Let's Phish: How To Scam Everyone, Everywhere, All At Once
Show transcript [en]
enjoy it hi everyone uh so as you heard today we're going to talk about something a bit different uh which is actually hacking humans and uh I I listen to quite a few talks about scamming and fishing and very often it was just about the uh stories of the attacks so what I decided to do today is to do something slightly different and look into why someone actually gets hacked uh when that moment when someone does what you want what actually happens to the person and how we can exploit it so that you can use it on actually any human being uh that you want to use it on so to tell you a bit about myself so
that you uh understand why I'm talking about this subject uh so basically I started my career as a broke filmmaker uh where I pretty much started hacking uh not computers but in a way hacking my life uh because you can actually hack everything if you understand the process of hacking now um something important is that at some point I went to study hypnotherapy and I didn't study it to become a therapist um I studed studied it to actually understand human mind but in the process I realized that um it was a good career you could make good money from it so I started to run it in the evenings and that's actually how I got
into social engineering because uh when you you see someone in front of you as a therapist you get access to a human being as you never do in everyday life because people don't hide anything um they basically show the processes of their mind without any obfuscation it's completely wrong and what I notice quite quickly is that people run different patterns and they run actually quite few patterns over and over again and you can see it on things like depression but you can also see it on things like everyday things everyday tasks how you respond to human being how you respond to stress and with these patterns we can actually use them as a vulnerability because once
you understand what type of pattern the person keeps on running you can exploit it we will get to that that's just a little bit of introduction and then I went into somehow I got into ethical hacking uh I did it for two years and now I'm actually on a career break looking for some new opportunities and new challenges and I do also quite a lot of research into Ai and uh content Creation with AI which actually is a form of social engineering as well like uh hacking AI but let's look into like what we what we already know about about hacking humans so basically people have no zero days what it means that unlike uh the
technical hacking we already know everything about hecking humans or we can always like there is there is nothing new to discover and that is quite important because the playing Ground is actually even with for us as the one who want to protect and the malicious actors which is quite important because we all have the all the information that we need now very important thing is people are predictable mostly in the western Society uh and mostly when you have employees because companies they tend to hire the kind of same pattern of people so once you get to know the company and their culture it's somehow much easier to hack someone within that company then as I said human actions are
dominated with patterns and that's one of the most important things uh that we need as hack as hackers of humans and as I said in modern society uh people have very predictable responses which uh with observation and this is actually very useful in Espionage uh you need to observe the person understand how they react and then you can exploit them so as I said uh everything is a pattern so is hacking humans it has its beginning it's a process and the end and to understand that we basically one of the most important things uh which sometimes when you heck you don't even think about but that's you that's what you do anytime someone does what you
want you trigger some uh you trigger some emotion and emotions are actually very important in people because they do one things uh we have we have two different parts of the brain one is the new one it is that kind of thinking brain the brain that you use to evaluate things to make decisions and then there is another part of the brain which is very old part of the brain and that was developed uh when we that was basically developed uh when we were in our um when we were in the caves so when the the brain was still quite new and it's still with us and that brain actually governs emotions and it governs uh survival and
that is that means that that part of the brain is actually the primary one so if the brain thinks that there is any danger or any situation where it needs to take over it switches of the thinking brain and goes into the into the emotional brain so which means that if you evoke emotion in someone you are slowly slowly uh stopping the thinking brain so then something happens what I'm calling AEL Vision uh which means that the sinking brain is shrinking shrinking shrinking and if you are triggering the right emotion in the person you will basically lead the person towards the goal where you want to lead him or her um that's why if you know what type of
emotion and what type of need in the person you're triggering you have much better uh chance to actually hack the person and we will talk about that because the needs the human needs are actually the most important when it comes to when it comes to hacking humans and then once you once you achieve that once you blur the mind of the person then you can you can do a manipulation and once you have the Rapport as well with person you can do whatever you want pretty much so that was our introduction and now I would like to tell you two stories of two scans um and I chose these to actually show you how a person gets
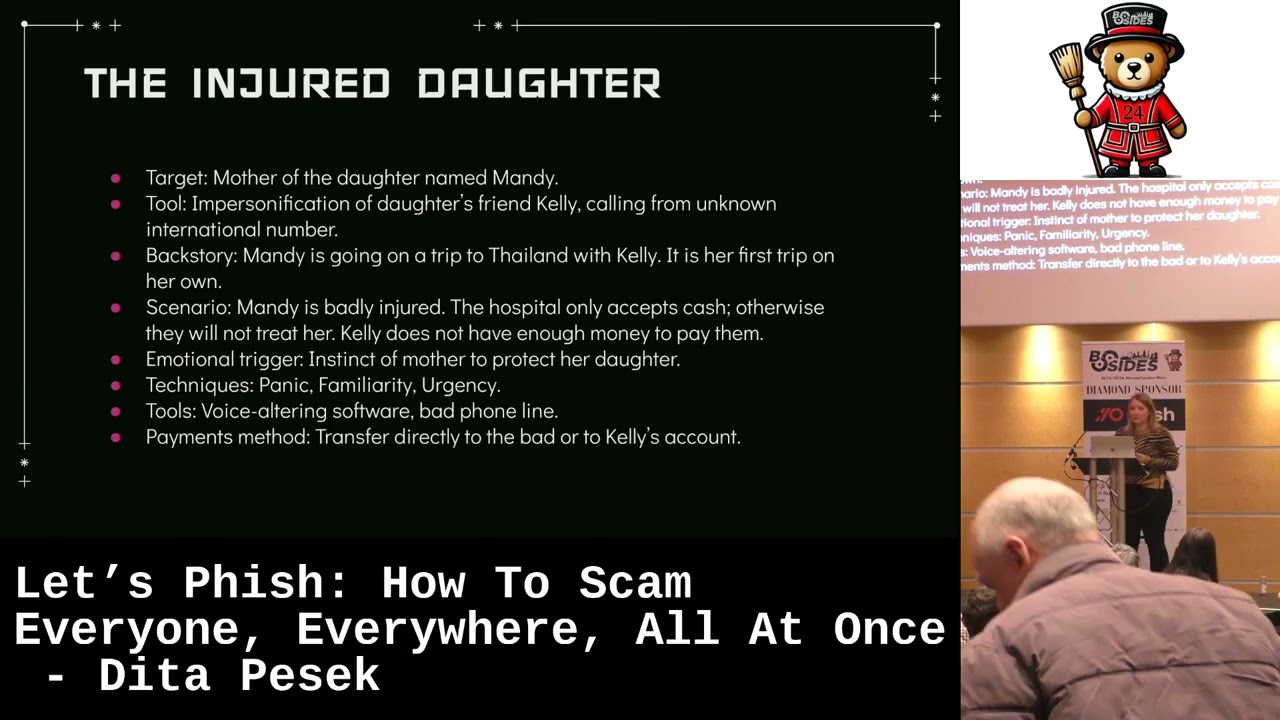
hacked and analyze why because as I said uh the why is quite an important question and I don't think it's being asked as much when you do the fishing exercises or any kind of redeeming uh so that can actually help you to uh do better better attacks so the first story is of the injured daughter so basically we have a Target which is the mother of a daughter called Mandy and the mother the Mandy is about 19 years old so uh she is she's young she doesn't know that much about the world and for the first time in her life she decides to travel to travel abroad and she goes uh with her friend Kelly and they decide to go
to Thailand from all the places so of course the mother is worried uh because it's actually her primary goal as a human being at that point to protect The Offspring and this is when we are getting actually to that primary code in every human being that comes with the DNA and we all have that type of coding and that's basically the coding that we are as human hackers attacking because if you focus on those types of codes in humans you have much higher probability to hack them so here basically the hackers are trying to exploit the need of a mother to protect a daughter so what happens basically one day um mother gets a phone call from Kelly and Kelly
is really dis is really uh panicked and she says oh we were in an accident Mandy had a uh Mandy had an accident she's badly injured she needs to go to the hospital I don't have the money my car my main car got blocked I need to pay to the hospital because they will not take us uh as they say that um they don't get paid by the insurance so they want cash so now the most important thing in this that Kelly is very who is not Kelly of course it's a scammer but the Kelly in this case she's very emotional and there is one thing about people we mimic other people's emotions so if you have someone
in front of you who is very emotional and mostly if you have the Rapport which there is because Kelly is someone the mother knows the mother gets more and more emotional which means that she's getting into the tunnel vision and the scammer can lead the mother anywhere they want pretty much because uh she is not able to stop and make the rational decisions oh wait I'm going to call my mother uh I'm going to call uh Mandy and confirm so what happens well because the scammer doesn't ask for that much money uh mother sends mother sends the money uh this is also very important because scammers very often ask for amounts that will not hurt the person too badly but
uh which makes it much easier to get it from them also so they will not be uh well they will be prosecuted but the police will not be as interested in them so that's one kind of scenario where uh there is urgency there is panic and there is familiarity uh which are things that we know that are used but the thing that I want you to understand that here the need of the mother to protect The Offspring is actually the crucial in this attack and that's actually what made her to pay the money uh this kind of attack is not not as common because it needs quite a lot of reconnaissance from the side of the scammer but uh with
today's AI like you can use AI agents for research you can use voice and personification you can use even Le fakes which means that the scams are becoming so much easier to do right now and they will get better and better which is actually something that we should be quite worried about because uh also quite clever people are entering the scene of scamming which is also quite important point and then we have another one which is which is quite different and this actually happened to a friend of mine and this is very very interesting scam so a friend of mine she is a therapist she's quite a known therapist and she um she's making money but she's in that
kind of state where she's not she thinks she's not making enough to sustain herself in the world and that is very important Point um the that is basically the point of survival for her this is very important that need to be to have stable career and that's what actually here was exploited so uh basically she decided that she wants to do a reality show and uh she had this uh rapper that she really liked and she wanted to do the uh main track for her reality show but she he was quite famous so she kept on following him in social media interacting with him and one day he sends a message to her hey I really love
your work uh and she is like oh my God this is amazing uh because I want to co I want to do a a collaboration with you and he says yes I would really love to work with you get in touch with my girlfriend who is my manager uh so she did and basically what happened the girlfriend told her yeah of course like we can do this uh we are very excited and it's very important like they were very excited about everything that my friend wanted from um and uh so the girlfriend told her okay so uh you can book us but you can book us for uh $10,000 and my friend was like I'm not
going to do that uh let's have a zoom meeting but of course because it was a scammer it took a while uh for them to arrange and things were always not happening but what's important in this scenario is that my friend and the rapper they were having conversation on what up through all this time and basically the scammer was grooming her so and he was very good at that I don't think that he knew what he was doing but he was just very natural at uh grooming someone because I saw the conversations and they were pretty much about telling her like how how they are connecting and how they have the same kind of objectives and this is very very good
technique for Espionage uh you try to make the other person believe that you are similar to the person and that you really have the same interests and that's pretty much how you get to people uh if they think that you are quite same as them and this is what happened to my friend of mine and after two weeks of course the scam tried something else and he was like he sent her a message uh I'm in Alaska I'm shooting a music video I uh my money got stolen my cards got stolen can you send me $2,000 and of course my friend was like this is weird but because she needed him because she she knew that if she has him
in the show she will get investors so she was placed into this dilemma that person who who would just who would just be some normal fan wouldn't be uh she wanted to believe that he was real and but thankfully she called me and she was like oh this is weet what do you think and she sent me the details of the of the rapper and in 30 seconds it was obvious that he was fake like the handle wasn't real um but what really hit home here for me was that for us in normal state of mind we would know it's a scam for her because she wanted to believe that he was real and because he was
actually attacking the need that was very important for her to survive in this world and to make money that's why her vision was already narrowed and he just picked her in a very right time and he picked very right need and I think this is the most important thing to take from this if you target the need of a person that is important to them you will have them like you will manage to manipulate them which is all nice but how do you how do you recognize those needs because it's lovely to talk about them but um you know we need some list we need some some list that to work with because if we have a list uh we think
methodologically so us as attackers uh our emotions will not be invol evolved involved uh that's why like psychopaths are very good at manipulation because they actually don't use their emotions their thinking mind is always switched on that's why they can always access situation like emotions are the enemy when it comes to you as a person uh not being hacked uh so that's always something you have to try to evoke in a person so just to summarize here like uh we know that time is important either either we need to close very quickly or we groom the victim of course like if you like in Social in cyber security we don't have that much time to groom the
victims but for example in Espionage it I like I heard about some cases where the uh agents who were on the ground trying to recruit people sometimes it took them 11 years to get to someone but eventually they have the time and they found the that one thing that the person was hackable for like that kind of stress point uh stress point of the person so we need to identify emotional triggers and then uh getting emotional response now I was actually wondering like how do we get this list uh because if I just put it together I would just put there the the kind of needs that I focus on and the list wouldn't be
complete so I was thinking and now this now it gets weird Okay um so I was thinking who actually did this before uh because someone had to do it um the manipulation is very old like it's it's been with us since we probably were talking so I was thinking like what kind like in history of humankind who was really good at manipulation and um so I was walking in the park one day and it actually hit me it was the church like the Catholic church was actually one of the best manipulators because they managed to manipulate uh countries for hundreds of years and make them believe that they are the the truth and now how they did that well they did that
because they focused on something that are the needs of people they focused on something that was very dear to the people and then I was thinking what what was it within the within the Catholic church that actually we can use in cyber security then I found it it was the seven deadly sins which I call which I called seven DS so that it doesn't look so weird and this is actually really ingenious uh what they did they basically took the primary needs of every human me that is actually linked to the code to the Survival Code that came with us uh that that came with with us in our DNA because we all have that
coding in us to survive and actually to to make the genome to make the DNA keep on moving forward and on a bigger scale this is the most important thing in a human so what the Catholic Church did they took uh these needs they turned them into something negative and then they said oh well if you if you commit it you're going to die come to church pay us and you will not die so um or die well go to hell pretty much so I think that this is something that looks weird but actually we can use it and I think that everything what we can find in the history that someone did before we can
actually reuse for our own purposes because we can take this and we can change them into something uh that is more accurate for us so last last is love and we know that targeting love and the need to uh have someone and the need to be loved is so huge in people then we have rough which is anger which is also very very big uh and you can Target a lot of employees who are angry at their employers then we have greed which is Need for wealth we have glutiny which is overc consumption or addiction which are actually things that are very well like you can use very well the addictions because the people have very emot like very strong
emotional connections to them and we will talk about how you can actually use them and then we have uh Pride which is Need for recognition which is actually the need that was targeted with my friend uh then we have SLO which is Need For Comfort and envy which is jealousy or need for fair treatment and basically if you take any kind of scam that you can think of you can find one of these that you can attach to and I think that this very important because that starts actually answering your why why the person got hacked uh if the person if you can't H the person by targeting one of these you just move to another one
because I guarantee you if you go through all these and actually focus on targeting the person with those you will hack them uh it's just then more about the way how you um how good you are with social engineering but okay so just to make this more fun I found some examples uh so we have love which is pig butchering which is actually one of the most successful scams uh so far and my friend even like I have friends who kept on like falling for scam somehow um but my friend lost all her savings to this scam which is really quite incredible because what happens um this scamer finds its victim on a dating app mostly on the
dating app and they pretend to be uh some someone in financial industry and they tell them oh I know this website uh send the money there you will get lot of uh which is mostly like a crypto crypto site and you will make lot of money and what's important here it's not about the person wanting to make money it's about the person wanting to be liked by the by the attacker uh very often this happens to victims who never met the person which is really mindboggling because for me like it's very difficult to understand that you would believe someone who you never seen in the real life but because the person who is attacked like their need to be loved is
so strong their vision is narrowed like they they don't think um they don't think rationally and this is why they get hacked and that's what I mean if you heck the need that is triggered you will hack the person then we have anger which is for example we have conflict uh fishing scams where someone in uh the scammer sends an email oh you've being youber reported to HR because of some misconduct um and if the person is actually already in that stage uh where they are angry and when they are frustrated they are far more likely to to clim the the link that means they're already in a state where their sinking is narrow actually these types of scams or fishing
exercises are great with companies they that have uh that have very toxic environment and of course it's easy to find out right now because we can go to glass door check the reviews they are very often quite uh accurate so if you find out that your client has a toxic environment I would I would try to focus on anger uh on these kind of anger based scams uh you will have much higher chance of succeeding uh then we have greet which I had to put that our lovely Nigerian print scam uh it's also Advanced fee scams uh where you need to pay a little to get a lot like recently there was actually scam with Alan musk which was
which was quite good uh where Elon Musk was offering of course uh millions of Bitcoins uh and was a deep fake and that deep fake was actually I don't know if any of you saw it but it was really good and very well done so as as I mentioned before the AI is helping these scanners enormously right now or right now and towards the future uh so you can basically focus on that a greet do I have that there I think the yes the Greet is also bribes um which will Al you will probably see people being Bri much bried much e easily um now because uh as we know that lot of employees now don't trust their
employers that kind of thrust between employee employer is being broken uh for last two years so people are more likely to take the SC the bribes and actually what is very important here that it's not about the bribe it's very often about the person uh being scared that the money will be tracked uh that someone will find out that they took the money so if the scammer uh finds the way how to convince the victim that the money will be cleaned or that it will never be tracked the victim is so much more likely to take the bribe uh I think that's something that's quite important to remember uh then we have pride which is
Need for recognition and there was this amazing scam I don't know if you if you came across it it's the Hollywood uh scam Queen if you didn't just Google this there is like a really great podcast about the scam and this basically the pride is actually need to progress in the career and which can be really really nicely attacked as well mostly for people who are struggling and want to progress uh you can do quite a lot of things with that like for example in this example uh the Hollywood queen which was actually a guy he was pretending to be uh very high positioned women in the film industry and he was Target or she was targeting um the uh
individuals in the film industry were okay with their careers but they Wen on the top and she offered them uh proposition to come abroad uh to do some reies like on locations or anything there and basically the way she got money is that the uh people who came abroad they were paying money to taxi drivers to the hotels and that's those all those people were actually the accomplices of the scammer uh which was actually quite elaborate scam but it's very interesting because there was a lot of psychology of the scammer involved so like if you are interested in Social Engineering I would recommend to to look into this and listen to this podcast okay then we have the need for
Comfort which is very good in places that you know have very strong due diligence like that have a lot of processing in place because we know that people always try to find different roof holes and make their life easier so there will be definitely something that they are over looking so for example in these places uh this fake invoice scam works because uh the employees just don't check anymore if the invoice is uh if if the invoice belongs to the right supplier and that's basically why actually the uh how why the attackers manage to uh make this scam successful it's because the people are looking for the comfort it's it's quite interesting like when start thinking about it
because everything is linked to that kind of need of survival in us and a lot of our responses are and once you start thinking about it it's it's it's become more interesting to actually hack people because suddenly you have so much more options and you can you can think uh which one will I Target and why it didn't work and that if you have specific Target it's it will help you a lot like if you have just a fishing exercise where you target everyone uh like like yes you will have a better kind of success rate if you if you think about like what is the environment but mostly if you if you have a specific
Target uh you need some ammunition and this is basically the ammunition you can use then we have gluteny addictions which is actually very interesting kind of uh area I find because you can do also quite fun stuff with that so we have like Pon schemes which is in a way addiction as well but I think for theed teur uh what is quite interesting about this that like addictions of course they they have very strong triggers in people so if you have if you find people who are addicted to uh let's say gambling so you can create fake Casino websites offering some discounts to them or also quite interesting stuff is that people tend to open their personal emails
sometimes on their work devices and as as the brain it forgets so if it if it sees something familiar that the person already know they can click it so for example if you know that someone is a fan of some football club you can create a fake newsletter that looks like newsletter of that football club and send it to them and put there some huge news like the manager resigns or something like that if it comes to their work email they still there's still a chance that they will forget they are in their work email and click it so I think this is quite interesting way how to get into a person Target something that is familiar to
them and if you find their add ction and Target that like you will get in you will get in eventually and I think this is the last one yes uh which is Envy which is jealousy uh need for f treatment so we have uh High Life fraud scams where it's more about uh finding like the people wanting to uh have luxury in their life but like there was actually very good scam for this in uh I don't know if you heard about that it was in like late late where a lot of women were buying uh underwear from this company and so the scammers created a website that was offering discounts for this underwear and it was like one of the most
successful scams like the like they they managed to Target like people in the accounts departments and uh there was like in the department where there was a lot of women and they actually made quite quite a lot of money for that so uh you can also like focus on something like that also what is with what what would might what might work in uh toxic environments uh is for example unfair treatment so you can you can create an email where uh it's like the fair treatment and fair pay is explained and it looks like it's sent from government if uh the people are already triggered by the employer they are so much so much more likely to actually click the email
so uh these were actually the examples how you can take any type of scam and attach to one of these needs or you can take one of these needs and develop scam around it or develop fishing campaign around it and you already know that you are targeting the coding in the human brain that is linked to survival because if you have to go from the from the bottom it's really difficult unless you really understand human behavior and Neuroscience and the human coding that this is in a way how you can uh how you can take the upper level and make it understandable to a lot of people so I know it looks weird but it actually it
actually makes sense so then I did like something fun just just like this is not uh as much as the part of the talk but I I was thinking because I was in pen testing before so I was thinking like we know lot of vulnerabilities in the computers uh so I did an exercise when I took each vulnerability uh in the computer and you can actually achieve the same in a human we cannot like open the brain and see exactly where the vulnerability is but we can use different techniques how to achieve the similar thing in humans uh but it's not that important I just saw that it's quite interesting way of looking at hacking humans in different
way uh if you are very familiar with the computers you can find the equivalent to uh to the hack in people and that actually proves that people are not that different from computers like the brain actually thinks in ones and zeros as well it has its coding like it's just far more uh flexible than the computers but with the AI like this kind of Gap will get smaller and smaller and you will find that maybe in like next I don't know I don't know the time time frame but maybe in next 5 years you'll find that uh hacking the AI will be quite similar to social engineering like we will start getting more and more into
needing to understand human mind because uh AI is also very fluid and I can already see like that it the different AI models they run similar patterns as the human mind and it it has different ways of confusion in them uh that the human mind has as well so just to summarize this uh basically anyone can be hacked it's really about resources and the time that the attacker is having so if if someone actually hires the uh hackers for hire who have all the time they have lot of resources they very often they most often work in uh groups like they will get to the Target there is no question about that and they very often get to
the targets through social engineering like they do a lot of reconnaissance and try to jump through different targets to the Target that they need to get which is actually quite dangerous and it means that if anyone wants to hack someone and they have enough resources they will do it and that's a question how to protect that it's it's very difficult in the modern society and the way the companies are done that that's why the people are becoming more and more uh important targets for the malicious actors because it's easy it's actually so much easier to to hack someone and mostly in this e economic climate when people are very stressed they already are coming to Eternal
Vision like they are much easier targets uh which no one really actually thinks about um yeah and then just consider those needs consider the needs that are linked to survival because if you and it's also in everyday life like if you want to hack someone and focus on those and you can start observing those patterns in people how they respond to things uh where are their little weaknesses uh like are they really focused on their career then you know that H like the pride might be the the important thing to Target because you know that that's what they need that's what they really need and that way you can start uh looking for that kind of
stress point everyone has a stress point you just need to find that and because it's because that coding is in our DNA you cannot protect yourself from that uh and human uh human actions are dominated by patterns which is very important if you start being good at observing the patterns uh you will start being a really good social engineer and really good at Espionage um and the last one in modern society people are people have very predictable responses it's because the way the system is made uh and actually actually companies are making their own targets pretty much and they they don't even consider that as a problem which is quite worrying but uh that's where we
are right now so uh yeah I think this is the end of my talk do you have any questions
[Music] thanks for the talk is really really good um I just want to ask on The Blue Team side how do you protect yourself from these sorts of attacks what was the first thing you said thanks to the talk it was good sorry I liked your talk so how would you protect against these things yeah like it's it's tough because as I said the companies don't even consider that being a problem and uh so they actually by their hiring process that they keep on hiring the same people they make it so easy for the for the uh first for the hackers to know uh what is the kind of pattern of the people in that company and also like if
they have the same hiring system it's so much easy to get someone some Insider in uh because they understand the process and a lot of actually social injuries done that they just learn something about the subject said what the person thought uh they were wanted to hear and that's how they got in so unless we unless the company start thinking about this in a bit better way like very good thing is to not have people in that stress situations because as I said if someone is stressed they're vision is narrow they are so much easier to haveck uh that's why like for example people in FBI they they focus on those people who are in this stress situation to hire
them as as as their um as their targets to get information from uh so if the mostly if the environment is really nice and people are not stressed they are they they are less likely to get hacked so uh it's if the compan is focused on actually looking after their people uh you will they will not be able to bribe them uh and the people will be in a state of mind where they can actually uh make the decisions about what's happening around them and I think that's the only way how the companies can actually protect themselves anything else doesn't look like cool so thank you so much for being here and uh enjoy the
rest of the day





