BSides Noida : Day - 1
Show transcript [en]
oh [Music]
[Music] stranded in the open dried out tears of sorrow lacking all emotion [Music] staring down the barrel [Music] moving with following the light that is
okay [Music]
[Music] my [Music]
but now you can start now okay
monthly
am i audible i guess the screen has to be rotated done
okay so hello and welcome to the besides noida 2021 virtual edition conference day one the site security conference is a community driven framework for building events for and by information security members the goal is to expand the spectrum of conversation beyond the traditional confines of space and time it creates opportunities for individuals as well as to both present and participate in an intimate atmosphere and encourages indiv encourages collaboration it is an intense event with discussions demos and interactions from participants it is where conversations for the next big thing are happening i think you all must be knowing already about the besides noida conference and that's why you're here so without wasting further time let me just first introduce our guest
today here his name is mr fardeen emmer his background is he's a back-end developer a system architect and a network and web pen tester so the topic today on which he is going to speak is the future of bug bounty hunting so before we start the conversation before we start the entire session i have an announcement to make which will be interesting for many of you guys so we have planned to give away the besides noida goodies to our participants rules will be announced during the meeting so don't leave the meeting before it ends as you could be the winner and listen to the meeting very carefully as because mr ferdinand is a very intelligent man we have already had an
ams session with them then without any more delay let's start the conference over to you mr fardeen you can start sharing your screen and also switch on your mind hey hi uh very first thing uh good evening to all the people and uh welcome to all of you to this uh beside noida 2021 and today's topic of discussion what uh from my site to all the viewers will be regarding the future of bug bounty hunting like api penetration testing and why it is the future of bug bounty hunting well let's uh clear this thing first the future of bug bounty hunting and api penetration testing has a very small uh relation okay the very first relation is
right now most of the web applications and all those things are getting uh patched up or having web application firewalls and all those things and apis are also getting uh you know strengthened up day by day but uh in return most of the things uh if you inspect in the best way possible then apis are always going to be vulnerable in the if an attacker has to be taken then in the best way possible if attackers perspective is and for develop an organization is the worst thing that you can ever deal with okay so we'll be talking about it and we'll be moving further so just an introduction about myself my name is a security and researcher and also a
programmer most of my work is an analyst part and research and in my free time i food generally i don't go that much heavy uh products and all those things more tools and quite some contributions are also done at gsoc also some of it then apart from that uh my recent achievement include one of the critical bugs that i found at cisf and it was not at all related to ncibc so don't take it in that way i found it at ciasf it was a project that they were dealing with and they were having some kind of issue with them and i helped them out and they and eventually they'll be providing me with some kind of appreciation of token and
all those things and this was a very different sector part of india so it was good apart from that i have secured canva and other companies also and through which i've got some smaller yeah great bounties and things like that so today's topic of discussion will be about what an api is or application programming interfaces then we'll be discussing about its significance in web applications and mobile application and all those things then we'll be discussing about what are the types of apis and what should be the implementation and how they are implemented it will be a very brief discussion so it is not going to bore you out then we'll be discussing discussing about overwatch top 10 api
vulnerabilities we'll move towards bug bounty sections where most of the emphasis will be on reconnaissance and finding your own first api vulnerability then we'll be uh dealing with the the very approach like my approach to the api penetration testing like there are a lot of people and having their own approach and i respect everyone's but this is my that what i do and then we'll be like dealing with difficulties and duplicates because just let's face it whatever we find it like seriously whatever we find it people are like always like they found a bug and they found a flaw and they reported it in any rdb or vdp or or any private products or projects of the
organization but they are not rewarded with it and they are very much agitated and irritated uh we'll be dealing with that also that how to overcome those stuffs and we'll be concluding with a with a very strong motivation for all the new bug hunters which are watching all the pentesters and to the security researchers so let's start shall we so application programming interface api okay mostly organizations have that believe that the best way to you know make the functionality as robust as possible is to implement the apis with the apis about with the application and we have to you know make our application as secured as possible but what happened is when they are not able
to you know implement apis with respect to the applications either web application or the android applications then it exposes a lot of vulnerabilities and that vulnerability most probably is the sensitive information disclosure okay now these information disclosure may be regarding to the company's assets it can be pii means uh personal identifier and identifiable informations that is getting your name email address uh many of you have heard right uh the recent past months only that dominoes got hacked and their whole data was leaked and all those things that was nothing but a kind of api attack only okay it was not regarding their application see one of the inputs of the api like uh one of the
end points of the within the web application which was corresponding to an api call was malfunctioned a small first was done and it revealed all the information that was to be not to be uh present in front of the public in the json form and it was a very bad way of you know securing the stuff it was the most insecure way possible like big companies not only dominos in fact in india also they had the same thing so that's why people generally take ciso in a very they're like okay he's speaking about uh information security and all those things but organization don't take right now they are taking it but previously they were not that much into
security they're like okay fine we'll be uh spending like around uh what do you say one thing of whatever we are earning through our revenues and all those things but they don't they didn't have that much of emphasis to make it as much clear as possible for the organization to be secured but hackers are hackers and they tried their level best and they just they tried their level best and they found out some vulnerabilities and they were able to expose it so now we'll be discussing in a very short view about what apis generally are okay now an api uh people generally say that their software they say that it's kind of a system it's uh
like many people things virtually these all are being saved in databases and these databases are being you know called out through apis so apis is nothing but an intermediary that takes your request processes it doesn't process it it just directly directs it to the processing area and doesn't feed it to the database that yes this is the part through which what you have to take it out the api gets the information so api basically is nothing but a socket socket and we our request is nothing but a plug and when we plug it out and we just switch it on the fan or anything like that when we are having a fan or something like that when we just switch
it on the fan works the same thing is with apis also one request we put it in the api like for example if we comment it whatever we write okay whenever we are just sending it or we just posting it that button sends the api that yes this comment is being made and it has to be sent to the database which is to be stored and all those things okay these are stored in temporary as well as the permanent basic and there are a lot of things that can that is done through api okay the work of api includes like sending and receiving requests parameterizing inputs and increasing the legitimity of the functionality of the
web application so this is a very small implementation there is an api gateway okay which works under a back end and there are a lot of things that you can see there is a micro services area then there is a micro service two api uh area and three area and then the these are the sub application that works traditionally and normally okay so the main part is what we have to focus on is how these connections are there okay the very first connection is like suppose this is an api and when we just request it like we put a like or we put a comment or we just request to search on google or anything like that
the api gets your input it encodes it it sends it back to the database database gets to know about oh these are the things that he wants to know about okay he wants to know about instagram he wants to know about sundar pichai he wants to know about so these are the things he api gets to know if you send it to the database database gets to know database it took out the search query it feeds it through the api and api calls back from backend to the front end your request so that's how like in the general way possible apis are working okay so there are a lot of types of apis but generally people are building like from
small apis big api huge apis those apis that are to be run back and forth one function or multiple function or multiple ways of paradigm to be used by the api to be uh implemented on the front end as well as in the back end and these are like four types of basically apis like open api or public api partner api private to internal api or composite api now like we all know we all are students and we all uh we all was students as well as our students and we used to be within our campus and all those things so people gener like people generally of the campus like uh admin and id people the user they
generally use either partner api or internal or private apis okay so partner apis like aws apis and google apis and all those things these are these are uh common as a partner api and when we are using some functionalities that are very much immensely to be used which is uh quietly to be used as a would you say for internal works and functionalities and all those things so we are using partner api and they are quite uh related to open api also then now open apis are those apis that are readily available they can be implemented anytime they can be you know used at as much as fast as possible they are open source and they
are very much good but when you are not dealing good with the apis then your information and the requests are done there what vulnerability lies okay and composite apis are complicated apis so these are the place these are just basic things that you should know about like general thing and these are the things what you have to pay more emphasis on the rest the soap and the rpc api rest api is the in like in the world right now is being used like most of the places because it consists of a lot of functionalities it provides a good fee good what do you say url payback like you are able to get the request in the most optimized
way okay it's not about the fastest way but it is the most optimized way because developers want optimization which is better or more important than you know finding any kind of uh you know hot watch kind of a api and that watch kind of an api is nothing but a soap api okay so is one of the most what you say complicated api to be implemented okay now rest api is easy to implement but it's quite difficult to you know secure it in the most of the places like okay you'll be able to secure it but there will be a lot of vulnerabilities that will be discussing on the rest apis okay that what are the
different kinds of vulnerabilities that you are able to find on rest apis okay the soap api is very complicated but it's complicated to implement okay but it's it's much more secure as compared to rest api but but the where the problem lies is the soap apis are the things that are right now being exploited in the best way possible because soap apis have to be you know updated in the in the most generic way possible but that they take quite a long time to update and all those things there are these are some developer stuff and then third is the rpc api which are generally used but not in that much of bulk they are used just
like that okay so not that much so we have to put attention over rest api as well as soap apis so rest apis is optimized so api is also optimized but not uh that much as compared to rest api soap api is difficult to implement than rest rest apis are generally found to be vulnerable but if a minute or if a major part if one has to research on then soap apis if not you know implemented properly then it is vulnerable so so comes first and rest comes the second so now we will be discussing about the vulnerabilities okay the ova's top 10 api vulnerabilities over just as a just if i have to speak about then
oh started as a project by three nerds or five nerds okay uh and then it became a community that is like seriously that is paying a lot of uh you know payback to all the security researchers and it gives the best thing that you can ever imagine and that is um the index the indexed vulnerabilities api is api or whether it's web or whether it's mobile everything they just you know whatever they search research it or find it out they just create an index of it and they just publish it so that they will be they can be or they might be used uh in the future instances also so obasa is right now an organization
and that full form is open web application security uh project overs generally cons creates uh 10 ap like creates an uh list of 10 api vulnerabilities this one is 10 like mo all of it is consists of 10 only and 10 index vulnerabilities and these 10 index vulnerabilities consists of another kind of vulnerabilities that are being used generally by bug hunters for chaining and all those things that's that's that's an exploitation part uh that's quite a huge but still it should be known by to the people so the very first thing what you one should know about is broken object level authorization okay what is broken object level authorization or pola so like right we just call it so bola
vulnerability is just like indirect object referencing okay now what is indirect object referencing a kind of vulnerability where you are able to change the response and in return what you get is the access of those information that is hidden okay so what it is like just example you get a parameter and there was your session id or a uid and when you just change the uid or the session id you will be able to get to know about that a section of uh your access to the another like you will be able to access another accounts uh information when you are able to access another accounts information then that vulnerability is known as broken object level authorization or
idol in web applications and apis it's a broken object level authorization the second is the broken authentication which is and will be till that time when people will be like normal humans will be programming web application and all those things then broken authentication is going to be the huge vulnerability to all those things because most of the scanners are not able to you know scan the the vulnerabilities that are found that are within the broken authentication part just like finding some secret tokens or finding uh leaking some api keys and all those things that comes between broken authentication as well as excessive data disclosure broken authentication also includes uh some two-factor authentication or oauth bypasses and there are a lot of things
that comes under broken authentication more of it is like general as well as you know level third to level second kind of vulnerabilities which are always paid in a huge amount if you know chained properly the third comes the excessive data disclosure this is like you are fuzzing an end point and in return you get a place where you will be able to you know get some pii information about name or number or anything like that uh regarding a huge list of it the same thing that happened with the dominoes that i discussed way before the fourth one is the lack of resources or the rate limiting rate limiting is a condition where a person that that a request is not put
to a limit let's for example if you want to see a a youtube video okay if we reload it like a hundred times for like five minutes then it is very much optimized so we are able to see the video of youtube that same video now for example what happens if you within 10 to 20 seconds if you are able to you know rate out around 500 request so within 10 to 15 seconds when you're able to find like you know rate out the like 500 plus then the the request that will be sent through the api will be in bulk form within the database and it might uh make the database either crash or
either it makes the web browser crash but in most of the cases generally it uh it affects the back end of the database apart from the rate like apart from limited limiting in this scenario another scenario is the bulk you know bulk requesting uh no rate limiting uh regarding the you know acceptance of the on the forms and all those things so you can just automate this process you can create your own tool and you can go over it and the lack of resources it's like uh there is no security hidden uh security uh header on that in such a way that there is no you know uh request parameter to be uh you know
sanitized so that's what lack resources all about broken function level authorization it is like when you are a user and when you are able to bypass your user privileges to admin privilege then that is very just about what bro bfla or broken function level or attacks is like sql injection command injection cross-site scripting and all those things improper asset management is about regarding if us if a scope has to be has been given to you and with a proper fuzzing if you are able to get to those assets which are being not included in the vulnerability management programs but still they are critical okay now for example you have been given a part of uh you know researching on a
particular topic or on a particular domain only and you are able to get to know about oh okay so there are there is a place where most of the sensitive token as well as you know passwords and our ids are also present there so this is a kind of improper asset management and last one is insufficient logging and monitoring and this is quite not found generally it is like you know generated and mitigated through scanners only so we don't discuss that much but still that is also a vulnerability so this was one of the bug that i found way before like not here like this after some before time only like it was like for example i got a
i got to one domain and within domain there was an api dot php part and then there was a user uh you know uh user parameter okay and that user parameter was giving some kind of information so i thought why not to try an injection attack so i tried it and i was able to get to know about what their database was like and what the second parameter was all about but the second version just uh reflected what the uh the you know the parameter it accepts it like it was not encoding it but i was able to get to know about the backend so i thought of why not to try the sql injection so i put up
just i took it and sent it to the skill to the repeat part and then just you know fast it and i just first sent it to the intruder part then i first the end point which was this at about the select uh this one okay we i use the union sql inject union part of sql injection which is good the same thing and then i was able to successfully get all most of the schemas and collaborated part which like information disclosure from it so now we'll be discussing about finding your own first api vulnerabilities and exploiting them ethically we like generally what happens is api people generally regard apis are okay so it's a new thing and the implementation
of api should be done very uh you know properly and all those things and finding uh bargain apis is quite difficult and people sometimes people will say it's very easy some will say it's only about the play of api keys but in reality api will finding an api vulnerability is requires a lot of things like it's about 70 to 30 ratio 70 is reconnaissance and 30 it's exploitation okay so let's move on i parameterized my recognizance methodology into these four parts okay the first is the passive recon second is active recon third is exploitation exploitation for the recon and after effects recon so the passive recon is like inspecting the scope okay what inspecting the so for example i got
it like uh dome example.com or i got google.com okay so very first thing what i will be doing now i should not be like testing google and finding it through google but still google helps a lot of it like 99 times google is very helpful in it so passive income is like um passive recon sorry passive reconnaissance it's like you know inspecting the scope we get at google.com we find it through google we go to showdown we go to most of the places where we can find the sensitive information and the end points always remember whenever you are dealing with api vulnerabilities it should always be first the end points why because let's face it the way it has been implemented
it will be very much normal and it will look like oh there will be encoding or there is some kind of valve applied and all those things but the one of the best feature of a of a bug hunter or a bug bounty hunter is to dig deep as much as possible even if it is a functionality okay so inspect as much as possible through google as see the source code what is the call they are being doing it and everything so inspect the scope second is active reconnaissance now active reconnaissance generally what people do is the first active then passive so it's it's your way of doing it mine is first do the passive and then the active one the
active one considers like this is what i generally find out is to use the prime scanners okay there are a lot of scanners in the market i i generally create the you know i generally create some command interface and all those like not command interface uh so my own tools i use it i do it manually there are some prime scanners i generally use derb under burster does search so in apis sometimes it helps in finding end points a lot exploitation part then i've used it uh to the places such as github the you know uh it's a gold mine by the way okay github exploit dvcv and like seriously it's a best place these are the best places to
get the you know exploits for finding any kind of vulnerability now suppose api version one is being implemented okay and api version two is in the research so even if you get api version one and you're just fuzzing the user place and you just get a sensitive information about that that this technology which is being used is quite outdated so even if you report that thing it's uh affordable so it helps a lot like 70 of my work works in this way only and the after effects is like reporting the reconnaissance why reporting the reconnaissance part only because you know most of the bugs that are found are not critical but you know these are the bugs
which are being made or being available to the people because of the developers mistake okay so most of the reconnaissance part is very much efficient and it is very much important for all the new bug hunters as well as to the old bug hunters because they all know about that reconnaissance very important part most of the sensitive key tokens and all those things it's all available on github and when we just leaked do not dig deep as much as possible we get it then what are the end points that it should be tested suppose there is a end point which is tells about v version one about any ap a dot php then we should change it
and we should look forward it click over it okay and then we should add any user parameter the very second part for example there are a lot of parameters there will be user there will be destination there will be ids there will be uuids you have to find it like on github there is a complete list of it on my instagram i'll be just posting it a complete list of it and through that you can get through it okay and after users you can just first the end points you can encode the you know this symbol and it is going to be a very good thing the third one is to get the etc password which is very much
uh by the way does the the vulnerability that i got in the sql injection was this uh second part only through this only i got it the third one sorry i wrote it the second one okay so the third one of api.php is that it said hc password which is like it is not generally found but if found it gives you a huge amount of one on the monetary award a huge amount okay the next one is the finding any parameters these one for finding an sql injection and then finding a destination or anything like that these two can be used for you know for cross-site scripting also for injection attacks any kind of injection
attacks okay and finding any file inclusions you can also work over that also then approach to learn api penetration testing now all the people who are in this meet should know that apis whatsoever you are dealing with you have to and you should learn about what is a tool that is generally used by the developers to see the requests the testing requests as well as those requests that are to be used during the production as well as to the end line now what happens is whenever uh a new developer or an uh uh quite a new developer or some experienced developer what they do is they are not if they are not using postman tool properly and they are not
using it or implementing it properly on the website or in web application then it itself pose a very big vulnerability so if a tester knows about postman tool and it is only it is always going to give him or the anish means a push means a plus one point over the developers and security team to find a vulnerability and do configure it with respect respect to bob suite okay because there uh let's face it whatever the request for this which will be made through postman tool to the burp suite for the testing purpose burp suite should be there with the postman tool the second one is the key to api pen testing is reconnaissance as i discussed
if you know about github if you know about uh anything like that github or you know about exploit db learn its functionalities and learn to dig deep as much as possible okay because in reconnaissance part you get most of the things like for example you get an end point you fuzz it through double startup search and anything like that and any tool like that so most of the things what you will be getting most of the you know the last point means the last end points and last thing that you want is the vulnerability that you want to find out like injection attack anything like that so that end point if not first properly through the
bus order search that end point if it is not found out also then you cannot fuzz any point like for example if there is a user one like suppose if this was the condition if you don't know about user parameter or even if you know user parameter and then this uh symbol is encoded then your fuzzing is not going to end up in a good way but rather you're going to be disappointed what you should know is to is to learn how this encoding is being done see the request how it is being made out okay so reconnaissance is the very first key second is to select the start mid and end point of the generated
api request so the start point is this the midpoint is this this slash and then uh open bracket and this is the end point which is the fuzzing point when you are able to encode these things and then you are able to fuss the point you might find it some kind of sensitive information now if you double encode it and then do it you might find another one or even you don't you won't be able to find it so you have to test and try each and every method and each and every way to test it okay the third one is to use of fuzzers as i told using double star div or manual tools that i generally use it but
using fuzzers makes a work easy but not confirmatory because fuzzers generally give a lot of false positives so you should be be aware of these uh you know fuzzes okay the second one is the generally flaws that like a general new person should find out is about sql injection about cross-site scripting about bola means broken object level authorization and finding sensitive information disclosure and improper asset management now why i chose these vulnerabilities only and why not there are a lot of vulnerabilities that can be found out and all those things basically when you'll be dealing with sql injection or cross-site scripting or bola or sensitive information disclosure like pii and api keys if if api key is found and if it is
exploitable then and if sensitive token found and if it is exportable then so why only i found out these vulnerabilities because these vulnerabilities are all time hit vulnerabilities this means that it is always going to pay you even if you you found a duplicate vulnerability on any rdp or vdp still they will be like okay this is working still now we are working over it but you found something as a token of appreciation we'll be providing you something okay and cross-site scripting also process coding does spray especially the stored cross-site scripting it's quite difficult to trigger it but if it is triggered it's a level 2 vulnerability which is very good then broken object authorization ebola
this is always payable even if you get a duplicate still it is payable because if that if like generally idols like internet object referencing are always you know uh sanitized with inputs and changing the uh you know numbers and numerals to the another number to access the another's uh and any others information or the user's information is not always uh available like once it is found it should be patched up and if it is not passed up then it's the security team issue so if they say that we have found this duplicate or we have found this as a duplicate report then you can inquire back and tell them that even if it is a
duplicate you should have mitigated it but the security team has it then you should be awarded like definitely then sensitive information disclosure regarding pii and api keys like if you find api keys which are exploitable in nature like suppose many times some of the students have also you know reached out to me and asked that for example sir if i found an api key how should i you know implement that or use that api key i always tell them that see if you get an api key don't just stand there and say that oh i got an api key no don't do that just never do that or you get a sensitive token never do that
okay try to exploit that vulnerability okay exploit that vulnerability create a poc write your steps of reproduction and then pay it back to them or just say send it back to them what happens is they get to know about your api case and vulnerability they'll be like okay we got it so they'll be telling you this is not a sensitive information and we'll be regarding it as whatever it is then information information disclosure i really respect your finding but we can't reward it so what at the back end what they do they remediate that thing okay so try to find api keys and then get that api points through google like you should know about how to google stuff
and using google find that api endpoint you can use showdown also showdown gives you a bigger uh push towards reconnaissance okay to that end point also if if you knows about if you know good about showdown then it gives you more push use that api key implement at that parameter and then find anything which is regarding to pai once you get a pii means personal identifier information under the sensitive information disclosure then you are always paid huge bounties just like 5k or 10k means 5000 or 10 thousand dollars or more than that also okay recently got it on api vulnerability only like 39 thousand dollars something and you and your best friend no doubt is github
expert db google and showdown so use them as much as possible this is showdown this is about postman tool and this is the booster so you learned everything about what should you know but where to learn it these are the places where you should learn it okay learning places is the contra contra is the biggest hub right now to learn about api penetration testing like live labs are there step by step things are there like step by step uh introduction step by step discussion and they teach not each but they provide that platform where you can you know learn as fast as possible this is the burp suite means support port swigger labs that created poetry tool uh this is
about postman now if you are not a reader then go for these three things not not these three these two things this one you have to be know about most of the you should know about postman tool so contra and bob suite uh these two places is the best place where you should know what you should know uh about how to learn it like what is the place through which you should learn like what is the place where i one can learn as a student okay and if you are not a practical person but you want to strengthen your core then these four books are very much good mastering modern web and testing this is
there are many sections of api pen testing in it like oauth and all those things api testing and development with postman this is going to give you a niche on about what api penetration testing is about rest api soap apis and different other kinds of apis okay my favorite is this advanced api security because this con completes most of the vulnerabilities and chained a procedure to how they are testing it and then there is api security and activated action which is also a good normal book okay so we are now the in the last section uh of the presentation which is dealing with the duplicates and difficulties uh just my own thought i just wanted to
say that i have you know found out like around 230 plus bugs in this pandemic and out of which only seven was rewardable okay so 230 bucks and seven were rewardable why because most of the like up like just 230 minus 7 223 bugs these all bugs were either marked as duplicate or not rewarded or will be rewarded by or something like that but they didn't uh pay uh you know paying back and they never paid back or anything like that they didn't just cared about what vulnerability it was most of the vulnerability that i found out was injections and then i found out about sensitive information disclosure and api key mismatchment then mass assignment and
all those things so i didn't get anything in return through these bug bounties and stuff okay i didn't get like 223 bugs i didn't get anything in return the first bug what i found out the first very first bug in this api penetration testing the first book what i found out i was not awarded for that it was said that thank you for your reference but this is uh we got a from another researcher and we appreciate your work that's it this was the only thing that they found or they just pushed out so the very first thing what every new researcher should know is to leave the expectations about your monetary or awards or bounty or swag and anything
like that okay if you find a bug just if you find a bug that's a very good thing okay on getting bug to be expected just don't leave expectations about whether it is going to be triaged or not also just find a bug if you are a new learner just find the your bug in front of yourself like you get ebola means project broken object level authorization you get a rate limiting only the least one that i consider it if you get a rate limiting you find it you create a pc you use the steps of conver steps of reproduction and then just send it away you don't have to think that much about it okay
and just don't think about bounty and anything like that first learn as much as possible okay and then quarrel about you should be given bounty or not second one is to read one flaw or bug at a time now what happened is suppose uh i've seen on linkedin on many platforms that what people do is they post it like i was awarded for this bug uh even they don't disclose the bug they just uh showed that this much a monetary of what i was given so if a person is experienced by bounty hunter or a tester they'll be like oh fine no issues that's a good thing you got to go to the mount of bounty but for the new
people it is going to be a huge you know blow it will be like oh my god this guy is earning so much and how i'll be able to earn over it but bounty is just me the first perspective is this if a person is in buck bounty the new people and the person who are just wandering here in there and if they get to know about this this attracts were going to like new people towards the bug bounty hunting they'll be like oh this is the place that i should do it this is the thing that i should do because it's giving a huge amount of money most of the people don't or not at all you know
put their failures on the places okay they just don't support the failures they i got my reward after seven reports or they won't be saying that i got my first sql injection after you know 300 plus vulnerabilities they won't because people want to show off to the people to other people so that see that i am earning this much amount of money people should congratulate him so while getting validation from others it's better to get validated okay even if you if another person found a bug let it his bug only he found it it's his approach one should concentrate on his way of finding because let's face it we should be you know available to only only those people who
are in front of us okay like we should be very much if even if we even want validation we should that want that validation also from only near ones like your parents okay if you show it to them they'll be like okay fine it's very good it's awesome then it's a very good thing and if you they are not appreciating also like many times it happens that people don't appreciate i've i told my mother once that uh i mean i got this bug and she was like okay that's good did you hunt it out like hunted out yeah i hunted that's why i got the bug and she was like no no no why didn't you swat it out you should
have killed it i'm like no no no i didn't found that bug i found a bug on web application mom and through that my mother she was like okay then i explained everything what it is all about she's like okay if you if you are free then do it otherwise if you're not free then don't do it please even if you're doing it then it is going to be you know it is going to give you a huge blow on your studies and all those things so if you are a student definitely do bug bounty hunting i will always suggest you because everyone wants to earn some cash and want to learn anything okay so if you if
you are in cyber security okay the big thing what you can do is to learn these flaws and apply it so that you even if you are like previously one of the speaker tushar told in a very good way that if you find a flaw and if you are not awarded still you can add it in your you know resume if you are getting any kind of point or any kind of hall of fame so you can add it in your resume that gives more impression because that money and swag is going to get fade away in some other way but that reputation and that hall of fame is going to push you more in your life okay
third thing is thinking creatively okay you know uh most of the bug hunters are different from each other because they have one niche okay and they are doing it and they are doing a very good thing okay so for most of the creativity stuff it is found there only like uh just for example like this is the creativity part uh and there or any other researcher is there okay we both are working constantly for each other but our methodology is different i can find a skill injection within five minutes the other person can find it within 15 or 20 minutes or even not they cannot find out so every person has different ways okay the fourth one is to be ready for the
best and get prepared for the worst which is you know attached to the second point only find whatever you want to and don't compare yourself and even if you don't get anything in return still appreciate that thing okay fifth one is to have a ready to learn mindset don't think of earning first think to learn first as much as possible it doesn't matter whether it's only a dmarc record if even if you get a dmr record and you exploit it and tell it to the people then still you will be uh you know given some account of bounty or kind of kind of you know monetary awards you you might get it so never stop
learning okay learn as much as possible finding new bugs are more available sometimes as i explained here that find the duplicate bugs and getting an all of them and putting it in your resume it gives you more bigger push than anything else then seventh is to find the difference between risk and vulnerability what happens is generally people find risk and not vulnerability and that pays a very bad thing and at last i would be just ending it by saying that read as much as possible accept your failures and use google as much as possible that is going to help you out and if you want to reach me in any way these three are places where you can
reach me so i'm available on twitter instagram and you can put your questions on quora also and that is all from my site and thank to all the people who were the viewers i hope you learned something in return thank you so much thank you very much for being here it was a very very informative talk we have had for past one so it is the time for giveaway now we will be having a link in the chat box uh on the youtube chat box so uh we'll be having it shortly it is a google meet link and as soon as you click it you will be having some questions [Music] foreign
[Music]
[Music] oh [Music]
the one
[Music] daddy [Music]
do [Music]
[Music]
but
uh
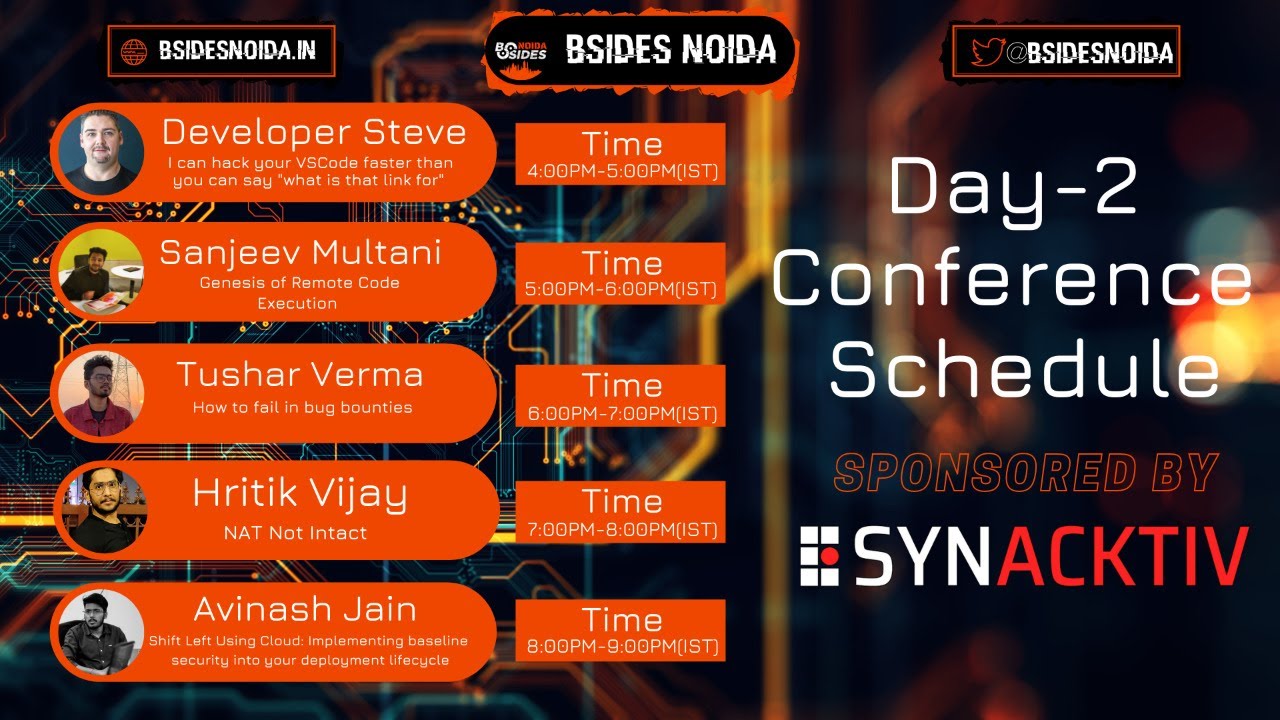
[Music] hello and welcome to besides noida 2021 virtual edition conference day one this is the second meeting we are having today so our second speaker for today is mr saurav kumar i welcome you sir for being here so a little background about mr saurav he is a security engineer at grid and cred is the company we all must remember the topic today on which he is going to speak is hunting prototype pollution in the wild so without wasting much time i would like to uh i'd request sora to start his meeting so please go ahead yeah uh so uh thank you for such an introduction so uh hello guys hello everyone i hope you all are doing awesome
and uh before starting the session i would like to uh first thank all besides team besides novada team for all the efforts in organizing this event thank you so much so uh now moving on yeah so now uh guys moving on to the topic hunting prototype pollution in the wild but uh before uh moving on the topic a little bit of filter about myself so uh uh my day job include uh working as a security engineer at tread and apart from that i love to explore and do research on various security issues most of the time i'm just curious about how things works and how we can break them and currently my interest lies on
javascript related security issues so to connect if you want if you are interested in javascript and its security i also do a bug bounty hunting in my free time so uh below i've given my tutor render so uh you can reach out to me anytime so guys uh let's dive into the topic that was a bit of introvert myself so uh the flow of today's session uh will be like this we will be covering uh prototype pollution uh on a very uh basic level and then uh we will be seeing the exploitation things like how it could be exploited then uh i will discuss with you guys the uh cases which i have found in the wild
during my hunting and then we will uh start looking at a different uh you know perspective of prototype pollution like how insecure this realization is related with protein pollution and how it helps in help us in certain cases to exploit uh the vulnerability and in the last i will uh share you guys uh share with you guys uh some patterns uh which you should which you can look for while uh hunting for prototype pollution and then we will discuss the mitigation so uh first thing first uh before uh starting prototype pollution we should be like why you should be worried about evolution at the first place right so uh let me tell you about something
that prototype pollution is a very javascript specific vulnerability right and javascript is everywhere on the internet it is a kind of duct tape for the internet and its impact can be used like rc it totally depends on the functionality of the application so uh uh this is this was a guy a bit of a motivation for every one of us to start worrying about prototype pollution and uh we should be learning it so uh guys moving on to the topic prototype pollution i have created a few points uh which i will discuss uh during the session and i and these points will give us a fair understanding of rotate pollution so i i broke uh the
whole concept in three points and i will discuss them one by one and try to give you guys a better understanding of pollution as a vulnerability not as a feature so uh guys the first point is of prototypal inheritance in javascript so guys uh first let me tell you that inheritance is basically a feature of object-oriented programming right but uh the inheritance in javascript is a bit of different than what we see the classic inheritance in languages like c plus plus and java right so let me tell you how this is different so basically what happens in protable inheritance we don't have uh like using prototypal inheritance uh one object in a javascript program inherit
all the uh methods and properties from the another object right so every object contains a hidden property called prototype which we will discuss later in the session so that and that property contains uh certain methods and properties a source yeah property and uh all the other objects in the javascript program inherit from the object dot prototype right so basically this uh this whole uh phenomena creates a prototypal uh prototype chain right so uh this was about uh these so these info was about prototypal inheritance in javascript and every other object in javascript inherits methods and properties from constructor object so constructor object is basically the object uh which is used to initialize every other object in your javascript
program so let me tell you a bit of how to identify a constructor object so usually it is mentioned by like like object and parentheses is there so you can see the last line right so in the last line the o start with the capital caps capital capital o so it's the upper case and then uh so it's the object so we call it object constructor because every other object is uh initialized using this object only now uh moving on to our second point uh what is prototype and prototype chain right so uh every object contains a hidden property called prototype as we have discussed as i have already told you but let's see like what is exactly
prototyping so can you guys can see the example screenshot here i have created an object but right now this object is an empty object right i haven't defined any method or any property inside this object but as you can also see when i try to access a property abc inside that object then i'm getting undefined because i haven't defined any property inside my object it is blank but when i try to access one of the method called tostring so i'm getting like its returning value like uh now i'm confused like okay so uh i haven't defined any method or any property inside my object so why it's still returning some value so now let me
tell you every object contains again literally i am rotating this again every object contains a hidden property called prototype and that prototype basically contains all the properties and methods which uh object inherits from the conceptor object right so every and one fair point is like every object out there every object in a javascript program inherits properties and methods from object dot prototype which is the prototype of the constructor object and these result in a prototype chain between all objects like how like suppose i created multiple objects and all objects basically contains a hidden property called prototype and inside that property that contains all the inherited inherited methods from their parent object which is the conceptual object so ultimately
all objects uh connected together get connected together in a chain and all of these were connected with their parent object so this whole prototype chain is created you can also see in the below diagram i have created an object and again the object is empty i try to print the contents of the object then i can see there's a uh there's another property uh called prototype so uh i haven't defined any property but it is still there so this prototype property is being inherited from object dot prototype means it is inheriting it from its parent object so you can also see like uh these all methods are looking a faded kind of thing so it is just to uh indicate that
these are the hidden uh methods and properties which is being inherited from constructor object so that was about all about what is prototype and how prototype chain works in javascript now we will see uh object injection uh to pollute object or prototype so guys uh basically what is what we do now like we our ultimate goal is to set arbitrary methods or properties inside object.prototype because as we have already told that whatever methods and property are there in object or prototype will be inherited by its child object or whatever object you create inside a javascript program so so if you create or set any arbitrary methods or objects inside object.type so it will be inherited by all other
objects out there so how we how we set uh arbitrarily values inside object.row type so uh there are certain methods or properties known as magic properties i will discuss two of them as of now one is proto so it is basically underscore function and the other one is constructor method or you can also tell it as a key for now so what happens uh when we uh what this proto do now uh this proto basically points to it's the parent object so whenever and whenever an object uh try to access this proto key then basically it points to its parent object so in this case it is pointing to the constructor object so in in this way we can access
basically uh object or prototype so uh read guys i'm reiterating this again that proto uh this proto keyword or this constructor keyword or property helps uh an object to access its parent object so in our case it is helping an object to access constructor objects so that we can set arbitrary values so behind the scenes this proto function or this proto method works as a setter method it used to set uh values in object dot prototype so let me show you the example i uh you can see the two screenshots on your screen so uh the left one was i have created another blank object sorry i've created another empty object and within that empty object i'm trying
to uh i am using this uh magic property called proto so by using obj dot proto i am accessing object or prototype now i am setting the arbitrary method uh property inside that object which is name equal to besides node so uh looks like i have set this value in object or prototype and now you can also see uh i have created another object right object two and once and again i uh again i'm trying to access the property uh access the property name equal to besides moving from object to so as you can see uh it's printed its value besides nueta so it means that now when we use this proto keyword to set a arbitrary method
in object or prototype then basically name equal to besides got set into the uh prototype or we can say object.type so as we already discussed that whatever value we set in object or pro type is basically inherited in all other objects out there that's why when i created another object which is object2 i hope you guys are able to see the screen so uh uh i have created another object object two which is again a empty object and i can even uh okay okay and we can even access this object to uh sorry we can even access the property name equal to besides neutral for object 2 also so you can now you can also see in the
right side of the image that uh when i try to print the contents of object or prototype then you can see there's a new value or new property is being set there name equal to besides noda so all the other uh methods which you are seeing is already there by default but somehow we managed to add a set a arbitrary value or method inside of objective prototype and it will be inherited to all other objects out there via prototype chain so uh that was about how we are injecting properties so uh guys uh if i want to sum up all the points uh we have discussed till now then it nothing sounds like a bug or
nothing sounds like expectation part here because here we are just utilizing the inheritance feature of javascript or prototypal narrative feature of javascript to basically set arbitrary values in object or prototype so by this is how inheritance works right so we are just exploiting how inheritance works like not exploiting now we are just utilizing how inheritance works in javascript so uh till so now right now the question is if this is a bug or a feature so uh uh till now it looks it really looks to me that everything is great and it's a only a feature not a bug but let me uh show you guys how it can be exploited so uh exploitation part is here i have taken
one example here uh using which i will show you guys the exploitation part like what would go wrong so first you will see in the on the left side of the screen oh sorry left side of the image where i am creating an person object inside the person object i am defining two properties name so name equal to sorrow and a is equal to 22 now uh i am log and now what i am doing i am printing the output and basically i am calling the method on the on my object which is two string method so as we have already seen uh that two string method is uh placed by default present in object or flow
type right so uh so basically we are trying to access two string method and as expected we should be able to we should be accessing that object because uh my personal object contains the prototype object which is which is hidden and that prototype object contains two string method so i can access two stick method on my personal object and it is giving me expected output now as i as we have seen we can use proto to uh set arbitrary methods in object. so what i have done i use person now i am using a proto property and now i am pointing to now it is pointing to constructor object or more precisely i would say
prototype object of conceptor object so now what i am doing i am setting uh i am uh setting the uh value of two string right so if you will see then the value of two string was maybe uh it was defined as some kind of function right so as uh it is a method so uh if you will go to object or prototype then there there can you please zoom when you're
in presentation i could not zoom all right go ahead uh yep so uh guys uh if there is any issue then i will also share the slide after the session so you can also take a look at the examples for now but for now try to uh be with me and uh see whatever we can we'll attach them yeah thank you thank you so uh basically what i am doing uh i am doing personal photo so basically now i am pointing to uh flow type and now i am uh i am changing the value of two string method so what i have done i have assigned a random string to its value so it it used to be
a function but i assigned its value to random string so now again if i want to try to access a two string method on my personal object then it it's giving me a exception error right why because this is not a function this is not a function this is basically a uh the value of boosting is now basically a string but we are uh calling it as a function so that's why i'm getting an exception here so suppose uh suppose now you got an uh javascript based application and you managed to manage to find prototype pollution there so now if you set any arbitrary value to any of these functions and suppose uh the javascript program might be using
two string method or any other method then and you change this value to a random string then these could these can lead to a dos attack on the application i am reiterating so uh this was the uh prototype pollution at its basic i can we can follow the prototype and set any arbitrary value in object or prototype and we can uh we can let the application return exceptions so which will be ultimately denial of service the application will not respond since we have polluted the whole uh code so uh this was the case of dos attack now let me show you what we can do if uh now now what you can do on the client
side also so uh another the same example now here what i am doing instead of setting any random string to the value of two string i am setting a another uh method called alert so i am setting alert method uh to the value of two string right so suppose in the real-world scenario or you uh you set the value of boosting to alert method and if the developer is using two string method anywhere in this program which i've see quite a lot so then it will pop up an alert box there and you will get a xss in your application in order to target so uh guys this was the two exploitation part which i wanted to show you uh so
that uh we get a fair understanding of how uh the inheritance could be exploited in javascript and it could lead to a different kind of vulnerabilities so guys it totally depends upon how what are the functionalities of the application so the maximum impact which you can raise uh of prototype pollution is rc which i think uh you might guys might have heard about host rc which oliver basically found in a prototype pollution in low dash library and he basically exploited that to perform an rce on ghost cms which is quite a popular cms so uh this was all about uh the exploitation part now you guys have a fair understanding of what could go wrong now
i will discuss a few points about hunting in the wild like uh what you should uh like what you guys should be looking at or when we try to hunt for protect pollution in the wild then what are the uh vulnerable operations like what are the operations which uh can cause prototype pollution so the first one in our list is recursive merging of objects so uh what happens in recursive merging objects we are we basically what we do we basically we have a source object and then we have a destination object the source object can be controlled by the attacker so what what and dagger do so a tiger basically uh recursively do copy operation on the
source object and they try to copy all the properties or all the unique properties from the source object to the destination object right so you can also uh as here i am taking an example of one of the cases which i found in the wild so it was a basically a it was basically a repository open source repository and it is it's having a 134k weekly downloads and npm so uh i found this vulnerable function set key pass which is basically taking two arguments uh the right one the right one set object can be controlled by the attacker and basically we are uh doing the recursive copy operation here and we are copying the properties from uh set
object to object so you can see inside the function that we are using a for for loop to recursively iterate all the keys inside the set object and try to see if there is any unique key then we are setting its uh value to object so now let me show you guys what could go wrong again in the right side so in the right side of the pic i have created a poc like how we can exploit this so what i am doing basically uh here i am uh the set function is basically vulnerable right so what i am doing i am passing so so i have taken an uh object which is basically the destination object so in
right now it's a blank object or empty object then this then the destination part i'm defining a path so what i'm why i'm defining path because you can see the set object takes three arguments one is a key path and then other uh argument is value so basically uh it's uh so in the past i am mentioning proto dot polluted and it i am setting its value to just its polluted so now what will happen since during the recursive during the recursive iteration under for loop it will uh once a time came then uh when it was it will be something like object dot proto dot polluted so now it is pointing to constructor object
and uh since uh constructor object and there there will be a new property which is being set in the constructor object and which is polluted equal to yes it's polluted so this is the new property which we are setting the concept of object or prototype now uh again uh now again you can see when we try to print or access the uh property polluted then it will print uh the value yes it's polluted because now it is being set in objective prototype and now it will be inherited by all other objects out there so this was one of the example now in the second part we will see property definition by path right so uh
basically property definition by path means uh for explaining this i am taking another example so this thing i also found during my hunting uh in the wild and so while looking at the source code i found that there's a function called set so again uh these function is taking our three different arguments and what what is happening here now like here this function is defining a value by taking path as an argument so the path and the value path part can be controlled by an attacker and then we are using for loop to iterate it iterate the values and set it and set the new value to object right now again uh the exploitation parties or the pus is
pretty much same uh we are uh one we have one side we have uh the destination object uh then we have the path proto dot polluted and then uh we have its value right so uh basically we are uh setting uh proto dot polluted like we'll be iterating under for loop and we will be setting uh the value of proto dot polluted to yes it's polluted but since proto is again used to access constructor object or more precise you can say object or prototype so this polluted property will be being uh will be set in object.type so since now again it is uh set in object or prototype so it will be generated by all other objects out there
uh so guys uh moving ahead uh we will discuss about uh relation with insecure de-serialization like how prototype pollution is uh related to insecure deserialization so uh before starting uh the uh the relation part uh let me tell you like if any of you are if any one of you might not be uh much comfortable with this realization of untrusted data let me tell you that insecure this realization is basically uh this realization of untrusted data uh where uh and for our session we are uh more interested into insecure destination of json so json is one of the serialization format and we will be using the inbuilt function json.parts to deserialize the json string here
and so uh if i tell you by the example then the json parse has a kind of interesting behavior when it uh works um basically when it uh parses the uh this serial serialized data json so what happens now like let me let's stick to example here so i created one object object one as you can see in the picture so uh the object one basically uh contain uh so in the object one i'm using this proto keyword and i saw set its value to one two three now i took take again another object object two and in now here now we are not directly defining a plane object here we are are taking our json string and now we are
using json.parse to deserialize it to its of uh java in javascript object right so now what will happen whenever json whenever we are we deserialize the json string and using json.parts then what will happen now then this photo is no no more work as an magic property now this proto will act as a normal keyword or a normal property it's no more a magic property when you are using json watch parts to deserialize it right so uh you can also see here when i try to access object one dot proto then the expected output should be one two three because that's how we access uh what i say properties within an object using a dot dot notation but
it is showing me the uh object dot prototype why because here it is they are considering it as a magic property and by default it uh points to the object.prototype but now but again if i try to uh access this proto keyword using object.2 then i'm getting the expected value one two three why because here now proto is not working as a magic property here basically it is now it becomes uh a simple keyword which is uh whose value is set to one two three so the guys guys the whole idea here is that uh while deserializing uh untrusted data which can be controlled by a user uh json.parts basically converts or passes proto keyword in such a way that it's no
more behave as a magic property so now let now let me show you how it could help so i am taking one of the examples from my hunting uh hunting on the wild cases so here i found or there's a function called t fill it so this deep filling is a variable function and what it's taking it's basically taking two objects as an argument so here we are not defining any path right we are not defining any value by path in into an object so basically here we where we need to take two objects the source object is being controlled by the attacker and what we are doing we are performing recursive copy operation on source
and we are basically copying all the unique properties from source to other to the destination so uh now what will happen uh now what will happen okay uh we we just need to we just need to pass the uh attackers control object which will contain the payload for prototype pollution in the source part so now let's move on to the right side of the image where i've created exploitation of the the vulnerable function so here i am taking a payload uh and this payload is basically a json string right and if you will pass the json string then it contains a nested object right so uh now now we will now we will see why we need
to parse it like using json.parse like right why we need to deserialize it before we can merge so uh let me show let me tell you how this whole reiteration will work so it will work in a way so suppose in the first iteration in the first iteration uh under the for loop we will go to uh it will reach out to the uh first property which is proto so now uh we will see okay if object dot proto exists or not because as i have told you during the merge operation we only copy the unique properties from the source to the destination so now object.proto uh since we are using json.parse to pass the payload so now
object dot proto will act as a normal keyword for our source object but when we try to see object dot proto exist on the destination object or not then it will exist called cause for destination object it is basically a uh what i say for the destination object it is basically pointing to object or flow type so since object dot prototype exists so it will not copy this part now iteration will enter inside the nested nested object part so now we will uh access the nested object in something like this way object dot proto dot polluted so now this is the uh this is how we will access using dot notation uh uh dot notion here so now
if you try to see if uh the destination object contains object.polluted so we see that no it's it doesn't contain because it's a uh what is a it's an empty object so now what you can do here now what will happen here since proto is working as a simple keyword for uh a source object but it's working as magical magical property uh for destination object so now if you will try to reach it via object dot proto dot polluted then it will again point to object or prototype and we are will basically setting a arbitrary value or property polluted to object or flow type so since we have set an arbitrary value polluted uh uh to the object or
prototype so again it will be inherited by all the other objects out there and uh so that's how basically prototyping will work here so we we basically needed to uh use json android parts to deserialize the user input so that uh we can make the proto keyword to work as a simple uh simple keyboard and not as magical keyword right so uh guys this was uh these was uh about uh these these so this is the very specific case uh which can uh help us in performing uh like uh exploiting prototype pollution using the json deceleration now uh i will just tell you like i am discovering one case of deceleration but there are other silhouettes and formats
like xml yaml so uh while i'll just suggest you guys or encourage you guys to just try your hands on to find all these try to see if you can find any vulnerable function in other simulation formats uh sir there is a request to all the learners so can i just interrupt you for once to all the learners they have to listen to the entire session very carefully as we have a giveaway afterwards after this meeting ends so we'll be having we'll be pasting the link of a google form on the chat box once this meeting end and we'll be having some questions related to the entire session we have had so each and every participant who
are willing to take part in the giveaway session we are giving away one mask and a pair of stickers customized by customized by mr uh great and it is basically from our besides murder so once people they submit the form for that they'll be eligible for the giveaway so please keep watching the entire uh session so you can please continue yeah sure so uh guys finally i would like to uh tell you about some patterns which you which you should look for which i've seen uh with my experience while hunting for prototype pollution in open source so uh basically you should be looking for or you should be trying to find all the uh operations or all the uh functions
where uh they are doing recursive cloning of objects right so whenever you try to look for prototype pollution within a javascript based application so you should try to look for where recursive cloning can be happening like i can give an example uh like uh so these uh these examples which i have taken here yeah so this example is basically taken from a javascript based orm so basically whenever it comes to javascript based on so there are 100 chance that there might be some function which is which was doing uh which might be doing recursive copying of objects you just need to check if there are any uh protections uh against that or not like if there are
any mitigation uh for prototype pollution or not if there are not any mitigation then you can exploit it so uh the idea was to identify uh try to be more mindful like uh it's called like smart fuzzing so try to be more mindful where you should look for and then uh try to read the documentations if you are attempting a target like if there are any apis uh which is performing recursive learning objects so you can directly jump to that code port section and try to uh see the uh how it's how it's working and if it can be exploited and exploited not you can also i will also tell you one more uh scenario where you can uh try to
find prototype pollution so if you see wherever anywhere uh like if any uh block of code which is doing in deserialization of data suppose there are multiple packages which do uh con serialization or deceleration of multiple formats like json xml yaml even binary formats so you just need to uh see like uh you just need to take a look at the source code and try to find what are all the vulnerable functions which are doing recursive which are basically recursively copying uh properties from one object to another so at the core uh this was about uh identifying the patterns uh always let uh let's quickly discuss what mitigation which you might face in the wild while looking for road
evolution so uh mostly nowadays the most common mitigation which i've seen is uh using uh basically they have they implemented a fast condition to look for the proto keyword while traversing so while doing the recursive operation of merging objects they look for proto keyword so if any of the property or any of the key in the object or in the source object contains the keyword proto so if any of the object or property contains the word key proto then they just terminate the operation so the user in like uh there uh so that user again need to uh start like the operation or not so these the second option was the most common which i've seen nowadays but
there are others also uh but the other other but the other options is not applicable uh always you should need to worry you should need to look for like suppose the first option you can use object dot freeze to freeze the prototype so by freezing the prototype uh you will not allow object or prototype or any other object to modify so even if somehow an attacker can manage to pollute object or prototype then your object will not inherit any method from object or prototype because now it is freezed right so you can you uh you can just see the last example where i am using uh where there's a thing about object dot create null so you have
seen i was creating this object like uh like like i was just creating object using curly braces but you can also create objects something like object dot create and in the parenthesis you can put null so this null basically signifies that we don't want a prototype object within our object right so basically whenever you define an object there will be a prototype property or object which will be defined by default within your object but if you don't want it to be there then you can explicitly mention it using object dot create null but again you might be needing uh some methods or those methods like two-string method or other method which it supports so again you should be mindful uh before
putting these protections on mitigations that you might be needing that thing so uh this was guys all about mitigation part and uh with this mitigation part i would like to conclude my session and so now if you guys have any question then you can feel free to feature to us and put it on the chat
uh hello
we'll go ahead uh yeah this was actually uh the end of my session like i would like to conclude
[Music]
foreign
oh
[Music]
my [Music]
the one
[Music]
do
[Music]
[Music] do
bye
[Music]
do
[Music]
my [Music] the one
[Music] this [Music]
[Music] so
is [Music] so
[Music] this [Music]
the one
[Music]
do [Music]
[Music]
[Music] my
is foreign
[Music] welcome kavisha you are the third speaker for today and uh very warm welcome to the besides noida 2021 virtual edition conference this is the day one and you being the third speaker we have already had a giveaway for two speakers where we uh were proud to give three pair of stickers in the first one and the and a pair of stickers and a mask in the second one so this is kind of a giveaway session where from your uh you know the session we take away questions we put it in the chat box and uh seek for the reviews seek for the answers via people and uh then they answer it so whoever are the
first three winners we give away them this uh them these uh goodie bags from the besides noida itself so in your session we are having three pair of stickers so please stay tuned for that now again inviting you and now again uh we are let me just introduce you to the entire uh team members as well as the viewers uh we have our third speaker her name is kavita said she is a security analyst and the topic today on which she is going to speak is have you configured aws securely awf from attacker's eye view so i welcome you again kavida and you can now start your session sure definitely over to you hey so today topic is have you
configured aws securely aws from the article's eye view so now you have the clear understanding that what we are gonna discuss that we're gonna discuss the configuration part from the attacker's perspective right what the article wants to do and how he just he or she the leverage of the particular uh user right so before we get started this little bit around me i'm security analyst at apps echo i just love to break the web application api and the cloud security i'm also member of different communities like null infosec and the breaking barrier linen circle and i'm active speaker at different conference so yeah that's just little bit around me so today agenda we're gonna discuss
reconnaissance technique because this is the most important step to find the misconfiguration issue so i'll give you a brief overview how do you find those uh credentials easy to instance why it's reconnaissance is important then we'll gonna discuss different scenario like how attacker has acquired admin level access from being highly limited imuso then we gonna also discuss how misconfiguration it's leading to ec2 instance to attacker to get access to credit card details of uh users right so that is easy to instance that is misconfigured but attacker leverage his or her permission and getting the credit card details of the users and then how html injection vulnerability allows to the steel instance metadata right this will be
quite interesting for you guys and how attacker has acquired full admin uh privilege access using lambda misconfiguration so i have covered like how the attackers see and how he use this misconfiguration to leverage his or her permission right so what are the attack vector you should look for right you must be just aware about this credential that most common almost people talk about hey we found this credential and we uh get those three bucket access this is only one vector there are multiple or i can see numerous uh attack vectors you can you should look for so second is instance misconfiguration is so for example here you have the ebs snapshot is publicly accessible or
the ec2 instance is publicly accessible like the ec2 instance is ideally easy to instance should only allow to the users within a vpc right but if this publicly available uh then it's issue how don't worry we're gonna discuss in upcoming uh slides so stay tuned then s3 misconfiguration most of people are aware about like bucket was publicly accessible or bucket was allowed to access by any aws authenticated user right so this is the standard one like uh most known but most vulnerable also most of people forgot to just uh do proper eyestream misconfiguration and also if the this is also placed it's vulnerable to this right but still you can prevent if you have uh involved
the default encryption or you have used kms right so many organizations miss those part and being the they are not able to like prevent their data being compromised right so one of this then access control misconfiguration so there are resources but the policy has not properly configured and that leads to the unauthenticated although or like another organization uh users are accessing the data of organization be right so this is uh related to access control misconfiguration then exposure of the resources via firewall then what do i mean by that that if the firewall is not properly configured right then like easy to ease or the rbs data right those are publicly available and that leads to a very huge compromise like if
i got your ids data right then it's really trouble for you guys even the ebs right so even though uh if you think about the network perspective right the port number 22 accessible to any random user right so so basically i can just do ssh and do whatever i want to do right so this is due to the uh misconfigure firewall right so one of the standard attack vector you should look for then network security misconfiguration so here organization forgot to like properly define that hey the traffic should come from this particular ip address or this particular range right so here are the lacking of the defining inbound and outbound rule what you mean like uh by inbound rule so if the
traffic is coming from the outside right so that is the inbound rule and outs uh outbound rule is what is traffic like from the inside your traffic is going outside right so that you should uh clearly define and uh you should explicitly mention that hey uh this port number and from this particular ips allow right so one of the standard how this is the issue we gonna discuss soon right in the upcoming then insecure custom application like some of uh people just forgot to think about this i have included that also okay how can the insecure custom application can leads to this like for example i'm just giving you a quick overview right so if you your
application is vulnerable to ssrf or lfi right and that is hosted on ec2 instance then and the role is also attached to that ec2 instance right then it's a definitely huge issue for the organization how that we're gonna discuss but i'm just giving a quick overview if the vulnerable to ssr i can get the im credential or the instance metadata right so these are the standard attack vector that is what to look for not only the lick credentials now we're gonna discuss discuss about reconnaissance before answering those three four questions how the attacker sees first most common step for the attacker perspective reconnaissance part right so first finding credentials so lots of people talk about hey you can
uh we found the credential and we got access to s3 bucket or we got admin level access right but how they are finding so here we have i just concluded that uh different techniques there can be multiple they but these are the most common that you can look for right what to look for then look first is hard coded credentials storing javascripts uh file are the client side right you can just search for it then aws cognito credential in response right so you must be thinking how do i find in the response don't worry i have attached the screenshot for the in the upcoming slide i gonna mention how do you find that but you can find in the
response as well right then again vulnerabilities in aws hosted application like ssrf and the lfi right so what i have discussed earlier so if web application vulnerable to ssrf uh try to get the instance metadata and try to get the credential out of it right uh then you can most common code repository such as bitbucket and github that aws error message searches access unit so we have observed that some people say hey this is not uh allowed to access right but in the response they are saying that this is your aws credential so indirectly you are getting the aws credential right then public snapshot right so here you can uh just search for it that
description like description and the secrets right so you might ending of getting the secrets or the credential or any sensitive information out of public abs snapshot because uh some people or the organization just make the the abs snapshot to publicly accessible right so here you can also find it am i publicly am i so that is ideal practice that you should not uh make your amis to publicly accessible but if the available right so you should always look for public images and try to get what sensitive information you find right then s3 bucket you might be thinking hey i how do i find s3 buckets so i have seen okay some organization store the admin
credential in that s3 bucket so it's most strangers not only that like credit card details or anything right they store that aws credential or admin level credential as well in the s3 bucket without even uh encrypted right so it's what to look for if you find the public listed bucket don't just go for it and file it here we found that s3 bucket is publicly accessible and we are able to get the data try to get uh this kind of things like credential or credit card details right so these are the word to look for and then rba snapshot you uh don't worry how do you gonna search for it what tools might help to
find those rb rds or the ebs snapshot right so don't worry about that i'm gonna discuss about that uh people looking for the one most common and most ignorable thing people looking for help online and ending up or copy pasting that complete information like for example if i'm a user i'm saying hey i'm accessing i'm not able to access this particular instance can you ah just provide me support around this but they are ending up copy pasting their whole credentials in that uh like looking uh while looking for the help right so this again issue so this is the screenshot i have attached that here if you see right the credential being uh get disclosed
in the response itself so it's uh this is how you find right so when you're intercepting the request please look for the response and see if you are getting the credential if you are getting see what kind of access you have right then uh for the easy to miss configuration so you might be thinking hey you talk about dc to instance how do we find the ec instance right so here i have covered some of the tools or the techniques that you can use so senses you can use for finding easy to instance for example compute one amazon aws start call so here i will get the list of ec2 instance that is publicly accessible and
what are the ports but make sure that you don't just browse it and access thoroughly make sure that uh you have the permission if you it accessible just file it okay don't try to get the more information out of it right then yeah this is census and you can use google doc as well google doc is quite uh and the most popular tool and that's what to try for you can simply say site star amazon aws.com w compute so it will have the list of easy to instant and sometimes you might ending up finding s3 as well right another is most popular showdown that is what to look for there is no wrong with it nothing wrong with it
because showdown and synthesis will help you with the two things one is finding easy to instance and also you are able to see the ssl certificate and what are the ports open right so by that you can also get idea that if the firewall is not properly configured right then you can just try to get the access to that particular uh port number right uh like if the inbound or outward rule is not properly there then you are able to access then it's like an issue right because from being outside or you are getting access to one particular organization ews ec2 instance right so this is how dangerous it could be so uh yeah i have attached the rules so he
or this misconfigure look like uh why like likewise means configured right so here i am saying source 0 0 like what you mean by 0.0 it's like any user from the internet that allowed to use port number 443 double three zero six that is my sequel double three eight nine that rdp oh dangerous mysql dangerous 9200 that is elastic source now this all should not be allow this publicly accessible right uh this should be you say this is the my ip range like your organization ip range that should be uh in the place but if not then you can just have the access to here i have attached uh radius instance that they have not
properly configured the firewall rules and i was able to get the radish data right so this is the one screenshot i have attached now to finding the rds endpoint right you can definitely use the google doc you just simply cite like particular any site you can mention which you are targeting and say rds amazon aws.com and say pass or password so you might end up getting uh credential db information right so this is how you should look for the rds endpoint now most common question how do i find the s3 bucket right now to look for the s3 bucket means configuration but how do i find right so first aid most common google search second is google talk right this
like how i was finding rds or the easy to instance same way you can find the s3 bucket as well showdown you can use senses you can use use osm tool sublister and a mask like how you can just pass your predefined uh nameless to this and you might ending up getting the s3 bucket because there is a standard uh way right that organization dot s3 amazon aws exercises i do three four ways to find the s3 bucket right it's the only three four uh ways to name the particular ester bucket right so it's easy to brute force as well so you can use the brute force technique as well in the dns record you might
get also then other tools like uh certificate transparency you can uh use right then there are numerous uh bucket finder scripts like bucket finder bucket inspector lazy s3 there are so many scripts available you can just use that and you might ending up finding that rocket and most uh favorite of the security professional is greyhead wall for bucket search right so you can also use that but it's a paid so but you can use all this method right so yeah so i have attached one of the screenshot that how i find the s3 bucket using google docs so you can use same technique you just in url instead of assessment you can use the credit card or the password
you know right how to but it's like how this is a standard query you should look for like star s3 amazon aws.com in url you can either use assessment password anything you are looking for now reconnaissance is done and you have found a credential as well but you might be thinking hey what can i do next right because almost people ending up hey we found the credential and we might end up filing the issue this uh credential is being uh lately in the github don't do that try to see what uh kind of access this particular user has and see how can you escalate your privilege or that particular victim user right so i have also covered uh like
like in the previous right i have mentioned that i have covered different types of question and how i'm being limited user to the high privilege user so standard approach i have like uh keep in mind like made the simple flow that can be a long flowchart can be as well but if you think right in general the odd ah all i can say got you got the credential right as an attacker now you should try to enumerate the permission hey uh what kind of permission i have am i uh limited user if i'm having admin level access if i'm having vc2 level access if i'm having only s3 bucket so this all should look it all
what to look for and after that see if you can uh like do the privilege escalation right if not then see if you are getting uh sensitive information for example that one particular having access to just list out the s3 bucket and there is no way you can escalate the privilege of that particular user but in the s3 bucket itself uh you are ending up getting the credit card details transaction details right sudan then it's again high level issue right so it's what to look for so but please start with the enumerating permission just don't say hey i found the credential and you are reported just follow this standard technique and for the privilege escalation don't
worry i have cursed some scenarios so you will have fair understanding that how can you do the privilege escalation from being highly limited user to being admin right so it's uh i have covered few scenarios so that might help you the first is how article has i acquired the admin level access from being highly limited imu right so first i got the victim credentials so i'll try to configure the profile then i just try to enumerate permission so if you notice right i have the permission of i am related and to get all the least data there is nothing else i have if you think about and one is sgs so it's as an attacker i was like um
that is so limited permission what else i can do but that is right so hey i can have the permission to do that yes right so what i'll basically do i just say sjs and get the credentials and just try to see what kind of policy attached to that particular user right so i have a credential i i try to list the attached policy of that particular user right so how do i get the username using sts functionality right so it's simple so aws i am list attached user policy and i'm saying hey username is this uh can i get the uh policy so i got the policy number and after that i'm getting the current
policy version i want to see what kind of persian it has and what is the policy name so i say hey aws i'm get policy and this is policy number v1 is a default policy and this is the number i was like okay let me see what else like what are the different types of policy available so here we have the five policy and it's what you look for when you have the five policy it's because you know there is this particular user only have the list and uh i am the leader permission what else you can do so you should uh work to look for the all policy right so after getting the list of policies just
try to enumerate the permission of the and try to get all the information about different policy so earlier was this i am get list and the default policy version right uh that is only get list there is nothing interesting but here you see right for the v5 i got that okay that is policy v pi and that is may be outdated but it has the admin level why it's the admin level like so that i'm talking about because if you notice right action is star effect is allow resource means also star that means uh like particular actor or the attacker can do any action on any resource so it's the kind of admin level access
so as article oh that's awesome now how do i make this policy as a file let me try if i have permission right so uh i try to make v5 as a default policy and there is no error and that success so this is basically privilege escalation how like for example you are being uh having the get and list permission or the limited permission now you made the wi-fi as default policy and the v5 was having the admin level credential so it uh privileged escalation and after that what kind of permission the user was having c got duty lambda access easy to instance level access everything it has so we confirm that hey this is how the
privilege escalation happen standard like we made the we enumerate the policy and we made the our permissive policy to default policy so this is like most standard so this is what i'm saying it's always what to look for the permission and try to get sensitive information or try to perform privilege escalation so that you can say that it's a high severity issue and this is how it works right so what was the my approach so far i got the hard coded credential i tried to enumerate permission i got that hey this is having the item related permission or the catalyst permission then i try to enumerate the policy and the one of policy was having admin level
access and i just made this policy as a default policy so this is the approach to do the privilege escalation okay now you must be thinking hey ah you say we want to look for the public ip of ec2 but i found that what should be my next approach right so you should look for is that any port open right is web application running on that ip like you found ip right but is there any web application running on that ec2 instance ip is easy to instance accessible to public user right is default configuration being used right so all these things you should what to look for now i'm gonna discuss like why and i'm gonna also answer how miss
configure easy to instance is allowing attacker to get access to a credit card details of the users right so you must be thinking hey this is easy to miss configure what else we can do don't worry i'm gonna answer everything i have covered one scenario as well so we found that hey this is one uh public ip of ec2 instance and we found that a web application being hosted on easy instance right so here you see that it's accessible on the port 80 and it's saying that hey url must be string so we thought that hey url parameter being used so it's what to look for right as a attack or the panel twister store right
so it's what to look for so we said url and we passed ifconfig and we found the ip address and so we just say hey this is vulnerable to ssrf if you are just newbie then you might be thinking hey we found your publicly accessibility instance and it's vulnerable to ssrf just don't do uh you you can file it but just don't limit yourself by doing this uh you should always uh try to get the metadata like how do you find it right so your ideal approach should be web application is hosted on ec2 instance yes it's a web application vulnerable to ssrf yes it's a role attached to that easy to instance yes then try to get the improv credential
right we did the same we say 169 to 54169 254 standard uh address for the instance metadata right so we are saying that metadata i am security credential i got the role and the credential as well so after getting the credential you try to enumerate permission like how i uh show you right guys key how do you enumerate the permission so same way you enumerate the permission and in this case we found that s3 related permission so basically you say ws ls profile ssri stolen credential like what you have found the credentials so you configure the profile and you just try to uh get the s3 related data so there is so many interesting things
like there is a card holder data that is secret being available so you can sure you got the credit card details of the user in this card holder data but there is another uh for the surprise package for you guys that uh qrv found the admin credential as well right so if you see right i'm using sync command to just uh copying this credential in my local account and it was success right so your admin user.txt i also uh downloaded the credit card information right but instead of only the credit card that is also what to get the admin credential right so this is what i have also discussed while in the records reconnaissance we were discussing right
that you might ending on finding admin credential in s3 buckets so you know we are finding right so uh this is all about like how the c2 instance how from being public ip to downloading sensitive information so how do we like let me just summarize how do we find out all these things and what was the like what was the laking behind right found credential with permission around ect related per operation right application is hosted on ec2 instance was vulnerable to ssrf rule was attached to that execution for example that is vulnerable to ssrf but if there is no role attached then how do you find the credential right so this is always uh to look for that
the question i have asked read queue or the flowchart i have made okay how to look for that is what to look that exploit to steal i am role credential now you find the credential now see how can you exploit rate right then try to enumerate the permission and found a s3 related permission and list as to bucket and download data this is all we have done and i have covered why we have done and what the reason behind it right now this is a little bit around attack surface analysis for this particular default configuration typing usage right because this public accessible ip the web application hosted our ec2 was vulnerable to ssrf no proper input validation was there
that's why it's available to ssrf rule was having to work like role was having access to work with the s3 buckets data storage in h3 was not encrypted for example that's why i told about right if the it's not encrypted then it's again misconfiguration issue why because if it's encrypted even though we are able to access but you are not getting to what is being stored because it encrypted and you are not having access to that master key right so that's why sensitive information being stored in the sd bucket like credit card details and it's more specifically admin credential now you say it's similar to sounds like capital one bridge how because there was a misconfigured
firewall and attacker got access to ec2 instance and he after getting the access to ec2 instance he also got the im role access to the s3 access right so that particular role having access to s3 and uh using that role he able to download he or she able to download s3 bucket data that is was having the credit card details right so this is all about capital one breach now another question how attacker has used html injection vulnerability to steal instance metadata it sounds like for you guys like in html injection hey this is not that huge impact vulnerability right it's a html injection but it's what to look for if it's hosted on ec2 instance and
using aws right like obviously using aws if they say to instance so what was the approach if the application was vulnerable to html injection then try to see if it's also available to ssrf right so basically you are saying h1b h1 so you found it's getting bold you found that hey it's vulnerable to html injection but what if i'm saying image source and the bob collaborator link and uh completing right uh complete the tag if i'm getting the heat in my above collaboratives am i saying hey this is sounds like vulnerable to the ssrf now what's next so it's hosted on easy to instance right then it's what to try further and the rule being attached then what to try
to get the credential out of it right or the metadata how that we already discussed right so that what to look for and you get the ec2 metadata so from html injection to the getting easy to metadata how h like you found the html injection then you found the ssrf application hosted on ec2 instance and then you got the ec2 metadata right so this is whole thing now how attacker has acquired full admin privilege using lambda misconfiguration okay so lambda is serverless right the you are using lambda function and that is all the any lambda level access right and you have not properly configured or defined the rule particularly right you might ending up giving
a list privileged user to the admin level access right so how don't worry we're gonna discuss how it can be possible so you got a credential first thing you do you list the user hey what are the users available right so i i found four five user you might ending up finding thousands of users based on how big organization then you say hey i got to be user now what are the policy attached to user right because it's most important so by knowing the policy you get the more information like how we did last time right so i try to get the policy out of it after policy i'm saying hey this is my policy version
okay and uh this is my policy number here i'm finding that hey this particular user having the lambda level pass rolex's and this having name as a lambda manager okay i say okay that's good there's another policy i found and that is having debug role that has two role i found debug and the manager uh right uh lambda manager lambda manager was having this kind of access and debug role was having administrative level access right uh but default was the lambda manager right that we have seen and now as an article you want like okay what can i do with the lambda manager right let me try to make this lambda manager role to the
admin right most fundamental try to perform privilege escalation right so for that you say aws is azim roll and here you are providing the arn value of the lambda manager and you got the temporary credentials of that user right now what you will say that hey can i attach the administrator policy to that particular i am user right so you use moto script or right so here basically what i'm saying that uh attached policy user will be the price like lambda manager and the policy ern will be i'm mentioning the policy of the debug role that is having the admin level access right so here i'm mentioning so indirectly i'm saying that can we just please apply
uh admin level policy to the lambda manager right after that uh we use the lambda function and to like to perform the leverage right the lambda manager to perform the privilege escalation using lambda function you first create the lambda function and you invoke it right so here i am saying aws lambda create function i am saying this is the function and the script you can use and here we say rule is a debugger debug why because it's admin level access and after that we just try to invoke that particular function and profile we are using is lambda manager right so basically we are trying to perform privilege escalation using lambda function and uh to be amazed we got the full admin level
access so here now we have made the lambda manager user role that is quiz to the admin level access right he is no more to the having access to only as a lambda level access right now he can do whatever he want he or she want to do so this is how you should look for that don't limit yourself being hey we found the credential and or this is the user having just limited permission we can do nothing so this all you should look for try to do the privilege escalation if not privilege escalation then try to get the sensitive information out of it now you must be thinking hey what tools i can use
a scout suit you can use this is you can do the attack surface analysis how because this crowd suit is a like aws multi like multi cloud uh tool for the ci's auditing so it will list out hey how the ec2 is mixed and figured out is configure right then you can use scroller then use s3 inspector it just automatically say that what are the misconfiguration happen for the s3 then you can use enumerate im to see what other permission that particular use paco for the penetration testing purpose is we have a question for you kavisha from the chat box okay uh shall i read it for you yeah sure definitely yes so it is it says if we create too
many rules for each how we will manage them like uh what can you just ex mention again if we create too many roles for each how will we manage them i'm assuming that too many roles for one particular user right absolutely right so what you can you should always look for the uh you should start if i'm assuming that this particular user is within organization right it's a multi organization like uh different uh you want to allow cross account then it's a different policy right but in general you should uh follow the im policy which uh clearly meant to mention that in the aws guide right like what is the standard approach you should follow
and try to use the cloud trail that you have the logging in place right that what is uh being requested at what time from which ip address is being made right and then uh you can also uh send this login information to cloudwatch if been uh this particular users access been uh escalate right that one we discussed so that lambda manager rule uh now having the admin level access right so that you will have uh information in that uh cloud and you will be notified right another use case you can use a security hub that is also used to notify you and another uh that is access control tower that is service being provided by
aws right that manage different roles for you are that that login information being done in this particular account right so this is how you manage or in general uh you can create a different account that hey this only being this operation on logging information always being done by this particular user right for example if the you are saying that this is the account a and there are different user a b c and abc users is having the admin level access be having the only to list the data and see having the uh for example login information but what if your account being compromised then it's a trouble right for you so try to create the
another account for the logging so same way you can uh just define different privilege and uh use this logging and monitoring services as well hello am i making sense yes absolutely thank you for answering the question davisha i have another one for you from the chat box itself okay from the live chat going on on youtube so it says uh let me read it for you how can i increase the severity of my ssrf where the server is on aws is there any internal aws by default credits or something which i can use which i can use so it's a definitely which i have covered right uh if the application vulnerable to ssrf right then
try to get the instance metadata if the rule being attached to that web application right so for you find that hey this is one level to um ssrf then try to get the instant metadata by simply saying 169.254. 169.254 iem metadata security credential first try to get the rule and that try to get the credential out of it so this is how you make the severity uh most now again if you don't want to just limit yourself by getting the credential what you can do you you now have the credential right the temporary credential you got now what you can do which i have already discussed that you configure the profile and see what kind of privilege you have
if you are like fully blessed you might ending up getting that admin level access as well but if not then uh see if is there any technique you can apply to perform privilege escalation right like i have covered two three so it's what to look for this is like ideal approach i have also mentioned the what was the flow for this particular attack if it is possible we can take more questions from the chat box we have enough time for that yeah
all questions have been cleared kavisha thank you very much for being here giving your precious time and to the people and to us we all from the besides noida team we are thankful for you being here
[Music] bye foreign [Music] um [Music]
the one
[Music] do [Music]
[Music]
[Music] foreign
bye
[Music] foreign
[Music]
[Music] the [Music] the one
[Music]
dog [Music]
the next speaker for today is philippe humeyao a brief background for him he is a ceo ceo at crowd crowd sec the topic on which he is going to speak today is leveraging the crowd power to regain faith in internet zero trust art architecture so we welcome you philippe uh for being here you may start your presentation yeah thank you uh i'm delighted to present that beside noida uh i'm filippimo and i'm actually the ceo of crowdsec and i've been uh in the past uh pentester for years and years meaning it's uh it's a job you know where you're a contractor and you have to break into networks and find vulnerabilities and tell a customer oh
you should definitely fix this because it's dangerous right so after doing this for years uh i've decided to switch to another line of work and created us a company that was more into defense side right so we were doing high security environments high security hosting and the stuff worked but the thing is you know it was complicated it was a stack of many different products and uh in the end it was you could not carry it easily you could not install it for a customer in say less than maybe two months so uh we looked into this with our cto and we're like okay how can we do it differently so that at least people can use it you know without
uh pain and it could be a very straightforward uh to leverage the security level and we came out with a an idea that would be let's share the signal of the bad guys right what if we could identify the bad guys and share the signals between us between all the sick ups community members all the good intended people and this is what happened so today we are something like 14 000 uh users sharing this across the globe and growing by the day by roughly one percent today we will be a lot of users very soon and the more we are the stronger the systems become so without further ado let's jump into the presentation first of all i think we've made a
mistake for all the last years i mean if you look at those companies those logos you know all of them nearly right they have close to unlimited budget like literally if you take jk morgan they have a budget per year of something close to um 800 million dollars in cyber security 800 million dollars i mean to the figure it's enormous it's i mean even governments don't have that in a budget most of time so and they've been hacked nevertheless you know they've been hacked whatever the amount of money they have been sending uh spending in this they got hacked which means it's probably the wrong approach it's not about like outsmarting the hackers because if outsmarting them
would work spring so much money would have worked and it did not so it's about outnumbering them we think the problem is not about outsmarting them it's about outnumbering them and why is this that so so much money didn't solve the problem because it's crazy right i mean when you invest so much you would expect results well they fight against impossible odds the first one is time time is in the symmetrical force playing for the attacker for the offender because you know times is always playing in on his side you never get to choose when you're attack you never get to choose when you uh when you get um a zero day or a new vulnerability or
something like that you never get to choose when the patch is available which is even crazier and actually you barely get to choose when you can deploy it so time never plays for yourself right it's always playing for the attacker the second thing is the perimeter perimeter is a considerable uh problem nowadays because you know people they are uh struggling already to deal with the current perimeter they had but now they have shadow ids things that are in the cloud seeing that are you know on sas services in containers in whatever is file wherever they can be you know it's everywhere and nowhere it's scattered across so you cannot really set the limit and so okay this is my parameter
and everyone else just go out no that doesn't work like this and that's a real problem too and now with this covet crisis we need to create vpns a lot everywhere around the globe so that people can work on distance okay fine but pretty much all companies were not ready for that at all they were just you know they had to do it but it was emergency time and you know it never is really going well in this case usually when when you do things in emergency it's not good so what happens is it's full of bridges i'm not saying everything is bad i'm saying at best the perimeter isn't even and the last thing
would be money i mean when you invest 800 million dollars in your security and the hacker that breached you barely invested i don't know maybe 80 000 probably closer to eight thousand dollars how would you compete it's impossible it's just not the same you know uh factor it's not the same amount you you're talking about so it's impossible to play in a casino what the bank would have a hundred thousand chances versus one to win against you you would not play in this casino right i would not either so that's why you know hackers are always winning first of all we are trying to outsmart them which is a mistake and second there are these three
strong factors that are playing against the defenses right so we we think at krautsek that this castle strategy it belongs to the 80s it's over i mean you cannot say i have a firewall i'm secure it doesn't hold anymore there's no firewall bastion thing anymore it's just over the things are all across the place and if you don't want that you will have to go back into your medieval old times you know with the pager and the facts and stuff like that and we don't want that right modern businesses they have to open themselves and this is the problem this is the gate to hell so we want to to solve this problem this is
our goal at crosstalk so how do we do it we think you should defend the thing wherever they are in their context and not try to outsmart anything or anyone that would be a big mistake the second thing is the only way of doing this is leveraging the crowd and for god's sake i'm speaking to indians here you guys are 1.2 billion something like that right so it's it's the utmost importance that we join forces together because if you think about it the hackers are probably what ten thousand a hundred thousand at a scale of the internet we are millions on the other side we want to defend ourselves right millions so why on earth would we leave them the win
which we can definitely defend against them we are so numerous so and the crowd has not been leveraged in cyber security i mean i'm talking here like meaningfully because if you look at it what there are bug bounty programs yeah what happens they are like ten thousand no there are hundred or a thousand people this is not enough this is not what i'm talking about and if you look at you know driving waze is a good example ways you know the leverage something like millions and billions of users that's why it's efficient in the first place so what i'm saying here is we should definitely team together this is the the main thing friends it's worked it worked too before like
facebook was very efficient you know it leveraged millions and billions of people working you know there is linkedin crowdfunding you know it and what about security right this is where we stand we are building the ways of cyber security what we want to do our goal is to have uh the same magnitude the same amount or maybe not billions but already millions of people collaborating together and what we do is we take local information from the logs from that every kind of work any kind of work really and we scan them locally at your place we don't export anything it's really on your site still and within those logs we are looking for bad behaviors you know people that are
doing i don't know credit card stuffing port mapping pot scanning http scan stuff like that and that are trying to compromise you or your clients this is what we're looking for and with those scenarios we often off we just can you know we identify those and we block them that's already really cool but there is better things to do even that this is where it's uh it's becoming really neat now that we have found someone maybe locally doing crap we can share his iep globally to the network and that becomes a lot more efficient because everyone reporting is generating a signal a trace that helps us all to defend ourselves so how does it work
well this is a massively multiplayer firewall if you want or an edr or an ips ids you call it whatever you want basically what it does it's scanning logs right and within those logs it's finding bad behavior so it could be any kind of logs could be locks coming from aws could be locked coming from seam elk kafka whatever you name it syslog you know john d and within those logs we're analyzing whatever happens and sometimes there are bad behavior people scanning your website credential stuffing credit card stuffing port scanning things like this okay and to find those you can simply you know go on to the hub there are a lot of scenarios that are already pre-made for
you uh i will switch quickly to this one so in this collection for example you can scenarios for apache for http for cpanel doth code hd proxy iptable so you name it the scenario already exists and you can download them really easily say you want to work with nexi you just cast paste this line of command and you're done i mean it's as simple as that so once you have found the behavior you want to block and the the engine found something or someone you can obviously block it right it's obvious but you can send for example captcha if you're working on an http layer why not send a captcha actually it's it's better actually it's
it's going to be more efficient and uh it's it gives a better result on average on http layer you can lower the the rights of the person the credential of the person you can prevent him or her from going into i don't know wp admin or slash admin or accessing some higher uh credentials or higher privileged credentials and you can eventually say send a multi-factor authentication for example say on your mobile you get a number or a text message or something like this if you want to just send this alert into a second room you know in uh in something like uh what's called a slack channel for example it's or to just trigger a script you do whatever
you want you detect at one place and you block at another place and you can do it in whatever manner you want and once you did this you found a bad actor with a bad ip and you know what we're interested in this now this ip if you're okay with this you don't have to share it's optional but if you share with us we share with you it's pretty cool so if you share this ip with us what happens is we check that it's a right ip it's not a poisoning attempt someone trying to fake a signal someone trying to think uh make us think that gmail is a bad actor that microsoft update is a bad actor or whatever else
you know and then once we see this signal is pristine and genuine then we send it to the whole network everyone that shares the signal is getting back signals as well and it's getting in real time a lot of ips that are dangerous for them that way they are not taking any risk and they are getting the benefit of having this uh strong protection uh for free and it's coming from the community it's kind of a global internet neighborhood watch if you want or some kind of um digital immune system rather it's it's even more accurate outside all right so once we have that we are safe from harm's way or more or less now
it's better than what existed before because it's actually faster like 60 times faster than for example fail to ban it's actually also uh it offers an inference engine it provides observability out of the box you have a docker container that will show you a console and you can see whatever is happening on your network you can have also observability replayability this is modular it's modern it's an easy grammar you can get so it's pretty cool um and then you have it's ipv6 ready it's multi os multi-layer and it has multi-stage detection you can do something like if this happens and that happens and then that happens well then it's a targeted attack for example uh so i have a question here quote sec
is though can i even use it on my temporary project servers since i have managed this request yeah of course of course you can absolutely use it in any context you want you can use it on a vm you can use it in a container you can use it on a bare metal machines it's absolutely not a problem it's already shipped for pretty much all the versions of linux you can think about for most bsds and um yeah it's it's available for for anything right so um next is it's free and that's probably the best part of it it's free in open source it's really something that you can leverage anytime you want any anywhere you want
there's no limit to this and you can embed it in your own code you can embed it in any hardware you want it has been reviewed by professionals so coded by professionals already but reviewed also and audited by professional it's free of charge it's transparent and you can contribute to it actually you're very welcome to contribute to it so now if you look at this tab uh this is the code tech repository on package cloud and you have you know packages for pretty much anything you can say tbn red hat uh you know arm various kind of architectures so it's really easy for you to find whatever you need in whatever context you need right
sorry back to the presentation i'm probably driving the host of the show mad doing this so hey it's time for a demo right we all want to demo so i love the demos myself here it goes so we have a shell here very simple basic shell and it's on the linux machine that is hosting uh nginx website with my sql so when you install the product uh with the deviant package it will auto detect everything for you you don't have to do anything here you see we will check for uh the values log files you have you see that there is apache httpd nginx sshg mysql telnet and smg and it will install every services
and scenarios you need to be protected all by itself you don't have to do nothing for that if you want to reconfigure later on you have the wizard super easy to do so now that it's running let's send some attack on this let's use nikto nixo is a very simple web scanner you know and as soon as we start it we see that cloud site coded it's it sees an http bad user agent http probing chrome on static http sensitive file inclusion and so on the force so it knows something is wrong and it's blocked already that's great right and if you see the decision list now this ip it's been banned for four hours that's
pretty cool but if we check our uh http server so you can inspect another sorry you can see the details of an arrow what why it has been been and how and for what reason you know the the isp what it tried to do you know and then if you check you can still access the web server why because this ip is bad it should not be able to access the web server it's because we haven't installed any bouncer understand that the thing is we have on the one and the agent that is detecting and on the other end we have a bouncer that is remediating the problem and this is exactly what it is
you have to install a bouncer so here for an nginx because it's an engineering server but you have bouncers for pretty much any technology right so you install the bouncer and all of a sudden any iep that has been either detected by you or sent by the central system to you is blocked right away so anytime you get someone scanning you bam it's over it's getting forbidden goodbye that's cool right but we have better than that look we remove our ip from this list right we don't want we want to be able to go on with the demo so now we'll send something else we can access back to the website everything's fine we remove the ip
what we see here is that we have the firewall logs and that it's blocking its ip table based and uh it toss the ips you know that are blocked into the logs fine we have an ip table scenario there's a parser for the logs and there's a scenario written in yaml that will parse all your ip tables output from the from the firewall so now that the this knows new trick let's do an end map right away we are caught and blocked for uh iptables can multiport so we know this that someone has been trying oh damn sorry i cut the demo i'm trying to be back to the right place i have a wrap
we knew that we were good for scanning right sorry here we were all right my bad sorry guys coming back to it was here here all right so we at the scan multiport we blocked it my bed so now if we try to access again to the website so we see first of all that the the ip is back in the list and if we try to curl to access the network it's banning us so we cannot do anything and now the cool thing is we also have a dashboard when you do this command it starts basically a container that is instrumented with metabase and metabase will give you a nice neat view of what's happening
on your machine right so you can get you know login password here right yep and then you can see what happened on your network right see the alerts see the scenario that have been triggered everything but we haven't made much things so far we have made a scan uh port and http scan so we don't have many stuff underneath necessary to put force but say we want to replay logs from the past that's a cool feature as well let's take logs that are a year old and let's inject them into our uh crowdsack instance and it will check if there were aggressions already in the past and tell you oh i would have done that i've seen this and so it's also
allowing you to see if your scenarios are not too twitchy and would not block something legitimate but when we do this we also inject all those alerts into the logs and into the container so if we check it for a year ago or three years ago or something like this we'll see every decision that has been taken on those logs right so we can see that you know actually this machine was across a lot and we didn't know about it right
and you can see a lot of metrics because we know you love it right so you get anything you want the number offline parse read where we found something you know when the decision was taken and so on into force and there's a brand new thing i should show you also we now have uh an online console which isn't better for now but i can show it to you so what it does is it's showing you in an even better way all your instances so for example caramel here is my instance it's my machine that runs 10 scenarios switching two bounces and i can check you know a few things but mainly i can check my
alerts and i can see you know what's have been happening where from what what has been attended by whom and how isn't it cool i can see you know the target machine who was sending the attack and the country it came from the ip it came from the scenario as such brute force user enumeration and stuff like that ain't it core so that's that it's for that's the the console you can see a lot of things here right all right so that's that's for the demo up you can get the next slide uh yeah so what can a behavior engine do for you well pretty much everything nowadays is spitting logs right your machines it's
spitting log obviously your web server is spitting logs your car inspecting logs your phone your spitting logs your router your microwave oven maybe so many things speed locks even planes are spitting locks but the thing is we can any time there are logs generated we can more or less find uh what's behind it right sorry i was sharing the wrong screen so we can see what's behind it so in the logs we can see applicative ddos obviously level 70 does uh crosstalk has a use case which makes it super easy to defend against level 7 ddos for free um there is drive by download you know ransomware there is resource abuse uh credential brute forcing you know let's say the
brute force ftp brute force uh active directory whatever there is so everything that is cross-site scripting sql injection that would compromise our web server port scanning obviously web scans as we saw credential or credit cost staffing this is called i mean if you reuse credentials that were used elsewhere or if you are getting a lot of people you know with microtransaction of 0.1 dollars with credit cards where your average cart is something like 30 dollars then it's credit card stuffing they are trying to validate credit card numbers and we can easily defend against that and credit and credential stuffing how do you know if you get someone reusing a credentials if you're not in the network if no one
else tells you okay this same credential have been used with me and with me and with me and you know a thousand people are reporting it then it's credential uh stuffing and it's extremely hard to detect if you're alone or impossible actually but scrapping some aggressive boats you know booking all the products or stopping websites from functioning or you know scrapping the images or prices or whatever targeted attacks i mean targeted assa attacks are also detectable because say if someone is doing uh um web scan and then a port can and then reinforcing your credential it's not just a minor thing they are retargeting you and and they want to get in right so what we're up to here is a
resource war understand me well i mean hackers the only thing they don't want is to be naked industry to be found by the fbi at 4am in the morning because if they do it from their own ips it's this is what's going to happen they will be sure they will be found by the fbi or whatever local enforcement agency and so what they do is they are hiding the activities behind ips that are either stolen or borrowed or bought for the for the job or sometimes institutional or state sponsor so this is what they don't want they don't want to do it from their own ips so they use other ideas what we do is we
are burning those ips one by one they are constantly you know uh and that's how we will fold the problem of hacking that's the best way of doing it it's not by outsmarting it's about numbering all right so you can see us as some sort of crowdsource intelligent intelligence it's it is what we are if you take uh the classical uh cti it's based on you know a lot of machine running uh fake services honeypot simulated services over a couple of hundred servers on a couple of clouds right but what we do is 100 different we are running real servers with real services in all types of environments and connection and not to 100 minutes we
already 14 000 harnessing the power of more of more than 30 000 machines around the globe we are the biggest honeypot ever on earth so far so meaning we have a crossover cyber intelligence and across cti which is extremely efficient and we want to become the internet trust broker okay we want to become the one source of truth that you could turn to and ask okay is this thing dangerous or not and this is where it's entirely uh new you just ask a question to our api because we also have an api this is the premium product and we will tell you this ip abcd we know it and it's dangerous don't accept it don't pee with it
or maybe this ip is dangerous but not for you maybe it's like a running crypto miner worm from whatever it's a granny computer and it's not dangerous for you okay it's not it's not perfect but it's not you can let it in your webshop for example um it's highly curated it's made for your needs only and you can make you can make either hot query or local cache query if you want if you have like a high performance network and that you want to you know interface live you don't have to do it online you can do it cold obviously in ipv4 uh about ip is a contextual thing you know before being bad it was good and
then it's been compromised by a hacker and then it would be cleaned again by his legitimate owner one day his administrator right and it suddenly wrote for a short period of time maybe 72 hours so what we do is like every 72 hours we remove all ips that have not been seen doing crap again meaning it's an auto cleaning system you know it's a probation period and if your ip is clean you don't have to do anything you will disappear from the ban list so it's different from what happened before so we have a consensus chamber to avoid poisoning so what we do is we have trust rank right so those trust rank are speaking for the
level of confidence and trust we have toward the person that is reporting an ip obviously it's done automatically by the software right but maybe this machine is very recent we haven't seen it before right so why would we trust it it's there for like one or two days it could be hacker well there are other machines they are here for like six months always up and running and the reported things that we could correlate so we are sure they are serious so those are transferring contrasts from two three and four are people that are either just joined the product the program or they are not yet uh at the top of the ladder we listen to them but we don't
trust them so if they have a signal it has to be validated by either a trust rank one actor or us we are trust run zero we also run a honeypot of our own and we can validate your own decision on your own spottings and if we saw them as well we also have a canary list it's a number of ips a white list if you feel that you cannot touch by any means so if you say for example google vote is dangerous well maybe it's fast maybe it's consuming a lot of resources but no we won't ban it gmail either or google or whatever or microsoft update or acmi or cloudflare on stuff like that we won't ban them you
know because uh it's unlikely they are really dangerous and even if they are they have to clean their stuff themselves and they will do it quickly we cannot block them and there are predictive algorithms that are digging in our logs and in our data lake to see if there are merging patterns like ipa and ipv and ipc and ipd are propagating in attack but spreading the load ipa is doing 20 of the job ipv is doing 30 of the job and so on so forth so we know that ipa bc and d are working together so if you saw ipa coming to your place you can directly ban ipvc and d because they will they
will come soon for you as well and once an ipa has been going through all this process which is actually occurring quite fast uh it's in an ip reputation database and it's broadcasted to the user network all right so your logs are never exported it's extremely important uh i see a question sorry yeah i mean should i read it for you yeah sure so so the first question we have received for you is crowdsec is dope can i even use it on my temporary project servers since i have seen malicious requests many times in my logs yeah absolutely i mean you can use it in any context you want it's super easy to deploy you have packages for pretty much
all architectures and all kind of processors uh and if you don't have you can just prove their sources and compile them it's done and go so it makes sense yeah absolutely to protect your projects uh with the classic and the second question i see is about the dashboard right all right so i'll read it for you philippe if it is okay sure would it not be helpful for the network since i'm not doing things much meaningful so it doesn't continuation to the first question the person has asked yeah well if you get attacks on your temporary project and see malicious requests we are interested right and even if you don't share nothing with the network it's still good to protect
yourself it's not a problem so if you see malicious attacks yes we're interested and if you don't share anything because you don't see anything it's not a problem the product is for free you can definitely use it to protect yourself
so i'll read the third question for you philly it says the dashboard part needs docker to be installed on the machine right yes um so it's it's already embedded in the system right so when you install kratzek you directly have the docker container pre-made for you the only thing you have to know in this is like you cannot run it on a very very small machine like with not enough ram and not enough cpu because obviously docker is consuming a bit of resources for itself you know so just be careful with this don't run it on a machine that has like less than one gig or two gig of memory but other than that it's not a problem it's already
shipped uh with the software so back to the slide bank one important thing is you have not you don't need to share your logs with us your logs are treated locally in your promises on your servers you're not sharing any secret of your uh customers with us the only thing we collect when there is an attack is the time stamp of the attack the offending ip the ip that's been aggressive to you and the behavior the scenario it triggered so for us european it's called gdpr compliant because we respect private privacy and private data and you don't have online dependencies so you don't have to share with us anything if you don't want to and
everything is for free except if you don't share right so it's pretty fair uh system i'd say um and how do we make money uh a lot of people were usually asking how do we make money well if you don't share with us but you still want to have the cti part we monetize it you can ask our api anytime you want and as many times as you want whatever you want but we will build you for this so if you don't share anything with us we will bill you for accessing the api this is pretty much how we make money and this api can be leveraged anywhere on your local os soon we will have a mac
port and a windows port it's on its way you can use it in your firewall or i don't know in the firmware of your network camera on your nginx or on the lambda or an apache in your arduino project to avoid your iot devices to be compromised in the javascript or php environment whatever you name it it can be anywhere and anything so just to finish talk some real world example that we had the first one would be this uh um bootnet right that was using 7000 ips to block an iptv system in turkey it was blocked in under a minute um by krasek uh on a virtual machine like with two cores and i think four
gigs of ram really really small you can see the use case on our website and um another time we blocked a credit card stuffing uh campaign thrown by a hacker that wanted to check and double check the uh credit card numbers he had uh in his uh that it was only and um he was stuffing the the payment getaway of the customers with numbers that he wanted to validate and doing only like 0.1 0.2 euros transactions to check if it was actually an existing number and if it could still be used and actually we could block it as well because it was super easy to find the pattern he was using because he was not
browsing any product he was directly jumping into the payment tunnel and and from there on validating the credit card number so it's pretty easy to follow those kind of attacks because they have like a signature so yeah what we propose here what we offer here is a crowd protection we use behavior to feed mr reputation and mr reputation is feeding back mr behavior and the bigger we get the best the protection becomes so now up to your questions uh we have another question uh which says what is the what is it what if an entire subnet goes down due to one malicious user so we usually don't block a full subnet except if the subnet is really bad right
uh you can block an ip and if you see something like i don't know 30 to 40 ips from this subnet flowing you can decide to block the whole subnet we would recommend though not blocking if you can in most situations but say if you're on an http layer send a captcha rather it's it's smarter it's easier it's safer but you don't have but if yeah if many many many ips coming from the seven subnet are doing crap then you can block the subnet if you want or not or just block the ips one by one uh if many people are using the same nat ip uh you know and one is doing crap and
there are 3000 users using the same net ip then the problem is a bit different then you know we would say uh don't block straight forward and try to rather use it a smaller manner to block them you know with capture or to or multifactor authentication and stuff like that um and if you block them maybe just tell them like there is really a lot of thing coming from your network clean it otherwise we'll block you you can also do that and there's another question i think vandal yes uh philippe it says that what has been the biggest achievement for crowdsec most recently so that is a personal uh one for you yeah i love that one um so one of the
achievements is like we had we now have close to a million ips in our database that's crazy i mean 14 000 installation and half a million ips in our database that is a landmark because we know that we are seeing a meaningful portion of the hacking activity online and another achievement we had is that we are being installed in two main tier one hosting providers in the us i cannot name it but it's actually deploying machines a lot with the software and we are seeing traction all over the world wheels we also are now used in 100 different countries uh which is for soft analysis close to a year old quite crazy
i think we have had enough of questions for today now okay wrapping up yes thank you philippe for being here and giving your precious time philippe is kind enough to give away a crowd sec hoodie to a lucky winner also we have mentioned in the chat box the link to giveaway form where you will find the questions related to the same session giveaway price for this session is a try hat me voucher and a pair of stickers so don't forget to fill the form once again i'd express my gratitude on the behalf of whole besides team to you mr yumyao for being here and putting up an a highly informative session now that we are heading towards the end
of the day one for besides noida conference 2021 i would like to thank you all for staying tuned and being patient learners i would also like to congratulate everyone who attempted to answer the questions for giveaway and irrespective of if you win or lose you're a winner already somebody has rightly said and i quote success is not final failure is not fatal it is the courage to continue that pounds and on that note i call an end to the day one see you all on day two and hearty thanks to everyone [Music] bye [Music] [Music] [Music] so [Music]