Paul Melson - Automating Malware Analysis for Threat Intelligence
Show transcript [en]
from a customer slash you know provider perspective he was the customer i was on the provider's side he's uh he could he could really give a good thumb lashing i could say and really make it sound like he just you know complimented my life or something it's really really good so um he also has a distinction of having an alter ego uh i won't say edward khan uh maybe you can figure it out on where he's from where uh security
[Music] kept secret in infosec and maybe if you're nice to him to let you in on the joke [Applause] um always always awesome to be back here in augusta besides augusta is definitely a go-to so if you're watching this at home on youtube um next year 2017 you need to be here um i still can't believe they let me speak quite frankly um so um yeah i'm uh paul nelson i do cyber stuff for uh for target i've been there about 18 months and um i have a pretty i have four hobbies um kind of in order uh my kids we foster dogs for an assistance program i collect beer and i collect malware unfortunately for you i'm only going to
talk about the last one so this talk is a little bit about automating malware analysis for threat intelligence but before we really get into how that all works and uh before we attempt fate with some demos i want to talk about why it is that we analyze malware in the first place i think it's an important thing to kind of baseline from right so malware analysis if we go back to like the antivirus days is actually one of the oldest practices in information security chances are pretty good that most of you in the room work somewhere where they had anti-virus long before they had internet connectivity in a firewall but what's interesting is that viruses
started out as kind of self-replicating destructive frankly pointless tools but now they are monetized they are just that tools uh for the commission of crimes of various types so when we're doing malware analysis what we're really doing right fundamentally is we're going back and we're trying to understand the capabilities of the binaries that we're running into and by understanding those specific capabilities we're hoping that perhaps we can infer the intent of the adversary right at the end of the day there's an attacker who's trying to do something almost always monetize something in some way or gain some sort of an advantage whether that's direct compensation for what they've done or whether it is some sort of tactical uh or intelligence
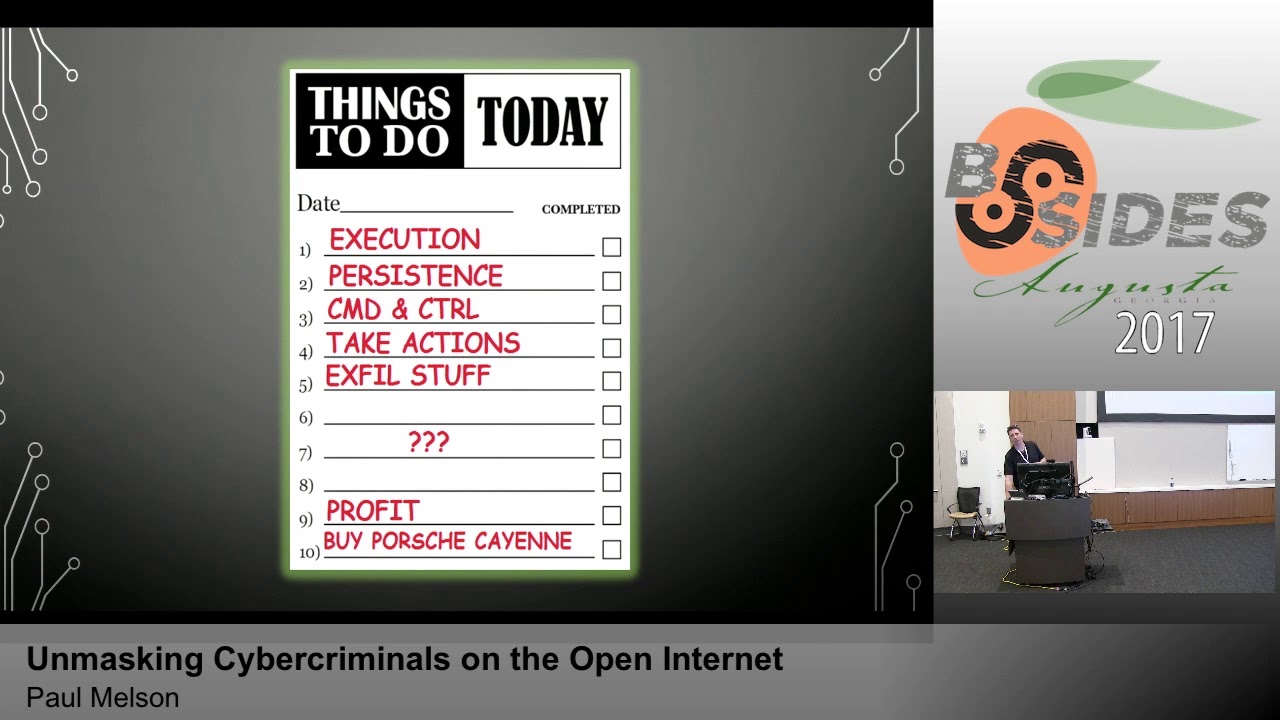
advantage the malware is just a means to an end and understanding the malware maybe lets us understand what that end is and so that lets me pivot very nicely into the uh the lockheed martin kill chain uh so we had a spirited conversation over drinks last night uh so with uh some of the other industry luminaries that are here um at this conference and um so so whether you're a fan of mitre or lockheed or um or the median attack life cycle they're all valid um but my point in bringing this up is i you know at the end of the day every attack has to go through phases in order for the adversary to get to the end
and so by looking at malware analysis right um we get to interact or we have the opportunity to interact we don't always see it and we aren't always there and present in the ir cycle but we have that opportunity to interact starting at delivery but when we're analyzing malware and one of the reasons that we want to automate analyzing malware is to get faster at this because the point of the malware is it will almost always tell us something about the installation and command and control right that initial payload that dropper whether it's a macro in a document whether it is a primary stage one loader that delivers a secondary mission payload or whether it's a handoff bot right there's an
entire industry in the in the crimeware family where they're dropping rats specifically for the purpose of selling access to your network to someone else somebody else buys it they use their rat to drop the new malware and then they ask they exit the scene and the new adversary is in your environment without ever having to figure out how to hack you in the first place [Music] and the thing about this is if we can quickly move from delivery stage to understanding installation and command and control because those are things that come with the delivery of the payload right by working through that then we have the opportunity to disrupt the actions and objectives of the
adversary so the speed at which we move may give us the opportunity to get ahead of the adversary and really ultimately this is the value of operating with you pick your model but with some level of attack model in mind so a little bit about my research um i collected data using virus total intelligence i like vti because it has an api um i did some reverse engineering on a couple families of malware i picked a new pos things and neutrino so this is neutrino with a 3 not neutrino the exploit kit also called cassadet by some of the vendors and the reason that i picked these is that they're widely prevalent and they have a kind of
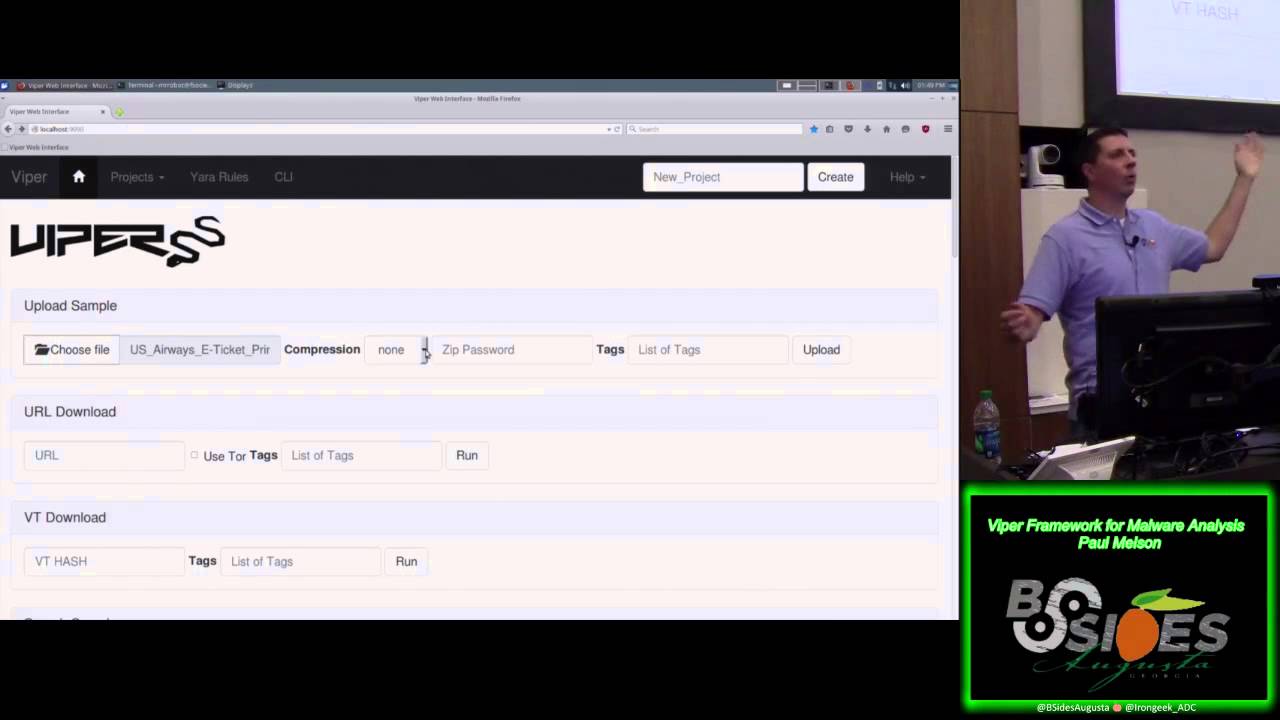
an understood end right one of the functions of neutrino is now neutrino does a few things it can act as a ddos bot and some other stuff it also has a credit card ram scraping capability which of course is new pos things bread and butter so i definitely have an interest in malware that does these things so we track a lot of that and the goal was to do some reversing on these understand them build some yara signatures deploy those yara signatures into virus total for hunting and then win virus total found me new samples automate the pull down of those and triage into a viper framework so a viper if you're not familiar is a static analysis framework
put together by next and kept breen and it's a community group brought to you mostly by folks that have worked also on cuckoo sandbox so this is the static analysis cousin to cuckoo's dynamic analysis and actually they have a pretty slick integration so i'm going to be showing you this because this is just kind of my favorite tool set to to do reversing with and it also it's handy because it has an api so it makes automation really really easy for people who are not natural born developers like myself so let's dig in on neutrino some of the stuff that neutrino does so here's these are snippets from ida some screenshots just to prove to you that that i know
what i'm talking about when i write these yara rules so here we've got uh some uh some strings that get created uh these are variables that are designed to capture track one and track two if you're familiar at all with mag stripes and uh and credit cards and the way that those work track one and track two are written data structures uh traditional mag stripe reader connected to a pc we'll just pull those into an import buffer usually the keyboard buffer and simply make those you know it's essentially like somebody typed them in and those will be just sitting resident uh in uh in one of the input registers uh for the process that uh has hooked
that device so track one and track two are uh yeah i mean it kind of calls out exactly what malware is getting ready to do [Music] this is some interesting stuff about neutrino as well so if you look at all the little red bubbles there you'll see things like maltest tequila boom boom sandbox virus malware sample virus sandbox um and so uh first giveaway of the talk is who can tell me what tequila boom boom is is exactly correct um so uh so tequila boom boom is the uh this is the sandbox and user id um that large total sandbox is in so if you see binaries that contain the strings of kilo boom they're
thinking about virus total the cool part about that is you can totally use that against them right vm detection in binaries is usually a sign of bad stuff and uh one final thing about neutrino um is that it statically builds command and control in so command and control can be flipped uh by the panel but in a lot of cases and in fact in most cases uh where we're talking about crimeware the the builder will simply import the command and control structure directly into the file itself right so if you have the pe binary you have the command and control data in front of you you just have to know where to look and in
neutrino it actually stores it in a base 64 encoded string that's just extractable by strings so it's some really really basic there's no fancy obfuscation here it's just enough so that you don't immediately go hey that's a funny looking url when you go look at it so but sure enough if you decode that you get the url of the panel the panel can move the botnets to new panels but they have to be talking to it at the time and all the c2 for neutrinos over http so so we've completed reversing here's some yara rules one that's uh the one on your right is strings based so we leveraged tequila boom along with some of the other
bot commands in the c2 along with some of the url parameters that we know that different versions of neutrino tend to use on the on my right your left you can see the same oxidation op codes are broken out there that's not exactly human readable but trust me uh that's a that's not a bad rule either so i don't have network this is one of my this is perhaps my sole complaint about besides augusta is uh so you're you're gonna have to take my word for it that the hunting script runs just fine in my sandbox every five minutes uh so there's my cron tab and then at the bottom you can see the vti notification script
which i'll show you the code uh in a little bit uh be gentle i'm not a developer you can see it reaching out talking to virustotal and saying hey what do you have for me hey i have these two uh these two rule hits for you um and then what the code does is it checks in with uh with the viper repo and says hey do you have this hash and in this case it's saying yes i have that hash so we'd take no additional steps but the viper repo says no i don't have that hash then we pull the file down from virustotal insert it into viper and then had viper triage it using the same yar rules again
and i have it do a few other things like tag it with import hash and if there are any packers that are identified in the file and a few other interesting tricks that you can do with with yara and uh store dash t in like so and then here's uh proof that i did in fact ingest this file into uh into my viper repo so you'll see the hash matches and it is in fact um tagged and ready for me to go ahead and analyze it uh at my uh at my leisure so let's do this
okay so this is the aforementioned terrible python code that makes up the my virus total hunting script so it's primarily based on requests in json and a little bit of regex because not everything does json as well as json should be done so here we build a list of rules um yeah so this is this is the list of rules this corresponds to the hunting rules i have to apply deployed at virustotal i have a substring or a subroutine here that just generates the import hash value using using the viper api we reach out pull notifications if we have any notifications we kind of come through and extract the id the hashes the rule set name the type
check and make sure that what we're looking at is an exe or dll this is a lesson hard learned if you're going to use automated hunting functions to pull binaries from whether regardless of whose source you use not this applies whether you're using virustotal mouseshare or any of the other available repos out there to to pull samples you definitely want to make sure that you're pulling down valid windows executable files if that's what you're looking for otherwise you will just end up with a file system full of other detection companies detection so um so yes it uh so a hack if you if you are so inclined if you need mcafee uh signature updates you
can get them off firestone and and everybody else's stuff too frankly okay um so so then we check make sure it's a file that we actually want um we check in with the repo and say hey uh do you already have this hash if it has the uh if it has the hash then we just skip it if it doesn't have the hash then we go ahead and pull the file down from virustotal and then store it and then come back here and upload the file uh via the uh the viper api and so this is sitting i've got a little t2 micro instance sitting out in amazon ec2 that does
hi folks anki here unfortunately we had a little video freeze up so we lose the speaker's motion and audio until about the 15 minute 52 second mark
so um so i have uh written a few things here some of the stuff actually calls back out to virustotal to pick up some additional information i won't be able to demo that but i have this guy here um oh so one thing you can one thing i've done right so this is the corpus of new pis things they're 85 samples in my repo and this is all based on using tags i have a little bit more neutrino than i have new new pos things but they're all kind of useful and oh yeah and just showing off uh again uh another module four so uh so new pos things i showed you encode c2 and base 64 string
so i just wrote a little string search that looks for base64 string patterns using a basic regex if it finds it takes that string tries to decode it if the d code is successful it gives me the value but that is like super helpful when you're trying to get c2 from a whole bunch of samples so let's do that um so this screen down here this is the viper api console just to show you that i'm not cheating and this is the demo version of the report and so what i can do is just tell it hey i want everything that's tagged a particular way so in this case i want everything that's tagged as neutrino and it's just going
to go in there and start generating this big ugly pipe delimited mess of stuff that i can then do later analysis on so you can see we're ripping out all kinds of stuff user agent strings import hashes compile times um file size all different kinds of things to just sort of get here's the set of indicators that i think i might want about this stuff i'm going to take a minute to talk about this approach versus metadata collection in a big data environment right it is also a viable approach to take and rip all of this metadata as you collect the samples right off of your source and put it into an elastic search environment and that will give you lots
of things because so something like viper keeps all of the malware samples in what i would call a zoo live on disk that lets me write new code and go back and re-analyze those over and over and over as i learn new things the problem is scale on that end but the challenge yeah but you give up the ability to continually reanalyze samples if you move through metadata collection in a big data environment so i guess in short what i'm saying is do both all right so now that you've watched this grind for a minute
let me show you one other so i did some kind of discrete ones or some specific use cases because uh so each one kind of you know i had to know i know i had to know a little bit about how to do the extraction right so either yeah most of these it's some variation on strings and decoding to get the command and control out there are a couple that i'm not going to show off here that are you know rely heavily on on opcodes which they're super slow because you have to i have yet to find an elegant way to not have to just iterate over a bunch of a bunch of different address spaces inside
of the sample to actually get the c2 out but this one should work there we go so and you can see it's starting to uh to rip things out um and all the way to the right there you'll see it start to parse out the command and control and this is all oh so uh caveat right this is all live i hope nobody is trying to browse to any of these sites uh most of this is old and down but um as we get to the bottom there's stuff that is up as of this past weekend so uh um you know i'm doing this all on a closed network on a machine that i'm gonna
reimage when i get back to minnesota but um you know anytime you're playing with live malware you know do so at your own risk and don't just consider the safety of the machine or the network that you're on i mentioned earlier i run all this stuff in amazon i do not do any of this on the work network that's how you get your laptop contained by blue team so um so but if you if you will look up here with me you will see that there are some really good reasons not to just automatically deploy all the indicators that you extract from malware so that is legit a sample of neutrino that somebody has actually configured the uh the email uh
spam relay functionality in the config so i found that it they they have a yahoo account they're using yahoo account to deliver you know spam uh for this uh for this bot uh net um so neutrino by the way is kind of like the scumbag starter kit it's uh all the documentation is russian um it is it is total skinny land um if you if you get into looking into this particular family of malware it's it's kind of hilarious some of the stuff that ends up happening um somewhere up here i think if we look hard enough we'll see um i thought i had a sample that so there we go 192 168 71.2 so for those of
you working on thread intel feeds this is from the special insider threat version of the intel feed so this is why we don't automatically uh deploy indicators this is the part of the problem i haven't figured out how to solve quite yet frankly um perhaps there's a a black listing or a protecting thing that you want to do and you're willing to kind of take the risk of the great space in between to say you know here are the the top 500 or so domains that we know we just have to white list and we would never want to deploy an indicator against uh just because it'll just be too darn noisy and these are the ip ranges that we
would never want to deploy an indicator against because again it'll be too darn noisy but short of that i really don't have a better approach other than i would say this is exactly the kind of stuff that when we pull it all together we want to send it right over to a team of intel analysts who can one help us dedupe it out of out of their indicator repo and to determine you know which of these indicators are actually valuable indicators and being able to pass that to them with the full context of things like an extracted malware config is a huge help
so the question is what if i uh added the registration date of those domains and used that as a as a piece of data so yeah bulk scraping um okay so a funny story about um well here let me let me let me pause on your question and come back to it uh because i've got a slide that will kind of talk to pieces of that right so because part of this is absolutely about let's unmask the bad guys so so this is uh this is a output of a slightly different run of the script i literally just showed you um and so what you can see here is um so i i just pulled out that's the shot 256 hash
value of the file the compile time from the the pe header uh so if you're not if you're not familiar with windows pe headers they capture a bunch of information like the import table whether or not it's a x64 or x86 uh architecture instruction set and and they also include a utc or an epic time time stamp for the compile time of the file itself and so what's interesting about that is that um when i i started collecting compile time specifically because what i wanted to do was build a campaign timeline to say hey this was built at this time and deployed now it is trivial to upset that and rewrite that data but i completely failed to
predict how common time stomping on pe compile time is um but that's not bad news it turns out so in this case though let's let's take a look so down here you can see 1992.0619. i think we can all agree that that was in fact not compiled on dos 4.01 i don't even think the pe standard had been ratified at this point in time um so so that's clearly a garbage date and that ties to this c2 but that c2 ties to the other two samples immediately above it uh but that is literally to the second the city bogus state as that time stamp up there which is tied to that you and then it seems to then sit
back to those two samples and what's really interesting is if you look at the compile time stamps on those two others those are only a few minutes apart and i propose to you that this is a pattern a behavioral pattern of a human being who does a couple of test runs with visual studio and uploads those to virustotal and then shortly thereafter uploads a time-stomped version of their malware to virustotal for checking and then deploys the time-stopped version because we can find the time stop version uploaded a whole lot more times moreover what i suggest to you is that because that pattern repeats i now have the ability to connect that c2 and that c2 to a single
operator does anybody want to argue with me or disagree with me on that so so and even if even if that's not correct that's a really interesting coincidence and coincidences are great because coincidences happen a lot it turns out when people automate things so this is uh across that neutrino data set i just showed you and so so i knew right like so down here on the left you've got uh 1970-01-01 midnight january 1st 1970 which is all zeros on epic time yeah so like that's like the laziest time stopping you can do i just i just smoked it like it's just gone now i can't be the only person who's mad that windows will run something with
this is a compile time timestamp but you can see we've got these two from ancient times down here uh on the uh on your far right but as we move down um what are the chances that on july uh july 9 2015 at uh 1009 pm in 31 seconds 62 different russian scumbags compiled the same kit and deployed it what like so right so this is a statistical anomaly there's no way that that is a legit timestamp right now if i'm looking at a single atomic sample of this malware and i see that timestamp i'm probably going to skip right over it because july 2015 this is totally a highly usable very much viable very active
uh piece of malware but uh 62 times and i'm still pulling new samples with that timestamp so it seems really really unlikely that that that this is coincidence so that is so what that means though is i think i have 62 samples or roughly a third of the samples of neutrino that i've been able to capture from virustotal all attributable to one person you know and i don't know what that is maybe it's like his kid's birthday or yeah the day he bought his porsche cayenne or whatever whatever whatever russian cyber gangsters drive so um so i took this a step further though and i said there have to be you know it's cool to be able to do this but not
everything not everything punches you in the face quite as bad as this one does so what other what other patterns can we identify and so i started taking multiple so if you're familiar with with nodegraphs or forced relationship or social uh social network analysis sna um so this is not technically a social network but the same algorithms totally apply right so what we do is we create a couple of connection types in this in this case um compile time values and c2 values and then look for all the connections between so the blue dots are binaries and the lines uh making up all those pretty little constellations are the different relationships so the blue lines are compile time and the
green lines are c2 and so right off the bat you notice there are two really big clusters um you don't have to be you don't have to be martin holstein to be able to figure out that those are probably related um but there's some pretty stuff that gets drawn in here too like this constellation here is really kind of an interesting one because you remember this screen here that is an expanded view of that and what we what we find falls out when we overlay this uh again is that there's actually a third campaign that's tied into this same pattern now i did nothing to prep this data this is literally just they have the same values
show me all the relationships where the values are connected and this falls right out see data analytics so this is new pos things um and and i i wanted to use two different variants because what i didn't want to do was just assume that this tactic could work and then if i got lucky it would work and then i could never apply to anything else ever again uh and it turns out um that that this bore fruit over here as well so this one is compile time and impash so i'm dropping c2 completely from the new pos things uh conversation and instead we're just looking at import apps an import hash write is a representation of
the the import table like all the function calls that the builder loads when the the binary first executes and when we zoom in so this one that's down here uh bottom left when we zoom in on that what you can see is a whole bunch of different compile times in the blue lines that go around the outside but all of the import hashes are the same across all of these samples but what's really interesting is then up in this cluster in the upper left for you is upper right for you um that's same import hash same compile time well again yeah so now you've got time stomping so this is these are all the things i
my hypothesis is what i'm looking at is that is a single builder for new pos things and the upper right quadrant is a single actor who likes that time stamp a lot so neutrino again compile time in c2 clusters you can see right off the bat there's a couple that that are very very tightly combined but there's some interesting stuff too if we kind of look out to the periphery of this graph and i uh so i took the raw extracts that i showed you i generated earlier i threw these in kumu with a basic social network analysis algorithm and and outputted these pretty pictures um and so when you really drill in on these
so this time you're looking uh kind of upper right on that graph out along the edge you'll see there's four kind of grouped together and this is them and we found the affinity um across two different c2s all using the same time stomping but what's really cool is we picked up this outlier too which i pause it so he did he uh the the actor he or she time stomped this to all zeros right some basic stuff but i posit that they screwed up and let one get away that they hadn't cleaned up the pe header for to their own satisfaction and in fact we are now able to date these two campaigns to june of 2015.
right because the bad guys screw up so now i'm going to pivot back to john's question about have we ever looked at all of the who is data behind them so um if you uh if you are in the if you are in ir detection uh or threat intel um i i got to put a plug in for domain tools or at least the capability that domain tools provides to do domain history because the ability to take a domain and see all of the ips and the original registering data because a lot of stuff gets kind of picked up and swept away and cleaned up and that's fantastic there's a there's a whole group of you know
miscreant punchers out there who find bad stuff and get it taken offline and that's fantastic because for most of the organizations out there they can use all the help they can get for uh but for those of us that are interested in unmasking the bad guys it's really cool to have the original registration data too and so uh to um so uh long story short yes and it's very interesting because just like they make these mistakes from time to time they make registration mistakes so lots of this stuff gets registered through you know godaddy or um i forget the i forget the one uh enu or whatever the one is that's in enom thank you yep the the one that's uh
um um the one that's in south america anyway or central america panama it's in panama um and so uh you know and all their stuff gets blinded every once in a while they screw up and their real details come through there's uh there's a neutrino actor and i'm fairly certain i have his apartment address in vietnam i don't wanna i don't wanna put it up on slides and put it out on the on the internet in case i'm wrong because i might be wrong uh but but it but it kind of looks like this if you look through the data right you have all this stuff that's just overwritten and anonymized but they make but they do
this so much some of these folks iterate through it clearly so often um right that you know they put out a campaign campaign gets burned put out a new campaign right just redeploy the toolkit so um so and every once in a while they're gonna screw up and uh when you catch them screwing up you tie that data back to all of the other commonalities that you have about the rest of the campaign that they're running and now all of a sudden we can start to build a picture of who's actually behind this stuff intel so um and then again just uh you know more more stupid tricks this time in passion size clusters and you see we keep basically the same
shapes from here to here so um so the thing the thing you can um so i've dug deep on these those two are competing versions of the builder kit for neutrino almost none of the neutrino that you see out there has been highly customized by anybody that can code their way out of a wet paper bag most of its kids that just run the builder script you know chain literally they have a nice little uh visual basic gui but you can set up the config run it and compile it and deploy it so and then the panel is all php in my sql and i'm sure probably also not the best at handling inputs but i
don't know anything about that um so other ttps as we look through this right so uh so i pulled all the i used domains and ips for uh for the c2 piece but the thing about url based c2 is is that domains and ips is only part of it so uh this is a bit of an eye chart and i apologize for that but you'll see i pulled this out into google docs and threw this up and highlighted some stuff where these patterns repeat right so at the top you'll see those are the same three domains um with slash fonts test slash images tests and slash jstasks.php a pattern that also repeats down here in the blue and then we find
an orange one where we think i think we have more of a complete picture because we need js images and fonts we also get cgi and ink does anybody else see it though right so now we i can tie those three domains together does anybody see the fourth it's right there the pattern doesn't repeat for that domain i don't have complete data the font slash tasks.php occurs in all three of the other ones so now just by looking at the naming convention that this person seems to prefer because people are creatures of habits we can tie all four of these campaigns back to probably the same person sitting in the same room in the same city
possibly somewhere in vietnam um so just for fun um this is funsies i i decided to take all of my data and and throw it at uh at kumu and after it stopped whining i got this picture um and so you totally can't read that um but uh but what this shows right so um your uh your upper left and lower right uh so upper left is new new pos things lower right is uh neutrino uh i think anyway i label it yes i was right and in the middle 1992 06 19 wait what so i was super excited for like five minutes well i went holy crap i found somebody changing malware families just by luck
actually i didn't super excited and i do show you this to show that it's possible that if that is what i had snagged that it would be possible to draw some of those conclusions but um thanks to a blog post that hexacorn wrote in 2014 my hopes were dashed it turns out that that 1992-06 19 compile time date because i thought to myself i really need to run this to ground it turns out that this is a delphi compiler bug but initially i was like oh that sucks and it does mean that i probably can't tie a single actor to to two variants of this thing but that is still a useful piece of intelligence
to understand that that is a delphi compiler bug because what it tells me is one i have somebody using both variants of this malware or multiple actors potentially using the same variant or multiple variants of malware using this old version of delphi to compile code on windows additionally i did some research and discovered that that's a thing that malware authors like to do because it screws up some other stuff and makes it a little bit harder for antivirus engines to detect when it's built with delphi so now all of a sudden i have a compile time signature that if let's say i've got um you know profiles running in my network scraping pe file data out and putting it
into uh into a data set i might be able to find something that was compiled with delphi which is probably not a lot of the commercial software that i run and certainly not a lot of the new software that my devs and team are downloading onto our network but might be malware so interesting data nonetheless though not as cool as i initially thought so um closing thoughts so one automating uh both the the hunting of particular threat tools and analysis of the data they contain is absolutely plausible using clustering of static indicators to find relationships can definitely reveal the presence of an individual because their habits patterns and mistakes fall out in that data and finally there are seemingly endless
possibilities for pivoting right i just picked kind of four things but we could have gone on user agent string we could have gone on we could have gone on different packer types there's all sorts of different things that we could have pivoted on as we were looking at this data and potentially found more interesting relationships between the actors right so this is i feel like i've just kind of scratched the surface on this approach to working from binaries all the way back to actual bad guys so um and with that i want to take it a quick second to you know so i like uh like anyone in the field um you know i'm blessed to uh to to
to stand on the shoulders of some giants and uh leverage uh work for those that have come before me so they probably don't even know how much they helped me with this but alan wyatt and nick hoffman all contributed significantly to my work and i want to make sure that they they get credit for uh for helping bring some of this uh into existence so thank you to you guys all right um and i don't know if i've got time for questions or if i just got to get to the giveaways man how about one question okay um any questions
i've had trouble using that before because things like dot net and auto it um have identical for every single file ever generated that is absolutely correct uh import hash has some challenges based on the builder um so i totally agree with you um net using identical import hash makes it not a great individual indicator um and so again right indicator indicator selection when you're doing this kind of analysis is sort of important if i were working with a family that was primarily.net i would have dropped that because it just wouldn't have been a differentiator uh in this case there uh they weren't net so so it was it had some value but yeah that's absolutely a piece of it is uh
you i go back to uh the earlier part of the the presentation where i was talking about really getting to know the malware you're hunting uh by doing some reverse engineering and understanding that and you you do you definitely want to bring that context and those learnings all the way with you into uh staging your analysis all right what's that giveaways all right um okay i gotta think of okay um what language is the neutrino documentation written in that's correct russian [Music]
all right um one more uh oh um yeah so the the 1992 compiler bug what compiler has the bug shut out first oh don't give me [Music] all right thank you very much thank you paul