BSidesCharm 2025 - A Theme of Fear: Hacking the Paradigm - Dr. Catherine Ullman
Show transcript [en]
[Music]
All right. Good afternoon. How are we doing? Still awake. That's a plus. I know it's late the first day, but the real partying hasn't really started yet. So hopefully uh you're still here with me on this. Um so I'm going to talk today a little bit about the history of uh the FUD that we now deal with and kind of how we got here. So this is going to be our agenda. I'm going to go o over uh I'll talk very briefly about me. Um, then we're going to talk about the idea of fear and loathing and the cost that that fear uh generates as a result. And then we'll go into the history. How did we get here?
Because those of you who've been here more than five minutes know that, you know, we're we we've kind of developed a shitow, right? In terms of all the the marketing that gets thrown at us and the blinky boxes. Um, we'll talk about the consequences of that fear and then we're going to talk about changing the paradigm. How do we get somewhere other than where we are today and I'm going to advocate to all of you that that's the direction we really want to take. So, how we're going to move forward and I'll enter I'll uh leave you with some final thoughts. So, here's a little bit about me. Um, I go by Kathy or investigator
chick. I work at the University of Buffalo. I've been there over 25 years. Um, I started in support a bazillion years ago. Um, and uh, I'm involved with a lot of things. I've volunteer for a bunch of conferences. I run besides Rochester. But odds are good. If you're in the Midwest or you come out to like Defcon or something, you're probably going to see me somewhere. Um, and most importantly, I love sloths. So, we have Flash up here. He's he's the sloth at the Buffalo Zoo that I often send money to support. All right. So, let's get into this whole idea of fear and loathing. So, here's a really early advertisement. How many of you were
around in 1989 thinking about antivirus? At least at least a couple. Right? So, this is a really early advertisement for this idea of there being antivirus. Now, you have to understand there was a time before all of this where no one cared about security because that wasn't a thing. And I know those of you who are old enough are looking at me going, "How the hell can you be that old?" Because I get that a lot. And here's what I'll tell you. I'll tell you a little snippet about my history and why I have this bizarre perspective. My father moved to what became my hometown when I was like 7 years old. and he began to run the
mainframe at the computing center in the college at that hometown. So what did we have in my house? We had a terminal. Yes, a terminal. That terminal unlike most people with a terminal did not dial up to a modem. We had a direct line to the college. There was no modem noise. It was just always on. And so a lot of my hacker friends when I share stories with them, they're like, "Oh yeah, I used to go to that place. I was, you know, I was freaking and that's how I got to the thing." And I was like, "Yeah, I just tell netted there cuz I could, right?" So, um, so my background's a little
different. Um, so anyway, back to this. So what do we see here in 2007? Uhoh. We need to protect ourselves. Is there a huge difference between these two? And how old? I mean, like, how many years are between them? A lot. We're still selling the same garbage. This is part of the reason we are selling the same garbage. People think fear is really a good motivator. They think, "Oh, we can bolster change. If we scare the crap out of people, they'll do something else. I'm going to say a blasphemous thing here. How many of you go to church where they tell you if you don't do the right thing, something bad will happen? And for how many of you do you
do the right thing because you're told that, right? Like I'm hearing some giggles. And the reality is there's a bunch of research out there that shows that fear is really problematic. What does it cost us? Well, you know, we spend a lot of money. Does that make us more secure? What? Marginally, right? So, in 2023, we spent 162 billion, right? That's kind of the worldwide average cost from Gartner. Um, in 24 it was 182 billion, up 12 and a half percent. Things must be better. We're spending more money. Yay. How many of you would say yes? It's so much better now. Yes, it's improving salaries. I mean, I can't deny that. It It improved mine a little bit, too. Um,
spoiler alert, it's not working. So, what we're doing is not working. And I think pretty much everyone here can agree with that, right? There are some things we are learning some lessons, but they're not because that we've tried to scare the crap out of people. I literally had a salesman talk to me years ago. He worked for Fire Eye and I wanted to get a Fire Eye appliance into our environment because I saw the benefit. I could we did a proof of concept. I could see what it was doing for us and I thought this would be fabulous. So, you know what he did? He called up my CIO and he made an appointment to sit down and talk to him.
What do you think he did? He he tried to scare the crap out of my CIO. You know what my CIO did? Marched him out of his office and said, "We're never doing business with you ever again." And we hadn't done business with them then. And that CIO is around for 10 years. So fear is definitely problematic. I don't know how many of you are familiar with Chris Roberts, but Chris Roberts co, as far as I can tell, coined the term blinky box syndrome. So, this is where you need the newest blinky thing, whatever it is. Uh, so back in the day, and we'll talk a little bit about the history of how we got here,
but now we're into AI, right? That's the newest blinky box. It's going to be whatever AI thing that someone can throw at you or ML or next. I mean, there was a time when it was nextgen, right? Like all these buzzwords. It's insane. And so there's this whole idea that you need the next Blinky Box cuz that's what's going to make you safe. And that's all spurred by fear. So, here's what fear really does, other than make cats look ridiculous. It it causes us to be incredibly defensive, right? And if you're feeling uncomfortable, if somebody looks at you and accuses you of something, what is the last thing you want to do? Comply or even even listen, right? You don't want
to hear what they have to say. If they're accusing you of something, whether or not it's legit, no one wants to hear that. The trick is if there's not enough fear, you're complacent and you don't care, right? And I think, you know, especially today, we see that a lot. If I were to ask you, when was the major latest major breach? You'd be like, I don't know. It happens so often. Which one? I don't even care anymore. But if there's too much fear, you're too afraid to make any decisions and we get totally paralyzed by that. And that's a serious problem. So trying to balance fear, it really doesn't work. And you wind up with these negative emotions and
thoughts about a product like the story of Fire Eye and my CIO. We never did get Fire Eye. We wound up do having to do other things. But, you know, it would have been a really nice solution to have in place for what we needed at the time, but we lost out on it because the salesman decided fear was the answer. And you know, it creates an overactive overreaction that is really un unnecessary. So, let's go back in time a little bit. So, the picture on the left from your perspective. Um, this is a little touching a little too close to home right now, but I thought I'd leave it in anyway. So, for those of you who are not
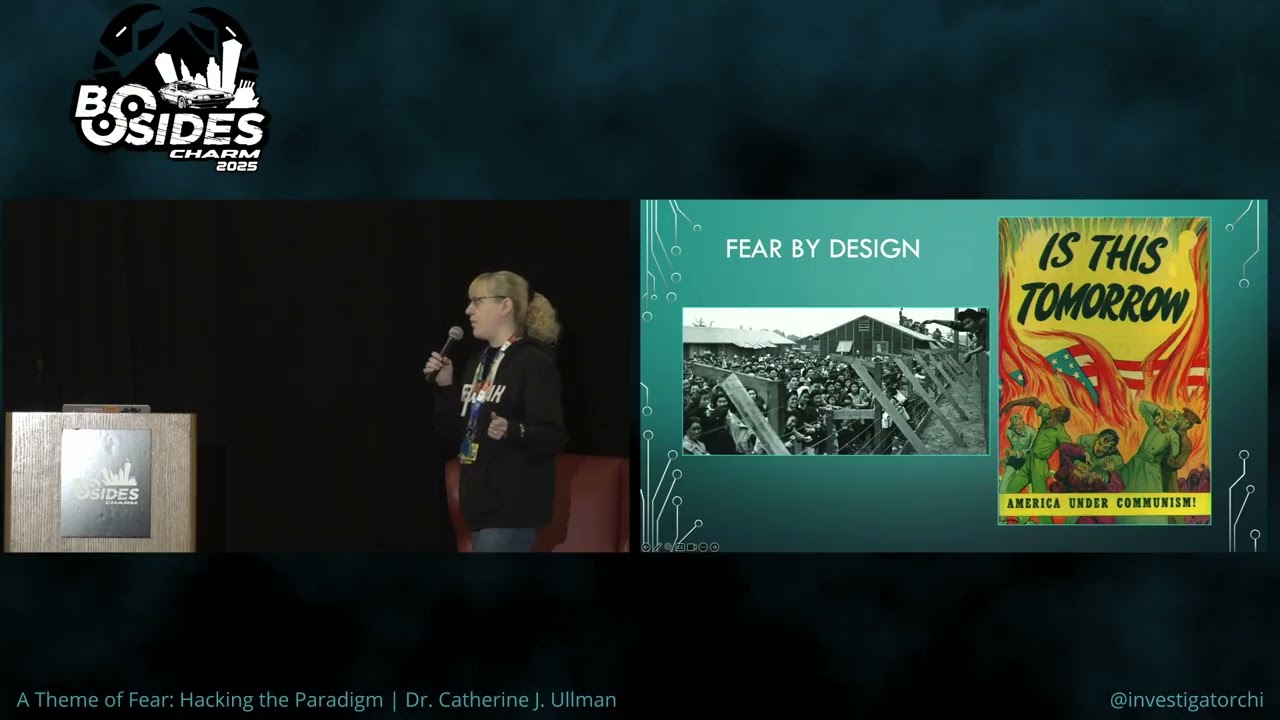
familiar with this, this is World War II. These were Japanese internment camps. And why were these people here? Because they were Japanese. Not because they'd done anything wrong. Not because somehow they were bad, but because they were Japanese. And because of the actions in World War II, the Japanese Americans were rounded up and put in these internment camps. The picture on the on the right is about Russia because we never ever hear anything about how scary Russia is. And gee, again, these images and the whole thing about Russia that seems to be coming back. So yeah, there there's this idea that we've we create fear by design, right? We have these things already circulating. Who knows about the orange
book? Anybody have the orange book? Yeah, a bunch of bunch of us old folks who know about this book. So this was the really early thing that was supposed to teach us about security and it was, you know, the dos and don'ts, right? And this was long before any of these terms, cyber security, security, because security wasn't a thing. It was just about risk assessment. And it's kind of funny because we we talk all about cyber security and all these other things, right? And and then the bean counters come along and talk about risk assessment, but in reality, we're really all talking about the same stuff, but this is how the government started with any form of anything to do with
security. So here's the beginning of the internet. The internet starts in the mid 80s. It starts with four machines. And those four machines, how why were they connected? Does anybody know or remember? No. Everybody thinks it was missile defense. Guess again. Education. They were four academic institutions and the whole idea was one was a backup for the other. That was it. They would let if you read the comments about why people think it was a military thing. If you read between the lines, you'll find that that was the excuse that the government ultimately gave, but that's not actually what happened. So these four systems, these four schools develop the first arponet. My first experience with that uh line
that I told you about that was Bitnet and Bitnet was uh depending on who you ask because it's their network or because it's time network and it connected the state university of New York schools. Um so and uh it connected the city university of New York and Yale initially in ' 81 and then other Sunnis followed and it had uh it used IBM internal internet protocols. I mean this is really old old stuff and you started you know then you have the corporate computer boom right people start buying their own machines and companies are using the internet and then we move to these early early developments. So we have the very first virus and the very first virus is
this virus called brain. And what did brain do? Well it didn't do a whole lot. Um, and John McCaffy decided he was going to help fix this problem. And whether you liked him or hated him, his early start was in fact trying to be kind of a good guy. And he offered up a way you could get rid of this virus. And what was really funny about it is that it was really this idea of copyright infringement. It had nothing to do with real viruses as we kind of think of them today. by the late 80s. So this is not a huge stretch from 86 to the late 80s. Semantic and sofos come into being. By ' 89 we had more antivirus
vendors than there were actual viri. Think about that for a minute. That's crazy. So, are you starting to see just the very beginnings of this? The government loses their minds and they're like, "Oh my god, we're all going to die. We're going to have our systems infected. It's a potentially devastating weapon." This was in a news article uh that was in the Toronto Globe and Mail. Uh, and then there was another article that had uh high technology equivalent of germ warfare. Smell any fear there anybody? We we we're you know that's not a thing. Excuse me. In 88 the Morris worm hits and this is the one that I think the bulk of folks in this room might have
heard of because um we teach this in schools and we teach this in various program. Sans talks about it and it crashes a number of computers around the world and as a result the first C at Carnegie Melon gets started which is pretty crazy which is a computer emergency response team. So that that's that's a big deal right so you can kind of see how this is starting to evolve. So because we're terrified now of some sort of external attack, we're starting to spend money and we're starting to spend a fair amount of it. So by 1990, we're at one.5 billion dollars worldwide. And if you look at the prevention dollars, right, this whole idea of spending 120,000 to 150,000,
this seems pretty reasonable given the fact that this sort of thing took out all of these systems. They're like, "Yeah, okay. That's fine." Ah, then we get into these books. These were the Bibles for some folks, the very early books about internet security because at the time we're still talking about machines that aren't doing a whole lot. They're not on all the time, right? And we have this idea of a firewall. What a cool thing. Why does the firewall come along? Well, we're going to see that in a minute. But what happens in uh 1995 that changes everything? Anybody guess? Uh before AOL predates AOL. Oh, I'm sorry. 93 Mosaic. So now you have the first web
browser because what were people doing on the internet? internet because it wasn't really an internet before this. They were doing talet. They were doing textbased. Yep. Games, BBS's, right? There was no like you click things and pictures come up unless it was asky art. That's all you were seeing. There was no web. Well, when this launches, the whole world changes and people start to want to be on the internet and doing the things. Ah, now they try to appeal to our emotional side. After all, virus protection is a matter of trust. Okay. So, you can see like this ad, we're just we're just moving forward into this fear and then we get into blinky boxes.
How do we get there? Here are the blinky box beginnings. So, in 1990, you have the first commercially available firewalls. It was this deck seal uh that was developed uh by this guy named Marcus Runnom. And it was a security gateway. It was the thing that protected you from the outside world so that when you were on the internet in theory you were safe. And as companies were getting on the internet now truly on the internet it was decided there needed to be this protection because we had seen all of these problems. It was considered virtually failsafe protection. Okay. So when I hear virtually failsafe protection I think of two things. One is the Titanic which was
unsinkable and the other thing I think of is the Irakcoy theater fire. The Irakcoy Theater Fire was a theater in Chicago. It was deemed fireproof and I just did a talk about this whole idea of security, you know, being secure and this whole idea of fireproof and and the fact that they're sort of misnomers because there's no such thing. So, in uh 1995, Mitnik decides he's going to hack the San Diego Supercomputing Center. He does a spoof, and he gets through the firewall. Uh-oh. We had AV, then we needed firewalls. Now, someone's gotten past the firewall. You kind of see where this is going. So, what about today? We have more money. We're spending lots more
money. We're buying more things. Now we have nextgen firewalls. We have IDS and IPS and nextgen all the things. And we have AI protecting our backside. What do you think? How we doing? Yeah. Nah, we're still we're still having a disaster. These these are the last uh numbers that I pulled from the ITRC. Um, you know, this is talking about a variety of different things like the compromises of 2024, the the attack vectors, like this just shows you everything's still on
fire. So, what are the consequences in this industry of that fear? Well, FUD. So, this idea of fear, uncertainty, and doubt. We see the fear-based marketing strategy. We've already talked about how fear is problematic. You're going to what what you see as a result is not only these emotional appeals, but in that we we see information misinformation. So long before what we have seen in the media recently as misinformation or disinformation campaigns, we were seeing in this particular space. and it's, you know, the the the one company saying something bad about the other company's product to keep you from, you know, potentially buying it. So, one of the stories, excuse me, that I like to share if you're not
familiar with it, there was a man named Jean Amdall and he had a great idea for a computer and then there was the giant IBM. You would think, oh, he's never going to win against them. But here's the thing. The reason in fact why IBM got anywhere wasn't because his product was inferior, but because they spewed FUD. DAL's product didn't have cooling fans. That was the big distinction. And because of that, it was cheaper. But guess what? It didn't need cooling fans. It didn't need them because of the design. The design put the power supply on the outside of the box. So, if it's on the outside of the box, why do you need a cooling fan? But IBM didn't
care. Oh, let me just go back for a second. I love this quote from Rich Smith. So, he used to be with with Duo when I first met him and heard him say this. The security industry generates FUD in order to sell hope. And I think that's true. Uh he's now apparently with a company named Crash Override. But anyway, this is the kind of thing that the kind of thing we would see about competitors, right? I'll stick with EMC because they showed that if I move from X to Y, bad things will happen. And you know, then the company that's trying to come in and displace CMC says, "I'm not surprised they told you because, you
know, they couldn't tell you. Um they they'd have to sell you more discs." It's like let me show you why the competition is just wrong. And this is the kind of thing if you look very carefully. What does this say on the bottom? Yes. By who? IBM. Right. So this is a real piece of marketing that they built internally that was leaked to the public, which is how I have it. I didn't get it from anywhere special. So we have a fear-driven driven image problem, right? I like this quote from a woman who also uh used to be with Duo. In large part due to mainstream media, the idea of security often becomes entangled with fictional concepts of the
people who are in the world of security are and what the data battlefield looks like cuz we never see an image like that at all anymore. But the reality is we fear what we don't understand. So someone who has malicious intent is not a hacker. So I am standing here proudly wearing my hacker sweatshirt. I am sure for many of you in the room this is old hat. I don't need to tell you this. For those of you who are new to this concept, hackers are folks who think outside the box. They're the people who understand how things really work, not just how they're intended to work. This is not a bad thing. And the origins of the term
hacker are not in a bad place. They came from a railroad club, folks, at MIT. Like, come on. But unfortunately, there are folks who don't believe that. So, um, we see fear in the development world, too. How many devs do I have? at least a few. Okay, so my husband is a developer and when I built this deck, I sat down with him. Now, I'll tell you what's kind of cool. He comes to not this one, but he comes to security conferences with me years ago. I took him to DerbyCon and he was he was hooked. Now, mostly he goes to Girkcon with me and he helps I run Besides Rochester. He helps with that. But the
point is, I sat down with him and I said, "How does fear impact how you do what you do for your job?" and he said, "If there's a breach and it's my code, I'm terrified that, you know, I could get called out for that." So, it's not just those of us who are doing either support or security, it's the developers as well. There's a huge demand on time. So, you know, if you if you have a bunch of code and you need to get it out the door quickly, they're going to terrify you into getting it done and getting it done right away or you could lose your job. um you know in a lot of uh computer
science programs and I have several friends who teach in that space and I work for university and I can tell you by and large it is not the focus in most CS programs it is the anomaly that should scare the living crap out of you speaking of fear if our if our devs are not learning security when they're learning how to code whether it's on their own or otherwise where are they learning it they're not and that's a problem Right? And to do secure code review does take time, but the flip side is much worse. So here's a weird idea. So let's turn this idea on its head. So consistency is a flaw. We are very consistent in our
business practices by and large. That is a thing. The problem is we are so consistent that it winds up being bad news for us. We are doing security as an afterthought. We're buying our blinky boxes. We're saying, "What's the next greatest best thing we can put in place?" I've spent the last few years saying, "We have plenty of blinky boxes. Let's get the most we can out of them instead of spending more money." And that is a weird concept to some folks. Let's work, you know, despite the users, against the users. like this is the theme that I see over and over and over again in my space. A lot of what I wind up and I do a lot of different
things. My specialty is DFIR, but I still work with a lot of folks in my environment who are not security people. They're not IT people. They're trying to get a business process done and they're asking me how do I do this thankfully and I say or they're saying I want to do X and I say well let's let's look at how we can do this safely. So instead of being the office of no I have turned our office into okay let's figure out how we can do that together and that has allowed more people to come to us instead of us being against them and we've already talked about the training. If the definition of insanity is doing
things over and over the same way and expecting somehow a different result, then it seems that doing security with all this fear is not a practical way of doing things. So let's think for a minute about this this Yoda idea, right? If fear is the path to the dark side and leads to anger and anger eats leads to hate and hate leads to suffering, why would we want to go down the dark side? Okay, once we fear it's going to lead you down that path. So even with the marketing and the stuff, you know, I I I've talked to other colleagues who try to scare their users into doing the right thing. It's not effective.
Everyone hates us as a result, right? Yay. So, this is from an older report that I found. Um, this is how security teams are often seen. We're doomongers. We are a necessary evil. And we are policemen. That's because we're understood in most cases. Your average person, whether they're a bean counter, whether they're a secretary, they don't know what the hell we do, because some of us are so far removed from those people, they never see us. They should see us. One of the reasons why I believe that I've been fairly successful where I am, I started in a support role. I let folks know they could rely on me. When I eventually moved into security, they
knew they could call me because they weren't afraid to call me. So, they would have an oops moment and they would do something wrong or they would not be sure and they'd pick up the phone and they'd send me an email and they'd say, "I know I can ask you because you won't bite my head off. What do I do now?" If we embrace that, it can we can use that to our advantage. So, this is, you know, kind of the same along those same lines. People think we're all about keeping the lights on, which to a certain degree we are. So, let me let me ask you this. What is the purpose of
security? Can you what? Continuous business operations. So, you're very close to what I'm thinking, but go
ahead. Yep. the the systems behind the business are safe. So So I will take I will take and go closer to what you were saying. Your job in security is to make sure the business keeps running because at the end of the day if the business isn't running why are you there? People will say well it's to protect the data. Yeah, but who cares? The point of the data is for the business. If the business isn't running who cares? So remember that part of your job whether you want to think about this piece or not in security is in fact to keep the business running. You need to understand your business and the way I got to know
my business was to get to know the people get to understand the processes and inject myself in kind and gentle ways so that I could be part of that and when business decisions are getting made people will call me. So, I love this definition
though. No one's ever seen that before. All right. Yes, there's the reason it's the top definition. So, I'm sure some of you have seen this image before, the duck rabbit, right? So, we need to change that paradigm. We need to change how we're seen. We need to change what we're doing. We need to focus on something other than fear. So, how do we overcome that fear? We have honest conversations. And we discussed with folks the risks of what they're doing in the context that they will understand. Your average user does not understand risk from a zeros and ones. They don't know about zeros and ones. They don't care about zeros and ones. We have to give them positive
messages, nonfear positive messages. If you want to change behavior and you try to do anything other than provide a positive message, you're shooting yourself in the foot. So, for example, and this is one of my favorites, there is a bitter argument over fishing tests. Now, for some entities, yes, I understand for some entities, fishing tests are required, and there's bitter arguments about fishing tests are stupid. They don't do anything. There's been research that shows that sometimes actually they can be detrimental. But what I will tell you is part of the reason why fishing tests are problematic is not because they're a fishing test. It's because the goal of the fishing test is to catch people.
Imagine if you went to a department and you ran a fishing test for them and you said, "Hey, 80% of your people did not fall for a fish." As opposed to saying, "Yeah, 20% of your people fell for this fish." Which is what is it you're trying to get them to do? You want them to not fall for the fish or at least question it, right? you want to communicate about that. The only way you do that is to get people to want to do that. If all you're doing is saying you fell for the fish, all you're doing is reinforcing the negativity. And negativity sucks and people will remember and that's all they're going to
remember. There's a tremendous amount of research that's been done uh on this subject. And um you know there there's uh Jessica um I'll think of her name in a minute. Uh Barker has done tremendous research on this subject. Uh and she has actually pulled resources from psychology showing why positive messaging is more effective than negative messaging regardless of whether you're talking about a fish or anything else in security. So we need to stop the us versus them to a certain degree. I get it, right? I'm in that us versus them now. I'm not with them. I'm part of us, right? That's a good feeling. But we should be embracing them as well because again, if the point of
security is ultimately keep the business going, well, that's kind of all of us, right? It has to be inclusive. Be patient. I get it. I want to tear my hair out. I was just giving a talk actually last week with a woman who who's a male worker, male room worker at the university. She's a very very lovely person who does not understand technology at all. And when she asks questions when I'm doing a presentation, I have to be extraordinarily patient, listen to what she says, and give her as short and concise an answer that essentially leads her somewhere else um during the talk because all of her co-workers know, right? This is not like just me. We all kind of understand that.
So, you have to have these techniques for dealing with the frustrating folks. If you tell somebody you're going to do something, please follow through. It really does matter. Again, I have people from all over my campus who come back to me and ask me questions because they know if they say, "How do I do this?" or "How where do I go for this?" I will get them an answer. I won't just drop the ball. I'm human. I will occasionally forget and they have to remind me. But it makes a difference. You're you are changing your rapport with those folks. It builds a community of trust. So this is what I was saying. You need to talk to folks at their level. If
what they understand is how to type memos or what they understand is, I don't know, how to clean trash out of your room, cool. Talk about it at their level. That doesn't mean talking down. It just means trying to find some common ground, wherever that is. Maybe maybe there's a TV show that you've watched that they've watched, right? And maybe there's some place there you can go with it. But either way, it's very effective by comparison. Don't do this. It's real easy to scream at people when you don't like what they've done, but it's not effective. But that doesn't mean we don't want folks to be skeptical. When I respond to uh to anybody who sends email to our
abuse queue, I always start with thank you for being skeptical and suspicious. Whether or not what they have sent is it could be legitimate. It could be something really bad. They might have fallen for something where money is involved. It could be terrible. But the fact that they reached out to say, "Hey, Houston, I think we have a problem." is that's worth acknowledging. So you want folks to be skeptical and suspicious and you have to teach them how to do that because folks with critical thinking, I'm telling you that is a tough tough skill in this day and age for folks to grasp. So you have to teach them in small ways. You have to
teach them to question all the things and play devil devil's advocate when you can right? But you need to have that additional evidence before you just blindly accept what folks are telling you. I love this quote. Does anybody know this author? A few folks, right? It's Yeah. So, so this is Sherlock Holmes. So, in the land of Sherlock, we have Sherlock and we have who else? Dr. Watson. So in a scandal in Bohemia, they have a conversation. They have a conversation on the difference between seeing and observing. So this is how it goes. When I hear you give your reason, I remarked, "The thing always appears to me to be so ridiculously simple that I could easily
do it myself. Though at each successive instance of your reasoning, I am baffled until you explain your process. And yet I believe that my eyes are as good as yours." This is what Watson is saying to to Sherlock. Quite so, he answered, lighting a cigarette and throwing himself down an armchair. You see, but you do not observe. The distinction is clear. For example, you have frequently seen the steps which lead up to the hall to this room. Frequently, Watson says, "How often?" "Well, some hundreds of times." "Then how many are there?" And of course, Watson does not know. And therein lies the difference between seeing and observing. And we need to teach our folks to observe, not just
see. And you also need to make sure you are observing and not just seeing. So question stuff on websites. Um, you know, question the legitimacy of email. Uh, one of the things that surprised the heck out of me was the fact that there are a lot of security folks, and I understand this may not be your role, but there are a lot of security folks who do not know how to read an email header. And I literally have a class on a talk on that where I've had to teach folks because I this was one of the very early things I did in the security space was uh beyond patching and cisadminy sorts of stuff. How do I know this email
is legitimate? Now, my father taught me how to send email at a command line when I was a little kid. So, I understand how this works, but a lot of folks don't. And if you don't know, it's worth finding out. It's a it's a it's a little tiny thing that can be really helpful when you're trying to figure out is this legitimate? And Microsoft gives you all these tools that don't always show you accurate information. So, it's good to be able to read those headers. So, if we have this healthy skepticism, we want to be skeptical of those fear-based marketing things. And that includes teaching your upper mucky mucks to be skeptical of that, too. And
not letting that fear run them out of town. Obviously, we all know the, you know, the negative hacker image is a bad thing. Share that with your friends and relatives. And I'll tell you, I hate the term advanced persistent threat. How do most advanced persistent threats start? They they walk in, but but how do they usually come into to a typical organization? How do how do they start? They're what? Credential compromise. But how does that start? Fishing, right? I'm an AP and I started with a fishing message. Yes. Yes, you did. And while that's a true statement, I think the media has gone, you know, batshit with the whole AP, you know AP thing. So, let your management know that
yes, legit APS are a thing that we need to be cognizant of, but that the reality is there's far less of them than there are of attackers who just do stuff, right? We have folks that get in the system and they do stuff and they're bad, but they're not legitimately an AP. So, let's get away from that. So, what where we have to go with this is this idea of nuance learning. It's very subtle. So, we partner with them. We try to find solutions together. And I know this sounds like a little bit of like business buzzword, but it really does matter. again, language they get. We know all these acronyms. Hell, I don't know some
of the acronyms we all use today. I have to look them up and I've been doing this a long time. They don't know the acronyms. If you walk in and start talking about that stuff, whether it's above you, below you, or next to you, we need to get away from that. Again, the us versus them. And focusing on who didn't click the link, the positive reinforcement is absolutely key. Then you need to go back to basics again. The whole point is we're here to keep the business running. So let's know where our sensitive data is. I mean we I think most of us understand like we need to go back to understanding the stuff we
are protecting so that we can keep the business running, right? So go back to those those fundamentals in operations. Where is that data? What is it? How do we get there? and removing the easy ways in. That's probably a good thing. RDP, how long has RDP been a problem? Right. I'm hearing Jesus. Yeah. Forever. Right. What are they using now instead of RDP? Not well SSH. Yeah. But but that's not where I'm going. RDP is a built-in mechanism. Team viewer, right? So, so if I can't use built-in RDP, but my company uses something like Team Viewer and what's another tool that's helpful in the Microsoft ecosystem to be very useful at helping, but it's built in now. It's not
RDP. Quick Assist. Yeah. So, guess what the bad folks can do with Quick Assist. I have a friend that just did a whole talk about that and it does not log particularly well. Get that crap off in your network. Get rid of these easy ways in. Know what those easy ways in are. Obviously, standard stuff, log monitoring, fix the quote simple things if you can. Don't let the goal of perfection become the enemy of good. I'm sure some of you have heard that. Which means you don't have to do all the things. Not all at once. One of the things that drives me crazy, how many of you are familiar with canary technology? A few of you. How many of
you have heard canaries are awesome, but we're not mature enough yet? Yeah. So, that's I'll just tell you straight up that's Canaries are one of the easiest, most proactive things that you can do and just stick them in your network and then go back to what you were doing. They're nothing. Canary tokens are free. Just do it. Don't worry about your maturity and you have to do this before you. No, don't go for perfection. Just get better. So, we need to get back to basics in the education space. We need to integrate security into the curriculum. Some places are trying to do that. You know, um I'm certainly an advocate for it in my space where I can
be. Um, we want developers to be able to evaluate their own designs and communicate security issues. My husband, uh, as I mentioned, is a developer and he has become a security advocate now in his own space because he spent enough time around all of us to kind of get that that's a necessity. So, in terms of moving forward, change is hard. You've heard this before, right? You come from these conferences and you have all these great ideas and then no one wants to hear them because infosc is a disaster and no one has fixed it. There's not been an aha if we just do this one thing. Well, it's because change is hard. But it starts
with each of us in some little way. It's not trivial. We're trying to change people. We're fighting a bias and that's tough. people underestimate the likelihood of bad things. So, they're more inclined to not care and just do them anyway. And that is that is part of the research that uh Dr. Barker, who I mentioned earlier, has done. So, this is a book that I read a number of years ago having to do with trying to change people and trying to change them from the bottom up instead of the top down. When change works, it gives folks direction. It's a good thing and small changes can snowball to help you get there. So, you know, how do we eat an elephant?
One bite at a time, right? Move away from the silos. You get a partnership and you get a partnership and you get a partnership. No matter what your role is, whether it's, you know, security all the time, every second of the day, you're doing it in some capacity and security is part of your job. Whether you're a developer, it doesn't matter. Partner with the community outside of it and infosc. Become that neighborhood watch. You're already here. So, you're partnering with us and that's awesome. Now, take it back and partner with your organizations and partner with the young folks. How many college folks do I have in this room? Awesome. You are the ne that part
of that next generation. And you need to understand that we're here to mentor you. And if you reach out to one of us and we're not helpful, find someone else because you will get people who'll be like, "I don't have time for that." Don't listen. Just go find somebody else. And those of you who are my age or older, and FYI, I'm gonna I'm gonna tell you a little secret. I'm 51. Okay. So, those of you who are my age or older, be here for these folks who are in school, who are try or, you know, trying to learn. They're maybe changing careers. They're usually eager to learn. So, let's show them what we know. How do we handle over that baton?
Well, we can partner with them at Bsides. Hello, we're here, right? So, talk to them, get to know folks. There are also places like coder dojo and there are cyber camps. We used to run one at UB although um I think we finished that out last year. There are projects like Odyssey of the mind and hack for kids and of course straight up mentoring. No first is you mean the the organization or Oh yeah yeah yeah right. Yes. Yep. So lots of opportunities including first. So yes, lots of opportunities, just depends on where you are. So I have a a couple final thoughts here. Our number one job in security and the reason we are hired to help keep the
company going is not to adjudicate. We're there to educate. The more you can educate, even if you don't think that's your job, part of your job, I'm telling you right now, is to educate. and educate folks at home, educate folks in the office, educate folks at your game night, cuz I know a lot of you do that, too, cuz D&D is awesome. Um, you know, learn what they know. So, this is a a very short story. So, for a little while, I worked for a company that had a bunch of folks who literally did all kinds of military work. And one of the things that they used to do, well they still do. They just I
don't work there anymore. Um they were they did rocket work, right? So what do these folks know about? Well, they know about physics and they know about rockets and they don't know a whole lot about PCs. So it was really cool to learn about rocket science from rocket scientists and teach them what I knew about making their jobs better. We can do that. So I love to end with this quote and I'm also going to show you I wrote a book called the active defender for so for those of you who are in the defense space the the core of the book talks about thinking in defense like somebody who does offensive work because if you
don't do that then you're missing half the story. But I like to end with this quote. I may not have gone where I intended to go because as I mentioned I started out in the support universe and in fact before that my degree was in music industry but ultimately I think I wound up exactly where I needed to be and I will end with this in case anybody is interested and I think we probably still have a few minutes for questions. Yes. No, we're out of time for questions even. Okay. I will be around the whole conference until late Sunday. So feel free to hit me up if you've got any questions. Thank you so much to uh the
conference h for having me and for all of you for being here. [Applause]





