Aarti Gadhia: There is no security skills shortage!

Show transcript [en]
[Music]
[Music]
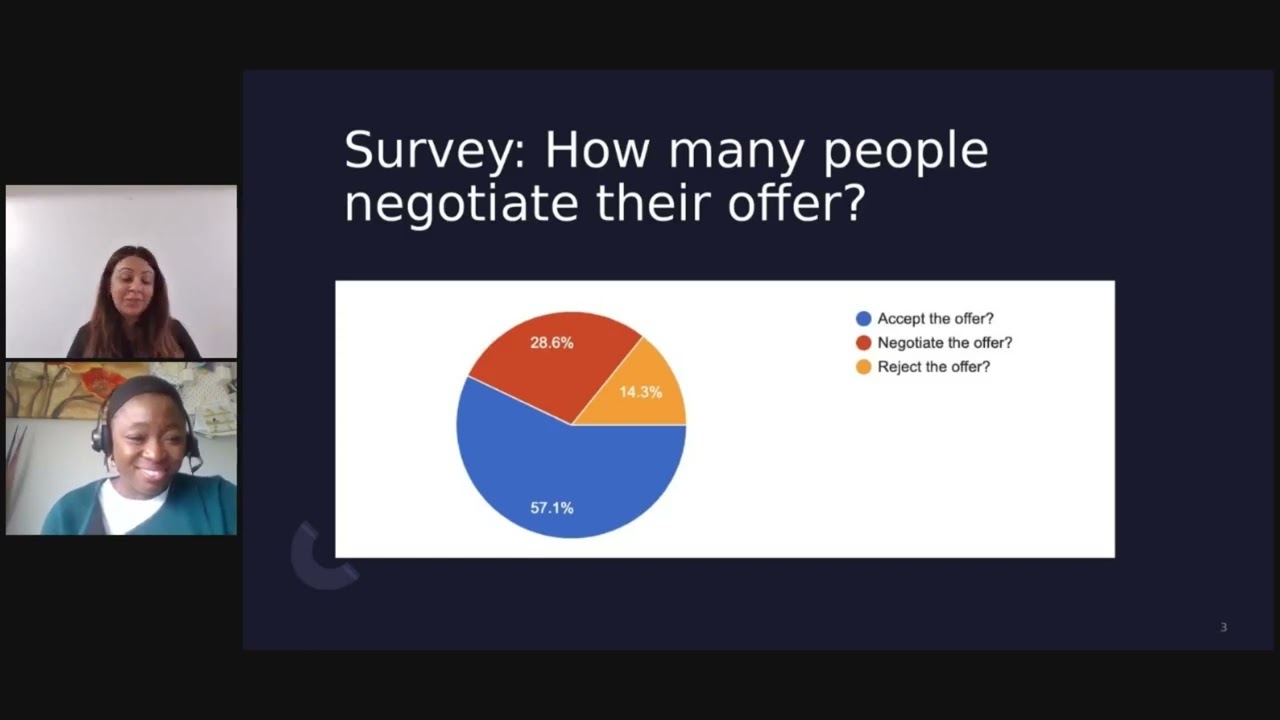
and greetings to all of you around the world in any other language that i missed i'm here as you can see with my stampede gear on we've missed stampede but who says we can't create our own virtual experience right working from home is the new norm for me as i've been doing this for over 10 years but not being on a plane and flying to calgary to attend this conference is definitely the new norm so i do miss that part before we get started as you can see on the side i've put a poll there and would like to hear your opinion so the three questions there if you can just select one of the choices and the first
question is is there a cyber security skills shortage you've got two choices yes or no the second one there that you can see is i'd like to hear how you join the cyber security industry is it that you've always wanted to be in cyber security from a very young age and this has been your dream job is it that you have a completely different background and fell into this uh like you studied something completely different and you fell into cyber security by accident or is it that your family or your parents or your friends were in this industry and therefore it was a natural fit for you and if none of the three apply choose
number four and then the last question this is a little bit of an interesting challenge for you all um and for us too uh so which of these three words are you tired of hearing first one covet second one virtual third one is 20 20. so the challenge there is to make sure you're listening uh throughout the presentation uh a bit of a challenge for us is throughout this whole presentation myself our lilithia and megashi we are not allowed to say that word whichever you pick and if we do by any chance by accident uh we know you're listening put it in the chat um you know once we've said it and remember only the first person
that uh catches us saying that word is the one person who will get something uh from us so we'll send you a private chat um get your email address and we'll send something via email and then the rest of you if you do hear us say it uh after that first person sorry your duplicates so you don't get anything uh panelists are you up for the challenge
so game on so thank you all for your participation on the poll and joining our talk should hopefully joining our talk there is no cyber security skills shortage in terms of agenda for the first 10 minutes after i introduced myself i'll share the changes we've seen so the rise of the gig economy and will explain the term crowdsourcing through some examples that i'm going to share i'll also share some data and some interesting statistics that help us determine if there is really a shortage or not and then we'll move into 30 minutes for you to hear the journey of three hackers as they share some tips so a bit about my background my name is
arti gadia some of you who already know me was born and raised in kenya africa i studied financial economics in uk and 20 years ago if you asked me what i wanted to be i'd have said a stock broker which is why i studied economics in 2004 my husband and i moved to canada and as a new immigrant i just wanted a job right i had to take a step back in my career and there was this entry-level position for an anti-virus company back in 2004 and that's how i entered into this industry into cyber security outside of my role i'm passionate about influencing a change to close the diversity gap in stem and in
leadership and this led me to startups stand out to lead to increase diversity on boards and she chapter sharing her empowerment chapters to influence a change within the organization to bring awareness to the board this year i was excited to receive the top 20 influential women in canada security award by it world and with sacra and this has helped me be a voice make a change and pay it forward as you can see i currently work for bakra i'm based in vancouver and if you saw my linkedin post titled full car roti you know that i love cooking the pandemic has hit the economy hard unfortunately we've seen massive layoffs furloughs businesses forced to close down and
certain industries have been affected the world has changed and the way we do business has changed it doesn't look like this anymore for some of you working from home is new some love it some hate it this has introduced the concept work from anywhere companies are shifting their approach and this has led to a rise in the gig economy and organizations are going through a digital transformation while competition has increased in the gig economy according to an article from ibis world upwork has seen an increase in 50 percent in freelancers on their platform since this pandemic instacart and online grocery delivery service has hired 300 000 freelancers to cater for the increase in demand and companies
have shifted from a full-time job offer to multiple gigs side jobs and temporary employees in order to save wages and benefits as they try to recover i also read an interesting article whereby cyber security workers were taken off their duties to help with i.t related tasks as organizations were faced with supporting employees to work from home to keep their businesses running we're all familiar with these tools as they are now a household name that you've been implementing internally or already have at the same time during this pandemic cybercrime has multiplied creating a great opportunity for unethical hackers and online scammers after all cybercrime is more profitable than global illegal drug trade that's 600 billion versus 400 billion
according to an article i read on yahoo finance nearly two-thirds of canadian companies failed to report cyber breaches during cov id whether there is a pandemic or not to echo a quote from roger grimes every company will be hacked the article from isc 2 shared that their 2.8 million professionals in cyber security in 2019 and we would need another 4 million to fill that gap so how we're going to find more is the problem that there is a shortage in cyber security professionals or is the challenge we can't find the right talent crowdsourcing and diversity is helping us fill that gap and that's what i'm here to sit and tell you so let's try and understand what is
crowdsourcing a quick google search showed me several definitions and a simple way of explaining this is the practice of obtaining information by leveraging a crowd either paid or unpaid the term crowdsourcing was coined in 2006 but has been there prior to digital age crowdsourcing and outsourcing is different crowdsourcing comes from a less specific more public group whereas outsourcing is commissioned from a specific named group though it can take a lot of moderation and feedback there's a ton of benefits that far far outweigh the negatives when it comes to crowdsourcing it improves cost speed quality flexibility scalability and of course diversity so let's take a look at examples of successful models that leverage this approach one of the most innovating companies
amazon for those of you who have alexa at home it's funny when alexa says when you've asked a question and likes to say i'm sorry i don't know that one well you can help provide alexa the answers and earn points each time your answers are used by alexa this is another great way to expand alexa's knowledge through a crowd and build its data repository last month an article from voicebot.ai shows that alexa crowdsourcing has gone global and it arrives in the uk another interesting app so relevant for today is mask count app there are quite a few mobile apps that have used crowdsourcing techniques for contact tracing earlier in october mass count launched their app which is a hybrid of wazes
crowdsource traffic info and the functionality of tinder you swipe right if someone's wearing a mask and left if they're not it's collecting scientific evidence that may help us understand how to reduce the spread of coven and you can use this data or it teams can use this data as i read an interesting article from computer world and it explains how if a company detects that a particular neighborhood has low mass usage and high infection rates i.t teams can alert employees and assign that area a low safety score so for example i live in delta and if i receive that alert in a neighboring city i'll obviously avoid going to that area because i'm heading into work i could
risk my colleagues and spread within the organization this will now enforce businesses in that city to aggressively enforce everyone to wear masks and this increases protection for all so how are we going to leverage a successful model into cyber security and what are the benefits well cyber security is fundamentally a human problem someday technology will be able to mimic and predict human creativity but that's not coming anytime soon unfortunately the attacker is focused on results they get nothing until they are successful i tried googling this and i couldn't find any stats but one thing for sure is there's an army of unethical hackers and that's why they are and will always be ahead of the game
and to compete against an army of adversaries we need an army of allies by leveraging a crowd you're creating a force multiplier you're able to access a diverse pool of talent with different skills backgrounds and experience to find high risk and high impact vulnerabilities you're using the same creativity your adversaries are using to attack you so why limit yourself with hiring two full-time employees when you can leverage hundreds of ethical hackers another interesting fact according to pew research last year is there were 29.5 million women with a bachelor's degree versus 29.3 million men in october i ran a fireside chat with three women from twitch hp and on lifelock and all four of us fell into cyber
security by accident we had project management we had engineering we had accounting economics and we're all today in cyber security in fact some of you know selena from when she worked at finning her background was actually hr to solve the four million shortage in cyber skills the challenge isn't that we don't have enough cyber security professionals the challenge is we're limiting ourselves and we need to look beyond the traditional way of hiring crowdsourcing and diversity is solving that problem and now i'd like to move to the next section of the talk so you can understand the definition of a hacker and how this relates to solving the cyber skills problem when you hear the word hackers the first
thing that comes to mind is that they are bad in fact if you see movies today they show someone um you know wearing that hoodie hacking the system and in that scene they say yes i'm in i have access so just like in the movies there are two types of hackers ethical and malicious and the difference between the two is the intent so you're actually now going to hear from three ethical hackers as they share their journey tips on how they became researchers also known as bug bounty hunters and how to be inspired in this journey so let's start off with introductions and perhaps let's start off with pharah if you can quickly uh introduce yourself i know right now
you're based in india right and it's past midnight for you right because i can see it's quite dark behind there yes and it's a friday or i guess saturday early morning so tell me a little bit about yourself and how you joined this industry all right first it's also diwali so happy diwali to anyone who's watching um i'm gonna start by introducing myself and i'll answer one of arthi's earlier questions so i fell into cyber security completely by accident i was pursuing a degree in mass media in the second year of my course i found myself having a lot of free time so i decided to do a course in ethical hacking it was a really basic course
and at that time my idea of hacking was just what they had shown in movies so i decided to go for that and then i realized that it's much more than what they show in the movies and i actually got really interested and went much deeper into it and i actually ended up graduating in mass media so i have that degree lying around but cyber security is my career fantastic thanks for that background lithia let's move over to you we met a year ago literally this time a year ago during os vancouver one of the meetups and shortly after you joined the uh i mean after we met you joined the os vancouver uh committee to help
organize events and you recently spoke so tell me a little bit more about your background and how you got into cyber security sure thank you alti for this opportunity hi everyone so this is lillipia so i would start from my undergraduate i have done my computer science and undergraduate and after that um i decided to choose like a cyber security field but when i went to my parents and said i want to be an ethical hacker i want to choose this stream they're like are you crazy or do you think about the future opportunities etc etc many more questions so i was like okay maybe i'm wrong because i don't have any uh complete in-depth knowledge on cyber
security so i compromised myself into software testing and i worked for two years and um while i was working i was finally looking into cyber security opportunities and then i got to know that i can still uh move on to it so i started my uh masters in cyber security here in canada so i i graduated recently while i was doing my master's i was into different platforms like awas for she instincts isaka and all these which completely driven me like a more interesting way of cyber security so that's how i am into cyber security and then um i started my uh role as associate application security engineer at background as an internship and apparently i'm
doing the crowdsourcing which is super exciting for me that's my journey of hacker fantastic thanks uh thanks for that introduction um rigakshi we actually met during this pandemic in may uh i was just looking this up yesterday and i can't believe it feels just like we've known each other for such a long time and it was during the iseca vancouver she leads tech uh one of the breakout rooms that we met and you probably just live half an hour from me but we still haven't met physically but we've had so many conversations um virtually um and it's like i said it just feels like i've known you for such a long time so help me understand a little bit about
your background and um how you got into cyber security hi arty thank you for introducing me and it's indeed a pleasure to have met you uh at chili's tech uh well hi everyone i'm rigakshi i also work with arty and others in my panel at vakrat and growing up i always wanted to be a doctor and many other things but then i realized that it would take quite a long time to graduate in those fields so i started getting interested in computer science and i did my computer science engineering back in 2013 after which i joined uh a company called accenture worked in different fields like devops business analysis and finally got into cyber security
getting into cyber security i realized that it's not just a hot skill right now it's a necessity it's a necessity to bring in a cyber safe practice in the world and i really enjoy this stuff getting into uh the computers of hackers who have the companies for their wrong reasons is a great thing to be in well uh outside of work i enjoy dancing and i really like energetic music i feel that it gives me a lot of uh positive energy yeah it's it's been pleasure to be speaking here uh for the very first time fantastic yes all four of us are first-time speakers at b-sides so thank you besides for this opportunity so before i head over uh to these um
three researchers just to sum up what i just covered and how it relates as i've highlighted to you and you've heard from pharah lilithia and rigakshi and myself many of us landed into cyber security by accident therefore things to think about you need to rethink about your recruitment strategy and how you can attract a diverse group into this industry so as you can see whether it's red hat blue hat green hat or whether you've studied hr or cyber security or whether you want to be a stock broker or a computer scientist or engineer each and every one of us can actually join the hunt and solve this problem in simple math there are 7.8 billion people in the world
i just shared earlier on 60 million graduates last year and all we need is 4 million to fill the gap so i hope what you can see you can all see where we're going with this talk and why by leveraging a diverse crowd diversity and crowdsourcing there is no shortage in gaap so i'm going to have this over to mr gakshi lalithiya and farah as they're going to share their tips and how they became researchers we're actually over to you thank you arthe for introducing me and uh i i'm as i said i'm glad here just be speaking at understanding uh a bug and its risk so uh today uh as i'm working at bukra i'm
really interesting to tell people how uh the risks involved in bug hunting can affect the bug hunters and how an application uh bugs can really be a business risk and why not uh so the agenda for our next few minutes will be how discovering an application is similar to meeting someone new exploiting of security bugs and how the mind of a security researcher should work the discovery phase of birth hunting is very similar to meeting someone new it includes two parts parts the first part is start of an actual testing just the dis by discovering someone new seeing someone's body language this stage covers information gathering and scanning then network port and service identification is conducted to
identify potential targets in addition to port and service identification there are used information and on target networks well security bugs can lead to something like this security bugs are completely different from testing bugs as they are focused on actin functionality as opposed to testing during the software development life cycle which focuses on intended functionality testing can definitely establish the presence of errors but can never confirm their absence exploitation of security flaws can lead to ransomware attacks where the attacker demands money to not leak business secrets or stolen data some other security flaws can lead to data link in such cases there are there is no extortion but some private information appears to have been leaked
for users of the business this may include credit card information bank details birth date or some other important ids phishing attacks are most common ways of attacking people and are getting combined with social engineering these days some attacks lead to loss of customers due to destroyed user interface which might lead to loss of revenue and in some cases complete shutdown of business many common attack scenarios involve exploiting one vulnerability found in an insecure application an attacker can sometimes stay on your network much more than the estimated time our aim is to party party and pardon just kidding our aim is to protect businesses and individuals by finding the and fixing exploitable security vulnerabilities before the bad guys do
let's discuss more about how mind of a security researcher should work discovering the functionality is the first phase of bug hunting most often this stage can be taken care by lots of free tools available online you can use tools like burp suit fluff and also try labs like pentester labs and glass to clear your basics given the fact that cyber attacks are the biggest threat to an organization's data and information a vulnerability which is technically valid occurs to do anything malicious is not really considered a business risk uh try thinking what malicious intent you can have to be an effective researcher trojan horses or worm are examples of gaining access to back door once they have entered your network they
have the capability to infect your connected networks and devices the worms these are are generally uh you made by exploiting sql injection and excess and a few other types of attacks try to think out of the box and gain similar back door entries if you were the hacker think about ways of escalating privileges by bypassing some security features of the application think about intercepting the communication between the client and the server and how attackers can view the data not intended to be viewed by them let's take a simple example of school application where students submit an assignment and the teacher grades them here we have the privilege escalation bug if the student is able to still edit the
application or the assignment even after submitting it to the teacher for dates well last but not the least remember to never publicly disclose a vulnerability everyone has different journeys as a hacker some people start the certification like ceh oscp and others and some people come from a defensive side of security like me even if you are not a hacker you still need to follow cyber security trends as of now in 2020 increasingly dependent we are getting increasingly dependent on iot devices with the limitation of security testing remote work is a lifestyle and a new normal data is increasing every day and so are its security concerns so i'll bug hunting well maybe start with an authentication
logic bug for instance when an application is logged in in two different browsers like google chrome and firefox if you change the password on one browser the application should be locked out of all other browsers you can report this doesn't that sound interesting well in 2020 we have had the skill shortage in cyber security by crowdsourcing of course it takes the crowd to defeat the crowd there is absolutely no educational background required just a desire to learn technology works to learn about hacking you can start with tools like burp suit over zap and n math uh which are used for intercepting requests and uh in early application elimination and they are very useful to learn
used attacks i follow lots of youtube channels like bug ponty thursday by stop it's stock parahava which is also who is also on our planet today uh the last speaker of the day and i believe that increasing knowledge is always much more important than learning tools so just show your malicious intent today we would like a lot of comments here if you were a hacker would you like to think and why uh i would like some participation from my speakers as well uh so um what do you think i can think um because i love cooking so i would love the secret sauce and recipes for some of these master chef cooks out there so that's what i would
like to hack for sure if i was yeah yeah audience just keep commenting we would love to know you you know i would like to hack my professor's account to get good grades what about you well i so i would hack some uh flight website and then just send a lot of miles my way so uh now lelithia who is also my teammate at background will present on how to search for a bug bonding program and report a bug and start practicing hands-on so over to you guys thank you thank you for handling it to me so uh hi everyone so i just want to say i'm the beginner in the crowd the word i say the beginner because uh i
got to know about these crowdsourcing options when i was in my last semester when i was doing my master's so after i thought like after masters i i should search for a job what are the options full-time opportunities all these but i don't know until my last semester that there is an option called crowdsourcing so once i am into the crowdsourcing then i really enjoyed it so i'll share my journey and i'll tell you what's happening in the crowd so to be in the crowd what you need is like a question yourself about your interest i would say your time investment and your interest is directly independent to each other so if you are interested definitely you
will invest more time in it so crowdsourcing has an option for continuous learning every day it's like a new challenge and every day you have to learn something you will be learning something so also the other thing i have i learned from crowdsourcing is being patient because uh we cannot get the bug or we cannot get succeeded in crowdsourcing right away because it's a huge crowd and the competition is more so we need to check how uh we need to wait for the right time but don't give up just try focusing on it and apart from that you can have an option for balancing your life so even right now we are we are doing with internships or
full-time jobs or whatever the domain you are in you can balance the crowdsourcing option that's a very good thing uh in crowdsourcing an investment in to be in the crowd investment is completely zero you don't need to invest anything just your time and some of your interests that's it and all you need is like a laptop and a good wi-fi network connection that's it so general confusions which i have came across uh along even with my friends are like what about the opportunities in marketplace for cyber security do you have any suggestions for new grads yes crowdsourcing is an option here they can obviously choose and there is no um gap to fill out it so let's begin
what's happening in the crowd for crowd sourcing so crowd sourcing platforms are something similar to bounty programs which are completely free and you don't need to pay anything you just need to register it there are a number of platforms you can just register it and uh start hunting so how do you start hunting so start from the informational bugs and then move towards the critical findings which uh i applied because if i directly go towards the aim and target for a critical bug and to get bounties or something like that definitely it would be a message because i don't know what's happening exactly in the cloud so always start from the low level bugs low level bugs are really similar as
merdakshi was saying just like if a session is open if you browse on two browsers for any of the program then yes it's a bug once you ask once you log out in one session other session should also get in if not it's a bug something like an informational bug you can start with so i i'll show you how the crowd the sourcing platforms and the programs look like so this is one of the platform i have chosen and if you can see there are a number of programs all these programs are different like it has retail hospital everything health care at different domains so you just need to see the programs they offer the bug bounty
programs if you can see these are all the programs and you have an option called something like submit report so submit report is like once you identify a bug you need to submit the report let's these are the programs with different domains so let's open one of the program and see how it looks like if you can see here uh it asks for login to check eligibility so what happens is like um the program brief generally has uh the reward range what type of reward they are getting for this i mean where you are sending a vulnerability targets that you need to search and out of scopes all these information credentials how to do how to enter into the system what
platforms you need to search inside this uh specific program etc etc so once you are do it then you're gonna um get some um priorities like that so if you if you can see here eligibility for this program if you submit more and more bugs and you have a weightage for your profile you will get invited to the private programs as well where you can test submit the report get bounties and all these so it it's like a continuous process and every program as i said it's like a different uh opportunity like some is like you can you cannot find the same bug and same program so my suggestion would be like every platform is having um a vulnerability rating
attacks on me which is like a brief it shows so all you need to know about is the overs top 10 vulnerabilities what you have so in those top 10 vulnerabilities each platform is having some uh vulnerabilities if you can see here broken authentication and session management which is also having some vulnerabilities which use specific vulnerabilities so which is varying from p5 to p1 so p5 which i considered as a low level or informational box and p1 are the critical ones so it depends on as i told you start with the low level so you can just go start with p files which is very simple it's like a logic kind of thing uh how it's attacking how the what's the
security impact all of these things you can think and start with p5 and then move on to b1s which are like a challenging task for each of us so while you are doing these bug bounties and uh hunting these in the platforms make sure you have a checklist there is a obvas checklist which is suggested but also you can make your own checklist and create for each and every program write a test name what kind of vulnerability you have tested because for one program you need to test like any number of vulnerabilities you don't know which one would be uh the valid vulnerable so definitely every application is vulnerable um we can see it once you are into it
you will definitely know oh wow these many vulnerabilities are lying in this specific program something like that so start doing manual recon that's my suggestion because initially when you start doing the manual recon you will expand the attack surface so if you have a target just uh try doing a manual analysis what's happening or why it's not working what are the sub domains what are third parties what are the hidden points hidden links hidden directories all these so if you can do the manual recon then even if you start with an automated tools it will be easy for you so directly if you jump into automated tools definitely there will be a confusion so start with the manual recon and then
go with the automated tools which will help you to automate the process of course so you need to have a burp suite zap or whatever it is but it is completely independent of your domain it doesn't matter at all whatever your educational background or whatever your mind is so other important thing i would say is like reporting a bug because i reported few bucks last month and uh the main issue was uh being most of them are being not applicable something like that the reason being that my reporting was not clear so believe me reporting a bug is a major thing while you are doing a bug bounty programs so be quick and clear the reason i said
quick is because it's like a whole crowd and everyone are free to hunt at any time so independent of the time zone independent of the location so uh if it's like a huge competition you need to be quick and it's not only be quick be clear so because once we submit the bug it goes to the triage theme and then it goes to the program owner they have to check they have to understand that yes this is a valid bug and this affects my company if i don't fix it so that's how they have to understand it's the only way we can do it is by while reporting so make sure you're quick and clear in reporting
always mention a security impact like as an attacker what i can do if this is not fixed why this is a bug that's where you need to uh answer in your reporting and valid proof of concept you need to attach the proof of concept by making a video or screenshot to prove that this is a bug so just see how reporting uh submit reporting how it will be so summary title make sure you while the title itself is clear so that's right team or the customer understand that okay this is the bug they have identified and the target make sure you choose the right target target is nothing but which scope you are testing and technical
severity which is must based on like other vrts that i have shown i have shown you for a broken authentication right so you can choose which one is in it so that you can assign it for whether it is a p3 p1 p2 whatever vulnerability details like which url you have identified the bug and replication steps are most important because in order for the triage team or the customer to replicate your finding you have to be clear what you have done and step by step procedure and then you if you are doing with an automated tools if you have captured any requests or responses you can paste it additional information will be the security impact and resources and
what extra can be added and attachments is not like your poc proof of concept and if you are joining with another hacker yes add them and submit the repo vulnerability that's it so it's just so simple process which you can do with even couple of minutes in your free time but definitely it will be an asset for your uh future for cyber security achievements uh so this is my old submission first time so you will have some achievements hall of fames added to your profile which you can add it to your resume and you can say i have hunted in this program there are a number of programs programs are nothing but i would say
websites or all these kind of things so for this one uh best practice i would say web code and oversat these two are web applications which are vulnerable and it's a free source free resource that's available in the market so you can just directly a login site just setting up is very simple you can just need to have a virtual machine or for a juice swap it's like a hiroko you can use and you can just log in and practice hands on these like these two applications will help you to check how to identify a valid bug in real time so i i use them a lot so i said i'm suggesting you or to practice on it so i conclude that
so there is no shortage of skills uh for cyber security also there wouldn't be and this should not be let's begin the crowd there is already a lot of crude and we need people more people as artists are saying so let's begin the crowd join the crowd and try hunting these uh crowd sourcing our platform and we can uh achieve this uh achieve the new uh cyber security skills shortage so by that with that being said uh after you have so now you have learned about how to do the black bounty programs how to search for it so after you have learned all these what is the next steps that thing going to be explained by
farah now i gonna hand over to her thank you lolita so i'm gonna talk about uh what you should what is the next step you should do after you've learned everything that regards about because in bhagavanti you might find yourself needing a lot of inspiration so let's look at what the sources of these inspiration are so uh the first source is write-ups and research papers written by some amazing hackers and then we have another source of inspiration which is the twitter community around bug county so let's go to the first source of inspiration so what are write-ups so write-ups are basically detailed walk-throughs of what the hacker's mindset was like when they found a bug
so how did they find it why did they think that that parameter was vulnerable how did they go about exploiting it and what was the root cause of the bug so for example you can see that someone wrote a write-up about posting gifs as anyone on facebook and then someone wrote a write-up about 10 interesting vulnerabilities that they found on instagram so reading these can be a great source of inspiration formative and it will make you want to get up and hunt and another so uh one place where you can find write-ups is uh following some amazing hackers blogs so you have uh ron chan file descriptor and uh orange sci i love these blogs uh they
write some really technical uh a little bit advanced blogs but uh they're definitely very very inspiring and very very informative you can easily find them uh from a google search or you can use these links that i've mentioned uh all right so next let's go to the next place where you can find write-ups so the next place is pentester.land so you just go to your browser and type pentester.lan and you'll get a list of these bug bounty write-ups so they have write-ups all the way from 2012 to 2020 so imagine that you've just learned a bug called idol from the web application hackers handbook but you don't know what it looks like in real life so you
go to pentester.land and you just type an idol in their search bar and then you find probably hundreds and thousands of write-ups that people wrote about actual idol vulnerabilities that they found in actual targets so that can be really inspiring again very informative and gives you an idea of what that bug looks like in real life and how you could also exploit it okay so let's go to the next source now we have research papers research papers are also written by hackers but they are a little bit different from uh from write-ups because they are unique uh methodologies and uh unique and new technologies that have not been explored before so you will not find
these uh methodologies in uh books or older papers and they are also performed on newer technologies and newer technologies uh also means more secure technologies so these are a really good source of inspiration and again it will get it'll help you uh kind of be on your learning uh learning journey all right so let's go um so let's talk money because a lot because a huge reason uh why a lot of people enter bug bounty is money right so the money part you will see on twitter so on twitter we have a lot of bug bounty hunters that share how uh how much bounty they've received so it can be a small amount it can be a huge amount
but they're constantly sharing it so it's again a huge source of inspiration for me i feel and also for a lot of people when we see people earning a small amount or anything they also feel like getting up and hunting so finally let's hunt you can do it all right so to summarize the talk a little bit we i'm gonna talk about what uh action items you can take as an organization uh to implement crowdsourcing uh in your organization so first uh you should consider these aspects of crowdsourcing was versus a traditional security model so like rt said diversity scalability flexibility these aspects are a lot more present in uh crowdsourcing than a traditional security model
next you should re-evaluate your recruitment process so if you're not finding enough cyber security professionals through your traditional method you should consider going a little bit um going a little beyond because as you heard that all of us come from quite different backgrounds next you can expand your reach so change your criteria a little bit and concentrate on looking for people with skills than just looking for qualifications because uh as an example artie mentioned about selena her background was hr and her skill was problem solving and now she's in cyber security and the last action you can take is uh higher uh don't uh be bound to an office uh or don't be bound to a
location because uh the pandemic has proved that you can work from anywhere and you can work 100 remotely so for example if you're hiring if you're looking for someone in vancouver you can probably consider consider hiring someone from calgary as well right so next uh let's look at action items as a researcher so like mega she said learn tools go ahead with certifications or books and go practice on pentester lab and seed labs they're very hands-on and focus on learning over learning tools next as lalithiya mentioned you should know how to search for a bug bounty program learn how to report a bug properly and practice hands-on again and lastly as i said read a lot of
write-ups read research papers and be active on twitter because that will really inspire you all right so lastly i want to conclude by saying that the mind is just like a muscle so the more you exercise it the stronger it gets and the more it can expand so there is not a skill shortage as such you just have to be in a constant cycle of learning and that way you can be the crowd and fight against the crowd of unethical hackers and uh initially we did a poll and 67 percent of you said that they think that cyber security has a skill shortage right so i hope from our presentation you understand why we think that taking an
alternative approach may result to that shortage not being there so finally um coved hello are you still with us okay that was just a test to see how many of y'all are still listening this is the end of our talk and pete pete patel was the one uh who caught us the first time in arty's presentation so we will be reaching out to you uh please write your email address in a dm to any of us and we will reach out to you so thank you for coming to our presentation uh this was a really good opportunity and thank you have a great day ahead well we've got one minute left any questions from any of you
don't see any questions thank you for all the amazing comments and uh thank you for this opportunity for us to present it has been fantastic as we prepared a few weeks ago and it's been fun right yeah everyone this is thank you everyone for your comments