands of new satellites. So this can go like from one very specialized system for like scientific missions like the James Webb Space Telescope to very large constellations of of of satellites. And then you have the user segment. Um you don't always have a user segment but if
you have it it could be for example your smartphone using a GPS uh service or sending a emergency message uh with with your iPhone. So one of the big challenges in satellite systems is that they are usually distributed globally. Um so you don't have just one antenna talking to your spacecraft because uh that would cause many problems. So this is an example from the Galileo system. Um so the European GPS so to say. Um so you have around I think currently 29 30 satellites in orbit. You have ground stations spread across the globe. You have different types of ground stations actually. You have for mission data for normal data. All of these are running globally distributed usually over like
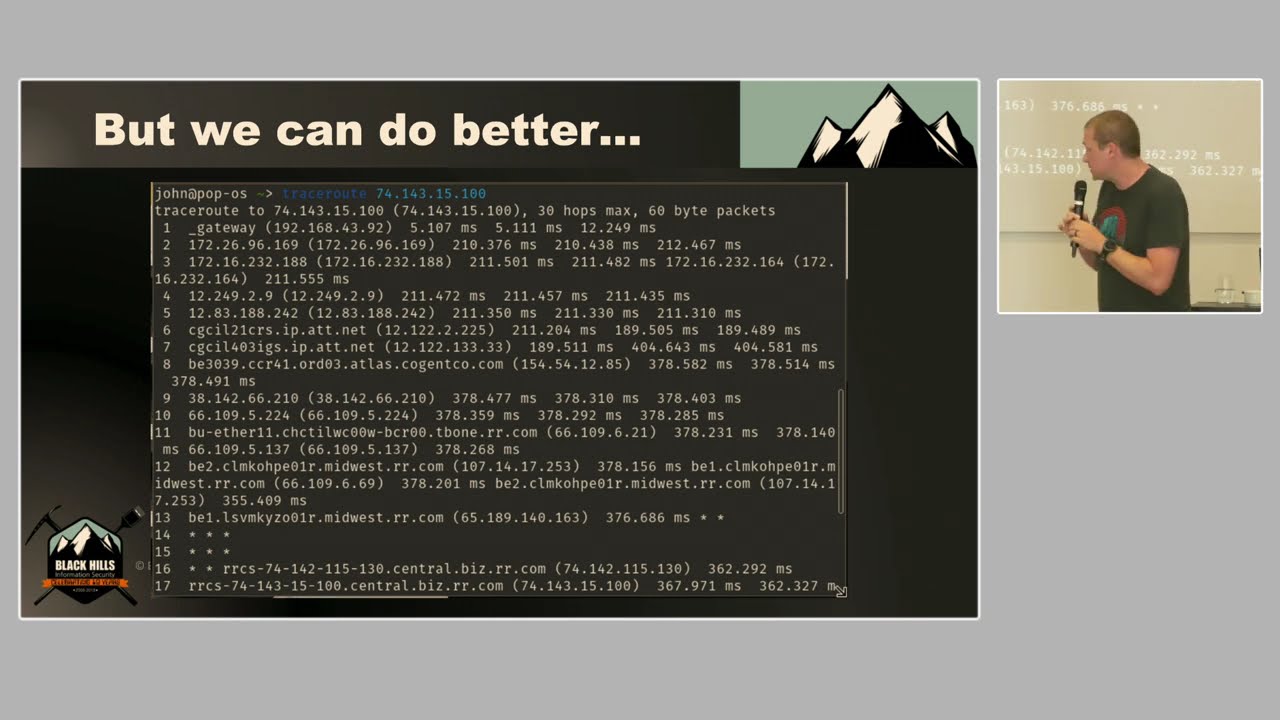
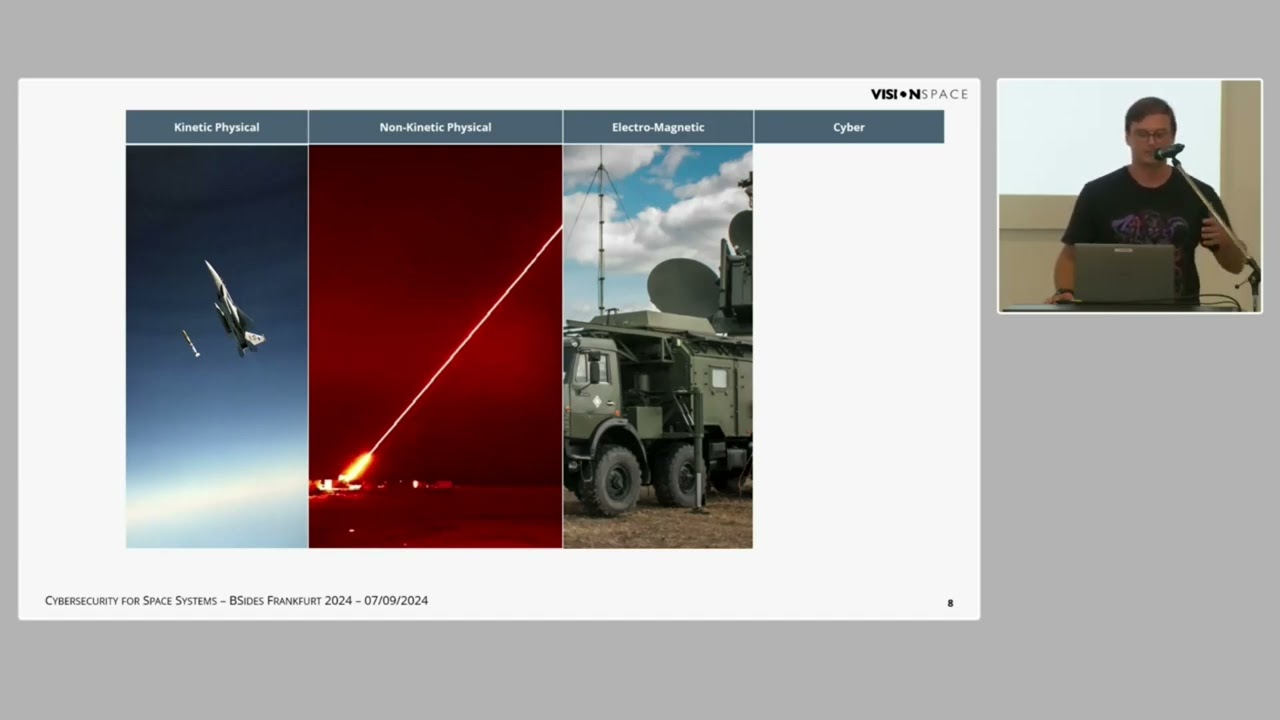
lease lines or something. So there is usually a high quality. Um and then you have a lot of facilities supporting this like science centers, operation centers and so on. Um, when it comes to modeling threats to satellite systems, there's like some very traditional threats. So, this has been already demonstrated by uh a couple of nations like the US and China and so on that you can actually shoot down a satellite. That's definitely something that you can do. Um, you can also point a laser at a satellite and it will have a very bad bad impact. So, this is the more flashy threat. Um you have of course electromagnetic so classic GPS spoofing, GPS jamming. You
can also attack the spacecraft's communication links. So the um housekeeping, so if you want to control a spacecraft over RF. Um and then you have cyber. Um so the next couple of slides I want to introduce you a bit to why cyber is a very interesting topic in space system security. um because it has its unique uh properties. So for for the different attacks we have different like subtypes of attacks. This is not a complete list. This is just some of them. Um so for the kinetic physical attacks you can you can destroy a ground station. Totally that's possible. Um but you can also launch a rocket at a satellite and yeah this will also definitely destroy the satellite.
Um but what you can also do was recently demonstrated by China. You can dock to another satellite and drag it. So you can move it somewhere else. So how how do you counter that? Um then come non-kinetic and electromagnetic threats. So you have what I told you about. So you can do like laser attacks. For example, if you have an optical sensor and you use an high power laser, you can permanently damage or at least blind it temporarily and cause a denial of service. So, if it flies over you, you can point your laser at it and it will very likely do something. Um, the same you can do with RF, especially interesting for synthetic
aperture radar. So, you can do like radar imaging of the Earth's surface with satellite. This is currently done. Um, but you can also jam that. We we'll show an example how this looks later on. Um and then of course in cyber you have all the typical cyber security attacks that you can imagine. Um what is now interesting is that attacks on these systems are typically not done by individuals. So this is not your uh lonely hacker attacking you. This is usually a nation state actor trying to do something. Of course, you can have a ransomware attack from a ransomware group that suddenly gets your IP address and I don't know finds a vulnerability in your
system. You can totally also have that in space systems. But the the most worrying things are the more sophisticated attacks by by nation states and also the things that recently show up more and more. And for that what is important to understand is that if you have like a kinetic attack it's very clear who did it. Like it's very hard to hide anything you do in space. You cannot shoot up a rocket and think no one notices. Everyone knows. Um everyone knows where it was launched. Everyone knows what was hit and what was the result. So you probably don't want to do that if you are not like in a in an open conflict. Um, then come the non-kinetic physical
threats. So, uh, a bit like pointing lasers at spacecraft. Still fairly easy to find out because there's like a physical limitation to how you can point a laser. [Music] Um, and also the the risk of causing permanent damage to the asset is pretty high. So, in cyber systems often the the damage is not physical. And with that somehow policy makers decided this is not as bad. So if you have physical damage it's bad and this can cause some escalation. If if it's not permanent yeah maybe you can give it a try. We see now with for example in in Estonia and and the Baltic there's a lot of GPS spoofing GPS jamming very actively um
also some some other regions um where where they're trying to to find out how far they can go. Um and then come of course the the cyber attacks where you have very limited attribution. You can try to find out some technique patterns. You can of course try to work with some IP addresses, but that's like they will have an infrastructure that you cannot attribute to them or that will look like someone else. This is like specifically built for that. They will have preparations for that. Um, and for an operator of a spacecraft, it's very difficult to detect it immediately and to to do counter measures. The good thing is it will likely not permanently damage your
spacecraft. it will just cause a denial of service of maybe some user equipment. Maybe the software will be wiped or something like that. Um but it will likely not cause any physical um damage. But for the attacker, it has a lot of benefits because it they can deny it. Um and they also have a near realtime like damage assessment. They they know what they did like an attacker is really blind in when they're performing a cyber attack. Uh just to briefly touch on the electromagnetic threats, very nice website by the way is gpsjam.org where you can see a current uh GPS jamming worldwide where there is ADSB data available. Um but this also has an impact on uh
ships. AIS systems are impacted as well. It's just visualized with the ADSB uh data. So this is over Estonia. And then we see um German also using against these sutic aperture radar satellites. So these are they can create topographic maps and very precisely so you can track down to a vehicle basically in a three-dimensional point grid. Um and we see that there is also jamming done. So this is like open source data. You can access the Sentinel hub if you're interested in getting some relatively fresh images from space and they have different channels and also the Sentinel one SARS satellites for example and here you can see over Sebastto on Crimea uh some some active
jamming going on on on these uh systems. Um there has been some accidents also for a satellite internet but also satellite TV jamming and spoofing. So satellite TV is something relatively dump. So it's usually it's called a bent pipe. So you send up a signal and this is distributed down. So if you send up another signal, it will be distributed down. Especially in older uh satellites like from from Astra the Astra satellites for example the older ones are just working with that principle. You just need to know the frequency how it's modulated. You send it up and it will be distributed. And there have been active attacks where I think it was in in the Netherlands where
they they overrode some some child TV with some propaganda channels was was pretty wild.
Um so um what what what I want to to come to is that um all of these things are very nice but our what what we see is that the cyber threats are the ones that are dominating uh all of this um because there's not just increasing capability there's also missing awareness of capabilities of from APS I think many people underestimate estimate how much you can do if you have time and resources. This seems to be like a general misunderstanding in the from at least my perspective in the space industry is that many people don't understand what a proficient attacker can do like just in the previous talk they will read all your documentation and for
space systems we have quite a lot of documentation which tells you how to operate a spacecraft. So they could, for example, use their own ground station and try to command the spacecraft. Um, in addition to that, especially in commercial systems, there's often a shared payload and ground systems operations. So you'll have multiple companies connecting into your infrastructure, managing part of it. Um, the the lines will not be very clear and definitely not zero trust. Um, the next point is satellite systems are super expensive. um it it comes cheaper and cheaper, but still uh they're insanely expensive. And once you launch a satellite, you want to keep it alive as long as possible, and you will
do whatever it takes because this is your number one cost is the satellite. And operating it is expensive, but uh as long as it's operational, it it prints money. Um this will cause a lot of systems that should not be active to be still active because the infrastructure is built 20 years ago and they are not upgrading it because it's operational and of course the the COVID 19 pandemic adds to this. So um suddenly you have a VPN access to this legacy OT environment for your satellite operator to operate the spacecraft from home without any multiffactor authentification or something. Um and this causes problem and this caused problems. Um yeah in addition we have a lot of
like inse insecurity by design. So um satellite systems are pretty difficult to reach. So once you have launched a satellite, it's very difficult to go there and fix something. So you'll often have like some back doors, some high priority commands, you can send some something something to do in case something goes wrong. Even if there is like a even if the communication is encrypted, there will likely be a way to turn off the encryption just because otherwise you cannot control the spacecraft. It costed you two billion. So what what do you want to do? Um so these are like hard trade-offs but often in my opinion the the wrong decision is taken. Um then you have a huge threat
from insider threats. Um because the space industry is very contracted out. So you have a very small core stuff in like all the space agencies and operators, but you will have a huge workforce out of that because for example in Europe it's how it's organized with with the European Space Agency and and others. There's a lot companies like ours who are contracted in and there's just so many contractors. It's it's impossible to to see how the information flows. Um it's impossible to track. Then we have of course supply chain attacks. Um not just on on hardware also on on software. Um and my last point is what I will uh elaborate a bit more is missing security culture. So
there is a huge like I would say hacking culture in terms of keeping things operational. So if something fails, if there's on spacecrafts you often have things failing you didn't expect to fail. and they're kind of built to handle these kind of things and the operators will find a way around to still keep the thing going. Um but unfortunately this does not translate to security. So this translate to safety of the thing but not to the security of the thing. Um just an example for to to to show a bit like because it was a pretty public case. Um so in 2014 there was a a blackhead talk from from Ioactive on uh visat terminals. So these are end user
terminals that are deployed everywhere around the world like you can get one in your backyard or you can install one on your warship and you have internet access. Um, and they they just got access to a lot of these terminals and tried to find some some vulnerabilities and there was everything like uh weak passwords, hard-coded credentials, insecure protocols undocumented protocols, you name it. Um, so yeah, the hope was that something would change. Uh unfortunately four years later they did another talk uh going into the technical details of the weaknesses in the protocols because previously they just said okay weak protocol and then people said like yeah we we we cannot really do something about it. Um so they followed up. Uh
next report came out where they showed that they can actually geollocate some of the devices which are deployed in a military context. Um which is pretty bad. Um so fast forward another four years uh some of set terminals were installed on on German wind turbines and suddenly uh the the energy provider Anagon faced an outage of like 4 and a half thousand of their wind turbines. Um this was the evening before Russia invaded Ukraine. So um the Russians deployed an attack against the the bioset satellite infrastructure and compromised um the the firmware of roughly 45,000 of these end user terminals uh deployed in Ukraine but also in the region. Germany is obviously part of that region.
Um and so suddenly one year later we see the the vice president and CISO of Viaet on stage at Blackhat uh with a lady from the NSA giving a nice talk about how they did incident response and um yeah was was quite funny to watch especially if you track down basically this and you see that actually the things affected by this were known. This was no secret. Um, and this is again what I would like to show. This is like an underestimation of effort someone wants to take if they really want to damage something. Um, in this case it was the Russians. They did an analysis on that. Um, and they basically got into the VPN,
jumped through a couple of networks, did a custom DOS attack on an internal protocol, and also deployed this custom malware to the to the modems via an overtheair update functionality over the satellites. Yeah. So, [Music] um, so this is not a singular case. Um so what I now have are some examples that we produced as as part of our research. Um so to give a bit of an introduction so the SLE protocol it's called space link extension is a protocol that a satellite operator uses to connect their control system for the satellite with a uh ground station and this uses TCP and it has an authentication mechanism and um what we do is we have
on the top we did a simple man-in-the-middle attack uh we have on the lower left we have the uh server side application. The lower right we have the the client side um application and we wanted to demonstrate that this is inherently insecure. So um just because it's like a it has an authentication mechanism but it has a certain lifetime. So if you can steal again it's like a bit like a cookie. If you can steal the the authentication uh you can do whatever you want. You can change the data. You can connect your own mission control system to it. Uh you can change data that is returned from the spacecraft to indicate like a state
whatever you want. Um yeah so all of this is known. This is actually written in the standard. There is a section like one paragraph which says okay confidentiality. Yeah we don't have security. Yeah not not really. Um it's up to the user to implement this. this is written like this in the standard. So we reached out to the standardization organization and we're like ah maybe maybe you could update the standard to make it like maybe use TLS, I don't know. And they were like nah. Okay. Um, so sorry, video is always a bit tricky. So, um, yeah, we we went to hunt. So we we started our journey with with some reviewing protocols but we we
found there's a lot of open-source software actually out there which we could test because we don't had any contracts with the companies or organizations operating them or maintaining them. Um so there is an open buck bounty program for NASA websites but there is none for the GitHub repositories just uh so no one looks into that. Um so all of these CVs we we claimed actually. Um so we found everything you will find in a regular JavaScript application. TypeScript you will find prototype pollution. You will find XSS CSRF you name it. It's just a JavaScript application but it controls a spacecraft. [Music] Um so yeah our latest publication was how to crash a spacecraft. So uh one of
the libraries they they shared luckily publicly is called crypto. So you can end to end encrypt the communication between your ground station and your satellite. Um unfortunately there's an outofbounds vulnerability in the header of that thing because you have two it's called security associations in that context and yeah you can just go over the boundary and yeah so the next example I have is from the mission control system. So these are actually is an exploit we wrote chaining three of the vulnerabilities. So we have a stored XSS, we have um session cookies which are uh not properly handled and we have an backend API function which we can call based on that which allows us
to exfiltrate any data on the file system because there's a path traversal or we can also delete any file any file on the system. Um, we we usually try to implement some exploits that chain things or that show the impact because from our experience, if you just report an XSS, people are are pretty bored and like, yeah, okay, I'll fix that. But, um, showing what the impact can be is is usually what what catches the attention. Um, so yeah, we'll uh generate our custom uh XSS code. Um so this one in involves a user interaction. So actually a user has to to load the JavaScript but you will see that they will not see it. Um so we're listening
back for the excfiltrated data with an HTTP server and then we launch the the mission control system. Uh we we load our new uh payload file.
And then we have the the funny thing about this. So there is like a script viewer. You can actually execute custom scripts written in JavaScript, but it doesn't show the JavaScript if you hide it. Um so our our payload is now actually already executed and yeah, we we got the passwords file. Um just just an example. So
um yeah so the the previous mentioned example is is here. So we have software running on a spacecraft and inside a ground station and actually both ends are affected by this vulnerability. So if we either using the previously mentioned protocol vulnerability change the data in the header that is sent to the spacecraft to like a value that is out of the norm or if we send with our own ground station an unauthenticated data package to this spacecraft the software will crash. So we have on the right is our ground as our radio simulator. Um on the upper left we have the onboard software running and on the uh lower left we have the ground station uh
running. Okay. So now we check we change to the encrypted channel on the uh ground software and now we'll send a uh command
So you can see that we got in the onboard software we got a segmentation fault and it will now uh restart. Unfortunately on the ground system it's not handled that gracefully um which we'll see in a second.
So yeah, we we sended our malicious payload uh packet to the ground station which could be done for example with a software defined radio and it will crash the the decryption functionality of that piece of software.
Um yeah, we we we do all of this to to raise a bit awareness also in the space industry because there's not a huge like security culture as we just tried to I just tried to explain. Um but there are some good things. There are things moving um often introduced by by policy makers or by uh customers like the military um using these systems. Um so there's first aspect is resilience. So um the trend goes to to like having multiple orbits, multiple frequency bands and not just buying from one vendor. So uh you will buy your user and devices from not just v one vendor. you will not just one use one satellite network to get your your
internet connection. You'll have multiple and the the receivers will very likely in the future support um multiple so with standardization like 5G antn for example. Uh for the user second we have OSNMA which is now becoming operational. So this will be an authentication service for GNSS signals. So basically they send you on a separate channel a a fingerprint for GNSS signals so you cannot be spoofed um or you can at least detect when someone tries to spoof you because it's it's not matching the fingerprint. And for the space segment like I said earlier so you can of course someone trying to to shoot a rocket at you or try to grab your satellite. So there are adding more maneuverability to
the systems. Um, same goes for electronic warfare. So they they try to be more resilient to to jamming attacks also using like laser communications which is a lot more directed and a lot more difficult to intercept or to attack and active sensor protection systems. Um what what we see is an increased you like use of cloud services also like the big providers like uh Microsoft and also um Amazon they have their own ground station network which you can access actually as like an AWS ground station service. So they have like sites around the world where you can subscribe to um this is like this ground station as a service concept. There's a couple of players out there. Um but this comes of
course always with a risk. So if you are relying on one of them, yeah, you better make sure that you do it properly. Um, another thing which was previously burned into the spacecraft is the software. Um, now with more powerful onboard computers, it actually becomes more configurable and now often actually users can run sandboxed applications on spacecrafts directly. So this is used for example for edge processing. So if you take an image of the surface of earth and you have cloud coverage above 80% um you might want to discard it. So there is like image processing going on on board and all these custom applications um which again introduces some risk because now you have suddenly
software from something someone else running on a spacecraft. Um yeah and then we have the the the quantum and crypto things uh which are slowly coming. So especially for the governmental side of things they are very interested in postquantum quantum cryptography crypto agility. So so the buzzwords but this is far from reality. So this is in the in the very early stages. Yeah. So that's it [Applause] basically. Any any questions? Yeah. No. Uh we we didn't test Starink. I know there's some stuff done on on hardware hacking and so on in Starink but we don't have any relationship to to SpaceX or Starink. So I have a question about uh vision space. So do you do consulting for the
European Space Agencies or like companies surrounding that and could you tell a little bit more about that? Yeah. So project so yeah we do consulting services for the European Space Agency for Humezad which is also located in uh Dharmmstad which is the organization for metrological satellites. So they're operating all the uh weather spacecraft for Europe which is then processed here in Offenbach. Um we we do European projects so like commission projects we do work with most of the large players in the space industry in Europe uh around that so there's like a like a handful of larger uh companies doing that and yeah we work with most of them
Yeah. So, uh since this is like public knowledge, we we are in a contract for example for building a sock for the European Space Agency currently together with Leonardo and Rhea.
Okay. Um question here. Yeah, one question. Um I think the upcoming NIS2 regulation also includes space um craft stuff and I I've learned that I mean spacecrafts are super expensive. They have to run for 30 40 years and they are very hard to replace. Um do you think there is a huge non-compliance risk in the space industry or are they kind of prepared to upgrade those satellites and ground stations and everything because that really sounds like the ultimate legacy systems. Yeah, I mean for example in Germany with the the BSI Grunch also for comfort system there are some new standards being ruled out rolled out. Um the thing is with the space industry they're very good at at meeting
requirements. So like requirements engineering is half of the business. So there will usually be compliant in a way. Um but it usually doesn't mean that they're safe.
I think the gentleman at the Yeah.
I mean uh of of course of like you will you will uh if you like do RF if you mean like RF hacking then you will uh face your your local entities because the ITU delegates that down to the the nations. So in Germany this will be the uh what they called uh uh so you will do like an unauthorized transmission in the frequency band that you're not allowed to use and then the satellite provider will file a complaint against your national authority and they will start an investigation and yeah and then things will slowly go. Um thanks for the talk. There's a lot of uh attacks going on in the internet as we know it. There's a lot of pew pew
maps as you know. Are there maps like for attacks into space systems? Uh how much is going on there? What's your estimation? Is this uh so the the attacks against space systems? So previously these systems were very isolated and because of that they were also kind of secure but it was often like counting on the parameter. So it was a lot parameter security. So you just had like a separate physical network rolled out like lease lines across the globe like huge costs but um it was kind of secure. Now this is changing to more cloud providers. You you are integrating some AI things here and there and it becomes fuzzy. Um there is very little known publicly about most
attacks I would say like only very few things make it to the news like if like a stock traded company is affected then they will have to disclose it or also if like local legislation requires them to report it but also to disclose it which is rare. Um, so it's it's a very gray field like it's it's very difficult to see because there is not much made public because it will impact like your integrity. So people will not talk about it. No, no one would say anything about it if if if any how possible. Um, for example, with the European Space Agency, they are in a special position. They're not governed by national law or European law. They
stand outside of the legal system. They have their own legal system. No, they have their own requirements, but they're like an organization similar to like the United Nations. You you cannot sue the United Nations. Good luck trying that. And good luck trying to to get a disclosure from from European Space Agency, for example. Any more questions, guys? Obviously that topic is really really interesting. It's going to be more and u more I guess commented in the future. But can you give an example of um cyber attack against satellites or spacecraft that really impacted the nation? I mean obviously if if uh attack against uh Starlink is being successfully executed it's going to have a big impact on um
yeah normal consumers along with uh military because we know that Starlink is actively used in uh Russian Ukrainian war but can can you give any other example that you know so this seems to be like still a bit of a no topic. Uh so it seems like they are still staying away referring from attacking the spacecrafts themselves. I I don't know of an attack where actually I there have been some reports of some old NASA methological satellites being commanded by someone unauthorized. Um but it was never done in a way that it would compromise the mission like on a long term. It would it never had an lasting impact. This seems to be something that is currently still
out of uh out of what you can do. So, but yeah, like I said, like with most more software running on spacecrafts, previously these were very like electronic physical systems, uh now with them being more modular, more programmable, it can very well happen that we will see some like malware deployed on a satellite. Um could could happen because often they're just running Linux nowadays. So,
Do we have any more? Oh,
okay. Thanks for your talk. Um, I'm just wondering about ownership. So if your satellite gets pawned and the attacker has full control of it, when you have virtual machines, websites, when your car is stolen, it's still something that you can grab which the police can shut down, a server you can switch off. Um, how is it regulated in space? As you said, there are various attacks where you can like shoot the satellite down. There's a lot of collateral damage that could occur. Are there any regulations or discussions about uh how the process would work there if somebody loses control of the satellite? Not really. So there's like the treaty of the peaceful use of outer
space by the United Nations, but that's more like
guidelines. Yeah. So I mean the satellites belongs is to the legal system of the country that launched it. And that's as much as I can say about that. So it's it will depend on the nation owning the spacecraft. So do we have any more other questions? Wonderful.
Hi. So uh first of all thank you for the very nice uh presentation. It's a very nice topic in my opinion. Um what I just want to ask out of curiosity is um do you also have done much cooperations like with central intelligence agencies or like with the military since they also operate with using like uh satellites as I know I think in Germany there's this big project like called uh sigant I think it is used by the BND I'm not sure can you repeat the question I'm not not sure what the actual question is so um my basic question was like is there also like a cooperation with the military or the central intelligent agencies like the BND for
example. Yes. So like I just said so the the the BSI for example they are now ruling out more policies also for operating spacecrafts and for companies contracting in the critical infrastructure. So it's now treated as a critical infrastructure domain and also space is a war fighting domain. So like the German army now has a space force as well. Um, so there's a a closer cooperation now between like critical infrastructure providers and cyber defense operations. So this is is really coming closer and closer together. The the cyber defense and critical infrastructure and and space is part of critical infrastructure, but also energy transportation. There's more and more uh cooperation like in in terms of like
NATO for example does a lot of things there. All right. Thank you. So, any more other questions? Okay, thank you so much. [Applause]