Security Monitoring: Avoiding "Oh Sh*t" Moments
Show transcript [en]
great thanks very much everyone uh so obviously as the title implies I'm here to talk about threat modeling and how it can help socks so to give you a bit of a background I've worked in and around socks for pretty much my whole career so either as a security analyst in a sock building new socks or in my current role where kind of I help customers develop socks or kind of improve their current solution um so again I've seen a lot of socks a lot of different types of socks a lot of different names CDC ASO gck kind of every every acronym you can imagine um and socks are a big thing in our business now right they're kind of a
Cornerstone of a lot of people's um blue team defense and monitoring kind of piece um and we're seeing more and more socks you only kind of have to look at the mssp market look at uh LinkedIn recruiters kind of trolling for people with sock skills to know that this is a big and growing area right but we're still seeing massive security breaches all the time um they're in the news pretty much on a weekly basis now and again latest stats are still selling us it's 100 days from getting into the network to detecting now on one side you might say okay that's good a few years ago that was up at 350 400 right but
you're telling me we've got organizations paying people as a full-time job to detect threats and they're still taking them a 100 days that's insane in my book and the attacks we're talking about they're not crazy sophisticated if you think about stuff that's been in the news lately um One login um DNC talk talk none of those use kind of incredibly advanced unknown techniques or abilities to get in it was a stuff that's documented and reported and people should be detecting you've got the capability to do it you know about it kind of it should be in there right so why did they keep failing well that's kind of a diverse question um I see a lot of different types of socks
some of them fail um fairly quickly some of them don't fail at all and succeed a lot but come some some of the common problems I see are socks that get flooded so it's that typical story of alert fatigue you're wanting to monitor everything everywhere all the time and effectively you can't do that you have to prioritize you have to be focused on something otherwise you're going to need a thousand analysts 247 Ching through alerts and even if you're doing that you're not going to have that Focus to be able to find actually the bits that are important tie them together to create the story identify the intrusion right on the other side of that you've
got the socks that don't have enough data so you've got typically you see this with some kind of lowlevel msps where people just take say prim to firewalls and say well monitor this or you've got internal teams where they haven't got the Buy in they haven't got the connections with the engineering teams to get the log sources they want pushed in to whatever system they're using um you also have the rockar rockar sock um this is one that I see far too often um and normally these ones great people working in them um great tool sets great data sets know what they're doing but they've got the infos Rockstar mentality that ego they're constant L
looking for what is the latest greatest zero day advanced nation state attacker and they're completely missing actually the everyday threats that are facing them they're the people that kind of I know have memory analysis of all their endpoints but forget about the SMB share that's Expos to the internet um you also get the secret sock so this is pretty relevant given the title of bsides this year sharing his caring how many people know of a sock that is tucked away in a little room that no one else can go in that they do their business they don't really talk to anyone else this happens all the time and these fail big time and they fail
quickly because no one talks to them and when they need to talk out to the business they don't know who to talk to so again humans are a really good sensor the rest of your business is a really good sensor if you cut yourself off and that you're losing a really key detection piece and finally you get those socks that have a big budget they spend all their capex they've got every tool Under the Sun but actually none of it's tied together it's not really doing what they want because they haven't thought about it they've just gone to infos and B all the shinest things right and all of these kind of tie back into a lack of Direction a lack of focus
on what is important to the sock what are they trying to detect where are they trying to detect it what are they trying to do for the business how is the business working how are they adding value so okay that's that's why socks fail sometimes so how can threat modeling help so threat modeling gives you loads of different things so first off of it helps you identify threats that you're facing real life threats how are they're going to appear also gives you B business context through threat modeling you do modeling of your systems and how people use it so you understand how the business is using the infrastructure you're defending again having a network diagram of how your
network looks is great but if you don't understand how data flows around how users interact with it you're not really going to understand it that well so you've got these threats you got the business context you take those threats push that out into use cases things to look for signatures to deploy to your systems things to add to your threat modeling Playbook you also identify the data sources you need to be collecting well they're collecting everything you can say Okay I want to detect this to do that I need X data source or Y data source and you can limit it and kind of focus it a lot more from that you can go away and say
okay look I want to detect these things using this data what tool can do that for me again most people come to this and say I've bought this tool what data can I give it what can I detect using it taking it the other way around gives you a lot more informed decisions about kind of what you're buying why you're buying it and again it helps Focus your priorities once you know what you're trying to detect what your high priority is you can focus more time on that give a bit less time to kind of those alerts those uh threat handling playbooks that a little bit lower down your priority and finally by doing this by
digging into those data sources as well you get more technical detail about your environment you're not relying on network diagrams that drawn 10 years ago and have never been updated you've got kind of accurate real- time data about kind of what the environment looks like and again sharing is caring right you can engage your business in the whole process of this so you can say actually I'm not doing this as an infos SEC thing driving is helping me but actually I want to go talk to the business I want to go talk to the engineers The Architects the legal team that use the systems and talk to them about all of this help them get involved in this
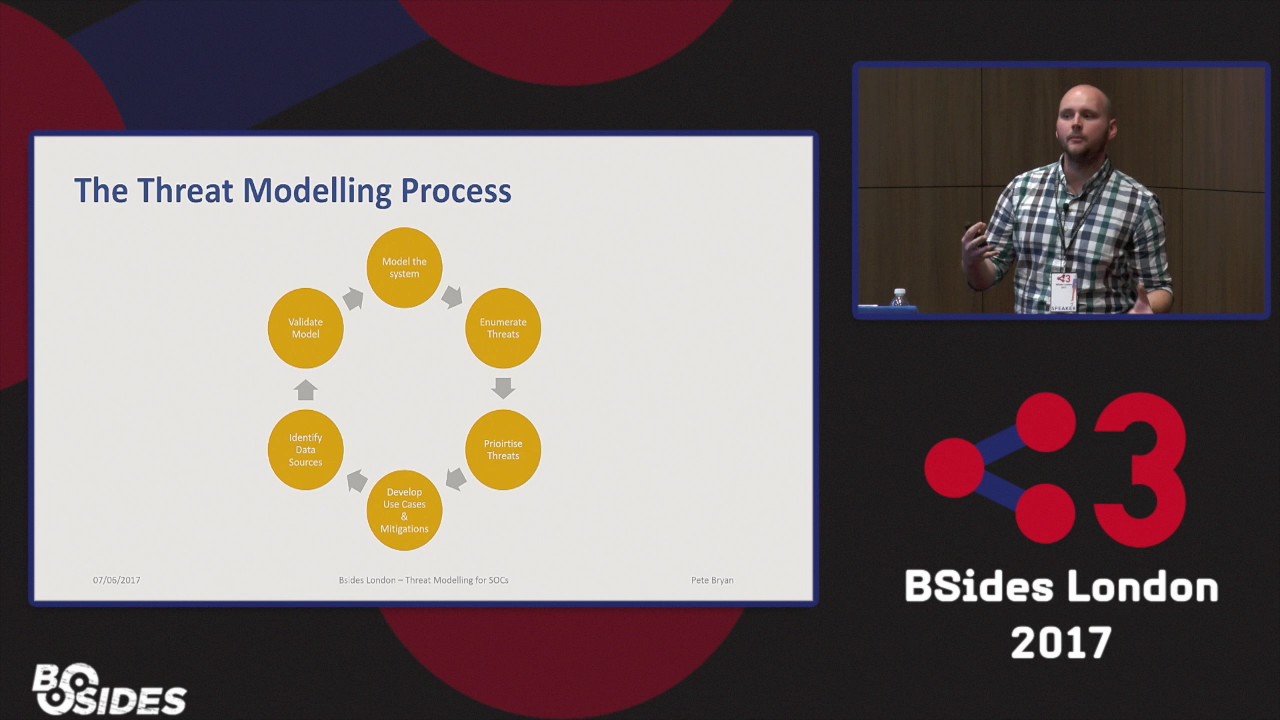
process help them understand why you're doing it get that visibility get that engagement and again you feed all of that back into your sock to add a lot value so threat modeling is great gives you all these things how do you do it so the threat modeling process is something some of you might be familiar with so it well the initial kind of threat modeling this is based off was developed back in the late 90s by Microsoft for their software development life cycle uh by a guy called Adam and again I've kind of used that process uh and tweaked it for for sock so effectively what you're doing you're modeling a system you're kind of looking at how it looks
like how the data flows what security controls you've got where data is you're looking at the threats that face that system where they face it how they might get into that environment how they might move around where the lateral movement's going to be what their objectives are going to be you're going to prioritize those again typically when I do this you get a couple of hundred threats that's a hell of a lot you can't just go away and do that you need to prioritize it you need to say okay what my top 10 this week then you go away and develop those use cases you develop mitigation so again I'm doing this from a soof
perspective perspective so you're going to want to detect the threats in there you're going to work out how you're going to detect them but actually you're part of a blue team for your organization you want to kind of help them develop as well by saying look we've devel identified these threats we're going to detect in this way but how about you do X or Y to help mitigate that rather than just relying on our detection um then you want to go away and identify the data sources you need as we talked about kind of what do we need to identify those threats where are we going to put it and finally you can go back and validate and say okay we
want to detect these threats we're putting in these use cases we're taking this data is that going to be enough um so I'm going to dive into a few of these elements of the model now fortunately in 15 minutes I can't go through the whole life cycle in detail um but modeling is one of the key elements so what you're trying to do is model the key processes data source and data flows in your environment so think about where data flows through how does it come in how does it come out how do users access it not just your external users but your internal users your admin users how do the dbas get the database how do your
customers access your front end and think about all the security controls they have to go through so again talking about those data sources your security controls are great data sources unless you know kind of how they fit into that model unless you can identify them all you're going to struggle to get them in and you're going to struggle to kind of process them and use them once you've got them in um kind of the key bit with modeling is getting the level right you don't want to be drawing a physical Network diagram in every single kind of cable and every single port at the same time you don't want to be too generic and it's a little bit of kind of give
and take something like this sort of level kind of logical you haven't got every single bit of infrastructure you got the main bits um tends to work quite nicely threat numeration this is obviously the next big bit in the process so the loads of ways of doing this um again one way that is quite good particularly when you're starting out it's a stride methodology so again this is developed by Microsoft for their software threat modeling um and it's basically you're thinking about uh threats that might occur under each of the categories in the middle um and again if you're doing this for the first time or you've got non- infos teams involved this is really cool to kind of
help give them a framework to think about um one of the other ways I really like doing it now um and it's quite good if you've kind of got maybe more experienced infoset guy is doing it is using the kill chain to map across the environment so okay someone wants to conduct reconnaissance on the network where are they going to be doing it how um someone wants to deliver an exploit how's that going to get in um also another good way of doing it is really scenario specific so let's say one cry happened um the other week you want to think how could that happen to me how could a ransomware get in okay let's take that let's model that on the
system see how they could get in see how could we stop it how we could detect it um and again if you've got some data if you running a socker at the moment you've got data about what attacks you're seeing take that apply it to the whole environment really good um there's also this great color game um that follows the stride methodology which is really good again nonino people you want to get them engaged it's fun it's kind of a little bit different um it's a bit less um kind of formalized um a little bit easier to think about so okay you've got all of this great stuff out of threat modeling how do you use it well you've got something
at pretty much every level it's really good to take a threat modeling report and say look we need to invest in this tool this technology we need to put some time on this here's my proof like we done thre model report this is the number one priority and again driving traction at a senior level to get engagement in security this is a really useful tool putting that report down having some data behind it fantastic um at tactical level kind of maybe sock leadership level using it to kind of Define what you're monitoring making sure that you've got all the areas that you need to be included in your your kind of remit uh is really
useful and forming the tool selection as I mentioned before and then finally at data Day level you're identifying use cases out of it stick them in your tool set go put in the uh the kind of stuff into your threat modeling uh threat hunting playlist Playbook sorry um think about kind of how you're going to do this on a day-to-day basis so okay told you about threat modeling it's fantastic right where' you go next so there's a bunch of resources online around threat modeling as I said said most people do threat modeling in a software kind of environment um not many people do it in infrastructure and I haven't really met anyone else who doesn't in socks but there's great
resources out there and they're really applicable so this book written by Adam Shack fantastic again not 100% applicable to to what I'm talking about but really good background um but actually what I'd say is just go do it it's one of the great things of infos of you don't need any money you don't need any kit you don't need any specialist skill to go do this just go go run it all you need is a room some whiteboard and a bunch of people go model the system just ask some questions and draw up on a whiteboard go through the threat and numeration piece using stride or whatever kind of methodology you want to do um and just make sure you're doing it
with the whole business again typically when I do this I'm working with a security team but I'm saying look let's get an architect in let's get an engineer in um and actually when you're modeling the system that can be some of the best interactions you get out the whole system because you'll have the architect there saying oh it's designed like this here's a network diagram and the engineer suddenly pipes up and goes well actually not really we changed that a couple of months ago because it didn't work here's how it actually works and from a sock perspective that's fascinating if nothing else um and finally kind of sharing his caring right so if you're doing this if you think
about doing this let me know I'd love to have a conversation about it I'll stick the slides up on peer list obviously after this have a conversation on there or just talk to me on Twitter again I don't know too many other people doing threat modeling for socks so if people start doing it I'd love to hear kind of how it works for them have they come up with better ways of modeling better ways of enumerating threats um and again yeah share as much as you can right thank you very much um if anyone's got any questions obviously





