Getting Started With Vulnerability Management
Show transcript [en]
So this is my topic. Um it's all about vulnerab vulnerability management and I will be taking you through what I've done so far. Um I'm a beginner. I'm trying to get into cyber security. And so um in trying to gain experience um I want to share what I've done so far with you. And so I created a lab and then um I try to use the N framework and then um sticks to try and then um manage how the vulnerability appears. All right. So who am I? I came from Ghana um two years ago to pursue MSE in information and cyber security. Um during that period too I got the opportunity to um volunteer. Uh this happened in um
London a couple of months ago and then I've been also going to conferences. That's what at least they told us. If you want to get into cyber security get network and that's what I'm trying to do. All right. So um let's start with vulnerability management. What at all is vulnerability management? Um so it is basically not just scanning you are not scanning is part of vulnerability management but the main the sole aim is um to detect or identify and after identifying what happens next is um you try to remediate or you solve the um whatever problem that appears and not just solving in trying to solve I mean you'll come up with a lot of vulnerabilities
um when you do scanning there are low vulnerabilities high medium a range of them. So how do you determine which vulnerability to resolve and that's what vulnerability management is all about. So these are terms that are related to vulnerability manual. You come up with them uh with these things a lot. Um we have the uh the NIST framework. I told you about it. Um what it stands for basically they develop frameworks um that helps companies I mean worldwide to help them improve their cyber. So a couple of frameworks we have the next um 853 800 um uh is it 57 or something I forgotten but I'll be dealing with the next 853 which is um security controls
and then um mechanisms and then also the sticks. So sticks are just implementation guides. Um primarily um sticks are supposed to be used to harden systems. Okay. So they are just guidelines that is guiding you um in improving whatever system that you have. So we have sticks for every virtually everything and it is it is mainly developed by the uh United States Department of um defense for its contractors and subcontractors and uh it is like I said to help them improve their security configurations, systems configurations and anyone can use it at all and it's it's a good thing if you have you you you have a machine I mean we all have machine you can use it implement it and then um
you're good to go so these are the terms that we'll be coming up with in the talk so why this talk so I I gained um an interest in cyber security when I was in Ghana I was working in um in the government like the council. And so I came up with a lot of um um uh things that I I I I saw needed to be solved and [clears throat] cyber security um happens to be those ones. And so I tried to understand and cyber security is very broad. Uh so I wanted to really go into explore and then identify my area of interest and uh I think I found it. I found um blue team
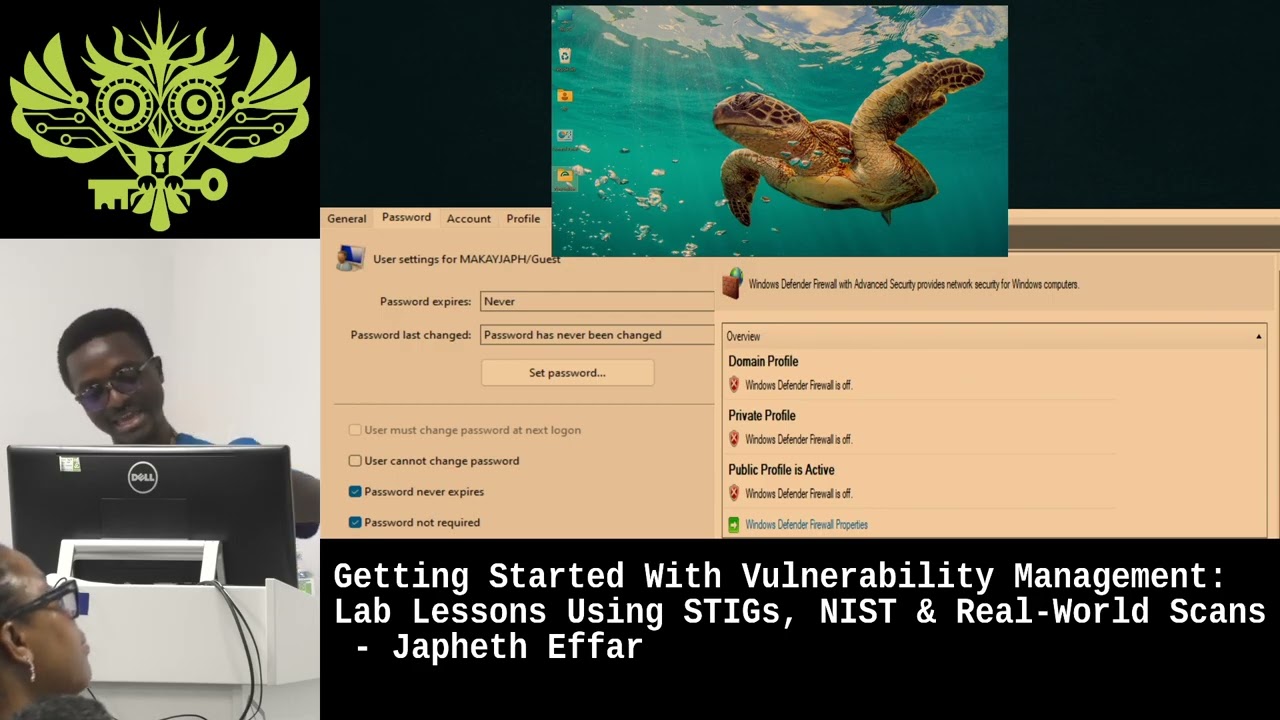
specifically and then vulnerability management and um as a fresh a fresher or a first timer how do I gain experience? So during my exploring and then I chanced upon this um this wonderful guy he he he he does a boot camp online and then I joined and honestly speaking it is one of the best you get hands-on experience and this that's the main reason why I have something to tell you today. So I joined this boot camp and then I've gained some experience hands on. All right. So what did I do then? I spin some VMs uh introduce some misconfigurations. So I'm trying to mimic a real world scenario. How do I go by that? And this is a typical example.
You look at your right side. You see that I've disabled the firewall which is a a security vulnerability. Firewall every every system needs a firewall multiple layers by the way. And then but the left side I introduced a guest account into the system and as a guest account there it needs some privileges. It it shouldn't have certain privileges so so to speak. So what I did was I give the guest account administrative privilege which is very serious. The password never expires and then it doesn't require any password. That is very serious. That's what I did and all this why I wanted to find out what will happen and it left the system exposed. So I moved on
and then scanned. That's the next step. I scanned with tenno. So tenable basically um is a [clears throat] vendor a cyber vendor top one such you have and and the others tenable is also there and so with with with tenable I I was able to you know identify certain [clears throat] um vulnerabilities there are many I we we'll come to that and then one thing about tennal is also um the sticks that I was talking about. Uh it have the guidelines already there. So when you scan the vulnerability, it just check your system to see if it matches. It audits the system and if it matches or it will check which one matches and which doesn't and then it give you a
report so that you go ahead and then remediate or resolve or resolve. That's what happened. So I think I will show you a brief about uh what the turnable is. So how it works. These are just screenshots. I'll show you the real thing how it works. Uh so that you have a feel of so this is this is the interface. Okay. And so to get to to to scan scanning for any vulnerability takes between 30 to an hour and so I mean our talk is not going to allow us but I'm going to show you how you can go about this. You have um so this these are this is the this is the interface. All right.
So and these are the buttons. We have the scan. If you want to scan you come here. All right. For a stick guideline, you need to create a template. And so you come here, create template, you go to advance.
Okay. Yes. And here you just apply. You give a name to the scan. You see that I've done so many of them. Um you can just give the name here. You you you you just supply whatever is necessary. All these are not needed. Um [clears throat] you come here discovery. Yeah. So basically you decide what is most important is this place the compliance and that is where the state guidelines are. Okay. So you have you search for Windows Windows. So yeah, this is Windows.
Yeah. And then you look for the stick.
So as I was saying, you see we have stick for so many things. You can see Oracle server here. You can um see so many of them. Um
Yeah.
Yeah, we have it here. These are Microsoft Windows 10 stick and then boom, you have it. So, these are the guidelines. You save it. I'm not going to do it. I've done it already. And then you scan. You come here, you create a scan and then you select the templates. All right, you select the templates and then you provide whatever credentials that you need to and then you scan. So when I scanned I found over 100 audit field. I'm going to show you and how I
Okay.
Yeah. So this is the report that generated and it's over 100 audits. So password must be at minimum be 14 characters [clears throat] which is something very common that we take for granted. Um built in Microsoft password complexity filter must be enabled and a host of them. All right. So now we are done with the and this is what I came up with. I chose the most critical. They were four high, two highs and then two medium mediums. Account must be must be configured to require password expiration. Um the minimum password age must be configured to at least a day. They are all medium. Password must at minimum be 14 characters and the password history must
be configured to 24 pass password remembered. Now how do you decide that's where that's what I was saying but it's part of the vulnerability management process. How do you decide which one to remediate first? Because in the I got to understand that in the real world like you you you like I said you find 100 are you going to solve everything the the company may say or your HR or whoever your boss or whoever may say no don't don't touch this we want you to do this but how in the end if you're given parameters how do you decide which one to remediate first and that's what vulnerability ility management is all about. So I chose the these two
uh password history must be configured to 24 password remembered and then password should be 14 characters. I based my solution on these two. The 8020 rule. What is the 8020 rule? So in vulnerability management um the 8020 rule is saying that 80% of security breaches could be prevented if 20% of um vulnerabilities that are very high. Okay. vulnerabilities that when it is exploited could cause harm, irreparable damage. If those 20 just 20% of those vulnerabilities could be remediated, it could prevent 80% of most breaches. And this 8020 20 rule 80% 20% rule is not only in IT or cyber security or whatever is applied everywhere even in in my research I found that is applied
even in business and the corporate world everywhere. The next one of importance is the risk prioritization in which the next um 500 853 comes into play. So then it's 5 8 um 53 is saying that you should focus on controls that directly impact that directly mitigate most of the vulnerabilities. Okay. So what it means is that um vulnerabilities that will be exploited easily needs to be remediated first before anything else. And so this is how the two um vulnerabilities were chosen from the initial four that I selected and then I remediated and then I risk hunt again. I went through the process again and then it came back that out of the 100 audit field it came to
about 50%. Which is I mean it's not ideal but in this in this situation um we are limited by resources so we made do with that. So what can I say about this that in this whole process small things matters. You see that we take grant we take for granted like um password password age uh password length. I was doing a research and um the most common password in 2025 is still 1 2 3 4 5 6. They said about um 60% or so of the like password that we used uh in 2025 come on is still 1 2 3 4 5 6. So you see that the small things really matters. You shouldn't over complicate things.
Just go by the rule. You need 14, you need 12 characters or you need um upper case, lower case combined with um figures, um special characters, point of view. We should take it very serious. And then the last one is security is everyone's business. So you realize that in a in a typical I' I've worked in a like I said I was working in Ghana and u people people just say look I'm nobody like nobody's going to attack me. I mean just do it like I'll just give two just some like random name for a password. People don't care about the security of their system. But but by the time you realized you see that we use
similar password for almost every account that we create online. So for all you know you have used the same password for virtually everything and you are there you are saying nobody I mean I'm less important. Nobody is going to attack me. Nobody's nobody needs my credentials for nothing. And then fortunately [snorts] they they they get their hands on your password, your credentials and the whom your credit card, your bank bank account is being emptied and then you'll be saying ah come on how what's happening. So security is everyone's business wherever we are. We need to take security very seriously. And so that's the end of my talk and this is my LinkedIn. If you want us to connect,
you can scan and then we take it from there. Thank you. [applause] All right. So any question?
All right. >> You got any thoughts on the differences between the dies and question? >> Yeah. Uh the question again I >> do you have any thoughts on the difference between the dieser sticks and the CIST sticks? They're both hardening guidelines. >> Yeah. So basic so yeah. So stick is guidelines for any um system. But the DA the DA one that I know is for the um I forgotten the the full the name. Yeah. Yeah. The defense industry. And then the other one I don't know >> CIS is sort of just a general benchmark. >> Okay. >> Available. Okay. >> They serve a similar function. Mhm. >> I think different focus >> different focus. All right. Thank you.
Any more? Yeah. talk when you talk about management. So are you seeing the whole terms of obviously when you're doing the ideas you're doing it for someone else organization and having say that that will fall under some policy saying you must do this. So are you looking at the end to say this is what we do this scam and then >> identify >> what do we do who's responsible for the mediation you know and on the prioritization are you also thinking right it could be a high risk by the scanner >> but to environment are you looking at the ant or is it more case of this specific to going through um proper reports and then
>> so for for for a a good I mean a good analyst that wouldn't be the best thing your job is to to to to do a thorough work present the report as it is but we all know that I mean in any organization they are I mean interest so they are bound to happen like your your your your manager um or sometimes even some systems. They have this legacy um softwares that if a vulnerability is fixed, it's probably going to cause them for instance maybe in a bank they are using um um a legacy software uh or like a Kubal or u forran for their programs and then there's a new update. You've you've done the
update. Okay, if you do the update, there's a probability that that update that update will cause the system down. And so what do you do? You have to leave it. Let it be. Okay? Or better still, you consult your like your head or your general manager, the board or whatever, and then you decide which one to remediate. >> That's what I was saying at the end of the day. vulnerability management and risk management. They are put together vulnerability uh analyst but at the end of the day the business decides to system the decide whether
end to end or just >> I think there has to be a balance. >> There has to be a balance and at the end of the day like you said the bosses decide and you have to comply. All right. [laughter] Okay. Thank you then. Um that's the end, right? All right. Thank you. [applause]