The Perfect Place For A Backdoor: Exploiting Virgin Media's Hub 3.0
Show transcript [en]
so a few words about me I reared for secu as you can see from the slides I have a managing security consultant and of his research lead in the letterhead of his op SEC I have more than 10 years of experience in the offensive security you can find me on Twitter on there X or e IDE IP and of course on England as well I have a few strictly technical certificates I like to do research and other stuff these are listed on the slide and I'm a frequent speaker of other conferences as well I was fortunate to go around the birds in the last few years and then give presentations about different topics all around the globe today I'm going to talk
about this device which might be familiar to you is his from Virgin Media this is the hub 3 or Super Hub 3 this is the latest the lost version of these devices as far as I know if you have a subscription with them for both pant most probably you will get or you already got this device hence ends up at least who has this device yeah many of you that's great now so I moved to the UK three years ago in 2016 we moved into your flats and we decided to get virtual media and actually we are pretty you know that service is really good so we had not no issues but because it was a
new country for me I didn't know anybody I was four also the time afterward and we can so I had to do something so what did I do I started to play around this this smaller and after one day I found one remote command execution bug so this is how this really started in January 2017 I asked for research time from NCC it was granted by by Matt Lewis the research director I got two weeks and of the first week I managed to discover more than enough five issues and then I break the device so I had to stop it and we had to buy some some new devices from eBay so it's really strange at least it was really
strange for me basically if you go on eBay you can buy the same exit device I bought sometimes so we both like six of them and I continued my research this is a very well known device many many people are using it if you go on Wikipedia and read about Virgin Media you will find that as of end of December 2012 they had almost 5 million customers cable customers and 4.2 million customers and broadband internet says at that time those those customers didn't have this device but since then because it's 2019 as you know many met many of the customers we're upgrading to let's say or new customers already you know neighbor even given this device so you
or take I think there are millions there were millions of of course the verse in danger when I discover this issue and it was it was a long journey you will see why so I had in her duty the the penetration testing the device I started to I started discovering so I scan the device externally and it came back with nothing so everything is theater nothing is exposed to the internet which is abusing you can expose the WI the administration interface which you shouldn't do ever is don't do it that's not a good idea but internally you will find three different ports port 80 and 443 for Twi over HTTP and HTTPS and port 5000 which
is a UPnP date I tried to you to break dominio p.m. PD but I didn't succeed so that's what that looks fine so I started to play around the the port 80 and 443 which is basically the same so my goal was to to easily take over device execute any kind of comments and codes on it totally own it which I later did but when I said the goal I have to figure out how to do this the best way to start if you want to do the same on the different devices or maybe the same device if you want to do this you should find those injection those those functionalities on D on the web UI on
the on the device which are really close to the OS level for example if you configure the biomass there you can set the SSID the the post phrase and so on if you do Mac filtering then you can set different backs or do port forwarding you can set different IPs and ports and so on and so on those are usually executing different different OS level commands in the background ping and traceroute those are the perfect example also these devices are owned through these these functionalities that's how it is as well basically when you use the ping and traceroute they didn't implement the their own thing and trace within the binaries they just use the external pink and trace through binaries
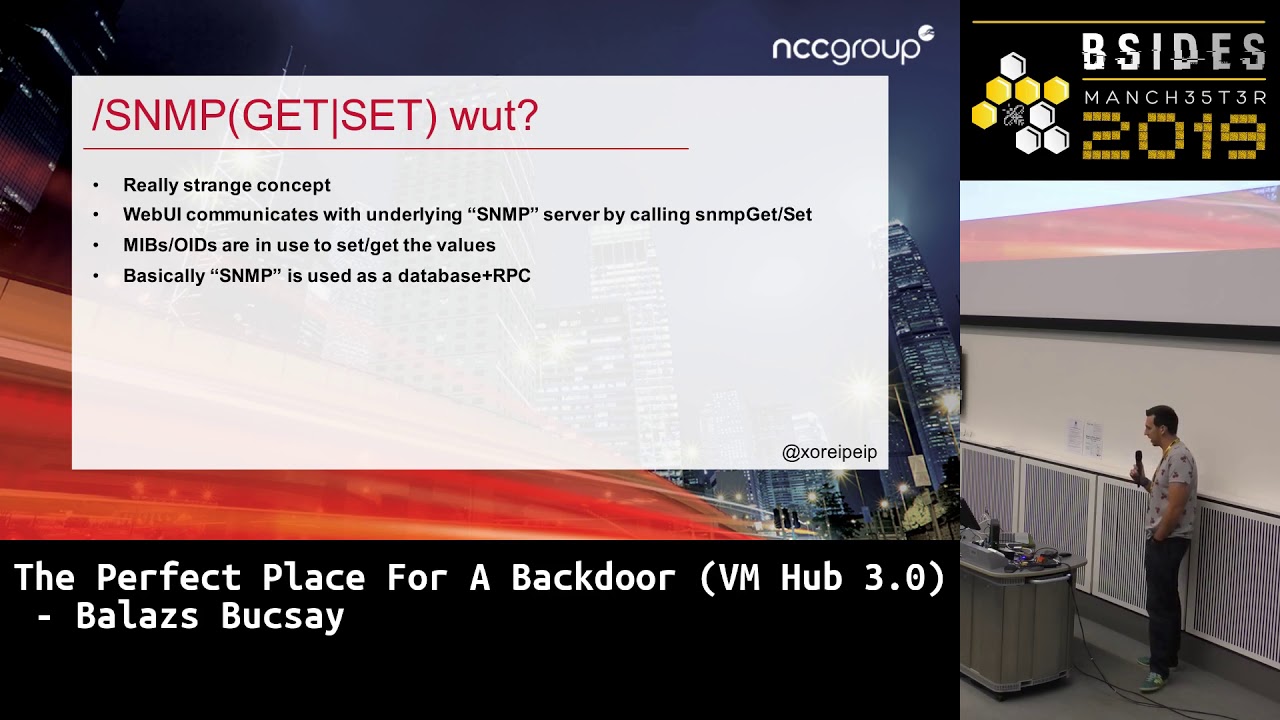
on the only on the operating system so I started to play around with those I set up a verb proxied everything's here and what I saw were these requests and as you can see it says all of them are get requests and SNMP gets SNMP sets this the name of the endpoint door or the function which is really strange because if you know as an MP that's totally different for the foe than HTTP and one has nothing to do with the other so I was really surprised at the WI sending the browser is sending so many of these requests that the verb could attend to it properly after a while so it was very strange so I started to look
into this was what's this and it turns out the that the device the the web server using SNMP let's say to to set the configuration to get the configuration and display on the Indy browser and to execute different commands as well different functional section so as you can see here in the indicate requests in this example there is SNMP self there is an OID orbit which we know from from SNMP there is an equal sign a value which is one semi call 66 which turns out that's the type of the value which I don't know in this case was that but anyways after that there is the other score an underscore which is the aunty CSRF token which is kind of
dodgy but it kind of wrote this wrong so then that's kind of fine and one more thing that you need to see is the commercial cookie which is a basic stiff where encoded string that's a Jesus drink it's towards some kind of session identifier like a session ID and a few other things as well so it's really strange because SNMP the difference different concepts they mix it up for something so I never seen anything like this I don't know why they did it but that was that was a choice that they made with this through HTTP good the device was able to sense different values get different values and most importantly execute functionalities from the web server web service binary for
example when you use trace rules these are the difference as a hug teammates or who IDs that had to be set the first one the zero one was set to 60 and the path was to the type 2 is e pattern that's what it means I guess that was the most T TR for the command ii o ID which was sets that was the hostname the type is 4 which is train industries that the third one was 31 whatever and the support one was set to 16 not 16 to another number these are integers at the end the seventh otto that was basically the execution of the of the comment if you sent as value if
you said that maybe to you to a value that is will exactly the function in the binary or marina library so i managed to do the most common execution I got the binaries I got the libraries I started to reverse-engineer them I use them either and as you can see this is using arm so when you do this kind of remote command execution once you should look for strings stretched string injection points first because if you are trying to try if you try to play it with integers there is a higher chance T to fail because if it is early easy to validate please do sometimes because those are just numbers it's not the same
for Strings because in some cases you tease you need special characters it's harder to implement whether it's harder to check whether this trick is wallet in that in that scenario or even it sometimes we do invite listing sometimes you do black listing it depends on the use case but is it's harder to do in general than that in integers so as you can see this assembly sleep ads basically execute space use commands first it's using a some printf that assembles the string that is to ask placeholders in the string which are which are the strings that will be put in there the return value of the ESL freedom sari will be executed with the system cool in
DVD system function so based on this if you can control one of the s lease holders the percentage s disorders in the industry that you can do at common execution this is tax raise from Ida Pro I I not only this example but kind of D compile the code as well as you can see there are three different ways to execute traceroute whether it's ipv4 ipv6 or DNS which means in this case if it was the hostname it wasn't an IP then it goes into this return third branch and just using a some pretty tough again there are a few placeholders actually four placeholders a D or was lost mine and then it's using system on the string
so if you can if you can inject any of those placeholders and if you see the B comment the first arguments after the D string is a string again which is hard-coded so you can't really do anything with that the second one is the best destination maybe you will you are able to control that b28 that's again a variable so you might be able to do something with that but the fourth ones the last one the bar tab whatever that that's hard coded so you can't really do anything with that the question is can you do anything with the desk that we 28 and in this case you can because that one of that is basically
the host thing that you can control so you know this was working lee was command execution poverty it is kind quite easy to difficult how to exploit this if you have the source code or if you have the binaries and you can either is engineered I didn't have either of those so have to do it blindly when you do it blindly there are lots of different space where you can fail because you have no idea how it works so you need to do everything step by step baby steps and if you are lucky you have feedback from the device if you are not lucky and I wasn't you don't have any feedback so you need to find something out so even
if you mean jackets of all its commands you can't see the whole foot you have no idea whether it's drawn or not there are different ways to do exactly it coding commands in this scenario in this case you can use backticks pipes semicolons or in-line execution as listed on the slide duty but you can not be sure which which is going to be working for example the semicolon didn't didn't work because that was a restricted connected for some reason because there was no no feedback at all I had to figure out how a different way to do this so first I use reboot the first time I managed to reboot the device I was really happy
because I knew something is going on all right so I had to wait a few minutes because it's footings really slowly I had to reproduce everything with the different comma then I used pink piping my colleague hosts but I had a buyer short running and I was looking for ICMP pockets and when I got first wrench which I was really happy about it the other thing that you need to do all for sometimes the puff is not set properly so you need to go with full bus it also pass the binaries it kept for example if we are using think it can be honored with user bin or as being whatever it depends on the on the on the
operating system and how this is done in my case I couldn't use space it goes cold singular cold semi colon backslash either so I had to figure out the payload which was working properly with these distributions first of all you really need backslash backslash is for escaping of you come you can bypass them by using different kind of weights similar codes if he is an koenings you don't really need single quotes so that's fine semicolon I don't know if you remember but might you send the OID to the value and the end there was the type of dban you like to be for string - for integers for for strings and then there was a
separator in the India but you said the value this was a semicolon so I could have used semicolon this case because that was a separator in the loop that Center so I had to figure out something else but instead of stomach oh no you can use just mm and science or pipes double pipes rely on execution maybe backticks the different ways and if you don't have space you either use different whites my speech characters for the best ways to do to use the environment variable ifs which is basically a set of my space factors space tab later you like carriage back and these kind of things and if you use that it will understand the commonly
done space that was my one of my payloads that I sent in this case I used a wallet host name for no reason that just just just improve you how it's birds and then I used the you know execution where I connected back to my IP which was my column am I set up a listener all that was and then the tenant was running was was drawn on the other device it connected back to me redirected everything which was the content of the shadow file so the content of each other one was redirected into the socket so I got the content of the shadow file and everything else went deaf no after the remote command
execution was exploited I got like I mentioned I got all the binaries and libraries I started to reverse engineer everything that seems to be interesting and I found this it was because which wasn't working in this forever and I don't think it's working it works now but it was really interesting to see this so basically this is a back door user if you use ie an omni user that the possibilities either blank string or solder link and as far as I know southern link is a different vendor like a different ISP so maybe we don't be that isp there is a backdoor user which you can use of the wi with the password of suddenly this is
I found that through interests they all bought this device it is prime ministership media but really the device is not virtual media this is a distant event door which I can't mention it's for stupid reasons and basically the the salad is a survival device or different ISPs Virgin Media belongs the different group which is Liberty global I believe and the earthing global has many different ISPs all around Europe and I believe in the USS r-- a-- so defendants under defense they use the same device for different ISPs the box is different the logo of them the brand the configuration is different but the operating system and the binaries the firmware is kind of the same this is
basically they don't want to develop the same things for for different ISPs okay so looking through the the web UI you don't need the format for this I was looking through the JavaScript files I found a dog based exercise I would applicated Pompeii's XSS so if you look into the device and then you click on a link crafting link which can come from an email a fish fishing leave our in somebody else can send it to you some house if you click on this for example which is on the on the slide now if you load up the sec you are as you see Google test the trust stretch test GS and these will execute the
JavaScript from this file so if you logged in you click on this I can execute any kind of JavaScript in your browser I can see your cookies which are used for authentication as you remember from the first HTTP president I showed you and maybe I can log in or I can do stuff on with your browser my goal was on out unauthenticated it was common execution I had the authenticated remote command execution part part but I had to make it somehow to be authenticated so I had this don't be his XSS basically but that maybe the authentication you I wasn't exposed to the Internet's so even if I had the credentials I come from get
because I don't know the credentials and that it's not exposed to be that and maybe remember I mentioned the aunty CSRF tokens so those were protecting against against against the malicious web requests that are coming from a different website then I look to the de binary's again I was looking for the authentication part authorization form and I know I saw this snippet of code where you can see if the credential content which is basically the cookie the credential cookie if the content of that because XML configure each tab configure more toxin or figure you are logged in right otherwise it says status denied you are losing so that was really good stuff because it wasn't just an
authentication or authorization by passing these kids for the bypass the on the CSF tokens as well so I didn't have to eat to Gary about that so it was really cool because if I send these cookies I use maybe DG don't base XSS and then the remote command execution of them then I might be able to do some unauthenticated you most common tax evasion right the only thing is of course I don't know if you know course or search and resource sharing hands up if you do yeah off of you that's fine so basically long story short what course does if you have to defend that page is open in your browser one webpage cannot access the other's data right so
I cannot if you have BBC open and my valid malicious website that I control I cannot set cookies for poor or BBC I cannot get the cookies from the BBC site I cannot get the I cannot load or get any any content from the other tab from the other browser right so that's that's basically the cross-origin resource sharing in the dishwater measure of course it's a bigger data so I was thinking about this maybe I can use the don't base exercise with the cookies - cookies and execute these SNMP sets requests they vote me or somehow I can do this but there was the course of course which which was blocking me so I couldn't I couldn't do this from the
browser even if even if there was a volley session because somebody just configured the router and clicked on the website in the next 10 minutes or in the next 20 minutes I couldn't do it is because the the session timeout was quite low because like 5 or 10 minutes so the the on top window is very narrow so I had to I had to stop working on this I couldn't do an authenticated it what Robert executional death that's all the time I wanted to weaponize this the next points but I couldn't at least not in a way that I wanted so I did some other the device I started to look in the in the architecture you think you would
think this is a really really basic device nothing special it's running Linux and that's it but that's not true so this is this is basically a Wi-Fi router on 2.4 and 5g this is a rotor and the dachsies model so it's it's more than you were saying I started to look into define my system and it turns out there are 14 different partitions of the flesh and two of those actually four of those partitions had two differently losses right one for armed and the other one was for Intel 886 which was really strange because I already owned the arm part so why would you have Intel 86 x86 binarism the operating system on the flash that
was really strange for me when I checked the mark-up cache and there was this IP 192 181 68 to file power to 545 for on that interface which is in red which is a different Vidan so it was it was quite strange so I decided that I am going to ping it and as you can see there is no latency so it might be Catman hack for some reason which is really strange or or tells basically no wire between the two operating systems or the really short wire and it turns out turns out this this CPU does this dance device is using is an Interpol few mistakes and in 2016 early 2017 if you google this this chip
you didn't find much about this I don't know why probably it wasn't well at that time but animées it turns out it has three defense course on the chip one is part of a physics as we know I already own that architecture and there is two other words which are intel 8 Intel x86 right so three different course two different operating systems running on the two different type of architecture which was really strange because we are talking about one CP arm and Intel is integrated in the same CPU I never seen anything like this before then I started to think about maybe I should own the other other parts other half of the devices well how
can I didn't there are two ways that I've came up with the leaves v is basically modifying the FS the filesystem rewriting it or changing some stuff on it or the other one is service exploitation so I went with the lazy V there are a few partitions that are used by the secondary architecture one of them are squash FS which is read-only so we need to get the the filesystem you need to dump it if you want to change it you need to be bundle is really to recreates before poor file system because it's read-only and you need to refresh the flash that's not hard to do cause it's kind of risky because if they
have some kind of signature signature checking or any kind of other stuff is my break the device so I what I did I mounted the X 3 partition just to see what it does I promoted this I rebooted the device at night practice so after my week officially after like four days I break the device because I brought on to the X 3 partition mountainous what I forgot about the secondary lecture that was already mounted so when I rebooted the device it marked the de partition s as corrupt or it is the FSC case but my year rebooter your your computer and it needs to be FSC can you know it is asking the question from you and you
need to write yes or no during the boot but busy for you contrary connect the keyboard or anything to this so that's how I break the device every time any better ability didn't boot because it was waiting for my yes all summer so now it was it is quite unpleasant I had to get a new device so that's my B or there are lots of these devices we gotta watch refresh Scott's portion of us if you decide to recreate this then you need to make sure that you use the these same compression algorithms you checked all the files and everything just to make sure that it is going to vary because if you refresh it wrongly then it's not
going to work ever again or of course you can get the flash you can go back to the flesh but we need to get out of the case and it's that's not something that I can do the other way after I break the device I had to do the other way the other way which was basically the service exploitation I scan the secondary architecture on the type II that I showed you I found one really old Samba which must read of X in no shares there was a public exploits in Metasploit which was working against it but should have been working assets but it didn't so I couldn't do anything with it there was an RPC client bounty the 1210
at 23 TCP port and someone knows services then I think deeper and I found these parts which is 5150 yeah I hope you can sis and if he read in the middle there is this command system so basically me the system comedy you can expect with any kind of operating system level command so I decided to execute a proper sshd on port 22 22 and I was it it was quite trivial because the depositors for the root user was the same as the US or the other manufacturer by the way I had access to the file system so it was quite easy Logan as you can see this this this secretary architecture was running and
still running on intel x86 and the other part which is doing the logic is armed v6 then a few months later I came across this thing which I completely ignored so far and I was thinking maybe I can do an authenticated it was common execution finally so as you remember the only barrier which was missing here is bypassing course so I quickly voted out the device when I realized maybe I missed something and I sent the request this was the response friends the host header was sent to the IP the nice changed ye the host header from the IP to whatever doesn't matter as he changed him and I got the same response can you
tell me what kind of whatever it is this yeah that's right yes reminding I think there's a reason why you know this yeah so the s rebinding and basically this is this is the distant grill to to cut the unauthenticated remote command execution working because with this you can talk to the device remotely even if it's on the internal network so if you don't know the NS rebinding it's really easy to understand if you have a hostname that you control then like you resolve that host name is will give you an IP if you resolve that hostname for the second time it might give you a different IP the browser will think that it is talking to the same web
page but the IP changed in the meantime in the background so in this case I created a Depot which I'm going to show you I really hope this build it is going to burn if not I have a video office so you can see it's like this so basically I have a domain which is pointing to to do a website which is externally available you can open it in your browser and after after a few seconds or in this case because I was lazy and cheap after 20 to 120 seconds it is going to change the IP behind that host name and the browser will talk to the device to the router this router has
by default the same IP all the time which is 192 mozzies 8:01 that's basically the default you can change it of course but nobody changes it so my exploits is going to change the external IP to this internal IP and the browser will think that it is something the same with sending the request to the same same device to the same server but it doesn't so what what my exploit does when you open these websites because I sent you a link what it is embedded into a website that you visit friendly and it is going to work in the background so when you have this website it will sense the cookie do that bypass cookie that I
show you I can do that because i i i execute my code in my own web browser right in my old domain then it is going to wait and in the background i do some magic to do DNS rebinding so I have my DNS server which tells for the first time this is the exid this is the website then if you ask it again it will give you the internal IP of the device so after a few seconds or more than a few seconds the browser will change the cache the IP will point to this device and I am going to start that time I'm going to execute the the author against device that time I will send a lots of
SNMP sans requests to set the trace room things that I showed you in the beginning there is easy to build execute the dropper sshd on the main architecture the are part exposed at portal 22 then it will exploit the secondary device the secondary architecture through that service that I shown you it will execute the drop pair on the secondary device and with some IP tables magic I will expose dead ports secondary sshd ports on 4:23 so demo time fingers crossed so I have my DNS server running on my server this is not the people that I just wanted to show you and here I'm going to scan this device as you can see you can see it right you
can read it for 23 closed for 23 22 close so everything is closed I have eaten access on this Olivia Google loads properly it's fine and I'm going to look at this this profited website which is the energy media how max points the tables they started the attack I sent the cookie and as you can see here the muscle it is going to sense like in every 20 seconds a request to be to the device with a 404 it is looking for a PNG and if if it's portal for that that's why because we don't have that PNG on the server that that answer that page nicer but might be changed after a while openness around 60
seconds not work then is we look for that big picture this device that I know the DNS rebinding is and when that happens we know from the JavaScript that we are talking to the device instead of the event page that deserves and we are going to do the exploitation okay so it wasn't 404 it was the 200th so we found the picture and now we are sending a lots of us and that be stuff I can told you I was cheap and I was amazing so that's why I are using this yes remaining pending there are different techniques there are more reliable but more expensive technics in terms of effort resources so basically you can
you can use those that you can do DSD binding in a few seconds so when you move and a malicious web page with this set up maybe you can be exploited in three seconds is now 65 7 right so if you go back and scale it again you can see now port 23 22 and 23 is open so I can look in port for 22 you don't really get a shaft like you you concedes as you can see I'm root UID 0 this is the ARM architecture one one core of v6 PI over six and I look out don't need this anymore and I log in on port 23 it is same password and I do the same stuff
two different course but both of them are autumn which is in town x86 crazy thing that was the demo and G seconds
the question is here the difficut hands is way and you won't be hacked this way because all these issues are fixed except one which is the s remaining or maybe that's because s well I haven't checked for a while so basically the question is if you do it if you get hacked and somebody implants it wants something in the secondary architecture on the on the auto parts would you have them would you ever not listen do you think that the forensics that you do against your device or somebody else does it will they be really 50 so I think it's quite frightening because you don't know anything about these devices can have a lots of different issues and
even if if you know and if those issues an exploitable they can hide their stuff in the secondary and architecture and you can't really do anything against them and from the manufacturer you have full access to the interfaces you can change the data you can spoof it you can sniff it you can do whatever you like in ANSI C we do responsible disclosure which is which is great but at the same time it's kind of annoying so I reported the the issues on March 12 2013 72 years ago one and two years ago and it took around one and a half years to fix all the issues I mean I understand the process I think I understand the
processes release know they need to test if ever they need to make sure that a detainee speaks had it in Italy to make sure that everything is working properly because if they roll out the further which often then they will break hundreds or millions of devices millions of devices and that's financially not a good idea so probably that's why they - it's really slow but one of the half years that I could publish this talk but not publish anything about this because we were waiting on the bad boy thank you so much if you have any questions then maybe you can do it mom we believe we have we have five minutes so otherwise if you don't want to have
questions here you can find me later no way or maybe make seven years