OfCORS! How To Do Cross Origin Resource Sharing (im)properly
Show transcript [en]
hello everyone um so I'm Cory I'm CG um if any of you Liam earlier boss so he's comday um but is living [Music] arounds um and other things um so primar some we that topic um but I'll get into why really as we progress um there will be some Theory so you'll have to power through that but get through it as quickly as possible um it's because it's a little bit of a lesser known topic compared to doing your excises all the popular ones on p on that um but it is an interesting one if you can find ability to crack um well okay um so I'll go through this sort of what and why of this walk in
particular um some of the theory there will be some memes to iners Theory um and then of a bit more of a demo into what is looks like and then tips and tricks and finding issues and avoiding of common pits that you might see an internal pest report that's 5 years old hasn't been updated in a while so why so the amount of times I've see sentences like these two so the application responded with the access control that origin header you don't know what that is you'll you'll you learn that today um me request from any origin because there's an Master risk or the API responded to this request with the access control is true therefore gain unauthorized access
to any s of data on the app regardless of yet what we don't see has the TA have we if we WR check that the application responding dynamically to our payloads um have we checked that we're that what we're trying to access is actually a protected resource just a generic homepage um have we actually tested outside of bur suite at all um have we verified that it's actually going to be in exp mle vulnerability or are we just assuming it because we saw an account header um and have we actually try first place um the answer is no to any of those you've seen it or haven't hopefully today your help so what's the risk if you're more
sort of business designed person why why am I saying here um so essentially um these are sort of right so um external sites sub domains of data um those more G targets um Can can in some cases lead to account take over or facilitate it um compromise internal networks is very interesting sort of find but sort on the RAR side due to limitations um and all manner of other probabilities that can also contribute to as well um but they can be really fitly to find in the first place even more fitly to exploit but you do look really cool when you do it so hopefully off use so we're going to begin begin with some
Theory it's not the most exciting thing in the world um but you'll need to know it if you don't know much about C if you're going to try and find um because of the can see so what is the origin same origin policy I'm what is origin it's actually this so three parts to an origin as far ASB are concerned so your your url scheme vertical your domain inclusive of sub important and your PCH which in 443 is going be hidden in your url bar but it is it does count so herey is cross origin so when are we Crossing An Origin so essentially if any one of these three components changes between your target it is a change of origin as
simple as that so if your Port changes sort of less likely if your your changes or something changes Crossing or right um if they're all the same right so these this is one thing need to check when you're approaching this um so what is the so s is a security mechanism that is essentially um prevents CR origin attacks it restricts scripts On Target origin from accessing data from a null origin with a few exceptions but um essentially including authentication information so s cookies um set of data disos responses um so under the JavaScript uh scripts word um will be able to load uh resources hosted on another origin but um the jaas on the same page won't
actually to so it's very restrictive it's all designed to prevent you traversing um there are a few exceptions which are a bit technical javascrip um so that at the end if you
wish so where does c play well it comes into play because the webs if anybody has experience it it's pretty inen there are plenty of times where you might legitimately want to access resources from some other origin to load um resources to host on the website make it easier to navigate fiter Etc so the cuse allows for relaxation of this to allow you to do that um and essentially allow cross in controlled man IDE um so essentially allows a retrieving origin so my website that built um to issue
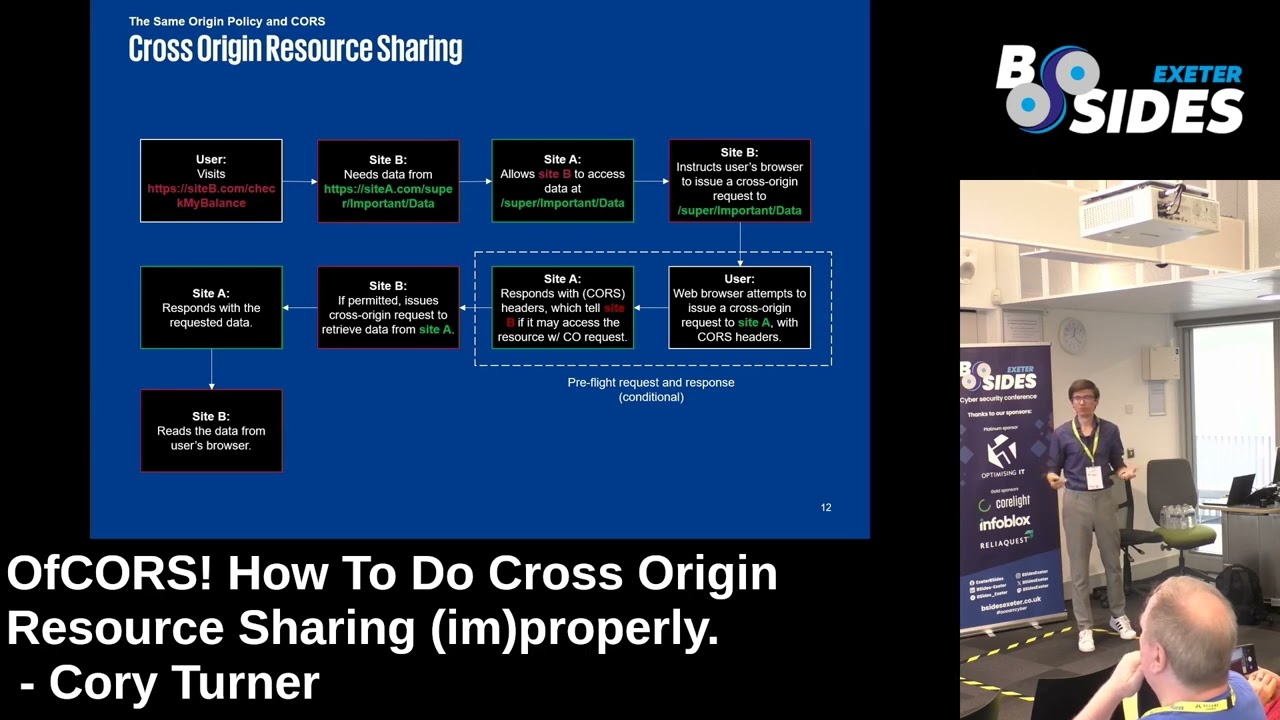
cross and importantly um that's sent by the user's browser this is critically important um you don't have really have a cause vulnerability if the browser is completely enged it's making use of the browser so the sending origin is is uh when the user has authenticated session is using the client client browser to then issue the request to some other origin um that's a Comm we get into later but remember that need ground um so if committed on by theing origin um treating origin then you can sh data so a cause policy on some tet website that's what it looks in nam terms so that's everything I just described so the user visits some site um that site needs data from some other
site and uh there'll be a course configuration on there that um will basically determine whether the sending origin is allowed to retrieve whatever resources it needs um there is this sort of area here that we'll get into get into a bit um but essentially there are two types of in the quest um which you will see um one of see
[Music] you almost I'm try to so why do I care about some he exchanges well um essentially for for you to have a meaningful cability you need a proteced resource you need a resource that you find to access that requires authentication we're not just interested in some generic
or um so um we need to determine whether we can issue what's credential request cross origin not just generic um so in other words we need to be able to sendal from AR Reeve some GC sensitive data so we get into the two types of so simple requests they're simple um it's it occurs when you have one of three uh H methods okay past we with those hopefully um and also when you have a select number of content type headers in your H as well it have something else and to get into but this is essentially what it looks like a very simplified way so we have uh oh I have other points I don't I'm W about so we have um our
fct's browser so go and visit. goes back and then we're trying to send a credential request over to get some sensitive account info specifying our e.com victim receives that and then sends back these two headers Access Control allow origin and access control allow credentials among other things um but this origin have credentials almost familiar you've heard of CA abilities um and then if committed by our victim SES cause policy we send back the data
to that's simp requests pretty straightforward just a few three requests are a bit more complicated and essentially they occur when you have other content type values so um you'll often see these more with Json um Json data being received um most modern browsers will enforce pre flights um in these cases um and essentially what it involves is first sending and options request to uh the uh victim.com and then the actual Essen the Au Quest is going to solicit vic.com on whether we actually allowed to send a credential Sol request so sending this first and then our count um as well um so what that looks like is here you have our options Quest We specify what method going to use and
then if permitted we get whole series of Access Control headers from. um and ited with true and Dynam a dynamically generated uh origin header value which matches our equal site then we can that data so we're sending two requests that won't happen if you're just sending reest [Music] only um this is why I mention involve our browser to
demonstrate s this is what it looks like hopefully [Music]
good so we're trying to get this API key over here as see down there from our VI little uh to retrieve it oh no we can't what's happening so what we can see here is an options preo that comes back to 200 but then we are following 302 back to our L AG so our access injected that so switch browsers here from the B browser to Microsoft Edge and it's actually been around that without changing anything else so why so seeing here first the options PreFlight in the browser PS content type which is what have initiated PreFlight and then on G request has been honored with an access account true header [Music]
right so we've seen there is an example of one um this was much to my surprise when I was a parents talk um and isn't all that well documented unless you are essentially what's happening no we're not moving moving um we get on on to the but to slow that down a little bit this is what pre request looks like so we have these specific headers here method headers and origin uh you will notice that although I am visiting the same site here and here in terms of domain our Port change therefore origin in response to options we have a series of of of AC head as well the important ones being origin and credentials as well our method has been
allowed and because it it does have the content type for um for Json that's also being specified in response in the actual cuse request we see that our session cookies has also been included as what Mak credentials um so essentially it's now being committed to authenticate there origin still here and we can see these head here as well and we get our API looking so essentially this is what I just covered so um when we have credentials what are credentials so they're not just cookies actually um that's the more common one you see but also you'll have things like HDD basic atlm authentication as well um those are defined as credentials as far as are
concerned um and why is it important to know what is is it's a bit tricky let take basic and authentication example so some of us who might be either used to looking at these things or not um we uh be used to saying process for specifying basic credentials in the browser essentially when trying to authenticate a resource that requests uh basic authentication going to get back this www authenticate header um and in this once uh your browser is going to submit another request basic and your credential basic encoded um us a bit more secure than um but importantly the browser will cach those credentials so that in follow on and subsequent for poed resources it's going
to automatically send those on to the T notation so bar authentication we have a similar looking authorization header but those credentials aren't going to be automatically sent by the browser um so when we were talking earlier about the browser being Essen middle man Target site that's important because if it's not automatically sent by the browser then the attacker performing this ATT has to know the token beforehand just onow sending it by itself um so unless it's being stored in some PR insecure Way by browser you're going to have to perform some other token and that one just token right um so that's why it's important to be tokens are bit a bit trickier so controls quite an annoying B of research
I ended up sing so most of us will be familiar with the first two so HTP only um trans JavaScript from access um cookies and secure transmission HTP all very well and good but same site is less friendly um there are three options choose from stct That's None doesn't doesn't really enforce the policy um but in the importantly in the absence of our Target app specifying it most browsers were enforce that by default so you won't necessarily know so not explicitly stated um and that includes chromium um importantly as well third party cookies is to be Dro by defa partian cookies and some other methods of of cookie handling as well um so when you try to send across origin LAX policy
in Chrome or chromium you get this message now inle um and you can end up if you have manage browser for instance with these being turned on edge that's Chrome I believe um and actually it does affect the browser by default so if you try to perform cross request with Max on on the to session then unless you explicitly tell that browser don't do that request you're going to think that there's no exp but actually there is you just need much to my own frustration um as a quick [Music] demonstration um so in this scenario we'll have a um cookie which go that's what the browser currently does and you see it limits it atic so that's what
stopped up our concept ear on just currently shade of Microsoft it's just the behavior that their browser so you see that is now
work and
see so bew you use or make sure you it [Music] correctly so same site this the last side I promise um so you have three settings uh currently so either none which is uh not all that commy these days in my experience can happen um for nonone browsers this uh can be the default um on chromi as we've seen chromium as well uh wor about default um is only permitted if the secure flag cooking so if team note um on LAX there are two conditions in which the browser will send c p on cross the first this uses the Gap method any method it's not going to happen and number two if there's top level navigation in other
words the user click something and then go to a website in that case the same will um and STS the most STS um the browser will not you're not going to have a fun time trying to exp probility in this case this is essentially partly a response to regulatory cookies and tracking so cookies as well just general so how can we avoid being we've seen all of these controls um but how can we avoid them so um the first thing is and the first thing most commonly see is not checking out the application atud resp Dynamic payloads we have this straight from Miss's documentation when responding to a credential request the server must specify origin in the value of an header
instead of specify so if you're not getting a dynamically generated origin back from the surface origin in your in your request if it's not being dynamically generated more issue um because it's that's just more um and so essentially what thats like this so regardless of what you're sending your origin just and two and three not checking that actually reation so PHP is not interesting resour Forest some serious issues with information disclosure um and also not testing out we saw before not only need a live browser especially when to send this to a victim but also different browsers will differently by default um and you need to account for that so when we're reporting we have to account for the
fact for what kind of uses are actually access site if it's the internet or environment thenation might feasibly be Comm one for instance so finales um I mention partition for um essentially this is a new is attribute or that can be set on cookies um essentially it adds what's called Partition key to our cookies um and what it means that when you have an embedded site within your own website um it's slopping it's preventing keep being accessed origin another when that website is also um so as summary don't be by that if you happen for there's no sh in it uh but uh try not to go down the around hle there um and also make sure your have is
dynamically generated um double check what the credentials are um so if You' got a bar token for instance or if you're if what you're testing is a Sone API that's service machine account but isn't going to be accessed in the browser um so make sure that you context system that you are testing um and always check as well you for your concept so You' Had Me Drown on so L um you can find me in one face and one face only and that's which is a little bit sad um I put the full link there um as if anybody's G I just look up kg find me hopefully um and uh yeah thank you all for
listening and any [Music]
[Music]
questions yeah if you have any um questions or just wish web security I will point you to knows it far better than I do while I'm long but yeah thank you for listening and um see you throughout the rest of the day