Purple Team Assessment

Show original YouTube description
Show transcript [en]
foreign
first I know I'm the last person between you and the drinks so I'll try to keep to my schedule of 20 minutes or so a second I know it's been uh long to this video I'm not gonna bore you hopefully you're gonna find it interesting but before we go I need to say two key points this is my personal Takeaway on purple team I don't represent my employer and second important point is if something goes bad and not responsible so yeah before we go I'm gonna take the opportunity to tell you a couple words about myself how do I recharge I love running and I love hiking and who am I well I've been in the cyber security
industry let's say the good size of more than 10 years uh most of my experience was gained in the UK and I recently moved back to Bulgaria and I'm here now to talk to you about cyber security and specifically about purple TeenNick but before we go into the purple teaming we need to know what a bad pyramid is well first time when I heard about what bad pyramid is I had like 10 things running through my head like what does that mean and I decided to uh find out and if you ask chargipti nowadays you're gonna get one of the things that was in my head which is effectively uh top heavy organization well I had
that running in my head the other thing that I had running in my head was well if you ask your local Mafia mafia boss nephew obviously I don't know if he was going to tell you well the reason such as King was a bad pyramid but apparently there is and we need to know about that to understand purple teaming when we talk about sidebar and we talk about the technical people inside but we can roughly split them into three different buckets one of them is the people who build stuff the other one is the people who attack stuff and the other one is the people who defend stuff and each one of them have their own color
the people who built it they have their color code yellow we have people who attacked their color called red and have the people who defend style color called Blue hence where we have red and blue merging that's why we have purple team well that implies is going to be something as a joint venture between these two teams I know that quite a lot of words here I'm going to talk about all of them just key takeaways this is a formal definition uh from nist what the red team does the main objective of direct team is to improve and emphasize on that is to improve the Enterprise information assurance by demonstrating two things uh successful attacks one and what works for the blue
team whereas the blue team is responsible for defending the organization assets to a good level of security posture from things like trade actors retinos if you like and so forth and so forth so we can see what each team is responsible for and now we go into the paperwork back in the day things will not start well standardized people doing red teams and they were asked to do ratings but we didn't had Frameworks to go to attraction of what the red team is and eventually after let's say a slow start Bank of England introduced something called sea best which is effectively intelligence red intelligence LED red team a kick-started with two successful organizations being on board in 2017 so
let's say 2017 was probably the first of my knowledge formal framework I.E paperwork that helps you to do a purple team shortly afterwards 2018 European Central Bank they introduced their own take of it which is stable unlike the C best the type is not mandatory is optional which means that well organizations do that if they want to and another difference there is that every country in the European Union can have their own take on table type of Netherlands being one of them uh I do have another three over here for completeness I'm not exporting this but they're there to show that other parts of the world have their own take on how purple teams to be done uh well based on
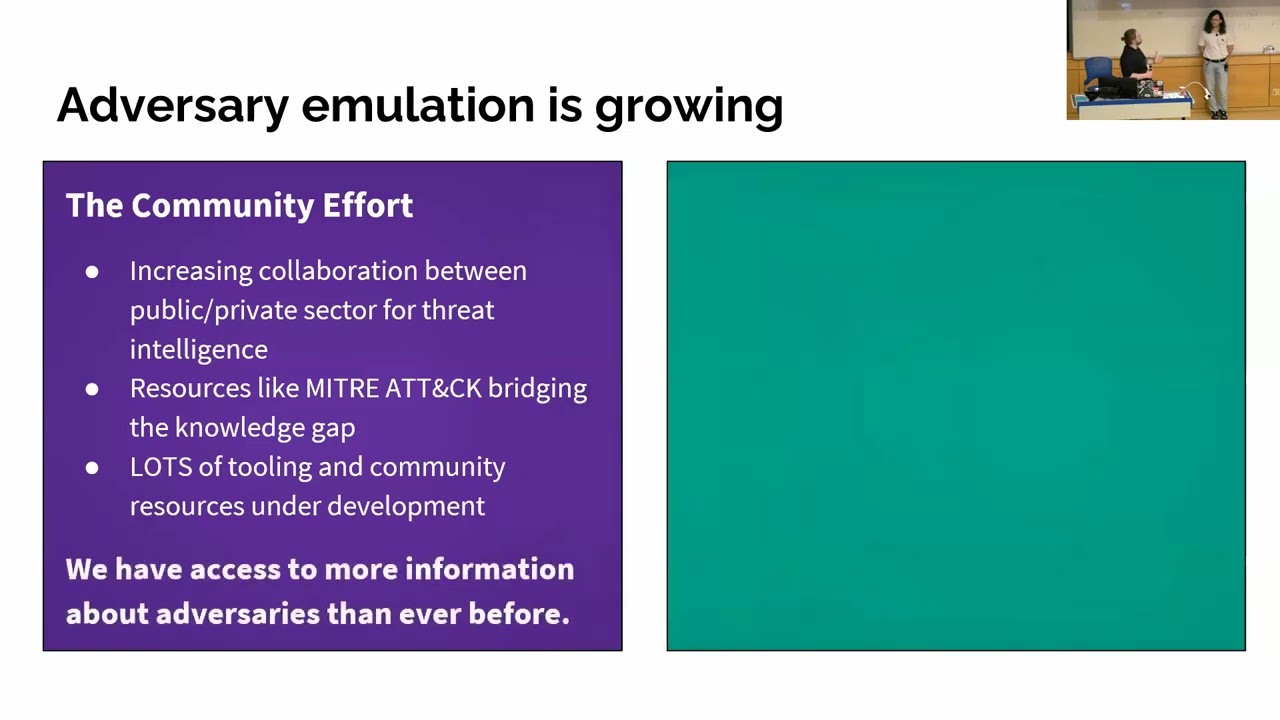
your geographical region you need to comply with one of these if you want to do a purple team and so wow on paper but actually how do we do that well took hand come more Frameworks sorry to say that but yeah and one of the things that I believe kick-started the formal process of standardizing purple team was Lockheed Martin uh back in the day that was a quite lint in my eyes kill chain but now I understand the value of it and the people took that to the next level they introduced Mitra attack framework and some tools come into hand over here we'll come run away with some tools I try to be then diagnostic but well it's
a big names I can't just ignore them they contributed a lot to the purple teaming and we have a commercial tool and we'll have uh some free playbooks out there why am I saying that I'm sorry about this I explicitly asked I know it's more front it does look different on different operating systems I don't know why uh apologies again yeah like a joke thanks it's Friday afternoon uh so what a purple team is we talk about Frameworks and executions but what what comes here over here is that actually that's a full on Blown uh project so a very rather project it has its stages the first stage is information gathering thank you uh which
is effectively cyber threat intelligence which is normally done by an organization in this case let's say organization a and the key Focus series on that is to deliver two things intelligence reports and the second thing important here is that this threat intelligence import might actually have to be able to be forwarded to another third organization and then we go into the preparation phase where in this case organization B took the organization a right intelligence report and bills on top of that what we want to have here as a key outcomes is a plan of what is to be executed uh going back to Lockheed Martin Q chain and a key way of communication change so we need to
know who is to communicate what to whom third stage is to execute a purple team obviously that's what the name implies execute the already approved uh kill chain if you like uh again communication is a key so at Key stages of the execution the organization that executes the purple team needs to communicate what's approved with the client and in my eyes the most important lesson here is well we're all trying to improve right uh as people perform a set nothing is secure hence we have detection and response and that's what we're trying to do here so with the purple team we give the blue blue team away to analyze attack outcome where we clearly know
what the attack was analyze what alerts were raised from that attack and what alerts were not raised and improve on the tools documentation and processes so next time when they have a similar attack things actually are going to be flagged in action appropriately and we go into the Q chain so um I'm not gonna go in the detail of this uh everyone can read it the point here is when you do a purple team I would suggest highly advice to stick to the Q chain and drill down in each one of these bullet points to a reasonable level of detail and and have that approved by the client so you can think of a reconnaissance so
we can think of all so that's what we want to do and break down that two to three different bullet points and you have your clients agreeing on that before you actually start doing the execution oh this one looks good uh I know it's a lot of words the point here is well that sounds pretty much like a red team no it's not uh what's the difference between a purple team and a red team I can talk let's say half an hour or one hour on that topic I've done it now I want to introduce you to the purple team and I want to avoid confusion so here I'm gonna just give you three different
three key differences what is a red team versus a purple team the first one is the purple team actually simulates attack or attacks while a red team is two action on objectives defined by the client so direct team is not limited to specific attacks and attack paths that are pre-approved by the client I they're not limited to approved kill chain uh second key difference is a purple team might require a client to interact with two different organizations one of them is to perform the threat intelligence the other one is to perform the actual execution whereas with the red team that could be done well just by one organization that's going to do the threat intelligence and the actual execution
and the third key difference is that I didn't mention that but it's a good way to introduce it during a purple team the red team and The Blue Team talk a lot by that I mean they might have regular workshops on every 24 hours for 48 hours where they sync up and they're a teaming well just common says that's what we did did you sell us what did you saw and whatnot this is really really timely feedback for the blue team during the actual execution which means that they can go and see what has been caught and what has been missed by the two quite easily whereas with the red team an organization just does what it does
and let's say for the sake of the argument the report is being delayed not being approved lands on the blue team's desk let's say after a month or so and they need to go back and dig through the lock locks of what happened one month ago and why the tools didn't get it well it's quite painful and it doesn't really help them to improve and I know I introduced a new topic and we'll think well another type of assessment well sorry which assessment is appropriate for us probably you've seen that it's my take again uh well other people's supports as well but as a very basic every organization should do a vulnerability scanning and it depends on how mature is the
organization they gonna go towards the purple side of things and we can see from a basic scan we go to assessment pen testing Red Team all this kind of buzzwords and we reached the purple team the one that I try to introduce you today and we'll have something a little bit more advanced called over here Advanced simulation but yeah maybe that's a topic for another day and I think I stick quite well with the timing any questions I didn't bore you today did I please thank you [Applause]