BSidesNcl 2021 From the living room to the boss' office: IoT aka. The bane of InfoSec Nicolas Boeckh
Show transcript [en]
let's get started um this is a routine specifically to security titled from the living room to the boss's office which if you listen to the keynote like this you may have understanding that it is not a fantastic thing iot is quite a complication to the information security landscape um so that's why sometimes some people go over and call it uh
i am a swiss student um a master's degree in systems and computer services um [Music] and so directly kind of going right in uh if you wanted a very long and formal definition of it you could probably go for this uh but we don't care about this uh for melanie as you know that's academic right let's go with the internet of things that's what it means and uh what is it exactly it's a device or a group of devices that are going to speak to others or to others of the same type or to systems that are supposed to control them and it's the general definition for it also things smart launches smart bridges uh
smartphones everything with the words in front of it um basically and other additional things the current state of iot in the world is that depending on who you ask there's between 17 million iot devices and 50 million iot devices the reason for the difference is what people qualify as an iot device so if we count every type of different connected device then it's pretty good and that is what
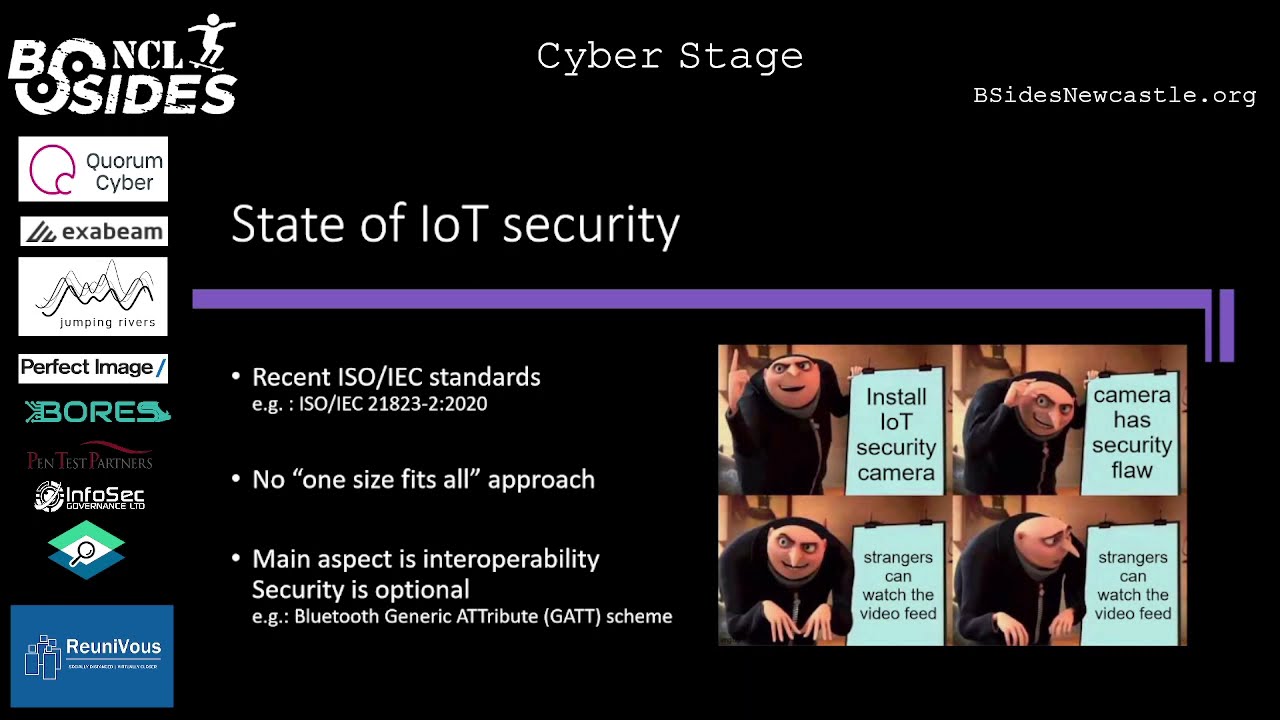
kind of you know it's pervasively everywhere and yeah that's something we have to deal with now as an industry um so it also does have a certain technological web from your young hardware implementation so whether or not you're going off of your own circuit boards or an integrated circuits or if you're basing yourself off an fstm32 board or an arduino board or something of sorts um it doesn't have a certain transmission technology with so you could also be transmitting using cellular networks bluetooth energy long-range rf rfid various other types of nfc networks and so yeah that's something we also have to deal with um now there's a fun joke about the state of iot security uh you may have noticed
uh once again in the keynote that there was [Music] we're not exactly there anymore but we're also nowhere near to a comprehensive security all right so yeah uh we've had a few iso iec standards popped up recently uh as recently as 2020 so last year uh iso ic 21823-2 for example uh speaks about the transport of iot systems so we're at least getting somewhere right but there's no one size fits all approach mostly because devices are there for every type of circumstance they're used for everything one of the main aspects of the iot is the interoperability of devices if you have analyzed a specific type let's say a wireless mouse and you have a computer or
a smart tv in theory they should be able to speak to each other without an issue the problem would be then the interpretation which would then require a driver so it's possible and they can communicate the interpretation of the communication might feel problematic uh one of the things that is used for example bluetooth is the bluetooth gas scheme which is a generic attribute or divides
[Music]
characteristic
so that's one of the things um now one of the the four problems that i achieved is sometimes the human is left out of the equation so how do we make decisions more accurately how does iot devices make decisions for us well there's the the usual is this than um where you know if something happened then have an array of consequences that's pretty much how it works there's the human touch which is you know when [Music] people which may or may not be the people being affected by these devices actually uh press a button and make the devices do something and then there's the very uh not at all over talked uh concept of machine learning and artificial
intelligence which yeah it's there i'm not going to talk about it because um so what are we going to be talking about uh we're going to be seeing uh the breadth of my auntie and what uh how hard it is to be a baddie and then uh basically the three letter agency recommendations on iot secured and we'll see how those recommendations are a little bit more um so yeah starting off with uh iot in the world uh so we're going to be going over various concepts of let's say iot deployments but it's not just one device it's a fleet of devices of different types that are interacting and we're basically going to go over these various interactions and
how they work so one of the examples of the home automation like i mentioned you have a range of energy devices iut maple devices and homes such as turbostats an oven for example for a bit crazy shutters doorbell cameras door locks in your air conditioning unit fireplace all those kinds of things and you also have iot and physical security systems such as surveillance systems that survive secure your vulnerable buildings um [Music] you also have various monitoring systems you have access control systems for example once again surveillance cameras you have tourniquets you have bad traders control um and all of these things can be programmed and interconnected in such a way that uh it isn't at the level of the device that
the decision is being made another uh interesting usage reality would be environment control and by an environmentally controlled meaning controlling an environment but to control the values coming out of the environment for example so imagine a carbon monoxide detector which has the ability to start your ac should the carbon monoxide levels be too high or just send you an alert that would be a pretty interesting application for that what other implications we have for this we would have okay so carbon monoxide carbon dioxide ozone no3 greenhouse gases water pollutants we can kind of use them everywhere a lot of iot systems kind of were injected in sewers recently uh that made of code because there was an
attempt if um [Music] well excrement could give an idea of whether or not a certain amount of population had a higher amount of code right and if we can see that it's a network so that's maybe not the nicest description or nice thing that could happen but it's one of the things we should talk about um other settings would be investment studies for example using a distributed control system to control observe and report on various things happening in an industrial site um we would also have you know an industrial cycle that factory runs kind of uh let's say vehicles could have robots you know the main idea is also to keep the humans safe [Music]
and yeah so all these devices should first of all not auto destruct but second of all not hurting other people that's a pretty important point uh one interesting part of about which you know everyone talks about it
um so yeah it's remote controlled um sexual devices uh so that reference was from the pentax partners um they had a pretty fun article about a chastity cage that they just over wrote and now that you know [Music] your problem to the people in them so yeah exposure to the individual's body parts that's pretty much interesting um and yeah so these devices might make you go with safe that's pretty much where there was a big boom in the industry um but yeah you might be catching another viral load other usages would be a minute of course would be death uh depending on the img device so i do put the reference in here but there is someone who have their
pacemaker imagine someone else happening in their
how often do you move how much energy there is of their breathing is but you could also do this from a distance like you instead of having someone under observation at the hospital you have someone being at home being monogamous so that's pretty that actually which liberates always nice especially in the current conditions so yeah we could talk about sleep monitoring devices vital signs temperature monitoring devices all those kinds of things and also pacemakers and insulin plus because that's kind of where it's uh so yeah discussing iot devices that interconnect in various settings i kind of want to touch base on maybe a home automation process and industrial automation ecosystems uh because although they are absolutely
dissimilar they actually have a lot of resemblances in how they interact with the world so i'm going to look at that um home automation yeah so uh but everything kind of starts with an iot club right you usually have an iot of either it's one led device connected to your phone which then goes via either an iot hub that is outside of your network or it's one that's inside of your network and that's one of the
because you want to pay less less for your electricity well uh you would have absorbent potentially attached to a smart meter both of these could send uh information to the iot so how much energy am i producing how much energy am i consuming um another thing could be a thermostat which controls the ac both of these things can have values that are sent to the id hub such as hey what's the temperature what's the air pressure what's the humidity and then you see yeah we cycle this much air or we cool down the temperature by this much and that was people that are a little bit uh stringent and or maybe curious to make a ton of math or just
see how ones were at their house um but if they could use potentially an air filtration systems which you know something fun another concept would be for example if you use a location type system on your phone that is linked to wherever it could be hey i haven't been home for the last two days i'm in a country maybe stop turning on the water or whatever every night that we conserve energy and the environment always nice other systems and a lot of maintenance so once again iot which then links to a router uh which at some point links to the internet that's nice and let's say that you have devices on your network such as a motion sensor or
surveillance camera so if you're on your local network right you eventually have a device that allows you to view the camera speeds so you can either be a camera like you know computer with the raw software could be an actual uh camera you know rig uh it could be a ton of things but what happens when you have like the detection yeah you have something that's detected and at some at some point you want to alert the user right because hey it's either the mailman or it's wrong it's people wanting to shoot you down and all night i'm trying to make this talk as international as possible this doesn't [Music]
you could do something that could deter the one of the bird worse or intruders or postmen um so usually for a host you'd have a dollar right but no um there you could just turn on lines or turn to give the potential intruder the impression that there's someone there and on the other end you could also have like a cloud storage or a local storage
[Music] is the person this is their license plate i can go and say hey there's this issue so yeah there's that and you know from the phone you would be able to use this footage on your uh cloud storage device [Music]
so you have all your devices uh they all communicate with the achievement and the decisions are made outside of your open network so yeah you can get the feeds of your camera your detection
and one of the good things with that is that it's easier to add yourself on the outside as well which some people like to have um um
[Music] this is where i fictitiously lived this is not where i actually live uh this is where i work maybe and this is uh a shop so yeah uh red is a shop herb was work and work just wherever let's say i'm leaving so i'm exiting a radius around my home one thing that could be done would be me having a smart oven hooked up to my router right [Music]
well maybe it would be a good idea if i informed my home network that hey maybe just for seattle to be off just to be safe pretty interesting um similar problem is
well let's say that um this evening i want to eat church or chicken or pizza or something and that requires the oven to be on or at least preheated now i know it's going to take about 40 minutes to get the workshop so i could from my phone and say hey preheat the other that could be interesting that's also one of the use cases for us um
what's missing in the fridge today forget any eggs today drink too much orange juice
but it's useless um another use case would be then more in the industrial construction site let's say you have a few devices let's say in this case uh excavators right then you have a few trucks because you need to move the stuff that you excavate somewhere else which is where you use those trucks well let's say you have a system for fleet management
[Music] so you also have some people which is not constructions but uh can assume they are working uh so you have a form of hub that also lives with human and material logistics how many people do i have how many people do i have to pay how many hours are being done who can i assign where to do what tasks depending on what their job is are they electricians or are they uh plumbers or are they heating experts things like that and also what materials do they need [Music]
[Music] now of course you would have some form of local management that could potentially prioritize various tax that's an option and retriggers them and those two would also communicate because hey you might need a worker to drive an excavator that makes a power sensor you need to be able to track the way when it breaks so that you can send it to the shop things like that there's a lot of things
[Music]
[Music]
[Music]
those people that are going to start the procedures to implement these you know networks because someone sold the most so they're getting the full benefit of it other people um another thing that's great one of the construction sites that has been kind of getting in place in the last two or three years is uh for example a worker carries mentioned made out of glasses and uh he's thinking they're digging their tongue right and what instead of hitting let's say a water pipe or something because they dug in 10 inches too deep or something oh they have it laid out and you know the layout of the pipe that is starting to exist now maybe didn't make this ten years ago if
it's starting to snap and that's at least some of the let's say uh more interesting uses for it at least from uh could also be like hey there's these electrical networks where this is the setup for electrical networks or hey we've seen this thing move since yesterday rather than could be an infantry system as well
[Music]
not exactly how to compromise spices but the technologies that are there that are let's say vulnerable to compromise most of the time so one of your attack factors would be at least on the hardware side it would be your uh you know your inter-integrated circuit protocol so itc that's a communication protocol between all your various components right um one of the fun things you can do with this is compromise the ack values which then draws what's going on on the scl one of the things you can do with that is you can trick a device not to respond or an interceptor to something about the response and then the movement will continue for example let's say you have some machinery robot
right and it's dependent on the ecga to say hey if i did a cycle of uh moving then the motor has moved that's fine now i'm going to stop them i'm going to start moving again [Music]
various things that you can do with um like a whoa let's say anything that uses an engine and software hardware um one of the consequences would be machinery damage that's a perfectly viable consequence um another factor would be the serial portfolio interface so that's pl where you could read the clock speed and the data screen so if you're sending data from one device to another let's say i don't know um a pacemaker so you have one company that's sending me the two other components so let's say the
[Music] right and you want to sabotage that so that in order to make the hey i'm getting this and i'm going to attach a new device to then inject some newer things of course it's not really feasible because we need to access that pacemaker but you could compromise it ahead of before it's implemented you could do various things like that one of the other things you can do however is get some information so from devices that are communicating let's say you have various sensors on the device those devices pull some data in in your main hub basically and are that sending into a competent communications component let's say a energy component but if you can let's
say intercept the feed at that moment you know all the data that is going to be sent you can also potentially extract the firmware of the device um another uh compromise vector or attachment would be uh that you were in a uer teaches as a universal segment um it's basically a hardware communication protocol from a device to the device and most of the time once we have this you have two devices that present the same reports and they will communicate to each other and that's you know using uart products and there you can you know intercept the communication and if you're being very very very very lucky and you're attacking something that actually has a
linux system on it you could potentially call a shell that's one of the things that you could do potentially on a router that's one of the examples here um what could be easier of course most of these things require you to have physical access so it would usually something you do in order to find a program find out where the device is coming home to things like that so yeah however other things that are being used
so you could uh you know use the generic attribute profile no generic access or the generic attribute system so you could potentially right uh read write on any characteristics so the characteristics like i mentioned earlier is let's say a segment of your entire band which is then reserved for push-pull updates or just full updates or notifications or things like that and one of the things you can see here is um so i'm compromising a 360 smartphone with a replay attack so they identify what is being sent and then they just resend it to the lock it still unlocks so it's things like that and so what can you do with that you can place some information of course a lot
of things go bluetooth nowadays too many things over bluetooth nowadays um you can potentially blue jack some kind of you know exchange um you know in person one of the members of the exchange and all of this is due to a lack of not understanding but of the implementation of various systems or procedures or things that you can do with a bluetooth such as secure pairing that there exists with you just very few devices actually do it it's getting better but it's been getting better actually right um another attack factor would be the endpoint let's say the device is connecting to a phone and the phone is contacting an end point to [Music]
um but you can also find some binaries like i mentioned before for both so um once again you know at definitely said they managed to download the binaries for the app that would then connect to
i guess um so what are the possible consequences you can spy on people if you have access to your cameras right you can set apartments that's actually one of the things that happens the most frequently nowadays it's less about compromising these network itself than having a staging area for botnet or having x devices be a part of a bot it's yeah uh you can also have some eventual package by prevention uh first date advice for a first-name person um [Music]
you could potentially access it maybe uh you could potentially gain physical aggression into the place like if you managed to compromise a smartphone reader an rfid battery or things like that bit over a few um that happened in history already for example the hickory deadpool it's a deadpool that you put on a door and basically you could compromise that that bolt via the mobile monitor because it was storing the credentials and an unencrypted database on the phone um so yeah it's uh the ethernet bridge that would bridge you know your that bolt to your network uh was also communicating uh you know amputee in an unencrypted fashion so you would have potentially
[Music] you know you could extract the logs and then find diversity right uh moving on to everyone's favorite company amazon that's a joke um [Music] the ring doorbell uh an attacker who was already on the network could potentially view video and audio coverage and of course attackers being on the network is already bad so you're already pretty much screwed imagine you have a physical piece of something that's save
so [Music]
to communicate between the devices that sounds fantastic um until you realize that they were doing this by having the device be a basically small wi-fi router with a constant uh wi-fi ssid uh which is pet chat um and you can basically track them using wiggle or other services uh not in real time but you can still and also another thing you're going to do is you could basically put yourself there and send messages which were pre-programmed messages to uh children but one of those pre-programmed messages plus media outside um which needless to say if you know your child and you get that and it's coming from a trusted source um you're going to do and if interested
sources number or something else it is um another example would be a child tracking launch hey um never too much to track one shot but could go wrong so that's one of the
and what happens is when you go and create this status location of that watch it does is it just requests your server and says hey i have this id send me a location back and okay that sounds funny well until you realize the researchers realized that they could just change the id and since they were logged in as a registered person they could also get the location for tens of thousands or hundreds of thousands of other children which is not good at all uh so yeah that's a case of uh you know sufficient yeah yeah it's a little bit of a comment um so i kind of said that at the beginning of the three letter agencies
recommendations well um yeah so first of all who are the three letter agencies that we're talking about let's start with the one that doesn't have three letters an isa uh it's the eu cyber security agency um it's an organism that publishes recommendations pretty actively um it's been active since 2005 and those forums and conferences uh an actual three letter it continued would be the nsa the us national security agency there are everyone's friends um they also public recommendations nervous the cyber security infrastructure and security agency publish recommendations and they try to be the glue between infrastructure corporations and individuals or corporations and cyber security it kind of works a few vulnerable mentions could be minor
so they manage federally funded research and development centers uh to support various us government agencies uh there's the national institute of hundreds of technology where they kind of propose standards which do include several security standards in the uk there's the information commissioner's office they are an independent regulatory office to ensure national data protection and in france
recommendations um that's kind of uh something that makes our iot team say oh yeah we live in a society where iot deaf teams they live in a society and sadly enough the number for emergency services society would be eight nine nine nine eight eight one nine nine nine one one nine seven two five three um which is a reference and if you didn't get it um one of those uh recommendations would be uh the frequent security test so you know it's an aspect of security by design it's one of those very modern things included in the shift left mentality which is putting security you know not in the last phases of development but more during the
requirements phases which is very good and it's one of the things to consider when we recommend you know frequent security testing is that it's not always the same company and person that is able to do these tests it's you need to consider diversity and externalization of this uh because otherwise people might get cozy in doing the exact same tests and getting the same exact amount of money at the end without you know testing anything naturally new um so yeah that's that's something security storage transit and kind of in math so in the calculations you're going to do it's to avoid using specimen proprietary solutions but rather relying on community and you know scientifically verified solutions
uh using encryption in transit and at rest for critical data so for example transport layer security with a perfect forward secrecy would be one of the recommendations having a certain signature for content and verifying that signature matches at the end very important and then using unique keys for any type of exchanges on the hardware from our software side over there update capability just make your devices updated please having a hardware that's specifically there for security such as uh components that are going to enable you to have a hardware word of trust quite important uh automatic firmware updates should be an option and those updates should be backwards [Music]
allowing you to avoid the code tampered with another aspect would be safer by default um i think so you know oh yeah top five recommendations for cyber security i know that's a little bit ridiculous um one of those concepts would be the principle of police privilege so all your users have i can do the minimum responsible to do whatever they're going to do all your processes follow the same rules they only have the amount of access they need they do uh having device passwords that have individual passwords such as not being a smart tv with a password as one one one one two to two um as a developer and password that existed i don't remember the company but it's
just as good i don't remember living if you have default passwords make them have to be changed and then you know also enable mfa and you know from passwords things like that and last recommendation would be uh live every day as if you were going to be audited next so record everything preserve logs on some form of storage have monitoring uh periods where you need to monitor you know what's going on to determine when there's something going not right and then perform your auditing if it's not an audit from another company or you're being modded
so as i'm closing in on time uh what are the conclusions so one of the things that i did um saying is that uh this would be from the you know from home to uh the boston office except i don't
the only thing that is going to change is the environment in which these devices are placed if the device itself is vulnerable but it's incorporated environment that is let's say shielding itself from all the iot devices on it or as you know segregating them then it's the devices might have the same issues but they're not going to be exploitable the same way uh all these recommendations have limitations because not everyone does an iot company can actually deal with doing all the recommendations i mean to be frankly a nice recommendations where i would use memory security there's about uh 47 pages and that's in very small forms and there's about 100 of them so yeah there's a huge volume of iot devices
out there just hilariously really huge and they're also very cheap which means that it's actually quite easier to just ship out a new device with a new patch and say hey mine right so yeah this talk is uh under a cc by essay so just use it whenever and yeah reach me anywhere here have made it on time yay





