John Strand - A Quick, Efficient Yet Not Entirely Sane Introduction to Deception (BSidesFrankfurt 20
Show transcript [en]
there we are all right well thank you so much for coming um you know it's kind of funny we had dinner last night it was a fantastic dinner and the question came up what the hell are you doing in Frankfurt um and I wanted to address that question because I think it's important one I like Frankfurt uh I'll tell you this story the first time I was in Frankfurt my wife is here with one of my children they can confirm the story it's all true uh the other reason why here is I like Beginnings I didn't go to Defcon this year I didn't go to black hat unfortunately I went to RSA and those conferences are becoming too
much they're huge and being at the beginning of a conference like I was at bides Transylvania I don't know if anybody was here was in that Romanian conference in clu it was amazing I love being at the beginning of conferences now I'm not at the very beginning of this conference but being at the second conference or somewhat the beginning is special you tend not to forget these things you tend to say I remember when I was there when it was a hundred people in a small room in a university these times are amazing and that's ultimately what I'm looking for uh to that end this is a computer security conference I provided a tiny URL for you all to go to trust
me uh it'll get you free Labs everything that I'm going to do today is going to be available for you to do in fact if we look at the labs that I have here let me go here I have a no no no no no no no no bad Microsoft um I'm part of anti- siphon security training and black hills information security we have a booth right out here in the hall uh all of you should get a copy of back doors and breaches it's free uh we finally got a publisher here in the EU which is fantastic CU I don't have to smuggle them in to Europe anymore and explain to customs why I have 500 of
these it's awesome at 400 a.m. uh in Romania uh but all of these Labs uh for these classes that I teach we teach pay what you can classes uh int to Sock core skills intro to security the ones I will be doing today are uh cyber deception Labs so I'll be running through those and these are all available you'll get access to the instance um which is a full Windows 10 instance with Windows subsystem for Linux running on it and you'll be able to do everything that I do here today with family and friends it's great to do over the holidays or with pets I don't know whatever you do uh so let me go over here I want to have
a little bit of a conversation about cyber deception uh for the longest time in computer security if you ever discussed cyber deception many times it was inter terms of honeypots we're going to set honeypots and the conventional wisdom in computer security is don't do honey pots or cyber deception until you have done everything else and that argument is complete and utter garbage it is incorrect and it's detrimental to the industry and we see this persist again and again and again Brian Krebs friend of mine uh says deception Technologies are nice but advisable only if your organization is already doing 99% of the rest of the basic security stuff I disagree with Mr Krebs uh Jeff Moss
another friend of mine um dark tangent founder of Def con and black hat said one interesting Omission Moss said was the apparent lack of use of deception technology I've never heard one speaker say and then I checked my Canario or and then I reviewed the deception Tech who here use uses deception technology we need to change that and I hate to disagree with these people uh because they're absolutely amazing luminaries in the industry but they are wrong every one of you when you go back to work should Implement some cyber deception Technologies immediately on Wednesday they don't have to be full honey pots they don't have to be complicated they can be relatively easy and they will
work so let's go through some of them one of the things when we're looking at detections these are this is a graph from a number of years ago on how organizations detected an attack right anything that has a little red or like square around it is external over 67% of the detex and organizations today are from third parties telling you that you've been compromised it could be law enforcement it could be your customers it could be your own employees that have nothing to do with computer security but it's 67% it's actually 66.7% of the detects that we have in the industry are from third parties picking up the phone and telling us that we've been hacked not from a magical vendor
not from a single pane of glass not security orchestration Automation and response outside of the organization and we need to have a conversation as to why that is and how we can turn that around and be better at what we are doing in the United States we have miter they have developed the shield engage framework and this is a full framework that they have of deception Technologies and it's a framework that I help them uh write so many of the things we're going to be talking about will be coming from this framework so I want to go on a little bit of a tangent let's talk about threat intelligence feeds there are right ways and wrong ways to handle cyber threat
intelligence the wrong way to do cyber threat intelligence is to spend a lot of money for bad IP addresses bad URLs bad domains when we purchase that a lot of those entries are old it's talking about attacks that happened on another organization a week ago a month ago a year ago it is not something that is necessarily relevant to what is going against your organization today let me further clarify at Black Hills information security we do over 670 security assessments and Pen tests per year the IP addresses that we are using today are not the same IP addresses that we used three days ago they are not the same domains that we used a month ago we
are constantly staying ahead of the detection wave where people are detecting the techniques the websites the URL the IP addresses that we use every single day so almost by Nature much of what you get from cyber threat intelligence is out of date before it even hits your organization as well so I think deception can be a technology that is cyberthreat intelligence against your organization right now what do the attackers doing post exploitation what are they doing for Recon what are they doing for active scanning and attacking this also applies to nation state level adversaries I have done nation state level hacking for the United States government I have done it for DOD I have done it for the
intelligence community and I have done it for Special Forces the main rule that we had every single time I did an OP was don't get caught that is the rule don't get caught and there's a number of reasons why we don't want to get caught number one getting caught sucks number two if you're nation state and you're using techniques or you're using tools that are really expensive brand new malware that bypasses endpoint brand new communication techniques that bypass firewalls that costs money in very real terms it also costs time so when I'm doing in operation for the United States government or when I did it in the past if we had even a slight chance of being
detected nine times out of 10 the Commander in charge of that operation would pull the plug because it wasn't worth getting caught so we want to do is change that calculation to where getting caught is a high probability and as I mentioned the stuff that I'm going through today is part of anti- siphon security R training but I have an entire class dedicated to this that's two full days that is free or pay what you can so if you like this and you're like I would like to spend two days going over a lot more different techniques we have a class that's available for you so I'm going to start at the very beginning because it's super
easy to do we're going to talk about Canary tokens by thinkest so if we go to the canary tokens website Canary tokens is free I don't know if you remember a security researcher subt on Twitter that was coming up with bypass techniques for edrs a number of years ago he now works at thinkest and harun and the team make this available for free you can generate these Canary tokens where you can create a web bug a DNS token a QR code which is fun my SQL dump if somebody dumps your database AWS key this one's fun because you can put it out in a GitHub repository or someplace inside of your organization and as soon as an attacker
tries to access that S3 bucket you get a notification fake app log for Shell redirect sensitive command this one's actually a registry key uh sensitive command that if anybody tries to run a command on a computer system it automatically generates a highlevel alert web image um uh uh Excel spreadsheet Word document tons of them uh one of the ones that is my favorite is this a cloned website when we're doing a taxs okay we will clone a customer's website for the purposes of a spear fishing engagement all I need is a user ID password two-factor authentication something like that I clone that website and then I send an email to the victims at that organization and then they go to that
website it I intercept their user ID password two-factor authentication and now I'm them in their cloud service this is standard level attacks that happen again and again and again what this does is awesome so I can put in a domain that means this is the domain if this JavaScript ever fires on this domain don't do anything so when it executes it knows the domain of the website that it's on I can put in my email address and then I can put in a little note to myself there we go and then I create the canary token and it creates this JavaScript um this is amazing because it says if the windows location does not equal Black Hills infos SEC then it's
going to go to Canary tokens and it's going to trigger this alert what this does and by the way you can totally offis scate this like so what this does is when a hacker clones owns your website it automatically takes this JavaScript with it now when the attacker runs that website it runs the JavaScript it sees it's not on a blackhills infos sec.com domain and then it automatically triggers an alert and I get the IP address of that cloned website before they have ever sent a single spe fishing email into my organization think about that let me say that again I will get the IP address of the cloned website before they send a single spirit
fish into my organization so I can deny list them before they ever launch their attack ladies and gentlemen this is cyberthreat intelligence not something you purchased that happened a month ago a year ago two years ago this is telling you that somebody has cloning your website right now and all of this is free all of it's free by Heron and the team at thinkest Canary um so I just went through all of that uh this is what it looks like at Black Hills information security at least this is what it looked like back in 2019 um we had uh we don't it doesn't look like the City MO because we import all of this into elastic I saw somebody
walking around with an elastic shirt shout out uh we import this into elastic elastic now so it integrates with our full stack of detection but this is what it looked like with them setting up actually this is a number of different attackers but at Black Hills information security we are constantly being attacked uh so we were able to identify and shun all of these IP addresses uh before they send any spear fishes into our organization and if we look at our filters we can see where these people are sending attacks in and they're automatically blocked so this is one week at our company in 2019 like I said it looks different in elastic now the
next one is word dos and I'm going to do a demonstration of how you can couple this with a share because I think it's hilarious uh but you can create Word documents that Beacon back the first time I ever did this I was working with the United States law enforcement agency they were working a case where a 12-year-old girl had been abducted we knew who had the 12-year-old little girl because he changed his Skype picture to be a picture of the little girl crying so working with this law enforcement agency they came to me and they said is there any way we can work to find where this individual is if you remember in the old days with Skype if
you went to Skype with a warrant they would basically tell you no we're not going to give you IP address and location information for any of our customers ever so what we did is another family member that was communicating with him via Skype was working with us we created a Word document we sent the word document to the suspect and the name of the word document was something like news clippings because his friend said hey you know there's a warrant out for your arrest here's some news clippings he opened up the word document and we got the IP address the date time stamp and the source Port if you have IP address date timestamp Source Port you
can go to any ISP in the world and you can get a with a warrant if they support warrants and they can tell you exactly where that IP address is at that time and we were able to get the girl back so I used it in that case that was a long long long time ago but you can also use this in your own organization where if you believe a system to be compromised you can put a Word document with a beacon in it with a name like credit card information Financial routing information information and the attacker will grab that document pull it open it up and then you'll get a call back from that
attacker now how accurate is this generally speaking location based on IP address is very inaccurate it just is many IP addresses here in Frankfurt if you geolocate it puts you in the city center of Frankfurt it's just yeah it's there we have to understand why because we can get a lot more accurate if we understand how routing works and we understand how networking works so I sent this email to my brother a number of years ago who works with us at Black Hills information security and he opened up the document and this is just using the Straight Canary token website I have the IP address the user agent string the token reminder says he opened it so far
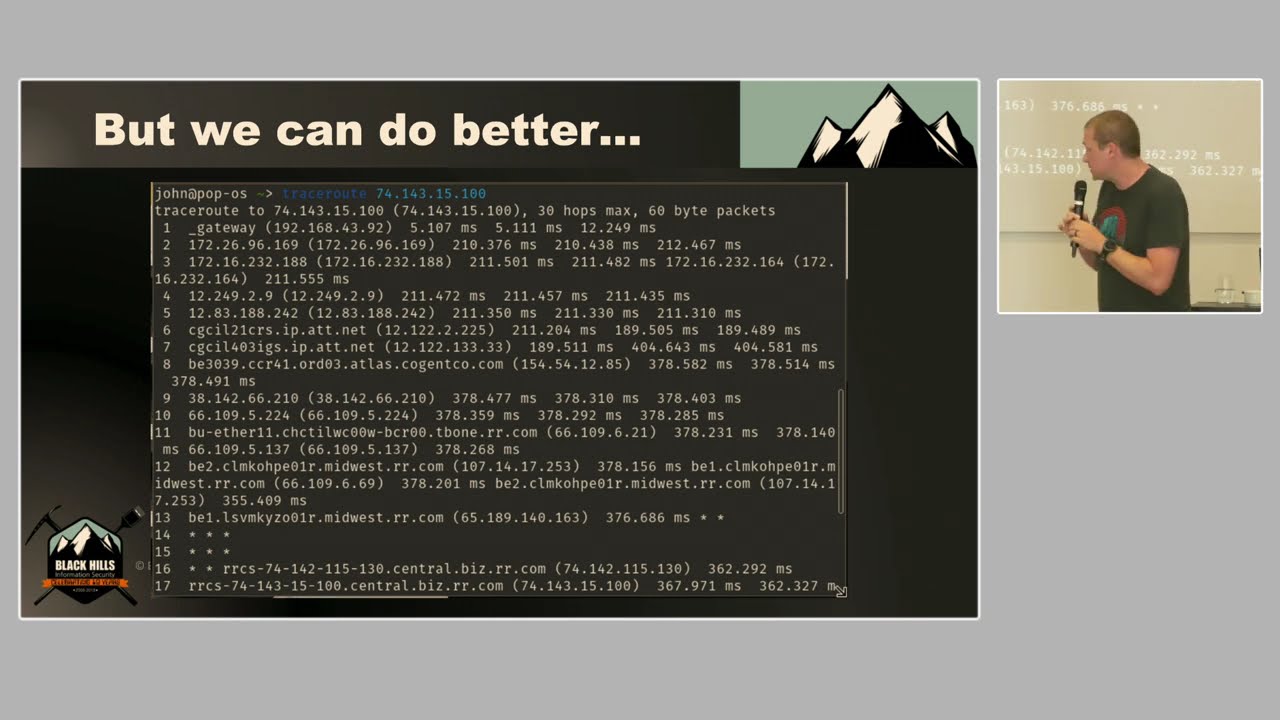
that's pretty good this is where everything went wrong on this particular one it put his location here in the middle of Louisville Kentucky we were all the way over there kind of where the U is that's not hyper accurate under any stretch of the imagination it just isn't now if I had a warrant I could get more accurate but I didn't instead what you can do is you can trace route trace route to this IP address will show you all of the routing hops between where where you're at and the end destination and here we have the end destination of the IP address that open the document I'm not interested in that that IP address is a dynamically
assigned IP address via DHCP isps do not track geolocations of dynamically assigned IP addresses because that would be insane not interested in that IP address I'm interested in this one this IP address is the routing hop right before the IP address of the hotel that we were staying at isps tend to be far more accurate in geoca their routers and where their Network infrastructure actually is and with that particular router it got us within half a block of where we were so you can see we're here there is a hotel where is it Hyatt Regency Louisville is where we were staying that's a lot more accurate and once again if you're working with law enforcement you can get
even more accurate as well but if you use the one with Canary tokens it doesn't work with Linux word processing it doesn't work with Mac word processing we can use word web bugs for that and you can create HTML you don't put this in side of the word document you would use vim and you would save it as a doc file format and here you can have the HTML the head casting stylesheet and then a one pixel by one pixel image source tag this one will work with all of these it'll work with Obby word lib office Apple text edit Microsoft Word no problem easy to use the next one I want to show you is uh I'm actually going to
do a quick demonstration you can actually couple some of these things with a honey share and I'm going to show you that one of the things you can do in your organization is you can create a share in your organization and let me explain why it's really incredibly important for you to understand what are the top techniques and attackers going to go through post exploitation if you understand the pathways that an attacker is going to take there's really only about five post exploitation techniques an attacker is going to go through to try to elevate their privilege inside of active directory they're going to do these five things one of them is a password spray one of them is using tools like blood
hound to identify shares and files in the organization they're going to do these things they just are and if we know that they're going to do those things we can put traps in those specific areas where we will catch them so with this one we're going to create a share I'm going to do if config like this once again all of this is going to be available for free to you all the entire lab environment everything is ready to go I've got my IP address that's great I'm going to become root the password is ADHD of course which I misspelled apparently there we go there we go all right now I'm going to CD into impacket now impacket is
generally used by uh pen testing firms uh to create shares that intercepts um uh password hashes so I'm going to go into the impacket directory and we're going to create an SMB share with the name secret now the way an attacker finds this is they have automated tools that automatically discover all of the shares that are available to them um a number of easy ways just get on an environment type net view by itself and will show you all of the shares on the network on a Windows system so very common for an attacker to do that all right so now I have my share is going to start up I need to grab my IP address here
17228 97250 I'm going to grab that IP address come on there we go Mr Computer well done copy that all right so now we have our share running so now what we're going to do is we're going to kind of go through the steps of an attacker trying to access that share um we have this net use star that means it's going to mount the next available Drive letter starting with z working backwards and it's going to be against the target IP address and it's going to try to access the secret share all right so we're going to go ahead and put that in that is not what I wanted my copy and pasting skills have
failed we go so let me cop copy and paste this again so we just very simply stood up a share that's all we did right and now I'm going to put in my IP address here there we go and I'm going to access it see if this works uh oh it looks like it failed something about demo Gods not being kind let's read this error though let's figure out and troubleshoot what happened here so I tried to access the share and Microsoft came back and told me System error 1272 has occurred you can't access this shared folder because your organization's security policies block unauthenticated guest access isn't that awesome that we have security policies that keep us safe you guys feel warm I
do it's great it's great what else do you have Microsoft these policies help protect you in your PC from unsafe or malicious devices on the network I feel I feel safer tonight knowing that Microsoft has my best interests at heart but maybe if we go back to where I have my honey pot running it might be possible just possible that Microsoft dumped my password hashes anyway so I love that error because Microsoft is like that's dangerous someone could get your password hashes and then it literally does that thing right here but if I'm setting this up as a Honeypot there's some great information here I have the source IP address I have the host name I have the name of the
user and as an added bonus I also have their password hash but this is enough information for you if somebody post exploitation is trying to enumerate shares in your environment you're going to be able to identify the system immediately and once again and I cannot stress this enough any attack or post exploitation is going to try to enumerate shares in your environment you name a share secret or help desk it admin any of these those are the first shares an attacker is going to go to but that's not all we can actually do some more things from the other side does anybody have want to throw a guess like what are some other things that
attackers do Post exploitation like what would you do anybody here do red teaming you know right what what is some of the techniques you do dump creds right and many times we'll do that through a password spray right where we try one password against hundreds if not thousands of users why would I choose only one password to avoid account lockout right so that brings me to another demonstration so once again with this one did this look hard to you the the honey share that I just set up did that look technically difficult at all you set this you forget this when it triggers then you immediately lock down that IP address that is trying to access
shares very low effort very high return on investment in your organization the next one is even easier the next one that I want to show is honey user um I'm going to use the built-in Windows Event Viewer and the reason why I use Windows Event Viewer is Windows Event Viewer is like the biggest piece of crap ever created for event log analysis it is it's bad is what I'm trying to say and if you can make this work with Windows Event Viewer you can make it work with Splunk you can make it work with elastic you can make it work with arite if you want to spend a lot of money but you can make this work with
your super expensive tool all right the concept is the same so we're going to create a user his name is Frank why Frank just I had to come up with a name I just did um so I'm going to CD into the tools directory like so oh wow so nice it did it twice there we go so I'm in the tools directory and I'm going to run this script that generates 200 users just so it looks like a semi-legit environment for the password spray um takes a few seconds for it to run uh but the idea is post exploitation I get on John's computer and I run a password spray against all of your accounts in the
environment I don't choose the accounts and this is important I don't go through and say your account in particular looks interesting you're an administrator you're an administrator they run tools that indiscriminately try to authenticate to every single account in an environment they do this by dumping net userspace slain to dump all of the users off of the domain then they automatically spray every single one of those users and the vast majority of organizations do not have the ability to successfully detect these types of attacks which is ridiculous uh any Sim with their sh their salt should be able to detect this but unfortunately it's a little bit rare So what I'm going to do is I'm going to
create a custom rule in a vent viewer that if anybody tries to access the Frank account it's automatically going to create uh it's going to show us a rule uh it's going to show us the event log in event buer uh so like I said if I can do this in five minutes an Event Viewer um you absolutely should be able to do this in your super expensive Sim uh it's not hard it's basically setting a rule if anybody ever tries to log into this specific account lock it or deal with it immediately now you have to log in you have to log in the account and this gets into a bit of trivia I'm going to call it
Frank what is Epoch time for Windows computer systems event logs oh sorry user accounts anyone know I'm getting January speak up you're really close what is it January 1st 1970 is a great Epoch guess it is correct for Unix it is correct for a number of things in the file system um it is correct in memory but it is not correct in this instance fanastic because of the Gregorian calendar cycle that is the furthest back that you can go for the Gregorian calendar uh instead of the Julian calendar uh so very good Round of Applause that I'd say like one group out of 10 get that well done so you have to log in because if you don't it says the last
time that Frank logged in is January 1st 16001 and we will not attack that account all right so we have all of our accounts created I'm going to clear my screen we're going to fire up some Powershell and we're going to use a tool uh that we created at Black Hills information security this is by Daft hacked or bull buic and um going set the execution policy unrestricted I don't think that came through we go all right then what we're going to do is import the modules for this tool and this is a common tool we use this all the time at Black Hills information security we see it being used by malicious attackers or variations of it
called domain password spray in the wild and we're going to fire it up with a password of winter 2020 now this is going to try to authenticate to every single excuse me every single one of the accounts on this system with a password of winter 2020 now you're going to see it get into like five or six accounts here but it's not going to get into Frank's account um and I really want to stress that it doesn't have to successfully log into Frank's account it just has to attempt to log in to Frank's account and because it attempted to log in to Frank's account if we go back to Windows Event Viewer you will see if I refresh I think
two or three new event logs where somebody failed to log in to the Frank account once again does this seem hard no this isn't difficult at all this is super easy to do it doesn't cost you anything I will warn you there are vendors that will charge you hundreds of thousands of dollars to do this for you um you don't need to spend that money like set up a honey share set up a honey user the class if you look at the labs there's like 10 15 more uh Labs that we have tons and tons of things for you to do to absolutely mess with an attacker's life and it doesn't cost anything at all um
if you want to create it in administrator account some people try to get a little bit spunky they try to create administrator level accounts and by the way if you're going to do this with a real administrator account you have to be somewhat careful um first things first don't be subtle on the name um I just called mine admin ADM administrator just right on the nose trust me no hacker in the history of hacking ever ever has looked at an account like that and been like that's pretty suspicious no they're going straight for that account the next thing you need to do is you need to lock and disable the account without locking and disabling
the account let me explain how give it a ridiculously long password I think that goes without saying the next thing you do is you set the log on hours to nothing so the account is enabled it is active but under no circumstances any hours of the day does it allow you to log in this account I learned this trick back in 2001 I had a friend that was a systems administrator and I decided to mess with him because we pranked each other all the time was it back then and he would log in and he was very frustrated because he would work work work and then his computer would log him out and he couldn't figure out why what I did was I
set his login hours to be a smiley face yeah things were different back then all right um then whenever somebody tries to authenticate to that account they're going to fail but it's going to generate an alert you have to set that up in your sim curb roasting uh once again post exploitation we go for curb roastable accounts it's it's one of the five right you're going to do curb roastable accounts right there you're going to try to jump in with curb roosting you can do the same thing create a service account that is curb roastable with a really long password and uh this is from a tool that we talk about in the class uh that
does uh Canary tokens with curb roastable accounts and I love this whenever I see this in reports from our customers where they we got an alert from your tester triggering this high priority alert someone may be attempting to exploit active directory for more information on what cerb roasting is go here and then we put this in our report and I love putting this in bhis reports multiple hosts on the domain were installed as traps activities conducted by bhis revealed that these traps were vulnerable to multiple insecurities and they made tempting targets any interaction with these toasts triggered alerts to the customer and reported to bhis during the test while there should not be relied on as the sole source of
protection they add a great layer of added defense and my testers about it constantly they always like well we had another stupid customer where they went through John's class and they set up all of these honey pots all over the place and wasted all of my time and I'm like cry tester cry collect your tears send it to me it makes the best one so all right um we have other tools in the class this one's Honeybadger um this is where we uh we use mono uh to compile this code and we create a straight executable it's cool once you get into an executable you can convert it into a ton of different things you can convert
it into Visual Basic you can convert it just about anything uh but this basically does a wireless site survey of the attacker's computer so if they're trying to off escate their IP address it'll Geo locate them with their Wireless with netsh um netsh WLAN show networks mode equals bssid you can submit that to Google and Google will tell you here's where that system is based on the access points nearby compile it and then the results are like hyper hyper accurate uh this one nailed it within 77 meters of where it was so it's really cool and you can get it there um but I have a couple of additional things I wanted to share uh
back doors and breaches we have this is so awesome because I used to have to smuggle things into EU I would show up with two huge roller bags filled with back doors and breaches cards and that was I was joking going through customs we landed inclusion of Poa last time I was here at like 4 a.m. and we had to sit with Customs for like an hour explaining why I had 500 decks of these they were like first they're like are these cigarettes no are you sure I'm like well anything could be a cigarette if you smoke it wrong thing to say at 4:00 a.m. don't do that all right uh but no they were super cool all
joking aside but we have the cards out there it is a full incident response tabletop game um I'm going to be here for a while if you want me to show you how it's played you want this it's one of the greatest ways to learn about attacks you draw a card for initial attack and compromise one for uh pivot and escalate one for command and control one for persistence and there's an almost infinite number of hacks and then you use the blue cards to do this and as I mentioned this environment that I shared with you all um right here if I go to this this environment this Windows 10 environment it's slow but it's free
and um it's completely available to you it has all of the labs that I have listed here are all available inside of the VM you can run any one of them and uh you can learn more about cyber deception and you just go here to get signed up for all of those free Labs but I'm going to leave you with a story okay got a few minutes I'm going to talk about the first time I ever came to Frankfurt so a long long long time ago in a galaxy far far far away as in like six blocks from here I was uh invited to come to the city and do some security work in the realm of cyber deception and
the contract was a very good contract I I it was over Thanksgiving which is Us holiday and I didn't want to go so I submitted a quote that was high and they came back with a purchase order and it wasn't in US Dollars it was in euros and at the time the Euros were 150% of the value of a US dollar so it was a very lucrative contract so I take this contract down to my wife and I'm like honey I've got to go to Europe I'm going to Frankfurt over Thanksgiving she was just justifiably mad she's like that's our holiday you can't do that what about your family what about you know there people we got
we got we got to eat and okay that's pretty much all we do in the United States on holiday we just eat and um I show her the contract and she leaves the kitchen and I'm like honey is everything okay she goes I'm packing so she booked the hotel uh the customer told us to stay at this hotel it was a really nice Hilton and it was really expensive and they were like we're going to cover the cost uh but she wanted to come and the kids were going to come we have three children and she goes that's really expensive I'm going to find a cheaper Hotel so she finds this hotel we fly out here airplane's
completely empty uh we land we get in the train and we take the train to the train station downtown from the airport and she's like I got us a hotel really close to the train station so so the kids and I we can get out and explore Germany I love telling this joke in the US because no one gets that they're like first they're like what's a train why didn't you guys rent a truck or something like why do you take a train I don't understand do they not have cars in Europe so we get get off the train we're walking down the street and like we're following Google Maps and it's like turn left and of course the kids and my wife
and I are just like this is sketchy we look down the street and it's all like red and like pink lights as far as the street can tell and we're like this is not it so we kept going and Google's like turn around go back yep so then we walked down the street it wasn't that far down the street and it was one of them high class hotels that you have here in Frankfurt it was one of those ones it wasn't a hotel it was an otel because the H was burnt out and it was one of those amazing places is where you had to push a button to unlock the gate to get into the hotel you know you had
to push it it's like and then someone in German you know shouts out what do you want because it's like midnight and we're like oh God please let us in the gate opens up we go upstairs and this amazing lady is there and Erica picked this hotel because they spoke English catered to Americans I'm like yeah right uh we know what you think of Americans um we showed up and she said oh my God you have children like yes we're going to need to put new carpet in your room so she shouts something in German and I don't know if you all know this but German is a terrifying language to people in America it's just a it's a
very blunt harsh language it's like you go and you see like this Romance movie on the airplane you're like God they're yelling at it each other the whole time so she yells at this guy he's like and he's like and he shows up and he's got this roll of carpet and he like walks up these stairs we're like what the hell is happening the lady made us a really nice little dinner with some cookies she goes we don't get many families here very often like clearly um finally our rooms are done we have two rooms adjoining each other so there's a door open between the two rooms my kids are in one room my wife
and I are in another room we're kind of freaking out people I'm telling you there's bars on the windows it's kind of it's dude it's sketch it's a sketch hotel and uh we get snuggled in bed get the kids snuggled in bed going to sleep the door flies open and the dude that put the carpet and by the way the carpet is like ragged cut carpet it's horrible he comes up to me and he goes don't turn on the television and he runs up to the TVs and unplugs the television's in both rooms which naturally means for my kids they spend the entire two weeks like trying to push chairs up to get wonder what's on these TVs you
know and uh so no but it was awesome we couldn't find another place uh and it turns out like the lady made breakfast for my family every single morning they were very very nice they were super polite my kids love Frankfurt they're all older now my youngest is with me and it's funny when my kids talk about it they're like do you remember Frankfurt Dad I'm like yes I do I I do I do remember Frankfurt why did they have machines that sold balloons on the street corner distinctly remember balloons on every was that Frankfurt yeah that might have been Amsterdam I don't know but we we we fell in love with Frankfurt in the worst part of Frankfurt
um the people that ran the hotel were incredibly nice like I said they took care of my family uh we we explored the town so when I got an opportunity to come back I absolutely took that opportunity so with that I want to say thank you so much for having me um we have back doors and breaches out here by the way the sap people I got to talk with them last night their talk is fire I am sure all of the talks are amazing but they're going to be talking about some cyber deception they're going to be talking about some Erp hacks they're going to be talking about detection it's going to be amazing you guys are going
to have a great conference and with that thank you so much everybody





