Exposing the Neutrino EK: All the Naughty Bits
Show original YouTube description
Show transcript [en]
yeah thank you very much so for those of you wondering is this an angler talk actually no no angler died Angler's gone just went away kind of fizzled some people are happy I'm kind of sad I had a LoveHate relationship with angler so I'm like whatever so we're going to be talking about nutrino I had about 5 weeks to prepare this I researched angler on and off for about 2 years and then BS are hard there you go and then I found out like oh I need to completely revamp my entire presentation so here we go let's do it okay our agenda for today we're going to be talking about nutrino not angler we're going to talk about what exploit
kits are how they function how they work and then we're going to pull apart a sample my focus today is on the exploit kit portion itself so we're not going to focus too much on the actual exploits that are being leveraged in there I'll mention one of them and we will break down what occurs the Shell Code that actually runs things of that nature but I want to focus mostly on that so for example like the malware that it drops Al like we're just going to kind of reference that Mo on you'll see what I mean all right I'd like this to be kind of a two-way communication so the bights crew really likes it when people are
involved and people participate things of that nature and I like to run my dadn mouth and talk to people too so it kind of works out all right so I'm like hey who does this you know participate or pretend like participating what do whatever and then here's my yeah we're not talking about angler sorry the programs went to fres before I actually officially changed it so no big all right this is me I work at incident response for Beal Corporation we're the largest construction and engineering and project management company in United States one of the biggest in the world think like Mega projects like tens of billions of dollars over years and years and years we build stuff I don't build a
damn thing I don't swing a hammer but you get the idea I have some education stuff some searchs but I know you don't give a damn so moving on I like to run my mouth though and that's going to help because I like to present and so I get to do that let's do it I like these things I do open mic comedy at the uh I was practicing earlier by the way at the local place where I live in Phoenix I love Retro Gaming I like to read sci-fi fantasy stuff and uh anyone here do CrossFit raise your hand don't lie don't you lie you you heard the joke right how you know someone does crosfit or they a
doctor yeah they'll tell you I started doing Brazilian jiu-jitsu and I'm turning into one of those guys like oh you have to do it trying to convert all my friends it's kind of sad so this is our security Operation Center it looks pretty this is a professional photo we had taken and I just like to show it off rert hangs out poses for us all right exploit kits what are they so exploit kits this it's a business it's a business of exploiting hosts and getting a particular strain of malware onto the greater number of hosts possible this is bigness this is a huge competition it's a vendor based competition so you may have heard of angler previously we're
going to talk about what happened to angler and we'll talk about nutrino but in reality there's three primary actors let's just pretend all right let's play pretendes that some of you in here create your own malware I'm sure you don't do that right but let's just say you did and let's just say that you wanted to spread your malware to the most number of hosts possible like how would you go about doing that well you would basically hire someone who runs the exploit kit and the thing is you give them the malware and their goal is to spread it for you so there's three primary actors there's the campaigns the people who redirect the actual traffic
to the exploit kit there's the exploit kit people who run the infrastructure to try to exploit as many boxes as possible and then there's malware authors who provide their malware and then paper to be distributed so it does so by we're going to break down exactly how nutrio does its little thing here but the idea is very simple the exploit kit landing page enumerates the hosts it checks its capabilities it looks for non-patch software essentially and if it sees that something is vulnerable it just goes all right go and if it fails it says ah [ __ ] it but if it works then it goes yay and that's pretty much works so it just
casts a very wide nck if you will the redirect process is pretty simple the host over here the user over here better yet goes to what here she believes is a completely legitimate site there's some funny ones get exploited by the way but I'll say that research for another talk and when they go to this site what happens is in the back end their browser gets redirected over to a quote unquote bulletproof site and that site is what's hosting a landing page for the exploit kit this is typically in the back and hidden I frames and all kinds of other fun stuff user has no idea it's even occurring and exploitation occurs and then oops so
anyone here familiar with a bulletproof site you know that term refers to you don't count can't say all right someone tell me Cofe what coffee damn good coffee though right tea oils yeah I like this how about a real answer dick yeah resp to damn right damn right you know when there's a problem like U always get popped right and they have open mail relays all the time and they're being abused so you send an email to their abuse department and they have terms of service and they immediately respond to that right bulletproof Hoster doesn't give a damn they just click delete they like I don't give a damn so they use those to host
their illegitimate software and such okay before we get too far into this I'm want to talk about mitigation and this is part of The Conversation Piece here we have a couple different tools at Beal that help us immensely with xplay kits all right so this is I guess a little plug for Open DNS and for funny enough I feel like such a weirdo being a security guy like oh yeah AB is great like really but semantic inpoint protection has an ID buil in and that little bastard catches a lot of freaking Drive buys specifically open DNS has this feature called the drive by download exploits and I don't know who runs that for them I should probably found out and
give them a plug but they do a damn good job it stop an angle left and right so we also have fire ey that just kind of alerts us but it's not inline so it's just more of like hey oops and then we go damn it and then we have to go de so that's not really mitigation if you ask me all right but what about you who here deals with exploit kits on like a daily basis or you know every once in a while who works on The Blue Team here it's okay I don't to say what tools do you use that that help you mitigate them open DNS cool
oh so you basically uh correlate activity and you hunt essentially right so what you're saying is basically they're looking for known ttps that they find in particular samples then they hunt for those in their Network and they say oh look oops right then I guess you can Implement those in your custom snort rules or you know whatever you guys are doing there anyone else what tools are you using what's helping you with exploit kits same same as me or us oh you have web ps's inline okay all right so anyone here else have a web MPS in line that's why what about emps you have M the email appes they stop a lot of the
the same type of Mal that will be dropped but of course not
methodologies
really all right
for legitimate research right [Music]
yeah yep okay so basically he says pretty much an implicit deny situation they white list very few sites of course some of those as you said can be gotcha okay domain tools AP what else are you guys using for your uh domain research and reputation scoring domain tools what else pass total pass total heck
yeah anyone else no fine whatever all right uh open DS investigate that's good bu total API correlations on those those are good talking on all right keeping up with exploit kits now I like to just tear apart the samples I really like reversing and I like to pretend like I'm a reverse engineer like yeah I know what I'm doing and you know I pretend a lot so what I do is I like to pick apart samples but I don't like to sit there and just look at all the different uh eks that are occurring and keep up with their changes and variance and all that I leave that to the professionals there are four of them that I highly recommend
one of them is Brad's site malare traffic analysis. net our sample today comes from that site there's also malare for me which is Jack site he's sitting back there hey Jack I'm sorry I uh can I ask a question yeah did you ask for really out speaker request yes I did hell yeah did yeah oh that's awesome yay thank you that is so great sorry to interrup I'm getting so drunk in this thing tonight that is phenomenal so in the the call for papers they had like a you know do you have a ridiculous request and I was like [ __ ] yeah I do I want a golden chalice that says chaps on one side
bsides Las Vegas on the other and I [ __ ] got [Applause] it that is fantastic when to walk around the hotel like what the hell is that I'll tell you there's a story okay that's so great okay uh broad analysis is a fantastic site and then there's malare don't need coffee just a guy named caffeine runs the site he's extremely involved in the EK scene I swear he writes a couple I swear to God I don't know him personally but I message with him I'm like you know a lot about these okay the evolution of the exploit kit anyone here ever deal with impac back in 2006 I don't even know what the hell I
was doing back in 2006 so I I don't know um we're going to skip ahead a little bit okay let 10 years ago what's up oh you think so look at that now the source of the actual back and infrastructure may have le for impact oh I that okay oh I'm just thinking of what to do with that all right anyway so in 2010 2013 it was really the game of black hole kind catch I like it it's not related to Pokemon is it po all right so 2012 and 13 black hole ran the root like it just literally just owned it was constant our fire I was like oops oops oh I wouldn't shut up it
sucked so the uh alleged Creator who went by the name punch was arrested in 2013 and immediately black bu just fell out the face of the planet so was he the one who actually ran it I still haven't seen confirmation of that but uh come on so after that red Kit nuclear Sweet Orange there's a bunch of other ones in here I don't want to go over every single freaking one those were the major players but angland became the big dog speaking of which hey what you
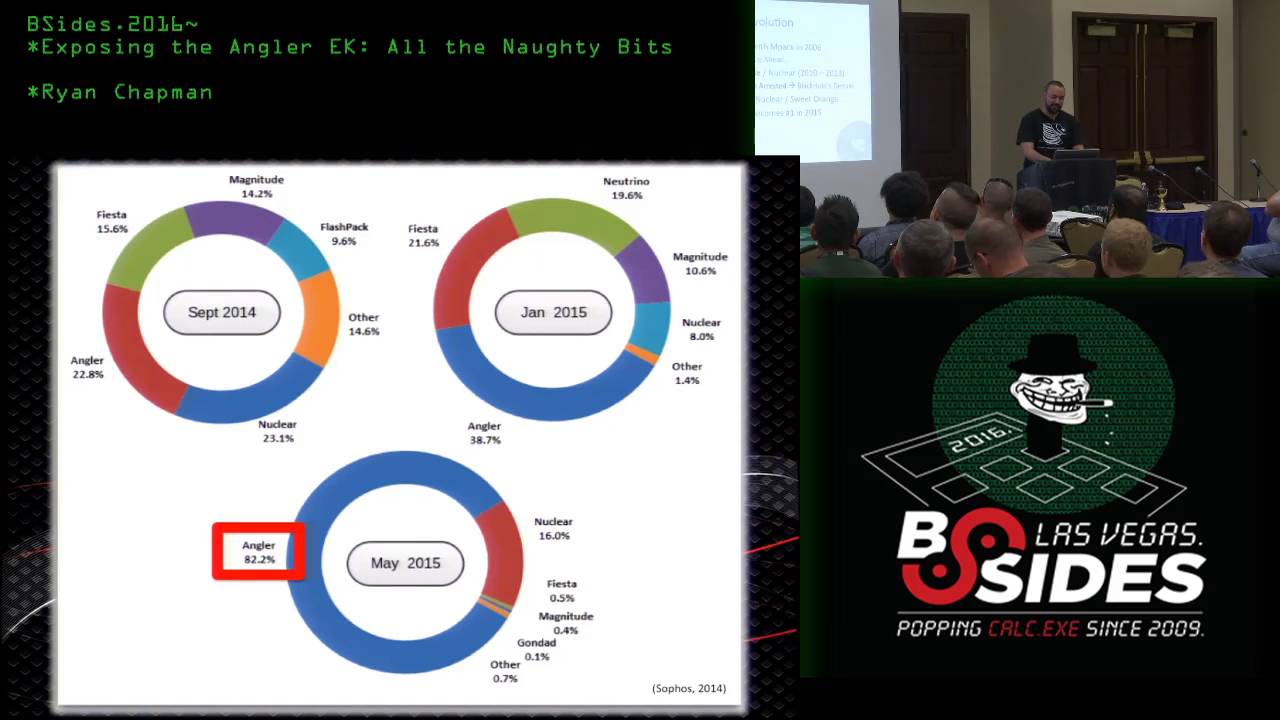
doing okay just pretend that didn't happen moving on so uh you'll see down here in May of 2015 angler had the The Lion Share of the market 82% and it just increased from there there it had a strangle hold really yeah so about that nuclear re word hard disappeared in April of this year just went away I have not seen attribution yet to it you where went away did you stop writing it all right so and then in June 50 people were arrested in relation to a lur malare campaign lur was using a derivative technically a variant of of angler was Triple H right was anyways these people all get arrested and then angler just disappears so the question
was well is is it gone gone or is it just like temporarily gone well the thing is that all the popular campaigns the people that get paid a lot of money to redirect traffic the ones who were very very devoted to angler they all switched to nutrino when I say they all you know what I mean the big names switched nutrino so everyone was like is gone in fact neutrino capitalizing on this cuz why wouldn't you they doubled their price so their monthly price went from 35,000 to 7,000 so that's another and then they made a statement say we're not going anywhere so I was like all right I see what you're doing there and then here's s secure Labs
showing that in June we have well technically July actually what month is this was that projections what the hell's going on I just realized that it's in the future man look at this what's going on here what kind of [ __ ] is that this is August right [ __ ] what did I do last night know am
I just Dr this morning that's all this is actually just going up to Mid June Oh I thought that was funnier and cooler all right so damn it this a recordered right that's going to be funny to watch later all right so nutrino took over nutrino uses a single Swift file one flash file to do all the damage we'll get into that coming up so I want to talk about campaigns first off actually we kind of already covered this the people who run the C campaigns are the ones who redirect the traffic to the landing pages right so technically they can be the same as the people who run the backend infrastructure for the landing page and the whole exploit kit
or they can be completely different so what campaigns are you all seeing in your networks are you seeing them EI test and pseudo dark glit are like the two common ones anyone know campaigns are saying noal what virtual virtual Madonna I'm going to go virtual Madonna CU I like that all right so EI test is an example and back in apparently started in 2014 I we had started seeing an art Network until a year ago is um it uses Swift file you know this is boring let's just do uh let's just do this so what happens is they compromise a web page and in that web page they inject some code that code links to a flash file that flash file
just creates some JavaScript the JavaScript switches over to an HTML page the HTML page then links to the actual landing page itself it was originally called EI test simply because the variable names the ID and the name down here you'll notice they EI test it's evolved since these original screenshots were taken this comes from a malare bites article by surura back in 2014 so it's very ridiculously similar they just kind of change the variable names it's just still called EI test to has a monitor to all right all right here are the tools that we use to decode some of the the things we're looking at the two big players are right here in the middle uh
free Flash decompiler and then flash develop or just without them I don't know the hell this wouldn't be happening I wouldn't know how the hell these things work so we'll get into how they help me out over here oh right here yeah nope yeah FF deck free Flash decompiler and then flash develop by the way flash develop is as far as I know gu it's my favorite I'll just say uh IDE free IDE you just thrw in the ER whatever SDK and then you compiled your hearts content so what I do he's right into the next plot what I do is I rip the code out with FF deck and I turn on decationated the hell out of these
things like I even can put there you're going to yell a bit you're like but then you just use their de obic and you're like oh I can read that yay like seriously without that tool it would have been hell oh man so then I just put the code into flash develop and then I can debug it and do whatever the hell I want he so here's an example this is when you have for example look at these class names that they're importing you see those what the hell is that just keep track of all this silly no that's stupid but if you look up here these features are off but as soon as you turn them on
Gadget [ __ ] so now everything's all like it just enumerates the class names and the variable names in order of how they're executed so it's like even if you're on say you're on class 3 and you're like [ __ ] what getss loaded next it's class 4 stupid yeah it's really really easy to use I love it all right and now we do the actual analysis what time is it oh perfect yeah our sample came from hour traffic analysis this was a the original website was Scarboro cricket.com
it actually leads to a dump and then in the dump there's like five or six there's one EI test in that dump and that's what we're looking at so the malware that this particular sample was involved in delivering it was called and I'm going to butcher this I didn't research how to say it properly so I don't know how to pronounce it anyone know how to pronounce that before I screw it up anyone else want to try no Bard bandor is this bandor [Music] but sure I have no idea I have no idea it's just a locker it locks it you know a locker is a crypto Locker variant W toe kind of thing right it encrypts all
the users files and this one's really ghetto it just pops up the notepad and it's like it sucks for you so yeah I don't want this isn't a Mal analysis of this m this is based on how it got to the machine so we're just going to go like that so here is a little wire shark uh review filtering on get requests and we see here the initial G request was for the compromised site so their scars were real cricket and then we have two requests after that and these are both EI tests right here the first one is the flash file itself because they use the flash file for redirection and the second one which is
very similar to the first one I'll show you exactly how is the HTML page and then from there it goes to the actual landing page and if you're wondering this is a swift file this is a call back and this is the encoded or technically encrypted malare so here what you doing all right I almost do my mouse myself so here's our little guy here and again instead of EI test now it's ner connection stuff whatever that's all about and then I have highlighted the actual Swift file it's embedded and here it is coming down and wire shark but that's that's boring so let's just skip past that all right now I I really want
to go into the full analysis of every line of code and how it works but for sure as hell on have time for that this seems ridiculous I kept getting pissed off because like I said I did this in five weeks and every time I extract more information I'm like y I'm so awesome it was just like this NE rabbit Soul like [ __ ] [ __ ] so for this one what I'm going to show you is what I did is I basically took out this is action script 3 by the way which is what you end up having the debug so if you don't know action script you just learn on the Fly
I so you look in here and what we're doing is we're calling a function called go go calls a function called Dot da see that look right there see how da one then passing two and passing three that's basically it generates JavaScript technically it decodes what you're passing into you know anyways and then there's the URL that you're going to go to so I just Trace these out Trace is like a console log you just shoot right from console right and then we get the stuff down here at the bottom and I've compiled it here so we get a JavaScript function so again flash file for the redirected EI test creates JavaScript the JavaScript is right here the
JavaScript creates a div called D it checks to enumerate the client to make sure they're running Internet Explorer we say that one more time it checks the client to Ure that they are running Internet Explorer now completely unrelated here how many of you force your users to use Internet Explorer are maying that you with management [ __ ] no you're Liars you're filthy Liars no no no no I'm calling BL on all of you you're trying to tell me that you like distribute Chrome or Firefox to your users are you allow them to use
it he say they have free will but they still choose IE cuz yay like if you have a user using iie just show them the screenshot and be like hey stop it all EA test redirects all of them from this particular set of you know campaign redirects we go Firefox screw it all right anyways just B me okay and then what it does is down near the inner HTML it sets it to the base URL of the Swift file itself plus a little suffix that's made pseudo randomly and that pseudo random part is created right here in this for Loop and it's basically going to be a bunch of letters and then one of these suff suffixes right here so I
ripped that part out and I threw it in a loop that runs 20 times and here's an example of the crab that spits out so it's going to be the base URL plus some crap like this our example is right here so in our live C see that Cur fing fun funkin HTM yeah so that's that's the actual HTML page that then redirects to the landing page uh here's some more redirect this is the actual HTML page itself it tries to redirect using two different methods it uses the meta refresh and it uses JavaScript location Stu yeah yeah yep to reiterate look this is all in the background these has no idea this is all happening
all right now we hit the landing page yeah so we've just handed over control of execution from our referring eii test campaign to the actual exploit kit infrastructure nutrino uses one swift file one swift file now one swift while the third time I said that for a reason and it's in bold up there that we've blocked Flash in our environment how many of you have blocked flash really yeah hell yeah suck it right likeo so the cool thing about this is um you remember the hacking team Corpus that came out right when that came out we actually had a recording this one uh we had an attempted thing and nothing happened and it was great so we actually
had we had four attempted emails I believe ironport mitigator for one of our systems stopped it and we looked at it and we're like oh [ __ ] that is targeted as hell and it was right after they had time like hours to weaponize it and we're like oh damn it and there was no patch yet so we kind of freaked out and uh after they released three more zero days from flash within like what was it four days or five a week or something we're like done gone so if you don't have flash disabled by now exploit kid throw some statistics towards management and be like just just cut that crap out I we still have it on our
clients and we'll whitel list certain internal uses and such but forget it okay and here's a swift file coming down it's boring there's the actual that's boring too all right the actual the one swift file had a decent detection back in early July gu um yeah originally for 7113 analysis 25 out of 55 aware even knew it was nrum like how we know that all right well they actually yeah yeah yeah so he's asking if we going to buy our see the Rel detection I believe on this sample it was either that day or a day prior I I might have made that [ __ ] up I believe see what I did there all right
the one swift file and this is what angler also did the one flash file contains within it a secondary flash file the secondary flash file is actually pulled into memory and then executed so when you're doing analysis you're really trying to pull out the secondary file which is what we're going to do so these binary data blobs are just little binary arrays that are stuck in here and they get actually converted into or they get pulled in as a bite array any remember the bite array in action script you can just kind of guess what it is just an array full of B Valu individual direct values for fast machine processing simple as that so
what we're going to do is I don't I don't even know how to I'm admitting on recording damn it I don't even know if you can put the binary data blobs in it I don't write flash I don't know I learned lingo you remember director you remember shock wave you remember that yeah back in like 1997 I learned the programming language for it I studied my ass off and I learned it and then like two months later they were like oh flash is better I was like [ __ ] piece of [ __ ] all right so I don't I don't know how to do that what I do know how to do is I
just manually extract the hex decimal values paste it in as a string and then I use Henry I pronounce his name either Henry T's he. as function he's got a two array and a from array to convert between Springs and arrays get it girl just do it our way and we were drunk last night and Keith cuz he's weird told to put Pokéballs on her chin I don't know why I left him in there all right so we're going to do some extraction here this is where we basically go into demo mode so let me do a little quick time check there oh yeah 20 minutes tell that's do so we're going to move over here this is a Windows 8
malare VM technically I actually got this when I little plug for S Institute their Grim 6 forensic 610 is their JC reverse engineering or malware certification so I went through that phenomenal class by the way and I just used this for my Windows 8 stuff cuz it's I like it so what are we doing we're doing a stage one actually no we'll just open I'm just going to open up flash develop directly and show you how I extracted out of stage two so this is the part where it gets a little like two-way communication is going to be kind of an because I'm just going to show you a bunch of code crap but I'll see what we get so this
resolution is horrible but that's fine all right we're going to compile it you're ready oh demo gods don't be a dick oh it compiled holy hell all right run it no that's oh I probably should have opened the proper project funny enough I really didn't plan that if you read that on the screen that was pretty funny that was 100% an accident but I enjoyed that thoroughly dumb ass all right uh so here we go we're instantiating the class name that they had and then we're starting a start Dam it. derp which is going to do this yay all right the first thing we do is we fill this array called Dam X and well it was called X but it was pissing
me off so I changed it to Dam X and Dam X is over here right there so this array holds some uh flash Bas commands EV been listening adding children to the stage load bites they try to off escate by just using this array of referencing index values in it rather than using the phrases whatever whatever so we fill that we do that okay go again and over here it's a looking for a stage environment if you don't have a stage environment you're probably in some kind of debugger or some type of working environment so I just skip the part where we check for the stage and I just I just call it function so we call
this function called R and R this is where it gets kind of funny because sometimes they just give you like these really freaking obvious names with their variables like they try to make it so hard to read and then you have crap like embed additional info and you have even better embed rc4 key oh RI an rc4 okay that's just the variable name there that's kind of weird so we're loading those and this is what we're doing here see how I I'm using the function two array and then I just have a big long it goes off the screen heximal value we're just making our own bite arrays because that's just the way I do it so once we do that we then start
this guy right here embed Landing this will eventually be the variable that will contain the decoded second stage if you can call it second stage technically I'm going to uh Swift file that's going to be loaded into memory so as we scroll down all those different you remember that big list of binary blobs basically those are all just catted see right bites right bites right bites and blah blah blah blah blah so we're just going to skip past all that and then we call this function there you go and then we call this function called D and D is actually a decoder so I guess they call it D because it decodes that's cute and
we pass in and look I didn't write that they wrote that you pass in your rc4 key and then you're encrypted Swift file and at this point now it's decrypted so what we're doing now is we're going to change it from a bite array to a string and we're going to call it stage two because I just that's what I just want to call it so we do that and then now we're going to trace it so tracing it again just means writing it out to the console so as soon as I step over this down here this is the two file we want so I basically just pop that into a x file and then I there it is now you'll
notice that down here what it does is it actually creates a loader a flash loader and then a loader reference object and it does some more crap you don't care about and then what it does it's actually being sneaky little chump right here see this uh function called m not only does it decode the second Swift into memory but then it passes a bite array to a specific function in that second Swift file and the purpose of that is multifold actually but one of the good ones for like trying to stop dynamic or static analysis is if you didn't notice that and you simply extracted stage two and you tried to run it it would be like where's my parameter
you're like [ __ ] parameter I just run it so it's another deop attempt it also makes it so they can reuse the second stage container and just push new arrays into it so they can quickly weaponize new crap and push out I'm sure it's for other things too but I don't so as soon as we pull that guy out I popped it up on virus total and we had a detection ratio of 12 out of 54 and this was uh a couple weeks ago on the 21st of July so stage two I just did that moving on stage two is is they like stepped away from the obis and they're like oh hell no one's going to find this
so we're just going to name everything like exactly what it is so there's some binary what are they call binary data blobs again and they're literally labeled like nw22 but see this Swift right here see that they're telling me this is a swift file for an exploit and that's one and that's one and this is a BB script exploit and that's one like oh okay thank you so doing analysis on one of these exploits I identifi I didn't identify a damn thing it was identified as CBE 2015 8651 this is the one part that really pisses me off in this talk because I wish I had time to personally rip all five of these apart and find out exactly
to ensure that they are the proper CDs that I wanted them I time I had to change for manually damn it so this particular CV this is what buyer total set it was so if this is what it is it's just an integer overflow if you're not familiar with an integer overflow essentially if you have a bucket where you can store a certain amount of contents and you fill it up and you overflow it you start overflowing your data into places that should not reside sowh you can probably get the instruction pointer to point to and then you can get remote code execution and [ __ ] like that so ah let's go uh let's go pull it out
we're going to take a look at the St two file now wait just go till 55 yes [ __ ] yeah all right hey how many people here have never debugged shell Cod before in your life raise your hand your hand was first you want to help me out later yourself you screwed yourself
bro well I mean never mind all right ask to borrow the cup what no what all right here we go let's do this and we're go back into flash develop we're going to load stage two and we're just going to kind of run through the code so if you're wondering what's going on from this point forward now we have stage two extracted out right and we have also have the binary data that was actually pushed into it so we're going to manually just shove that crap in there and run it and I'm going to debug through it show you exactly how it works eventually once it it creates these five exploits we picked one I
grabbed one of them and I analyzed that one but we don't have time to deeply analyze it so I'm going to show you the Shell Code we're going to walk you oh should I thought he left I was like did he leave what the hell screw that guy I'm not doing that you sir what's your name Ned Ned I said like you just made that up Ned Ned over there he going to we're going to actually have him debug the Shell Code and we're going to see what the Shell Code does it's really weird I don't know why they do it you'll see all right so here we go we have stage we don't we didn't do it yet we're going to
open up the proper file before we do something stupid again stage two CL that and Main okay so in stage two we are using get it girl and we're passing the array that I extracted out of the previous silliness from that M function so this is the stuff that's supposed to be hidden like you're not supposed to know there right we'll just pop it in there and what that's going to do first we're going to compile it oh that's new but I can make that and I will okay get your type declaration okay so as soon as we start debugging we see that we're in this method three ET gets called over here that runs method three we go in here so
all right what are we doing well first off we're getting rid of this that's my way that's my way and there okay first thing we're going to do is we're going to call method six method six is going to create a variable with strings to enumerate the client meaning it's going to find out exactly what machine it's running on what browser it's running on the fun stuff right so let's take a look at how they do that I there we go so lost my place there you go so what this does it uses a combination of two things number one is it uses external interface. call anyone from external interface from action script it tries to grab the container to
the engine that's actually processing your client side browser scripting meaning it runs JavaScript in our case so we're going to run JavaScript and some of this JavaScript does stuff like this window. naavor doapp name simple as that just regular JavaScript commands and it pulls the results back in another thing it uses is it uses action script's capabilities feature which I just found out about so apparently within flash Within action script 3 itself you can enumerate what it's running on and such using capabilities Library okay so it's going to grab if there's a debugger present the resolution of the screen it's all this crap so we're going to step past this and then take a look at
the results didn't step past now and bar one so here are the results of processing that screen resolution is a little off here now by the way I bull I lied I lied to it I told it that we're running i1 Netscape with my window name we're running Windows 9 with Windows 8 on full string and I I gave the user agent string for I don't know something I pick one and uh so I just like to it instead of having it try to process that because we don't have an external interface available it might be bugger so I just told it that we had stop and move on the life all right next so we're going to
call function 8 and our method 8 what don't you dare what you doing I just H the wrong key cool story all right so here we're going to fill up this variable called variable two and this guy does my locals am I blind you see local over what did I do all right whatever there we go so a variable two now is this do you remember that bik array that we actually pushed into the secondary Swift that was extracted out what was in that well it just got decoded and what was in it is this stuff over here there's a list of links these links the back URL means like if this if the exploit fails like just go back to
where the hell you just came from uh I don't want to enumerate all of them but some of them are for the specific exploits and there's also a ping back so what this little sucker does if it finds out that it's about to run an exploit it hits back to the server and says hey we're going to run this one and it just helps understand which works best in what environments basically or at least I think that's what it's for I don't know and then here they actually give us look they even call it key for the payload there's our decryption key for the malware it's going to download later oh cool thanks could have OB that a
little more whatever and then here are the actual whether it's going to run these particular vulnerabilities so three Swift or Flash Bas vulnerabilities and two IE BB script based execution chains that's going to try to exploit okay so we jump on past that stop hitting F6 F6 yep all right now we're going to call method 10 I don't know what the hell it does here's what it does oh now we're looking to see if the client is actually inside of a nonstandard like browser type of environment we're looking to see if we're running Phantom node.js couch JS Rhino which is a a front end basically for the fire monkey JavaScript engine which runs in like mosa Firebox
and then also if for in a debugger so right now this is part of checking to see like should I run right now or should I like back off is what it's looking at and we're going to lie to it of course we're just going to say yeah dude you're good and then we're going to run into method 11 method 11 is the Ping back and all this does it creates an image location and that image location is just going to Ping back to the servers by just trying to access it and all it does is it tells them like so far so good is what it doing pretty simple stuff surprisingly enough at this point
right here it does not provide an identifier it just loads a standard source and gives the link for JS ping so later on however if oh anyone hear the question I'm
sorry that's horrible I plan this all wrong okay so screw all that all right here's what it does at the
end [ __ ] ah cut me off do I have to leave can I do five questions sure yeah okay so skipping that slow stuff over there here's what happens exploits in a row like ducks sitting on a fence being shot down we have duck on from you threw me off my game we have two different DB script and then we have three different flash exploits these are separate flash files that are once again loaded into memory right so let's go take a look at one of them I pulled out one of them and the one that I pulled out was this one right here the one that executes what I believe is this G right here now when I
extract it out I was going to show you how appar typ so what it does well actually first up I popped into into virus total this morning actually I forgot to upload the virus total like oh the virus to when I did it only had five out of 54 hits and that's actually what tells me it was potentially this particular CV the signature which I don't fully trust but based on the actual chain that I was going to show you it does look like an integer overflow I just couldn't confirm it a time so but notice it actually Associates it with rig see this little guy right there rig is one of the other popular exploit kits right now it's not
as popular as nutrino but it's probably number two I'm assuming right now pretty much so what does that little guy do well essentially it loads up some Shell Code are you guys fam the concept of Shell Code if you're not oh I love the slide in y shell code is essentially what you're trying to do is you're trying to change the instruction pointer in the CPU which is what tells the CPU what it's about to run or actually execute you're trying to overwrite that with the beginning of your personal code so once you can obtain that the CPU then starts processing your code it's called Shell Code from an old term just coming from usually it was used to pop a shell
or like a reverse shell so that I can maintain access to or get access your system I should say so we're going to take a look at some Shell Code the Shell Code that it actually loads in this Swift file does a couple things it finds itself in memory required I'll show you why it exor the rest of itself to prevent static analysis and then it actually creates or calls process create a which is the antiv verion of process Creation in the windows Library so here's static analysis of the shell code the problem we have is down here see where the analysis fails down here well that's cuz see right here see that 9 a value that's a single bite exor
key that it's going to use and it's going to Loop 596 times heximal times and as it Loops it's going to decode itself so static analysis fails flat because it's it's not exord so we're going to do live analysis oops IGN that all right was it Ned was your fake name Ed yeah you want to come up here and decod the showell code
okay I pop the Shell Code to an executable we take the executable and we drop into Ali debug two and Ali debug all right what you're going to do is you're basically just going to be pressing one of the F Keys when I tell you okay all right now hold on the first thing we're doing here is the shell code is actually going to jump down in itself so you'll notice here it's going to jump short so go and hit F7 so now we just jumped over here see we jumped this memory location this memory location now is going to call back up here so why the hell is it going to do that anyone know
why what's that yep so when you do a call wait what yeah sorry when you do a call in Assembly Language you're doing two things you're pushing the next instruction location onto the stack which is kind of like your working variable Zone let just consider that for right now and then you make a jump now the reason we're doing that is what why do we want to have that address on the stack for bu what I'm going to now know where I am I'm going to know my location so because of address space layout randomization and windows was a Vista and uppr uh sh C whenever it starts to execute and even when you're trying to exploit something
you have no idea where you're actually going to land in memory so by doing this it's finding out where it exists yeah so go and hit F7 and look down here boom see that now we have the value where we we reside now all right go ahead and hit F7 we're going to pop it so now eax up here contains our location so we know where we are all right hs7 again we're going to clear ECX that's the counter register so now we're going to basically start to Counting we're going to move this value here into CX 596 and HX go and hit F7 and then we're going to start our Loop this starts the
loop right here oh oops I'm missing my uh there you go we're going to start the decode process so go and hit F7 right now we're moving we right now we're actually going to EXO by 9A and we're pointing to this location over here following dump memory address so right down here we're going to start xoring these values all right go and hit F7 and you'll notice it just changed from B something to 22 and if you keep it I was going to go through this more time we just got to keep going yeah so basically yeah exactly what it's going to do so it's starting at the bottom and it's xoring it's revealing itself coming
back up toward the top so what we're going to do is we're just going to click right here go ahead and hit uh F2 and then F2 again and then hit F9 all right we just what you do what the hell did you do Ned you dick all right so now we've just done is we've exor on exor basically so if I do this oh hey look that's the data that was hidden previously so this is all being done in Shell Code in Assembly Language on the processor right so now what we're going to do is we're going to jump so hit F7 and then F7 F7 guess what F7 and again and again and
again fcking that thisy he's like yeah okay this right here we're pushing fs30 points to what's referred to as a process environment Block it's part of the thread information block the tip so essentially what that does you're trying to find out information about processes that are currently running so what you want to do is hit7 again we've just found intd it was just up there so what it just did is it just found the location of ntdll on the system we're looking for colel 32 when we find Kel 32 we can then find the functions that live inside colel 32 and then we can call it and do [ __ ] so hit F7 again I did I
write this did did you just write that L and you I don't remember if I did that or not all right7 again again then one more time yep then one more all right one more all right one more okay one more and one more and one more all right what we're about to do here is we're about to load the functions that are actually inside Cel 32 so if you look at the very top right hand side up here hit F7 one more time I like do it one more time now there the first thing we have up here is a function name acquire srw lock I don't know what the hell that is Okay cool so
what we're looking for right now is now it's going to start a loop it's looking for a particular Windows API based function all right so we have a little bit of time thank you very much Dad much
appreciated it's going to take the string that it has right now and compare it to these this value here and then if it finds that part it's going to compare it to the next value here so this is basically what it's looking for we have the values of what it's looking for so when we decode that like say we just pop that into python it comes out as we're looking for Eric Eric's ass yeah anyone here name Eric anyone put your hand up your ass bro no whatever okay so it's actually started in little Indian format so it's actually backwards so we're looking for something that starts with Crea and ends in sa a which is create process when we
find it we end up right here so let's just do that guy two f n take that off f n all right so we just found the process that we want and then I'm just going to expedite this process hereit
wait for
it all right so I skip fasted because the time got me what a dick all right so what it's going to do is we have this data in here and it starts with command. exe see right here so what that's actually trying to do is the following it's just calls I was going to show you where it loads the argument but I wasn't looking in the right place cuz I got Rush of time so I skip it that's fine what it's going to do is this right here it's going to run this there's also some officiation here the carrot if you try to run out in a JavaScript interpreter it tries to run an exor dick you have to
run it in command prompt oh stop now which comes to this and this actually just executes the malware so it opens up a stream on disc I was going to show it to you but we're basing at a time so this right here here's the thing though why the hell does it do this the Shell Code does not execute a call to like URL download or something but rather it runs command prompt in additional JavaScript that functions as a downloader so why the hell does it do that I don't know I don't know why do maybe I don't know man like that's St just do it you have code execution on the box so anyway so once the malare
runs in this case it was the B so it enou disc and then everyone screwed everyone so that's it that's how uh that's how the trainer works [Applause] for about this right now all right any questions no I didn't watch it I was hoping no one noticed that thanks dick hopefully it was watch I don't know went in Vegas
right yeah yeah that's it now uh you talked about how a JavaScript will pull down in a swift file yeah Swift file so if you're blocking a JavaScript or at least making it so you have to click on yes run this in the popup will you see that it's coming from some wacky URL SL whatever that's thewi file bring you down that's a damn good question so the JavaScript is running through The Interpreter that's inside the flash plugin and I don't know if that particular aderes to the same settings that you have in your browser everyone cat saying when the javascript's running in the Swift file like if you have JavaScript disabled or like it pops are you sure you want to go
there just play stupid like would you actually see that the engine is technically different but I don't know if they tie it back to those settings so browser so so you may not you may not be able to to see what's happening if you have JavaScript in the browser yeah it depends that's that's something good to check though what I'm going to follow up with that that's a good question I like questions yeah
damn good question he said it looks like it's all flash based JavaScript I threw that in for you stuff right so why does it depend on IE well first off EI test depends on IE up front but neutrino also I skip that I'm time about it does do some checks on the host I forgot to show you that by the way it does enumerate your host it looks for EET it looks for malware bikes it looks for FF decoder which is funny ffd DZ it checks to see these things all installed there's a whole list of it again timing wise I forgot to show you that I was even your feedback bu's gone anyways yeah
so I forgot that you oh why is been Explorer well there's two VB script exploits they're specific to IE because only IE runs VB script right but for the flash based ones I don't know because in the flash based ones that I analyzed nothing in there was solely dependent on IE so I don't know yeah Che it's running AAL Environ sure the hell does how much time we have like a minute or two yeah we have two minutes technically look this is the part that I didn't show you guys yet so there's JavaScript I jump to the the Shell Code because timing and stuff but over here uh actually over here and there and look
it even says debug me okay I will and then we open up this and we hit that so this JavaScript executes like this right before the final exploit fires off right and what this does it fills this variable V and then we can just be nosy and take a look at variable V and if you look at variable V here's what it's looking for it looks for virtual box it looks for VMware tools Fiddler 2 which is just like web based logging stuff wire shark FF deck so the program that I use for my analysis it it'ss installed it won't run uh EET antivirus Bit Defender there you go there's a list
soing yeah I didn't even think of that's pretty simple if anyone didn't hear that to protect yourself just install water shark so yeah it's going to look and enumerate to see it's installed be like right yeah right just pushing out the ACM what you're all right we're pretty much I got double stop now which means shut my mouth so all right G thank you very much