Deconstruction Of A Linux Adversarial Toolkit
Show original YouTube description
Show transcript [en]
all right so yeah this is a presentation there we go so it's it's it's very light so it's so malware malware is a good thing to do read all right either way so so what to expect so today we're gonna do a rough I've only got about 20 minutes 30 minutes so I will talk quickly and some of it will be a little bit higher level but effectively you are here today making sure you're in the right presentation the sample 78 deconstruction of the Linux adversarial toolkit caveat did appears the little clicker didn't particularly work with my Mac so I may be backwards and forwards pressing a spacebar so bear with me all right so Who am I just some guy that
likes computers some random dude and just stumbled up on the stage if you wanted to know a bit more about me I won't waste your time there's some information about me in the schedule pamphlet and you come chat to me later if you found interesting or tell me off either way so some things that you probably should have to get some value out of this presentation so it's imperative you actually know what a computer is aside from that knowing what Linux is is probably a good step as well being scared of system calls is probably not a very good thing for this presentation being able to read a very light amount of assembly is welcome
however a lot of the stuff that you will be reading is in source code so it's not too bad it's important you know what implants and controllers are and most importantly you can get over the fact to think that it's only Windows that has malware malicious actors do compromise other platforms that is definitely a thing so let's go what to expect inside this presentation so in the theme of summer gnats expects a full tear down and rebuild of a Linux adversarial in use implant it's not like some implant that found on the internet from like ten years ago whatever it was this is an in use implant expect the analysis the original binary expect the
re-implementation of the original binary back to source code and also expect an implementation of a compatible replacement controller so the controller was never available to me so I thought whatever just rot my own so just quickly I was gonna get back here - Who am I so the only thing I'm gonna tell you right here I need a caveat here as I am a Queenslander so we are by up by all means the most Australian people that live in Australia so I will try extremely hard to behave myself but the way I would have said that last point in Queensland Oh would have been [ __ ] it I didn't have the controller so I just write it myself all
right so just please be aware I will try to behave please know this presentation if it seems a lot on the details come see me afterwards a chat it was a lot of work that I pumped into this before I got to slides and I had to condense this thing into under 30 minutes I just please keep that in mind if you think its life but I can answer any question that you have about the thing under the hood alright so second caveat copyright information I did not write this implant the implant the original one is not mine if there's a person in the audience thinks that it's your implant I'm cool with that would you hand up your lap if you're a
bit weird about that happy to come and have a chat with me later I do have questions and if you're not weirded out I did make some bug fixes so if your your organization takes commits upstream more than happy to make some our promise I won't include any back doors to your back door promise that's a price all right so the sample so this particular sample is one binary within a suite of tools used by an active actor and when I say active actor locked in the last six months it become an analysis candidate due to the fact that during Bonnie binary triage it appeared to have some really novel and interesting features and siding that I figured your mails
well dig into this thing and see where this is going to lead it is a 64 bit elf binary so 64 bit Azzam 64 bit into a platform assembly and it was built on target using GCC so that's no indication at all of how how I knew or how recent it was it's just the particular bill was 447 which is circa 2012 that's fine we're looking at about 58 cave of binary so we're looking at all right so as far as the analysis component goes we have two parts there's presentation there's an Ulster component and I've got to have a small number of slides for reconstruction but then we just go into a demo because if we do the
analysis you don't really need to see me do it twice so it's so as far as the analysis goes static only it's only saying as some of the other day when one of my mates one of my colleagues we're having a chat about I hear dynamic static and I'm like whatever mate I like to read the book and I like people reading it to me so I just artic analysis this will be my last Ida Pro project from next week unfortunately I've already installed the JDK under my machine and from next week I will be using exclusively Ghidorah so get on that bandwagon nice and fast so this is a full reverse-engineer like full software reverse engineer of a sample
back to complete source which is not my typical way to perform analysis for those that in the audience and I'm sure there's lots that do analysis usually it's fairly surgical you typically approach analysis for binary with a subset of questions and if people request the analysis of you look if that's the kind of business that you're in and you reverse binaries for a living as part of an organization typically you get really [ __ ] off when people asked you just tell me what this thing does because that is by no means anywhere near providing some kind of app specification for you to do in a timely fashion however in this case that is exactly what I've done so I've gone from
sample binary sample back to complete pretty close back to complete source and I was looking about few capacity hours of a soft reverse engineering to do that for a small sample 58 case ample alright so as far as analysis goes there's two things when I have a quick talk about so one we got protections and command and control because they're the most interesting things well everyone will just leave if we have a chat about how it took me maybe I don't know five six hours to reverse their custom argument passing for like argh see and I'd be that's not very exciting so protections so this particular sample had a few novel low sophistication user mode protections there's binary is user
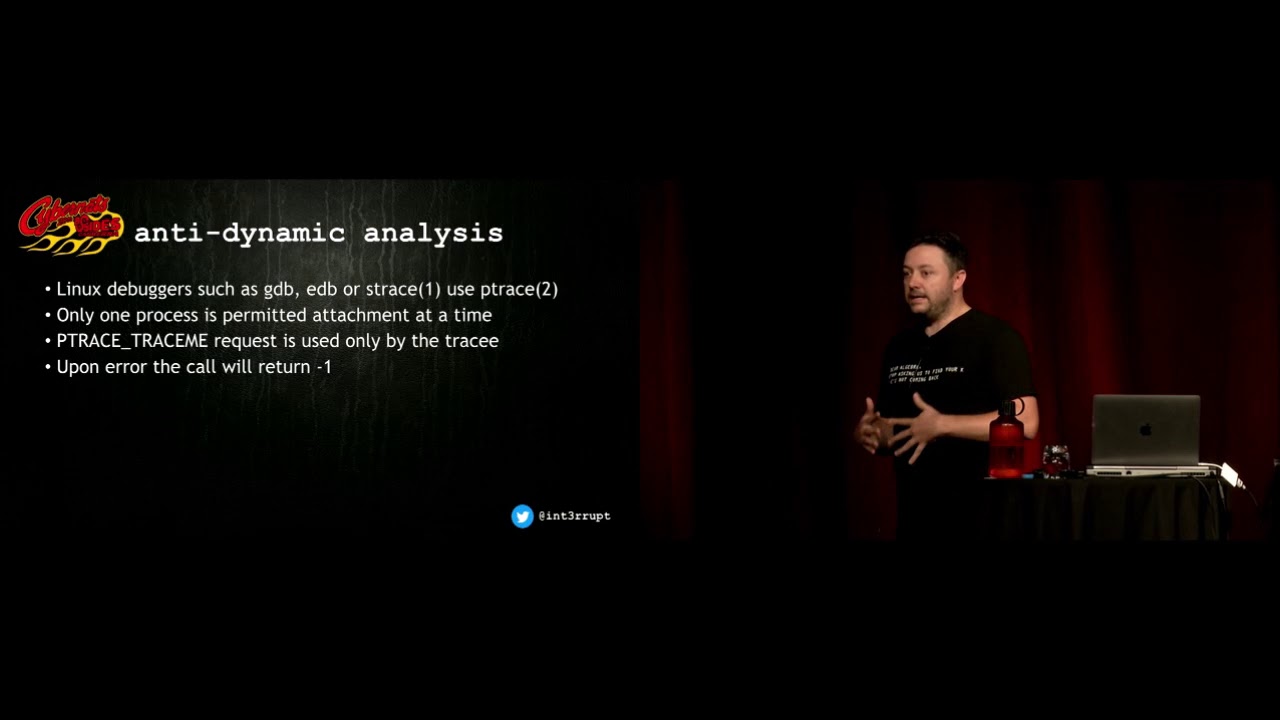
mode there's no kernel mode component to it had some anti static analysis some heavily obfuscated strings can't thing you'd expect in a typical sample we're not going to cover that in the slide or is presentation it did have some anti dynamic analysis and it also had some anti forensics as well so let's let's hit off on some of those so I know this might be small for some people to read but if you can there is value in there so the particular binary had a function which is now back into source code and this particular function did a few things mostly for anti debug and it would ensure that your ancestry so your parent process that is calling
this process is what you expected expect it to be so at the top there we have some hard-coded names of expected processes which include what we got like start proc que order D system so thing processes that you consider to be legal not anti debug or not debuggers and not processes that may be nasty to you're nasty and on top of that as well it does another nice thing so I saw it from just checking who your parent process is it also actually does some debugger detection as well so and this gets called in various places inside the implant just to make sure everything is shipshape and things have been changed as is performed execution and there's
two different ways this particular function will operate so it'll either give you a soft exit so it'll just return with a return code then you can decide the calling function what to do once it's returns if it says it's found something it's not supposed to be there or alternatively it's got a strict mode where you can exit hard and you just quit out of the environment and again this is not just again to reinforce this is what was implemented I just went backwards so it's none of these heat things in here my mod mark modifications so one of the interesting two in here though towards the top you've got a function called P trace me or I call PP
trays me and for those people that have done some debugging in Linux or they've hit any debugger stuff in Linux before you might be filled in with familiar with a system called called P trace so P trace is what all your typical debuggers use so gdb s trace et cetera et cetera P trace system call it allows you to be able to debug a process and give control of the process to another process or alternatively a tracer can request access to another process interesting things about P trace is that only one process is permitted to it be attached one process submitted attachment at a time so you can't have multiple processes actually attaching to your
process to debugger at a time that significant another significant factor as well in particular function that was called inside this implant is that it call something called P trace me so there's a whole lot of different ways you can call P trace with a whole lot of different requests this is one and this is the only particular one that a trace you can call as opposed to a tracer and if that doesn't work say for example someone's already holding your process it'll return an error code of negative one didn't work this is this is what it looked like in the binary so if you can see here if you're not familiar the symbol that's totally farm and you'll see it called a
P trace you'll see the number one being loaded into EDX which is saying call me with the P trace me option and if the thing doesn't work you'll see on the right hand side if it's less than what's expected it'll call it'll call exit with a one so what that you're seeing there is that if it tries to say yes please trace me whatever it is and it's already being traced it will [ __ ] itself and quit out so a TD button novel small but does the job call the multiple place in the binary so this particular binary also had an implementation for anti forensics as well so incident responders and forensic caterers in the audience would be very
familiar with the concept of you know disc analysis or metadata analysis and chronological order of artifacts and you know timestamp metadata time metadata creation/modification times inside file systems this one here all this implant also had a very novel way to actually deal with that as well and employers anti forensic technique which we call time stomping and what it does here so this particular function which again is called in a few different places what it does is you give it you give the function your destination file that you want to stomp that you want to change this file time because you want to move it within your timeline your chronological order to sort of throw apart the investigative ability of a
friend's account list so you give it a destination but you can also give it a source as well so it will copy its time and then update its own modification time and its own access time to effectively blend into the environment so that's exactly what this does here using function calls within the Linux called stack so you can call stat on a file in Linux it will give you its honored information and inside that inode information it will have meted time metadata information in there so it copies that and then it users you time or update time to then write it back to the nasty to the nasty that you're trying to hide there is
flaws in this I don't half the original developer of cared or knew whatever but the thing is with using you time it only actually updates access time modification time so there is a anti forensic floor in there your creation time will remain as it was nice to know all right so let's move on to command control I've no idea how I'm gonna put on them either all right let's move on to command control so this particular sample so what made this sample interesting sorry from those few novel techniques for for protections was the way it went about its command and control it used a novel method that you know when you read these things you're like ah [ __ ] like what am I think
of that lot I should have done that you know mainly it's what the person that invented the potato peeler is like that was a good idea people like to peel stuff you know mean works so I said use a novel method which is what's highlighted a sample for me to tell you about it today and aside from its the way that it talked to the sample so way there you know the unknown controller that we never have a copy of talk to the sample which is cool implementation of the actual implant itself was functionality that you would expect from a typical backdoor rat so that's the kind of stuff that's inside the sample all right so it's now we're
going to see that solders talk through it so effectively what this sample has doing at a very very high level to be able to talk three up for the controller to be able to talk to it typically in a network environment you've got oh you know if you've done some soccer programming in the past II but listen for a socket you know you've got a your to bind to a port and carry on and [ __ ] around whatever they say in this particular case here in this particular case you and that and that's not very good because like if you're on linux and you see like you know like a net stat like what tln it's like are there's some
we something weird listening on there and look at the process and I found the badness so that's as far as OPSEC that's not that's not a really amazing thing to do so I'm sure I'm Jimmy there's a few people in the audience that have like used like Wireshark and stuff before I'm sure me that's not a and I'm unknown concept to some people and be able to like you know look at a packet capture for some people that I've used Y shark I'm sure you've also used it too actually perform packet capture as well so I'm not just like look at someone else's pickup actually take your own pickup so why shark and it's command
line brother TCP dump actually use a library call we pick up and this implant also does that as well so what this particular implant does is instead of doing soccer programming it decides to do lead pcap programming and it writes a filter so well first it listens on the any device so the any device is using lead pcap it allows you to listen on it on any of the devices that are actually present or resident on the machine that does have a few caveats because with the any device so if I was to write this implant I would not use that and because I reckon that's a really bad way to do it so if there are
some cabinets for the any of any devices that you can't put into promiscuous mode so the IP packets have to be destined for your machine and if I was trying to do something clever I would just like not do that at all and just listen actually look at what the common device is that I want to use and I would just listen on that device turn the thing into promiscuous mode and then I could fire packets to anywhere inside the segment and I could just task on that so there's fire if you're if you're doing packet capture on some kind of like IDs and I'm not a network guy so if you know me you'd know how much I love
ragging on people that do network stuff so it's so if you're if you're like you know I got this new beaut ids/ips packet capture layer to whatever ain't got to do nothing for you because you're going to see telemetry going to or tasking going to some random device in the network and meanwhile your implants sitting another host and there's just sniffing stuff and promiscuous modes that's why all I've done it I would have done a lot this spilling so what it does listen to the any device packets that are destined for it it then filters those ones outs or only wants TCP and even though it's only wants TCP it takes any packets on any port so any packets
that come in is TCP Don the entire port range and what it does then it's processes those packets so when you do lib pickup programming you eventually go into this pcap loop and then you give it a callback function and you're able to process the pcaps as they come in to do whatever you read them you know transform them do whatever you want it's very roughly how very basic like IPS or IDs works and that's what this does so reads the packets coming in on the network completely skips the hold TCP completely skip the whole soccer program paradigm so that's that's great so what is what is this callback do so what this callback does it actually goes
and parses so again this is this is not leap big cap code this is code from the implant but the code goes and goes and passes the data structures and make sure that the IPS version for it goes through and you know checks some lengths and whatever some other garbage so but then interestingly it goes on to check that certain flags of your packets are set for tasking to fire and then if those particular flags are set it will then go and read the TCP payload it will process that and then after that's process then it will schoo and do your execution so that's the way that works so you'll see in the demo so I won't keep waffling on
so in a nutshell so listens to roared traffic on any device filters that traffic checks the presence of the the acknowledge and the push Internet Protocol flags if it passes that it then it decodes and decrypt the TCP payload and then a processes and then executes that payload all right so control so what kind of tasks we'll be looking at so interestingly the first thing it does so this is inside the decrypted payload so once we're inside the decrypted pilot the first thing it does is it checks a password that's interesting silent inside the inside the payload itself which I would deem to be actually be a campaign code hard-coded in written for the food for the individual victim and
then it goes on to check to see if it's one of seven different tasks so we have you know about this password and a semi colon a colon and then we have the the task string and another colon and then if the particular task requires arguments to it and IP address a string whatever it is that all comes after and then after it's been processed we hand it to the execution function and the execution function is what does the business so and what this does here doesn't do it inside its processes Forks off a process does the execution the parent waits does it stuff so in the original sample a few interesting things now like above like just the boiler
itself but the original sample had four tasks sorry seven tasks but only four of those tasks had a couple me implementations so even though the binary the network protocol is geared to at least take seven that we know of commands it's only been implemented for four I only had three in mine because two of them were very very close some 40 or whatever keep going so so of the three tasks that were in there that override implemented so we've got cabe it to which you give like an IP address and a port which is a number password so we have a password protected which is again that passwords hard-coded just into the into the implant a reverse shell and
this has no terminal support which is very very different to something that you'd expect to use like you know SSH that has you know for you know PT wire support which is effectively what KB did so it's why sort of mush them into two for the sake of timeliness it has another another command string command called tack bow where you can give it a string it is executing arbitrary command but you don't get anything back it's just a single shot so you don't get anything back coming back to you so nothing from standard standard error or standard out and also has a lead command a IPT which actually disables the firewall so if you look back here you
can sort of see up there you can see like the task number six effectively all is doing is just firing down like an Diane iptables configuration command for you to accept everything it's pretty cool alright it's a reconstruction so the original sample I have reimplemented in ANSI c99 it's pretty much 80% complete I will finish the rest the proof asam's a proof of concept controller was written in Python because that is like way faster and my objective was to ensure that my implant and my controller were interoperable with the original sample which I can test and hopefully the unknown controller that may be used for one day all right so some considerations though so descent
ask him to the control and we sort of already talked about this before with you know like socket programming descendent asking to the controller you need to transmit be encapsulated traffic so the encapsulated tasking inside a valid TCP network paté like encapsulated in TCP protocol typically this requires to connect them to a listening port on the machine so in this way here so you know as we just said before we know the way the implant listens tasking it hasn't bonded to a socket it's not listening so how do you connect to this thing so typically the way you would go about this is you may say connect to like a an existing port you might do like a like a some kind of a
scan the environment see what ports are open and you might connect to say like SSH whatever 80 HTTP whatever it may be and then even though you're at the application layer it has no idea what's going on you just fire the stuff anyway and that's enough you've passed enough gates at this point for your implant to know that it's that the traffic is for it so even though you're seeing stuff coming on 80 it's actually going to something that's that's not listening on anything at all they're on I thought that was a bit [ __ ] so my controller actually implements its own one-sided skeleton tcp/ip stack and so what I can do so just the transmit side so what I
can do I can descend raw packets to it I can skip the triple handshake and I don't need to bind to a port at all I can just send whatever I want whatever I want it doesn't matter all right let's do demo yesterday what if this gonna work so I had done live demos in the past that was a bad idea so I've got a movie all right okay so what I've got here so I've got two VMs do everything in console I've got an attacker and a victim just want to say how awesome vagrant is so if you're not a Hoshi Corp user become one it's fantastic so so we have attacker on top and a victim and
I'll talk you through as we go along here we go all right so just to demonstrate me this is just to demonstrate some stuff say yep saying Who am I one of our ID yep the victim the attacker whatever it's interesting to what's important to prove to you that we're actually on two different hosts within the network so there we go there's the first one you see dot one three six it's fine sitting on the same subnet and the victim should be close by probably next one over one three five that's fine it's totally okay to like go and break into your neighbor's house it's exactly what gonna do here we go so netstat so
just to show you as we go through you know what's listening what's going on so the only reason I got a tea is cuz I install the package just before this that's awkward so it's netstat so it's all we've got there is 20 SSH saying for the victim SSH what's next it's like watching movies awesome my son thought this is so wicked I tried on him we thought it's fantastic alright so just to prove to you I wrote this thing so I got an implant let's see that's compiled are we going I'm sure lots pill that right see that it's like what option comes neck on GCC is takes so long I mean here we go implants uses
lip pick up implants threaded there we go so never happen implant that's right see what that does it runs but your runners route so in the implementation it actually checks to make sure it is route which is very important for a few of the features inside the implant one of them being is that you can't perform packet capture you can't connect to the to the raw PF socket unless your route it's very important so has to be route it's not an issue it's not a mess this is not the implant was not about proved esque it wasn't about persistence you can do that in other ways that's totally fine it's a backdoor so you assume at
this point that it's not a big deal that's fun alright so we've run it nothing is listening as we expect it's listening listening for packets on out of out of P capture packet capture it's a controller in the game so intentionally put in a typo just so you know that this is not like machine learning AI whatever your sense all right so here we go so my controller so I've got all the all the particular commands as I said the implement there the implementation in the implant doesn't support all the commands so I'll put that in as well that's fine let's do some stuff let's do some stuff here we go so the first one I
said so execute arbitrary commands so tak bow that's important so we do an LS and in our home directory we just got the implant we don't have anything else okay
didn't want to retype your buttons push up so let's do that and let's give it a string and let's just slide oh no I'm always touched when people create files it's very moving so let's just touch your file on the other person's file system that's fine and this is very forensically friendly telling people at their owned it's fine okay I'm using a follow text interesting say it's nothing is listening but it's there there we go just appears that's pretty cool that's pretty cool times there we go so we know our implants working that's pretty sweet still nothing that's pretty cool it's not nothing all right so something next so if you've got say for example your admin is like
doing string searches like has a really cool cron job where like every 20 seconds he looks for text files that contain pwned alright that seems like a fairly reasonable way to do detection so on top of that so say for example you continue on and if you do that then you just go oh well I didn't see any internet connection so [ __ ] you must be hitting me over ICMP whatever yeah I mean so it's I don't know why but that's just must be so let's just block all outgoing ICMP let's just do that for no particular reason it seems like a really fun thing to do there we go all right that's fine that works we can list it
there we go that's done droppable ICMP packets and we'll just ping the machine
there we go as expected as expected all right so luckily our implant in our control I had the ability to annihilate someone's firewall so let's do that doesn't need any options this time it's the command done there we go out we go sucking sucked in mate sucked in all right so we've got our last commands so we've got through I got three out of the four three and four were pretty much the same as I said the full implementation of the last one is any differences between well you know how much extra effort was in there to dev for full terminal support so you get all the extra nice bits and pieces you get with
you know like line endings and colors and all that kind of stuff so it was pretty much the same those session leaders and you know all the right stuffs but for the sake of this demonstration this one is fine so we still had nothing listening as long as great we'd like scribble these file will give me a farm but now less is less like let's take a shell on this machine let's do that so our final commands for the controller and kabat - mr. check there it is give it to you give it an IP and a port
and I know this some people it's like I we're Christians written another shell why [ __ ] what it is use netcat but it's a and i do actually in a second but the it's important to know that this is we've gotten to the point now we've read an implant and we've actually been able to make a replacement controller for it so this is talking to like the real stuff there we go ask for a password there we go all right now we've got a connection now we got a connection I'm port one one three seven one three three seven there it is all right so once a password we give it a password again password is this isn't the
original password passed where they came from the implant I didn't make it up magic syrup that's what came out of the implant Holly obvious skated obviously but that's what it was now we have a shell what do you first thing you're doing you have a show here where my there we go root there we go we're inside the other box blade main do some LSE's like LS route I've no idea what I did that for but I wasn't going to recall my presentation at this point I was too far in was in too deep oh whatever it's fine it's cool yeah this is the one I was supposed to do and there it is there's our file there's our
implant and if you still don't believe me if you still don't believe me I was like oh I'm gonna wigs it but like maybe the audience doesn't believe me there we go so it's IP show the IP address and come on top faster and we're inside that neighbor we're inside 135 there we go owned owned owns using someone's own implant the best way to do it all right so then we got the time the end already we are you demo all right c3 right questions however I don't take questions because like one like people ought to ask me questions where there don't really want to know the answer that's want to tell me the answer so I'm not
gonna do that that's a waste of my time and the one question that everyone always wants to ask at this point it's like I sweet so you found this implant Christian was really interesting don't really give a [ __ ] about the talk about cigs and like oh you know this found some really really cool like compiler up them into optimizations let's have a chat about that and how many less cycles it takes people right now I'm gonna [ __ ] about that I want to know where the binary came from I don't know about attribution that's what I want to know about so as we saw the password so this is very no I
don't do attribution for a living so this is just observations that I've made along my travels and I will let you to decide for yourself alright okay the password was magic Sarah that's a thing so Google is an awesome way to do attribution you just push it into Google and attribution comes out alright so magic syrup is a thing made by magic so the reverse shield password is a popular seasoning made in the Philippines it's big interesting and the tasking strings were all likely derived from Cebuano which is a very popular language spoken in the Philippines Cabot is actually trained roughly translated to the word attached so that's our shell attached to the machine tech bars run as
an exercise but yeah run commands so and there was also another set of strings and saw this binary which I'm not going to share today but that were overtly declaring the actor was Philippine politically motivated but all right Philippines have a sophisticated see any program probably not Cyclops misinformation probably probably all right so in my spare time did I have much off I like to read blogs watch presentations at home I work from home and I particular like I work in a cyber shared which is a converted cardboard and not a particular like go in a lot of places so I watched most of my presentations stuff in the cyber shed you can always find me this option all
right so it's so as a result don't go to really go to many conferences anymore used to but over that so you know I watch people's press so in December fire I had this lava defense summit and they got really excited people get really excited when they talk about actors you don't see very often platinum in this case they got up on stage and you know carry on about year we found platinum and we've done some attribution whatever you know Microsoft report about it's been a while like no one ever sees platinum alright and true to their work so I've given you guys a little bit more than most people give you but true to
most info stack presentations they give you sweet FA like you're hunting I think I've seen this presentation made about forty times now trying to derive intelligence from the slides or from what they say trying to write Yara cigs or whatever whatever I can get out of this thing I've tried to well and truly squeeze blood from this stone we have the slide here so it's particular sample that they've found so this is a window sample it's not an example particularly sample that they've seen that they've happily attributed to platinum and they talked about this password thing so it's not on the slide but when the guy is actually talking he actually says campaign password I'm like I'll it's a
bit interesting that's a bit interesting alright and if you look here as far as the format goes this is actually inside again like when they talk about this is actually inside their payload so this is inside their malicious actor payload their implants whatever so it's encrypted and you've got this password and a colon and more stuff that that I tell you about just you know try and lead you on inside there slide and if you remember when we went back to what my process text looks like we have something that I call a campaign code and it's format is pretty much identical to that one so yeah it's a light lead I got a little bit more
reversing to do at some of the Crypt to finish that's usually a good indication but I don't know no one's ever said that they've spotted a platinum Linux sample that's pretty sweet but stay tuned there we go any real questions
you