Koadic C3: Windows COM Command & Control Framework
Show original YouTube description
Show transcript [en]
welcome this talk is about Kodiaks III as you can see up there is command and control by Zack and Sean as you can tell I'm new at this these talks are being live-streamed because of that I would appreciate anybody who has a cell phone turning volume down so that we don't in the middle of it get a phone ring for everyone else to hear and harass you for the rest of existence because it will be recorded as well I'd like to thank our sponsors very sprite privity productivity tenable Amazon and source of knowledge it's their support along with the other sponsors donors and volunteers that make this event possible and I want to thank you all of you for
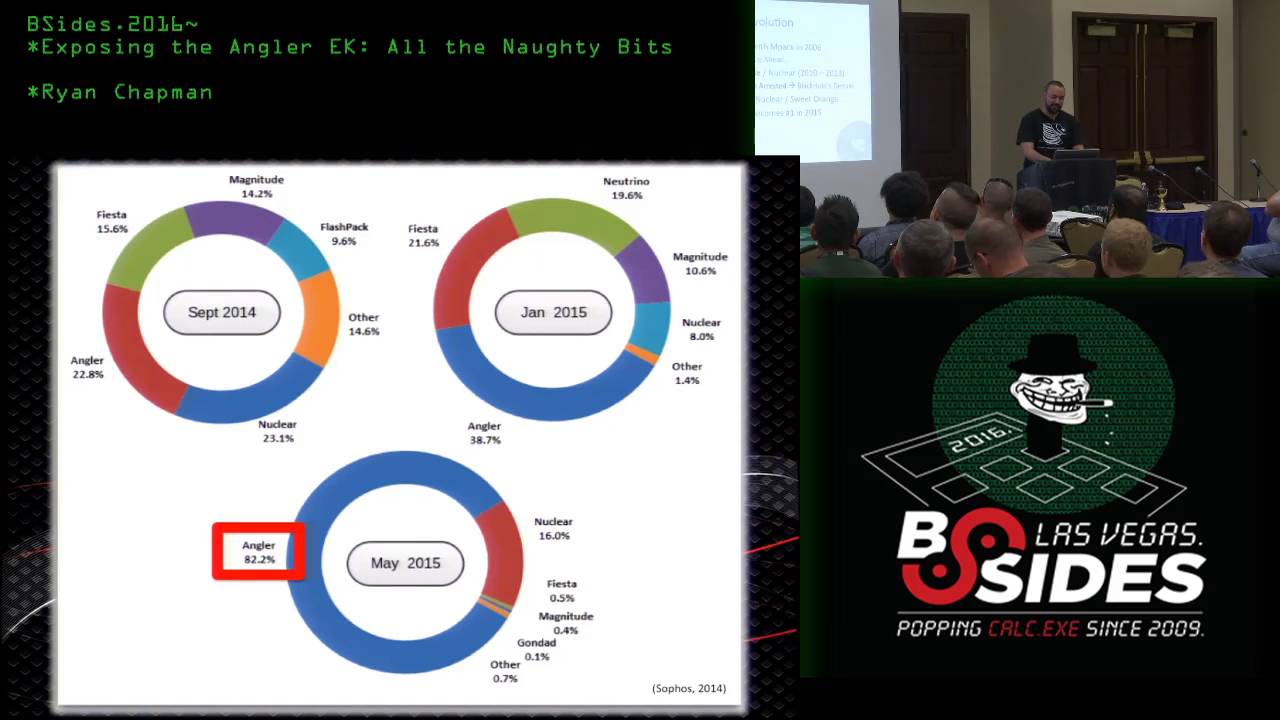
showing up because if it wasn't for you there'd be no one here to listen with that let's get started I turn it over to show yep so on our agenda today we're going to talk about some of the current open source malware options that you have during a penetration test and then we're also going to be releasing a new tool today called choleric c3 and it's an advanced rat made out of J script and VB script and we're going to talk about some of the hell we went through with Windows scripting quirks and stuff like that and then we're gonna have some demos at the end so first of all I'm zero-sum this is Elif not and not with us today is Jenna
Matias and Nader's well we're the red team that r is since we worked on the eternal blue extra bacon poured that stuff to Metasploit did some original research on that kind of thing so just quick couple notes before we get started you using this tool you know we aren't responsible for what you do it contains a ton of overlapping research so windows script host has been around for 20 years or more so there's a lot of things that are already well known about using the script host but we did advance the state of the art a little bit and we'll talk about that and what we're releasing today is just a prototype we've used it on real
engagements but there are you know a few boats so submit taxes or fixes and not Texas and just to be very clear we're talking strictly post exploitation so this assumes that you already have a shell on a box you want to do something interesting with that shell you want to move around the network you want to privilege escalate that kind of thing so the current state of when does post exploitation you have mature Perdue cobalt strike power so Empire pretty much a standard toolkit now or you can roll your own start that hard but most most people just use the normal tools so we'll talk about some of the downsides of PE malware so that's portable
executables it's meterpreter cobalt strike that kind of thing in a post exploitation setting most most of time you're going to be dropping a binary on the file system and that's exactly what av loves to eat up especially PS exec actually does drop a binary on the disk so that is one area it's what you normally do to get around that is you use bail evasion or shelter or some type of crypto Packer to evade the payload from a V so that's one of the downsides is that and a post exploitation set in P now is not a good good choice there are downsides to PowerShell Empire so it officially requires Server 2008 service pack 2 you can get it working on earlier
versions but you also need a more modern version of.net from any of the features in PowerShell Empire and another really bad thing about PowerShell is that a lot of the things you're doing in PowerShell are getting logged and I have right here a screenshot of the Windows Event Viewer logs and you can see Windows PowerShell is a first-class citizen and the logs and then right there is one of the error messages you'll get if you try running PowerShell Empire and you don't have the proper net version so was kind of out of that frustration for me that I embarked on this project last October how I wanted to look at I was pen testing and I got on a box and
the wrong version that was installed it was not able to run Peyer so I started looking at jscript and P script VB script researching that pretty deeply so one nice thing about that is that it works on Windows 2000 Service Pack 0 possibly the earlier versions of NT I haven't tested it it is directly baked into Windows it's not an add-on like PowerShell was kind of bolted on later so it's much easier for them to log in things like that so you get access to all of the comm optics that expose a prog ID and we'll talk a little bit about that in a second but there are ways to execute completely in memory so you don't to drop a file to
disk to get a script to run and that's one of the main benefits of Empire there are downsides to the windows script host which is jscript and VB script you don't get access to the windows API at all traditionally so that's a really bad downside we'll talk about how we kind of worked around that there's no threading model so when you have an agent and an empire you know you're running a lots of jobs on it and so it's nice to have all that threaded so if one jobs hanging you can still do other things with that you're missing a lot of the standard functions you'd expect in a programming language such as base64 encoding you can
do it with cert util and some other binaries that are in the system folder but they're not on all versions of Windows and then one of the biggest problems is that all strings and jscript are wide inna to the strings which means that an old byte is inserted if you like have a shell code string you have no bytes inserted between every character so it's really bad for making Struck's or show kid so comm was kind of introduced as a what way to write the class in one language and have it be able to instead be instantiated in another language so what you would do is write a C binary that would expose a comma object and then you can play with
it and vbscript and jscript and stuff like that and it's an arguable precursor to dotnet it has some slightly different goals but it's still relevant and it's found everywhere in Windows and it's also distributed so that helps with lateral movement things so this is an example of instantiating a comm object and jscript this is the HTML file calm object and actually from there we're able to get the clipboard data out of that comm object so you don't have access to windows API but you have access to all the interfaces that these comm objects are exposing and so that's what we kind of explore it is what what with this attack surface can we do with all these
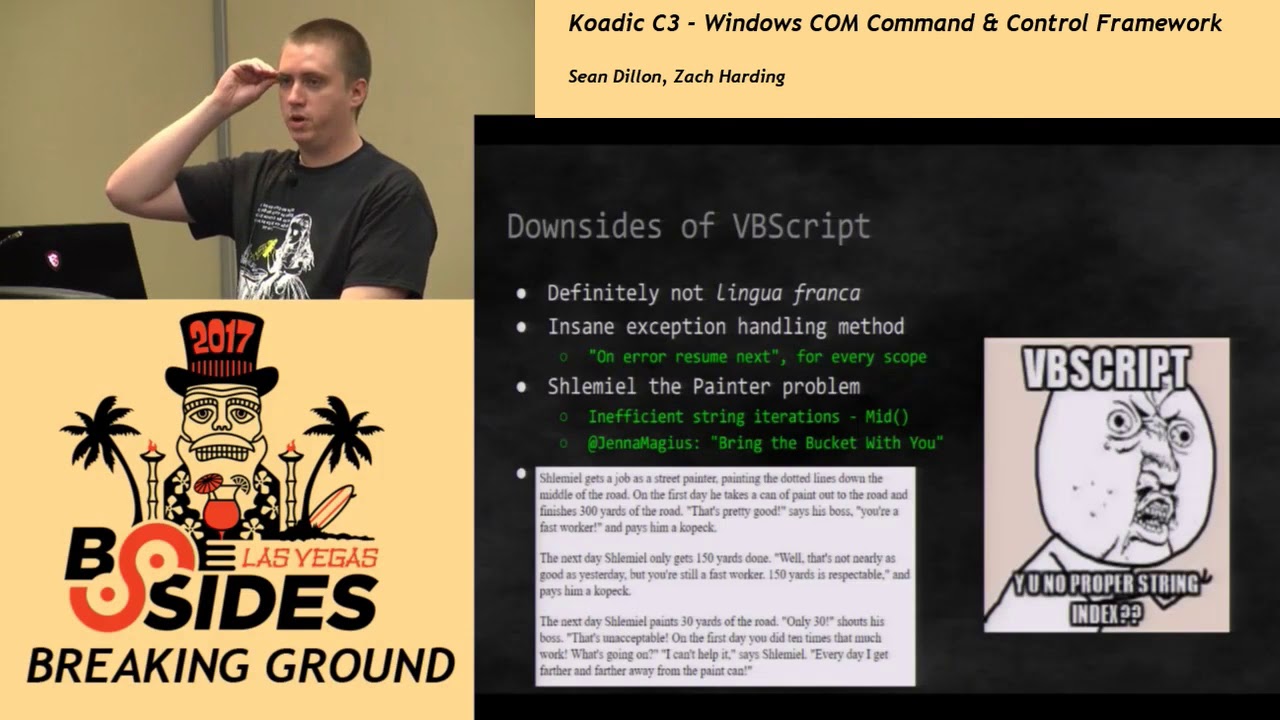
calm objects we originally started the project in VB script but we quickly abandon it if you've never played with it it's really messy language if you come from the C type language it's not fun to work with it has a weird exception handling methods so instead of like try catch blocks that you didn't JavaScript you have to do on-air resume next revery scope and then every line of code you have to check for if an error condition was set and then there was also email the painter problem which is the thing with string indexing so if you have a string what you really want is ov-1 lookups so if you want to go iterate over that string you want every
lookup to be of one but what you get is every time you want to index into a string you have to count from the beginning so you get o and pack toriel to traverse the entire string so we originally found out a way to get past that every thousand iterations we move the start of the string pointer up but it eventually be just moved on to jscript which does have proper string indexing during the course of developing this tool we researched read line which is kind of the interactive shell on linux and unix systems and so normally then right here we have a screenshot of meterpreter and as we're trying to use it we're trying to use Metis plate and
meterpreter shells are raining in it's over right in your input field so you see it's kind of staggered so we figured out a way to redraw out the shell every time a new shell comes in and still have your output and not and we committed that to Metasploit PR 75 70 it's still an issue and Empire Metasploit actually has accommodated out for now because there are some issues because they support Windows which does not have read line and it was kind of messing with that so they might revisit it but our shell does fix that issue I'll just talk about some of the Kuwaiti terminology before we get into the kind of the architecture of it so a zombie is
what we are calling a agent or a session as we call them Metasploit a stager is a web server that we're spawning that is the cc3 server an implant is just a plugin that you can run on one of your hood zombies and a job is an implant it starts what are many jobs on a zombie so we haven't plugged in architecture we have a load method for our plugins where you can register your variables and then we just do a straight string of a place of tilde and then the variable name and then we have a run method which for stagers it'll spawn an HTTP server and an implant will start a job the job
class is you start many jobs and those report back so we have a report Handler and then we also have a standard Lib KS which we added a lot of helper functions that will you know so you can run commands on the system upload download files and also perform all those HTTP operations it's just an easier interface and working directly with the calm objects we have all the traditional implant categories you would expect so you can pivot move laterally across the network you can persist manage and utils are kind of like running commands or uploading files elevate so we have a number of UAC bypasses let's the run as administrator' prompt on windows we have
gathered so that would be things like dumping the sam hive or scraping the clipboard we have a scanner so you can actually do a little bit recon you can get a TCP scan through comp we have the fun stuff so Empire it will play thunderstruck it'll max volume and play thunderstruck we have cranberries zombie song and then inject is all the ways we figured out how we could get access to Windows API and then from there we run either metric hats or shell kit so the stage your architecture generally to hook something with the post exploitation context like Empire you would run a manual and you can also fish somebody and ie and then if they say yes I want to run
these ActiveX objects you can actually hook them that way office macros that kind of thing we're just using the simple baked in Python HTTP threaded server so you do get an encryption through TLS or SSL for the C 3 server depending on if it's enabled on the target so Windows 2000 Service Pack 0 does not have TLS enabled what we do is long poles that's kind of the old-school way of querying a web server before WebSockets is you would just make a call to the server the server will hang for a while and then when finally there's some work to be done it'll reply and so that's what we do we just do a long pole
and then when the job is ready we clone a new stager and a new job and I'll explain that and so again so we're able to long pole HTTP forever because we're calling into comm and so comm is the one that's taking a long time to return if you run too much jscript even for just a few milliseconds it's actually based on the amount of operations you're doing and jscript you'll get this script your unresponsive prompt on your it'll pop up on the desktop and the user has to click yes or no in order for the script to continue we'll actually hang so that's why we fork on a regular basis so this is kind
of the way the before the first time you call home you don't have a session ID attached to you URL so we assign us to a session ID that we fork to a special job called stage and so then if you call home to the server with a session ID but no job ID you're in the stage part so now your long pulling to get a job it's when you want to run something and so when finally you have some work to be done Wilfork a new stage so we don't have all that script execution and then we'll fork the actual job that you want to run so that's kind of my threading model is we just fork a bunch of jobs
and then finally if you call home with a session ID and a job ID and these are all UUID fours then we'll send a job payload which is just straight jscript that will get valve and then so that'll do work and then use the API is to report helm with whatever the output of that job was and then that job will exit so traditionally we do have support for the file-based ager so this involves dropping a malicious jscript or VBS file on the disk and you can accentuate these with z script or w script but it's pretty easy to disable the windows script host and some environments do that and also AV your writing to disk so
there's a thing called HTML applications on windows and inside the system32 folder is a application called MSHDA Exe by standard and so HT lock applications they're kind of based on Internet Explorer except for they have a different kind of security zone sandboxing method that lets you get access to the registry the file system and a command shell normally when you go to a website and explore you're not going to get access to that stuff so the payload for this is really tiny it's just MSHDA and then at URL and so that's we've run into issues of a sequel injection and things like that where we're able to run a command but we have a very limited space but characters end
so this has helped versus something like PowerShell Empire which has just these huge stages and then so this is going to pop up a window on the desktop when you run an HTML application so we experimented with many techniques to try and hide that window and I yeah I spent a lot of time working on that and eventually I just wrote some J script that I'll move the window off screen and resize it to one pixel it'll blur to remove the focus and then there's also some XML in there that will hide the window from the taskbar but I thought this was like really bad but I also he can get some malware examples that do
the same thing so I don't feel so bad so with run DLL 32 that's just a standard application as well and this lets you run an entry point inside of a DLL there's ways to trick it into running JavaScript so kind of at the bottom here your loading the MS HTML DLL and you're running run HTML application on it and then that's getting the entire command line and Eve allying that and it starts with JavaScript so now it's just going to start evolving JavaScript so we're kind of taking advantage of I would say buggy behavior and the way that that works and this actually gives us less wind omitted visibility when we run it through run DLL 32
so the MSHDA stager we actually have immediately fork to the run dll 32 version it's a little bit longer of a payload to stage and then the final stage that we have is called reg server 32 so this is what you had run to install cob objects and that kind of thing and so subti his guy has been doing a lot of research on this topic for a while now and he rediscovered that there was a behavior called comm scriptlets so these are just kinda to help you install comm objects but they run jscript so it's it's less sandbox and MSHDA so MSHDA is still kind of in like a weird internet explorer security zone but register for 32 just doesn't
have any of that sandbox thing so you can actually broaden as many instructions as you want with this kind of thing it's not going to pop up a thing the one thing I did find out is that it does write the file to disk which is unfortunate MSHA is not present on Windows 2000 but this is so you can stage with this on Windows 2000 so there's a couple ways to run commands from comm in the shell so one is just the W script a shell object they have two methods available one is exactly what it's run they're a little bit different exact lets you get access to standard out but it's going to flash
a little command prompt box which is unfortunate when you're trying to stay hidden so we have to use the run method which we don't get access to standard out and it but we kind of use this weird syntax at the bottom that just piped standard error and standard out to a file that we put in temp and then we just read that file and so you can actually run asynchronous commands or you can wait and get the output and then another way is WMI which is the windows management interface I think but that just lets you run 1/32 process so you can actually start other commands but I don't believe you can get the output easily so the way
that we do it mostly or completely is with run so one of the main things you want to do with the tool like this is you want to upload and download files so uploading in this case is that we are writing from our c3 server to our zombie so binary data is really hard to work with in J scripts and writing byte by byte if you want to write to a file it uses a lot of instructions so there's a thing called a do DB stream which I believe is some access database comm object or something like that but it lets you write the HTTP response body which is a stream object directly to a
file the only problem is is that you get an error like this where it's a safety settings on this computer prohibit accessing a data source on another domain so it's part of the Internet Explorer sandboxing so I wrote this code right here that just creates a temporary database in memory writes that database selects from that database and then now all of a sudden your stream is from not another domain and you're able to write directly to file so just a quick workaround another thing that we had was downloading files this is where you want to get from the zombie there's file interesting file on the zombie you want to pull back to the server through a lot
of hard reverse engineering of it we figured out that it was double encoding in the post data because that's how we're sending a file back as we send an octet stream and the HTTP so it's double encoding it with Windows 12 5 2 and then it's encoding that again with utf-8 another problem with sending post data is as soon as you send an old byte it cuts off the HTTP request right there so we just add another layer of encoding where we encoded back so yeah we could back slashes twice and then we added back /o x 34 all noelites so we have to do three layers of decoding it's really slow especially if you use like the Python decode
so we added a hard-coded lookup table we were able to reduce the time it takes to decode by about ten times so it would take about a second per megabyte now whereas before it would take 10 seconds per megabyte so some of the UAC bypasses that we have in here are by enigma like streets and other guy has been doing a lot of research on this kind of thing so these are current user hives so any user can write to their own current user hive and that's not a problem and then Windows has these binaries in the system 32 folders that auto elevate to administrative rights and then they're just searching these current user hives that you can write to from a
BD medium integrity for a command to run and then they just eval the command and run it so I don't know why they do that it's kind of insane so they aren't kind of like cracking down on a couple of these and in redstone 3 they did fix a couple of them but there's another project called UAC mean by the H Firefox and that has 35 plus methods and some of those that we can do from this sandbox common environment so one of the main things you want to do when you get on a machine is you want to after you've elevated you want to get the ntlm hashes off a machine so windows and I believe
XP at least has it but I believe a service pack of Windows 2000 has a program called Reggie XE which just makes it really easy to dump these hives so in order to crack or extract hashes you're going to need the same system and security hives in order to decode decrypt those and once we have those we're going to save those two disks and we're going to pull them back to the server and we're going to run secrets dubbed up PI by course security and packet and it's the same thing for domain controllers except for now instead of getting the same hive you're looking for the NTA NCBS bit so you can we using a volume
key a no copies just to create a copy of the C Drive and then pull the NCDs did that and then we also need the system hive and then we run the same tool to extract the hashes from that so there's several options we can choose to do our HTTP communications in calm you'll notice that there are many different versions but very similarly named so this like XML HTTP and then server XML HTTP so XML HTTP is kind of your original Ajax Way active on X object to do web requests and so this is going to be a very sandbox collet now server XML HTTP this is what you would be running if you were
running like a classic ASP web application that be if you want to do a rubber Chris from the server so you're gonna have less sandboxing that way and that's kind of like the cross-origin domain policy of browsers and things like that it's kind of baked into these common objects so they all have basically the same interface but a little bit different behavior especially when it comes to security so we take advantage of these to make a port scanner so I found out another thing called Ajax port scanning so you can scan a local network using Ajax so we use the server versions and we are able to just scan and depending on the error code we can tell if a port is open or
closed so when you're scanning from this you're on your zombies land you're not on your where your original c3 box so let's say you get a foothold past a firewall now you can scan that internal network for other boxes that might have four or five open which is SB it so that you could pivot to and then there's a W script Network comm object and this gives you printers and network shares that you're connected to on like zombie so that could be helpful too so PS exec is one of the main ways that you pivot in Windows environments so there's that this was originally a tool from sysinternals and so it's a sign to Microsoft binary now and you don't even
actually have to download this binary on to the zombie you can just pull it off a share at sysinternals comm when you do that you it does originate from the internet so you get a dirty bit set but the bypass was that we just exactly in a different way so using WMI instead of w script shell and then we don't get the little dirty bit pop-up saying are you sure you wanna run this program it didn't originate from this computer and then you just run it like you would normally run it if your wrist is sitting in doing things with PS exec so the Metasploit PS exec is not this same binary this is the
official Microsoft one and it's not default but yeah like I said you pull it off the share what's on the Internet another way you can not laterally move is through WMI so you can create this ActiveX object called WM scripting dot the SW BEM locator and then you can get to the roots and be to part of any host that you have a login for and then you can set your impersonation levels and then spawned a win32 process on there through w- so that's another way to laterally move and then kind of just recently or in january enigma x3 find out about MMC 20 plus the Microsoft management console it has an application it has a function called execute shell
command so you can actually execute a shell command on another computer and then just this week there was a lot of research going on on Excel application and outlook dot application and it is believed that these can be used for the same type of distributed comm lateral movement so you can spawn these servers on another computer and then run functions on them then from there going to shell on another computer so that's stuff that we don't actually have in the tool yet but it some future work that we're looking at but we do have WMI and PS exec plugins so now we're gonna talk about kind of how we figured out how to port to the windows API and get access
to that so work gave us office licenses and we didn't really use them very much until we had an idea to run shell code through creating a visible Excel comm object in memory so it's not actually gonna pop up with GUI and then we're gonna run Excel macros which are visual basic which is not visual basic script you get full access to the windows API and then we also set some registry keys that will disable all of the little pop-ups that tell - are you sure you want to run you know macros so using that we get access to the windows API and from there we're able to inject shell code or reflective DLL another thing that came out this
year was dotnet - Jas by tyranny though he's at project zero but basically this uses some of the column objects that get installed with dotnet and they let you load a serialized object into memory and so from there you're able to get access to the windows API cuz that has access to all the windows API or you can just run a shell code another free tool that we found is called dynamic wrapper X so this was written in like 2000 by a guy named Yuri Popov and released is freeware and this just is a comm object that you can register and that lets you get access to Windows API directly from jscript so subti figured out that you
can that there's a process called registration free comm because normally when you want to register at a new comm object in the system you've got to write a bunch of registry keys and write files on disk and all that this you can just drop this DLL which actually comes back to zero at a 61a virustotal and a manifest file and then so you'll have to write all those registry keys and then you can load this dll and then get access to Windows API so once we got access to Windows API we wanted to use the mimic ATS that's available in PowerShell Empire and that was kind of one of our design goals is that we
wanted to use that DLL because it's a known dll we don't the recompile mimic ass you just want to use the one that they're using the only problem is that the DLL mapping and PowerShell Empire is done from PowerShell it's not an actual reflective DLL or the loader code is built into the DLL itself written in C it's written in PowerShell so our limited instructions did not help for that because actually loading at DLL is a lot of instructions that you need to run to parse all the PE headers and map it and a memory correctly so we did not we weren't able to use that method so I created a DLL called Manish M DLL which
is a proper reflective DLL and so all this is going to do is well first it's going to tell if you're on an x64 system and you're running an x86 process so if you've ever run the maquettes and you're in an x86 process on an x64 system you're going to find that it's not going to work correctly so we first determine if that's the case and then we'll fork into an x64 process next we're going to prop process hollow out notepad.exe from the sis native folder which is a fake little symlink and windows that does get you to the proper system32 folder that you want depending on the architecture and then we're going to inject that Powercat
stock dll and do it then we're going to get the debug privilege which is kind of like you got no privilege on Windows then we're going to elevate our token to system and then we're going to run whatever command that you entered as a plug-in option and down with it well if not run the demos okay all right now we're gonna demo this up I don't know everybody likes the demos and nobody really likes to not have the demos so we have a little environment setup right here we have domain controller in a small little domain and what we're gonna do is we're gonna assume that we've gained compromised over at least one of the machines here and we're gonna
introduce chaotic to everybody here okay so right now we're we're going to be using Python too so here it is it just loads up just like this you get a nice little help menu you get a lot of the different options and stuff like that so we're going on just a minute
yeah our screen I can't see it I know you guys can so okay here we go so we're going to so look at the info right here and we're gonna set the callback and normally this will determine what your outgoing IP to the Internet is automatically so you can leave it at 0 dot 0 dot 0 but we have a weird setup going on but we don't actually up Internet so you just to manually type its local IP right so it gives a nice little string right here this is our payload that we're going to need to get on the compromised machine so if you're on the machine right here just lay it in and I
it's awesome
okay
second
a host only network here
okay so let's see the skin so that's what's supposed to happen so there we go and you just run that command and no window would pop up and then you can close this right here and what we should see is we should see a zombie come in right here so here we are with the zombies and we get a little bit more information about the one that called back we see right here that this was not an elevated command shell so what we can do time to demonstrate the upload and download capability to this is we can use the implant to upload a file at the local file
this was MSHDA
all right so we should
so as you see right here we took the putty file and we've uploaded it to the computer there's no bin no windows or anything like that and there's not much logs associated with any of this and so just to prove that we're doing this correctly we can take a shop sign with the file we see here it starts with a t1 this is our Shah song right here and if we're going to go back here and we're gonna use the implant to download the file again and make sure that the shah's matches right
so we put it into the temp right make sure we got the right samba here oops
there we go and then we got the file back here on the local machine now look to the temporary and we can make sure that they match and indeed they do so as we see we didn't lose any information and now we got the proper upload and download functionality here it's all over the windows script engine so that's all well and good right but if you want to laterally move laterally move and you need to elevate and stuff like that it's kind of the idea of what we're trying to do here right so so as we see when we look at the zombies right here the zombie that we got on this first machine it's not elevated right so we're gonna
try to elevate through a little bit of a bypass here so we're going to use an implant and we're going to elevate ourselves and we're going to use a little trick with the event viewer all right so we're gonna set the payload to zero and we're gonna set the zombie to zero I think we're on zero right yeah and we're gonna run and if everything goes right we should get a job back with an elevated UAC yeah and here it is right here and you'll notice just like this little star is indicating it's an elevated privilege type of zombie the baby here so we take a look and indeed it is right so we can
open up a command shell right here you know we give it a little little whoo I look at groups screams a little messed up because of the display here but you'll notice that we are indeed using an elevator privilege right now yeah here we are okay so we can just exit this all right so what we want to do is that we have the another machine over here right and we can see we can scan from this machine right here just like we do and everything else we're gonna use another implant and we're going to scan and we're going to go to adjacent machine in the domain
and we say that it is open right so now we now we can no we can try to do some lateral movements to this machine so we're going to use another implant right here and we're going to I guess we should probably just dump the ashes on this machine first right yeah so we're going to use the one that we were talking about on the slide which is the dynamic rapper X right if everything goes right we should get nice hashes right here here we go and I'm sure everybody's really familiar with this screen right here alright so we've got these nice hashes that's the mimic cats output that will may have plaintext passwords and also hashes of
the machine right so now we're gonna try to move on to the next machine here okay pivot
soon we get that from the mini cats output right there usually do
so this is using the WMI to literally move across the network right here
yeah the font is a little funny here yeah oh I do thank you
and here we go and as you'll see the one that we got back is also an elevated privilege we have elevation know what so you could see here he has multiple IPS because he's pivoted so he has his first shell which is the low privileged medium integrity and then the next one was where he elevated and then the final one is where he's pivoted and you can see he can run commands on the new box I don't think it's only that backslash yeah that's gonna take a while too so so do we have any questions about any of this that's going on right here yeah yeah it's gonna tell the machine that has visited hmm okay I free could you repeat
the question a little odd right okay I'll repeat it so who's asking if when the second machine calls home if it's gonna come back through the original box that we hooked first or if it's just gonna go straight to the server it's going to go straight to the server there's not really a lot of networking you can do inside of comm outside of HTTP requests so we can't really tunnel things through unfortunately yeah we also have things like grabbing the clipboard and so forth and so on we can demonstrate later if anybody's interested
so we just want to talk quickly about some of the mitigations that you can do to stop an attack like this so there are actually ransomware that are completely written in jscript now that do all their crypto and jscript and can do a lot of these techniques nothing too sophisticated but they might might get that way especially with the way that PowerShell is getting more and more sandboxed and stuff so one thing that Microsoft has is the ANSI malware scripting interface and si and so this was hooks that they added for antivirus that would allow them to get access to scripts before they execute it was originally intended for PowerShell but there is also a script of
VB script sport so that is something that malware or anti-malware should look into another thing is device guard app Locker CI it's all kind of the same umbrella terminology for app whitelisting on Windows it's a real pain in the ass to set up you have to do a lot of registry and PowerShell and things like that to get it working I'm hoping Microsoft will add a GUI or something eventually but right now it's not fun to set up but it's the best way to harden an environment but not very practical really but if you do get it working you want to block the windows script host HTML application comm scriptlets and just whitelist the apps
that you need and don't run anything else another mitigation is you can delete all of those exe s that we're using for stagers Windows Update will probably put them back and another thing that I haven't tried that will probably break the system is if you leave a lot of those default comm objects including the script parsers themselves those are common objects but there are components that rely on those so you might break your system and have to reinstall so one thing we want to do is add some of these ways that we've gotten into Windows API I want to kind of have that added to Metasploit as just like a super module that just goes down the list of all the
three ways that we have to get to Windows and so then we can add that as a target for things like PS exec which does have a PowerShell target but it doesn't have a jscript target we could add that some more future work we need to explore comm some more it's a very large attack sir for some windows underexplored probably more cool things that we can do I don't like releasing dirty code but you know some of the codes rushed I'm kind of a perfectionist when it comes to code so I'll probably be fixing up a few things at least a little bit of a plug-in revamp there's a little bit code reuse between plugins that I want to
clean up and then also I want to make jobs task based so if they're doing a lot of the common things we can kind of not have to rewrite a lot of that code another thing I wanted to kind of add is a minimizer and obfuscator Forge a script that will just kind of change the payloads up a little bit because right now they're all just standard payload every time we've kind of neglected persistence implants which would be kind of cool to add and then since we're using the basic Python HTTP server we are vulnerable to denial of service and things like that if someone if you put your c3 on the internet someone can come
by and just totally open a bunch of connections and slow you down so that's one thing that we want to kind of work on is limiting throttling and not IPS they can connect and stuff like that if you're interested in knowing more about comm the best talkin c-calm was this year by tornado project zero at infiltrated 2017 it's called common sixty seconds it will tell you everything you need to know about the origins to come how it works why it works kind of more to the point of jscript stuff as the talk that was at b-sides Nashville this year by sub T and enigma x3 called windows archaeology a lot of overlap with our research and
then establishing a foothold with JavaScript by sub T last year at Derby Kong another he made a very basic jscript grants we kind of as we were developing this I saw that talk and then just it kind of gave me the idea for register for 32 and things like that and so we put this code up on github right now it's a github zero sum slash chaotic and we're also doing a workshop at Def Con it'll be a lot more see and shell code and stuff like that but we're all I'll have a github up for that when that comes out so check that out as well and that's it from me and zero so R 0 so
Menelik not ever since there's any more questions yeah about time for just a couple questions if anybody is a maybe one when utilizing TLS too well Haider traffic basically is there a risk of people being defenders being able to track down the certs and then using that to figure out all the machines that you're on yes so you do need a valid certificate to do TLS communications because it's going to go through the normal windows HTTP processes which is going to check the third store and see if this was validly signed for that domain so yeah that's one thing that will I mean it's pretty easy to get a TLS sir these days but with let's
encrypt and things like that but it's one thing that can be tracked for sure
anybody else
yes yeah yes so he asked if we've used this on engagements where other things have been getting caught and yeah I mean we still run into you know NT for Windows 2000 domain controllers and things like that you know it does work in Windows 2000 at least the core does a lot of plugins don't because Windows 2000 very bare-bones OS just generally have a whole lot but we have run into it like I said before with sequel injections where we needed really small payloads and so it was one way that we could stage and just get a better shell and then you know it is kind of a niche thing we don't this isn't like our first choice you
know we'd rather use meterpreter or something you know more direct capabilities but it has come up and proved useful in a couple situations especially on older antiquated systems ya know we got a couple so you see we have disk MSHDA reg server and then run dll 32 just different ways yeah MSHA is definitely the smallest string that you can do because it's just a mess hg and your URL
thank you guys very much [Applause]