BSides Noida : Day - 2
Show original YouTube description
Show transcript [en]
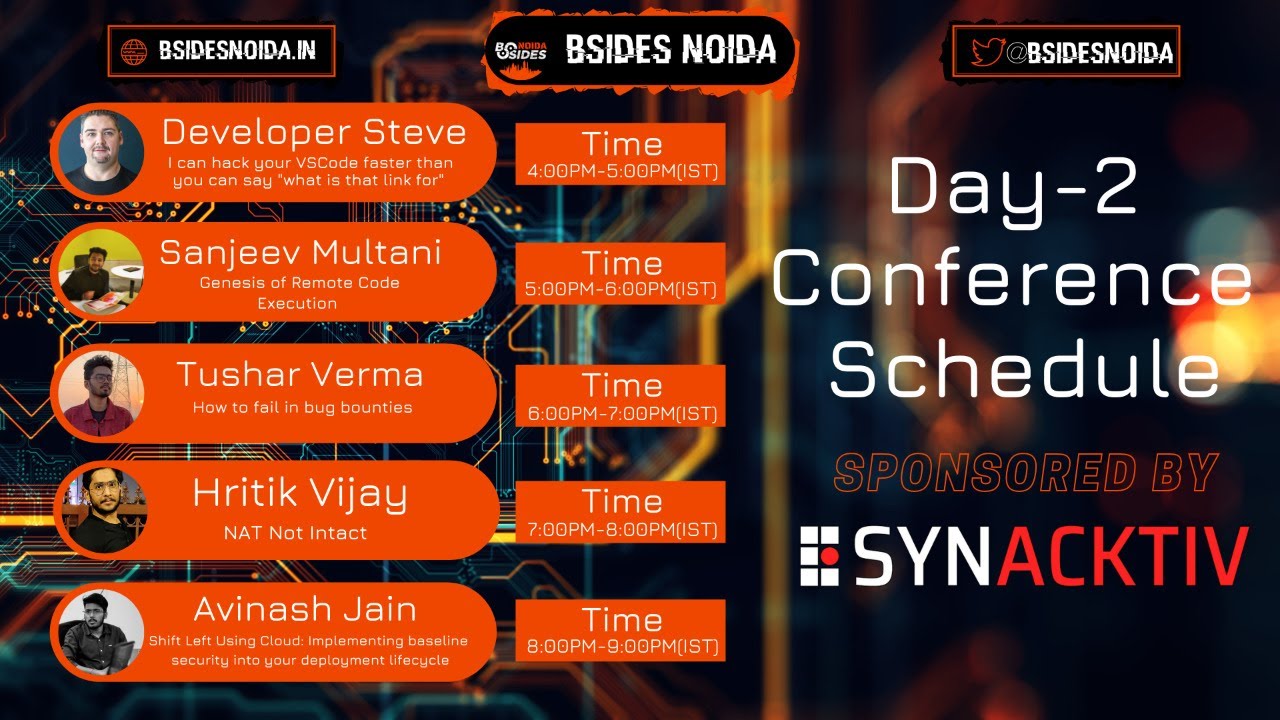
is free and the world has not been broken up into narrow domestic walls into that heaven of freedom my father let my country awake a very warm welcome to the day two of besides noida 2021 virtual edition conference sponsored by synaptiv i am vanna and on behalf of my whole team i greet your gracious presence here as learners and wish you all a very happy independence day into narrow domestic as we all know already beside security conference a community driven framework for building a minimum welcome and by information security community members the goal is to expand the spectrum of conversation beyond just the traditional confines of space and time so here are some insights to each of the
session firstly our guests will be giving their presentation and exploring the horizons of a topic they have chosen secondly in the end if time permits we will give we will take up questions from the live chat and guess we'll try to resolve the queries and finally after the session ends a link will be pasted in the chat box which leads you to a google form it contains questions related to each of the sessions which i assume you will be listening to very carefully answer them and the top three people in each slot will be awarded some besides noida goodies so without further ado i take privilege to introduce our first guest for today developer steve he's a senior dev
advocate at sin sync sec and also an advisor to the bereimol iii the topic he has chosen is i can hack your vs code faster than you can say what is that link for we welcome you sir you may start your presentation amazing thank you and what a great intro um indeed like as a developer from many many years now one of the things i love with communities like this is the open sharing everyone learning everyone on different levels but sharing what they know between each other so it's so amazing to be here and happy independence day to everyone as well i might uh might add um but yeah thank you very much for joining the
session thank you very much for tuning in and i'm looking forward to geeking out with you all but i do have a disclaimer before i start so i do it right at the start it even has an asterisk on it but um my disclaimer is i love tech jokes so i have a whole lot of them and i i always love sharing these because well especially in times like this it's important we keep smiling we keep laughing and again like we keep learning with each other so anyway this joke is open source so please feel free to share it around but why did the vulnerability get because it ran somewhere um please put all comments uh emojis
face palms are accepted as well into the chat boxes depending where you're watching and we'll get to questions at the end or have a look at a whole bunch of emojis and face pubs anyway hello uh my name is developer steve funny story that is actually part of my legal name so developer steve is actually my middle name one word too um so i got married a few years ago and me and my wife decided to combine our last names and create a whole new last name so cooper plus houchin became kuchin so kuchin is my married name and when i got my name legally changed i thought you know what everyone i've been an evangelist or an advocate for so many
years now for companies like paypal braintree for xero for telstra for ibm that i thought everyone just calls me developer steve whenever i'm at an event or just geeking out with folks which is well that's pretty much most the time just like today so i thought you know what i'm going to make developer steve my middle name or i'm going to see if i can make it my middle name it turns out you can so there you go which is still weird because it's on my driver's license so it was slightly unintentional but here we are um anyway hello so if i haven't met you before um i'm developer steve everywhere if uh i'm always happy for people to reach out to
me i'm on linkedin twitter facebook yeah you name it kind of all over the place um mastodon very well using that um polywork yeah everywhere anyway happy to connect with folks so um please feel free reach out um always up for geeking out always up for sharing new things learning new things because i mean that's what the industry is kind of all about so i've been like a coder for many many years now a developer back in the days of anyone that remembers it and again pop it in the chat if you do remember these days but back in the days of q basic that's where i first learnt coding which was an interesting time because we
didn't have the open source communities and the amazing community conferences like we've got this weekend there wasn't a lot of that uh sort of matured industry that we know today where we've got open source libraries dependencies communities you know groups of people building up platforms in whole new ways and going through my developer origin story as i like to think about it over the years like working on startups tinkering on little side projects it was always leveraging community projects or libraries or dependencies in so many different ways and in indeed even in my digital agency days building up campaign sites i always used to like to think of digital agencies as like organized chaos i loved it because i mean that's where
you well it's a lot of pressure yeah but that's where you really thrive because you build out a project in next to no time next to no budget and then the client wants some changes afterwards anyway that's a whole other talk um but the point is like over the years we i've been privileged enough to see the industry mature and in particular build out some amazing frameworks some amazing libraries and dependencies that really help developers in their day-to-day life so if you take the code on this screen for example instead of writing an entire you know many pages of code or loads and loads of code just to handle that one function i just npm install a thing and now i can
have very few lines of code and i can build out this amazing application from a developer's point of view like one thing i always love to remind developers or even remind myself is when i build these applications out i'm building them out with that end user in mind like i'm building out an amazing button that orders them food that connects them to somebody that connects them to the world that brings them entertainment like i'm building that piece of functionality using that open source framework using that open source library dependency to change their life to change their day in some tiny little way something i've always been really super mindful of over my developer origin story
is just what else that that functionality that i'm deploying what else that brings in with it like a bit like that meme i love that babe because quite often and even sort of thinking back through dev origin story when i have deployed a particular thing for a client like quite often i'd have to go back and clean it up because i deployed something without understanding fundamentally what was what was hiding within it what vulnerabilities were being surfaced and if you think about an iceberg the very top of the surface is your application code is your your code exposed to the public world and of course as we know as security professionals as developers as industry
people really or industry community we're one big family um the number of packages open source packages exponentially grows each year which kind of makes sense because quite often you'll see that one library sometimes will split off into a dependency some of its functionality is split into a dependency which will then get used across the entire ecosystem sometimes because that one piece of functionality that splits off as a dependency library then gets utilized across a multiple of different community types because well they might like the functionality or it just saves them time in their library so we see this exponential growth across the holistic ecosystem year on year and of course no surprise and as the
security folks will know like we see this rig bring with it vulnerabilities being surfaced year on year and of course if you think back to that holistic iceberg stack like the one on the left your application code or that app that's being deployed or that app that you're supporting is literally just the tip of the iceberg with the holistic stack that that application needs to go to fruition so your application code is built on the next layer down which is open source code and we'll get to the last two sections in a moment i just wanted to mention talk a little bit about the open source supply chain and in particular the security that is now becoming more
apparent more surfaced into well all over the world now everyone's really like this is a really hot topic at the moment in particular with governments around the world looking at how they can secure open source supply chains for business which is a really important topic because again and again we're seeing this compromised supply chain where one particular component can literally bring down an entire industry an entire delivery method and you think this now also affects everything from utilities food production like so many industries in so many different ways and again this goes back to that exponential growth across the holistic uh ecosystem we've seen so many examples of uh this too where like with electrode native
notify where and you can see the timeline on the screen here where a dependency was added to initially added to a library maliciously let's say which then got pulled into everyone's updates everyone's upgrades all those new installs and three weeks later when that one was fixed up three weeks later a new dependency was published into that which then had flow flawed effect through the holistic chain and of course we all have different stories about these type of scenarios if you do have one pop it into chat we'll have a look after this one thing we tend to find is um across mostly ecosystems so uh with like maven central ruby gems and npm it's the
indirect libraries and um repositories which are causing issues uh with vulnerabilities being surfaced in applications so we don't see this holistically across the entire language ecosystem so php for example and python we see a lot of direct dependencies or sorry direct libraries which are the issue for vulnerabilities being surfaced across the stack and i just want to point out too a lot of these communities do really really amazing work i've been doing open source community work for so many years now and quite often what we see is there's a time delay sometimes between the the volunteers behind that community or the people just contributing their time or contributing to the project there's a time delay between the initial
vulnerability being reported back to a library or a dependency or a platform and then there's that time delay before the vulnerability can be surfaced more investigated identified and a fix can go into place and then a fix to be tested and then a deployment to go ahead so if you are using a particular open source component or you're using work done from the open source world please always remember to contribute back i know you do but i just like to point that out one of the ways we do that at snake is through
am alive the frame is not set okay
okay hello again everyone you might have noticed i switched scenes i mean murphy's law
i think i'm live hello everyone okay i'm gonna assume that i'm live and i'm gonna switch my scene back there we go cool no one's saying anything i'm gonna assume i'm live i'm going to keep going anyway welcome back um so one of the ways we work pretty close with open source communities at sneak is through a program called sneak advisor which is really cool because we work closely with um some very very very a broad range of open source communities to be able to help them identify threats as they appeal vulnerabilities as they appear but then also on the other side of that if you're looking to use a particular package or a particular platform this is a great way
to do some due diligence and see the number of people maintaining the library how frequently their upgrades come out all their updates come out and how quickly they can turn around fixes all that sort of stuff so it's a great way to do some due diligence on the packages but then the other side of that is we get to work closely with them and contribute back to a lot of those amazing repos again as developers well from developer standpoint yeah it's in my middle name um the this is really cool because i can do some due diligence and then also be able to determine you know what um what sort of support that particular community has behind it um also shout
out to the security people in the room that uh well everyone really but in particular those that um are part of the vulnerability disclosure program for node.js we help run that program uh and keep everyone safe in particular i like keeping those end users safe keeping people stacked safe and keeping well the whole ecosystem safe as well so if you are ask somebody that has contributed to it or are looking to contribute to it thank you and ultimately like as from from security professionals point of view from developers point of view from the devops point of view like this is um all this is critical to keeping um keeping end users safe keeping infrastructure safe and well keeping the
entire holistic ecosystem safe but as we know in a cloud native world perhaps of way more than just code now because you've you're able to deploy applications really super quickly onto infrastructure that scales as your application does so if you take containerization for example docker currently has 242 billion downloads to date which is insanely huge that is a lot of containers being downloaded which kind of makes sense when you think like that exponential growth with uh that we see in open source communities and libraries like a lot of those are growing because so many people are using them to build out those amazing experiences of course as we've just been talking about and this makes up the next part of
our iceberg view is a lot of those containers carry with them or built from the same comp same open source components that we know there are known vulnerabilities in so it's no surprise that a lot of these uh docker images are basically carrying the same vulnerabilities with them in fact the top 10 docker base images on docker hub are carrying security vulnerabilities in them by default straight by year on year we see the same thing again and again the way to mitigate that all the way to stop that from an infrastructure point of view is to start with the most minimal base image and only add the bits in that you need for your particular application
so there's another way i like to think about this yes there's a texture coming with great containerization comes great responsibility there's a few more of these you'll spot them um the last part of our iceberg before we get into the fun bit and i mean we kind of slightly had some video fail already my demos are totally gonna work now right this one in particular anyway we'll get to that a bit um the last part of our iceberg is infrastructure is code which from a development and deployment point of view is really cool because i can deploy things really really quickly really really easily but of course as we all know as the security professionals will know in
particular like the clout number one cloud vulnerability is misconfiguration so just making sure you've got all those different permissions set right those different um things inside those configuration files having making sure that they're all set up in a nice and secure way making sure root permissions all those sort of things inside your configuration files are absolutely critical you might be thinking but wait this is a talk about like development environments why don't we just talk about all that because there's the fifth part of our iceberg and this is where fun stuff gets really fun yes development environments this is where we're going we needed to see the whole view before we got to the fun bits
so this bit as a dev this bit really scares me a lot and we're going to get into why in fact i'm going to show you why hopefully it works now it'll work um so this one actually is kind of surprising and kind of not so we've seen a few examples of this already this year and if you think about it a lot of the development environment tools now are built from this open source these open source components we've just been talking about so homebrew for example yes i like home brew a lot it's one of my favorite things i'm running on os x anyway spoilers um back in april they literally had a security incident
disclosure this is on their blog this is on the homebrew blog um it was a disclosed vulnerability in the brew core framework that actually yes just basically allowed a particular vulnerability to be injected as a dependency into some of the brew repos so already like we're starting to see this now crea these issues also creep into the development environments which i was very shocked at at first but kind of makes sort of makes sense given that they're built using the same things that we see vulnerability surface in so if we take vs code for example and this is where things gonna get really interesting um 14 million monthly active users for vs code which makes sense like it's it's
used everywhere now everyone uses it for so many different things and it's very adaptable it's one of one of the easiest tools to promote one of the easiest to pick up and start using um it has so many different vs code extensions like 25 plus thousand of them currently in in the ecosystem and all those extensions are basically built using the same open source componentry that we've also been talking about so this is based on some research our security teams identified earlier in the year in particular there's four extensions that we've um we've published some research around um so latex workshop uh 8.1 6.1 open in default browser which we're going to be looking at today uh hopefully
uh 2.1.3 now open in default browser which is the gif currently playing and we're gonna have a play with in a minute had half a million downloads today so there's half a million people that potentially hopefully have updated to the latest version which this i believe is patched in what we're going to be looking at i'm using in the demo we're about to do i'm using the previous version which still has this vulnerability in it um instant markdown sorry we're going to be using instant markdown why was i saying open to default browser anyway instant markdown 1.4.6 so we i've got 1.4.5 installed actually i have them all installed but we're going to be looking
at that one particular which had over 120 000 downloads today and basically it enables developers to pass markdown in real time so as you can see on the gift there and i swear this last one's real um i forget what it actually did but there's a vs code extension called rainbow fart yes that's a thing and there's a um there's some vulnerabilities inside the older versions of that one as well anyway i have a full uh write-up which you can all take a look at but i'll give you the link at the end uh there's a diagram but i think given the time we've already delayed let's just go to the demo yeah let's do the
demo thing all right so first thing i'm gonna do oops i just fix that back up first thing i'm going to do so there's two parts to this demo the first part is this is the attacker view so this is this is the malicious view i feel like i should be in my my um black hat hacker scene um this is a malicious view and then now remember i said that this really these really scared me a lot so i thought about running this in my local environment and i thought that's probably not a good idea because what we're about to do is a file traversal hack through vs code on the attack machine i thought i may not want to do
that in my local environment um and there's a really good video of my manager lira and hillary doing this for the first time on a sneak live stream not so long ago where his password file was actually shown on by our security researcher who discovered a lot of these or who was demoing these he pulled his mac password file out and displayed it on the live stream now i don't need to point out that he has since changed his passwords anyway that being said i'm running this inside of vm yes i'm running os x inside os x this is a meta demo yes let me just make sure this is woken up i think it's
a bit stuck probably going to want me to yeah okay it's going to want me to log in again i knew it was going to do that that was intentional slightly anyway so on the attack machine i've got an index.php file i've got a track.php file and that index.html i'm not doing anything with that that was just the template that i got this some of this in set up in so the index.php what it's going to do is leverage the one of the vs code plugins the markdown plugin to basically do a file traversal on the use on the target user's machine and it's going to grab a file and return it out but it's actually going to send
it back to track.php where we'll save it as a as a text file using well it's just going to set a file using the using time from in php so what that looks like here it we're actually going to get a target file so kind of like a capture the flag i thought this is a nicer way to do it so on this machine on our target machine here in my root directory i've got a file called passwords so if i do a and i'll do that we'll do cat passwords and inside that file i've got omg i got rick rolled we'll find out why that's gonna be funny in a moment um so what it's going to do is basically
open up we're going to send the user a link and there's some ways to do that through let's say a social engineering hack for example where we're going to send the target machine the developer machine we're going to send them a link they'll click the link and using ngrok on this machine it's then going to scan for that file using the exploit and post it back so at the bottom of the file i'm doing a fetch on my ngrok url and it's going to send some form data back with that file in it and while that's just a ctf style file you could do this with any file which is how i've basically seen it done
anyway i'm gonna start up my ngrok like so and then i'm gonna start up my php server like yeah that started like so now i'm going to switch to my target machine so as you can see here i have vs code running i'm using a markdown i'm using the markdown extension which is the vulnerable version so it's the previous version to the current live one and it's it just does mark down inside the browser so you can see there that's pulling straight in yeah it always goes blank for a second and then it renders it uh let me change there we go so i can do this is mark down [Music] and it's gonna keep doing yep just like
that and then wait i heard a bling did someone message me uh yes can you please zoom in on the phone uh i can't make it bigger uh yes uh hang on yeah it's kind of running inside the vm window let me see how's that okay cool let me make this one a bit bigger um so yeah just does some basic markdown uh i did have a link saved in here and now it's gone oh there it is so what we're going to do now is this is so this is the attack this is the target machine this is the developer machine so if i was going to basically get a link to the developer to
to the dev to say hey this link's really funny you need to check this link out it's worth looking at when they click that particular link it's then oh look i've been rip rolled oh what's this file it's downloaded now you'll also notice or you may not be able to see it but what it's actually doing is opening up a whole bunch of iframes inside the same window and as it does that it's basically scanning for particular file types so if i was to inspect element here i'd actually see all the network requests of it looking for that passwords file and again this can be done with any file you want basically but what it's actually done
i didn't trigger i'm gonna let me refresh this window this does work so you can see it's downloading this file here which is part of the attack hey there we go and you can see now back in oh you may not be able to see it but back in my vs code exploit on my attacker machine i can see this text file sitting there so and this is the text file which has been sent from that link that i had running ins well on the on the developer machine and if i open that i can see the data from that password file which has just been dragged in it's basically been sent over from the from the target
machine over back to my my attacking machine a and it worked so the code for this um i'll put drop the link into the chat after there's a really good write-up which talks through all the four plugins we're talking about there i just wanted to show oh yeah i'll make this code available because the original one didn't have you've been rick rolled in it which i found fun because well everyone loves a good recruiting conference um the only other one that's going to show is we have these other demos too if anyone's keen to play with them so these are exploit demos these are sitting on the sneak github i'm not going to go through them in full detail
but there's um yeah these just yeah these have a whole bunch of fun exploits that you can play with um again going back to the open source vulnerabilities i'm talking about a lot of these have a lot of them in it including um one of the vulnerabilities discovered in a markdown library which uh ex it basically gets around some uh some sanitization so that for example there we go there it'll do a javascript attack inside browser but there's a whole folder full of exploits that you can play with um you can try for yourself at home um we also have some fun toys in java if anyone's keen to take those for a spin again these come with like all these fun
exploits that you can you can try for yourself i think that was all the demos i've got a bunch of other demos but um let's get back to the slides anyway yay that actually worked so um again i'll drop the link into the chat after this but we do have a full write-up on how how it works and then also how you can try it yourself uh there's a few already been discovered but again like there's this is because a lot of these extensions are built using those open source libraries and dependencies and frameworks like they're carrying the vulnerabilities now into the development environment so just some tape gonna go through some uh takeaways um please be aware of what you're
installing in your your dev environment no more can you do that whole brew install thing or um you know npm install that thing like just know what you're installing do some due diligence take a moment because it's potentially surfacing known vulnerabilities into your development environments and like that's how as from a developer's point of view that's where we do all the magic that's where we build all the amazing apps for folks who want to make sure that very first step is like kept nice and safe and clean and then of course always be scanning source code containers and infrastructure to make sure everything's kept nice and clean and it would again we're protecting those end users at the
end of the day and making sure their data is kept safe making sure their experiences are kept safe um and also from the infrastructure point of view like i've been there where you you get that bill at the end of the month someone comes up and goes hey you know why is it so expensive um make sure you're scanning that infrastructure too because that is as critical as the aforementioned other two i just wanted to do a quick shout out for sneak con that's coming up um it's free to attend it's region friendly it's uh early october um again tickets are free um this is some great talks from um people over the world including
some of the sneak people behind sneak code which has some amazing machine learning stuff in there we're actually spoilers we were supposed to swear just about to launch php scanning inside sneak code any day now i am literally waiting for it to get launched um which is gonna be really interesting because um there's i've seen the numbers for it and there's some interesting stuff in there um anyway totally worth checking that out because it's going to be some great talks also the devsecond leadership awards are open now so um the this is a great way to recognize anyone you know doing some really cool work in the devops space be it uh an individual maybe running training courses a
community um get those nominations in uh this is open right now and just finally please as always use your tech superpowers for good and always remember to be excellent to each other thank you very much thank you mr steve for enlightening us with your words if at all there are any questions let me just see it in the live chat
i'll say yay my demo worked with me thank you
okay so there are no questions as such so thank you mr steve for enlightening us with your words there were moments we bursted out in laughter what the pleasing personality you are and i'm sure the viewers must have added a lot to their knowledge after this session i would request everyone to try and attempt the giveaway questions the link has been pasted in the chat box already the exciting price for this one will be three pair of stickers so stay tuned for more thank you again steve for being here with us giving time
[Music] so [Music] so
bye [Music] foreign
[Music]
them [Music]
this [Music]
[Music]
but
oh
[Music]
the [Music] do [Music]
[Music]
[Music] uh
uh [Music] so [Music]
them [Music]
and one two three [Music] do
[Music]
[Music] is [Music]
them [Music] the one
[Music]
[Music]
yeah welcome back everyone i hope you are out the strength
now it's visible welcome back everyone i hope we all are learning a lot from the experts in the field but this is just the start of the event and we are not done here we have a lot of exciting giveaways ahead in this marathon the second guest for today is mr sanjeev murtani he's a cyber security consultant at eva india the topic he will be exploring today is genesis of remote code execution we welcome you sir you made me start your presentation
i'm so sorry i was nude yeah i'm not able now yes thanks thanks everyone uh thanks for joining in this beautiful summer happy independence day first of all and uh it's great that we are connected on such a occasional day so today uh like first of all thanks to v6 noida for inviting me for like for multiple topics and there were multiple uh like suggestions for the topics which was coming in and i like once again i chose one of my favorite topic uh the remote code exhibition the buffer upload so uh just before starting i just want to like tell everyone that namaste i hope you are all doing good and this uh like pandemic time and
all other thing i i hope you are not in the coved wave and all of the thing and i hope there is no wave three again and session which i will be taking this will uh not be for the beginner level i can say i'll try to make it like as big as i can but again uh like for this for understanding this particular session you need to understand like how exploit works how exploitation works and people should know that how how the things works actually and uh there should be like some terminologies which we should be familiar to people and like i can add up hindi too if some people is having trouble with english start
so like for exploration particularly like i i believe that like everyone should have a proper knowledge and understanding that how expedition works and whatever the type of exploration we are having whether it's manual arbitrary code execution remote code execution or any kind of exploitation or privilege escalation you can say for the further the privilege escalation of memory corruption and basic chart then uh like you will be properly able to understand like uh why and how we are going ahead with this topic so i'm so sorry if you're not able to understand this but yeah you can always dm me on my instagram linkedin and all of this follow the series so i am just starting with so first of all uh
namaste good afternoon holla ciao assalamualaikum subscribe and my name is sanjeev multani who i am i am basically a cyber security consultant and an indian cyber security researcher i've been working with one of the big four that is e and y on st young and uh past pny i was working with luxidius as a lead trainer and as a security analyst also and i'm a 360 degree baptist guy that means i'm a cross platform guy i i do babies and that's wonderfully assessment condition testing and uh like you can say multiple assessments or audits on mobile applications android ios thick lines exe web applications network applications active directories and a lot of stuff but uh the most amazing
thing which i feel like because i'm not more of a bug bounty guy you can say because web web is again web is having a common practice i mean everyone knows what is exercise but the thing which which excites me which which gives me a kick or something like that that's getting out our own cbes and getting our getting out our own experts so uh before starting with remote code execution and i'll come to what is remote code exhibition again but for the bug bounty hunters and for the professional hunters we are having right now i just want i just have one single question uh like one simple question itself so for the bug bounty hunters i i
i know that you must be having a good bounty on sql injection on excesses csrf and iodine and multiple once again so you you can just do html parameter pollution attack but that estimate parameter pollution attack doesn't give you that much of bounty i mean you you get me right so uh i just want to have like one answer from you people that what is the most uh i mean the most bountiful or i can say the most profitable attack which you can get and after getting it out you will get the bounty of of the millennium you can say it's something like the bounty which is the maximum multi which is coming up and i'm not even
giving uh getting right now you can just go to bug crowd you can just check microsoft right now you can check uh any other platform google rpdp multiple rdbps programmer over there and you can just what is the most expensive kind of a bounty which is coming up and what is the most and this this basically leads with multiple uh vulnerabilities multiple vulnerability leads to the same same uh attack which i'm talking about but what is the most top priority like and which which i always check like i do assessments for a lot of organization right now uh i do vapd for more most of government organization majorly they are life insurance companies and uh the banking sectors i'm into bfsi
sector banking finance and insurance uh industry so i do papd for them so so what is the first thing which i which i found because uh in banking and every industry the pi data is is most at the risk behind it is personal information index it's something like your for example you go to paytm i'm not saying paytm is my client but i'm just giving an example so for for example i just say paytm so paytm must be having a radha card your paying card or they must be having your debit card credit card and the cvv itself and the expiry date itself they must be having your account number also because when you transfer the funds to
your account they must be having your account number so these are pi data so to to uh you can just secure this data the first uh like you could say job of mine is that i need to understand that how the infrastructure is secure where these data pi data and these credit details are stored you can say so uh what's the first kind of you can say the most top priority attack which i always try and for bug bounty hunters you can always try and all the things so i i guess you already guessed it right it's my it's one of my topic so that is remote code execution even mithray method is a just
like nvd and nist and asp is a npo based in u.s same like that mithra is one of the npu base in us which maintains a database of ce's the attacks cvs are basically common liberty enumeration ids basically which gives you a id to a particular liberty but let's say there is a movie which which got released so who is maintaining that index of a movie that is imdb just like that there is a vulnerability which came out in microsoft edge for example who is maintaining that vulnerability and nasty they both are maintaining these particular uh vulnerabilities counts so according to misery also this vulnerability is on the top like they are coming at the top and you're going
to see some keywords like memory buffer and all of the things so the most profitable magnification is basically remote code execution and c is basically one of the most like you can say most juicy kind of attack very attractive uh exploit which every other person goes ahead uh this exploit came resistance i guess since microsoft xp times and it doesn't matter because uh rc doesn't work on any operating system it works on a service every attack works on the service when you do when you say that you are doing a html parameter pollution attack you are attacking a service that is http service again or it can be any other service so https service or any other service so when you
talk about that attack works on a service and when i talk about rce rc is basically a kind of attack where you can uh exploit a particular operating system without even touching it so you must have heard about that anyone can hack your iphone like if i say can you hack my iphone yeah you can hack my iphone but uh not with pegasus i'm talking about but you have to do some the intervention in the phone you have to take access of my phone and then you have to install a package or something like that any iep a package just just for example yeah if you say that can can uh android can be hacked yeah
android can be hacked too for android you just need to like you can install any ap malicious apk and then android can be hacked but what kind of rc is what kind of attack is that without even touching a mobile phone without even touching uh any laptop or any server you can just basically okay so you can just basically uh get a access of a device in a remote manner remote management you can just like uh get a shell of a computer screen or a computer operating system it can be any device it doesn't matter it's a laptop or a mobile phone it can be a router too it can be a iot device too my
alexa 2 which is working over here so uh it can be anything like it so when i talk about rc the first question which which is coming to people and i will come to this point again how they are created kernel expert buffer flows these are different topics but when i talk about rc the first thing which i have in my mind is what the hell is rc like i mean yeah we have heard about the genesis word earlier and the terminator genesis the movie but uh let's let's understand what what is the exploit and all of the things can you see my screen right now is my screen visible clearly okay so what i'm doing is i'm just using
a cute kind of operating system i i guess you all know that and that os is called linux so here is my calendar which is working and yeah just give me one sec my mac is heating up like a rocket okay so i just by doing some stuff in my kali linux and uh i'm so sorry like i was to be honest i was not having much time to get multiple os to get attacked so for that uh okay just let me just remove this out it will take time my mac is getting us a bit slow yeah so i have a kind of operating system which is running and magnetable so first of all i need to
understand what what are the operating systems are running on my network and what kind of os i am having so i can use multiple tools like you can use uh and map for getting a complete services details and other things so i know one of the id which is working and the system is just on my left table and this is i'm just checking out and i i'll not be getting into depth of like how can you find the ipad with this that's what i was saying that uh this this session is for a little bit advanced for beginners again so you can just get the ip addresses out i am just just thinking to check that
whether this ip is working or not command.3 if i'm working yeah so this is working perfectly fine so if i just want to check that what what ip is this so for checking this out i can just map and just find out the list of services so you can say our list of uh commands i'm just doing a normal end now just
so that i can just get the services out sir can you please increase the form yeah sure
okay so just said uh just just like what i was saying is that whatever attack you do you don't want a service you find you need to find out the services which are running on any port number and uh this is not meant to get these services are the only services which are running on tcp these services can be on udp also for udp you just have to change a command to and map hyphen scu so that you can just find out the services so i know that okay i am having multiple list of port numbers and i know that there is some particular uh you can say port numbers and some services running up so
when i talk about uh this uh how i can find out a particular attack or a vulnerability is working on this particular machine i can do and map hyphen fn script just like that and if you want to just just don't want to do a ping pose or you can just remove the thing package you can just icmp packets you can just do 5pm and you can just put out one uh which one is basically a combination of multiple bundle uh lua scripts which is in n map and then you can just put iep it will second back again so when you do that and when you hit enter you will get all the vulnerabilities
which is coming out in this particular uh you can say this you can find out all the vulnerabilities over there but the point is that i i don't want to uh i mean like just do that you can also do that i know what is what is attack which is so we can use multiple things again but let's get into a bit of basics because this will help you out when you when you do exploitation so when you talk about you hack a machine and when you when you exploit or whatever you do again like in that case what actually you do so you basically do a socket connection and you need to understand what is the
socket and what's the software connection again i'm just going a little bit of a basics so when you talk about the socket the socket is basically iep and a port number and when you have a combination of this ip and port number this is the socket now every device is having an iep and a code ipad address is up like you can say is the address logical address where the machine is running on on the internet and there is a data entity which is running a server so what we have to do is we need to connect two iep and port number and we need to make a socket connection between both so what we have to do is we
need to basically get a connection between these two before doing this either we can use python script python scripting is the most uh like you can say feasible one in this connection uh socket scripting telling you this thing because when we do the genesis partner the the manual exploitation manual rc you will get to know that what what what are we doing over here so when you have this iep call and port number uh this is basically a socket now for this socket over here uh we we need to connect either we can do a path python manual scripting and we need to understand how to make our own exploit so that can be done that's
manual uh attacking again i'll come back to it uh in another 15-20 minutes but just to understand uh how uh rc works so i'm just using like let me just initialize the database so i'm using a tool over here it's a very common tool which we all know and this tool is msf console and this this is created by uh rapid seven and the one of the initial creator of msf is uh hd murray and that is the guy of which we'll be using the exploit so we'll be using the exploit which is created by hd modern and he was one of the initial developers of metaphor framework again taking a bit of a time
nobody's in case we need to extend the session i'll see what i can do okay coming back to the topic so what we are going to do is with msf console basically we are going to use a particular uh automated socket uh connection script you can say so whenever we say socket connection script that is basically known as an exploit so exploit is basically exported by which we attack into a machine and then we do some stuff come on but it's lagging
machine is getting heated up
sure
uh
i think it's time to change the machine now
so for rc cheat sheet if you want to so there are two things again one thing if you want to understand and learn how how to perform the rc part uh there are again two parts to it one is automated automated you can do from exploit db you can get exploits from source like you can you can use search for at any time and you can find out the rc's which are present over here search point is a already automatic tool which is present in your uh kali linux and you can just find like let's say any any application you have like i say microsoft for example so for microsoft uh this will give me a list of exploits
which are present on export db and packet stock so there are two particular domains where you can find a list of experts again just like you can see over here i just top it on because microsoft is a very cute kind of opening system you know so we have a lot of experts for this so again and for learning purposes uh so for learning i'll say that if you do a metasploit and you do a attack and just like what i'm doing right now this is just a new thing again this is you can just learn these things by a youtube video and you can just do that if you really want to understand how rc works
and uh getting uh you can say our source resources for rce you need to understand how buffer overflow works first because buffer overflow is a creation of rce when you talk about remote code execution remote code execution is automated just like what i'm doing this is the automatic process and i'll do that in just i can say five minutes but when you talk about remote code uh the buffer of your remote code execution which is the manual one it literally took me three years to understand how these things work you need to understand python you need to understand assembly language you must have a good hand in assembly language and python both of these and
then you have to understand the uh kernel and the registers and all of the things so it depends on you again like what kind of person you want to become i chose the hard way out like for learning buffer overflows and all other things that's why some people call me mr buffalo flow but again yeah you can say that you can just run out these things and if you want to uh like you can you can say run off buffer flow i'll give you a kind of uh link which can be very typical but you need to understand python and assembly first so i'll give you a link which you can refer and then you can
so we have a message running right now and this is metasploit for framework version six and uh this is just a banner don't don't get uh like rejected what actually is happening so over here i just need to understand what kind of expert is running out so if you remember that we were having a particular os running and with these services again and if you talk to me like what are these services these are a particular and you can see these are the port number which are running on tcp and these are some services which are the name like microsoft service microsoft running service 445 is basically smb 139 is also assembly there are two reports
which are used for smb and that's what we are going to export right now uh assembly is basically uh they give us a samba service which is for file sharing in microsoft so which microsoft used for file sharing part so i'll come to that part later but uh let's understand what a rce is so that you can get an idea so i have a microsoft xp with me on the left side of the table i'm not touching that particular machine i'm not even doing anything anything i just have this particular machine with me this is which is mac os and i have a kali lens in it so what i do is i just search a particular exploit
you can find out this exploit by that vulnerable command just which i just showed you this command okay hyphen fn script uln you can also like find out this particular expert with that but yeah this particular eventually and you can just find out the vulnerabilities which are present on a particular ip address but uh what i'm doing right now is i'm not spending much time on that because i have to get understand the menu so i'm just using the attack right away so that i can just searching ms 03
uh it's seized
yes sir your voices let me let me stop this my bad so this is not internet this is my mac i guess because my internet is working
we need to do something
so someone asks you that should you buy a microphone system when you were a hacker the answer is no then you will say sir why do you why you are having it at least we haven't the only answer why i am having it is business meetings
yeah cool thanks so i have this particular exploit i just searched ms-03026 so this is not basically microsoft reference you can say microsoft also give microsoft is a very cute organization you can say so they also give one liberty reference to all their own vulnerabilities okay so i just use this i just copy and i'm just pasting out this this particular name of the expert this exploit is against uh connections now i need to understand what actually uh this particular script is doing or this particular exploit is doing i mean what they want to do come on man write slacks
okay good so when we talk about this again uh we need to understand what actually is happening so for that we just have to do show info so when we do show info we get the information about this particular expert so you will see that okay this is attacking a port number 135 if you remember port number 135 was running on that machine that particular machine which we were uh basically we are planning to attack that was showing us that port number 135 is in use yeah you can see now msrpc is a kind of a service which are running right now so we have port number 135 running now what we have to do is we need to
understand what what actually is this exploit and what it do so over here we understand that there is some keywords which are the running that is stack above our overflow some kind of keywords again and this attack works on microsoft 2000 xp microsoft 2003 and multiple operating system so a tag is always on a particular service that is not on the operating system again so i need to understand how this attack works i just do show options and i'm just wrapping this thing up quickly so that we can come up to the manual part so when we talk about uh again this kind of show options kind of script guys i'm just making a font less so that we can
get the whole options with this yeah so you can see that it's asking for our host now our host is basically the address of our victims so we just want to get the address out now over here i'm using up i'm in a private network id so we are using a private ip addresses if you are into a global i'm not suggesting you to do it again if you are into a if you are a professional cyber security expert and you work for organization then you can do it again so what i do is i i just like set our host and the ep address of that particular machine 1.3 my rose has been set
so and earlier the msf was telling me that please don't say the magic word please don't say the magic word let's write the magic but right over here so the magic what we have over here is exploit we are just running the expert so this is the automated one guys it will take maximum five minutes can that can take two minutes so can take 20 seconds if you use a bash bash programming language and once you do exploit you hit a particular operating system and you get some cubed kind of things and you have a sending stage remember it's telling you sending exploit remember so sending exploit is a kind of a which it's using
because it's sending a malicious file from this mac operating system to that msi operating system and it's sending off by sending a file sending a file sending a file and after sending a file when these all the files and you can see it's sending in stages multiple stages like first say second say third stage it's sending on multiple pieces basically like when you copy a file it gets in pieces okay so you can see some metaphase session on better something talking about metaphor metaphor so this metaphor is basically a kind of a remote connection which is coming up and you can see my metaphase is dying again and again and again and again and again i don't know why
i'm still trying to basically had that particular operating system okay my five-minute session has been dyed i don't know will it work or not let me retry i guess come on
okay guys i think my operating system is acting very weird so i'm just stopping my operating system over here and i'm showing this attack on youtube just like we do on another script so you just write a attack name this attack name which i'm showing you this will be on windows 7 and sometimes
sorry my screen has been pushed
yes
come on come on come on
awesome okay guys just after this i need to change the operating system so i'll be requesting uh two minutes from you to do that
[Applause]
[Music]
uh [Music] so
[Music] stranded in the open dried out tears of sorrow lacking all emotions staring down the barrel waiting for the final gates to open tomorrow [Music] moving with some motion following the light that says [Music]
[Music] do [Music] [Applause]
[Music] so [Music] good
[Music] stranded in [Music]
staring down the barrel waiting for the final gates to open tomorrow [Music]
is
[Music] [Applause] cool cool thank you so sorry guys for the glitch uh when max windows came into action you know and let's start from the exploitation part again so i have my kali linux in this particular machine also i hope you will see my screen please confirm yes sir your screen is visible and you are audible thank you thank you so this is the windows operating system which was running which was my left machine you can say i'm just restarting it so that it doesn't get some problem or something like that and we just again get back to action and let me check whether i am into the network i hope i'm not into a different network
okay i'm into a different network so this configuration you have to do when you are basically into a attacking scenario side by side is running a message
and back again [Applause] cool so my ip address is 1.4 that particular ipad is which was coming to that particular windows machine this is the windows machine again uh the ipads which was coming i can use multiple os but i was not having any other operating system no windows 10 nothing so that was only windows which i was using and i can't hack my base opening system please don't ask me uh to hack my facebook system again so i just search ms-03026
search ms03 26 we got the attack back again we use the attack like use this and again show options there was the last thing we were doing we have to set the r host and this is basic subways which this is taking time due to the glitch this is just a basic step which i was not expecting that this village will happen and the ip address is set back again and i just do the magic keyword again that is exploit okay unreachable which is still unusual
the iep is reachable okay so whatever reason it is i don't know why it's not working maybe the day is not with us so again you can just go to google and you can just find out like how this attack works and you can just go to eternal view and uh when you talk about it on the blue attack this was working on windows 7 windows uh like you can say 2016 server r2 servers and all of the things i am just playing a particular video so that you can just understand what actually was happening and what actually these attacks do
one interesting video from hack five so if you see in this particular video this guy will be using again metasploit framework back again so in this meta spread framework he just set up a particular ip address just like you can say he's setting our port number and he set up a particular idp address you will see that the ib address will be missing and you can just find out this thing again and once the address will be in place this person will be having one thing that will be the access of that particular machine you can say
yeah see it's hacking right now you just use exploit and after getting the exploit this person will get metadata session five open and you get the meta better you can see now this meta button is basically you can say the particular access of that opening system you can you can open up the camera if it's a mobile application you can do anything again and when this this operating system is hacked and when the rc work basically people are usually like what actually happened and when people get to know that they are actually hacked so they are basically like this and this and this so they can be multiple expression which people can get so let's
back again understand that what actually rce and what what is expert development so when you talk about rce what actually rc did is it basically sent a particular kind of a malicious payload or a malicious file to a particular port number and after sending that particular file to a particular port number that particular uh machine basically get into a socket connection so again i report ippo so for the ip address of my machine and the port number of my machine it will get connected to a port code and ipaddress of a different victims machine you can say so when you talk about exploit development in exploit development we need to understand and when you talk
about genesis of rc we need to understand first that how remote code execution works so what is the basic step to get into a remote code execution so the basic step is let's say we have a particular uh like you can say handle that is twitter i'm just giving an example we have to do over here and on twitter we have a sign we can just go to twitter sign in and uh and it can be application and it has to be application again uh but it can be anything again so i have this sign up with phone and email address now it should ask a particular phone number like my phone number is nine eight nine
eight nine eight nine eight nine eight nine eight something like that now the password can be manipulated it can't be anything
username and password we sent a particular uh like you can say malicious payload to that particular application and that malicious payload
but the application is not that pretty simple that it will ask me and okay it will say okay let's connect it back again so what we have to do is we need to crash the application first to understand it where we can send a malicious payload or a malicious uh you can say uh payload which is created by msf msf venom is again a tool which creates multiple payload and socket socket handling connections again so when we talk about that it's i'm just giving you an example so remember every attack works on a on a service so on that particular service let's say we have a service over here and this service is ssh now ssh is
the kind of service which you can use to login into a different shell let's say like you must have used scheme viewer and you must have used uh any desk by team you're any test what you can do is you can connect control others machine by ssh what you can do is you can control others command prompt that is legally again it's a service for that so for example by this particular command prompt i can access this particular command prompt this particular command which is coming over here and that that can be done by ssh so ssh has particular parameters like every service have particular parameters if we talk about these services and these parameters these parameters can be user
that is for user name pass for password and how do i know these uh these parameters you can just get out get it out from rfc rfc is basically like if you talk about rfc of network services like if i talk about ssh you can get a rfc of sss that is uh ietf.org which is available over there and you can find out all the like you can see parameters which is working for ssh like if you come up over here and if you just search user let's say so you will see that there can be a there must be a particular service which is and if not over here see these are the references and all the
things if not from here you can just write ssh parameters so you have a lot of parameters for uh for multiple services you can just get out slh command and services and this is what not for not one particular service this can be for multiple services again so just like ssh we can have http http parameters like put get post again these are the methods which you talk about but these are the parameters options delete it can be multiple parameters again just like that we have multiple services like ftp same same way we have ftp parameters over here so in ftp in sss in multiple ways we got the parameters so as per what i want to
show right now is that as per the username and the password which we have we have parameters and anonymous anonymous are basically anonymous login when you don't know the username password if anonymous login is on you can just do anonymous anonymous and you can just get the shell of a different operating system that's what you can do so what i do is i just write ssh address username is anonymous and see the password which i entered if you see the password i have a password which is like this and this is not only the password the password goes like this and further the password goes like this can you can use how many digits are
these how many digits are these basically so when you talk about these digits these particular hahahaha which are entered what will actually happen if this will works on your windows operating system in windows you have a very good quite cute kind of a screen that is known as blue screen of death uh bsod we refer in the short form and if it will be on an application application basically will get something like the application will be crashed so what i do is so do you know do you think that this can be a password this haha can be a password this can be a password this can not be a password i mean as password
password for now and this cannot be a password again if if i have an application let's say and in an application i just have to like okay let's say i have zoom i'm just giving you example and i believe my zoom is locked in yeah it's connecting to google it's logged in so let's say you have any application on that application you try to log in so when you try to log in basically uh what actually happens is it will ask a username and password it can be any app again it can be your instagram application in your mobile phone i'm giving you an example so you just enter a particular keyword and you want to check that whether your
application is getting crashed or not so this is the first stage of rce where you identified it whether your application is getting crashed over here or not so when you talk about this what actually will happen so this the process which we did right now we basically do this with as we enter a is not i've just made it q so when we when we enter a is over here we get an error and that error basically give us tells us that whether the application is vulnerable or not or whether we can hack a particular application or not so that error is basically known as segmentation fault this segmentation fault is kind of an error which tells you that okay this
application has been crashed or this operating system has been crashed so when we talk about this what actually happened so every time every developer let's let's say on our in our mind of developer and every developer must be having a kind of like they they use parameters and they use input variables so when you talk about the application let's say there is an application that is type now they have user and they have a parameter which they created so the data type they use in user can be for example let's say cap car user they have a user kind of like you can say a parameter and same way they have a path like character username and character
pass if it can be mobile number it can be int or you can mob it can i'm just giving you an example of parameters so when you talk about this car this this again user or this pass or let's say over here and we make an array of 20 because more than 20 user name a year it can be not more than 20 again so password can be more than i can say not more than uh that's 30 characters or 20 characters or something like that and mobile number we all know mobile number is of 10 characters 10 integers again so when we have these is this fixed that only 20 characters a particular person can enter when a
developer do is it fixed it's not fixed actually so it depends on the compiler which the developer is using like we used to have turbo c plus plus dev c plus and all tools so in terms of plus plus if we talk about integer let's say and if a person is entering uh or then a array of ten so integer and turbo c plus plus the uh the size of integers which basically used to have uh two whites so when you talk about two bytes so this basically happens ten into two and a user can enter 20 numbers in a way just like that if a person is using dfc plus plus depth basically usually takes four bytes so
you can say it can be ten
do you think these are 20 or these are 40 these are more than 100 and when we have a limit crossed like when we have this like it's asking for 40 numbers and let's say we enter this and this is 40 and if we say we just enter more than 40 days 41. like this can be 41 i'm just giving you example in data with the application error data segmentation fault code now why i'm teaching that data structures and all other things because at the time of my bca i i barely passed with the passing numbers i to be honest i got 41 or 14 numbers in these topics but when i talk about hacking these things i need to learn out
these things so when i talk about this this is basically a process that is known as fuzzing and spiking they get two processes which people use and again this is the same example which i've used over here now when we talk about this it's the same thing against just see like 20 into two at 340 bytes but this haha is more than 40 so it gives you error what is uh that is segmentation fault so when i was learning segmentation font segmentation font in the earlier spaces i was like in every every kind of error it's taking me to segmentation form so what the hell is segmentation form and this was me in the initial stage of when i was learning
expert development so when you talk uh segmentation fault is basically indicates memory corruption it tells you okay after this
which is running behind that particular website like domain so that server must be having a particular uh you can say hosting like apache engines can be multiple uh hosting servers which we'll be using and they must be having an interface that interface will be crashed something will happen for http service again so every service will crash and they will get a segmentation form if you are able to get this kind of error in an application uh that means the application can be hacked in a web application you will not be able to do it but in a like you can say exc application will be easily able to do it so when you talk about again
segmentation form segmentation fault is basically a process where pieces of memory are overwritten and like all other things so i guess uh guys i have some device issue which i am having facing so i will not be uh going ahead with a demo part which i basically created but the demo can't happen so i can take questions uh we already have 10 minutes so if we have questions right now we can take it are we here so yes sir i'm just looking at your friends sure so sorry for the glitch guys uh the machine is not working properly of course my macbook was not working and my macbook was having the kali linux and windows 10 all of the things was there
and the exploit had to be happened on that particular machine but it somehow if i show you it's working on the floor right now so it's not working at all so so sorry for the glitch for more on buffer or flows and talks like this i have given multiple talks you can just search my name on google or on youtube and you can find multiple accounts let's in on the same concept on similar concepts you can see yeah when they're updating any further questions you have already answered
in a different talk back again and uh like i'm thinking to make a complete demo of this thing and uh upload it on my twitter and instagram so you can just connect on connect with me on instagram and i'll show you that how this this talk has to be presented but due to the devices it doesn't work thank you so much for inviting me again and i sign off
i request everyone to open the google form link in the chat box and attempt the questions top three people will get a mask and a pair of stickers thank you sir again for being here [Music]
bye
bye foreign
[Music] this [Music] my [Music] do [Music]
[Music] my [Music] foreign
foreign [Music] so [Music] do [Music]
[Music] the [Music] the three
[Music]
welcome back everyone
an application security engineer and synagogue team member the topic he will be presenting today is how to fail in bug bounties we welcome you so you may start your presentation thank you so much okay so uh we are going to see how to fail at bug bounty hunting so the thing is like i was saying every day i i'm like seeing on whatsapp on my dms on my instagram on my linkedin like everyone is just sending a message like okay sir i'm facing problem in this thing i'm crazy following this thing so basically if you are a beginner in both bounty so this is the talk for you okay and if you are like experienced also then also
you you can watch it because like i will be saying some other tips i will be giving some tips which may be helping you so basically what is happening this is a feel like nowadays everyone is in this field everyone is hunting on same program we have more than like there are many combinations in this field so we need to be a prop we need to make a proper plan for this thing so let's start so okay so before that let me give you my introduction like who am i so i am working as an application security engineer i'm also a part of synagogue red team and i'm a full-time bounty hunter and part-time infrastructure and speaker
so let's start a main thing that is failing at bug boundary so basically what is happening like at a beginner we are doing some con mistake like everyone is doing like it's not like okay if only you are doing like in my case also when i was a beginner in this field i also used to do the same mistake so we'll be seeing all the failure first then after that we'll be going for like how we can change our approach so that we can have a like if you are if you are like just finding bugs and reporting and by any problem you are not able to like go for bounty then of course you can
learn from this thing so we let's start so the first thing is you are participating in the wrong program okay so the first thing like there is no uh like thing like okay wrong and the program is the best program for anyone see what is happening basically as a beginner if you are just going for a program which is having more than like for example if there is a program having more computer like there are more testing on the same program then of course for a beginner like you like if you don't know that much verbally because of course when we are going to start this field we are not well known for all the our material so
the competition will be written up on that program so that is not a program for you or just for example sometimes what is happening there are many programs available for them the payout is very less like they are not paying you that that much okay so in that case also if you are going to start testing on that program then of course if you are finding a bug you are reporting then they won't pay you that much so that is the program which is not for you or you can go more ahead if a program is having the scope less like for example all the assets which they are providing are very less then in that case also if
you're a beginner then the because the assets are less and the competition are more because you are seeing the crowd is more and more nowadays in this bounty so because the assets are very less so if you are trying to just report about ability then the chances of getting that verbality like maybe they will be giving you not applicable out of score duplicate these things will be it is a fixed thing you'll be getting that so always try to take time to do the program this is the first step for anyone who is doing bug bounty so then the second one is fail to read bug bounty guidelines nowadays what is happening we are just
entering into any program let's see you are testing on background platform or hacker one we are getting a long paragraph of all the guidelines which they have given now this is a time like you need to first keep everything okay like for example if you're trying to uh start testing if you don't read these things and the chances of getting your bug out scope is very high so as a beginner i like in my case also i was also doing the same mistake at start but now i have been learning okay you need to first read all the things which is given on the program um guidelines the third thing is lots of duplicates now for a bug bounty hunter this is a
very common problem like you also know and i am also seeing every day on linkedin on instagram like okay i am just reporting about my t and i am getting a duplicate so first thing is don't take it as a negative uh manner okay take it to the point okay if you're finding a moment let's see if it's any moment here it says yes rf it's idol it's a sql injection it's a rc if it's bleed also the thing is you have founded variety okay and the main thing is because you have foundation they have accepted it abundantly the company is accepting it but yes because anyone has reported earlier so they will not pay you so don't get
demotivated in that because you are learning main thing in like we are doing one piece for learning we are just breaking the application for that we can learn more and more so don't get demoted it's a part of this thing okay if you're in bug bounty you're doing hard work i know like everyone is doing hard work but the luck is like a main factor in bug bounty because if any anyone has tested this this application earlier then they must have found it vulnerability so of course we are seeing a lot of duplicates so in the next slide we will be seeing how we can cope up with this like how we can uh try
to get the number of duplicate layers now the fourth thing is uh fail to show impact nowadays what is happening we are just trying to we are just getting some api key we are just getting some access keys or id and all and at that time we are just uh going like okay we have found something and we will report it no uh if you are just reporting these things like api keys the id password you know you are getting on any uh txt file or or any sources then you need to show the impact and what is happening in the beginner video you just failed to show impact so that is a problem and that's why we are like not
able to just if you are reporting a bug then they won't accept it now the uh fifth thing is you don't stick to a program now this is a very common problem um like for everyone what is happening if we are like going for a program uh and we are just testing it and after a few hours if you are not able to find any vulnerability we we just jump into some other program and that is not a way if you are in abstract also you need to understand the application and it takes time like in few hours you can't uh like explore everything all the functionality you can't uh explore everything in just few hours or in few days like it will
take time to depend upon the application so if you are like if you are a beginner then you must be doing like you are you are just seeing a program you are just testing for a few hours and then you are jumping for different program so that is a mistake so we will be seeing like how we can overcome this now the main thing is you don't reckon now as i was like telling from start like we have a lot number of people hunting on the same program we have competition we have crowd so if you are not doing recon then recon is a very important phase uh in this because the record will help you to
increase the attack surfaces recon will help you to just find some better endpoint some end point which are very like you can find bugs on them so reckon is the thing which you are not doing maybe so you are feeling it now the last thing is bad report writing so maybe you may be like a very experienced one you know how to to find the bugs you know how to uh just be on a same program but at the end of the day you don't know how to make a perfect reward as i know like okay we are or we all are in corporate world we know how to just make a report writing but uh like basically what is happening
uh sometimes if we can't explain for example if we are just reporting a bug and the program owner can't we like we can't we are not able to uh let make them understand okay this is the permanent and this is the impact so they won't be accepting the uh our report so that is the thing like if you're in buck or hacker one sometimes we are not able to explain them like okay we have found this and they are not able to like understand what we have found so in that case they just make it an a like like so this is a thing which you need to be uh seeing this so approach towards a better
bug bounty hunting so we'll be seeing all the like all the failure thing like the things which we are doing wrong and how we can just improve it so the first thing is take your time in choosing the right program now what is this like okay we have so many programs if you are if you are just going for like uh just crowd like so there are many programs available so you need to uh like go for some points which are very important for just making a program which is like a program which is best for you the first thing is the scope the assets assets means the in-scope item and the out scope item so
when you are just uh jumping into a program you need to first analyze all the scope item on our scope item basically what is in scope by outscore item means i incorporate
so you need to first analyze that because if you are testing the autoscope target for autoscope assets then of course they won't be paying you they will be marking you duplicate also sorry they will be marking you as not applicable or out of scope so you need to uh just choose a program which is having a good number of assets because you are a beginner now the second thing if you are choosing program should be number of report dissolved why i am saying number of reporters because what is happening if the company is active means like if you are seeing the number of all the depot which is always more means the company is active the company is all
the bugs which are been reported they are trying to patch that volatility they are trying to fix all the communities so the chance of getting the bug duplicate will be less because the company's active application will be updating every day so if you are seeing the number of the bug or patch or more then you can go for that program the third thing that you need to uh just see is the payout and i think in in like in this field in bug bounty we are just going for payout thing so it depend upon your priority like if you want to see the payout also then just see the payout for all the classes of vulnerability
then only we just take a program okay if the payout is good then we can just just try to hunt on that program the fourth one is time to twice and time to pay out like okay so in background or in hacker one they are just giving you all the information like okay uh after a particular time like after 24 hours after two days after three days they will be giving you a proper uh like uh answer that okay your bug is like valid or not and then after some time they will pay you also after their fixed time so just see like okay if the time to try this less than you can report you
can start testing on a particular program so that is the thing you need to uh like do so take a time take your time choosing the program and the program which you see like okay which which gives you all the things uh like they have more assets they have payout is good the number of all the bugs which are been reported
now that the second one is read and understand bug boundaries before that also one more thing is like if you are testing on a platform platform so platform has some their own vrt rating like if you are in buckthorn they have a phone vrt rating if you're a hacker one they have their own rating policies so also please see these things because sometimes what is happening many bugs are like they are uh like uh let's suppose that hackerman is accepting that particular but we won't accept network so with difference in platform you need to change your approach also the the technique which i am giving you through the program is for the platform one if you are testing on rdb program or
if any company is hosting the program on their site only in that case there is no guarantee like okay like if you want to test on their problems you can test but the chances like okay the time to try and time to uh bounce they are not fixed okay so if you are testing a platform then you can just try to use all the tips which i for choosing the right program now the second one is read and understand but bounty brief now what is happening if you are testing our program they just give all the focus area so the main thing is like focus area is like it's a very helpful for a beginner
because they will be giving you all the names for the other warranty they want us to test okay the main thing now what is happening
there is a message from the audience youtube audience they are asking you to slow down a bit okay okay yes thank you so like the main thing what is happening if uh we are seeing there are some guidelines uh present the first guideline is like the focus area so in the focus here they are just just telling us all the moment what empty they want us to test except what they are interested in csrf csrf idol or sql injection or these any moment they want for mobility which they want us to test now as a beginner you may not be knowing all the varieties okay so you can first make a list and now bug bounty is all about learning
and then trying to use that uh like what the thing you are learned you can use it on a program or an application so that you can practice that so okay i have been like seeing all the list then i can make a list of all the vulnerabilities let's say if for example i'm testing for csrf then i can make all the functions i can first try to get the functionality all the functions all the all the parameters from where i can test the csrf on the particular application then after that we can make all the cases okay and then you can start testing a particular program so in that case what will happen because you know the like
what the company want from you so so the bug like if you are reporting that bug then they will be accepting the chance of getting it acceptably more and also you must be seeing the out of scope thing is also given okay so out of scope is like if for example i am seeing like there are some low hanging fruit let's say demarcus i think it's everyone is knowing this type of vulnerability so spf demarcus autoscope in every program so if you are a beginner and you have just learned skill marketing and you are just going to report it on a program then of course uh like they won't be accepting that so you need to also see
that and in some program what is happening the dos attack is also uh in scope area so in that case because we have seen uh understand all the uh thing which is like on the brief of the program so you can report and you can be like the whole crowd is on one side and you can be on the best side of that because you know okay this company want these type of quality only now the third thing is understand the variety of the bug and try to explain impact program owners now this is the uh like you can say the main thing because if you're finding any vulnerability and you can't like explain the impact of the
probability then it's like not like if you're reporting also they won't accept it like for example uh let's suppose that um if you are finding an api key and you can't exploit this is very common uh like i'm saying on that like many are posting on linkedin on twitter on instagram like okay api key uh we have found out and we need to report it can we deport so if you can exploit that api then of course you can report it but if you if you can't export it api then it's not worth it like okay you have found api key you can report but then the company will be asking what's the impact so you need
to just give them a proper impact if you're running any automated scanner and they are just showing you something like okay there is one military let's say like in work many times if many people are doing scanning and they are just getting caught so you need to exploit the course you are just reporting okay you have got a call but you can't expect you can't give an impact to the company then they won't accept it so whenever you are finding any already just go for like okay uh like just first try to um means get an impact like explain the company every impact for object vulnerability now the fourth thing is keep yourself updated with the
new updates on old programs now what is happening we are testing on various programs okay as a beginner we are just jumping onto programs we are seeing like okay we are like we are getting boundary also we are just moving on to program program now the thing is the application will be patching that particular vulnerability and then they will be updating now as the company is updating their application of course their functionality will be increasing and as the functionality will be increasing of course the box will be more so after few like after few months of ub you can just come back to the same roof and you can start testing on the old program also on
the plus point is what is happening when i like in my case if i am going for an old program testing i know the program very well okay because i also have tested i found the bug so in that case what would happen because i know these means the functionality how the application is working everything so that the chances of like if i want to just find a bug will be more like if anyone is trying to like he's new to this program so he will take time to understand the functioning of the program but in my case i am very old because i have been testing the program earlier also so i know how the program
is working so in that case you can be on the like you you will have some advantage so always be updated with the whole program also like okay you're testing your program uh daily but just go for some old program testing also maybe if you are not getting books on youtube then you can uh just try to find the bug software program now the thing is record and i was thinking record is very important for like everyone and like one is the like most important thing for anyone who is doing bug bounty so you can do one thing you can start with manual and automated record so why i'm telling automated and manual both because sometimes what happened with
some automation we we may miss something so you can also do things manually also so you can try the scope is recon by herzbotra why scope click on because uh like scorpiocon is like it's a very best way to start like like if you want to start doing recon as a beginner the scope based icon will give you all the things you want like okay you need you know that if your scope is small you're scoping medium or your scope is large then you are knowing like okay what are things you need to test what are things you need to find what are things you can do if you you are knowing all your scope so
chances of getting your bugs not applicable or autoscope will be very less so you can try to uh like learn this copy second thing they are like blogs uh there are some videos also for that so you you can just and also if you are doing automated record like there are some framework so if you are doing this automated account also try to use all the information like it's not like okay you are doing a require automation and you are finding various information and then you are like like you have found so much information but you don't know how to use that so in that case it's a waste of time for you like you are doing a recon
scan and you are just just throwing the framework in your uh like in your os and then you are finding a bunch of information and then you can't use that and it's a waste of time also so try to like do a proper icon like all the things which you are getting all the like let's say all the means all the information you are getting you need to understand how to use that thing like for example if i am getting a medium scope target okay because i think large scope don't get generally and small we can't do that nothing so in medium scope what is happening i'm getting uh like let's say a url let's say xyz.com
so i i will be going for the first thing that is the subdomain so after getting the subdomain what all things we can do so we can just try to first get the active uh one so we can just filter out the active subdomain but now also what we can do we can do some more end points we can find some end point to the the all the these this are left like for example if i am getting any and unactive for them like for example if the company is blocking me from there so then i can try to bypass that if i will be able to do that then of course the domain which i am getting the url
which i am getting is already like a you all which is not tested by many because that the company is blocking everyone and if you are able to do some more things on that and also one more thing is like if you if you are trying to use only one tool for recording like you are not doing the concrete you need to use some more like for example you want to find go for way back use more and more tools find more parameter to test on so that is the thing so that whole thing for record now we will be seeing uh like better report writing so as i told like okay we all are in corporate world and we know how
to just make a report or not but in bug bounty basically what happens uh the first thing is because like there are many combinations everyone is just what they are doing they are finding bug and then they are just reporting it like so what you need to do for to be out of the crowd you first make a proper heading the heading looks like you need to show some impact also like for example if you you're finding any leak information then just tell them like okay you have found information about one lakh client so it will be giving you like a proper uh like let's say or report title for example if i'm getting any
leak information and i'm just leaving them okay you have i have found some leaks of your client and i'm giving them one lakh of the client so the difference see like the impact they will be getting now after that we need to explain them the verbality how we have found our material what is the vulnerability and don't give like them like you are just copying pasting all the like about about the permeability give them a short intro point wise is very good don't even pack up it's like we are just giving a report we are not having any history class so don't give them like cooking pad of long period of 100 words for 120 no don't
give like that just keep it short just like in point wise tell them a proper step to repeat like how you have bought your community this is a very main thing if you are wasting your time in just uh like just uh for example you are just giving them all the uh like everything about the burger or the vomit you have found it's a waste of time you need to first tell them the main thing is like how you have found our ability and the main thing is poc you will see the thing which you need to give them because you'll see like if you're giving them then it will be very easy for them to
find the material okay that they can confirm that that the permitting is existing or not so the poc can be in the form of video or in the form of screen sort it's depend upon your audio you're giving okay so after that when you attack the poc on your report then just go for uh like for example if you have uh just given these thing then just tell them the impact also and impact is very important if you're not telling them
and at last just tell them how they can mitigate the vulnerability this is very important your abstract uh like you're in absolute field you are learning how to uh just do find a flaw then you need to also explain them like how you can mitigate that so these are things which will be helping you and if you are properly doing these thing then of course you can be like just finding a varmint of course i am damn sure that the boundary is on your way okay so now we can go for tips for beginners so basically as a beginner everyone is facing problem okay it's a common thing because in birth warranty everyone is like not knowing everything of course in
my case also i was also at a beginning i was also not knowing many things in bug bounty so what is happening we all are seeing like everyone who is doing bug quantity is like they are just uh saying okay money money money so don't be giddy start with uh let's say go with the point-based program like in buckaroo nowadays they don't need point but yes i think uh if you're testing on the program then of course the main thing is learning so you are learning the cloud is less so you'll be able to find more bugs on that program and maybe bug is giving invite also for that so if you are going for pointless program then it
is very helpful because you are getting private invoice in the same thing is there if you are hunting one point by program the crowd is less so in that case if you are just like for example you are just finding bugs on the pointless program so they will be sending you some private invite and then you can go for bounty but at start if you are just testing the program which are point-based so mainly learning so you will be learning more and more vulnerabilities and the competition is less on the point because all the experience hackers or the hunters or anyone who has a guy who's testing on the application they will be going for the program which is giving
give them boundary so that is the first step that you can follow now the second tip is go for the white scope target now when i'm saying white super target means the target like for uh i was telling like if you're choosing program just see how much acid they are in scope so if you are having a medium scope or large then it's a perfect one for you as a beginner because in small scope of course the crowd is more so in small school the chance of just getting a valid bug is very less okay all the bugs are like many have been testing on their application they have just reported at work earlier also and anybody you know
luck is very important so of course you are late in that so of course you have you are knowing that community but they have been reported earlier so if you are going for any like medium scope or large your scope is large then you can do recon you can find some more endpoint then you can start testing again yes you can get uh like you can get some bugs which can be accepted and they will pay you for that now the the main thing is no low hanging fruits now see low hanging fruits if i'm doing no lowering fruit it depends like why i'm saying this so if the program is new like for example you are getting a private invite
and that is a very new program first program no one has tested start with low hanging no problem but if you are seeing a program is very old like many have tested many have been many bugs have been reported then of course uh that program like if you're reporting any low hanging fruit then they they will be like okay the bug has been reported earlier so it depends so nowadays uh we are seeing like every program has been tested uh like by everyone so because you are like okay every day we will be seeing new program but many programs in buckner also also are tested by many so try to get some more uh like like say
sql injection or you can go for lfi the auth misconfiguration idol so these are some vulnerability if you are in buckler then there are p one p two vertices so these are variety which are very good now the main thing is what is happening as a beginner you all are thinking like okay i can't hunt for the auntie so don't uh think anything like that if you want if you're thinking like okay these are very tough so of course anyone can find okay just you need to spend some more time on the application now the main part is if you are like uh like you want to learn these community then you can just start learn the art of
talking like everything is available okay everything is available on the internet in fact i am also learning from internet i am also just finding i want to learn anything i just go on the net i just search the all these words like i want to search rc then i will search rc and i will be getting many blogs because there are some talking talks available for searching and all so you can uh like search find learn and then use that thing on your application the main thing is you can let's learn hack and repeat these are things so always uh like in a day just prioritize your time just give two hours for learning and then some hours for
hacking so it will be a very important time because you're learning daily you are you are making your you are upgrading your skill daily and then you are trying to like see after learning you need to also do a practical thing okay so lab solving is good you are solving labs and you are getting work but success and it's a very good thing like okay you understand how to appreciate behaving and you have found you have expertise so learn how to find things by our own like everyone like everything is open source every hunt by country sharing their blog there are many things i've also said many blogs many tweets and all you can just search these things and you can
start learning on your own you don't need anyone like any guided event or for that everything is now available okay now try to learn the use of word extension now what is happening this perfect session is a very underrated thing like many don't know we all are just going for scanners and scanners are not good according to me i don't use scanner i don't automate things if i don't know automation i i'm doing things manually so basically what is happening birth extension will be like okay it's not full automation it will just automate your some part some part only and that is very like if you are like technical application then you can be a like you can have a plus point
because of that so learn how to use the buff excellence for but like if you want to find idol or xss file upload there are various extensions available on the work suit store okay so in that case you need to learn these things also because it is very helpful for everyone okay now um the last thing is learn changing different vulnerabilities now what is happening we are finding any low impact but let's say html injection okay on any any functionality so we can change that particular quantity also but as a beginner we don't know so uh start learning how to change different nominality okay i won't be teaching that now but yes i'm just giving an idea that you need to learn
the training okay because chaining is a very important uh for everyone and after chaining you can just just make your low impact but a very high impact okay you can change some like sql to r so you can change lfi to rc you can change srf2r so you can say that tman injection ssrl so you can change different verbity you can exploit more and you can get boundary from that also and sometimes what is happening you are no you are knowing like some program they are just giving okay this particular bug has been found so you know so you can first try to find that particular bug so so your learning will be uh completed now you can try to
change that moment like for example if in a particular
you if you are seeing any any moment on file upload you can try to change it to rc so that is the thing you can just make your work more impactful okay there are many vivid blogs also uh on the internet there are many tips available you can just search for that you can learn from them okay one more thing i am like many of hunters are just saying that tips and all and see every uh tips every step to reproduce like for example anyone's trying to do accounting or attack or any other attack it depends on the functionality so if if that guy is able to do that for particular thing it's not like you can also do that thing
so read that that tip understand how he's uh like doing these things and try like don't start testing that steps to like you have seen the step you're copying the step in every application that is not a thing you need to understand like every application is having some like every app having the functionality behavior is different so that is a mistake which maybe you have been doing so don't do that they are also like i am seeing many automation scripts are given like they are just making uh some like they are just making some tools and all so see like you are just uh making a tool and then you are if you want to use a tool
you first quality so and the learning will be zero because all the things will be like the tool is running in the background and you are just seeing that so you are not learning anything so try to first do things manually then learn uh how to automate things and then you can automate it by yourself that is the best approach you can do now avoid screen sort now this is the um best thing uh like like i have been like okay at start i was also posting various screenshots okay and now nowadays i am seeing like many are posting but see screenshot posting is not bad in my time what i did i just used to
tell the bug name and how and any tip so if you're posting any screenshot then of course just post a tip or any sample any sample of report let's say for example you have been learning from h1 reports or you are learning from medium blog then just attach something uh like from them create a beginner who is like in the in this field who is just intend to enter in this field you can learn from that source but nowadays what is happening we are just saying okay they are just posting uh like okay i have found this bug i have found this bug and i have been given this much bounty they don't uh just give any like tips or any uh links
of the report or resources which they have referred in that case you can unfollow them okay because like i have been uh like sharing uh every like if i am finding any variety then i am saying all the blog which i have been referring and i guess i want everybody for experience fun then you can just do that thing also okay like you can just uh like means you can also give some tips any dog any uh payload which you are using so that any any beginner can also do that if you are it's a very basic if you don't do that then if you are following anybody who is just posting a screenshot not tips no
help no support just unfollow them or you can ignore them why because uh as a beginner you are facing problem in this and he's just posting his success of course see success posting is not bad but uh the thing is we need to keep in mind that everyone is at a start is at zero and they are not feeling okay with that okay so of course if you are feeling demotivated by this then you can just unfollow that that guy no problem the second thing is don't compare everyone is like comparing like okay this personal guy is just going and he's like he's finding only rc sqli the big permit so if you're comparing them then just
compare like he's like experience like he's hunting for more than one year two years so he know many things in compared to you so when he was also at starting off at zero in fact i was also at zero like in my first two months of hunting i was not knowing how to find sql injection i was like scared about sql injection how to find sql srf rc and these type of bugs okay so uh i also feel this problem like okay that particular particular hunter is finding many bugs and i am not able to find work but nowadays i can also find the box which my like all the hunters are finding so it will take time you need to
give your time to yourself so that is the main thing if you're giving time you're learning learning then of course at after few months after like one year two years you can start like you can get that bug also so just keep a target like okay you need to learn these type of these probability and start focusing on that you can follow follow a guy like who is posting tips on that practical and you can also text him like okay and one more thing like in texting don't message anyone like hello hi i'm been i've been like getting messages like hello i don't you can just uh just message any uh okay or facing a problem in this
particular field in this particular bug then we are happy to help okay now spend more time in learning and believe i mean you you will be getting success now see the problem is like bugs want to enter are like just like you are just going for money and it's good like okay everyone wants money because money is the thing which will change life i like at that time when i was also beginner i was also if i was getting money from this field i used to like okay i'm getting a money so my lifestyle will be changed but if you're not learning then bug bounty is the field which which want everyone to be updated like every
day new uh like there are many things are like coming there are many cvs one already are coming so you need to be updated with everything okay so you need to keep learning daily learning should be uh like your priority and bug bounty of course so if you are learning then of course you can find more bugs and you can do a full-time content but yes trust me i will be saying uh don't do full-time burgundy because sometimes what happened we don't get bug in like always so you can just find a job and yes bug bounty will also help you to get a job also because like if you are like an abstract you are finding one it
is no other approach of this so you can do these things just try to things like if anything is demotivating you then try to ignore that thing okay don't allow anyone to be the reason for your demotivation okay you are on your own you are self-made just try to find the mobility and report it try to learn more and more and then you you will be getting success for sure now comes the automation part now i will be like telling you uh like many of our them are automating accesses sqli in my case i am a guy i'm testing on the windows okay i'm only doing i'm only uh uh having one period which is burp suit
so for testing modernity i can't tell you any automation script okay because uh like if you're if you are in a learning phase then or atmosphere is not good for you for decon you not you need to uh like automate stuff because everyone is automating and you need to be fast enough like if you are finding a program and then you want to if you if you want to start like doing record on the target manually then it will take time and because of combination you need to be fast enough for that so for that you can use some automation framework i have been seeing many automation framework and the best three is the first one is
the reckon ftw the second one is beam tool and the third one of meteors these three are the best automation tool if you are going for default 50 fpw i think my all required methodology which i have been following manually is like like for example i am i was very totally impressed by this
this tool is best for you okay so you can use this tool for your default automation the second one is the project theme so based on mythology if you are following him you will know about him like what is the scope-based record methodology so this project beam works on the same so if you are following this scope-based record methodology you are doing things you can you can use this game tool and yes like i am sure like it will be very helpful for you the third one is medius it's a like a very good scanner tool if you're doing a recon scan it's a old tool but yes it's now also good if you want then you can
also take it like in your life you can use this also use any one if you're it's one of these i am not going to use but they're going to have to ftw is my favorite one so now comes the bug bounty resources so we have been like uh seeing uh like for a whole day like for a whole talk like okay we need to do this we need to do that we need to learn and all now the main thing is bug boundary source like like if you ask me from where i am learning things i think many of uh like burn that they don't want to like tell these things but yes see i am very
open to it i was learning from all this which are open source okay so the first thing is you can go for some free sources which are the port secret lab see uh like when you are solving any portfolio lab one tip which i will be giving you don't see the solution if you are seeing the solution of the labs then it's a waste of time you are just wasting your time in solving lab because you know the permitti and what is the problem with beginners they are just just asking one question from everyone i have solved the particular portfolio and tested lab everything but i am not able to find the flaws in the real application this is
because you are seeing the solution in the lab you need to not see anything what is this lab and just see okay sq injection lab is there you have learned sql injection try to find try to see how the application is behaving if you will be able to uh do that thing then it will be you will learn the approach also but if you are seeing the solution if you are seeing the payload what is being used and all then it's a waste of time you're solving for cigarette but trust me if you're solving the portugal lab like like just treat it as a real application then you can easily use that knowledge to hunt on your application
now come the paid uh sources from where you can learn so the first one is the pentester lab it's a very good thing if you're trying to learn about bulk bounty the web application parts and pentester lab is very good uh all the batches from recon back to essential patch everything is good i have been using this pentaser lab and trust me it's a very good thing just keep on notes about all the uh like all the labs you're solving because it will be very helpful for you in the later on also like bounty the third one is the bugbountyhunter.com trust me if you are like want to invest some money then bug 100. is very uh
good i have been like trying to i'm practicing on this platform and it this platform has around 112 to 100 plus formality and like he has made a application which is real life application type only okay so if you are like want to invest some money then go on for this because like if you are testing on this particular platform then you will be knowing like how the application is like how the reason behaving how it's working so it is a very like uh like if you are like for example you want to learn either or let's say or then you know like how to find on a real life application type one because you
know like he has made like all the quality which he has been finding on the real application he has just add that on his platform so like this is the best thing which you where you can invest two more things where you can like go for practicing or the try acme and hack doubles so hydra box is free of course if you want to go for vip then of course you need to pay halter box is like okay it is more like on an npt thing okay you are just like playing and map and all but you if you want to find uh like some like if you want to practice the works and all then you can also practice
from the box like
okay like they are finding this informative and in real life it's very hard to find so if you're solving from the hacker box then you are learning things okay and uh interacting also there are some machine which is very good there's some uh like all for like for learning bugs would for like they are some uh like everything which is having all the box lfi and every other books and all so you can learn from that also so these are the things which you need to uh like like you can use for learning there are some hackerman report you can like start uh like practicing from there like you can read five a heck of a report daily
so that you can learn things from there how the like how the hundreds are reporting things you can also just see some blocks on medium on a particular minority how things are working there are many blocks available so you can just see you can if for you if you want to learn drakkon then there are some hearts both are talk and nam so you can see that also he has been posting like he's just uh like every uh hunters who is famous for experience are coming there and just like just giving the hint like how they are doing records so it's a very best thing for you so you can do these all things and i think that's all enough for like
uh this talk so if you have any uh like any problem any doubt regarding the stock or regarding bug bounty you can contact me on my handles all are given here i will be posting uh all all these slides on on my linkedin and twitter or you can just see all the links here so thank you if you have any question please uh i will be happy to give the answers uh sir we have questions from the chat box yes if you can read them okay
wait um
okay i think okay so the first one is what to do when i found some critical bug but it is auto scope and what should i do see uh like for example in uh if you have an rc okay and then like you're saying like okay it's auto scope like then don't report attack because the company don't want you to report that thing so if you are finding also then just keep it with you like okay you have learned things from that so it's good but uh like don't if you're reporting or what you can do you can just mail the company like okay your from this permit and it's out of scope but because the impact is very
good so if they can like accept this community depend upon the computer company okay if the company is like if they if they want to uh like if they want that their efficiency applications be secure then they will accept that no problem but in most of the cases the bug which are very impactful it is not auto school like if you are testing for sequential and all like that then then it's not out of scope but in some cases like if you are testing on background and a particular bug has been it's been like everyone is searching for that particular but let's see if you are finding sqlite in a parameter and everyone is just just finding that bug
and reporting then they will they will be giving it a autoscope bug so in that case uh okay like i think that's all your question about and now you have let's say we got some connected 30 domains for one domain that is in score so we go and test for bugs on all the subdomains or should we prioritize some subcommittee fighters then how to do that see if we are like having a scope the scope is very big start testing from the first one to the last one don't escape anymore like we can't prioritize anyone start from the first one or like you can make any pattern okay it's depend upon you test every uh
parameter every uh like scope url which is given on the in scope list okay because if you are like missing out anything then of course any other hunter will be coming and he will be finding some flaws in that so try to like like test everything which is given in scope item don't leave anyone and when you are getting any like domain and any you are and all then try to get some more end point automatically like you can for that there are some rules also uh like the gao and vivek world so you can find some more endpoint from that and then start testing don't prioritize it like that okay you need to test everything don't
skip anything in a program take your time take like two weeks one month test every functionality don't skip it okay i think that's all
these are it okay so yes sure thank you sir for explaining so well and taking time to clear all the doubts this wholesome experience of learning and participating is a very unique one breaking the monotony from our regular schedules and we are thankful for that i would request everyone to attempt the giveaway questions the exciting prizes for this slot will be three pair of stickers again thank you to sarsa for joining here taking out time from a busy schedule and conducting this session thank you so much for being here
[Music]
my
uh [Music] boom [Music]
one
do [Music] bye [Music]
[Music]
i'll be introducing you then
welcome back everyone three sessions done and more to go but the enthusiasm with which we are learning is worth appreciation so pat your shoulder and pull up your socks for the upcoming slot also do not forget to subscribe to the besides noida youtube channel and share this video to as many as possible now i'm delighted to introduce our next guest for today mr rithik vijay he is an independent security researcher and a curious developer the topic he has chosen for today is not not
hi vandana uh thank you for the wrong man welcome and hi besides everyone attending the session you already know that uh topic for today is not not intact so without further ado let us begin into the session this is the most common slide that always receives our presentations who are i and i don't have a lot to say this is the toughest slice for me i'm an independent security researcher independent as in i don't really have a job right now and i am a python developer and i contribute in open source not a lot i can disclose or whatever i have anywhere to display so before uh checking the jr the first would like talking about what's not intact let's
see why matt what's it and what's not in fact what's the problem if you are not familiar with that so it starts with uh the ipv4 capacity like the ipad ss you see 192.245.1.3 these are ip addresses separated by three dots and four numbers there could be maximum of around 4.3 billion of them and that might sound enough to you but wi-fi networks alone constitute 11 billion in our world you can check this out statistics on google.net this is an awesome website you should certainly check that out but that's just the wi-fi networks internet connected devices every wifi network has like five or six in devices and it might be connected to internet and there are devices that are not wi-fi
networks still connected to internet by ethernet and other uh means so you have a lot more devices that want to be able to communicate over the internet but ipa addresses are limited to 4.3 billion so what do we do ipa just exhaustion there is no way to accommodate everyone here in all in these limited span of ip addresses then comes nat this is our savior what does that do what's it well the one sensor no one's interested in the full form it's it simply maps internal ip address to one external ip address now if you see that there are not enough ip address so if you take your 10 devices and map them into one ip address and then launch
it launch it to the outside world the outside world is going to just see one single ip address as simple as that and behind that you have 10 different devices all having different local ip addresses so you might consider your home router as an example you have a mobile phone you have a computer all of them whenever you go to what's my ip.com or assembler site you see a single public id and that's the reason behind it well it's also the reason behind my fellow hackers why your reverse tcp connection never works outside your lan network so you might have uh used a meta printer or netcat to initiate a reverse connection to your computer but you don't have an
ip address directly pointing to your computer you have an ip address provided by your isp and you can use that but that doesn't point to your computer that doesn't work in the reverse direction independently if you initiate a connection it comes back to you that's totally okay and that maps the packets correctly but if there is a connection coming to the magic device it won't automatically get broadcasted to all the devices and why all your hacking videos are a total mess when they are not in no local networks this is one of the reasons well basically it's this you're you're a host and uh you have a packet so you have a computer and that initiates a package it starts a
get request or whatever and it sends to your router which is a nat device as well and router takes a packet and sees oh this is the packet now i made this it's my packet and now with the ipads of router it goes forward into the uh whatever network is over there in the outside world so this is how that works well breaching that so this is my entire point of this presentation we are going to breach the mat well the simplest approach is to use nz rok i am sure you all are familiar and most of the web developers are familiar if not all it's used to uh get the local websites up and running on
you know internet without even having a hosting ban or anything it kind of bypasses that in a way so you should have a look if you haven't else you can look at bef beef it's a browser exploitation framework well one thing that's always connected to you the internet is your browser right so if you can exploit a driver you can find a vulnerability in that browser you can totally have access to the internal network of that victim or even more than that who knows and i think that's it the talk's over that's good these are nice things but these are not something that constitutes my talk have a look at these you will enjoy these
tools but the talk is going to be something else well dns it's a very simple technology uh in the easiest terms it maps your domain name to an ip address very similar to how you have used to have phone directories and now we have a contact list in our mobile phones so we find out the name of our friend and then we hit enter the name doesn't travel to the mobile phone career provider what travels is the phone number right name has no relevance over there similar with domain names if you type in google.com or besidesmoda.com for that matter that name has a little relevance after after a while in the network channel what is relevant is the ip address
behind that name and then all the communication move forward with that ip address now let's see that in action if you're on a linux and if you're not you should be you can use a utility called uh dig it's a very nice tool just fire dig and then space and writing whatever domain name you wish to find the ipad yourself for example uh besides noida and then you will be able to find out the ip address behind that domain name so it's a very simple utility and how dns works is totally outside of this presentation because uh it's simple but complicated and do give this a command a try you'll see that this size node contains two ip
addresses what happens after this is none of our concern but um this is it moving further we have one last part of our puzzle in this and uh in this talk here same origin policy if you have worked with web browsers or if you are developing a website you might have heard of cors and it is required for a website to be able to access another website's data so this is a requirement in a way that a website like besides a lot in cannot simply fetch the twitter.com address and simply get whatever information you have there on your feed it's just not possible and to enforce this uh structure we have something called same origin policy
well uh someone wants to just spot forward through nat actually that's not possible uh why we'll talk in a bit uh so uh you have a co rs and uh you know what cois is but these constitutes are all the puzzles of our current presentation this this is all the prerequisite knowledge that you need to have to carry on with this uh talk so let's see what how can we exploit this and we are going to exploit same origin policy itself there comes a question what if besides noida dot in points to a real web server which it is right now there is no doubt with that so uh this simply points to a real web server and
we have two really funky technologies at hand that is dns and uh cors right but what happens when after opening the page it changes your current dns and start pointing to 192.168.1.1 or maybe any other local ip address anything at all nothing nothing uh that's that was similar to besides no ideas ip address anything different at all but it is uh certainly totally possible and it could happen so what happens uh when we do something like this we uh in a way we bypass cors right because you have the same domain name besides but the identity the entity behind the domain name the ip address behind that domain name is totally different so this way we might be bus by passing
the cois policy so at this point this is a very uh this is a very crucial point and uh nearest wants to say that no hacking our server we are not hacking your visas right now but uh are you along with me as of now because uh by now we have constituted uh everything that was important to this talk and uh if you are with me then uh let me know in the comment section or whatever means you have over there because these two policies are very important dns and cos and this is our attack scenario so how are we going to carry on with this attack well it's something that i just told you
it's a besides noida and it right now points to these domain names and after a while user browses your website and does a little bit of experimentation on the website they are just having hanging around maybe so like a social media or something like that it's they just have to be on that site after a while it changes its ip address to a local ip address this is our entire directory which means browsers have no problem for the website to allow access to 192.168.1.1 and your entire internal network is this way exposed to the outside world now ravi chain has asked a question in the chat like how would it change the dns too uh so so here is the thing besides noida
dot in in this context is the attacker's website so let's separate who is the attacker and who is the victim the victim is the person opening uh let's say example.com i don't want to just carry on saying this is an attacker so let's say victim is there who is opening a website called attacker.com and they are browsing the attacker website and they are having fun after a while attacker.com is controlled by the attacker right so they can simply change the dns from their dns panel there is no big issue from there they have the entire control in the dns panel maybe it's uh any dns service provider i'm not sure if i'm about to take names
but uh they can simply change the ip address from there and you'll see that you'd say that it is a manual task but of course it can be automated every dns entries could be formed in uh in a api format and you could uh strike that api to change the dns entry and of course this could be automated totally but right now we are going to move forward with a little bit of manual interaction now let's talk about dns rebinding and i see push has already mentioned that there is something like dns rebinding so i literally just showed you what's dns rewinding so let's not talk about it okay and this is our talk this is the essence of our talk where um
will be showing the nsu binding so are you with me now because uh i think i maybe have moved too fast i'm not sure it took a lot less time than i expected but uh if you're with me right now just uh let me know because after this uh i have something uh exciting for you okay let me have a look at the chat real quick okay okay okay okay uh no questions as of now and uh moving forward live demo yes this could have some problems but uh bear with me i hope this works because live things not really work all the time let's take some rest sorry it's okay sir please go ahead
oh yeah sure uh so let's take some rest i mean uh literally let's take some rest take some rest well this is the website with my very poor development skills i have created just getting activated very less time i i have awesome development skills so this is the site and maybe uh the user on this side is browsing these uh videos over here they are moving forward with watching these videos and they're just spending time on this site nothing nothing fancy to see here on the left uh this is the attacker's screen so let me just do one thing i'll just log out from there and zoom in so you can see i'm assessing into a
server now this server is attackers server over here and uh something on the left has no relation whatsoever on the right so on the right this entire thing is declined but on the left this entire thing is the server now let's see how what we are going to change now first of all the attacker goes ahead and into this this is a very simple tool that i have created uh it's called dns rewinding tool and i'll share the source code and maybe go through the tool as well a little bit but uh let's see how this works and in action right now so first of all because it's a python tool i'll simply start activate the
virtual environment and um nothing fancy at all python3 and shell.y so we have a shell on attacker server it's waiting for the client and what's the clients doing nothing they're just browsing this website nothing fancy over here now moving forward to the domain name panel this is the panel that attacker has control over now see here i am doing it manually but it is totally possible that this entire operation could be automated when the user clicks on the website link so in a way this is a totally uh no interaction attack kind of thing users just have to go over to this website and then simply browse the site and meanwhile this shell over here is waiting for the
connection from the user after the dns rewinding takes place now as i said that dns um is a very uh not so simple protocol so it takes a while for the dns to propagate but if you do it correctly you might get lucky you might it might take uh sooner it might get a little while it might take a little while so the main important thing is that the user gets engaged on this website they are watching the videos or doing something now while the dns is propagating in the background uh let's uh have a look what i have done in the other window so these are the dns records and you can ignore all the records except this one
this is a techsound.rest right and this is my website address it used to have this ip address which is the correct legit ip address but after the user opened the site i changed it to a local ip address which is 192.168. that one that's one and then over here what is happening on the user's side if i simply uh open this uh uh this console here you can see lots of logs happening over here what's happening here i'm just showing this logs to show you that something is taking place in the background so what's happening is uh let's say let's say let's say that it uh yeah here you can see it says attempt field
and then after a while it says like there are lots of errors and uh something is happening and dns takes a little bit of time for rewind to take place so we are going to have to wait a bit meanwhile uh while we are waiting uh are there any questions in the chat uh we can uh do elevate those questions right now uh no questions are not there you have already resolved okay uh my thoughts then i should have watched it for this moment uh anyways this is the time where it gets a little bit awkward because you know you are too late and sometimes it takes a while uh sometimes it takes a few seconds
sometimes it takes more than that let's just try to save it over here again maybe i didn't save it properly and let's wait then we get the connection in the browser this is really bad okay because of lots of failed attempts it's be trying slowly now still failing oh with the sucks
okay okay okay okay shall we retry this procedure maybe maybe i should i'm not sure all right okay uh this tool automatically lowers the retry time it's not meant for instead oh there we go here you can see we have uploaded navigator and whatever injected so yes because dns rebinding time totally depends on whatever da uh how long the dns propagation takes so you want to make sure that the user is on this website they're interacting with this site and they're doing something on this website well right now it took around i don't know maybe two minutes or three minutes four minutes and when i was demoing on my user and it took me 50 seconds 60 seconds so it
really depends how the dns is behaving uh at that time so now we got a client that is connected so and we got a javascript shell what can we do with the shell well of course it's a javascript shell i can alert hi this is the most common thing and we get an alert hi wow that's it right no we already had access to this website we already could have alerted whatever we wanted this is not the point at all the point is uh that currently this site points to the internal ip address of the user so what we can do is uh uh this comes with a built-in uh function that i have written it's called
navigate you can navigate to whatever page you like so let's navigate to a page called slash that will be 192.168.1.1 and then i need to provide what request i want so this is a very dummy function i have get request to the home page now i could have post request to whatever page i want so basically we could take this navigate function and make it into a proxy so that user attacker would have a total access like uh like they are inside the user's computer they will have access like that they will have inside the uh users users browser session at that time so after i hit enter nothing really pops up here because uh
function went ahead if you want to see i i can just go ahead to the user section and show the uh console it says navigating to this and then it uploads to the uh server and then it says injected these are just logs these are not necessary at all i'm just showing you to explain what's happening and uh now we should have something at the uh uh at the server so let me just uh quickly open one more window here and i'll ssh to my server once again and this time i'll go to the dns rebin directory which was the directory i launched my launched my uh on this shelf from and then we have
some files in the logs directory now this creates some files like these sorry and these are the files that store the data that we just pressed so let's try to open this one well it it is not required that will hit the correct file always it's a really a demo thing so file names are kind of random you can say but you can totally uh convert it to into a live proxy that you will be able to access from the attacker's end so here i can simply use the e-links browser and use logcat.log and then try to open okay it's the same one let's try a different one oh yeah the file name is i mean the sizes are
same so these could be the same one and let's try this one there it has a different size and dividing took place and the time stamps here are kind of messed up because it's experimented with the server with the time stamps so sorry for that that's its remote aws instance okay it's also the same let's try it different one okay we have this one
let's try to inject it again probably we didn't get it at the first time and something should have happened over here and over here we have some files um let's try a file with different size let's try this one
here so on the attacker side you can see this is gpu and home gateway right so this is the router's home page usually any attacker would never be able to access your router's home page they would never be able to access anything on your local net network it could be hope it is rooters homepage because it's 192.168.1.1 it could very well have been a different ip address to a different device on the router side it could have been a raspberry pi or maybe what not and we have the username password fields over here this doesn't look very good because it's a command line it's like a command line browser so it looks like this but uh if i go ahead and from the
attacker's point this is the attacker's uh browser if i simply go to the url here and uh okay it's not right the same url here that we just test we can see it in all the uh css and however it looks from the user side so this is deep on home gateway this is accessible at this website that is from the attacker's endpoint and uh this was hosted in the user's home and this is something that uh you know that that's totally crazy so you would expect that while you are browsing a website while you are having some fun on that website that website would never be able to access your rooters login page that website would
never be able to access anything on your home network but guess what that is not a firewall that is something meant to get away with the ip exhaustion issue it's not a firewall at all anyone can access anything even if you are behind well ah you know like i'm really uh happy that the live demo worked properly because i had no idea if it would work let's uh let go let's go ahead and talk to a few things about dns over here now why did it take a lot of time for me to uh for the dns to propagate i mean it changed to 65 dot whatever service ip to one nine to one six here but it took
like five minutes here for the dns to propagate why because the ttl it's called time to live it's different than the ttl that's in the uh tcp packets is the dns dtl it denotes the time in seconds how much time is there until this dns cache will be invalidated at the uh whatever software is caching the dns it could be a browser it could be whatever the router or whatever there is so this is uh the ttl and the cloudflare provides me two minute five minute and these are really useless for me because waiting two minutes or five minutes is is this but if i had my own dns server i'm using cloudflare right now but you
could totally host your own dns server by let's uh buying dns so so let's talk about uh hosting around the installer a little bit uh so you could host your own dns server instead of cloud cloud share and while you are configuring your website doctor asks you to set the name servers to these addresses you will be setting their name servers to your own dns and you can install this bind software to you know like totally get away with this cloudflare you won't have cloudflare you will have bind installed on attacker's computer locally so there again there won't be any manual work because the attacker would simply ask the bind server to you know change the dns lower
the ttl time and reload simple as that so time to live will be very short and users the browser window will be hijacked as soon as possible right and uh regarding dns so these are the points and uh for the source code maybe we could uh dig deep into the source code how this uh this shell works over here if we have enough time but uh right now let's move forward with the presentation impact and protection so what could be impact of this we are just accessing users internal network well to be honest it's not just user's internet we have a lot of services exposed without an username or password without authentication at all in the internet
network so there could be anything that you could access for an example you know what uh if you have something bizarre example in your head feel free to drop that in chat maybe we could uh build up on that and make a tool for that explicitly as well but on the top of my head i can think that if user can access the router's home page well most of us don't really change the admin passwords it's usually admin admin or admin password they could simply log in if that's the case because that's the local network then they can move forward and find out your mac address well what can they do with the mac address
remember i told you about a site called site called wiggle.net it's a really awesome site what it does it maps mac addresses on the map so if you have a single map mac address that you have no idea of where it is located you can go over here and enter it uh in this field and then you can search and it will show you at which position on the map that mac address was last seen or was last recorded in wiggle so you could try this totally uh you could totally try this out and then you can pinpoint where your user came from well that's a really bad thing to happen but that's just stealing the mac address it's not a big
thing next what could you do well uh you can move forward and then you have access to rupert's admin panel right you could very well change the entire firmware of their router you could install something called ddrwt wrt sorry uh you can ddwrt and then it's a totally custom operating system for your router and they will be able to make a persistent connection from your router so even after the user is outside your website or outside anywhere the attacker would be able to access the site uh the uh the uh users uh uh users internal network plus so there are endless possibilities here i can't even think of what bizarre things an attacker can do
once they are inside your local network with the protection well of course file firewalls because i already told you nat is not a firewall it's not uh something to protect you it's simply something to solve a problem so install a firewall that could uh disallow domain names to change to a local ip address well what is an example of that firewall we have a no script plugin in firefox it claims that it would be able to do what i just said if some dns starts to pointing to a local address it will simply stop it but not most of us do that right now why did they talk about all of this about bypassing that and everything like
this i mean is this even relevant will this be relevant after a while well we have been using that for a long time and it is relevant because the attacker can simply access your internet network second point ipv6 is coming and slowly it will replace matted connections and every device will have an ipv6 network and then by default your internet exposed to the outside world unless you have a firewall rule set up and uh this is mostly it for my presentation i think we ended on time thank you very much if you want to look at the dns debian toolkit that i owed and beware this is a very very uh you know like uh
immature tool i wrote it in i don't know one day or two days or maybe less than that and the formatting is very bad so you could have a look at that tool and let me know if there could be any improvements you could certainly pull request it's totally open to it no problems at all and uh i see we have some questions in the chat right so let me just uh yes sir there are questions okay and uh okay let's let me start from the top here is does the attacker change the address manual or is it automated well as i already told you if you move forward i'm sure that cloudflare also provides you
an api using which you could simply do whatever i did manual and make it automated and if you want to take it one step further you can eliminate cloudflare totally you can install a bind name server or dns server and then you would be able to automate the entire process without using any api without using anything uh anything external it could be entirely attacker based attack and then we have can hackers steal local storage data like if any access token is stored there well now uh the point is in our attack the user was on this website right texan.rest and we bypassed the same origin policy this is the policy that disallows the browsers to access
for the websites to access data from a different website now in local storage if i had something stored on like this domain by default well i will already have access to it there is nothing to bypass if it's on a different domain name then i don't think you can bypass you can access it anyway at all because there are some things called host header protection as well in different domain and different websites but these things are not present in the local network so in most likelihood no you cannot do that and uh someone said this is a dna binding yes right it is pns rebinding this was the entire point of the talk uh the name of
this attack is dnsb binding and i have felt that is it it is a kind of an overlooked attack but at the same time it is a zero click attack if you say the user has to well not zero click one click attack user has to click on one url that you send them that that is this website and they just have to be on that website they don't really have to browse it they could browse it but they just have to be on that site and after that everything is done at the attacker's end and we have shortcoming of maths and i guess there these were the questions that i had in chat thank you very much for
having me so uh one thing i think you can take over now yes sir okay so thank you sir for clearing the topic in such a depth i sincerely appreciate your gracious presence and the whole team is thankful for that uh now it is time for the giveaway question i request everyone to open the google form link in the chat box and attempt the questions top three people will be getting three pair of stickers from this slot so thank you again sir for being a part of this session this conference and we hope to see you next year soon okay offline and not in this online home run i wish i will be there with some uh
different like uh attack next time and right now i thought i think there is something on the chat it says as we have the jsl can be escalated like we do with other js based attacks um it's a sorry harmony i pronounced that right along uh please go ahead and have a look at this url that i have provided over here and you can explore whatever you want inside this shell and you can have a look at how this uh shell works at the attackers and what is it i think i think these this is it so um
[Music]
uh
[Music] do [Music] this [Music]
the one
[Music]
[Music] bye foreign
[Music]
food [Music] the one
[Music]
do [Music] so [Music]
[Music] do [Music]
welcome back everyone due to some urgency our final guest mr sanjeev multani i'm sorry mr abhinav jain is unable to connect with us so we have decided to wrap up the session early now that we are heading towards the end of session uh 2021 besides noida conference i would like to express my heartfelt gratitude towards the speakers our sponsors the viewers and the whole team for making it a successful event i also thank the team for considering male is eligible enough to be a part of the process and adding some value to the whole event i would also like to thank everyone who supported this event by any means someone has rightly said and i hope if
you continue to think the way you've always thought you'll continue to get what you've always got i uncode on that note i called thank you all and wish you a very happy independence day [Music] so [Music] do [Music] foreign
[Music] [Music]
[Music]
you