Fantastic Attack Types And How To Find Them by Randeep Gill
Show transcript [en]
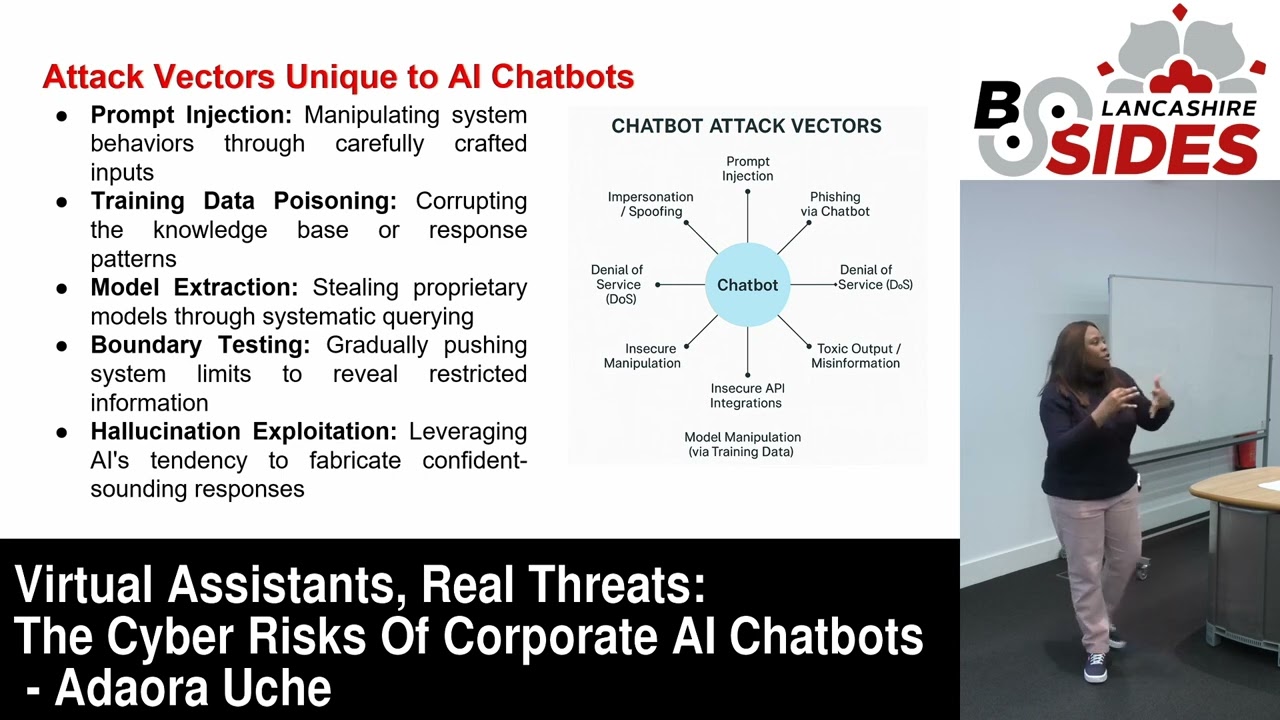
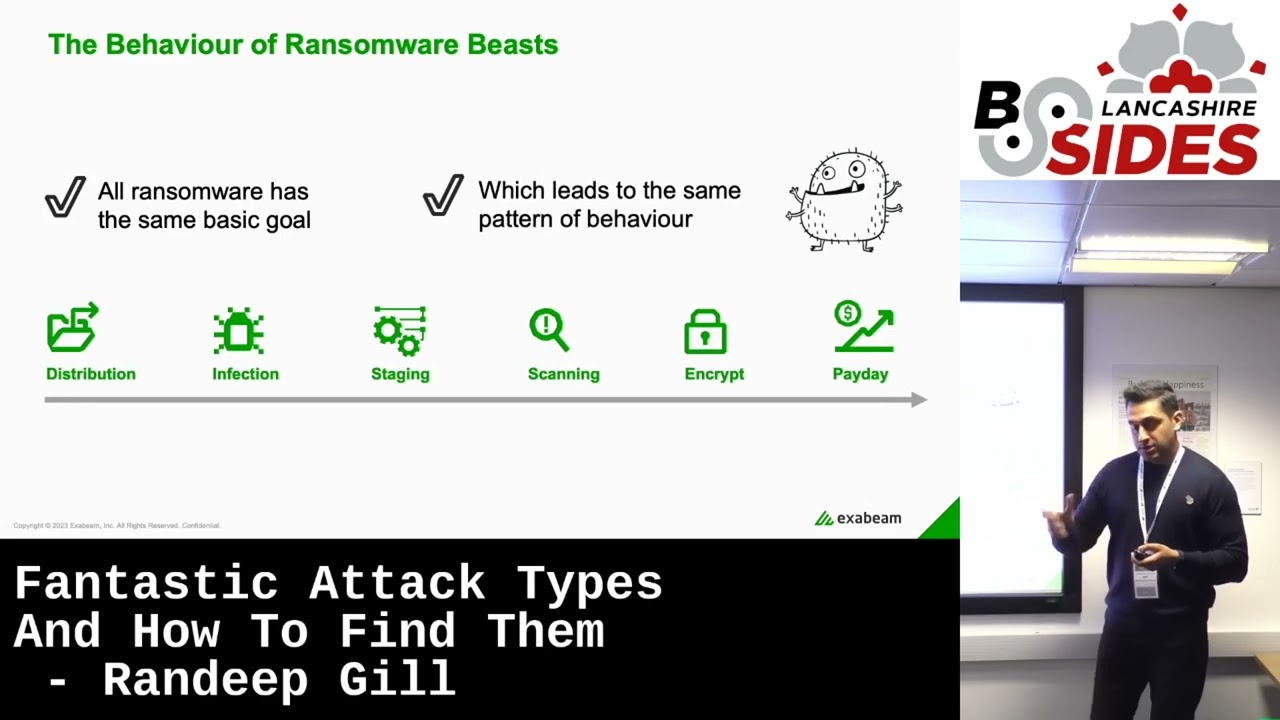
[Music] I think the first thing I ask is how much can I move as much but also how much time do I have I'm standing between everyone and lunch I think I probably drinks as well I've got 150 odd no slides if you're looking for Harry Potter this is not it sorry it's not that fantastic Beast about fantastic attacks but similar stuff I who works in a sock anyone here Works in security operations center who's a student cool stuff who's there for the free stuff oh yeah oh yeah beach beach balls frisbees we've got those and some pens as well um thanks for my presentation now this is more of a guidance we are going to talk a little bit about what X-Men do if you don't know already of course we will but certainly we're going to give everyone some ideas of maybe some guidelines we can use when we work in a soccer course best security practices and based on the Taps that we see here so first of all a little bit about me I started the stock about 20 years ago 25 years ago let's train my age that's actually me now um I'm still a trainer I'm learning from you and also going to give back to you as well I'm going to share our knowledge together as Beast Hunters looking at those attacks there's Footprints of those beasts as well together in essence you know really when we look at beasts or attacks there's very similar footprints that we see uh and there might be more but there's a lot of similarity that we see through throughout all these attacks that we see in a present day and past day as well I worked in a soccer about 20 22 years ago and you know what we see then we're still seeing now those types of things are you know there's always some sort of malware dropper a legitimate program you know uh malware hiding in a little program or adaware or perhaps more sophisticated Trojans being dropped by a phishing campaign or drive-by download to a doppelganger domain uh or even with flash drive being plugged in something as simple as that but there's always some sort of malware somewhere what we see in every single adversarial attack is it always involves credits uh one of our Executives says all about the credits whether it's ransomware uh type of Beast or anything else credentials are of the keys to the kingdom like an escalate privileges move around the environment establish a level of persistence and and hide their for amount of time and I'm almost halfway there for data or exfiltration or cause brand damage wherever it might be but when I used to work in a sock and it still is sometimes the problem now is we're always scrambling when I scramble to look at our various Investments we've made we've all made some very powerful investments in cyber security and they're all our excellent in what they do we're either trying to patch a system rebuild a laptop or or block an IP or plan a hash whatever it might be and often you know what if we don't have those consistent processes what happens is you know we're constantly trying to do our own thing and try trying to fix this problem which is looking at these footprints let's look at a zero a day everyone uses this term zero day what does that mean you know someone finds something wrong with a piece of software that can be exploited Hardware software firmware could be exploited in an illegitimate way now what's the responsible thing to do this this researcher perhaps it's me or you should report it to the hardware software vendor right and it's a hardware software vendor uh sending email says yes I'll patch it for you very quickly thank you very much the best practice really what really happens is on some occasions your email can get ignored a patch is released 90 to 180 days later which being generous by the way and everyone's scrambling to ask those questions the csos when I used to work in a sock said well have we got this thing is how do you know we've already been breached uh what do we do for the future all those little questions I'm panicking trying to ask these questions so the best way would be a patch is released for everyone in a seamless way moving forward everyone heard of a anyone heard of the spring shell Bridge yeah this is nothing has it cameraman thank you very much but this this was this was a really sneaky Beast uh it hit itself within the various programs it took advantage of a Java exploiting spring shell framework and then the connected to a commander control um and took advantages and vulnerabilities were within the Java spring framework now what did uh organization generally do they did in fact enabling TLS so you can look inside the encryption of the firewall maybe I opened up some of our IDs systems to look at specific signatures maybe increase the signature capabilities on the endpoint tools but there's all scrambling to do different things but what they couldn't again answer fully is well okay you know have we already been affected where did it come in from how did it happen these are all the almost the outcomes that we're all looking for yeah so when I take a step back on any attack or beast that I look at I really want to ask questions across the board I don't want to specifically look at a specific tool and say well okay well is this the first time that Randy has access his system is this the first time or is it abnormal for particular users assets processes to access or RDP to the specific device is this endpoint process real is it legitimate should we allow it all these questions should be asked across the board when we're working in cyber security and not just specifically on one particular tool log4j we have to deal with log4j anymore messy right yeah it was a holiday killer for me right uh I mean we we deal with a lot of plants from various verticals and uh it came in on Friday Apache released a patch and another one it's what happened another one happened as well but the same sort of methodology here um the the executives of Mercy's organizations are saying fish as well we use this Apache Java thing right this is the normal utility which almost tells us that anything can be exploited so are we patched are we not patched uh what are you going to do for the future and this is the questions being asked of all of our Security Experts so let's look at some things we can work along with and arm ourselves with the right Beast hunting kiss I'm not moving too much across the street very good really we've all made good Investments and that's that's the premise of my presentation nothing that we've invested in organization is inferior we'll we have excellent endpoint tools we might even have an excellent perimeter security platform as well ideally they need to be working together to really form the footprints of the Beast to give you the full picture of intent what is this Beast actually doing where's it going what where is where what's actually happened I want to relate this to an example ransomware who's had to deal with ransomware so you've had some tough times and and this is this is quite prevalent ransomware has been around for a long time 20 years ago when I was in the sock and even now in its forms we saw uh the British with Royal Mail recently and Beyond they're evolving as ransomware of the service you can get I.T support on ransomware tools and anyone can sit there and run a piece of ransomware distributions through the places we know uh through a social engineering campaign like fishing for example um drive-by downloads to to domains all those classic ways of uh interacting with uh with the end user and I take a step back look we always tend to look at a victim's ah it's your fault you didn't call it I.T policy we can all be victims uh I could send you an email say hi I'm Randy if I presenter today you open the link you can be infected I can drop a download and start to move around the environment if I wanted to so we're all victims so let's be kind to everyone so the infection uh started new enumeration that's going to see a ransomware scanning file scanning Network shares and we start to stage and start to encrypt uh um uh the environment and suddenly it was Payday for for the guy or the girl the adversary who certainly is uh take advantage of this type of attack how do we stop ransomware always the question uh is it can we even stop writing well should we be looking elsewhere of course we could lock down all of our machines right all of the critical IPM systems but imagine the disruption to the end users that if you're trying to block every single process that runs the Change Control would be crazy how about we look at the scan phase and say well okay well if I see elements of those footprints that they're merging press things that I could be looking out for that could be interesting we'll come back onto that maybe it'll trigger an iocs thing that I know the ICS out there remember if you have a zero day ransomware attack they become immediately useless so how about we look at going back to the the scanning process well okay if I see things like the first time this process is accessed well the first time this user's done something the first time I've seen this machine connected this machine added with other things that's more of the behavior I want to look at also as a response we also look at the whole workflow maybe I want to use my firewall my endpoint tools if I see this Behavior to Banner hash at that point or block an IP or even email the user so looking at Behavior becomes a lot more prevalent a lot more uh better way or better approach to look at ransomware and probably other attacks I'm a fan of miter who who follows my turn works with a big fan big fan no vendor does all miter ttps is never going to happen but look at all the Investments that you might have within your organization wherever you are in a university or in a bank where it might be you can all have elements of it why not use what we know then No No's use those to trigger off say okay if I see specific ttps that's interesting if I see those ttps plus a specific process execution or a behavior around each machine for the first time that could be interesting being able to see so why not use that framework you know why I think this is powerful this is probably not the only one is is when I visit organizations that say to me well do you know what um how uh how do I check or how do I test maturity of my security organization how do certain security it's an ongoing process where you need to start is your processes your people and your tooling that's Sony key the second thing is align with some sort of framework this could be an example where are you in the mind to coverage today Mr his customer and from there start to push that out to your Affiliates if you work with Partners as well okay how about the processes of the people going back in stock now what I see uh often and this is now alluding to some of the tooling that we have actually been doing perhaps other tooling as well is these key elements of actually getting to a point where I can respond better uh best detection best triage and investigation but love to respond if you have inconsistent collection and going back to my soft days when I first started I used to use a SIM to find things and the first thing I asked was well what logs are we collecting um are they being passed or translated and are they consistent because I don't know what to search for so consistency is key from The Collection perspective we need to collect conversely various sources from Cloud to on-premise from Legacy systems based upon that I say well how we detecting stuff just on signatures that's useful um what else oh well we're creating correlation rules very useful in some instances but what about the unknown unknown stuff like the behavior Randy speaks of how you're dealing with that well this individual going this way and this individual individually goes the other way so a little bit inconsistency which case causes inconsistent triage investigation and we all might have our own way of responding if there's no process in place it might be well someone might then rebuild a machine Others May call up the uh the person at hand or the machine at hand and say well actually I'll just pan up the network and leave it there so what we do need is a consistent web collection a consistent way of detection based on Behavior we talked about the behavior just now around looking at ransomware how about looking at true Behavior and the only way to do that is to understand normal in your environment because what works in a bank might not work in a university or am I not working at another it organization so we need to understand normal first before we can look at anomalous Behavior so many discounts is this actual um uh research has done by polymun and the percentages here really outline the amount of time everyone or a soccer lists sock engineers and also spend where they're spending their time we spend a lot of time doing triage investigation so you can almost tell them what I said I hope that this is where everything has to be right why because we have a lot of a lesson of things coming in so we we need to have this one we need the information at hand we don't want to be pivoting from the system to civil system so a lot of time is spent there and obviously response can be automated all this can be automated but this has to be correct excellent pitch but I'll move on put the price pictures here so let's look at some other things we can try and do to make things better a bit of a handbook approach so perhaps we want the ability to look at Footprints at any point in time so ask that question those questions you saw earlier on well I've seen Randy do something Anonymous right what did he do last 10 days 30 days lost 365 days look forward but what is he doing today what is he on a normal day the ability to retrospectively scan and the environment from a single place by the way you're going back to the tooling Investments you've made you your systems are doing this your files are collecting logs of what's going in and out your environment who vpn's in your endpoint tools are collecting what's being processed maybe some alert space of antivirus or whatever it might be your behavior how about putting in one single place to give me a story snapshot how about how about uh go with what you know if you if you know something is bad stick it on a watch list credit correlation rule this is just a snippet of how uh our our collection platform you can create a correlation for J if you like if you know it put it on there it could be an ISC as well I'm going back I'm going back to log 4J again which I love very much and it worries me is well is asking not only uh well have I got it has it executed what I'm going to do remediate I want to know actually based on the logs which they have my my network devices my endpoint devices you know is this the first one that's happened is this a new Port that I'm connecting to what is normal for this for this organization emphasis on normal um I've talked a lot about Behavior so far and I certainly abide by that but the power is understanding normal the ability to Face line everyone's environment based on the context we're given and the logs that we're giving the information that we're given it is very very important in understanding anomalies that ain't going on to look at these adversaries these pieces touching a lapses we all know about lapses yeah dealt with it too they were focusing on the tech tech companies but uh they moved on to government and medical as well certainly and probably other things they've been around a couple of years actually if not more but um this is a classic Insider threat classic compromise credential use test as well of what they did sending uh uh malicious emails out with a fishing camper link with a downloader and everything else went crazy after that so a real real life and not so long ago case of uh compromise presence inside a threat what I'm going to show you is how we can apply that behavior-based approach to what took actually and I'll move on to this slide uh two weeks oops two weeks for Mandarin to solve and Mandy is an excellent of what they do and let's look at that behavior approach but before I animate this slide is Randy mentioned that actually a lot of times it's been through an investigation I've never been in a sock what does that really look like uh to me why is he spending so much time there and actually this slide gives you a rough example of the question we'd asked well if I've got an endpoint tool I'm asking what processes are running if I've got a primitive firewall I'm saying well what's normal in the file what's blocked what's allowed these are this is just a subset of questions but as a subtanalyst for those of you who work there this is this is some of the things that I'd ask of my platforms let's go back to lapses mandates approach there of the of the footprints they found and certainly the mapping of our Behavior against it now it's uh this goes back to exiting but certainly if you look at some of these statements these are our fact-based machine learning rules uh if there's a connection to an idea of system uh via RDP um we're using the behavioral analytics you can say well okay who was the first person to access that asset who usually accessed it from what country when how and when before in real terms what does that look like we need to have a chronological timeline of everything in our environment at any point in time so I can look back and scan automatically it's good and bad together bad stuff is great because that's uh it guys and girls get very excited with it finds that find the adversary how about understanding what's normal and that's very key to building these timelines as we see here for lapses but what if we're beginners at some of them up and I'm still learning the the main thing is having a platform which allows you to learn having those prices in place you can follow those guidelines so you can have a more consistent process to respond and the ability to then build your own using an API using python descriptor own Integrations uh and also responses as well I love threat Intel use threat Intel quite often yeah all the time yeah open platform to to integrate with threat Intel feeds to feedback and add context and insight into what's going on in the big bad world back into your organization so key hopefully that was insightful for you news ideas I'm still holding everyone from lunch for another 15 so I'm kidding thank you very much for your time [Applause] all right you can grab one or two questions if you like for the audience any questions anyone any questions I don't know what's for lunch no questions excuse me just walk yes one of your slides where if you talk about education and things yeah and so on an alert typically would you then have Playbook as well aside yeah this one yeah yeah certainly so so okay this is an X being screenshot but yes for example let's say uh I've been a tier one analyst before and when I've gone into organization well okay well what I do what do I do when an alert comes in what do you want me to do do you want me to go on to the platform and have a look that you can uh organizations can have their own playbooks run books also call to say well okay I want you to get some context around that alert I wouldn't I want you to tell me what happened before and after give me that story and have a timeline and then as a basic thing maybe go and check it with fresh and tell logerticket email the user right so this could be part of this process it could be automated or it could be manual as well depending on how severe it is often that I used to say I used to work for an endpoint vendor let's ban every hash in the organization the white list everything but that's not going to work what you do need is a place where you can have consistency so you and your colleagues can follow a participal path have that consistent response no yeah any other questions thank