How Attackers Can Use KMS to Ransomware S3 Buckets - Bleon Proko
Show transcript [en]
so hello again sorry for all the technical difficulties with the CTF it never happened on our end yeah DRS aside so uh today I'm coming with u uh with a talk that I've also done on uh besides Tiana related to how to use KMS uh service that AWS uses to uh manage encryption keys to do someware which is not the initial you know the initial idea behind it uh first off this is me I am a a cloud researcher at permiso I'm also the author of nebula uh Cloud penetration testing uh tool I'm I've been working on different companies throughout different different years uh starting from tacom to banking and right now I'm doing research on cloud and I've
been working with different Cloud uh uh different Cloud researches on AWS Asia and digital otion so uh the topic of today will be kind of uh cat and mouse game between our uh threat actors and us which are going to be the uh Defenders so our threat actors as you can see here are financially motivated as most of them they are not Nation supported so they don't have the resources they don't have the funds they don't have anything they have a relatively low budget and I mean almost no money they have a couple of laptops and uh ransomware is a goal to them because they want to get money that's the whole goal and it's easy you you can
just do it and you can just ask money you don't have to do anything else you don't have to sell them you don't have to bargain or anything you just put the price and that's all we as Defenders are again financially motivated Defenders because we randomly get paid uh we again are not Nation uh nation state supported we again have a relatively low budget so don't don't expect us to have much uh security systems put in place so we are we are talking about a company that is small with very important data but not so much uh security systems and also our data is in S3 so ransomware is a risk to us because if we lose them we lose
practically our Revenue so what is a ransomware and how it is usually done so in in a normal conventional classic ransomware you just get the access to the data you download them you encrypt the the original data you keep the the download the data then you uh ask for the uh you ask for the ransom if if they don't pay you can share the uh the all the information online you can sell it or anything if they do pay most of the there's a high chance that you will again do that but you will give them the data uh what about the S3 on the S3 you have to get access so there is a saying
that uh in Cloud am is the new perimeter you don't need too much perimeter security as much as you need access control since because you are using the API to do anything so you need to have access to that you need to download the data then you can do everything else you can encrypt them you can you know put them back you have all the data stored you know you have all the data stored and then you can just ask for the for the random and then you can do everything else that you were going to do in the first place the thing with this is that our threat actors do not have the money they
do not have a large infrastructure they do not have the guarantee that the client will get will pay them so they cannot just invest large amounts of money to get uh a whole infrastructure to uh to to keep all those data plus they are afraid of the monitoring so what do they do they start to look around and them being the crafty hackers that they are they found out they they look at the KMS so what is KMS KMS is literally an encryption as a service service uh that allows management of encryption keys and uh practically allows you to encrypt the files or encrypt any data that you want without having access to the key so you don't just spread it
around you don't just lay it around you don't just pass it in a notepad you don't have all of them you quite literally have the the you know have a service that is doing that for you uh so what you actually do is you just send the request to the KMS and they will just give you the cipher and again the reverse you send the cipher it will decrypted easy easy stuff so just one API call they also have something called the KMS policy so as I said uh identity is a new parameter so they can uh you can Define what is who is allowed and who is not allowed the way KMS works is
that if you allow access to only one identity nobody else will have access to it and if especially if you put the effect here to deny and then you say everybody except for this identity quite LLY not even the rout will have access to that not even the root account so the there have been cases when uh users have been locked out of their keys just because of doing this on the other hand S3s allows you to uh to put the conf uh the encryption configuration because of obvious reasons and by using both of them an attacker can create or modify a keys policy to allow only itself access to the key then put the
policy then just encryp the bucket they will have to do an you know a reedition of all the files but they don't need to to locally copy them and after doing it they quite literally have encrypted all the data and the way came works is that even if you want to decrypt the data you quite literally do not have access to the data because you don't have access to the key in the first place so you can't literally even download the data and I don't know try to do something like uh uh if you could brute force it or in the case of NSA probably use the back door on the rst but uh that's as I said that's how it is
now what does this help how does this help uh the attackers don't want to download the data and they don't need to download the data they can literally quite literally lock the data so they can just put the uh the policy uh put the encryption configuration just Rec copy the files to so get the file do a loop with the file uh grab the file and then reput it back to the bucket and they have encrypted them and when they want to give to allow the client access to the data they can just do the reverse so from encrypt to decrypt and again the funny thing about this is that if even the route doesn't
have access to the key they cannot even look at the key policy so they will not know who which identity has access to this key unless they try to do something different so let's put our blue heads now and start to understand how we can kind of prevent this yeah uh so what what we saw is that even though we The Defenders or the administrators do not have access to the key when they open the KMS dashboard they will get an error saying you don't have access to read this key and they will have the the key ID so they they will know which ID is doing the Mayhem on the other hand even though the route or the
administrator doesn't have access to the to the key they do have access to each identity so what they can do is quite literally get create a policy that allows GS describe key because the attacker might revoke that that right then list all the roles all the users uh put a new access key or just delete one and put another one for the users assume the roles and then just try to do describe key on that key and as you can see here this identity has access it's supposed to be admin user here sorry if it doesn't look so good so we found out that that identity has access now that we know which identity has access we can
protect our so we can uh revoke the the ransomware the blue teamer one on the other hand you also have the cloud trail logs which is a lot easier method than just looking you know just doing all of this but yeah you can just uh clearly look at the logs and then see which identity has touched this key and then you will know who uh who has access uh to the to the key and then again revoke the ransomware so the the threat actors don't want to go there you know it's a whole hardle they will lose the access they will lose everything they will not do anything with this what do they do though what happens
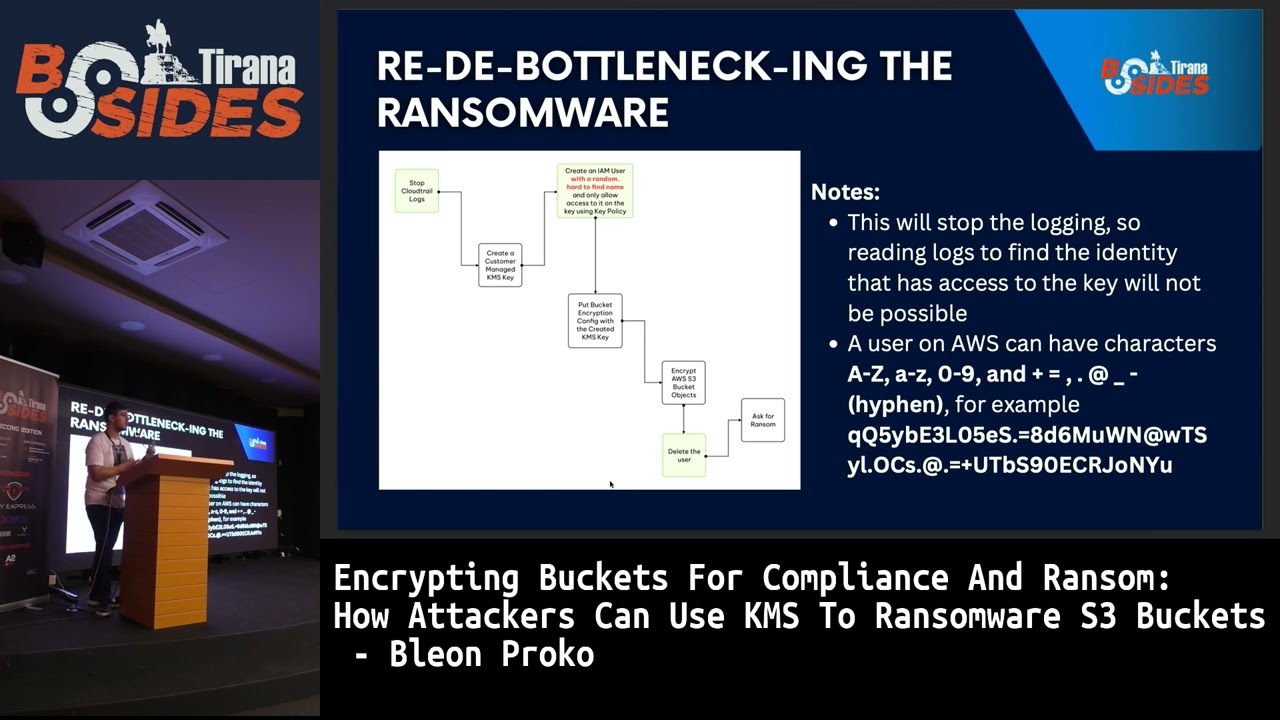
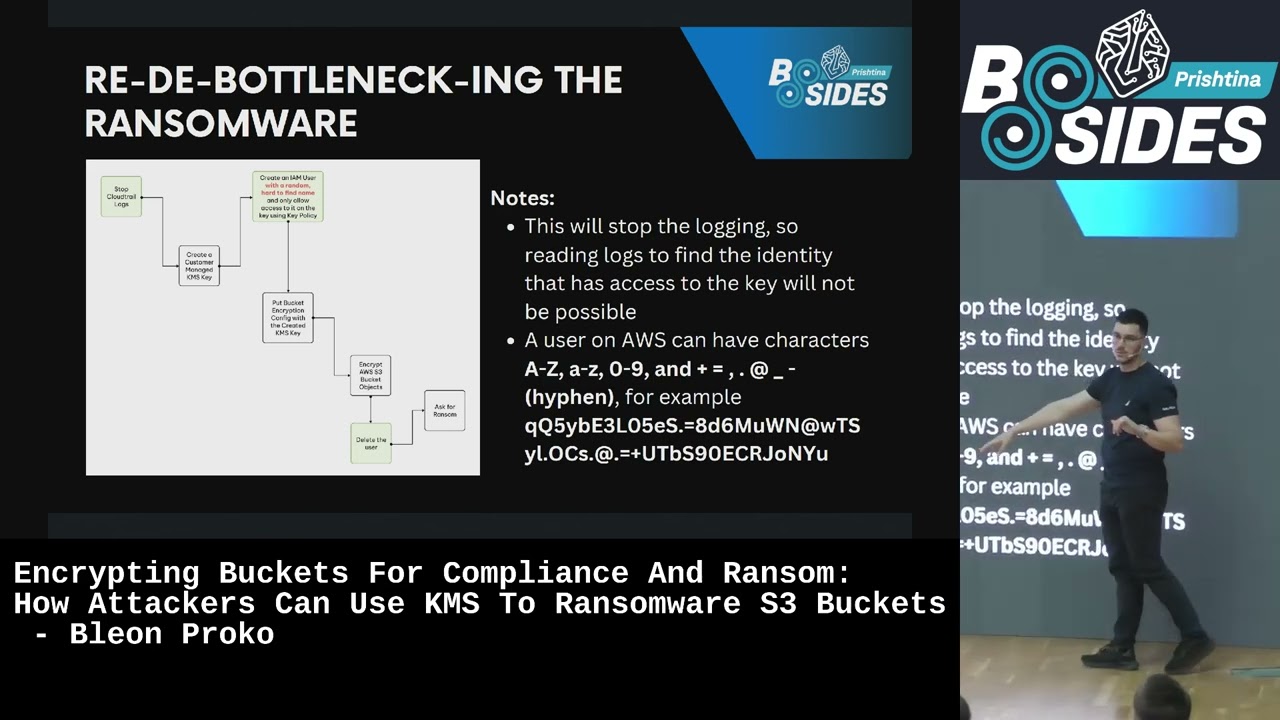
when you go stop the cloud trail logs and for the sake of the argument we presume that they have access to do that they stop the cloud trail logs before they start everything then they create an imem user with a very random key uh with a very random name they do everything then they delete the user right now the Defenders will not know which user is doing this they will not have logs and they will not know what you know which identity has access to it and when everything is being paid the uh the attackers can just say okay this is the user have fun you know create the user and just decrypt the the data and
quite literally a AWS is being very generous with what it allows on on a username if I'm not wrong it allows 40 64 characters of all of them so you know random was never an issue to you know to the attackers what is the issue again with that one even if the cloud trail are sto you know the cloud trail lcks are stop there's still the event history event history is a feature that uh AWS has AWS cloud trail has that keeps every event of the last 90 days you will you will have used uh event history if you have used Cloud TR lookup events lookup events quite literally grabs that uh so again having
a random name does not work for the attackers on the other hand uh what KMS does is that it doesn't use the username on the policy but it actually uses the user ID on the policy so if you delete the user and you recreate that again they will not have access to the key so again they will have reached data distraction at this point there is no way to return the the data but they will not have uh done the the randomware with the low cost that we wanted to to do so again this is not something the threat actors want again AWS is very generous and allows a something called a cross account KS key
sharing quite literally how this works is that you can put the policy and allow one account to access the keys on another account think of this as an infrastructure where the whole KMS keys are put in one account then everybody else is uses and then you restrict access to that to those uh to to that account an attacker can do the same they can create their own account they can create their own key they can allow the compromised user access they can do everything they can remove the policy when and then when the uh Target pays they can just recreate the policy and allow the Target to to decrypt the data quite literally this works and this is
actually the best way and this is actually the way that uh rhos SEC uh did it like you know what rhinos did on on a research like four years ago if I'm not wrong five years ago this actually works because you don't have to keep the keys you don't have to keep anything you don't have to have the data stored in you you have the account and everything and it also works for each each object not just on the Bucket Level but you can quite literally encrypt object per object so you can even you know mess with them and create like 10 keys and then just randomly do them so that they will have to find 10 Keys you
know it this is just an addition but even the Bucket Level encryption does work unless the Defenders have created an SCP policy which uh is put on the organizational level and only allows resources to be accessed from their own organization right now the attacker's account is of course not on the organization the attacker has to put the account on the organ on the organization and that would include other issues because right now they they've given access to the diff to the to the Target and since they do this there will be an access denied because the resource is outside the organization of the of the target so again the Defenders crafted as they were as they
are they manage to to stop this but our attackers do not do not give up easily let's go back to the to the first Transformer what you do is you you get access to the data you download the data you encrypt them locally what if you can do the same thing with KMS you get access to the data you download just one file you get you create a key on your own account you encrypt the file with the key here locally you put the file back again on the bucket then you delete the file right now quite literally you are not storing all the files uh locally because you are deleting them all the time and you are
encrypting them with a key that is on the KMS and you are again ROM wearing them and the funny thing about about this is that uh when a bucket encryption is put uh bucket encryption configuration is put on a bucket other files cannot be added unless access to the key is given in this way that doesn't work the file will have the same name and you know U each time you upload the file with the same name it overwrites the old one so you you will quite literally just overwrite the file with the encrypted version which leads us to the idea of the version there's something called a bucket versioning in AWS what bucket versioning is is quite literally keep
every version of a certain file in in the bucket so you quite literally are keeping 100 versions of the same file think of this like uh git commits so you have everything there meaning the attacker will have this version which is the encrypted version but the defender will have this and this and the rest of them and other than that there is no uh to my knowledge there is no restriction to how many versions can be of a file I did the test once I create I rewrote 50,000 uh you know versions of a file all of them were kept so you know uh to my knowledge there is no restriction I mean if there's a million I don't know
if you'll need the million versions of a file but again at least you will need one one more to to protect that oh yeah of course yes of course but as I said let's because if we go by that logic yes there is also uh there can be also restrictions on how much can be downloaded and there can also be a cost on on every download for the for the Target so you know yeah yeah uh there's also something called an uh MFA delete MFA delete is an extension of uh bucket versioning which quite little tells you you have to put the MFA code each time you modify an object or each time you modify the uh the bucket
configuration the thing is this one here most of the times will not be present because buckets are usually storage that is dynamic and everything is done through a code so uh you will need to find a code that will just create the MFA and then push the MFA and then do the modification you will most likely not find this unless it's a backup but if you have this one it's it's it's an extra layer of security by default this is not enabled you have to enable this even if you enable the bucket versioning and how do you bypass this there are two ways the first one the easy one just you know suspend it if you
suspend it there's no uh there's no uh bucket version anymore yes there are versions but you can delete them you can delete every version you can list them you can delete them again we are presuming they have the rights to do that the second one is you can quite literally encrypt the file then you can list all the versions and then you can delete every other version except the encrypted one right now it doesn't matter if versioning is enabled they will only have one version on the bucket and that one version will be the the attackers anded version so right now even with bucket versioning enabled they will still have only one version there because you
deleted every other version after you put the encrypted version there so you know you do the reverse of what bucket version uh bucket versioning does and yes this is the whole idea at this point uh the attackers have managed to bypass uh so they have managed to go through all the hardles they have bypassed the scps they have bypassed the bucket so they have they have compromised the user created the key on their own account bypass the SCP with the method of you know encrypting each each file uh once per and then they have also bypassed the bucket versioning so right now the target has nothing to do so the target is run word so we lost
guys sorry they B they beat us uh yeah just to show you we also have everything so uh in permisso we actually we've actually seen not seen ransomware happens but we have seen Keys being misconfigured so many people having access so we have uh we have alerts quite readily for this we have alerts for the key lockout we have the we have alerts for uh cloud trail of course logging being being tempered with or the bucket encryption being tempered with or even uh the external um external uh resources being used so you know just just a heads up yes we do cover you on that one and conclusion again I am is the new perimeter in I I I'm not saying you
shouldn't have uh you know you shouldn't put uh you know perimeter security but focus a lot on the IM if everything is done through uh privilege without with actually no uh no need for an access to the to the Target you don't need to focus too much on the perimeter as you do mostly on the on Prem but you need to focus on the on the am secondly bucket versioning is something that you should enabled unless as this said you can AF you know if you can afford it of course because if you cannot afford it you can again do something you can just rewrite your code and then just uh you know delete the previous version and
then put the the new version and you do quite literally the same thing that is being done when you create an access key or when you create the a third access key so you delete the previous version and you have the the other one so you will not have too much versions of of the same file if you do not need them if you only need them for uh for sort of a backup you should use scps you should first of all use an organization I've seen a lot of companies only use one account and have everything there and you should use scps to limit the access on other regions and especially resources outside of your
organization that you do not want to get access to there are some businesses that have connections to other businesses yes you can allow them but you should not allow access to everywhere and yes again as I said previously this is something that was that started from rhinos SEC uh so they they use the cross account technique which we later on find found out that is uh you know could be stopped but yes this was the the first idea that you know that they were the first one that that started this so good us to them and again I want to thank a lot of people so I want to thank the P zero team Nathan Debo and Ian and Opie
for all the ideas that they have done for all the the help that they have given thank you to the ux team for all the designs and the marketing for all the merge and of course the design and thank you for the rest of the permisso for being awesome thank you any questions thank you do we have any questions yeah has one give me a
second so thank you uh my question if you can go to the slides you Shar the use cases are those available open source or somewhere uh we haven't so they sort of is are you can quite literally just get everything and you can create some some uh some uh you know simple bus scripts but we are working currently on a simulation tool that will have different attacks including those this ones it's a thing you know it's kind of a difficult thing to share some uh something related or ransomware automation stol especially on you know something like this which can be used with the the targets uh Services internal services so I cannot say that we will release that unless you
know we see everything or we try to to limit it as much as we can but right now what the only thing you can do is just get everything here and just try to to automate this the second thing is would guard Duty protect from those no because I don't know if they have I haven't checked if they have updated but to my knowledge no because uh creating the bucket encryption configuration is something normal you cannot just stop people from doing that or locking the keys I have never gotten an alerts while while locking the keys and I have like 15 in my own test account and I don't know what to do because I can't close that
account you know right now but uh no to my knowledge they do not do anything of that the only thing I think can be tried is too much data being dumped and too much data being downloaded a bulk download and there's to then too much data being uploaded I think that can can be triggered but other than that to my knowledge no thank you any other question thank you blon that was great thanks for the presentation