An In-Depth Analysis Of Vulnerabilities In Cisco VoIP Phones
Show transcript [en]
Over to you. >> Good morning everybody. Welcome to my talk. This is your your phone spying on you. My name is Bash Bash. That's where I live. Yeah. So over the past two decades I was doing IT security. Uh in the past 15 years I focused my um um I focus on research and consultancy mainly. worked for multiple big companies you might know SEC group that's where we were colleagues and one of them um I started to learn assembly uh which made me a software reverse engineer a long time ago when I was 13 years old uh and yeah I usually do these talks around the globe this is my hobby I went to the US couple of times been to Europe
more than a couple of times and even to the region Philippines also Australia and Singapore so far. Um, I believe I'm a friendly guy. So, if you like, just find me after the talk. I'm happy to chat. Here are a few ice breakers that you can use on me. I love to travel. I've been to more than 75 countries so far. Uh, I love to do IT security. That's why we are here. So, I think that's a really good fitting topic. And also, I like to do sports like kayaking, cycling, and hiking as well. and other stuff too. Uh you can find me on Twitter and LinkedIn. Please uh send me a request if you like or follow me. And
you can do the same to my company Practic Kaying. Last year I kayak the tennis uh in length from source to u to Greenwich. It was about 200 m 300 km to 10 days. I loved it. It gave me a really different perspective of the city. Uh it's really nice to see from the from the from the river. A little bit about my company. I founded Montto information security two years ago. Um it's a boutique consultancy company. We do all kind of offensive disability uh services traditional pentesting network web cloud source code and uh config reviews. Uh one of the big things that we do specialized trainings. We do uh I do actually software reverse engineering
training. If you want to learn it from scratch or you already have some knowledge then I can teach you in a few days. Do I can get you to intermediate or advance level uh depends on what you like. Um yeah and also we do reverse engineering and that's this talk about really. So this uh this talk is is the result of a joint effort with the Davinc from Belgium. Uh I was doing the reverse engineering on the software side. They were doing the hardware bits and I didn't have the skills then. Uh that's changed. So we had Leu who removed this chip really easily read off the content that was the firmware of the uh Cisco phone that we analyzed.
So at that point we had three different Cisco IP phones in scope. One was the 6851. The second is 7841 and 8861. If you don't know these numbers, don't worry about it. These are just like uh versions of different phones but they are using the same firmware. So we download the firmware from the chip. We downloaded the same stock image from the Cisco official website. So we had two different firmwares same firmwares but the running firmware that we dumped had the variables the the initialized data everything else. So it was a little bit more useful. And sometimes you find uh the the stock firmware encrypted. So that's not a nice way to start uh a research.
Depends on. So uh we know that these devices are really well known. These are from Cisco and I seen these devices including that one around different offices. Probably seen these before. It's all around London city um or or they call it or full of all of UK um Europe and the whole world basically every financial institution use these devices at least at one point uh and government offices too. So I had the initial mindset which was totally wrong that this is a Cisco product or these are Cisco products so I'm not going to find anything. This is a huge giant that uh that must be secure and um these devices since these are widespread they are used everywhere
these must have been tested several times by quite a few people. So my baseline was and I'm going to talk about this a little bit more at the end of the presentation. My mindset was totally different back then uh probably still effective. I thought that I I won't be able to find anything at all because it was V secure, right? Well, these are the phones that we tested. This is the 8161. Hands up if you've seen this before or similar to this. There you go. I'm pretty sure you've seen this because it was front of you all the time all of these presentations. And this one is the last one 6851. So these are different series but the all
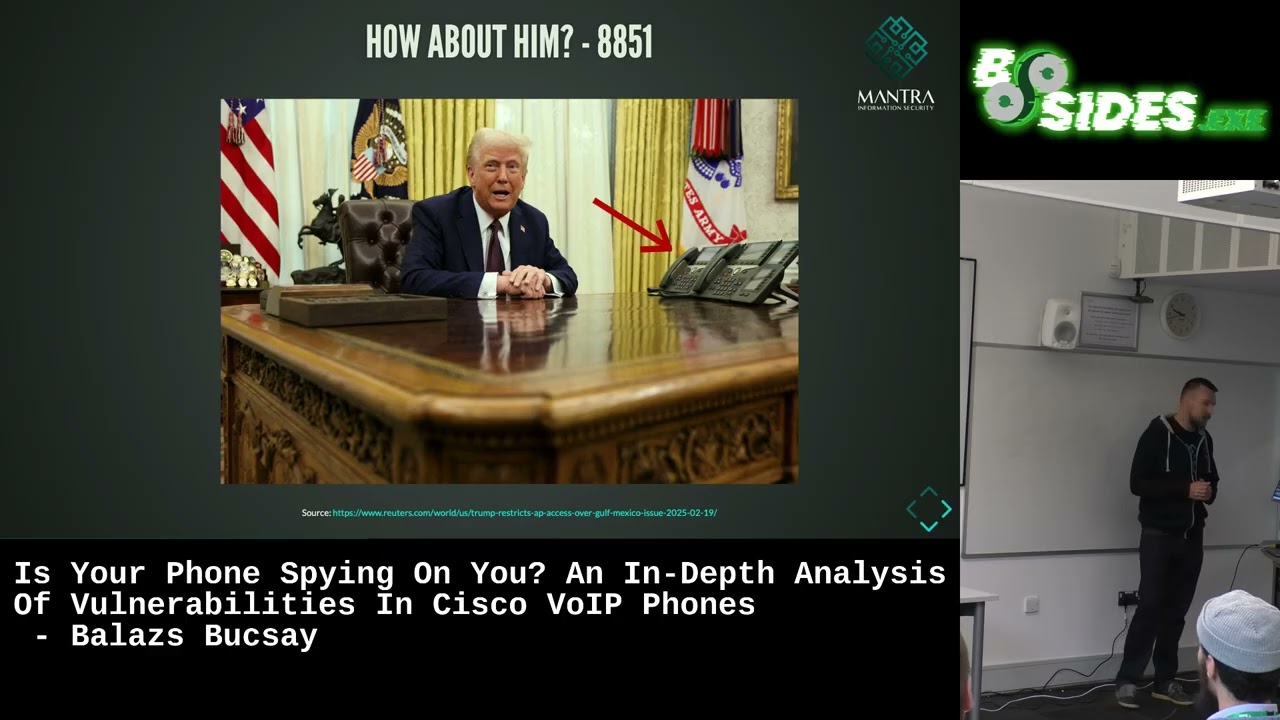
of these three series are using the same firmware. So the hardware is a little bit different. You can see that some has uh like colored LCDs others don't. Uh there are slight differences as well but basically they use the same firmware so the function is kind of the same. There's a different series 8851 which wasn't tested by us but this this series is using the same firmware and guess what do you know this guy by then right those two phones there are 8851 might be using the same firmware probably not that's a big question there and good news is Biden Trump is using the same devices uh as as Biden this is from this picture
is from January. So, it's quite quite recent. Uh there are slight differences to these devices. I'm not going to lie. There's a key expansion unit at the back at the back of these devices. So, you can uh generate cryptographically secure random numbers and that helps with encryption. So, that's a big plus. But usually those are not coming with the device. So, the reality was quite different. I couldn't be more wrong. in five to 10 days we found I found quite a few issues. Um these are the three that got CVS assigned right so let's go through them the first one first issue that I found this wasn't even assigned a CV it's an authenticated issue if you go
to this URL/log/ messages then you can get the vlog messages file if you know Linux if you know Linux uh Unixes Unixes then you know that that's one of the logs and you will find a lot of information in Yeah. So basically from fully blackbox testing uh dynamic testing we went to somewhat gray box because we got a lot of dynamic information from the logs including crashes. So if you manage to crash a process on the device somehow remotely you will find the debugger output uh the stack traces the registers the the the stack everything in the logs. So that that's a gold mine for researchers. I really appreciate that. Um, the other one, the first that got CV as a sign was
a denial of service. Basically, an authenticated buffer overflow which we couldn't exploit for some reason. But what you could do with it, you could crash that process as many times as you like remotely, right? And the device, these devices have a watchdog service in in them. And if something crashes more than three to five times, it's going to reboot the device. So what you can do, you can send the same request, the same payload over and over again, and you can put the device in a reboot loop. So you can make it un unavailable for a long time or forever. There's another buffer overflow. Obviously, this is unauthenticated. What else? Uh this is basically not a mon buffer overflow.
It's it's for BSS. VSSs is a segment in um in ELF binaries where you store the initialized data. If you store any sensitive data there and you can override you might be able to control the flow of the process. Uh what we man what I managed to do is basically I managed to override some of the data that store the proxy details. So any concept uh any any HTTP requests that were sent after that uh went through my proxy so I could intercept those codes but it was quite limited. The other thing that you could do it was basically the same stuff as before. You could create a process and more the multiple times you create a process it
rebooted the device. So you could put it into reboot loop and make it unavailable unusable at all. And the the biggest one I would say uh is the information leak. It's unauthenticated. What else? Of course it is. It's basically a feature of the device. Uh they just forgot to put authentication on it. You could start uh TCP dump. You could stop TCD TCP dump on it and you could download the PF file. If you don't know what DCP dump is, it's basically a tool in Linux or Unicus where you can intercept traffic on an interface or on all interfaces and you can dump it into a file. So any network traffic that goes on on those on those interfaces, you can
capture it and you can store it in a file. Well, these devices are IP phones, right? So what do you do with them? Um, you make phone calls. So if you can capture those, you might be able to replay those as well. So I think it's a critical issue. Cisco disagrees with me, but that's fine. So I um I put together a demo for you just for the show. I hope it's going to work. So let's just raise to the demo gods. I wrote a few scripts so you don't need to uh struggle too much understanding this. So basically I'm going to start capturing [Music] the traffic. I need a volunteer who could pick the
photo up please. You can get a really cool cool sticker in exchange. Anybody please? Thank you. [Music] Hello. Can I tell you a joke about UDP? >> Yeah, you wouldn't get it. Thanks. That's my Thank you so much. So, that was it. And I'm going to start the capture and download the file. If everything went right. Yeah, there's a piece called pcap here. It's wireshark probably know it. And this is the stream. This is basically what happens. One of this is probably you. This This might be me there and I can replay it. So, let's see. >> Hello. Can I play you? >> Get it. >> There's a little bit of loss for some reason. I'm not sure why, but yeah, that
was the demo. So lesson learned basically the few next few slides is going to be about that that was the Cisco de um I thought that these I won't find any of these issues because it's going to be Cisco and it's going to be a well respected company but I was quite wrong about that. So um there are millions of devices out there. I'm pretty sure that um basically all bigger financial institutions have these devices. Um I reported these these issues to Cisco in 2023 I think end of the year. They managed to fix it in a few months maybe five. They released the issue the the the patches in May 1st of May 2024.
U but the thing is there's no OT or any automatic way to patch them. So I'm pretty sure that most of these devices are still vulnerable on the network. So I just want to remind you that these issues were found in 5 to 10 days in total. So I guess this is just the tip of the iceberg. If you want to go find some more, I'm pretty sure you can do that. So I was really surprised about this. I told you that I am doing research for the past 15 years and still I'm finding these issues and I'm really surprised. So basically, here are a few questions that I'm going to to ask, but I'm not going to answer because I don't
know the answer to that. I'm just really surprised that uh I I don't really believe I can't really believe that these these issues weren't find before, weren't found before, right? So these are really trivial to find. If it wasn't me, it should have been somebody else. And also there is NSA. We know about them. Uh they do all kind of research. Uh, I'm I I would be really surprised if they haven't found it yet. And still the president of the United States using these devices. They say they use a different firmware. Uh, which might be true. I assume it's true. But if they know about these issues, they remove these issues. They left them in the
firmware. So, you know, it's it's really dodgy for me. I'm not sure whether it's ignorance, incompetence, or something else. I don't know the answer to this but also another question that it raises that what does it say about the state of the security in embedded devices right so if if you can find these issues in any big vendor embedded devices what could be out there so yeah I won't be able to tell you about the the answers unfortunately but if you have an idea or you want to chat about it I I'm up for it so just find me after the presentation and I can give you a few cool stickers as well if you
like. So yeah, uh I wanted to p my presentation a little bit about research. Um I hope you're okay with that. So I told you that um basically I had this limited mindset as a researcher that I'm not going to find anything and it wasn't easy to break through that. Uh I just want to ensure you that if you want to do research that's an easy thing to do. You don't really need knowledge to do that. You don't really need uh experience to do that. You only need uh mentality. You need to be curious about it. Right? So um if you are more curious than fearful then you are you are already a researcher. So you can go for it and you
can do your own things. Just because you do research it doesn't have to be super valuable. It doesn't have to be groundbreaking. you just go for it and anything that you anything new that you learn and you are going to learn a lot of new things is going to be a big value to yourself and that's what it should mean uh that's what it should u mean to you so that why you should do research really not because of the fame or anything else uh I'm not going to lie to you it's not easy because you know it's a research doesn't start with guarantees guaranteed outcomes so basically you get and I won't talk these numbers but you
get like 95% failures and 5% success. So every time you try something new, it's almost guaranteed that you are going to fail and it's not going to work out at all. Um hands up if you tried bug bounty before just a full few of you. So probably have you heard about bug bounties? Yeah, most of you. Okay. So, basically we we kind of know that you can get paid really well with P bounties and uh we see those tweets, we see those people who earn millions would get P bounty. So, why can't we do that? And I think that's that's one of the reasons why because we don't have the researcher mindset. It's not like that they they
everything that they find uh get them paid, they are a little bit more successful or or or something like that. So if you tried bug bounty before you know the grind when you try to find issues and you won't find issues in 5 days in 10 days or whatever you might give up and you say that okay I'm not going to do that but it might be that on the sixth or 11th day you would find something there is impostor impostor syndrome as well I guess everybody has that to a certain level um including me it just you know it depends on how you manage it manage it if you give up everything because you have that that's
not a good way to do it. I understand why you do it, but probably you should work on that. The burnout is is quite real because if you have so many failures, you know, you will give up at some point. It's not that easy to do it. Um the reason why researchers do this is the the uh emotional highs. So after doing 10 days of research and finding nothing for example, you might find something big and then that gives you a really high emotional high, right? And that's that's your achievement. That's that's something that uh that's something that drives you. Just a few examples in this re research that I did in uh in the Cisco on the
Cisco devices, I found a few application services crashing on the device, which was a really good feeling. at least I found something but then later I had to realize that these are not exploitable or I can't exploit it because I don't have the tool set to do it. Sometimes when you do bug bounty for example you find a critical risk you submit the bug uh you wait for the big bucks to arrive or something like that. Uh maybe it's not about the money for you but you are really proud of you that you found something and they call back to you that they ignore they either ignore your rejects your finding or they say it's
complicated somebody else found it and you don't get paid you don't get the the appreciation that you expected. So these are the emotional highs and emotional lows which comes with research and it's not easy to handle. I already told you about the assumptions that I had about the Cisco devices. Basically uh I have these I have these all the time. I always think that I'm not going to find anything because these devices are tested by numer numerous uh researchers and internal teams and whatsoever. And I figure out that that's not always the case. Sometimes I think that okay this is a really easy test case that to to to test really trivial one so I'm just
going to skip that because you know this can't be a bug it must be patched. it must be must be fixed or whatever and it turns out they didn't didn't touch it or they didn't do anything with it or they just made a mistake by patching it. So whenever you have these toads just ignore them and do your best. Also there is this there is this uh other one trusted products or services. You might think that this is a trusted vendor like Cisco uh but you need to ask the question is it trusted by who? Right? Is it trusted by what why why is it trusted at all? Because I would say Cisco is a
trusted vendor but you can see what kind of issues they have. And um the last thing about this one assumptions just because it's a big brand big brand doesn't mean it's secure. So keep that in mind. I this is not my first presentation about research and my findings and uh sometimes I find that this is what people see right you have the research on the left hand side as the starting point and you have the results on the right hand side and because it's two different points uh people just connect it with a straight line but this is not how it works this is how it works really you do your research you have the first idea
you do different variations of it and you fail you have your second idea and you fail multiple times third, fourth, fifth idea and out of 100 or 20 different ideas you find one result, one whatever it is and this is how it looks like and this is just the distortion of reality what people think it looks like. So I'm just giving you this information whenever you hear something in the news that some researcher found this, some researcher found that and it's a trivial issue like this one. These are really trivial issues, right? But to get there, you have multiple steps that you need to go through. It's not it's not always that easy to find these issues even
though the bugs are trivial. Um if you have people around you or if you are researcher and you need support, these are the things that you should expect from others. I would say um just because something looks easy, it doesn't mean it's easy. So that's something that you you might want to think about. Sometimes I feel jealous when I see these articles or presentations. Uh but I need to remind myself that jealousy won't move me forward or drive me at all. So I need to be humble and I need to learn more. Uh that's the only thing that that will drive me forward. And feedback is really crucial I would say. So if you find something really cool
maybe give positive research. If you think you can improve on that, constructive research, constructive feedback is is going to help because you know the researcher can learn from that. Um, and there is the responsibility as I mentioned I reported these issues to Cisco which was a good call because they fix them. But sometimes you need to think about debugs who is going to be affected by them. Some vendors don't like to to fix issues. Some vendors like to ignore reports. Uh but you still have the responsibility. Probably it's up to the vendor because they just want to save their assets. They just want to save money. They want to save their reputation. So they won't fix it or they
don't um uh they will just ignore you. But you have a responsibility to to the clients. You might be a client to Cisco. Somebody else is definitely a client of Cisco or to the end users. So you might want to report it in different ways depending on who you feel um responsible for. So there are different respons responsibility and there are different disclosure techniques. There's the full um sorry responsible disclosure. That's what I did. I reported the bugs to Cisco. They fixed it in a few months and these were all reported and and patched. There's full disclosure. Sometimes you need to do that when the um when the vendor is ignorant or they just don't
want to comply. So you need to push uh your truth through uh by saving others uh from their ignorance. non-disclosure. When you're fed up with these these policies and processes and ignorant vendors, you might want to keep the bugs to yourself. And obviously there's commercial disclosure like Bounty and Zero Day Brokers, but that requires a different conversation. So yeah, closing notes, my message is if you do research, never doubt yourself. Don't build up imaginary bind boundaries because that's not going to help you at all. And um one really important thing here is stop reaching up to others. Comparison is the tea for joy. So if you compare yourself to somebody else that's not going to help
you because there will be always somebody that is better than you. Basically you won't be able to be to be the best of anything. Even though that doesn't doesn't sound nice. And the last really last thought is that you should make time if you want to do research or if you want to learn anything new basically you should make time for it. You should waste that time on on your research because that makes you learn about stuff. Maybe it's a waste of time but after that if you learn something new you won't find it as a waste. So that was it. Thank you so much for being here. If you have any questions, happy to hear.
>> Question on the phones. One of said do you have to have the XML service enabled? Can you ask what it does and how you enable it on the phones? >> Okay, so the XML service by default you don't need to have any kind of privileges. You can just log in and enable. if if it's set up uh properly then you need admin privileges to to do that and with the XML service and actually that was by default on previously in previous device previous firmware uh you can do a lot of um remote management uh through that service. So basically you can I I think you can update the um the firmware remotely. You can make you
can change the background. You can change text. You can add contacts to the device. I'm not entirely sure. It's it's a long list and it was a long time when I looked into it, but there's quite a few things that you can do. That's good. Um you went through the CVS, but you said you still discuss Cisco TCP function. Most companies that I've seen will deploy phones where it's one Ethernet PoE to the desk plug into the phone laptop or desktop is then teed off the phone colle. >> Yeah. >> So if it's deployed in that mode your ability to TCP done on the phone actually capture any traffic coming from that attached device. I think the um the
default mode how you run this is uh capturing the traffic on all interfaces. So, it's going to be the PC, it's going to be the phone, uh, everything basically that is pumped into. And the follow question with the TCP dump feature that's in there, is it might not be fine on the Unix machine where I can start tracking say I want to see this destination host ID. I'm thinking now of uh I just want traffic to the domain control or something like that if it's on a >> Yeah. So the the the feature is limited. Uh I think you can specify the interface. By default it's all interfaces and that's it. You can't specify anything else. But when you do
the dump, you download it and you can filter it in by whatever you use. >> Okay. Any other questions? So there special devices I understand. Do you have to know whe [Music] >> I mean uh if they do a version check on the firmware remotely they could do it they might do it >> but yeah >> but there was not like disclosure >> sorry there was no version disclosure when you check sorry >> there was no version disclosure unauthenticated that was possible. >> Yeah, I think you can do that. So I think the possibility is there but I'm not sure whether they implemented those products. I think you can do it. >> There was one more question.
>> Yeah. Yeah. So you took the packet capture and you were able to like get the audio. >> Yes. Would I be correct in assuming that that means these phones just transmits employed [Music] in? >> Yeah. So this so this is not just a phone. This is a computer, right? You can configure it in so many ways and voice protocols are really complex. My point is by default it's going this is the default mode. So it's unencrypted and that's a really good way to demo it. Obviously, you can configure it more securely. Uh you can configure encryption on it and that's why you have the key expansion unit on the on the devices in the overall office. So you
can do that and that's going to be more secure. But the question my question is and I understand it was a good question but my question is that do you want a secure device where you can't do TC3 dump even though if it's encrypted or you want to have encryption and DC3 dump together? So you know there are different layers in security. I think there are two different layers here. Not having TCP dump on the device and also having encryption enabled. So yeah you can you can enable encryption just a bit more. Um I'm unaware of any um external entity PT like PT or wherever you provide your mobile phones that does real time streaming.
companies set it up internally if they want to. You can always go to where you hand off to the PCT session controller and inside you can have it encrypted with this bit out there wire very easily and even on your home BC home if you can phone into it now you can do the same. >> Thank you. Any other questions? Yeah, even if you have questions or you you know you come up with it later, I will be around for a full day even in the uh after party or whatever it is and please find me. Thank you so much.