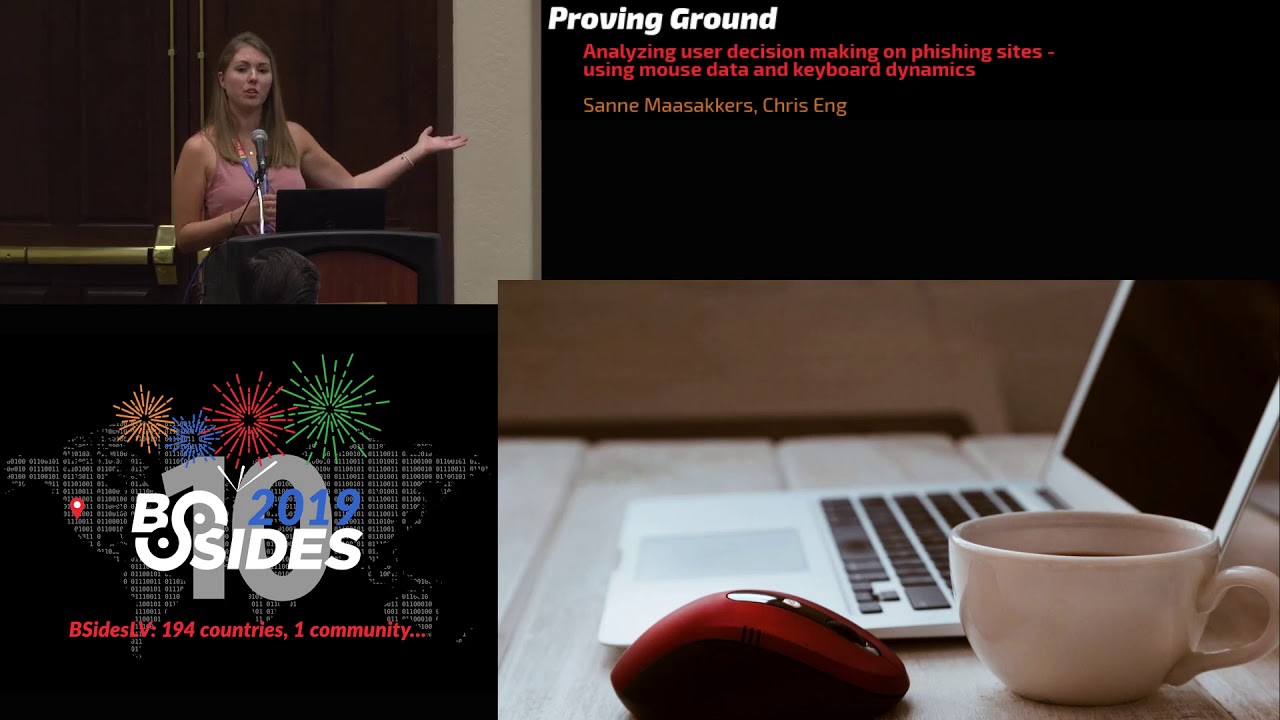
Analyzing User Decision Making on Phishing Sites Using Mouse Data and Keyboard Dynamics
Show original YouTube description
Show transcript [en]
good afternoon and welcome besides Las Vegas I want to be louder than those guys next door because I hear them all the time come on once more welcome all right thank you we like to thank our sponsors especially the inner circle sponsor here is the critical stack and Val Mel I also like to thank Amazon blackberry and NSA the National Security Agency that's what it says on the form okay remember your of your cell phones please be polite turn them off okay I have a microphone and I will pass them around and the first three people who ask questions get a pair of socks mm-hmm all right so amber I think that forms on the back I'd like to introduce and I
could try to say her name right it's sana must I said my soccer no well thank you yeah well thank you all for being here first of all of want to thank my thank my my mentor Chris I think he would be some work here yay well my name is Salim a so Chris you did pronounces very well it's Dutch so that's why it's very hard to pronounce but I will introduce myself later first I want to play a little game with you because you're all security experts right first I have this website a screen chief of a website you go true you just go browsing on the Internet encounter this website take this take a
couple of seconds to look at it because now you're looking at this website did you see some differences I'm not homesick luck with the show here but did you see differences 1 2 3 yes right well there were some differences on these websites because the first website looks a little bit more legit because it used the smartphone dot store as URL and has an SSL certificate and the second website has the smart smartphone story dot virus scanner Pro dot your dot uk' so that seems fishy and there are small typos and misspellings on the websites so when you see those websites on the internet do you behave differently well I don't think you will because your are
security experts but I did a little test with with a small set of people and well I was wondering do people behave differently when they got these two websites and that's what I'm going to talk about today I developed a model what is user behavior and do people behave differently so my name is Shana massacres I'm a pen tester working for folks IT is a company in the Netherlands part of NCC group and this is my daily life well not actually my daily life because I was asked to be a hand model for the national news and during my work day I don't use Metasploit with him I don't know what it is it was a very
stupid exploit well this is 99% of me in media and 0.1 percent in my actual working life so yes I am making the world more secure every day just like you do all day so I was wondering could I combine phishing social engineering with my previous job in web development and security so that's why I came with this presentation so phishing well we perform phishing assignments almost every day to test the security awareness of our customers I think you will do as well but what we know after we have performed an assignment is how many people clicked how many people filled in the credentials and how many people actually cuted malware but we don't know what
happens in the meantime do people like the website are they wondering on the website are they clicking it away after they filled in credentials but didn't submit it it's almost like okay we only know some things but we don't know how to actually behave on a website so that's what I did actually but before I needed to know a little bit more about the psychology of fishing so why are people clicking on wings on websites first because they don't know it's a phishing website because they don't have to knowledge they know no second because it's called visual deception the phishing website looks exactly are almost exactly the same as the legit website they're using the same logos
they use well very good type of squatting maybe use all domains or domain takeover so it looks like phishing websites so even when you are ok aware you still don't know it's it's a phishing website and last but not least because you're have a lack of attention for example before you have your morning coffee or after a long day of annoying colleagues like mine yeah you don't have the attention anymore so you're just clicking on a website and ok fine so I did a little experiment like I said I created two websites I already showed you a screenshot screenshot of the phishing website so I created two websites one with the heuristics of alleged website and one
with the heuristics of a phishing website those two website were presented to a test group they were included in a questionnaire so I sent out a questionnaire to a group of 30 people not in my network because I have a lot of IT specialists and security experts in my network so as I asked some people including my parents to spread nerd because they are not in the field and I asked them to browse to to websites first browse through the legit website perform some simple tasks like okay go to the website go to the login page register add a phone to your to your card and then finish the purchase I did the same with
the second website so with a phishing website perform the same steps of course I switch the order of those two websites after 15 participants because maybe they already learned from the first website so there so their behavior would be differently after they had to to perform those steps as some some general questions to gain more knowledge about people so for example age and education but also if they have experience in buying a line because maybe it could they already got scammed and they didn't see that the difference isn't okay that would be clear and I also ask the question did you see differences between those two websites and what did you see which difference did you see so this was
my setup this is a screen shot of the website so it was called the phone store it's not a real brand because they have brand Association and all that kind of stuff so I made up a brand the phone store and it was a phone what phone webshop with iPhones it looks like this and it has small differences I use the official official visual similarity model because it had to be almost the same because if it were if it was a completely different website and yeah of course the setup wouldn't work so this was the website those differences can be placed in three categories the first one is in content there were a lot of researchers that
placed all fishing heuristics in three categories and those are those three the first is content so that could be text could be images the second one is content and URL so you're using another URL could be a total different URL but you could also use IP address for example and the third one is the use of SSL certificate I know that a significant amount of phishing websites use HTTPS but I still decided to use it because well the websites really look alike so I wanted to have a clear indicator that it could be a phishing website so that when I yeah when I applied those heuristics it looked like this so this is the phishing website
I used the logo the same logo but I changed the dimensions so it would mean not that sharp as the normal website I used some typos typos here that was there not that many I used Chinese characters could be any character but I wanted to show that okay this website could be a scam web site could be a phishing website because it's translated from another country it was just a small indicator that it's not completely legit then I used it at this one I think it's very funny Fisher's tend to use fake security logos on a website so I just picked some security logos from websites it's not even a website security logo so I use that one
to create a fake security ID on the website so people think it's it's secure but it's actually not I also wanted to add a small time pressure so it was a big quick only few devices left in stock so that people are going to their goal and are going to buy that phone I also used a difference in a price well this is in euros because I'm from the Netherlands but it is a little bit more and you have to dollar amount I chose to use a price that's not that far from the original price because if it's too good to be true well of course we all know that it's too good to be true so it
shows a little bit less than the normal price but as you may know iPhones never are in discount for Hilly's then we have the login page and here I also used the fake security so you can see that it's not secure because you're entering a login page there is no certificate so it says it's not secure but I said yeah this form secured and encrypted but it was just text with a green font awesome look I can so it's still not it's still not secure of course so these this was the phishing website now I wanted to gather information about their behavior but first I needed to know what behavior is of course so I read a lot of
researches most researches were in the UX context UX domain but it was one researcher that researched the behavior in combination with security because it was about biometrics and security to create a continuous authentication application so I thought well that would be fine because the goal of that research was to distinguish people by their online behavior and this then was exactly what I needed so behavior what what they researched was that behavior is or contains Mouse beat so your speed with the mouse on your website click frequency and key press frequency the hand amplitude so the maximum width of your hand on the website the idle time and efficiency I will show later what I would
the amplitude how do I platoon was calculated and efficiency but to get ya together this information to get this information I had of course capture information on the website so that's why I decided to use Mouse capturing so on what time stamp are you on what coordinate on the website the click press or the clicks of your mouse so which time of which coordinate and at the key presses I capture the key presses not not a real key process but that a key was pressed and in which field it was pressed so that information was sent by an API to the database so I could use it for data science data science well how does that look like I
made a small screen capture how'd it look what it looks like here you see me scrolling on the on the phishing website so it says ok go to all I phone models ok I just scroll through the website I go to register and in the questionnaire I asked to go to the login page first and then go to register so I'm just entering some information now you all know my password so okay I'm login I go to the show add something to my cart okay there's something in my cart do I like this yes okay I want to check out and that's where it ends you don't have to fill in your information because it
was research ok so I was added to the databases and user all time stamps and mouse x and y's were edit - for the clicks and the key presses so this was answered what after what I did on that website so I can use this what this information for data science the users I also captured a dimensions because I had to normalize all screen dimensions because my screen is smaller than your screen so had to bring it down to one % so what I did on the screen capture resulted in this this is the screen or this is the heat map with all mouse movements please note that the y-axis is going from 0 to 350 every certain refers
order because yeah my screen is starting at 0 in the left top of course and 350 percent because your website is crawlable so you go further than 100% this is then the mouse movement and this is when I use convex Holling that's it is a technique in in game development to enclose all points to calculate the maximum hand amplitude so I only had to brute-force all those those dots that were on the line to calculate the maximum length of the hemp amplitude and this is how it looks like when you connect all mouse movements this was needed to create to calculate efficiency efficiency was defined by researchers different ways I used to to define the
length of the click path so the length between two clicks divided by the actual movement between those two clicks if you're very efficient you go from one click to another one just in a straight line if you're not efficient you click you go all through the website like crazy and then go to the next point to click and if you divide those two numbers then you get efficiency so if you're very efficient then you're close to one if you're not very efficient you're close to zero so any question also ask something about education ages and if you ever bought a line if you got scammed if you saw differences and not resulted in a lot of information that I
needed to process well in total the word 30 participants and more than have 100,000 interactions I created our models to check them what happened these are some statistics most of the people buy online every month there was only a very small group that buys once a year and the second pie chart shows how many difference they saw only content is the light blue one content dot plus URL was to record content URL and HTTP is the orange one so if you saw more than one different difference of only a content only a typo for example then you were one of the 80 free participants percent of participants if you saw more than two year twenty percent exactly all three
categories there is 30 percent and 70 percent of the participants didn't see their friends well that's not very good so what are the conclusions well people behave differently on those two website because the efficiency on a phishing website was way hired and the efficiency on a legit website so yeah it works time pressure was edit maybe they feel pressured so if they go directly through the target we don't know but there are several things we can think about next through that well it was only a set of 30 participants but we have to test this on a bigger set that security awareness defined by the number of categories in differences they saw is very low between the ages of 16 and 25
and 56 and older so we should focus on security awareness for those two groups my generation knows how to recognize fishing apparently so what to do with this well I was thinking about future and what are the next steps I was looking for the future and this was the image I got and Google it is a rapper the future what what could we do now well I'm definitely going to use the this model in our fishing assignments so we can not compare the if there are differences in behavior between the legit website and a phishing website but we can definitely check if there are differences between between the fishing assignments so maybe that one with a
bigger logo one way the typo works better than the other one not only looking at clicks or or downloads or fielding credentials but also at their behavior at the website and what are more next steps well I put everything on the github and the websites the API the data so you can use the data set as well as all the our scripts so you can use this in in your own research you can download it and I added a research paper of 70 pages if you want to know more about this research and if you want to know more you can follow me on Twitter or LinkedIn thank you are there any questions
there still sucks they're very nice the boat the two websites were main and laravel it's a PHP framework and the API was created on lumen that's a micro framework for api's everyone wants it sucks where you test were you testing to see if people refused to complete the test on the fishing site and did you have results in that way yep I had two people that didn't want to click on the second website and said immediately nope this is fishing anymore in my generation in my age were you spied a surprise by the group that noticed no differences and what do you think training wise you could help that group of people out well I was not
surprised because most of the most of the the people that were older than 56 didn't see the differences and younger than 18 so they were there yeah I'm not very surprised if I look at my own grandma and and granddad actually because they didn't grew it didn't grow up with cybersecurity I keep telling them that but they still use the same password for everything so no I'm not surprised at what do we need to do I don't know I'll have a granddaughter in security some are like that and so is there a way to track websites that are actually watching your clicks because I haven't seen that very often is that commonly is that feedback very common well you have
trekking trekking blockers that tread that block a lot of trekkers but that's why I decided to create my own API because when I use for example Google they have services to to track your behavior on the website and a lot of the Trek behavior would be deleted or blocked so yes there are a trekker blockers that look this kind of information did you notice any other correlations in the group that was less likely to fall for the fish were they more likely to be working in tech or associated with tech or were they more frequent online shoppers why didn't go deaf far actually but the data set is online so if you want to if you want to
check it out please do okay thank you everybody
[Applause]