GeorgeNazarey
Show transcript [en]
[Music]
um I got into computer security because I was hacked I was running an ISP went to the post office got my mail had this great big letter that the postmaster says I need to C ID to get I'm like great what the heck are they giving me I I receive it I look at it it's from the Secret Service if you know anything about United States Secret Service not normally mail you want to get from so I open it up it's about 10 pages first pages just want to let you know you've been hacked we need you to check the next 10 pages to make sure that the usernames and passwords that they got are
legit okay drive home get to the system start checking first one correct password second one correct password 97% of those were correct I then realized maybe I should get into security this was a Linux box it was a Etsy password file Shadow was a little too complicated back in '95 to actually create it and make sure everything was working correctly uh and I was giving out free bash accounts so you know here's taet to my box you get a free account and oh how did I get hacked I have no idea it was a 16-year-old in Seattle that was actually a pawn to a bigger group uh that went across luckily they did get caught uh I
didn't get to testify it was been kind of good but I don't think that would been good for my resume um but since then started working with a little bigger companies you know from startups to Fortune uh 100s uh and in my free time I like giving back to the community you know either open open source uh I like abusing networks uh just because with ntp uh just a hint I get over 150 million ntp request per day you know so I'm trying to get back on the ntp project uh Weather Underground is a great thing nobody else is in my neighborhood news guys are always wrong so I might as well help them be more
incorrect with it and you know bird buddy is a very interesting uh AI project because they're trying to identify the birds that going to your bird feeder pretty good at catching squirrels so agenda today couple things I'll be going over one going to make some ass assumptions just so we're all on the same page then we're going to be looking you know packet left and network the main goal of this is how do I get information out of the corporate to someplace else without being caught don't worry I'll also give you how to kind of catch these people on the on the same thing because I couldn't actually get in front of here say hey
here's all the bad things you can do without having some ethics at the end saying here's how you catch them so my assumptions your normal user on the box that you're sending it from everything that I did here was not an admin user wasn't any special privileges you own the destination so whatever server you're going to you're some admin there you know it can be a virtual machine whatever but you own that uh any domain name servers when we start talking about DNS you own the NS you own that domain as so you can actually change the records you're actually getting the name requests coming in and these ideas are for educational purposes only yes that has to go back to Legal
from the other side so first one old school we've all watched spy movies you know they bring out this little tiny camera you can still get these on eBay that's where the picture came from um you know take pictures get it out okay not really the best way of doing it nowadays we got digital cameras might as well do that the thing in the bottom left okay that's a copier I don't know if they exist in offices anymore but you know it's a great way to copy stuff going out but but then also if you go on a secure site and stuff like that you can also hack into those because now they're on the
network and see what other people have scanned going around well let's get to modern day not too old school so a lot of the information I went was going through rfc's now can I get a show of hands of who knows what an RFC is okay how many people have actually read an RFC good okay good basically the same people you got stuck like I did have to figure out how work so let's go back to the RFC make sure it works so the first one we're going to go get into is W uh Wireless networking commonly known as Wi-Fi or the internet like the kids like calling it today because you know we had
to now go by numbers because I E 802.11 was too complicated to start putting letters underneath there but if you think about it that's only been around since 1997 okay I can say I was in college then hopefully most of you were born by then you know uh looking at this but if you look at the picture here okay the Lock's supposed to be a good thing okay if you're a corporate you know you have a network great almost all my network now is because everybody has laptops because the people are coming in and out of work we're not going to give them a desktop so you're using Wi-Fi just to make it easier you you can actually have
meetings everybody goes to the boardroom and you have it there well great you got that locked down because there's you know you're using WPA some type of authentication you actually know what it is but let's look a little further down and if any of you turn on your phone now you'll probably see some very similar type locations you're going to see a coffee shop or a hotel next to you I got to put the NSA van because they're always driving around you know trying to collect stuff you know but can I connect that network with my work laptop and if you say yes I can now not have to worry about the rest of this
presentation cuz I can now upload stuff at the fastest speed that I can get everything off the network and you're not going to see a single thing with all the stuff that you put on your Enterprise you spent all that money you did a great job you're 100% secure but now I'm talking next door talking to the coffee shop on the first floor and I'm now getting all that information out so as a way to correct that very easy in Windows you can lock it down here here's only the Wi-Fi as you can do it there's a bunch of Agents out there too that can help you lock it down well let's get a little bit more
complicated here or a little bit more in the weeds what else can you pass across Wi-Fi during the initial handshake when you're looking for this is it one way or two-way it's two-way so I can start actually sending things out over that this is probably the more complicated way to get information out is if I'm peering for stuff that password field I can actually send data out through it how many of you actually checked the password field when somebody's trying to log into the network yes it's slow okay none of these methods are going to be extremely fast I'm not going to be moving terabytes at a time or pedabytes at a time but I can
then get out 32 characters doesn't seem like a lot but 32 characters over and over again because nobody's watching this it'll just go mean think how much you've tried to hack into your neighbor's Network because you were on a different cable company and you couldn't get on your neighbor probably didn't guess unless it was me next door so when I said 32 characters wasn't much you're probably thinking in your head well what type of data can I actually send over 32 characters what important data well this lovely thing called encoding so I can take something that's binary and make it into text which just about every single password field we'll take these characters there's a couple that can't but going
back to Wi-Fi all these are legitimate characters in a Wi-Fi password and also think about this is 64 this is base 64 there's a base 32 actually you can probably create any base you want off of it you don't have to follow rfc's if you're trying to hack for educational purposes only okay so thinking about as we go through here I'm going to be using a lot of encoding because it's a very easy way and most people just make look at it and think it's garbage kind of looks like encryption going over the line it's a bunch of random characters what what is it exactly but says I'm doing the encoding I know how to do the decoding
now everybody knows how to do Bas 64 it's a very simple function you know you have a decode and encode version of it but if you start doing your own type of encoding if you wanted to go down to 8 bit to really get small or if you wanted to go up to 128 or 256 going across it you can start playing around if you that gets a little complicated because then get into Unicode and may or may not you know accept it in different protocols but at least Bas 64 and Below you get passed in just about every single protocol the only disadvantage of encoding is it gets roughly 35% picker between 30 to 40 I I was seeing some
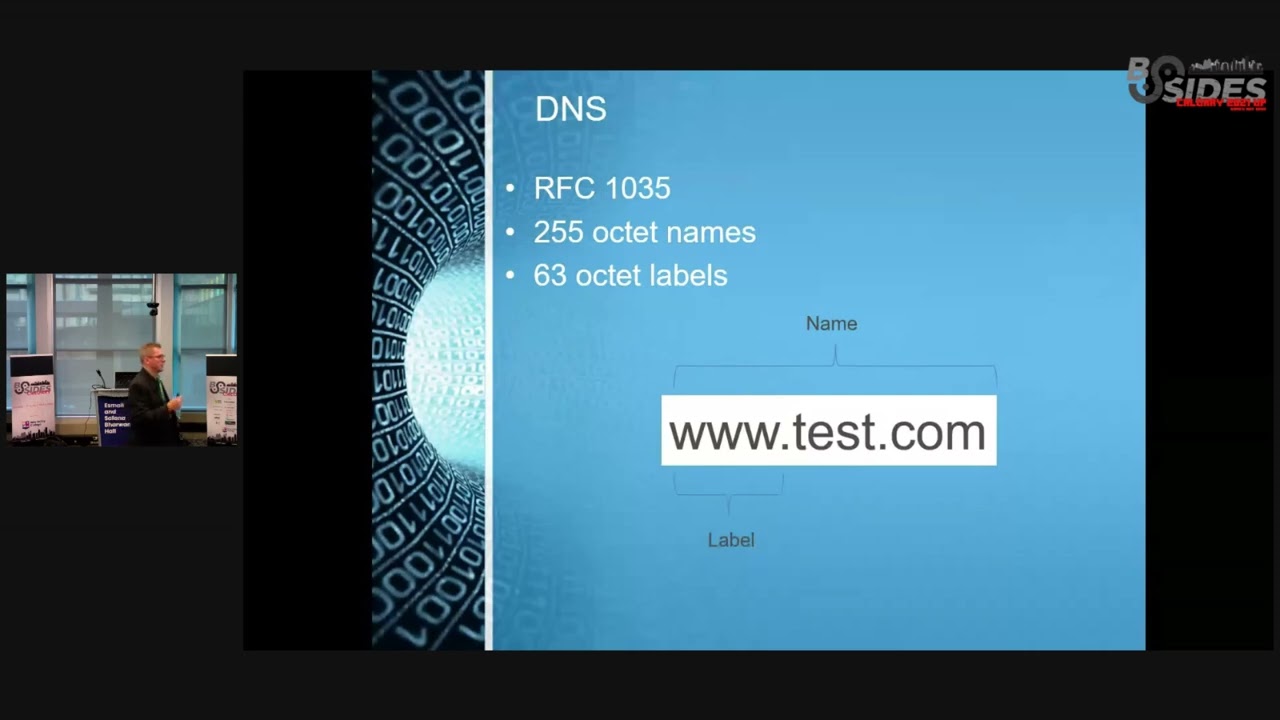
basic hello world uh programs that were really small when you get inance some of the larger files it's closer to the the 30 Mark so if you want to get that petabyte out okay you're going to do 1.3 pedabytes it's going to take a little bit longer but still you'll be able to get it out you might be asking how can I get a pabit out a couple slides I'll show you but it's going to take about three and a half years so DNS we all have to live DNS now the nice thing is it was written a long time ago because people got sick and tired of the SE host file if you ever had to you know it's a
great way to hack a box but but picture back in the 1970s you're calling up your buddy saying hey I added a host here's a new host please add it to your file that's exactly how it went around um so came a wonderful thing of DNS so now we have a very nice Network it's probably one of the most redundant networks in the world for how many root servers we have and going down especially if you get outside the US us and you look at the international uh root servers not just the North America ones uh and it can do up to 13 different DNS root servers and that's because of packet uh limitations only uh go in
UDP now if you look at this and you're probably saying
George name sends it to the DNS server hopefully that DNS server may or may not have what you're looking for and it sends it back to you I don't care what's coming back that's in material here I have
20 extremely small if you have that you probably don't need to hack because you can probably sell for about a million so you're good to go on that but then that gives me another 250 characters to send across now I don't care if I'm using Google's DNS corporate DNS it's still going to send that resolution out very slow 63 octets per label up to 250 characters roughly if I had a do IO but you can get that information out now there's two ways are getting caught here one if your Enterprise DNS person actually looks at the logs and just realize why the heck is this person looking up all these domains and it looks like garbage here and why did I
just overrun my log my DNS log space that's probably you'll get caught not that they're looking at the logs just I ran out of dis space uh on there but most DNS servers will relay it for you now if you own or if you can pick your own DNS well that's even faster yet I can start sending them across now on the reverse of this you can get information in there's a lovely record in DNS called text files so if you had to get some tools into a corporation since you're hacking there you encode it put it as a nice text file 1 2 3 4 however many it takes and you start requesting those so you just brought something into
your corporation okay DNS is going to allow it because person's looking for a text file who really blocks text files some people do but kind of legitimate coming in and now you can you you decode it and now you have your binary whatever you want to do if you want to bring scripts in it's a very quick easy way of getting scripts into an organization by putting them into a text file now how do you block it when you start putting limits on how many DNS lookups you can do for a specific root domain because if I because to push this out I'm looking up tens to hundreds to millions of host names which you know
that's going to just add a little bit too much uh data going out you will see something strange or you actually do DNS query logging this is a great way to catch it on the other side too if you're actually doing it all you need is the query logs you don't have to return an a record a a AAA whatever type of record back I just got to look at my query logs here's all my information that I just got out of the organization if you're really get fun you can do this over a DNS SEC and it's all completely encrypted going back and forth doing with the text records then the next one that I love
I've been in uh mail way too long going back to RFC 820 821 822 and then they put twos in front of it now they have fives in front of it we're probably going to have to redo it again U and this also relates back to why do we need encoding when email was created they were expecting only to say hello what do you want for lunch send me back that's it this thing of an attachment they did not think about it back in the 1970s okay but encoding they had to go back to it because in the SMTP protocol there is no binary data going back and forth unless you switch over to TLS then
you start getting binary but by default there is no uh binary code going back and forth now trying to get out on pork 25 that's kind of easy most people block that if you didn't first thing go back block pork 25 outbound just so you're not a spammer uh but if you are if you are able to get out interesting thing in the RFC is you do the hello tell who you are you can do an ELO for the extended commands so you see where the mail from is that command line you can put 512 characters before you get an error and before you actually start a tech before you actually start an email message so think about all the mail you
can send out now I'm at 512 I'm no longer at the short domain stuff uh of 255 I'm up to 512 just the commands going across if you're doing any type of analysis on it it looks like valid commands given that the your tools that you have monitoring it actually follow the RFC you might get some cutback from it uh just for the simple reason of hey who actually has a 512 character command going across but it is in the rfc's going back through it they have not changed that since uh they they started initially the other fun part you can do uh with mail and this is kind of kind of breaching a couple of those
how many have a Gmail account how many have a lot of really fun documents saved in draft if you start a document save it in draft it's never actually sent an email then you go home open up draft and you can take stuff out of it this was used actually um back 2008 2007 a couple uh adversaries were using this as a way to save stuff because hey I didn't actually send the mail there's no track of a record of it going from point A to point B just I put it here person on the other side logs into my Gmail account because you know sharing passwords here and they were able to download it and it just
went across as a web uh transaction so how would you stop this take the dictator
approach web proxy or something like that and start looking over uh this information that's going across a lot of this comes down to web proxies get some type of man in the middle to actually see what's going apart uh back and forth don't know if your employees will like it or not but it's your network you get you get to control it now this one I had a lot of fun with icmp one of the most R rudimentary protocols that are out there we all use it but we don't know that we use it and just about all the important machines on the internet use it and the lovely command that we love is Route not found no U it's actually
ping okay so using ping uses a very basic icmp packet here's what uh it looks like from the RFC now if you use Windows you got 32 bytes of information into random data how a ping uh Inc packet works I send some data out to host that host takes the data puts it back in the packet sends it back to me to see if I can go from point A to point B what we're also used to is it times it to see you know what type of timing that you have on there Linux gives you a little bit bigger little bit packet the other thing is Windows do ABCD and the whole alphabet Linux starts from zero through
through nine and then does the alphabet well that's random data there is nothing in the RFC that says what am I supposed to put in a ping packet it just says data so what happens if I encoded data broke it into small packets and set a ping across now you can can send a ping packet up to, 1500 bytes in total size before you have something breaking it now reason I bring that up is because if somebody's if you have a network admin and they start seeing ping packets broke that's kind of an odd thing because most people never put a size of a ping packet uh going out there Google takes it a step further if
you ping 88.8 you can't do anything bigger than a 56 plik packet you go to 57 you don't get your packet back 56 you get it but the average network will allow you go up to, 1500 I said earlier how do you get a petabyte across start one of these going every tenth of a second yes you'll see network traffic there but if I take it down to normal 56 byte size I can send three Megs a day how many Network admins in here can detect three Megs a day going across the network of a ping packet that looks like random data okay trying to catch this trying to trying to find it is nearly
impossible now you can also use this on the reverse if I'm pinging something and I'm listening to the pings on the other side it's a lot harder to receive the Ping it's very easy to send the Ping out receiving it on the other side is a little bit more complicated because you got to actually get down deeper in the T in the uh in the driver to actually see all the network coming across wire shark's great for this uh any type of packet capture is great for seeing it and then going through to capture it but I can also send data now back in as my reply so as long as I'm sending out I
can and you can also on the reply back change the size of the reply packet since you control the pin going out you're not checking what's actually coming in except what you want to come in so I can see if I can get that, 1500 bytes coming back in towards me which most firewalls will allow a ping to come back now the the fun part with ping easiest way to stop it turn it off at your firewall then all your CIS admins now hate you because they because box isn't working I'm going to Ping 8.8 or figure out your famous uh IP address oh it doesn't work then you got to go talk to network people and like oh yeah I turned
that off for you the other fun part is everybody uses ping because everybody has turned off NS lookup so ping has now become your DNS resolver on a lot of networks to actually find out what the host name is
now SSL there's a couple fun things you can do with this it's a great tunneling protocol it was the child it was created by Netscape because it says hey maybe we should encrypt this stuff pure data going across the network might be a bad thing and oh wait we control the browser how many people have used Netscape as a browser yes okay how many people have bought Netscape as a browser good better yet okay that that's why they're no longer out there okay we never actually paid for the browser okay so they came up with this idea in '95 it's a way to secure tunnel okay we all know how SSL works there's a handshake
and you're good to go whoever looks at the handshake okay you're using a handshake because it's going through a proxy no pocket capture yes you can hide stuff in the handshake handshake going back and forth can be up to 8K depending on the size keys you want to go back and forth so that's 8K of traffic you could send out and a normal person will see oh that's a handshake that's an SSL handshake now if you're going through a web proxy if you're going through any type of inspection just killed you in in your footsteps but I can now have data going across I'm assuming I have a mediocre Network admin okay not the top
tier guy or anything like that looking at these but that's information I go across that plain light it's going to look like garbage because we encoded it it's going to look just like a certificate going back and forth but you're able to get information out that way so this way of using protocols that were never meant to be but you can now the other bad part about SSL is everybody's now encrypting thank God the let's encrypt I use it on all my websites as long as my DNS is working correctly um so everybody now has free search before you know you had to pay $100 $200 not too many people used them now they're free uh but now I can no
longer see my traffic okay as an organization unless you have some type of web proxy or something like that sitting in a way I can't see what's going back and forth makes it easier for people to get stuff out of your network because now it's encrypted I am still putting a bet down in 2035 I can send pure text across the network and it'll be the most secure way to send it because nobody's looking for Pure text in 2035 okay but everybody's talking encryption we got to encrypt don't want to see it well it's a great tunnel for the bad guys to get across too and God forbid if they open up a VPN it's all
going the nice part is though you can capture this also by looking at at traffic this is very easy traffic to measure and to see going back and forth and the last topic because I know everybody loves QR codes great idea when it was invented okay UPC code only has maybe 20 characters okay going cross if you really want to go really deep into it uh but now they're like hey let's put a lot more characters version one you could have I think it was about 120 130 characters so very good for invoicing you you know very good for packaging for scanning and stuff like that the initial use and then some bright person goes hey
why don't we put your URLs behind this smart move the last version that was just released uh I think it was last year 40- L you got 7,000 characters you can put there quick question for you is there any malware that's ever been written that is smaller than 7,000 characters yes when was the last time you went to a restaurant and says oh scan this I still like paper copies I think Alberta's cutting cutting us off come January 1st or asking for a paper copy of a menu but you know still being allowed to gather that information put it into a different type of encoding because now I'm putting it into a QR code I work in
marketing our new marketing Camp door okay so it's an easy way to get information out I also found a really fun way of doing um there is a project out there where you can make an animation on QR codes if you want to take that even a step further take the animation with QR codes and then put stenograph on top of it there is so much air coding in this that it can be pretty much unreadable and it can still process and you can still get the data out so if I take the eight eth bit and just change it to do my uh stenograph going across
so quick question how many people scan the last QR code I will have a count on how many people [Laughter] scan so just credit is going on um I hope you guys found this enjoyable you know as an idea thought of over a couple beers couple ideas you know able to change a you know put the red hat on not always defending but also thinking of ways to defend it you have over 10,000 rfc's that you can start reading through and you can maybe find these little tiny nuggets on how to get things out given they're not all on protocols and stuff like that they they do cover a lot of other things good reading is actually
from RFC 1 through RFC 10 because you can actually see what people were thinking when the internet and these protocols were were coming up but it's a good go out there um I don't think I missed anybody on this if you go to uh just one thing the template downloading it I did get kind of scared because it was all in
Russian any questions on any of the ideas that were brought up yes sir mention begin one of the project yes exp uh ntp is the open ntp or network [Music]
time in time um but coming out here not as much there's a lot of ntp servers on the west coast that are competing for my uh ntp request um but doing that data dump and actually analyzing is really interesting to see the in increase at about 5:00 p.m. and I'm guessing that's when people open up their laptops when they get home so then it's checking it daylight savings times is always cool too because you get a huge Spike because the clocks are going nuts uh and then also when Windows releases is a new version of Windows you get a huge uptick on that as well it's it's free to join uh they actually do monitoring for you so until
you get to a certain level which normally takes about a day or two for your uh ntp server to level out they give you free graphs on you know how how well or how accurate your time is than in Back Sir what uh you can get it out um it is there is a secure version of ntp um where I where I thought of using it as a malicious sign is like the NT open ntp service only checks you every five minutes so you have four minutes and 58 seconds to alter the time when they come and check you or right a Special Rule saying hey if this IP is checking me give the correct time
everything else change it so think of how much fun you can have to go hack a website have everybody come to ntp2 come back a week or two later change your ntp server to three years ago go hack them come out good luck finding those logs you can find it I'm not saying it's not findable but good luck trying to you know search through there and find that information any other
questions man you guys are being nice well again yes
what's your definition of so so if you want to get a Word document um thank you for bringing that up that's where you use the uh 64 base 64 encoding so you take the word doc it then becomes all those characters and then you use that you split that up for however big your data is going out and then on the other side you just reverse the idea and actually in in the icmp Stu you could actually send binary if you really wanted to you don't really have to encode it depending on how sophisticated you want to get if you want to have a fun project right it's very easy to do you're going to have so much fun right in the check
sum section of it cuz there's seven different ways of doing it and you can go to 15 different universities and they really tell you even different ways to do the check sum to come up with
it well if there's no more questions thank you
no so what second comment if you do uh hit me up on LinkedIn I will L up with you uh I am local uh in Calgary so and I am in security field here too so so thank you [Music] guys





