Unmasking Cybercriminals on the Open Internet
Show transcript [en]
so it's a real quick I just need to do an a/v test so so please bear with me the seals have nothing to do with the talk well that's all I need to do okay thank you thank you all right I promise I promise that will that will pay dividends all right excellent all right thanks sue so as Phil said I'm Paul Nelson that's that is my twitter handle up there the hackers the movie font so yeah and I I do cyber stuff and I hate bad guys and that's kind of part of what this talk is about so but Before we jump into the the fun stuff and the entertaining stuff and all of that I got
a I got to put a couple dollars in the in the jar so so the all of the main points that I want to make in this talk are really predicated on work that was laid foundationally years ago by by a couple of really really smart people in our industry and there's kind of a running joke among a few of the the attendees at the conference and just some of the other folks that work in the industry then you know when you invoke either these things you have to put a dollar in the jar so I did I did actually do that and I have donated in honor of David Bianco and might Clopper $100 to rural
technology fine so that's my dollar in the jar which means you know what's coming next right the period of pain so a quick primer if you're not already overly familiar with pyramid of pain this is essentially the concept that bad guys leave behind different marks right there's there's different indicators and and different pieces of intelligence that we can use in leverage for detection and actor tracking that are harder to get and I want to introduce the concept because the thing about TTP's is really when we say TTP's what we're talking about is tool selection and behavior and humans suck at changing behavior right it's really really easy to change the hash value on a file you
can literally append a null byte to almost every file format on the planet and change the md5 hash value of it but to change up the things that a person does is really really hard and so when people do some things that work for them they tend not to change and so if you can give visibility to those and glom onto those that tends to tend to have kind of a good life to it and so this is a point I'm going to come back to later in the talk but I wanted to introduce this and and the the second this is the world farm world's famous Lockheed Martin sniper kill chain I love cyber kill chain you can prefer
different models and different taxonomy --zz for this stuff but they were really the first ones to describe right you know an attack goes through phases and if you understand all the phases that an attack is gonna carry out then you don't necessarily have to focus on detecting the very beginning of the attack you can disrupt in the middle and really your whole your whole job is a defender and I am I'm a defender that's my that's my deal is to prevent the bad guy from getting to their actions and objectives right which means you have all kinds of space to to get in and disrupt what they're working on but one of the hardest things when we start
talking about threat intelligence and I guess this isn't in a way a threat intelligence talk and I don't want to you know that's threat intelligence with the lowercase T in a lowercase I but the it's really hard to get a good view of all the things that an adversary does right and the reason that it's hard to get a good view of the things that an adversary does is in order for you to observe them doing what they're doing one you never get a good view of everything that an adversary can do because they only do what they have to do to succeed right they do the least amount of work they do the easiest thing
for them to to progress right so you never know how good an adversary is it's unknowable right you you can't know you can know what they're capable of but in order to know everything they're capable of you right at some point they get disrupted and then you don't get to see the rest of it and that's the second part right to get the best the best telemetry the best information about how threat actors operate you have to see them operate right they have to succeed the best information about how threat actors behave comes from when they're successful and that runs completely counter to what all of us in defense right if you're in blue team right your
job is to stop those bad guys and stop them as fast as you can with you know right like you kill it with fire right like you know you know the contain with prejudice right you know the whole point is like as fast as possible disrupt that actor and what that means is is that you get to learn the rest of the stuff you'd want to learn and this is frankly the the challenge this is the tension between between the the defensive detect and respond functionality and the intelligence collection piece of it so and I'll get into why that's why that's important as we go on but so we're gonna start with one of the things that bad guys throw
away a lot which is malware right malware is disposable Palin right did everybody agree that like there's more malware than anybody cares to so there's so much man and and and I thought I thought early earlier on in my career naively that I could get to a place where like I had a really good understanding of all the malware and then at some point there's kind of a limit to what's out there and and the more the more I learned like it's it feels kind of just like a like a just a title way of crashing on the shore like there's just so much out there but at the end of the day it all has it all has
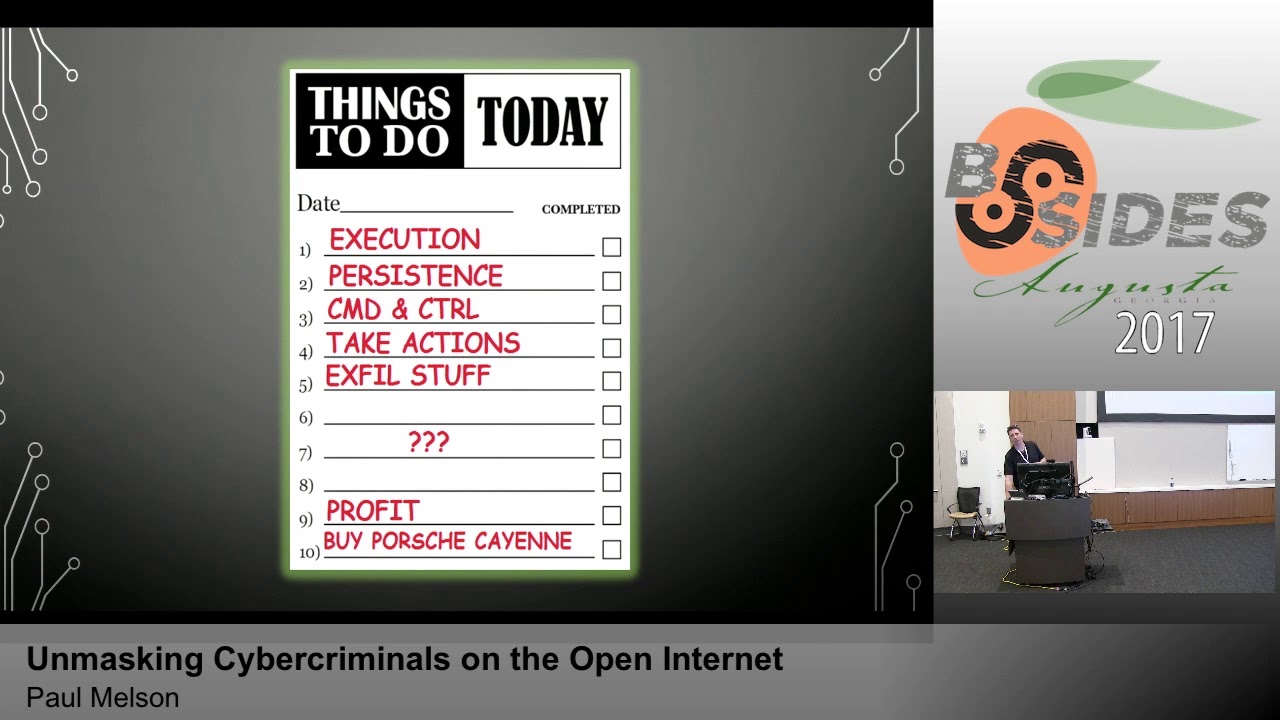
to follow kind of you know it's prescribed role inside the kill chain right it's a malware has a to-do list right and so it's yeah right it has to run somewhere right in a lot of cases it's got to establish a level of persistence you have command and control right because the likelihood that you're going to predefined a payload that you're gonna drop into an environment and have it run completely successful to completion and deliver the mission back you know that's a not never gonna happen but pretty close to never gonna happen so usually there's some level of interaction and reporting and adjustment that the the adversary is gonna want to do and then they're gonna want to take
actions and you know maybe maybe steal some data of some kind or you know or possibly worse right maybe maybe it's not exit raishin maybe the mission is just that seems to be a tactic that's on the rise in a number of in a number of arenas right now so and then and then somehow that that helps them make money so that they can buy their Porsche Cayenne because that's the that's the official vehicle of cyber criminals so let's uh let's jump into the trivia so trivia question number one so please raise your hand rather than shout it out the trivia question number one is who recognizes the c2 panel on the screen
okay so this does not wanna cry no no no says the screen shot itself is actually kind of a hint all right so all right I'm gonna end up having to make up some more trivia questions I guess that's fine so this is this is a newer version of the diamond Fox bond that panel in Diamond Fox's Diamond Fox is the star of my talk today Diamond Fox also known as the gorynych or I'm sure I'm mispronouncing that but Russians can't say you all correctly so it's fine it features features prominently in today's talk but but a lot of the stuff I'm going to show you right like this stuff diamond fox though so if diamond fox is
a it's a rat and a builder and the c2 panel that you can just buy right you can go on you know you can go on exploit that iron ore or HF or you know a number of other ground underground forums and if you got some so Bitcoin or some Eagle you can you can get yourself a copy of this and run it yourself and it's interesting because because I've actually started to see samples show up where it's it's Diamond Fox but the builders been back doored so when you run the Builder you join somebody else's botnet of a different family so that's pretty epic but but so anyway as well do has a lot of
functionality I first found this started paying attention to Diamond Fox because it seemed it's kind of so Diamond Fox is where black POS has gone to retire so one of the things Diamond Fox offers is a cards you know card Rams great being functionality for stealing credit card numbers out of memory they uses black vos is what it drops but in addition to that it's keylogger and the web form and RDP login passwords dealing it does screen captures and it can do email and spam relay right so it's kind of a Swiss Army knife for scumbags and it is one of several and and I want to make the point that it's one of several because we're
we're gonna get kind of a little bit deeper on Diamond Fox but this stuff that I'm going to show you you could do with anything like almost any of the of the commodity class rats out there are gonna have some of the same things going on with them that we're gonna talk about about diamond box also before I move on warning live malware so I'm actually gonna go pretty deep on showing some pretty real stuff you're gonna see a lot of domains and a lot of information I'm not obscuring I'm if it's obscured it's obscured for the safety of the of other potential victims or it's obscured for my safety so that I don't accidentally get into a gray area where
CFAA is concerned and that'll make more sense as we get into this but it is not obscured for your safety and it is not obscured for the safety of the bad guys now I don't care about them but I do kind of care about you so just you know if if playing around with malware malware that means is not your you know is not your not your you your specialty it's not your hobby you go slow be careful this is live in fact some of this may still be hanging out on the internet so so I want to talk about why we start with malware binaries in the first place and using PE which is the
Windows portable executable format why we want to pivot through PE files and what some of the things that we can do there right because this is the stuff they give away they have to deliver the payload you have to get some malware for the attack to move forward they can't obscure it I mean they can do some things to make it harder for signatures you know your antivirus and the rest of it but if you as an analyst or analyzing it they can't hide from you what's in it what it does if you're willing to work with it so a couple of things you know import has compiled time instruction symbols and so I've highlighted those if you
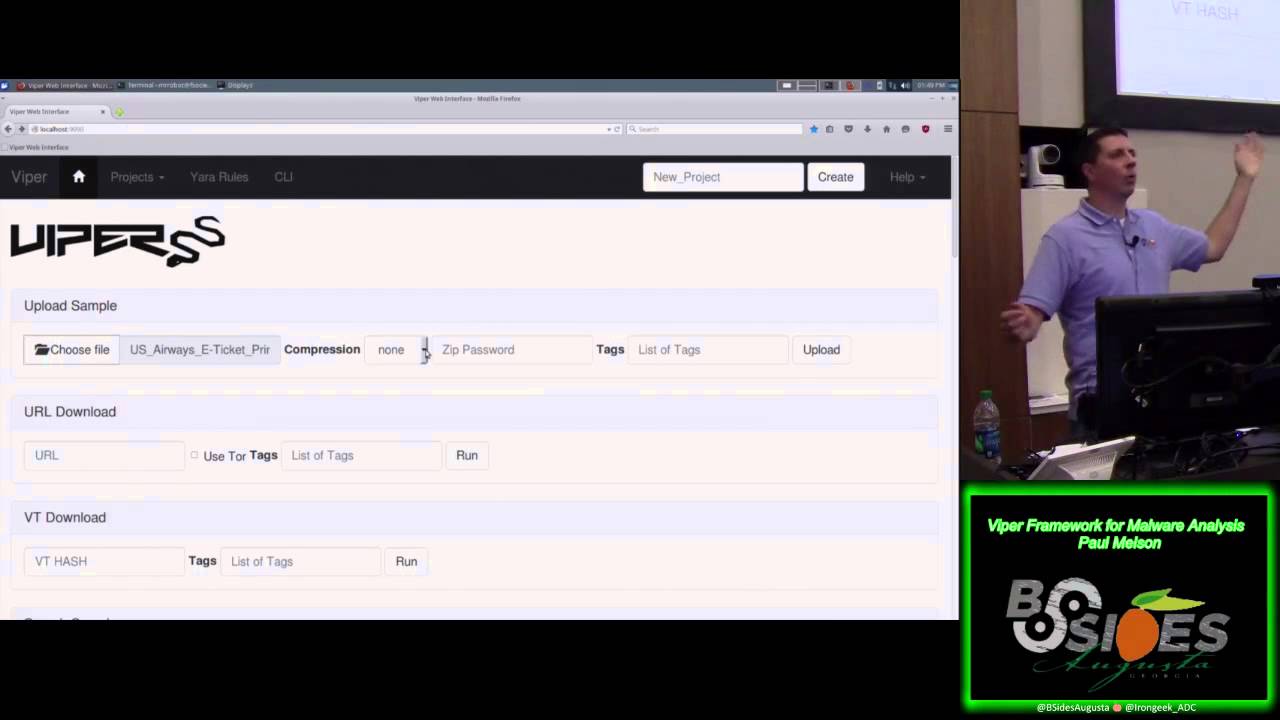
follow me on Twitter like Phil suggests you will see lots of screenshots mostly from my phone of me messing with malware and this is a screenshot at the VIPRE framework which is my you know favorite triage tool for handling malware but the VIPRE cognizant last year this is not a bike to talk so this is all the VIPRE but but so so you can see that compiled time I promise you that 2015 date I'm not showing you old malware that's interesting and I'll explain why in a minute that import hash to the import hashes Muse's and five of the contents of the P key files import table import tables are you know all of the the DLLs
and their subordinate function calls that that a an executable file hooks when it run in the operating system you can't not have an import table now you can put garbage in the import table so that you know nobody knows what you're trying to yeah like what exactly you're trying to call right so you can mess with some of this stuff but you can't not put in the import table things you need right so this one obviously right is based on that's MSB be m60 DLL so okay so back up trivia question raise your hand if you know what that tells us about the language this this file is written in the gentleman in the beer that's correct
this this the actual rat is built in Visual Basic do you need a ticket to the event tonight all right so for this gentleman so yep it's building VB as somebody who versus malar I hate VB it's probably the worst thing to to reverse engineering also so there's you'll run into that if you play with memory long enough there's lots of stuff that looks like it was written in VB who's actually run through Kryptos that use VB and then unpack the the actual malware after the fact because like I said analyzing visual basic file says is the suck this one is actually legitimately written in DB hmm so so it's still a thing and additionally you
know we were able to to use B walls bamps detect which i modularized and viper and pull the command and control so so that URL right there is what this binary phone home - to get its instructions on how to be bad right it knows what to do but not when to do it and who to do it to so the bad guy tells it to me this is where it gets its instructions so being able to extract the the config so here's the example though some of the static stuff I talked about you know import hash compiled time so this is just a simple multi go graph there's a couple hundred Diamond Fox samples so the
little yellow dots are individual instances of Diamond fox that have captured in the wild the green bubbles are the compile time extracted from the PE header and the red bubbles are the calculated import hash and so if you look in the upper right corner of the screen you'll see that 2015 oh six twenty eight day you'll see literally dozens if not hundreds of examples of Diamond Fox that are all compiled on that time right and then there's that one little red dot immediately below it because it only has the one stick to the one compiled time but that's the importation and if you were to go back and look these lines up it's that date
value even had import half right we have all these samples across the top now the chances that that that somebody actually went out you know the chances that that globally a bunch of a bunch of the ABAT hunters or would be bot herders compiled hundreds of instances of diamond fox at the exact same time are pretty low right so what this actually gives us is some telemetry and we could go hunt this right if you you don't have to know much more about the file than if it has this specific compiled time down to the second and this import hash it's gonna be Diamond Fox right that you could use that as a signature go tomorrow no
matter how many times they they they essentially reap if they don't change up the actual builder and compiler set that they're using this will ring through every time so so that's you know an interesting way to start sourcing and analyzing this stuff without having to go too far right I mean this is this is fairly if you're new to malware analysis highly recommend mark ox and Myers PC studio P studio is fantastic and it will it will turn you into a malware triage analyst in a matter of minutes really actually a great tool so let's talk though because one of the other things that we got out of our sample write is that domain and
it would seem based on the fact that that's a route path that seems to be declaring itself as diamond fox it would seem that maybe that domain might belong to our attacker it might not so one of the things that we got to be careful of right this is the you know it's totally a thing that bad guys will hijack other people's infrastructure and host their C to comms on there so that if the C 2 gets burned it's not their problem right and it can't be tracked back to them but pivoting through domains is fantastic right I love that with bad guys use domains because they leave a bunch of data lying around right so they have to
you know in order to set up that domain they have to go through a registrar and to go through the registrar they have to fill out a bunch of forms so you they can go through registrar's that will hold that stuff private for them but if they don't right we end up getting things like the name the organization name address and phone email address and the name servers and these are all these are all mandatory fields right like this this has to show up in the Whois record for the domain it doesn't mean they have to tell the truth but that might not matter right so so here we go trivia question number 2 or 2.5 anybody
recognize the website that this screenshot is from hands in the back I closed yes sir yep so that's domain tools do you do you need a ticket for tonight okay we've got our registrants information I will so a lot of the analysis that happens in this talk is not especially it's not an especially insightful but I'm gonna have to skip over stuff so that this isn't an eight-hour talk so just trust me when I tell you that that is not dudes real name and that is not as mailing address but some of the stuff that's in here turns out to be correct but we don't really know what yet the one thing I do know is that when we
don't have an obfuscated right like we don't have a privacy broker handling the the registrar that that email address has to be something that the attacker controls at some point in time it doesn't have to be their primary address but they the fact that it was used means that at the point in time of the registration the addit that the attacker had control over that email address and so that's important because that becomes an artifact right and the other thing that's interesting right well and also the name servers if name servers are interesting right you know I mean dove server maybe maybe not I mean that's that's that's unique enough that if it may be matched with some other hallmarks
we might be interested in that and it might tell us something so so the gentleman in the back childhood of another product name and this is a screenshot from that product where we pivoted on some of the same information it did some lookups there's lots of ways to get it Whois data and all I did was simply take the the name and address which like I told you before our garbage right like that's that's not the real mailing address of this individual that is not his real name but he registered a bunch of other domains with it which is sort of weird that he does that and you'll see why later that it's weird that he did this but he did and
actually if you if you google that name so I will so the address and the phone number purport to be from Nigeria I will use spoiler alert our bad guy is actually from Nigeria and that name happens to be the name of a famous fraudster who got a bunch of time in jail he was a who's who's a pastor who was defrauding people of money and and got sent to jail so it's interesting that he picked that name I don't know if maybe you know culturally that would be similar to somebody registering something is like John Gotti in the u.s. I don't know maybe maybe not but so that's a thing but anyway we've got some
more domain interestingly enough to we see in a couple of these we're picking up more email addresses and these are all good artifacts to capture because these are all things you can pivot on right like so he probably had control especially Gmail addresses right they don't cost anything they might be disposable and they might not lead anywhere but if you had control over of just the fact that you see them later gives you a link back right so we've got to think about this as capturing those unique data points they're useful and pivoting on that right and so that's what a lot of the talk is so all in all you we've got 49 domains registered by
this identity and and if you can see that line up there in the upper left that has the red box around it that one is especially interesting because we're going to see it again later and the so anyway even though a lot of these domains that I'm showing you aren't probably used in malware community control the interesting thing is it doesn't really matter because what we think at this point is that the actor had control of all of these domains right legitimately or not he had control of them which means that whether they are hostile now that could become hostile in the future because what the artifacts we have are here's the domain that was registered and used for command
and control for a piece of malware and here's 49 other domains we don't know if they're malicious or not but we know that they're under the control of an actor who's involved in our so if we don't recognize or have to do business with any of these domains from a pure detection standpoint why not why not detect these as well right let's pretend there see - until we know they're not because what's the what's the business impact and in this case unless you're in a particular vertical in a particular part of the world it's going to be none but because I don't want to spoil the surprises later is pretty good so let's talk a little bit about passive the
collection from from an intelligence standpoint this is also pretty useful right and so so I want to talk a little bit about you know what else can what else will malar tell us about itself like what else does malware leak right you can run in the sandbox and get some interesting stuff about it but so we know that so now we know where the the infrastructure is right the adversary infrastructure and maybe it would be okay if we passively interrogated it to see what what might might come and and so I want to talk about a couple other things right so people that run botnets are essentially going into a service provider and some administrator role for themselves
right a lot of rats are the core of them very similar to remote management tools like you would use on your enterprise network today and so a lot of the same principles that apply to making that work at scale apply to making malware work at scale like testing and so and that final bullet point there there's no place like one 27001 so this is a sort of tangential to this talk but but I made a minute Twitter bought earlier this year called scum BOTS that you can follow and scum BOTS does a Hunt's malware for me one of the most recently I turned it loose on paste bin which is which is a good chunk of that tidal wave
of now Twitter I mentioned like oh my god I had no idea which malware was on paste bin and the bottle eat wheat salad about about 70% of the malware it finds because the other stuff kind of falls into Uncategorized or on parsed data sets but one of the things that surprises me is this somewhere between 15 and 20 percent of the malware the it rips the configs from halves the c2 of one 27001 and and when I first saw it I initially thought one that Ryan was trolling me and that to that we had people that were just playing with builders and testing like the Builder itself just to see if it could go out
but like you know just making mistakes right just clicking next too fast and like screwing something up right and then they would go back and learn but actually as I started going back to some of the static pivots I showed you earlier with like the Builder yeah some of the toolmarks from the compiler of the Builder of the region and some of that stuff I started realizing that I could tie stuff going live with one 27001 to being followed hours later by stuff that had live c2 and who's probably built on the same system and bought herders are unbelievably fond of installing their rats on their own computers to connect to their situ and test and make sure that all the bad
stuff that the rat supposed to do works that sounds potentially interesting so back to my earlier question what if we were to possibly interrogate the command and control from our diamond fox sample so this is this is our specific actors diamond Fox panel or more correctly my mirror of his panel if you take a look at the URL you'll see that's all local on disk and we're gonna spend some time with this guy's panel so caveat time so CFA has you know lie lays out specifically certain things you can't do and in no case did I would I or can I recommend that you would infiltrate or interrogate another computer that you don't have explicit permission to access
by using a stolen or found set of credentials or that you attempted to exploit any sort of vulnerability to get access to anything that wasn't otherwise openly available to any browser that might connect to a website on the public Internet that is a hard line I did not cross here and the reason that that's a hard line that did not cross here is a I don't look good in orange and B then the hard part with this is is that we're gonna look at this guy doing stuff to himself but we're also going to be in an intermingle with potential victim data so there's a lot of data I just can't in good conscience show you because it's coming
from other people's systems and and since you know they've not you know it just wouldn't be the right thing right so we'll leave it there so so yeah word what good's a keylogger without logs not very good isn't it I mean that's kind of been the name so what happened when our bad guy decides to test his tools and what he's testing with is a key logger and then if he decides to log into his own panel and then he logs into his own domain hosting control panel and then he logs into other customer wordpress panels so it turns out that our actor also has some legitimate appearing businesses including one where he does web design and web hosting for in
particular he focuses on the the entertainment sector he works in he supports a couple different kinds of businesses but but in particular oil and gas and musical entertainers based in Nigeria so so yeah here here we have him just kind of owning himself and leaving his password and his own log files so if you wanted to take control of his body head and his symbol is going out scraping the logs off of this and logging into it but that would be a violation of CFAA so I did not do that and you should not do this so more customer wordpress logins remember when we did that domain pivot I told you you know pay attention to me
we're gonna see it later there he is logging into it so this is this is useful information on a couple of fronts right this is useful because we know now one not only does not only is it really likely that the registrant and the Bach master are the same person right but also that what we're looking at here is not a victim but is the actor right like we're getting really get confirmation on two things right one he has control not just of the domain but of the system itself and that the the activity that we're looking at a particular time range inside these logs is the the bomb master himself and and and this is borne out by
by some dates his real victims that start to roll in for another 11 days after the testing so it's a in this case it's a nice window but we still want to be cautious so and you can see there a bordo means there he's just I mean he basically logs into every WordPress panel that of all of his customers so and and and he doesn't stop there it's I pages pages and pages of logging into different accounts like one of several Bitcoin wallets he appears to control like his is hidemyass login so and also some more email addresses right so here we have them logging into to Google with some other email addresses and what's
great about that right this is here so you've got in you you've got more email addresses to pivot on so we could go back to domain registrations we can go back to us and searches on Google we can you can you can start trying to build more and more around the identity this actor based on the information that he is providing us in Bonhams here let's see what else oh here's much twitter accounts that he controls let's keep an eye on on this bottom one down there because I think we're gonna see that again let's see what else Oh Facebook developer logins because in addition to the websites he hosts he also manages the social media presence
for several of the businesses there's websites for so of course he's got them all tied back to a single developer account and you're gonna keep seeing you some of the same email addresses and the same names over and over and over again right yeah we saw and again there's that there's that domain again two more times from earlier let's see okay final trivia question so can anybody so first can everybody read the the domain that's highlighted in red if you can't read it that it says in detectable net anybody raise your hand tell me what in detectable net is okay well I'll have to make up some more trivia questions later all right so in detectable net is a
hacking forum similar to exploit Dada N or hack forums net and so so maybe later we see him use this site to do some other stuff right but but this is where he's I mean yeah this is I think my via for me this is my confirmation to scumbag right like this isn't just some guy playing around with the thing he found like you know he's legitimately actively involved in in cybercrime and has a presence on performance which by the way and you'll notice I didn't obscure this he's using the same email address that he used to register those domains to like have an undetectable Sinemet login and I'm not sure how without violating CFAA you
could get registering email addresses off of underground forums even the known ones but man if you had those think about like the Intel pivots you could make with those I'd be pretty cool all right so cool we've also got like his IBM login up here and - what else is on the Instagram accounts and stuff so so I mean yeah I mean we pretty well have like at this point yeah if you're a no saint analyst right this is a dream come true like you got you've got an actor dead to rights tied to multiple personas multiple domains multiple social media platforms and now you can start building out and starting mathas interaction see who else this person's
talking to the rest of that but what about some more what I would call actionable intelligence right from the defense side like okay so here's yeah we have a diamond Fox you know file you know a rat and we have in CTU and now we know who the bad guy behind it is and then it's you know or at least we can we can start to build a profile around the actor I want to be cautious about saying that we know who he is right because up to this point the names and addresses are fake right so definitely not enough to order a drone strike or handcuffs but so oh yeah I love long because his rats
not done with the logs so so in addition to in addition to all of the logins that we captured with with the password capture for web forms he also walked literally every keystroke for a week and a half the truth panel one I hope I don't type his back as this dude it's pretty awful I mean some of it some of it to be fairs the logging format almost but we can see here right at the beginning in this he immediately like so cool I got my guy my bot is now checked into my my panel and my testing is going well and I haven't bothered to uninstall it now I'm gonna start working on weaponizing the doc so
here you can see starting to prep from malware delivery document dot exe is the same file as I showed you at the beginning so here you've got that window name the the red is window names for the window that he's typing into and so you you can see he's got Anka log Multi exploit builder kit so it's Anka log if you're not familiar with it I wasn't before this but it's it's a office and PDF document exploit builder it has some older runtime exploits and you can just do interactive click to run but it will let you load a payload URL into a script inside of a document or a PDF and then if the person is it is you know
unpatched not running antivirus and will click on anything and keep clicking yes until it stops offering some things to click which is not nobody at your company or line right it's not nobody it's not everybody thankfully but but so so it's not the best exploit builder but it's you know probably well in this case cracked by hex 22 so so that's cool these netiquette paper tools and you can see them you know starting to work with and there he is staging you know and you are all those hashtags are there are actually HTML miss renders of /so so you can see him starting to build the URL for a Python script that will do the embedding for him we come back here
here he is actually opening up Microsoft Word to make the doc file that he didn't have when he ran the script the first time so he'll eventually get it right if you can see the words in there it says potential I think it probably was maybe said confidential and the keyloggers not great or maybe it just says potential document below I don't know he's not trying real hard the rest is the the Python doc builder and script running down here so he completes and he builds this document what I don't what I would like to show you I also don't think it's appropriate to show in a very public forum like this is the rest of this where you can see
him do some some spear fishing and some targeting with the with this right so we get we get to see how he's delivering it it's it's its email it's yeah he's trying he tries about this hardened email as he does here with the doc but but unfortunately that's that turns out right like I said earlier right like bad guys only go as hard as they have to go to succeed and it turns out in his case you didn't have to go that hard so so anyway so that's kind of cool because we get you know we get a look inside of that so one other thing that I just kind of wanted to show off is some of some of
the other stuff that the panels leave lying around right so these image files right are part of the panel kid and so we can pivot on these as well google image search for the win and there's somebody else's diamond fox panel another domain that we can you know so this pretty low tech stuff right like just get a collection of images from from different malware panels do some Google image searches and and you know if Google's crawled it which yeah it doesn't always but sometimes it does if Google's crawled it and seen the image sitting out there you can find the the domains of some of these panels hanging out there so that's pretty awesome to it again more passive
intelligence collection right so let's recap a little bit so what did we learn right so we we've established an actor identity we established that this person has control of domains and social media accounts we have some comms info forum a list of email addresses that vide has control over we have a phone number and it'd be interesting to see if that phone numbers at you know legit we have a Bitcoin wallet we have some other accounts that again if we were willing to violate CFA which I'm not you're not we could get more Bitcoin wallets associated with him and and we were able to get toolchain in TTP's which is view is fantastic right because going back to
going back to kill chain earlier right we now like now we've gone from a single piece of malware a couple of quick pivots and just some basic analysis right I haven't done anything especially high-tech here right I mean I did that multi go thing but you could totally have skipped that to get the rest of this and so yeah right so we've got the delivery exploitation installation and command and control and we don't know actions and objection active yeah we don't know what his actions and objectives are but we might be able to guess based on some of the targeting info that we gleaned as well so you know yeah we we've got great visibility to
the actor actually weaponized I mean delivering their payload were yeah we are all up in his c2 it's fantastic this is yeah but as from an intelligence perspective to work back from something as simple as a malware sample forward to this level of visibility is kind of in my baby that's a big win right like highway I wish every adversary that we build profiles for on my team like I wish we had this kind of telemetry so and let's let's you know come back and visit the Pyramid of pain and I paid good money for the use of this slide so so and we got everything but network and host artifacts out of this this analysis
too right I mean we basically started with with a hash value mat a tool and you know we were able to pick up everything else along the way now I want to clarify that what we have is a set of TTP's for this actor right and and we could check that that last box the network and host artifacts if what we were starting from is a malware sample recovered from a victim system on our network right we just you know we collected this sample from from the wild and so you look it wouldn't be too hard to get this going in a sandbox or yeah even uploaded to like hybrid analysis or one of three tools and gets him in this
telemetry to you right we have everything we need to check all those boxes but but back to my point about we have a set of TTP's for this actor right the value of those TTP's to us long term as is really dependent on how much success the actor has right there are two things that make actors pivot right one knowing that the cover is blown and that they can no longer go to non-extradition countries for vacation and two is that they don't work and really it's the other way around right they change when stuff doesn't work right this is I'm making money so if I'm not making money I'm gonna change up what I'm doing till
I'm making money so just because we've observed an actor trying a thing if we don't have a good valuation of how successful they were we don't know that they're coming back to these TTP's or not so like I said I'm not sharing a lot of the the victim activity we could say that he's had some success but not a lot I wouldn't be surprised to see this individual pivot again perhaps slowly but but I don't I don't think that I don't think that he feels like he's got a winning formula here I'm guessing he'll he'll make some adjustments as busy as he moves forward so that brings me to my next point so let's talk about
Intel games what are the things we still don't know I mean like if we really want to own these bad guys right if we really want to know like everything we can know about them what don't we know like so we still don't have a real name still in another residential address right so ergo no handcuffs or drones right we don't have any photos of the subject that we could handle law enforcement to support put some handcuffs on this person we don't have any information about known associates so was there you know anything else fun that we might want to collect about this person to who knows but let's see shall we so let's go back to that phone number
from the domain registration and start doing some public record searches this is his basic Oh sense stuff man I just googled the the number and a couple of different formats came up with this one and we come up with a Sam but in this case it's a Samuel mcclain a different address but actually in Lagos Nigeria so what happens if we look at social media profiles Oh check it out like now we have a name associated with this guy and oh hey remember that domain and that email address from earlier so this is your guy right like this is this is you know 20 minutes of googling around and we've got a photo and social
media presence that appears to be legit and an intentionally public for our guy oh and remember that Twitter account that he had control over it's the one that's associated with this event promotion thing he's got going like tacked to the front page of his thing right so like we're just getting all of that like correlation or just dialing it in right like like there's multiple pieces of information that support the conclusion that this is our actor so what else right known associates keep searching on that number we find some more Facebook's here's here's that same number being used as part of the real estate deal on Facebook which was sort of a weird pivot for me and I
thought that it might at first just be a typo but it turns out that it's not so that name there that Nick dunamis venomous he is also in the event promotion and a music production business and actually without going too much further but so here's a here's a picture of Mick behind the camera this is he is definitely an associate of Sam's you know without having to violate CFA and email problems that I only have to assume are there we're able to through some of the other targeting information correlate some things about make and some things about who this rat was intended to go to so and by the way it lets you know if that wasn't enough you
know recognize make he's hiding back there in the back but he's also in there with with this guy in the front who is this guy who to be clear I don't believe this individual is directly responsible for any of the cyber crime stuff but what he is responsible for is working with both Sam and Mick to put together this music video and you you can't be you know so this is I had to finish on this in this way [Music]
[Music] so supposedly I just wanted to like holy cow day like I am I have a music video produced by the Bob master and his real estate scam buddy it was it was a weird and random ending but it was so much better than I ever imagined when I set out right cuz in a lot of cases we end up with dead ends and the rest of that but I thought you know that was just too that was too much fun to not share that these dudes produce the you know recorded this guy live and produced a music video so alright questions so I did not see so there's no logs in the SMTP server for portion of the of the
bottom so he is not he is not here Nigerian prince sorry question how did I get access to the admin panel that's a that's a great question I did a little bit of trickery with the user agent string so so Diamond Fox comes precompiled with the same user agent string in it so that's I guess I kind of yada yada it over that that's another good one if you it's kinda it's got a my app it's got an IU for my app user agent string hard-coded into it so you know that that tool set is actually pretty dead legitimately so you see that outbound from a network more likely than not it's it's diamond fox and so anyway in this case that's
all I did was is it's like a one-liner to begin script against against his directory and then there are a few things that I come in know about Diamond Fox like the default log directory is logs so it's could crawl doesn't get it the first time you can just append that to the the control panel or move up a directory or move down they do a couple of other commonly using so so yeah I didn't actually get access to the panel I don't know what his password is and I never had control of any of the bots that were connected to it all I did was passively recover with W get the actual log data to assess what was going on and
fortunately for me the the first and longest running bot associated with his panel was him so which was a fan fantastic and super convenient but like I said happens way more than you would imagine so other questions in the back
so so in this case in this case in this case I'd like to take that question out so one last question we're starting to see so at this level know they're all still pretty terrible at OPSEC there's it's hard right because at some point the guys that are this level either get better or get not right and so keeping visibility on the ones that get better is pretty hard because you don't you don't always get all of this right I don't always get dudes Facebook profile baseline based you know based on pivoting off of a single malware sample that yeah but that was what made it a good talk is it was extraordinarily deep so but but what I would say is is that
there is no shortage of people playing in the low-end commodity space with terrible oh say sorry terrible OPSEC and the reason is is they don't need right they they don't need good object to be successful enough to make it worth their time right alright I'm told we're out of time so thank you so much [Applause]