New Era of Telecom Hacking

Show transcript [en]
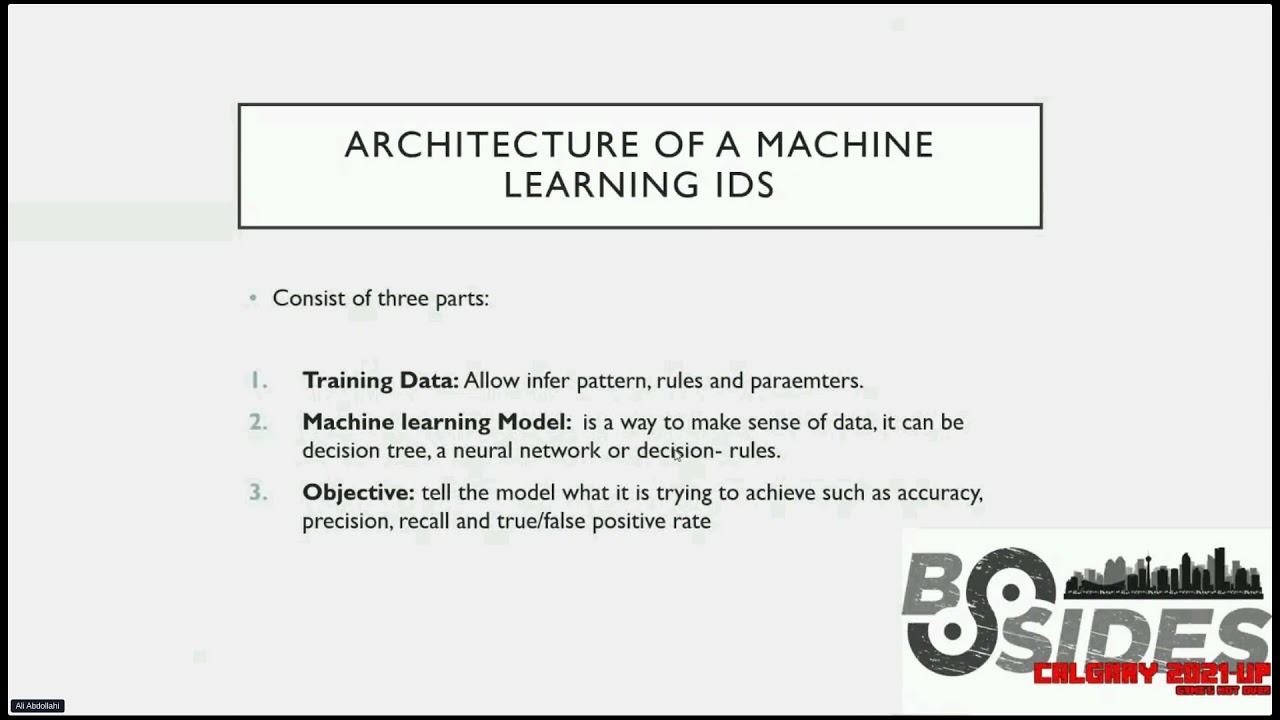
hello my wonderful audience hope you're great safe and ready uh today i intend to talk about something new in uh field of telecom hacking um it's really really hard for security experts telecom engineers and mobile operators to deal with signaling and telecom attacks so why it's hard the answer is because telco networks are complex and includes many segments like radio signaling ip backbones i.t packet data etc so in this talk i don't want to talk about basic and traditional tags uh i just want to illustrate how we can break into a hardened telco infrastructure while they are using security devices first of all i want to introduce myself i am ali a cyber security searcher
focusing on all aspects of offensive more than eight years um other books articles as well also i'm regular speaker and trainer at in international conferences holding massive computer science and many international certificates and i'm working as a bug hunter
so according to the news as you can see in this slide many fraud and other types of cyber incidents have occurred in um past several years while they are they are using telecom and mobile infrastructure in top left corner you can see that malfactors exploit ss7 network to inject a malware to attack on financial companies and banks and in other news on the left side you can see that uh hackers targeted uk metro bank through ss7 and on the right side there is a news regarding to vulnerabilities in mobile networks in united states
in this slide i divided all possible attacks and vulnerabilities in telecommunication first is a subscriber profile data leakage the second one is network and nodes data leakage third one is tracking mobile subscribers and breaking their privacy next one is sniffing spoofing fraud like um transferring money using ussd operations or making free call or cheap calls as well okay uh for those who has no enough background of mobile network here's the architecture of a mobile operator each mno or mobile network operator has three main segments include radio access network ran which responsible for all audio and basement communications like your connectivity from your handset or mobile phone to the tower circuit search network cs network handles your voice and sms
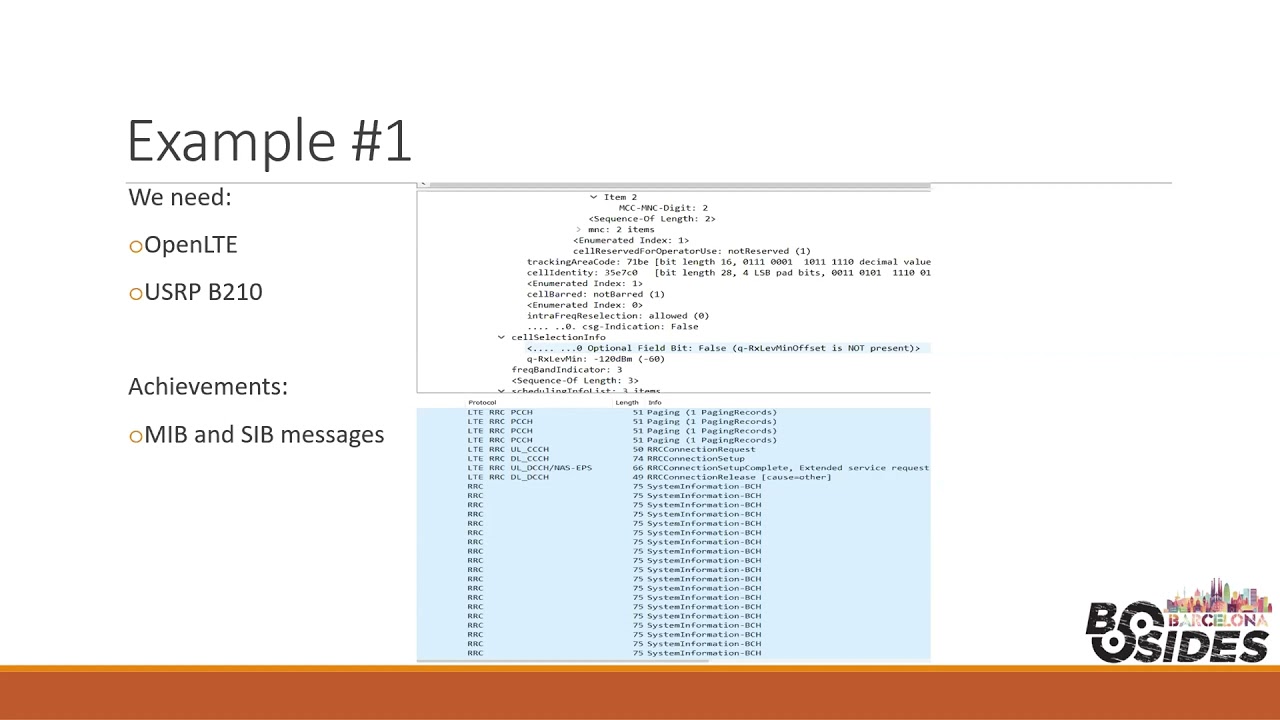
and packet network is responsible to bring your internet connections and data security in radio access networks okay uh mostly there are three types of security mechanism in radio access network first is phone registration or any kind of policies for your hardware and imei second is enabling ciphering algorithms to fight against interception and men in the middle third item is using only lte and lte advanced infrastructure instead of traditional mobile core networks in 2g and 3d so now we want to review the high level architecture of ran or ride your net access network in radio access networks we have cell tower bts in 2g node b in 3g and e node b or evolved node b in 4g lte
you can see that e nodes b passing your traffic to ps and cs network packet switch and circuit switch networks based on the traffic type if you want internet your traffic will go through ps network and if you want to make a call or send a sms the traffic will go through cs network and uh why using imei policy to fight against phone smuggling lawful and security monitoring tracking stolen devices and criminals um okay now with the help of motorola c uh 150 and uh 118 and osmocom bb software we can set an invalid or fake or even duplicate imei and set up a call to test network reactions you can see that i set my i said
my imei to all zero so that's an invalid imei and now so according to the screenshot here uh network sends identity request to my phone and the type of identity was imei you can see here and and i replied to it using an invalid imei set to all zero so the network is wonderful so the network accepted my invalid imei because ciphering procedures completed and this is the imei policy bypass here because net mobile radio network and the whole operator network accepted uh my phone with me as a subscribers mobile subscriber with an invalid imei okay so uh there are some types of ciphering keys like kc srs and rand or random number in radio
access networks which harden the radio network to avoid active sniffing and they always store in hlr or hss in core network so hss or hlr as a subscriber database has a component called auc or authentication center which um responsible for ciphering and authentication procedures to bypass and get these information we are going to uh targeting aoc or authentication uh center in hlr hss by abusing ss7 and signaling access as a roaming partner
and as you can see i sent a malicious ss7 map or mobile application part s-a-i or send authentication info to targeted core network from ss7 network to retrieve ciphering info and the network respond me via rand stress and kc values in clear text that's amazing so another security mechanism is using uh lte and lte advanced uh to bring uh highest quality and performance uh having more security and privacy in core and radio segments and other factors like voice over lt or volte or flexibility etc okay guys let's review bypassing method here totally uh there is a general way here downgrading subscribers to try additional technologies like 3g and 2d which uh which are vulnerable to many attacks
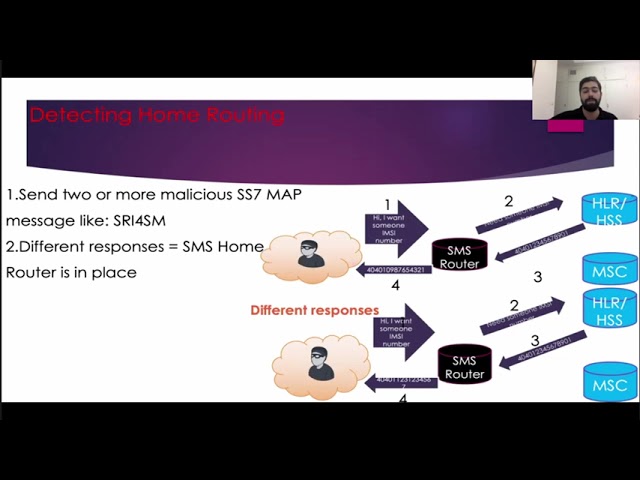
like men in the middle to perform downgrading we need to use a signal jammer security in circuit switch network or cs core network using sms home routing is the first uh item and the second one is signaling fireballs so uh home routing act as a proxy and the definition of a home router is hot to hiding uh subscriber mc number which is very valuable information um to perform hacking scenarios from um from a hacker or malfactor perspective as you can see a hacker requested to receive emc from hlr or hss and the hlr hss respond with a real value however home router change the value with a fake one
so how we can detect if home routing is enabled or not uh just need to send two or more malicious ss7 message like send writing info for sm or sre for sm that's easy if we received different responses it means that sms home routine is in place in our targeting uh in our targeted operator uh i'm writing bypass uh in telecom networks we have uh three types of duties or global title which act as ip address ms istn or your phone number consists of mcc or mobile country code ndc and sn mc number consists of mcc mnc mobile network code and msin and mgt consists of mcc ndc and msin so as you can see hacker can abuse mgt
number and a valid random mc number to request other information regarding to targeted mobile number and it's real easy
uh signaling fireball okay uh mobile operators use uh signaling firewalls uh to protect their signaling infrastructure signal packet inspection filtering white and blacklisting
signaling firewall bypass to bypass these kind of variables we need uh just to playing with tcap so what is tcap tcap is a ss7 sub protocol and it's like tcp you can see a wire shark a screenshot from my wireshark here that this is um transaction capabilities application part or tcap tcap begin message and tcap and message so um okay to uh to perform bypassing we need to remove application context name from tcap or sending double operation message let's get into it uh removing app contact's name from tcap message uh okay to start the procedure we need to remove dialog request section from our malicious ss7 message then there will not app context name to point to malicious ss7
map message you can see here
so sending double operation message most of signaling firewall block or accept a message based on message type so each signaling message has its own op code or operation code and it's a vital number in this screenshot you can see sr4sm and it's related up code here so um cord according to the picture hacker is trying to put a legitimate ss7 message to opcode in the first step and then put a malicious ss7 message so signaling firewall will check just the first operation code which is pointing to a legitimate operation and you can see here that the cs code nodes and functions uh respond with the real number and signaling firewall uh will check checked the
first operation so and signaling fireball thinks that it seems legitimate s7 message so the hacker bypass signal fire roll and will retrieve the real number or any information that's a hacker wants to receive from the core network
like here so here that's that's it that the subscribermc or a network information received by hacker here okay so uh solutions uh first and important thing is uh hardening the devices protocols and communications based on industrial standards like 3gpp etsy etc using firewall or if you are using signaling firewall already you can um fine-tune and optimize it a t-suck or telecom uh security operation center is highly recommended periodic assessments and audits are necessary and training and security awareness are very useful thank you folks for your attention and you can stay in touch with me uh sharing knowledge and experience together and finding more friends stay safe and healthy