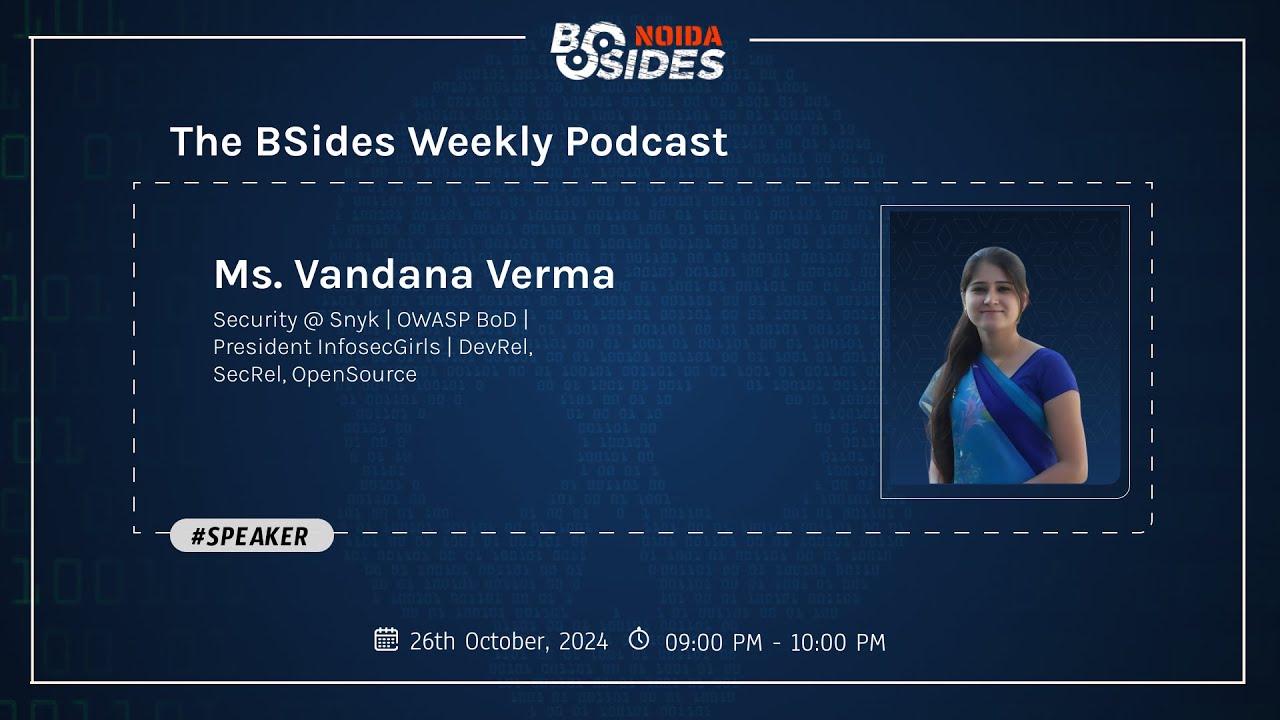
App-solutely Secure with Vandana Verma Sehgal
Show original YouTube description
Show transcript [en]
e
e e
start hi welcome back to the podcast where we delve into cyber security Concepts today we'll be meeting wandana WMA seal into the world of snake hi ma'am how are you I'm good how are you absolutely fine ma'am thank you so much for showing us your presence today so ma'am how are you feeling how do you feel about cyber security how do you deal with it living into the world of cyber security since so many years ma'am when it comes to cyber security it is something which which is very prominent part of my life because I started my career in development but then just within a few years I moved to cyber security and this is something um
which has taught me a lot I've grew I've grown in the space so there's so much to learn every day there's something new which is coming up and uh it's it's one thing wherein uh when we say that change is the constant thing similarly in cyber security changes are happening and we're learning from them whether it's application security whether it's cloud cloud security iot and now we're talking about AI so AI security and and U it's it has taught me a lot and shaped my career and I'm sure my peers in the industry would also agree to the same thing wherein they they share the knowledge they learn from other leaders so uh cyber secur is is is something
where you just keep growing keep learning and you would never get bored out of it absolutely ma'am looks wonderful ma'am so so many years in cyber security can you just give us a little Glimpse like how did you start and interest cyber security and because as far we know that there are less women in this space so interest like if you would like to give that Glimpse to the audience sure so um back then when I started my career it was not a full-fledged thing wherein people say that I want to move to cyber security cyber security was still a very very hidden part of the it and I was asked to be in this project of cyber security and
told that you have to do it uh because the other project was getting over and I didn't want it to be on bench but I think um when we say Serendipity that was something which happened to me and it was the best thing wherein um I got introduced to cyber security learned the basics of it learned what is network security and then um different parts of uh application security Dev secops and even uh I would say that as my career progressed uh I I became more involved in the communities so oasp is one Community which is which is very special to me and uh where I've served as Global board of directors as well so um this uh
space in cyber security actually um made a lot of difference in my career and when you say I started I started as a network security person and I've come a long way wherein I I can say that I'm part of product security so over the years it's the different roles that I've uh taken up in the same space but it's a lot of learning ma'am that's a huge role like I myself I'm inspired at the moment right now big fan uh so ma'am when we talk about application security specifically so people do get puzzled like they like what is application security so can you just give a little glimpse of exactly application security M application security um
simple words application Facebook Google um Gmail Instagram application CHR Firefox web based
applications app is um so anything that where we can actually attach security to it um it becomes application security starting
with for example for WordPress WordPress gives you the platform different different extensions
website what next for organizations or
companies design reviews from security standpoint threat modeling threat so threat modeling is is equally important
interesting developer securitys operations team Vel team or
security
Facebook issues figure out is application security or similarly mobile mobile apps security mobile device security is also part of it so ma'am SE I
think if we talk about
it and we make sure security
aler Ops in simple terms wherein
develops that's amazing so is this related to vulnerability management as well like when we talk about system real life like experience stop the to real life example okay where you were managing something like this and it was a big turmoil situation say and you had to face it if you could just share it with the audience sure um in 2017 actually uh there was a vulnerability uh in aache older version aache 2. something version um that was actually giving attackers remote access to the system so they could play around with it so or or I would say more than remote access but remote code execution so if I am an attacker I'll be able to execute
my code on your server so that I can get as much as information M so um 2017 this was a big issue for a lot of organizations Apache said uh that uh we are we we we have seen that there is a big vulnerability or a critical vulnerability in this particular version and we will be updating it soon they said it inary in March they released a patch F uh oh Ma'am just for the common audience what's a patch patch is something um it's an update in simple
words okay
okay sounds perfect ma'am uh ma'am when we talk about application security like in specific so challenges examp for example and application Securities of how will I manage that as an entrepreneur or as anybody who is being you know correlated to that role to how will they manage it first of all uh J entrepreneurship or any any further application um the most important thing to remember is that we need security at all times because we can't take a chance on that anyone can get into our system and it's like
OTP OTP for example
authentic instead of legitimate
user then you're good to go similarly um
authentication something which you are let's say it can be authenticator can your IR can be biometric auth
parents appc programming
interface entry validation is something which is very important or application security
top 10 risk or vulnerabilities most follow that's even application
securitys top
amazing for understanding vulnerabilities
but okay when I was asked in my second organization saying that you have to enter into application security to uh the first thing application security that was web security testing guide so that
Bas but
abely so ma'am when I talk about gen z a genz it's all fun and thrill for them so they try to delve into these Concepts more than ever so message if they're interested to know more about this field or if you know they're looking forward to build a career in this so is there any message you would like to give them and to even refrain since they are more of like I said fun and thrill so is there any message you would like to give them I would just say that you have more energy uh more curiosity than probably the old days so it's better that you invest that energy in the right space and
want to get into U get into ethical hacking what we say it there are so many platforms where you can enroll yourself whether it's Buck crowd whether it's hacker one whether it's any uh whether it's um there are so many other places but hacker one Buck Crown is something which is very big you should enroll yourself and what what you will get to see is that there are many organizations who enroll the themselves there and let the attack let the hacker find vulnerabilities they actually P them so you'll be getting paid to do it and uh uh curiosity is something which is which is very very important in cyber security and you jenzy have it so I'm
sure you can you can find the the easiest way to figure out the vulnerabilities in apps so you totally have it it's just that you need to understand the basics of it and um that's the best play place to start from okay so ma'am uh when we talk about application development so what is the future of it in the coming times I think it has a very bright future because when we say application security it's not just um talking about the simple applications but the new technologies that are coming up now we're talking about AI we're talking about Cloud applications applications will be there every day there are thousands of applications which which are getting online or there are business
which are getting online through the website so absolutely it'll be here to stay um I wouldn't say that it's going to go away anytime sooner but but even though you'll say that oh I will have mobile applications you'll have applications you'll need the security for that and for that people would would have a job for sure there are tons of jobs which are still vacant where um there right people are needed so this job is going to stay this space is going to stay and only thing is that there'll be enhancements there'll be new languages there'll be new techniques tools that'll come up um but the basics would remain the same uh ma'am since you just addressed the job
part so I would like to ask you and in fact an advice myself I want as a youngster that if we people are looking out for opport opportunities in the job sector in this so what is that one thing we should be focusing on in terms of finding the job in the application sector or maybe in overall cyber security because this thing is very trending these days like everybody's like cyber security there are no jobs we're not getting it we have studied ample we've done internships ample but we're not getting out of it so as a q as neutral point of view or maybe somewhere we are heading towards wrong I think I would say uh
or you are heading somewhere wrong for sure but um connection is something which is very important networking is something which is very important so connect with the right people if you let's say love about application security or Cloud security or iot security people on LinkedIn send a warm connection request what I mean by warm connection is send a note that why do you want to be connected with that person and I'm sure they'll accept your request and um then you can actually share your views your blogs your discussions with them and there are people who who actually want to see uh people who have some kind of knowledge to share so I would love to get
similarly there are many people um I think I shamelessly send requests to the people who might want to get connected because it's very important and I cannot just learn everything by myself that's why we have this we have this conference coming up whether it's bsides whether it's oasp whether it's blackhead Defcon or any other conference like all of this is connecting people and very important we learn from there and and let me tell you most of the time uh when I go to a conference I might not attend all the sessions because for me it's not possible anyone trust me it's um is u i make a lot of connections I meet a lot of people whether it's
networking area whether it's U during the lunch hours whether I especially set up some things early on by putting on LinkedIn like I'll be at blackhead this year or I'll be at bides besides Nora and um um I would be glad to meet you up let's let's just catch up if you are around for a coffee so it's about networking where you warm connect or even uh when you are attending a session just asking for speakers LinkedIn profile so that you can connect uh with that person after all and say that oh I got uh I was in your talk and I want to get connected and learn more about such and such topic so I think
that's thing that needs to be done uh which I think you all have it already because I used to be an introvert and now I'm becoming an extrovert and you you just you don't need someone to push you to speak you're already there that's good absolutely ma'am that's so wonderful to know from your end I mean seniors when they come and tell us this motivational thing so we actually get up rooted from that okay there's a hope for us but what is exactly happening right now in fact when we people go and apply for certain things we have been told that you know the kind of payment which you will be getting the kind of payrolls
which you'll be getting will be very less right now so why is that happening apparently I mean uh because cyber security is a very expensive field very difficult to in comprehend it's not an easy system to get into the computers and get to know each and every single data what's happening to R maybe beginning it could be the it could be one reason or but get your hands dirty get as much as exposure during the internship um there are so many apps which are there which are vulnerable um like the they are just built for the testing purpose test them there are so many opportunities where you can be part of some webcast or some
podcast uh or some books which are written read them because if you have the knowledge you can ask for the right compensation as well but if the company has like okay for beginners we are only going to give this then I wouldn't comment on that to be very honest the company standard there are some companies who are giving really handsome pay to the beginners also so it depends from organization to organization and B based on your experience as well or your learning so is there any specific like is it just application security so example of course there are certain fields which under there are divisions right so application security is there bug Bounty is there penetration testing is there so
Fields specific which you would like to advise to the people who are looking right now on this podcast field so maybe that's where you can get some sort of rooting in cyber security this is some high because at the end of the day people do come to me and they like Money Matters we have studied we have done internships but we're not getting something out of it so of course money matters but is there any field specific recommend in cyber only apart from application I think um everything in cyber security pays well but it's just that your passion matters I feel so just giving you um a link for breaking into infos so you need to select yourself that which
part of cyber security or information security you want to move into and I don't any specific uh um sector pays you well or pays you less it's it's I think everything is amazing in cyber security so um I think at least I don't know if any that oh this pay this job pays less or this job pays even if you are non- technical person and your project management or you're part of U um the report writing part also you pay you get paid really handsome so in fact that was very intriguing to me such a good field to work in when I talk about tech application security bount because is like basically marketing social media handling or as of
now I myself I'm into content in cyber security so what is that one thing which part would you like you know like to recommend the people I think um project management or even technical writing is something which is getting big these days because every organization needs a technical writer for the blogs so it's totally amazing to have more and more blog writers who understands the cyber security even if they don't do it but they actually um spend some time on it so that can be really good if you start putting efforts in that area it's just I believe that's amazing ma'am term use o in the middle of the conversation what is that exactly because if somebody is
looking into cyber security and they have no clue so how would you define oasp for any person who does not know any information regarding that um oasp is open worldwide web app worldwide web application security project so it's a project it's it's a foundation where there are a lot of projects a lot of chapters around the world um and these projects are related to application security depops cloud iot and there are standard also which it has built and it's not just the foundation who has done it it's the volunteers the leaders who have done it um it could be you it could be and and I let me tell you there are so many students who have
created projects in oasp so uh I think it's it's a simple plain nice Community where people connect with each other and learn from different projects and even organizations pick up those projects to train their employees that's amazing ma'am uh ma'am we do I think have some certain questions uh being asked on the YouTube can we take that over yeah yeah please sure let's proceed with that just take a look at
it uh also ma'am until that time just one last question I wanted to pop in uh in fact one of the most important cyber crimes uh I am actually a cyber journalist at this point I'm writing about cyber security the crimes is on an outage I think I would say that um when I talk about application security specifically so application security cyber crimes expl if you have to explain someone you know how you can refrain yourself or your organization from being you know protected from any sort of damage being done to your system advice for anybody see um when it comes to application security specifically then I would say take a look at OAS top
10 and in general if we talk about cyber crimes then absolutely you should definitely um first of all be very Vigilant there are so many fake calls Fake Messages fake WhatsApp messages which keep coming up do not click on the links do not give one time passwords to anyone whom you don't know or whom you do not trust and if something happens there is a national cyber crime reporting portal um you should definitely refer that there is a number there you can report you can actually report a call there and they do definitely work because my friend was part of one cyber crime where somebody actually um uh forged around 20 G um and he actually got it back so by
reporting it actually makes a different even though you might not get money so soon but then efforts they track down the person so cyber crime. go.in is something which you should definitely keep in mind because it'll help you and not just for cyber crimes but for maybe um cyber stalking or if somebody's teasing you online it's very important to report it and people do help these teams which are part of the police they really help you uh ma'am you since you just addressed uh and for the audience who's listening to this the number is 1 1930 and we'll just mention in the bio also about this uh uh crime reporting portal I think you guys should be totally uh
going there and Reporting it rather than being numb it's very important for the criminals to come out there and it just helps the police to catch the culprits easily so please to get your crimes reported it's very important to do that as a citizen and uh first thing is to definitely not panic and that's something I always tell people um and ma'am we do have the questions uh which people have asked let's just dive into that if we're okay with this okay uh ma'am so the first question we have is um it's Raman he's asking how can I enter the Cyber sec security field without any certifications you can definitely enter into it there are so many platforms
there are so many tools which are available uh let me give you this link uh for breaking into infoset you can just go through the different resources shared by the different smmes uh there are let's say if you want to um learn more about how you can break into application then hack in the box is has some really good boxes where you can uh try or uh get your hands dirty and try those skills the vulnerable applications like security uh Shepherd or Juice Shop from oasp is a great place to start then um you can also um go ahead and try or register yourself on Buck crowd and hacker one so that you get to have
access to the apps which needs the pen test or security test testing so I think when it comes to security certifications my view is that it's just a gatekeeper if you have the right knowledge maybe the first interview it might get you but after that your knowledge might twist so get your hands dirty put it in your resume and make sure you do not dab too much about it whatever you know post that in your resume because sometimes recruiter is like I want to know everything what you've written in your it's very important absolutely ma'am uh ma'am the next question is from aeka she's asking I'm currently pursuing an mtech in cyber security do I still need additional
certifications or is the mtech degree sufficient you do not need uh even mtech to be very honest it's good to have uh in cyber security I've seen people who are journalist I've seen people who are ma'am count me in please who are psycholog who are uh police I've seen lawyers in cyber security so you do not need but what you want to do you need to do the basic research around that whether it's application security or not whether it's network security whether it's threat hunting uh threat modeling whether it's iot security whether it's I security mlop security anything you need to do research and if you have done your thorough research in that you connect
get connected with the right people I think that's all that's all you need that's all I I feel so uh ma'am next question we have from khati tanuja uh she's asking as I'm new to the field how can I deal with deal with an imposter syndrome oh you're new but I deal deal with that every day whether I know it for trust me um any any ma'am any example you would like to give on this to her oh yeah absolutely um so after five years being into network security I was asked to be part of uh application security and I told my boss that I've never done it and I don't know how will that happen no
I don't know your application security so what should I do uh the person said I'll give you 3 months to check out I'll give you a mentor so looking for Mentor is something which is very important but then Ming does not mean they'll spoon feed you they'll just tell you you can refer to this this then this and then you have to further read things then you have to come up with questions and ask the relevant questions we have so much of of information available on the internet so getting a mentor actually helps you getting through this imposter syndrome but let me tell you whether it's you're a beginner or you have 20 years of
experience at some point you get that imposter syndrome and another story is that when the new vulnerability comes and you start prepping about it researching about it and like oh how is this happening now when AI came into picture everybody was looking through it and like will I be able to do it what will happen to it how will I be able to deal with it but then there are so many models started to come and started to research and understand about it so I think it's it's it's okay to have in poster syndrome but making sure that you have that back in the mind that you can do it there are people to support you
have right mentors not just one but multiple mentors learn from them do not do not want to or I would say do not say that you just want to be like them you're you you have different personality you have different learning capabilities maybe you are better than anyone else but then learn from them and and and execute what you want to do for anyone in the audience who does not know what's an imposter syndrome it's basically where you're trying to judge yourself uh at times or you know trying to be more competent than the others as usual you just trying to feel as
IFR I think M ised to completely break it down really well thank you so much ma'am for answering this um okay let's do start into the next question okay so there is uh samika she's asking um what's your view on the importance of mentorship in cyber security especially for women wow I think we have so many platforms which are available for mentorship for women but to be very candid about it I I have a lot of mentors who are men also it's still respect the bond that you create and uh the right kind of questions you ask them it it does not matter whether it's a women or a men but if you're really comfortable just for the women then
there are so many forums like infosite girls you have women in cyber security um in US you have visp which is women in security and privacy there are many forums who are there who want to help more diverse candidates who are there to Mo motivate you and Mentor you so you can join them and uh it's just about learning from them and uplifting others absolutely ma'am wonderful uh then we have next question it's uh for those interested in leadership roles in cyber security what steps do you recommend they take early on I think we discussed this but just since it's a question let's just go ahead with it can you can you say it again please
uh for those interested in leadership roles in cyber security what steps do you recommend they take early on first of all when you talk about cyber security uh you need to understand the bigger picture uh whether it's risk management whether it's GRC whether it's application security you should understand the basics because a leader is someone who is actually helping out the other people in the team not not just verbally but but technically also and a lot of times motivational so have empathy learn the basics get your Basics right from the beginning so that if let's say when you are a leader of of some role or you have some role you know what you're doing and you are able to
help them out I think that's all you need and empathy that if something happens you're there for them that's these are the two things you need and there's no rocket science I've seen people who are in the industry in in just 5 years they have become cesos there are people who've become cesos after 15 years because it's a big company and they both are equally excellent in their own roles so there's no Silver Bullet to it to be very can to be very honest so there's no Silver Bullet to that uh for the people who are in the audience uh cisu is a chief information security officer uh and you salute them many multiple times whenever you meet
them so yeah the next question is how to find a mentor I think we've we've been past this supportive encouraging okay so next question is um why are communities important Bravo even ma'am I want to ask this why are communi is important communities are important because uh because they connect you with other people they connect you with um different Ro roles and or or let me take my example here when I was working in my first organization I didn't know much about communities when I moved to Bangalore somebody one day uh just met me and told me out of the blue in one of the trainings that we run o Bangalore uh why don't you come and join us or uh
come for the meetups that's when I realiz that the there is a community that was my first introduction and back then in 2012 and um over the years I realized that I've overcome my fear of speaking I've made new connects I have U made friends in the industry I've learned from other people and their Journey so communities actually grow you personally and professionally both and that's my take on them okay that's amazing we have some person wide Battalion uh he's asking I have BCA Advanced diploma in cyber defense and CH wow and I'm interested in cyber forensic so which companies more support uh to cyber forensic in India oh I wouldn't be able to name the
companies but I think all the top um top fours uh Consulting companies do it even IBM I've seen doing Accenture doing it so most of the companies do it it's just that you need to look out for them in LinkedIn or maybe no.com I wouldn't be able to give you a glimpse of the company names particularly but most of the big companies have it and top four is what we call it as the lawy PWC all of them have it for sure they have the forensic
teams ma'am then we do have the next question it comes from AA and it's a very interesting question how can I for a new chapter of infos girls oh you need to reach out to me you have my LinkedIn please free to drop a note note to me I'll be more than happy to discuss and talk more about it not to me okay ma'am uh next question is uh how do you prioritize which vulnerabilities to address first when multiple issues are detected in an application that's a very good question so it depends based on the apps because there is a vulnerability which could be a critical one for my application but could be a very low severity based on
the client facing you have if it's an internal system it might be a lower medium level vulnerability but if it's a client based system or um a system which is there on the um in the production maybe it could be a critical vulnerability because users have access to it so it depends from systems to systems then I look at the CVSs score look at the severity what has been given by the CVSs and then I actually check out if it applies to my server or not so there are multiple parameters which are there and based on that like we have created a CVSs calculator based on that we define whether it's high severity or medium severity and whether my
application is client facing or not whether it's on the internet or whether it's in internal app or external app or whether it's a crown jeel or not so there are multiple parameters on that when you start working you get to know what applications you're dealing with what kind of apps those are whether it's from financial sector or it's um healthcare app and how much you need to concentrate on that then you can define that oh this this could be a critical vulnerability for the users or for the patients then you say oh I need to fix it early on and then are some apps where you can take some exception and say that we can work
we can wait for 15 days and then we can work on it let's say if the application has to go live right then and there and you have a critical vulnerability and you say that we can buy and have an exception for 15 days or 10 days then I think uh that's where you can U wait but depends on okay um ma'am when we talk about uh cyber security specifically and whenever I see my in you know even around me in my circle why is it that uh women do not belong to this field so much why are there such less women in this field specifically in cyber security domain so if someone says that women do not belong
here let me tell you women have a brain where we do multi-threading and um uh we can multi threading multi-threading in our brains we can connect dots easily if we want to find out something that we would be the best people to work for CBI I would say that because we can connect the dots so easily so we have we are built to do it we born to do it and nobody can say that you you cannot do it I think I I feel that um I belong here I've been in the space because I felt like this is for me I can figure out things maybe more easier than other people so if someone says you can't do it I'll
do it twice for myself not for them H nice ma'am ma'am we have one more question uh it's about to end so we'll just wrap it up with this so the question is what's your view on the recent uh star Health preach oh okay okay star Health preach I think I don't want to comment on that my might sound controversial just a little uh okay so uh let's just take the question in a way where we can speak a little on the topic what exactly happened I mean opin see first of all uh when you talk about these Insurance breaches or Health Care breaches um it depends um that how exactly it started on the internet it
says that um the the star health and aligned uh Insurance actually received um a ransom demand of $68,000 that's what received and it was asked uh to them that oh we are going to be leaking your customer data and you do not give us that money we will just put it on on the internet so this data might uh they might have got it from maybe from a um from a server or somebody might have lead so it's still M uh just I'm so sorry to just cut it right there just before we proceed to this uh segment uh can we just give a little Glimpse to the audience what exactly is this because staral data preach I don't
know if people would be a little aware regarding it so that's why I said that U most of the people think that oh we are talking about a breach but if I say that it's it's an in very simple terms there was an insurance company um which uh for which the data got breached now what data it uh it was about the health insurance of different people their names their email addresses their phone numbers their insurance numbers all that data um the the data leak was surfaced on Telegram and uh uh then the star um and then the Star Alliance team or Star Health sorry star health Team then they said that they became victim of Cyber
attack and their operations remain un affected like they'll just be running running it and uh um attacker when the person got the data send them an information saying that now I have your data um if you do not give me this money I will make it public and that's what happened like this is what I understood but then there are multiple stories to it and what has happened was I think there still investigating and that's I don't want to comment on that because every company has their own story and they they they try and make sure that they come back strong from that so I'm sure they would they every company wants to do their best to secure their data
and especially with Healthcare uh sector they really really do strive hard um but these kind of mishappenings happened and um there are people specifically targeting such organizations so I wouldn't just comment on saying that their security was low this and that happened U they trying
right now we're in besides podcast somebody bumps into our system God forbid not so but we are taking every security and preventive measure to protect our system so what is that which goes wrong like system example I'll take the biggest example apparently a be sing sh right they got a big bumper and uh it was basically logged in from the US elections like he would have got the earnings but his whole system got flawed and of course luckily he got the data back because YouTube of course has a back end in the system but why is it that they had all security measures every single thing in their system to protect themselves yet they got hacked
what is your take on that oh it's very simple when you are on internet you are never 100% secure because there must be someone who will be looking out to find one floor and to report it to the team uh reported to the vendor or the web web application team or to just make the most out of it so it depends so when you are putting your data your pictures your content out there remember you are there out and you can never be saying that oh I've done everything and I'll be 100% no even I can't say it there are people who looking out for the data and maybe my password dump is lying somewhere
somebody might have uh got my LinkedIn passwords or Facebook password from some leak and it might be lying somewhere so I wouldn't say that so this is something inevitable this these things will happen because you're on internet uh it's just that how you come back strong from that is the most important part so I wouldn't say that you are always secure there are new technologies new updates which are coming up sometimes even a secure system after an update become insecure so how would you say that so ma'am what's the point of having a protective system in that case when we are anywh in a probably you know in that sort of place then don't do syst disconnect from internet so
basically uh the point is in short when when you're on the net you are anyway going to get affected in any case system protect that's the Crux yeah see this is there's so much that you can do you have the best of security team you have the best of everything but if a new technology comes new attack comes what would you do you'll just update your system you'll just work on the um on on working on updating that system or patching that system that's the only thing you can do but if a hack happens um then you have to recover from that right and sometimes that you forget to turn off certain port or you uh or your
user um from their own ID is able to play around into your system so it's just that sometimes the basics basic things uh make up to a breach so you can't just guess it whether it's your data or how you going to be handling it so I wouldn't say that uh when I'm on internet my pictures are 100% secure uh it has happened to me during pandemic where uh I updated my pictures on the internet back in 20156 uh when I was very happy that I'm traveling this and that and it hit me that no I shouldn't be putting too much of pictures I removed it but during pandemic my one of my friend shared a
picture of mine which I deleted long back and I realized that when you are on internet you share anything that'll be there in the archives forever so what absolutely so whatever you post think before posting and when an organization is putting it website on the internet which means they want to do business and they they understand everything now especially now that they are very they're becoming very cyber aware they're doing their best themselves but still there are um tips and tricks which keep happening so you don't have a control over that just like so something very sensitive case happened recently and the girl SES was all on social media and it was Supreme Court's verdict to take it off the
internet yet it was not taken off so will it never go out of the social media handles or is there any other way to get R out of it h can you repeat your question again so example uh the rgk uh case victim she was uh having her pictures lathered all over the social media which was of course Very insensitive to do but uh the Supreme Court's verdict was to take it off on social media handles so why is it that the social media handles have still not taken out of course if they have still not taken out is there any other way from the social media handles wherever the picture is probably available um yeah if it's Twitter or
Instagram Instagram uh has all the right to disable that account and if it's from the legal it depends from countries to countries law they can do it like if you are um code to give you personal chats they might not give because they're encrypted but when it comes to taking down pictures I think code can give verdict and Instagram may choose to adhere to it as well or they might have to do it so they can bring down any uh uh let's say I've seen there are many channels or there are many uh handles which have got disabled because they were not complying to the policy so I I think they can do it they have all the authority to do it
we can only report it and then they have to take action we can't do anything about it it's the team it's the app owner or the the team who are managing it they can do it absolutely ma'am I just asked this question because if it happens to any of the victims in the future T tou would not so possibility like system that's why I just ask a basic question okay so I think ma'am that's it for today it was great having you on our Show podcast uh was really fun and uh thank you so much for giving us so much of awareness about the uh Concepts tricks tools and don'ts what to do what not to do and uh I personally had uh one
of the best podcast uh until today and to the audience thank you so much for staying tuned in and uh let and of course stay tuned in for other podcast episodes as well so we'll give a wrap to the episode number three today and thank you so much ma'am anything you would like to tell the audience as a wrap up um thank you so much everyone I'm sure you all have lot of stories to share I would love to get connected with you on LinkedIn or Twitter uh and uh if you would like to share your stories or if you like something please do connect with me I'll be more than happy to chat with you thank you
please follow M on LinkedIn or whenever you want to get in touch with her she'll be more than happy answering your questions and thank you ma'am and until the next time stay updated guys stay safe be cyber safe thank you so much ma'am thank you guys thank you
[Music]
know for





