Workshop: Recon with Women Hackers
Show transcript [en]
[Music]
[Music] i will get started i like to start off with my greeting which is jambo namaste bonjou konichiwa and greetings to all of you wherever you are in the world it's friday morning for some of us friday evening for some of us or afternoon wherever whatever time zone you are welcome and thank you for joining us this morning calgary yes please we would love audience participation so please uh we are a fun bunch here we it's friday things didn't work in the start but hey we want all your participation to get us going so please in the chat from each one of you feel free to share where you're from where you or where you
work and uh maybe a fun fact about yourself and as we do that i'm proud to um have you uh make sure you're okay with sharing because i can't see yeah uh just so sick no worries i am um i'm excited and proud to be uh with these amazing women here in cyber security that i've worked with um over the last i would say 18 well maybe 18 months or maybe less than 18 months i think we all met during the pandemic except lalithi i met you a little bit earlier at uh maybe in 2019 says when i met you at oh asp so super excited in terms of how we've connected we've all worked at bug crowd some of us are still
working at bug crowd we're just so excited to work um with three of you with that we are we have an exciting workshop there's going to be a lot of interaction you'll be divided into some breakout rooms uh that you'll see um but i'd like to start and kick this off with introductions and perhaps let's get farah to start her introduction so hello everyone i'm farah and i'm from mumbai india and it's night over here but you can't really see that so i work at crowd as an application security engineer and i also make youtube videos on my channel so go and subscribe and i in my free time i also do some bug bounty helps me be technically active
and learn new things as well so let me now pass it on to mukakshi hi everyone i'm nigakshi i had i i met all these three amazing women at buck route about last year i'm currently working as a security consultant i'm so excited to speak at cyber security awareness month uh i'm sorry i'm just not able to share on time uh let's let's start that's okay we we carry on that's okay no problems yeah are you able to see my screen now yes we can so yeah if you want to continue with your introduction and then pass it over to lilithia yeah yeah lolita go ahead and you're on youtube
you can give your introduction now can you hear me you you're mute can she hear uh you and still can hear you can you hear us yes but we can't hear you great hey um this would be such a challenge to type things i was just talking about this yesterday that you know i'm okay to lose uh powerpoint sharing capability i'm okay to lose video but i'm not okay to lose voice that's a tough one how do you type up your whole talk track um and get the viewers to uh read it out well while lilithia sorts her audio issues uh maybe lily thinking you might have to jump out and jump back in but
while uh sorts her uh audio issues i will do a quick intro to myself uh so i'm arti gadia um my network knows me as a change maker a change agent uh for me you know my purpose is to be a voice and i've dedicated my entire career to breaking down barriers and boundaries for underrepresented groups in stem and in leadership and that's what my passion is is to create opportunities and and change um and and how i've done this is to stand out to lead through she sharing her empowerment uh which is or a chapter started up within the organization and another founding member of oasis western canada i'm proud to say there's been a
tremendous impact in being a voice and one thing i'd like to say is join us in being this voice i currently work for bug crowd and um i'm currently on the oas vancouver board i also recently was appointed on the observe id board as well which is a leader in identity and security multi-cloud hybrid environments proud to share that both boards have a 50 gender representation on the board and outside of work um this is where my fun factor is coming in is i enjoy cooking i can make a routine under a minute and i enjoy riding my motorcycle so that's a little bit about me excited to uh be with you all this morning uh with a fun
interactive workshop where you're going to learn a lot with that i'm going to pass this over to mrigakshi who's going to go through an agenda of what you're going to see for today um lalithiya just let's pause latey are you back yes i am uh are you able to hear me now yes now i can hear you so if you don't mind doing your introduction so hi everyone uh yeah sure so hi everyone good morning good afternoon and whatever it is so this is lalitya so i'm also an awas board member uh i'm doing it for almost two years now and the cyber security graduate and then i work with all these amazing ladies with
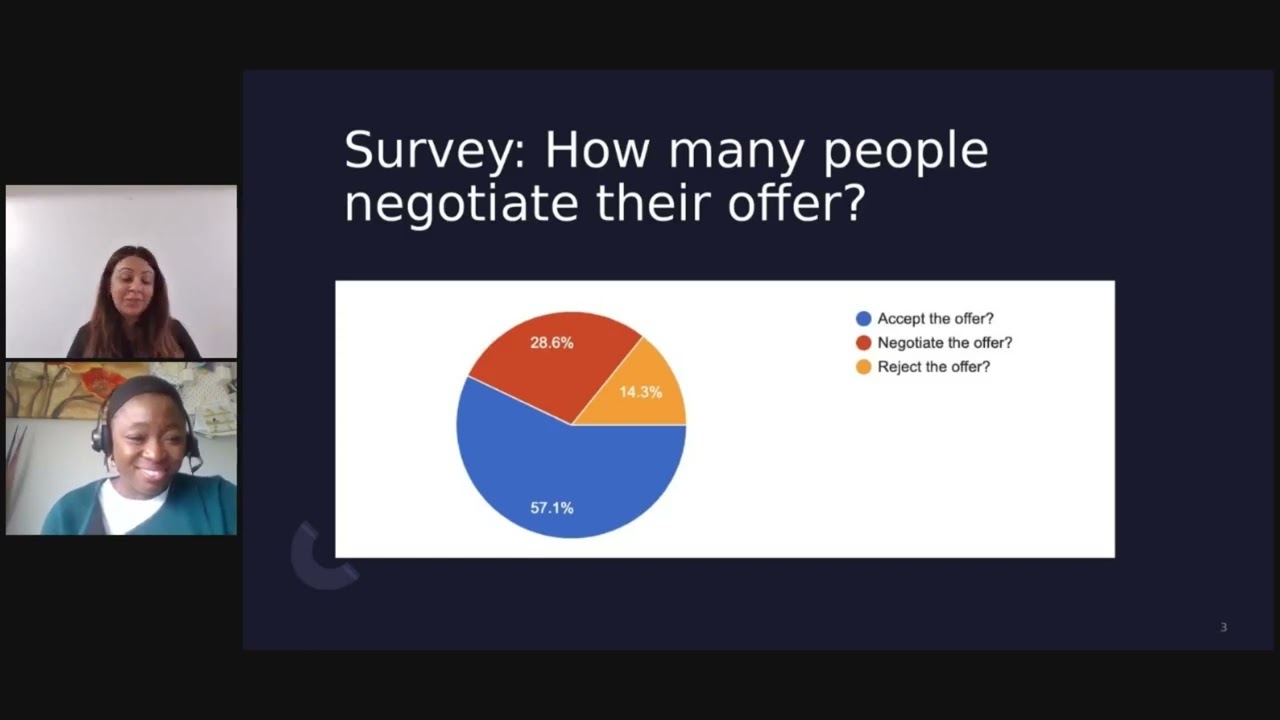
in buck crowd and uh still i enjoy myself doing bug bounties uh with buck rod and hacker one so yeah i would thank beside calgary for giving me this amazing platform uh to do some reconnaissance the basic reconnaissance the workshop with you all so yeah let's get started awesome so with that being said i'm going to pass this over to magazine and she's going to go through the agenda yeah uh so today we will cover basic recon uh we will go through host demolition some facts about subdomain animation and we will end with google talking before we begin we are going to hand you over some questions uh just fun questions uh we would like you to
concentrate on those questions later when we give you about one and a half hour of uh doing those questions but all these questions are there in our slides and we are actually discussing how to go about those questions of course we'll always be available for all uh three and a half hours um maybe we won't last three and a half hours but whatever time we are all together we'll be available for you to solve them uh so that you uh can bring out what we said in our presentation and uh go with it yeah excited for it so um we have uh 27 people we have about 30 people here we want you guys to be divided in groups
of uh some some groups like maybe seven people in one group so group five groups or three group three groups uh does anybody want to volunteer or let us know uh what their skills are if they are like really a beginner or they are more advanced uh so we have some set prepared for uh all of you
i cannot really view the chat uh does any of you have can look into the chat if someone's replying
i think i'll create a poll and i'll ask them uh about that for
it's creativity on the go right
hmm
there we go paul from pharah is live
thank you
[Music]
okay we see the results maybe we can proceed margachi as 80 have chosen beginner okay so we will just uh divide you into three breakout rooms uh when you join the session do you see a breakout one breakout two they have written like woman hackers breakout one breakout two and you will have to join those breakout rooms once our presentation is over and then uh each one of us will be present in those breakout rooms to help you out if you have uh issues with the questions let's so uh have you shared the doc for the questions
yeah let's yeah okay let's go ahead uh well let's start with reconnaissance is the first step a hacker a pen tester or a bug contact hunter will take uh well a lot of job is with advertisements have phone numbers leaking have what they do at work leaking does uh is anybody saying something there's a lot of disturbance i'm sorry it's probably just an echo so make sure we'll mute ourselves okay uh yeah so uh in job advertisements there is a lot of stuff leaking there could be environments a company is working on and vulnerabilities associated with that search engines like google bing and yahoo could leak a lot of information about our targets this is all a part of
passive reconnaissance uh well you must have heard the term google docking for i will take care of it in the later part of the video linkedin could also uh give you a lot of information about your target or facebook twitter of course there is a particular database called who is search where we can find uh where our target belongs to the registry of the target there are sites like crunch base where you can find things about acquisitions and there are way back searches and old urls can be found out uh there so i'm going to show you a small demo of how uh who is works for example i have my kali linux here i search about
a domain on who is like who is evil.com so and and then just click there so i'll i'll found out where this domain belong to the domain name the registry domain id and uh registrar's name so that's how i can know a little bit more information about my target um here i'm going to show you uh another demo about hack this site dot org so i'm going to search robots.txt uh there are some sites some particular urls like robust.txt that could give us a lot of information about websites and some of the hidden links in the website search engines search from these uh these urls also there could be admin directory exposed in some of the uh
targets we could also search our directories uh by using some of the uh search uh some of the tools like go buster here i'm going to show you how go buster works so uh i'm gonna look into my directories from inspect element i see that there are some directories there but i want to look for more directories so i have used go buster as my tool and there's a command which goes to the for looking into directories and then u minus u for the url and this is a small word list that i have used uh for the go buster tool it's let's start and it's going to search some of the urls it's also going to show me the status
so 301 is generally not found 200 or 302 might be a directory that i'll be able to find so 302 is a redirect that means i might be able to find some directories so i see that this uh there's no 302 or 200 directory yet so there's one here so i'll just uh open that up
yeah so now i see that s directory is uh should be available yeah it is available so i find one more directory here basic recon includes a lot more uh finding information than this all uh it could be finding the ip ranges or cidrs that is classless uh idr uh by use of tools like mx toolbox or domain to ip converter we can also look into the fabicon hashes well favicon hash is nothing but a murmur 3 hash of 64 encoded uh 6 base64 encoded version of the url so when we find the url of any of a website it could be of the form any website favicon favicon.ico and so we will find the favicon hash an insertion on a
website called showdown.io ssl certificates are really important uh for websites to be original uh anybody if the ssl certificates are not uh secure enough or can be copied people could fake your website and an intruder could create a fake version of your website uh let's see a small demo of how this works for example on shorten.io yeah so first i'm going to show you how i can search hack mx toolbox at mx toolbox i search my website hack.me and i will try to find out if there is a dmrc policy dmrc policy is the one that will help you to have unspoken emails so somebody cannot spoof emails from your organization support emails or admin
emails and similarly there is spf check spf is also a policy set so that people could not forge emails from your organization yeah so here we notice that there is spf record but there was no dmrc record the policy was was not doing what it should do again i see short not i o here i can search through country for example i search country colon ca and then i can find a lot of information about uh general uh leakages and so that i can know about my target mode this is a general search general search is not really important because it's not related to our target but you see that it's showing some of the services being
leaked here [Music] again i and the ssl certificates being leaked there now i'm going to show you how particularly i can search for uh webcams and some other information from on this website there could be some uh important uh webcam leakages that that could be of importance for our target yeah so also there is a github repository where i could find uh the shortened hashes of particular uh products like uh atlasia and jenkins uh these are just common products and they have just written down the favicon hashes of these uh companies so i'm just showing you how to search the hash on the website so you write h g p dot favicon dot hash colon and then the hash number
so after searching this i see that some of the targets of this uh atlasian were available on schoden so shoden actually works on grabbing the request that machines sent to each other that is called banner grabbing banner grabbing database is recorded in schoden and that's where we get this information from generally sites should hide this information but we have this information because they they have not been able to hide it let's move on to a quick demo of uh how to find a favicon hash
yeah let's find out the favicon hash of google.com favicon.ico with uh we will do it with all of you uh so i would like all of you to open uh google google.com uh favicon.ico everybody with me here
hi i would like uh my uh audience my participants to uh i cannot really see the the chat here yeah they're they're following my house so
yeah let's see i hope all of you have opened favicon.ico google.com favicon.ico and what we are going to do here is we are going to see this is the link we will use this link in a python uh code it's this very small code response equal to respect request dot get and then we encode the content into base 64. so we are just encoding this uh website url to base64 and then uh it's printing the favicon so i'm saving my file uh my python file to output three dot output.txt and now i'm going to see what output looks like so you see that the base64 encoded version is a large file and i'm going to copy that
i'm going to open an online show labs.com and convert this into more hash so this is the small number seven zero eight five seven eight something uh that's that's the number i'm going to search on showdown dot io
so here i'm searching it let's see yeah so i get some of the things related to google and let's start with host discovery
thank you mrigashi thank you for handling over it to me so let's discover about a host discovery before we start with the host discovery i just want to ask you guys how many of you are having kali linux pre-installed with you all you can just reply in box
awesome so few of you are having don't worry i have some open source uh tools as well without uh kali being needed okay uh so i'll just begin with it yeah next slide actually so we'll we'll be doing a host uh enumeration in this uh topic so why do you want to discover a host it's just a general question why do you want to perform some reconnaissance on a host because if you are given some target you want to explore how many targets that are included to that target so you just want to recon one particular target target to see uh what are the other hosts that are present in the network and if you want to convert some
unmanaged um hosts or targets into a managed set of targets then you want to really do a host enumeration so what exactly is host a host is a computer that is accessible over a network any computer it can be like a client a server or any other type of computer which we can say so each host has its unique identifier which we call it as a host name that allows the computer to access it so we have an ip that is assigned to a particular host name and every host has its own targets like other clients servers and other type of computers so that's what we want to enumerate so this is where you find more
vulnerabilities while doing the reconnaissance next slide
okay so let's discuss on some open source tools of enumerating our target so first command that we have which is an open source is like host command and then we have nmap ns lookup http status dot io it's a web page which is like a director you can open in a url and then uh do some reconnaissance and subdomain enumeration i'm going to cover this in a cli uh using in kali next slide please
so um how does the host command works so who command line system is your dns lookup operations input like it helps you to find the ip address of a particular domain as i said like if you have the whole you can figure out what site which is is it under and if you are having a ip address which what is the host name for it so that you can just you know if you are given a target as an ip address and you want to find out the host name for that then you can just uh try these commands and it has number of options which you can do like check uh ports uh the name
servers and all so let's do the basic uh comment uh i have given an example on the screen if you see a host with an ip can anyone say which host name which domain name it is under just try running the same command and just let me know what which domain the host ip is for
uh yeah i'm able to see pharah as is sharing i'm able to see the chat yeah it's for dell uh dell.com that's the domain which ib we got it using uh the host command next slide please so with this whenever you are given an ipad easy open source tool that you can use and even if you see a on screen it also shows uh what mail server it is handling so each and every uh address or the domain name will a particular mail server so it shows the information of what main server dell.com is using next slide please
next slide please actually yeah so another tool that we are going to discuss now is the end map so this uh even just need to install it sorry previously
yeah previously reduction yeah no no no the before and map one before yeah so nmap is a spring you know the n-map one
yeah so nmap is a fingerprinting tool uh what do you think i mean it's a fingerprinting uh tool so fingerprinting is nothing but it's a software that has a group of information that can be used to detect uh the internal software network protocols operating systems or any hardware devices that are connected to it so when we say fingerprinting tool for nmap nmap uh discovers tcp ip fingerprinting operations like it shows is uh what kind of open ports that are uh related to particular domain and uh based on this information an attacker clean um start food printing exercises and can develop accurate vulnerabilities based on it attack scenarios and to exploit the vulnerabilities in application system and uh this uh is completely
focused on application layer of the osi model but people think it will be in transport late but not if this is completely focused on the application layer of osi model so for to work with and map we need installation and uh on slide i'm showing you three quick steps to install nmap you can just uh install update the com update the linux with the sudo apt-get and then you can just install nmap that's the simple command sudo app get in install and then you can check the version then you can see your nmap will be installed on your system is anyone having in nmap installed pre-installed i think nmap comes pre-installed in kali so everyone should just be able to use
that command
got it i think some versions are missing okay might be here so if you are having a and map on your system just to man and map and check you can try different options using the nmap which you have some questions in your exercises uh next slide please okay so when you do nmap with the dell.com this is what you get as an output so you can see uh it scans the whole uh domain name and gives you the open ports uh because this is like a tcp by ip fingerprinting it collects all information within the application layer and then it shows the open ports that are on the network so with this you can see what are the
open ports that are related to a particular domain so that's the use of nmap and then we come to ns lookup ns lookup is a server that directly communicates with the dns server it's another uh way it's over the open source tool which we have in kali which helps us to check name servers and mail servers that are attached to a particular domain so if you can try that command that's on the screen like ns look up and set the type as a name server for domain as a dell.com and you can just tell me what are the name service that dell.com is having no go back let them
the question was to check uh the i mean use nslookup command and check the name server for dell.com
[Music] you can just try running this theme comment that you're seeing on screen
and see how ns look up communicates and gets uh with the dna server and gets us the name servers that are located for dell.com yeah exactly screen like actually
so you can see the servers that are located for dell.com in this way you can just enumerate uh type like with the name servers or mail servers using ns lookup commands this is another basic reconnaissance that we do while doing a vulnerability testing next slide
yeah so http [Music]
if i have a website it's not practically i mean it's a lot of score of that particular url etc so this can be made easy which gives you an um page loaded you can enter the domain name and the other url that you want to see and it will show you which
i think lenithya probably had uh an internet issue and dropped off i'm just gonna add her back
okay we'll just wait for alithea to come back
this
here
are you guys enjoying the workshop um did any of you learn anything new so far that's good to hear i'm glad i think b-sides will post uh the recordings later uh probably once the whole conference is over it'll be up
let's discuss some of the questions uh till aliyah comes what do you say yeah let's do that uh we'll just uh talk to everyone here because i can see like a few people active so let's just discuss it with them and get to know uh what they've learned it seems like they're liking it so uh i think i shared a doc at the beginning of this so if um y'all could just open that and we'll go through some of the questions and see if you all are able to answer it some of those topics were covered in our presentation so
uh do you all have the dog does someone like to come and present here what if we start sharing and uh i can just share my screen probably
so any volunteers from the audience uh who would like to say anything on any of the questions if they got answers to any of the questions we'll be so happy to [Music] listen to any of you
okay so can you all see my screen so let's go through some of the questions um that's awesome okay um let's go through the um first question why do you want to perform host discovery as a part of recon um i believe laritek covered this topic before about host discovery but uh i would love to know what you all think uh why is it important to perform host discovery as a part of recon
oh lolita is back i'm sorry i'm i'm so sorry i don't know what's happening with my network actually today uh could you are you able to share this thing i'll just share it for you lolita nobody's yes uh just shared yeah thanks uh we are at http status dot io
yep yeah so yeah um so you can use this tool it's an open source tool uh that you can directly go on to the website and click on the url where you can uh just see the number of uh redirect url status quotes of particular the url uh you can just try doing it hello am i lost again no we can hear you
hello we can hear you go ahead okay so yeah uh we have some questions related to http status dot i go in further and i will just go to the next topic uh next slide please vera
yeah so now we're going to discuss about subdominant enumeration so before we go to sub my enumeration let's uh discuss about the domain name so what exactly is a domain name and uh what is a sub domain and what what exactly this schema is so a domain name is like hello i lost this we can see the screen [Music] okay so i'll just go with the um without the slides so if you see uh the url that is present on this screen the http yahoo.com so that the dot com it's referred to as a root level domain and the yahoo is a sub domain for that dot com and the https is the schema that we are using so if the
schema identifies the protocol to be used whether it is like a http or https uh which we can use it a domain is particularly um the ip address that goes to the dns server and i adds a domain name to particular uh address which are stored in a dns service so if we consider dot com as a root level domain then the sub domain will be the yahoo one so top level domains are the uh one of the most highest level of uh the hierarchical domain in the system um after the root domain and um i'm not sure what's my next slide maybe i'll just see in my screen
subdomain yes abdomen is just part of an uh root domain if you consider yahoo.com.com and yahoo yahoo is a sub domain for dot com and if you consider news.yahoo.com then news is uh is a sub domain for yahoo yahoo.com so in that same way if we want to enumerate the kind of sub domains so what is the use of enumerating sub domains um suppose we have a target that is given to do some reconnaissance and find out vulnerabilities if we have given xyz.com so we need to identify if there are any sub domains that are attached to that particular uh domain so that we can have more chance and possibility to find out vulnerabilities uh because everyone will
be focused on the main domain but if you are focusing on the sub domain and if you if you can enumerate the sub domains and if you can if you are able to do some vulnerability testing then that's a valid uh error that can be bug that can be identified so we have a lot more sub domains and subdominance levels i it's like a 500 sub domains max so um how it work so it it's like it's used to organize and navigate to different parts of web applications or services the subdomains and if you can see the hierarchy the dot is a root domain and we have the subdominance is arc organization.com um or ncaas or
authentication something like that and if you are dividing the dot com as well we have some sub domains here we have yahoo.comnetflix.com or spotify.com or area like google.com something like that and even if the other sub domains for those particular level of domains again goes to like news.yahoo.com finance.yahoo.com entertainment.yahoo.com something like that so each uh domain can be divided into sub domains and if you can enumerate the sub domains we have multiple chances to do the reconnaissance and i find out vulnerabilities so uh what is the use like you can find uh interesting uh assets of the targets like different service web applications and if you have forgotten any hidden or forgotten applications that which help you to uh find out
vulnerabilities then you can find out um so the tool that i am showing now is the sublisted which is a cli tool that helps in enumerating the subdomains so what exactly the sublister do it enumerates sub domains using all search engines like if i uh i mean we need to install sublister and for that we need python and pip would be the easy way like if you have a python input then you can install i have given you the link uh how to install the sublister if you need i'll just typing it in the chat as well so you can just quickly install it on the kali linux it doesn't take much of your time and once
you run the sublister command without giving a domain to particular website like if i'm giving sublist if i'm running sublisted with the domain of uh my name is dell.com it runs through all the search engine search engines and it gives us a n number of multiple sub domains that are uh hidden for that particular domain that's those are not hidden but we actually don't know we cannot directly uh check it so the sublister is an optimized and accurate uh tool i would say that would give uh domain names a list for you to identify and enumerate the sub domain so this is how it works um like say we have done if you can see on the screen if you can
share the last screen of the other screen next one that next one so this is the hierarchy i'm sorry i'm just not next screen do you want to be on the hierarchical domain name system of news.yahoo.com no no just next slide next slide yeah next slide yeah this is the one so if you can see on the screen how it works i have typed a command for uh sublisted for a domain of yahoo.com and you see it it's uh searching in all the web server search engines and it is giving me the results of the sub domains that are presented for yahoo.com which you can enumerate and find out vulnerabilities so this is how you do
enumeration subdomain enumeration for using sublister with this i think i'm done with my part and you guys will have questions on on this topic i'm sorry i'm just having a bad connection in between and next slide will be continuing by farah uh lalitha we have a question for you here uh does subdomain have different public ips assigned or they they are all tied tied to the main domains ip
hello yeah hello are you able to see the child no my screen is just blood okay uh so we have a question for you from uh prashanth does uh public ips equal to ip addresses he's asking about public ip addresses uh
hello it it it can have just different ip addresses hello yeah we can hear you here you can have multiple
yeah and prashanth i think you can always join us to maybe answer some questions uh just join click the join button here and
all right so uh i guess i'll continue on from here so i'm going to talk about how you can perform recon using ssl and tls certificate so first let's talk about what those are uh they are mainly used to enable an encrypted connection which means that uh any communication from the server to the client is encrypted and it also has another function of demonstrating ownership of that domain so what that certificate does is proves that this organization owns the domain and some details that are included in the ssl and tls certificate are is the domain name the certificate authority the organization the expiration and uh things like that so uh there's another there's a type of uh ssl
tls certificate called wildcard certificate so if you see a wildcard certificate with a domain which says star.yahoo.com or something similar where a star is there it means that it's a wildcard and this is a wildcard certificate which can be used with multiple sub domains of a domain so if there is star.yahoo.com it will act as a certificate for news.yahoo.com chrome.yahoo.com and any subdomains and this goes beyond just one subdomain it can be uh a few levels of subdomains uh as mentioned earlier it's a hierarchy so the uh a pro of doing this is that it does an easy setup over there but there's also a call that if one of those sub domains is compromised then the
others will also likely be compromised so now i'm going to show how you can do subdomain enumeration using some gui tools so there's no kali required for this all you need for this is your browser and these are website names so if you go on crt.sh uh it will help you look for subdomains uh from the ssl tls certificate uh that was explained earlier and subdomain finder dot c999.nl is also another uh finder that's on available on the browser you don't need to install any tool for it and it will give you a list of some sub domains so why don't we try one of those right now so if you all can just go to this
website crt.sh and in the search bar when you type in yahoo.com uh these are the results you'll get so there are quite a lot of details over here like who is the issuer so the issuer name matching identities uh the common name uh and uh about its expiry that it's not before and not after and when was it logged and also an id uh which is for their purposes so let me know if you all did this and if you all got the same results as seen on the screen
let's go uh is anyone with us yeah uh could you repeat the question i think no one has answered yet yeah so there's no question as such or if you can just go to crt.sh and type in yahoo.com okay there's an error so uh there's probably some issue on their end uh but don't worry we have another tool that we can uh experiment with so if you can just go to subdomain finder.c999.nl you'll see a page like this this has a much more friendlier user interface so if you can just go here and type yahoo.com you'll probably get a simple list of subdomains with the ip addresses let me know if this website gives issues
to
yeah that one is good uh it's very easy to use uh i'm not uh i don't if i don't feel like using a tool on a cli i just use this one
yep there are lots of results yahoo.com is a big one but there will also be smaller applications sometimes that don't have as many results as yahoo.com does
okay so uh i am going to move on now to the next topic uh we already did this so let's go on uh now i'm going to talk about uh google docking for hacking i think this was very briefly mentioned by makashi earlier that you can use search engines like google bing uh to perform your recon so that's what we're gonna look into today uh so firstly let me explain to you what is google talking so google talking is nothing but they're like filters for google so i'm sure when we've shopped before we've used filters while shopping that we only want products of a certain color certain price range certain brand so uh google docs are just like those they are
filters for a google search so it allows you to get much more specific uh results and that allows you to get specific search results which are related only to your target and are relevant only for that so for that reason it can be used for recon while hacking uh because it helps us discover very target specific information so uh this is one example of a google doc this is the site dock so the site dock essentially allows you to look for sub domains of a domain so uh the star again means wildcard over here so we're just asking google to look for subdomains of spotify.com over here um we can also uh get much more uh we can
enhance this a little bit further by putting two wildcards so that then it gives you the result for the third and fourth level domain and uh we can also use the minus sign to remove certain uh sub domains from our search results so while doing bug bounty there are some targets that are out of scope you are not allowed to hunt on them as per the policy so uh what you can do here is you don't want results for that particular domain and you just use the minus sign and write the domain's name and there will be no results from that domain uh that was how you use google docking for domains but you can also use google
docking to find sensitive files related to the target or hosted somewhere on the targets websites so here as you can see i've given site.spotify.com so that's my first dock i can also combine it with another dock called exp which basically stands for extension like a file extension and file type also does the same thing so as you can see uh in the values i've given pdf docx pptx so these are essentially file extensions that i've given and i want to know i want only those file results on spotify.com that have those extensions uh there are also some more sensitive uh file extensions like log con ba key back and these essentially uh mean that their backup files or some
kind of configuration files and they might have a little bit more juicy information if you can find it um another dog that we can use to for while finding files is the in-text doc uh we can give certain keywords that uh we can tell google that look for this domain and look for files that have these words in them or look for uh pages web pages that have these words in them uh so some word examples can be confidential or internal use only or sensitive and this sometimes uh gets the attackers some sensitive files um okay so that was how we did files now there's also another thing you can do with google docking is
look for the targets information but not on the target sites on third-party sites so i mean if you have a business you're not just using your own assets you're also using some third-party sites to maybe uh organize your sales data or do some marketing data or something we all use that uh in our organization so some of those examples can be trello.com codeshare.io and jsfiddle.net so these websites are generally used uh for uh putting up some code snippets or putting up some kind of lists or some to-do lists like there's a lot of things that you can do with trello.com actually so when you search for this it tells google that you want to search these
sites but there should be the word spotify somewhere in those pages and that's the results that uh those are the results that you're gonna get uh now we can also do uh we can also take another approach and use google docking for specific bug types um so your as you can see uh open redirects and xss are can be commonly found on certain parameter names like redirect url is a very common parameter where attackers usually find open redirects and xss so i have asked google here to show me all the subdomains of spotify.com that have redirect url as a parameter in their in their url and uh we can also use uh that a similar approach to find admin panels
or login pages or sign up pages or some of them can also be insecure so as you can see here i've given site spotify.com and in url sign in login auth these are some kind of common words that are used for a login page or a sign up page and lastly i want to say that you can mix all of this up you can combine and use all of these dogs together for the best results because there's no limit as such and the more dogs you use the more specific results you'll get the more obscure findings you will have and that is the whole point of bug bounty is to find unique findings before anyone else
does so yeah that's all i had for you today and thank you and now we're gonna go and work on the questionnaire that we gave earlier uh we'll also provide you these slides so you guys can use that as a reference by solving questions yeah i think uh all of you have the questionnaire and there's a link at the end of the questionnaire for our slides
uh no tj we don't have a list of references uh but we have mentioned though all the slides in in our slides which sites we visited all throughout
thank you i'm ima
anybody ready with any answers we really want to discuss uh the questionnaire now because we are going to open up the questionnaire and discuss all the questions there
i think we have 35 33 people here uh just come on our stage on our stage join our stage volunteers anybody
please don't leave the conference join our stage
how about prashant
movie yeah we have 28 people left now so it's okay uh let's discuss the questions here
anybody who wants to volunteer type uh why in the chat and then join us
hmm
so i'm going to share my screen for uh these questioners i see a lot of people here uh 10 15 people are there so uh first question you see i hope everyone can see my screen yeah mikaki we can see yeah so first question is find the txt file in in the website anybody was able to find a file may be in dot well known directory
sure hammer please uh join the uh presentation by just clicking on join uh and maybe uh we can discuss any question that you've you could answer
are you able to join us by clicking join
there should be a little button at the top saying join and then we can accept yeah but if it's not please uh
so i'm going to open this website and
so
so this is the website the first question answers here uh security.txt is a common website founder dot well known this is uh this has to be public john in general this is not really a bug but uh you can always get a lot of information from here uh let's look at some of the more questions i think i have already shown uh how to find the favicon hash of google.com favicon.ico and uh we can always check uh the dmrc policy by mx toolbox so let's go to mx toolbox
so i just search my website here and uh i see that the dmrc policy has been pub published and the record is found uh
so for the for question number five i would really like you to do task one and two on this website so it would be really good if someone volunteers for this one you just have to sign up here and there's some very easy tasks that you can do
yeah so hama is here uh jaime would you like to uh do the second the other question it's it's simple would you like to try it
i think you can speak uh you have to turn on the mic yeah hi hi hi ma uh would you like to uh try the this question the next question sure um sure uh can you can you share your screen with us
okay um maybe i'm not even i won't be able to track that i need i probably need help uh oh you will be able to crack we are always here to help everyone's available okay so i went to the website
um what do you want yeah uh could you just uh i think uh indeed once yeah sorry uh which question are we trying for we are trying the second part uh for the indeed one so the first question is just uh i mean the context related question you don't need to perform any task on it it's just a basic idea why do you want to generally do a host discovery or as a part of recon i think we have already someone has already given answer in the chat before when i am doing the presentation ah okay yeah it's just like why do you want to perform recon simply why do you want to do a host
discovery sure what's the use of india so okay so i see the answer in the chat i'm sorry i'm not prepared for this one so it's i don't know services and which eyepiece to target yeah which if you if you just want to discover number of hosts or what are the open ports that are available for one particular domain then we can we'll just do uh this host discovery host enumeration okay so do you have a kali linux pre-installed on your system um i nope nope i don't think i to that's okay uh yeah you can try some other questions which are like
yeah sure uh jaime let's try the hack this side question that the question number four and five you see on your screen
okay identify the name of the server uh oh okay so i have some troubleshooting uh did you end this green shirt yeah trying to it's frozen for me for some reason oh okay i'm not able to okay
oh gosh okay i think um can you hear me at least yeah we can hear you
okay uh i think we can take a break for uh 20 minutes for participants to look into the questions and we can come back uh i i think not everybody is from calgary so i cannot really tell the time but we can come back in 20 minutes if anybody knows any answers to any questions because we have about one and a half hours still in the workshop we'll still be talking with all of you we'll be solving every question one by one and uh yeah just uh try and solve those questions by yourself and we'll meet you in about 20 minutes i'm going to share my question number four and five from the sheet that fara shared
and sophara if you want to continue with the your part first till the time i sign up for the site that i've given there yeah i'll just go through the google talking part as well uh yeah sure you can start with that i think you all can see my screen now um as i said if you can just open google.com um [Music] we will uh go to the group two set of questions beginner question i grew to uh the website that we're gonna use as our target for these exercises is spotify.com um i already gave a few examples of these in my presentation so if you have uh if you want you can just keep that
open on this on another uh tab as well but i'm gonna share my screen anyway so um the first one is uh just a question why do sensitive files get indexed on google um so if you have a robots.txt file on your server you can actually specify uh certain file types that you want google or you don't want google to index while they're searching so for example if there are certain sensitive files which have any information about your server that you don't want the public to see you can you can restrict that from being from appearing on google search results in a similar way you can also put certain things that you want google or
to search for so maybe some marketing uh data or something like that you want uh to be seen in search engine so you can allow that on your robots.txt file now let's look at this which dock will you use to find a potential ssrf and write down some urls that you found through google docking that may be vulnerable to ssrf so first let's talk about a little bit about what ssrf is so ssrf is basically an attacker tricking uh the server to make a request to some internal resource and since the internal resource is receiving that request from the server which is a trusted resource it will allow access to that and as a result it will allow
access to that internal resource to the attacker uh so we're basically misusing the server's trust in its own domain uh and that's why the name uh server side request forgery so there are certain docs uh certain parameters in urls that are generally vulnerable to uh ssrf so let's find out what those parameters are first so i'm just going to look for ssrf uh common parameters and let's find a cheat sheet or something like that or we can just look for ssrf google docs and here we'll have some results so let let's open those up
okay so as you can see here uh this is the host in this case and we have a page over here which you're requesting access to an internal file i'm just going to zoom my screen in in case this is not properly visible so uh this page parameter over here is vulnerable uh and we can request an internal resource by adding a payload over here so uh this is this would all also be the answer to my question which is uh write down some urls that you found your google talking that may be vulnerable to ssrf so something like this a url like this might be vulnerable to ssrf we can test it for ssrf for sure and uh yeah
this is what it would be so here we are reading local files but you can also do some other things uh here you can see uh these are some other websites and these are some other parameters that are vulnerable so that's kind of how you would go about looking for google docs for a specific bug type um next uh question write down three urls that you found that may be vulnerable to an xss and three for uh sql injection so uh similar to what we did in the previous question i'm just going to look for xss google docs and here you actually have a huge list like top 10 top 100 xss docs so uh
you must often see these parameters appearing in your url like question mark q equals to or search equals to or keyword query these are really common parameters that we see across a lot of different uh websites that we use in our daily life uh so these can also be vulnerable to xss and any exercise payloads here uh in the in these parameters uh we like we see that happening uh quite often so definitely a good place to look for xss docs and we also had a question for sql injection so let's see what we have for sql injection so uh yeah similar to uh this we have view items.php and id uh i see id
parameter being the most vulnerable uh by like so far uh but there are also some other ones like uid we have docs sometimes uh and the ids can also have like different kinds so here we have pid we have just id uh f id so uh id parameter because it uh is enumerable easily it's generally vulnerable to sql injection too um let's look at the next question uh find out five third level and three fourth level domains of spotify.com so for this let's just uh go ahead and use our site doc that we saw earlier so i'm just gonna do site star dot star dot because we are finding fourth level domains as well so just gonna do that
and you can see that we have support.spotify.com i think we need to have a space here and i'm just going to remove one of these so we can get more results and we don't want anything other than that so i'm just gonna remove our regular spotify
so we have open.spotify.com artist.spotify.com accounts.spotify.com uh so as you can see that you know using this we can enumerate subdomains we don't need any tool it's just a simple google search developer spotify.com and the regular www.spotify.com um so we found our third level domains and let's find some pdf docs csv or txt files i am honestly not sure if this has a results because most companies they do a pretty good job of not exposing these files but sometimes we might get lucky and that's all what bug can't be about anyway
i think we need to look for them individually
yeah so as i said it's kind of not very common to uh find files through this kind of search uh for spotify.com they are a popular target for bhagavata so it might not be available uh perhaps we can try another target so i'm just gonna do google.com and see what comes up
yeah so as you can see we have a lot of pdf files that are available over here uh of course everything isn't sensitive and we probably have to look at the files a little bit to see if they have anything sensitive in it but in that case we can also uh use other dogs like in-text confidential or internal use only to filter out the search results even more but yeah there's a lot of space to uh experiment with google docs you can combine them you can use one two or you can combine different kinds of docs so yeah i think uh that's the power of that and i i mean i think i'm done with the google
talking questions so uh let me hand it over back to mykakshi sure uh i'll just share my screen yeah i'll just share my screen and show uh some of the questions that we have not done so uh so this is the sheet everyone sees i think and uh so i've already shown you how to find the txt file it is not well known security.txt the answer to this one is and you could also find robust.txt that was already there in the slides and i have shown you how to find the favicon hash for google.com favicon.ico you can always go back and refer to uh the slides and we will definitely provide you a link to the to all the slides we have
again uh let's see the last for the dmrc uh that also i've already i can show this part again so i'm gonna search mx toolbox and
i'm gonna find my site hack this site dot org and search for mx lookup and here i can find uh that the dmrc record has been published so uh that was question number three and for question number four and five i wanted you guys to do basic level one and two so let me show you level one so i've i clicked on the basic mission and this is the basic mission level one uh can can you see my screen is it large little can you zoom in yeah let me zoom this
that's better yes getting better now zoom back in [Music] so anybody who wants to solve this question with me this is the idiot test if you can't complete it don't give up maybe try learning html don't be begging someone else for the answer that's a way to get hated uh enter the password and click continue so anybody anybody just guesses while guesses what's the answer here we have 12 people viewing this come on uh just a while guess that what would be the password here
anybody in the chat
uh any of the audience know it
okay any of the speakers know it maybe farah or arti you're available do you remember what's the password here i don't remember actually so yeah so as the name says the idiot test it doesn't want you to actually write any password um you just have to click submit here and that's it so oh okay sorry but you have entered an incorrect password
okay really
don't give up on learning okay so i think let's see inspect element we couldn't really do it without writing any password maybe we'll find oh so its value is password here can you see the inspect element so it's password let me try writing password because in inspect element uh it's written type password and name password that means that the value of password should be password i click on say sorry again
okay
yeah it's value's password so that should be it
yeah i i have no idea why this is happening
uh so i'm i'm just moving on to level two uh network security sam uh set up a password protection script uh he made it load to real password from an unencrypted text file and compared the password to that user enters however he neglected uh to upload the password file so he did not upload the password file let's again try clicking on submit and uh yeah it says congrats so this one uh this one just happened because this person forgot to upload the password file and uh it got completed yeah so maybe i'll try again uh this one the answer to this one is password because it's written in html in this inspect element so those were my four questions
i think is still having issues with joining so she might not be able to go through a question
so i think we are done with the workshop for now uh anybody still has any questions or would like to volunteer we are still available uh for next one our you can always ping us you have our profiles on hoppin and you can always message us privately on linkedin we are always there to reply to them and uh yeah that's all for today a huge thank you and well done to uh miguel farah and la lithia this has been fantastic just uh seeing the three of you um on this workshop and uh such a pleasure every time i joined this session i learned something new so thank you for sharing this with the audience and the
participants