How To Introduce Proactive Security In Your Team by Wiktor Wielento
Show transcript [en]
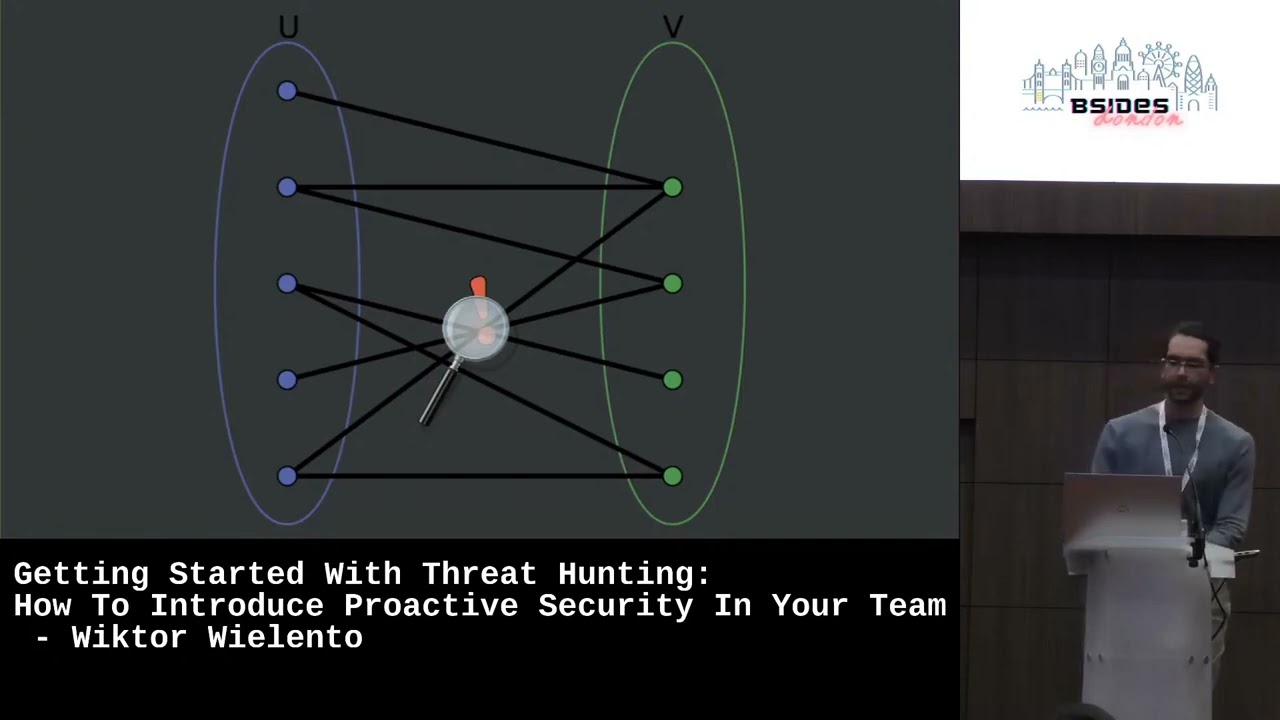
so as many of you probably heard security can look at it like this that's right a dumpster fire and in many ways that's true we do have problems in the industry we often get locked into a panic mindset where we only look for when an incident is gonna happen and that's the conventional way to go about it and it can it is great but can miss a lot of stuff so let's flip it let's be the ones looking for trouble this time let me introduce you to threat hunting it is a proactive security measure where we assume a sophisticated attacker has evaded our tools and is present in the network and that means sorting through
tons and tons of data I mean a lot of data this cannot be understated and this is why originally it's a domain of larger organizations with big budgets who can deal with this sort of thing six months ago I started work on implementing a thread hunting program and since then I've distilled some principles from my experience and research that I think I think we can all apply no matter the budget so imagine a scenario you are browsing through Twitter and you see a company you follow has been hacked there is a fire in the neighborhood how can you take a proactive approach to check for similar activity in your network we need to assume some things
you add an article and learn that the particular vulnerability was used can the same attack be used against you this is how a hypothesis is born hypothesis I used to narrow down the scope of the hand and help Hunters sort through all of the data having a good hypothesis can make or break the hand so how can we be sure we can nail the making the hypothesis we can use Knowledge from three domains first one being your own knowledge this can be awareness of security flaws in the products use good knowledge of most common attack vectors or anomaly observed the other one is knowledge of others so I mentioned that Twitter post before and that's a one of many great ways of
positioning it gathering information another can be subscribing to a threat intelligence feed but those can be really expensive uh if you don't have a budget for that just do me go make your own so create an RSS feed and gather a bunch of blogs or websites you follow to look at every day and stay on top of things the last domain is the knowledge of the environment and this one really comes with experience the more you experience the the network you're working with the longer you uh you look at the logs from the network the Mario the more similarities you will see you will get to know the roles of different users what times they log in what they do on
the systems combining all of those domain I acknowledge from all of those domain can make can mean making a great great hypothesis that can help cut down on the amount of data you need to process okay so you've done some brainstorming you probably have a few hypotheses so no word well first we need to know what we're working with so how do we get your data do you have to visit a few different places to get the logs you need this can mean this can make it hard to make contacts if the logs are siled off in a bunch of different applications it can be really hard to distinguish between when a certain event happened and the
the next one next one in a different tool in this case I would suggest starting with getting a CM or an alternative that can help congregate your logs into one place so after we gather the logs we know where to get the information we need so how do we get know if we are logging enough and I know what you're thinking logs are really expensive as it is Splunk is already killing your budget but hear me out I think we can strike a balance one of the great ways to do that is mapping your log sources to miter attack by doing that you can assess how your logs correspond to a particular technique and this can be done even in a
simple Excel spreadsheet by by mapping those you can you can strike a balance and lock the techniques you carry the most while letting go of some others that you may not find as important you can also use official logging recommendation for from vendors they have some information on their websites of how of word logs makes the most security sense so remember that attackers can also linger in your environments for months so we need to strike a balance in terms of retention as well try to involve some other departments like compliance or maybe finance and just think of a way of how you can make everyone happy and have a good retention time so you can get the
looks even if they happened a while ago okay so we are making progress we know where to find the looks and we know what techniques we can detect so what comes next well we need to make some context different vendors can present the same event in a slightly different context for example One log Source can have an IP but another can have a username so how can we piece them together it takes a lot of work but when done right it improves data consistency allowing more complex analytics it also standardizes indicator names which means you don't have to keep guessing if a destination AP is called destination desp or maybe something completely different luckily there exists open source
security data models I will point to some of them in my resources and they also all the slide offers slightly different flavors so just after doing some research pick the one that you feel most comfortable using okay so after you find the model you like we have the context we are ready to take a look at what's going on so let's take a step back how do we even know if what we find is malicious after all we are looking for that one percent of threads that's lived by our security tools well we need to find areas where things could happen and every model who will help us determine if that's the case we can start building awareness of what
is expected in our environment and there are many practical ways of doing that you could for example take two assets and assume they are free from any malware and just take a look at traffic between them similarly some simulate some activity try to note what happens what looks are being generated and that applies to both machines and users take a look look at the users of those systems what roles do they perform what what hours do they normally log in at knowledge of the domains can really come in handy too do you see any security risks in the workforce that the users are doing you can be extra thorough in those areas and start building some
documentation around that and that will kind of did that will lead you to baselining the environment a baselining is establishing how traffic looks like when it's business as usual as usual when you look at when you know what logs look like when no incident is happening when something goes wrong you will definitely spot that start to ID any anomalies you see in the logs what do they mean where do they come from start looking into them and making documentation by this point you are started to organize hands and disregard any irrelevant alerts and remember it's not a job for one person this is a lot of work and other teams can also help for example if you
need to determine that your most important assets assets try to involve compliance team or maybe a users of the systems after after all they are the ones who use it the daily I rotate the schedule of doing the hands involve others from your team this can help build skills of others and keep them involved in the newest threads and be prepared to fail most of the times you may not even find anything malicious and your hands can get halted by missing data or incorrect incorrect looks but just keep documenting it and even if you don't find a threat you will find many misconfigurations that you wouldn't normally focus on and what might what might make sense to
you to others can look like this and this is why documentation is really important uh how linear processes and document everything that you do and after some time you'll be ready to start your thread hunting program so happy Hunting that was my presentation so I'm ready to take any questions you have
hi can I imagine Mike stick your hand off if you've got a question
hey thank you for that that was very interesting um you mentioned in there obviously most of the time the Fret hunting team will find nothing what kind of things would you suggest doing I guess to prove to the business that the threat hunting program is worthwhile when it's not finding anything most of the time and this is why it's important to document everything and it can be done in many different ways for example if you are mapping logs log sources to miter attack techniques you could demonstrate over time how their map map the Lexus is your mapping are increases you are covering more and more tactics as time goes on and also by documenting your miscellaneous findings
like misconfigurations you can present them in a presentation or just a documentation in some one place where the um upper level business people can take a look at them any more questions [Music]
no great well thank you very much Victor





