Opening the Black Box – Software Security from a Hardware Perspective

Show original YouTube description
Show transcript [en]
hi hi besides I have to make the customary apology to everyone for being to talk between you and beer so I'm going to try not to make this too long yeah I'm going to be doing a talk on software security but from a perspective of hardware and so I am a full ta electrical engineering student and which is the reason that I've yeah I'm more interested in getting my hands dirty and then finding shells fired traditional path so traditional security and what we are familiar with mostly involves a network based attacks against computers or desktop machines or servers x86 hardware I'm broadly speaking obviously this required well this is when you have no physical access to the machine and so
it's looking for vulnerabilities for services that are open to exploits and of course if you have the hardware name with the screen and the keyboard then you get this game over and whatever security you had on your hardware you can consider void and yeah it's earned and at the end of that so hardware extends beyond computers and servers to things like infrastructure so Reuters firewalls switches mostly just things that connect all the devices that you care about so much together and carry all of the sensitive important information and so what are the vulnerability is here well on the inside of most of these is Linux which is something we're quite familiar with now what's nice about Hardware recently and
more recently is that a lot of embedded devices are running Linux and well sometimes it's a bit overkill and it's the easiest way to get a product to market quickly you can take a system it's cheap it's it's the cheapest quickest way to get a product to market is to use something with embedded links so obviously that extends beyond networking equipment to things like IP cameras when a storage devices and these devices also run Linux and are also on the network but are often disregarded not necessarily in the corporate environment but in your home for example so getting in let's assume that all the network services are perfectly secure and not open to vulnerabilities which is very seldom the
case but let's assume that is the case there is no keyboard or display or any obvious human interface to get into the device so how do we access it how do we exploit it and take advantage so a lot of hardware devices have a serial port which is a thing we're used to well we know from older computers when you know used to use a serial board to connect your mouse or to get a terminal into a switch or something other and often these terminals expose a shell sometimes the shell is unauthenticated sometimes the shell has root privileges and then you can essentially do whatever you want some time well usually these devices also have a bootloader which basically
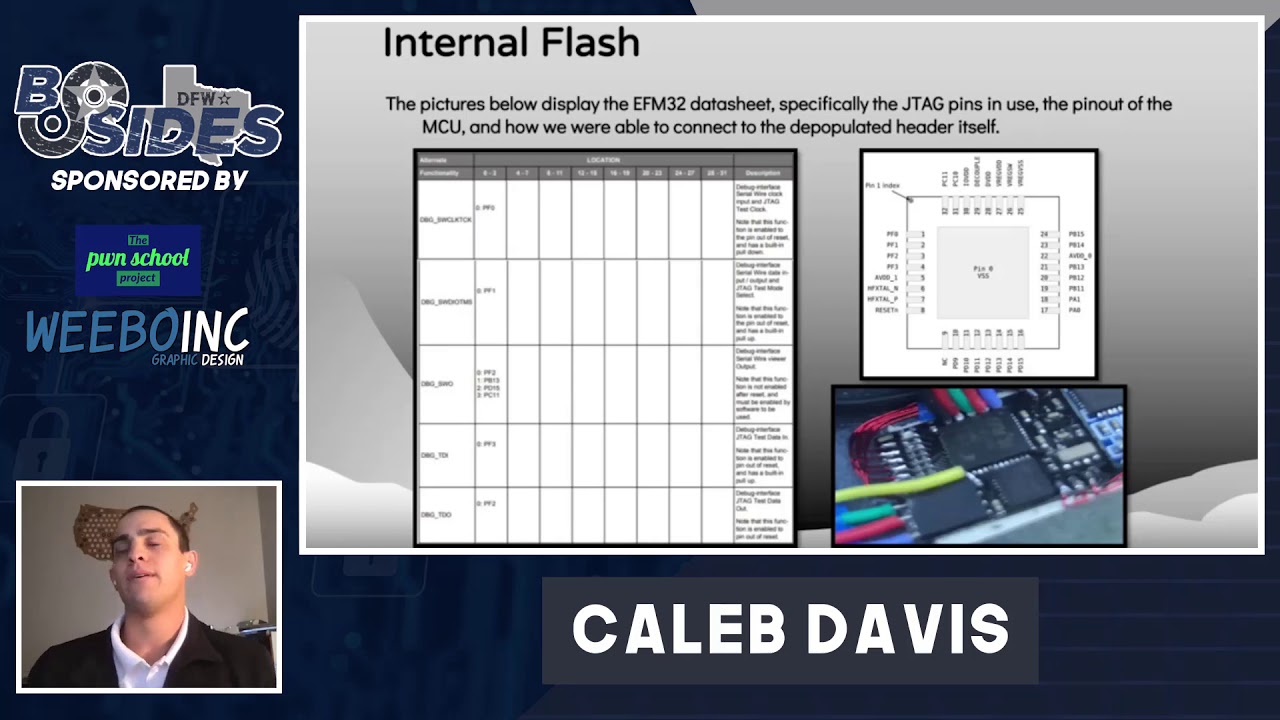
handles the bruising of the whatever firmware is loaded onto the device but if you stop the bootloader then you can control the device like that and and from there you can dump the firmware over over the network and once you have the firmware it's essentially the same taking a hard drive out of the desktop computer and then again you have access and you can do what you want now that option is to connect directly to the devices firmware which again is the equivalent of taking a hard drive out and so if there is no serial port or the boot loaders and allows us I've also encountered cases where the bootloader is a generic thing we
allows all kinds of things to happen over an Ethernet port which the device doesn't have and so obviously in that case the bootloader is useless so if you can connect directly to the flash chip with a programmer you can buy from six dollars in ebay you can again dump the whole contents of the firmware and you have yep you can access the device of course this doesn't just mean that you have the firmware it means you have the firmware and you can change it and you can put it back which opens a whole bunch of other interesting possibilities and just a disclaimer this is not specific to this brand but it's essentially a white label product from
China which is sold under a whole bunch of different brand names and a fellow security enthusiast sent me one of these cameras and say there's some weird network traffic but I can't get into the device so maybe you can do hard way of magic and tell me what's going on so I opened up the device it did have a serial port which you yeah get to know how to find and the shell that it presented me with was running Linux 2.6 and the shell didn't help me because there was I didn't have credentials and and it was turned out later I could find them but I didn't look hard enough sir I went down other avenues that I was more
excited to try so what I ended up doing is stopping it in the bootloader copying the contents of the entire flash which is usually about four eight megabytes into the RAM which is usually considerably bigger and not not much of it is used at that point and then transferring it to my computer over the network port once I done that I had the firmware image so I decompress it sent the same friend the et Cie password an ett shadow files which he cracked and then gave me the credentials then my cereal board was useful because I could log in and then I could do whatever I wanted and one of the nice things is he
couldn't find the root password but he did find the admin password which was limited in some ways but because they booked the permissions and I just checked which scripts were running and had started matically on boot found the ones that were running as root and because the permissions were broken I could edit these files as admin so I there was some basic utilities like NC sir i just added a line that opened a reverse shell to my machine and restarted the machine and suddenly I had a reverse root shell on my desktop so a lot of the stuff is I mean it was nothing on the network that allowed me to get into the camera
assuming there were no credentials there wasn't really any way to get in but using some hardware techniques I was able to get the password and get access to the device so like I said the things you can do from here once you have the firmware you can either extract files informations contain the firmware image is obviously the line X firmware and but can also contain user data like Wi-Fi passwords and other interesting information depending on what device you're accessing and you can also modify the file system so you can add binaries and you can replace the version of busy box with something else you can add netcat you could add take your route and add iodine or p title and add
capabilities to that and you can also boot an entirely different firmware image most brutal odors have the option to boot from tftp or over network so you could try out completely different images without actually making any changes to the device and and again like I had with the IP camera you could add a backdoor so have it open reverse shell to a specific IP if it exists and so why are we doing this one of the reasons obviously is research in security and investigating devices and learning and I've learned a lot of stuff indirectly from doing these things not just so much about what I'm finding but the process and that I go through to find this
information and also adding adding functionality like I said adding different boundaries to a Rooter to make it do other things that it's not supposed to changing the purpose entirely which I've also done am and of course just for fun if it's something that makes you excited and on so there's a blog by a car mableton guy's name is I think it's Chris but I could be wrong and he is an embedded security expert some of you may recognize this website this is a list of some blog post titles that he has so there was in May 2014 hacking the DSP w 2 and 5 smart plug the next blog post was hacking it again the person after
that was hacking it again again what if I again again again I think he stopped with that after that then there was this one which was a newer model obviously much later on crutches followed shortly after when they fixed the problem that he used to hack it was followed by this post because for the most part vendors don't seem to care that much about security on embedded hardware and I sometimes feel like not enough people are looking at it but there are some gaping holes and in some of it and a lot of the time it's not even yeah it's over the network it's using traditional techniques to find these things and what this guide tends to do is tear the
firmware apart and investigate what causes evolving road season why it's a problem and he grows quite deep into it and disassembles binaries and does exciting things like that this was something I did I'm in light of well with the intention of changing the purpose completely that is called a seagate duck star and it's a device that's used for nath storage so you put your hard drive your seagate hard drive in it where that logic analyzer is not supposed to be and it provides access to your data over the cloud and but you know it's your own data and you have the storage locally so also over your network it wasn't a great product and kind of failed commercially and sellers
supplier started selling it at a loss but it runs debian so once it's running debian it's essentially an errand box raspberry pi kind of thing and with gigabit ethernet which is quite attractive for a bunch of stuff and i ended up using it with a logic analyzer for doing some other stuff which is completely not what this is for and at the moment it's running a media server and a web server and a proxy and something else which it handles quite well but it was never designed to be used for that and again that's playing with bootloader thanks different firmware images another very interesting thing that I found essentially a USB device when it enumerates the host controller asks it
for its USB descriptors so what she did was ask assets words used be descriptors but ask for a ridiculous amounts of well a huge size response which it didn't give because it was carted properly so this wasn't a Wacom tablet so using some hardware techniques called glitching basically got the guts cycle precise control and glitch the power so that this process amidst an instructional something along those lines and basically didn't validate and the request and ended up splitting the entire contents of the flash memory out in response to a request for a device to scripture so they managed to get the entire firmware off this chip by asking what are you and telling it to tell you
just keep talking like go on so obviously the point of increments in memory until you have the entire image and so we're here from here and this is made me do some crazy things like get excited about this and it's not exciting at face value because you can share a Wi-Fi hotspot and share storage and and it's got a battery in it but what I see it as is a small platform device running Linux with a battery a USB port and an SD card slot and a wireless radio which if I can run some generic version of Linux and I can turn it into all kinds of things it can be a tour box it
can be a download or literally anything that you can do with the Linux toolchain run on a limited platform like that so it's made me start doing things like picking up pieces of hardware like this and trying to make it do something entirely different and what's nice is if you're able to get access to the firmware directly you can brick it completely and you can just write it back again so I have broken this irreparably at least twice I have so yeah that's what it's ended up making me do and yeah so that's just a small window into what I do and what gets me excited and yeah my taken security from hardware perspective but where
perspective but