BSidesCharm 2024 - Defenders can use ATT&CK! Oh really? - Lex Crumpton
Show transcript [en]
[Music] welcome aboard flight attack your non-stop service from vulnerability City to defense Fortress please fasten your seat belts as we take off for the heart of cyber adversaries tactics techniques and procedures I will be your flight attendant today my name is Lex I'm a cyber security engineer of socks and blue teams at merer I've been there for almost 3ish years previous to that I was at the dod I was an exploitation developer digital forensic analyst and for Hunter so I've had experience in both offensive and defensive sides I I've spanned the gambut by now I am a DMV native born in DC raised in Maryland I've been here my whole entire life I've never left right and I'm an avid lover
of behavior analysis I feel like at the TTP level which is the top of the Pyramid of pain is very pivotal for Defenders so that we can help like bolster our defensiv and try to get ahead of the adversary hopefully one day so let's go over some pre-flight checks first what is miter attack miter attack is the knowledge base of adversary behaviors it is that it's a model to help you learn what happens when an adversary tries to get in what happens when they've gotten in and what do they do after they've gotten in some key points it is it's based on real world ad observations sorry there's no proof of Concepts everything that's in
attack is based on what I've seen in the live real time from people who have seeing it dayto day it is free open and globally accessible we want everybody to use it students organizations you on everyday basis we want you to see what's going on and this is in line with mit's public interest mission right and because it's open source it's a common language for everybody to use let's say back in the day one company was talking in one language another company's talking in another language and they just did not understand it was not effective so miter Tac tries to bring that goal together of like helping people talk in the same language that everybody can understand
and everybody can do a good job at a good job do a good job at their dayto they work it is also Community Driven right our our mission is driven by people who give us information so that we can put into this framework so if you see something and we don't have it contribute it back to us it comes directly to me right so that we can put it in and we can help evolve and enhance this framework moving forward Defenders typically have a lot of questions so miter attack is very known for their offensive side their red side which is the technique description and then the CTI side which is their reporting that gets contributed back to
us all the references that we get in attack itself so where is the defensive side like where do we live within this framework we have questions about how we can use attack how do we make defensive recommendations back to our company what sensors and tools can we utilize to help collect this data what data are we collecting right what behaviors are important to us and so we're going to go through some of these questions and answer some of these questions by the key features are on attack based in the defensive section we've come up with a six-step process and I'm going to call them our stops for today because we're on a flight right but our six-step process on
how we can get to that end goal or that end destination of making defensive recommendations we have determined prioritizing which techniques are important to you researching those techniques researching defensive options that are open to you uh what are the capabilities and constraints of that organization that you're trying to make defensive recommendations for some trade-offs that you have to consider when getting to that point and then ultimately the end goal of making those defensive recommendations so first when you're trying to prioritize which techniques are important to you you want to think about the Red Team Tools CTI or cyber threat intelligence um how are you're collecting the data for your organization what tools the adversary is
using and any other other things surrounding that that's going to be your first step in saying what should I be looking at next we're going to get to our first stop or our first step and researching those techniques based off of how you prioritized it in this example we're going to look at CTI reporting we saw ap39 was using spear fishing emails with malicious attachment and or a hyperlink so we have some key pivot Points in here we have spear fishing we have emails we have a a miter attack technique which is t204 we have malicious link malicious attachment and we have ap39 and cobut kitty there's a lot of key words in here that we can pivot from as a
Defender so let's go through some of the things that you can do with attack and once you get all of this information you're going to go to attack you're going to go to the right side of the page you're going to see a search bar you're going to type in some of those keywords that we just went over user execution t124 spear fishing uh malicious attachment malicious Link in this incent I'm going to research t204 and it's going to bring me to user execution at the top of the page you're going to see that adversary description explaining what this technique is all about but if you scroll down a little bit you're going to see
this procedure section and it's going to give you some softwares and groups that have also utilized the same technique and what do they do when they use it use this technique you see these red lines here that explain like hey ABT 32 33 and 39 all use this technique black Tech cobot group all use use the same similar technique where they're using emails containing a malicious link containing a malicious attachment and trying to do something dirty to your system this is important information we found our key technique that we want to prioritize for our information so let's figure out what other options that we can do so that we can make a defensive recommendation to our organization to
say you need to be worried about this and our next step we're going to go over some research and we're going to research some defensive options miter attack has defensive options that you can look at we have our detections our data sources cyber analytics and mitigations so detections is like our highle overview of detection strategies that explain what the adversary behavior is doing and then you have the data source level because detection is a little high high overview level data sources is like the in-depth level of collecting logs and sensor information that explains what that behavior is what type of a behavior that is um outside of data sources there is a subcomponent so there's data components it's the
activity action or metadata of that information you just collected so let's say and we'll get into example actually I'll wait for that um cyber analytics is going to be your ml version of detection queries you say you found the adversary you found this bad activity and you did it by hand next time you don't want to do it all by hand again you want it to to be automated so that's where your cyber analytics are going to come in there are going to be detection queries you can put into this uh stem this this tool to help you find that activity faster and then lastly mitigations it's going to be your configurations and other like security controls that going
to help prevent this this technique from moving forward so those are four important areas in attack that's already there free and opos source for you guys to utilize so let's go back to our example we had t204 user execution we're trying to stop a user from executing a malicious link or or downloading a malicious file because they got it from a spear fishing email right when you scroll down the page a little bit more you're going to pass procedures you're going to pass medications for a second we're going to go back in a second but you're going to see this detection section when you think about spear fishing and you think about something being downloaded what
happens on a computer it's going to create a file so our data source which is something we're going to collect is when we look for file monitoring that's important from the data component level we're going to look for the creation of that file and so here you'll see you have file creation for this detection this that's your first start you're going to read this open text area that's going to say what are we actually looking for we're looking for a newly constructed file that was downloaded easy peasy or so you thought something that we've included into attack more recently is including including what where you're going to collect this data from what SIM is going to do what your
sensors you're going to look at um what actual event IDs that you need to be worried about and so you'll see in the second red line we say hey use cismon event ID 11 that's going to be your file creation cismon is openly free accessible to everybody to use for your organization so that's why we have it here because everybody can use it remember we're free and open source and then from the analytic perspective we've given you an example of how you can create this detection career moving forward for your organization for our spirit fishing AML this is not so much the the right example but you get an idea you're going to use your um analytic to look for a
file that was written to system 32 theoretically this is going to work right you're going to look for a dobat script file that was downloaded to your system you're going to utilize your cismon um sensor tool that we mentioned earlier and we're going to look for vent event Code 11 which is your file creation this is how you structure your detection queries or the start of your analytics so that you can put it into your sim okay so that was a good example for the first three what about mitigations attack has mitigations all right here for you guys right so for mitigations for user execution you got execution prevention non reconstrution prevention use your training telling your people not to
collect the malicious link guys okay I I've been in I've been in tech for 10 years how are we still clicking the just like if it looks Shady don't click it it's just that easy but we got to tell you guys right so use your training training your people not to clict the malicious link so that you don't get this malicious download okay again attack has both mitigations detections data sources and cyber analytics to tell you all these things so it makes your your day easier so that was our stop two doing research on the defensive options I gave you all the answers we're going to go to step three when we're look at the
capabilities and constraints of your organization you're trying to make those defensive recommendations for consider your collection your deployment and your response let's say your organization already has cismon for a collection Source easy peasy you have the data source that you're looking for so you don't have to really do anything new possibly new analytics I just showed you how to look for a file in system 32 for a b script can you add that to your organization it's an easy win looking at the deployment are these are these products already deployed in your system or do you need to consider something new sysmon is a little TDS where you have to do it on hand on Prem but maybe you want
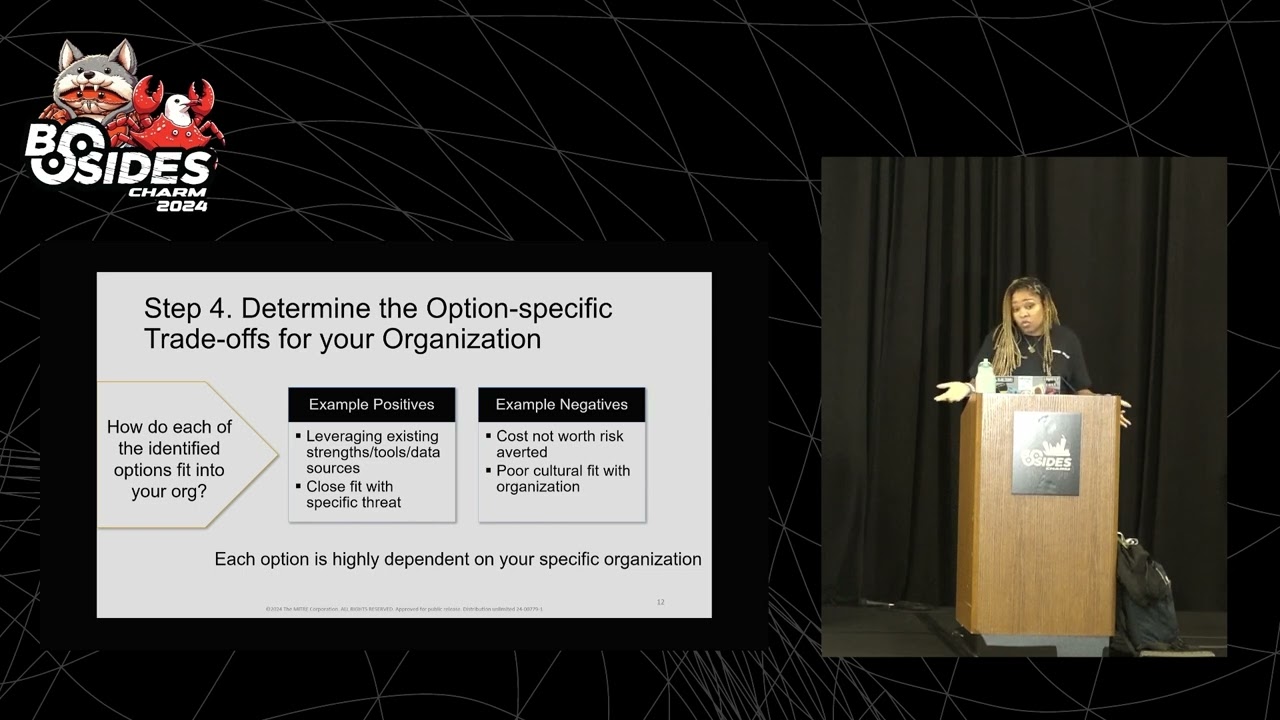
to add an EDR product or ndr product to kind of help move your process faster right and then the response you you got something simous going on here how fast can your people respond to the incident what is the amount of people that you need to respond to this incident so these are the things of like us constraints use uses patterns that you need to consider when you're trying to figure out the capabilities and constraints of your organization that was an easy stop three okay stop four is even easier determine your tradeoffs what's the risk and what's the reward what's the positive what's the negative how do you identify the options that are going to fit into
your organization like mentioned you have cismon in your organization you don't have to use another tool you're good that's a positive you have a large corporation that has a lot of team members and can the amount of hours is going to tape is not going to it's not going to be a lot that's a positive you don't need to hire any more people you don't need to bring in any other tools let's say you're a small organization you need that EDR product to kind of help out and that's a cost that comes with it is it worth the risk of the money and the people and the time that's it's going to take to bring these tools
into your organization to help out with making those defensive recommendations or finding these detections for this adversary Behavior does none of this fit like are you guys not good in detections you guys have a small sock or a small incident response team and it's just going to make poor morale trying to work long hours that's a negative it's it's not a cultural fit right so you have to really consider your organization the capabilities and constraints and what are the trade-offs for the risk or the high reward when you're trying to bring in bring in these options or recommend these options easy stop four okay we're going to get to stop five making defensive recommendations this recommendation
layer that I have here is very CTI focused but it can apply to the defensive side so you have your policy your risk and accept accept acceptance your Tactical your operational and your strategic so from your Tactical standpoint think about when and where the threat happened looking at the immediate dangers how you're collecting your data where's the malware signatures IPS URLs log files those are things you think about from the operational it's where an attack may come from and how likely that attack is to happen think about your vulnerability management your malicious tools your traffic the implementations of how they're trying to do this activity and then your strategic side with which is kind of my favorite but it's who is
targeting and why so that's like the attack types the attack Trends um long-term planning trying to figure out how we can stop these adversaries from moving forward remember Behavior Analysis we're trying to get better guys okay so that was super super easy we went through all five steps we gave you all of the answers of course attack doesn't have at all okay I'm missing some things that's why I still work okay I still have a job because I can still add things but there's a lot of good good things starting there for you guys so that you can get to that making defens of op making defensive recommendations so some use cases on how people can utilize what we're giving to
you and attack you have your defensive Gap assessment your behavior analytic development in your stock maturity let's say you were missing the Sison you were missing the file creation or the file monitoring we just told you in attack you need file creation and that you need to look for these other collection sources you need to impl with these tools that tells you hey maybe I need to look at what my my organization is giving and how I can fill some of these gaps so we're not missing that spear fishing um technique or that user execution technique that's downloading a malicious file Behavior analytic development we gave you an analytic to kind of help that ml perspective or that
automated perspective of like what is the adversary doing from a behavioral level we're not just looking at the ttps we're not just looking at the IP addresses the the the ORS or anything like that we're looking at the behavioral level and that's what those analogs are for and then at the stock maturity you see all the work that comes with doing detections right you saw the the strategy the operation of the Tactical recommendation layer you saw the mitigations and the detections and the analytics that come with it can your can your sock handle that are they are they adapt to respond in a cyber incident or a Cyber attack or when everything something malicious happens
right so that's how you can utilize attack in these three perspectives okay my day-to-day got easier did yours we gave you how to identify the technique by giving you the adversary technique description and and the ttps and the ID names and everything like that the the procedures that tell you what the softwares in the groups and how they used it that's all there for you we gave you the detections how you detect it how are you finding the incident how are you're collecting the data how are you're going to automate that to find the incident so you're not doing it on hand all the time and then we gave you the protection layer which is the
mitigations how can you effectively Implement those safeguards to make sure that this adversary is not utilizing this technique again for your organization I know that was super fast but thank you any questions [Applause] throw it at me I'm open you won't hurt my feelings yes
or
[Music] is can help show your leadership I'm improving yeah yeah so for the people in the room who didn't hear how can you use attack to measure essentially your organization from a defensive or detections perspective um the answer to that is attack has an attack Navigator right it shows you all the techniques it has all the relationships built into it and so you can ultimately put in those data sources look at the detections look at those mitigations and see how that Maps up that way where is the color and it's more of a numerical value for you um outside of that it's there is also an Excel spreadsheet that gives you the same information all of the
relationships all of the detections the data sources the mitigations that can look at and compare that to your organization of what you have and what you don't have cool any other question yes so my organization CCI
of for our organization but my question is concerned with
that is a good question okay so I'm going repeat the question does attack do attribution or are we are we letting the organizations do the attributions themselves I will say there are some things in attack that are not attributed fully to campaigns but they all should be attributed to a software or a group yeah I will say that um so I think it's yes and no if there's things that are not intact because we don't have everything um I would say that that's a a spot for you to fill where you can contribute that information back to us so that what you're seeing is also what we have and we can give it back to the community
right um and then anything else that it should be there for you to see and if it's not there again contribute it back to us cool oh wait I'mma get this one in the back I saw you first
yeah yeah so repeating the question back for everybody who didn't hear um a lot of stocks in blue team are worried at the lower level period mid pain which is just the ioc level and miter attack is very good at giving the behaviors at the TTP level so how can we switch going from the ioc level to the TTP behavioral level I would say that you do need both at the end of the day so when you look at analytics you're utilizing those ioc's to enhance those analytics right you're putting that IP address in there you're putting that that process name those are still important um I would look at the a false positive rate of what your organization
is able to detect if it's not working when you're trying to detect some of these ttps maybe you should start considering the behavior aspect of like what is happening under the hood that ioc's can't answer and that's a way that you can move forward cool uh next question yes it was just more of a comment on thing about
Tuesday yes we are yeah we are really in the ramp down we're getting ready for lease running around like headless chickens because it's Tuesday yeah cool next question question comment yes
okay the question how can you utilize a tax to focus the data that you're collecting Defenders typically have to see all the things we have to know all the things right and so it's a lot it can be thousands of terabytes that you're looking at on a daily basis from your sim so how can we Short change some of that with the help of attack attack has been implemented in a lot of places this is the the benefit of being open and and publicly available right so that means people have built dashboards they have built analytics they have built detection strategies that are C that are focused on the tactics and techniques and some procedures but the
tactics and techniques of attack itself so look at some of those they will be able to help you kind of like funnel down into what specifically are you looking for and that's important to your organization





