Viper Framework for Malware Analysis
Show transcript [en]
um okay so today I'm doing a lightning talk um and a live demo uh which is like going to Vegas and um gambling with the last two bucks you got and I already lost one um I don't have a display up here to drive my demos so this is going to be real interesting so please uh play along with me okay so before I get into talking about Viper or how to use it or why to use it um I wanted to stop and uh say thank you to the folks behind the Viper project um so it turns out that if you write blue team open source stuff you don't get the $10,000 bug bounties the
security researchers do for OD day so this is my way of giving back to the community uh so uh if you're not already aware um Claudia GUI B herder who's also the The Man Behind the cuckoo sandbox project Kevin Breen Raphael v um Alexander jger and about 24 other folks who have their name on the GitHub commit are the folks that make the Viper project possible um so a little bit about Viper what is Viper um at its gut uh it's really a repository and framework for doing static file analysis um it has definitely a malware vent I definitely have a malware vent in uh in how I use it and why I use it um but uh but you
can use it for just about any type of of static file analysis um it's guts or Python and SQL light uh which is nice because it makes it real lightweight easy to deploy to just about anything you want to run it on and it's got a fairly straightforward architecture um so it has a has a web UI which makes it nice for your entry level analysts it's got a metlo shell like command interface which is my favorite um I don't have an adapter otherwise I'd show you I actually I don't have any bars either um but I I am in vit work constantly on my phone um I have probably the greatest job in the world um so as a result of
that I get interesting alerts sometimes and I'm able to triage files quickly from a server in Amazon from my phone with Viper and then send emails down to the amend analysts and go hey I don't know you caught this but you should really go look at this and um I it's it's it's a lot of fun um kind of the middle stack the software stack is the framework code itself the framework also offers a a series of bre apis uh and it's got a module interface and they made it really really easy and we're going to show off all this stuff uh in in a little bit of depth here in the demos made it really really easy to
write your own functionality for the Viper framework so if Viper doesn't do something you want to do today if you can hack it up in Python um you know it takes you eight hours to hack it up in Python then in nine hours you can have it as a Viper module uh it's pretty easy to to set up and deploy and then the underline um there's a file store where all of the binaries that you check into the projects go and then a cite database that handles all the metadata and indexing so part of what was driving my desire to do a talk on viper is uh the what I'm calling the zoo use case
because I don't want to I don't want to come up here and and say that the Viper is the best static analysis tool in the field in fact it's it's probably not you probably would use it as a as your primary go-to and certainly not your only go-to for malware analysis if what you were doing was single file single incident triage analysis of one file right there are lots of individual tools that are better faster for particular pieces of the puzzle but what the framework really gives you is the ability to take and build a history of the malware that exists or that you found um either through information sharing and intelligence gathering um from other sources as well as what you
find in your own environment um and what's cool about Viper is and I'll show this off in a minute is uh just like uh um just like blogs or anybody use uh using uh like Confluence or jira work you devops all the things right um You can tag posts and you can tag people in posts well Viper has a tagging uh functionality that lets you define what metadata is interesting to you and then assign it to a file and then go back and search on it right like your own interesting indexes um so you might do that by varant you might do that by when you found it or you might like I'm obsessed with import hashes right now
I'm going to show you the value of that in a minute so where Viper really has an opportunity to kind of move the ball forward though is the ability to analyze tag our facts group them together and then iterate through those and then learn and because you've got them in a repo if you learn something six months from now you have the ability to build analysis capabilities into VI and go back and reiterate over your entire collection and the reason that I I call this the zoo effect is um you ever been in the zoo and and seen the animals and you notice the the signs where they give you know like the Latin you the genus and
the and the the species names um right the idea is is that we want to start building a lot of data around the relationships between different pieces of malware because if you've been doing malware analysis for any length of time you've come to understand that bad guys are lazy and the people that build B malware and sell it to bad guys are even lazier and greedier than the people that use it and so it's all just reused code right I mean there's some new bespoke malware out there but increasingly right we take this piece of functionality from over here from Zeus and this piece of functionality over here from dryex and we uh you know we
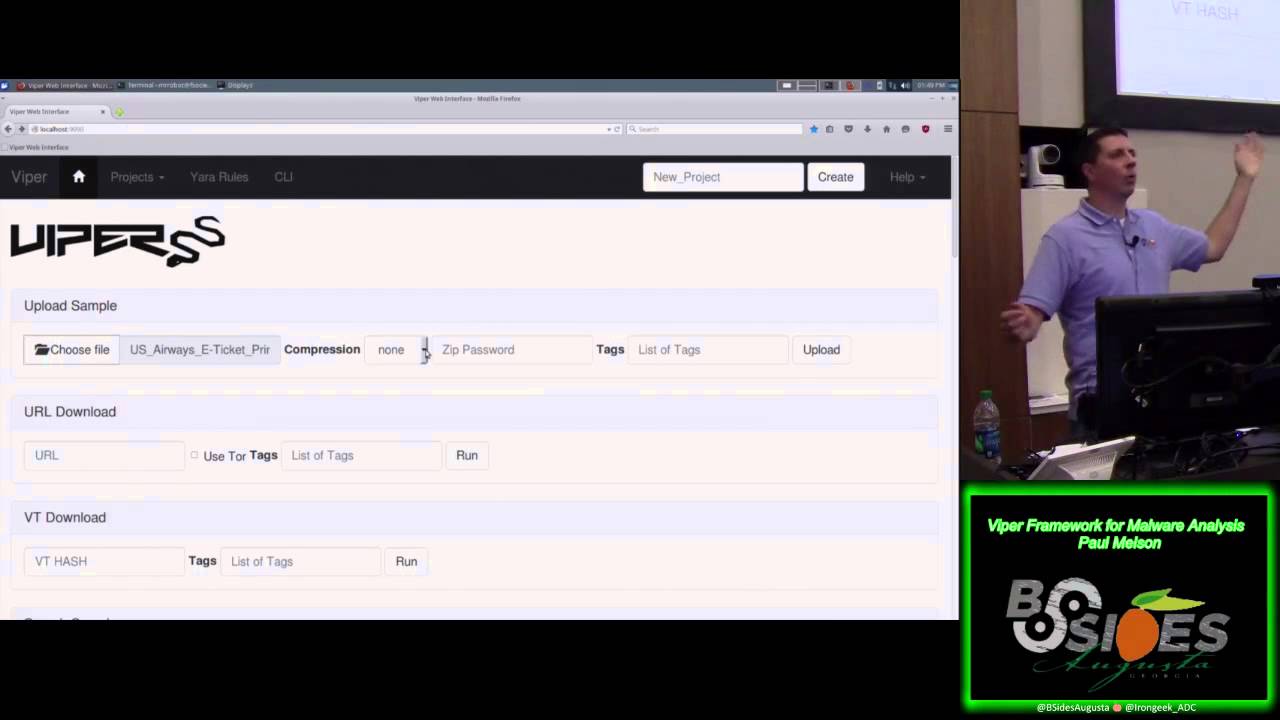
slap a new U you piece of C2 on it based on something we you know we saw from Ghost R and we iterate through it and we put it out as a whole new thing but it's really not all that new so this becomes a way over time to start discovering those connections in your environment um and there's some some interesting things to be learned um and some quick ways uh that we can do some of that stuff so that was really all I had to say about Viper now I just want to show you that wooho right um so we the here um all right so first I wanted to kind of show off the the sexy web interface that
Kevin BR for Viper um this is really slick just because you know it's a hey personal VI try and first I just I'll just scroll down into so you can see the repository some basic functionality on the front page um the web UI by the way if you're doing anything with Yara development uh this is fantastic because you can take a large number of samples of malware that you already know all the information about and if you're doing y rule [Music] development and so come in here build your rules edit them it has a functionality from the artifact to edit in line and then you actually have a plugin by which we can uh we can
run um y over a sample you can also go back through and look at all the different pieces of malware that have been uploaded into the repository um the database by default keys on shot 256 um this is useful to know when you're uh when you're working with the API if you want unique identifiers by session knowing the shot 256 value of file um is the key you use to interface with it I'll show that off in a minute and over to the right there you can see some of the tagging uh that I've done um so these values on the right these are all import hatches right so everybody familiar with P in and how that how value calculation works
for that we take all of the the imports from the p00 of the binary Genera uni c um and so this is like a it's it's an md5 value but it's not just the md5 of the file it's the md5 of a certain subset of contents of the PE header and it's interesting because it gives us some idea of um how how the file intends to run when it gets there and so normally you would think well this is a you this is a pack executable it's you know OB it's not all that unique to things but I keep see missing p over and over and over again and what's interesting is if we go
through thises across several different uh types of you know variants right some of it's NJ some of it's Manore so on and so forth so [Music] um if nothing else right um that gives us some some idea that there's some relationships there at least to how the binary is getting packed and that might be really interesting right typically we look at mv5 values as being somewhat low value right um in terms of it's trivial to take D exing raw binary repackage un5 deploy um but so some of these other static values are proving to be a little bit more persistent and reliable for detection so let's
um one other things that they did by the way I love this this is so culturally appropriate who everybody so what's the password to my zip infected that's right but so I love the fact that they thought that through though right everybody everybody hands the malware samples around the zip files so that upload happen relatively quickly you can see it here and now I can drill into this all sorts of information it break down start taging in here um I have installed the PS deep so for those of you that are familiar with fuzzy ashing do a fuzzy search and see if there's matches it's not working and then we can go to the modules we can ex individual modules so
maybe want to see this really hard to Myer sorry
um so this is the web UI um the other thing that is pretty cool about this and I I won't demo it for you but uh highly recommend it right so I mentioned earlier that CL the key developers Viper is also the guy behind cuckoo sandbox cuckoo integration is built in so if you got cuckoo sandbox running go ahead and put an endpoint uh config in to Viper to point it at your at your cuckoo server and you can go ahead and take samples directly from your viper environment run them through cuckoo and then it will tag the result in Viper with the with the cuckoo report so it won't actually reinfor all the the report data from
cuckoo but we'll give you a quick link so if somebody's already running through the same box you can go back through and uh and view it later right so it gives you a nice and um you uh triage desk to work from for for those artifacts um and let's you do you know one kind of one web interface to do both your static and dynamic analysis all right um this is the command line interface for Viper this is you know everybody's going the kind of I really dig this though I use it a lot um tying here I can go through all my stuff in my
REO and then I can do interesting things like ex search
this is another one I really like search string Das Capital H will we'll go through and look for anything that looks like a like a host fqdn or IP address hardcoded in the binary because that's usually a good indicator that something Fun's coming on um all sorts of things that we can do I'll come back and demo a couple others in a minute U but so let's switch briefly to code so I mentioned earlier that Viper's got a a modular interface that lets you write your own modules um this is a really really simple kind of hello world version of it so I don't actually uh bring in any outside code from Beyond what the B framework is already capable
of here um in fact this functionality of file. type is uh is readily available um inside of the info screen that I showed you earlier but let's say you just wanted to command that all it did was give you the same output as if you were running file from a command line uh just get the file Ty output can everybody see this by the way or is this hard to see good okay so
um so essentially reference um a couple of basic uh you know a couple of basic pieces of the uh the modular framework right can call it in Viper comment and core session work within the session and declare a module uh Define the initialization and the run and that's pretty much it uh instead of using uh standard uh you know print commands from python everything goes to a self log and you can declare which uh which logging level each piece of output has so that's a basic use case this is a little bit more advanced use case I yes yes it is um and so uh raise your hand if you're familiar with PD studio um and not seeing enough hands go
up by the way so if you do malware triage um your homework for tonight is to go out and download PD Studio 8.5 is the latest release out PE Studio has to be the greatest uh static analysis tool uh for for PE header reading on the available free code really cool stuff um my big problem is is that Viper runs in Python I could P into windows but I love Linux um so I had to go out and recreate uh my favorite feature which is the function Black List so um so what one of the things P studio will do is read in all of the import functions I told you I'm a little obsessed with binary
Imports and uh and it actually keeps a Black List these Black List are AVL files you can [Music] see I'm going to walk up to the screen sorry so you see see there a couple lines up where it's uh where it's calling in my uh that XML file that's just taken right out of an unzi version of PE studio and uh what we're doing is we're taking the file that's in the open session in Viper and we're just walking the PE headers uh iterating through them and then uh every time we come across an import we're just searching for whether or not it exists in The Blacklist file and if it is then we're just reporting
that out so we give you an example how that looks so we can P Imports pretty [Music] straightforward nice I'm going to have to choose
it nice Packer by the way right single in so but that's really interesting most normal files don't have just [Music] um so we can get a list of all of the Imports right so by dll here's all the function calls so that module that I showed you up on the screen um I rewrote and you can see here it's cross reference all of them so everywhere you see a bang in yellow on the left you can see you've uh you identified a uh a blacklisted function getting an idea of how many the functions that it calls are blacklisted is definitely interesting to give you some idea whether or not you've got a suspicious file on your
hands all right uh and for my next stupid bik trick um we how about this okay perfect so um I've only got two minutes left so I'm going to skip over running this one for you but um one of the big problems that Viper has is that I walked you through um some prettyy manual uis what if you had a large number of samples that you wanted to import and automated tagging for so this is a script you point it to the directory run this and this will access the API um which is right here on the top the top half um take the individual files upload them take a local hash of them and then reiterate through them tag
them with PD import has and any other tags you wanted to add to them uh but for my last trip there yes indeed so um my last trick I thought I would show you um how to Leverage The API to actually go ahead and uh build some visual analysis based on what's in the repel right so one of the things Viper can do is you can use SSD to do fuzzy hashing functions against all of the files as well against any individual file well what if you could iterate through all the files and then using networks which if you're not familiar with a node mapping library for Python and build an actual map of these
things
so so this is fuzzy glow you can see it just kicked the crap out of the API for a minute here
because we're going through mapping relationships and been pulling back all kinds of artifacts out of the repo to build this [Music]
table so here we have a node map of all the different samples with their names it's a little bit messy I probably some stuff we and fost clean this up you can see we're able to map all the different uh relationships between all the different families and some of these it's very obvious why they're related and other ones uh maybe not so much um they're definitely some where the lines get longer meaning the weight is lower so that there's some relationship but not necessarily a solid relationship suggesting that there might be some code ruse going on so U anyway a quick and dirty way to get an idea of you know whether or not items in particular repo
are related to each other using in this case
so least so um I'm going to open source all this stuff um but this is my dirty Floy to get over a th Twitter followers I'll be posting this stuff to GitHub on Monday and the announcement will go out on your Twitter account if you've got more questions or just want to talk Viper uh after fact this is where you can find do you have a giveaway um oh trivia questions trivia question for a BL handbook okay sure um can you delay quick trivia question um bo boy okay um all right so here's a really esoteric one I named I named fuzzy hillow after another project uh that's uh that's often ripped off in the security
Community if you can name either the project or the author of the project as book as yours after it is I ripped this off from after Globe rafy Marty