On The State Of OT Cyber Attacks And Traversing Level 3.5, The ‘Airgap' by Ric Derbyshire

Show transcript [en]
morning um I have a really difficult task of following Holly so uh apologies for my performance um so this talk is on a state of OT cyber attacks and traversing level 3.5 the artist formerly known as air gap um I was kind of hoping there was some kind of Pride for the longest title but uh don't worry about it operational technology is Niche but this talk is very accessible um it doesn't really follow any sort of technical research it's kind of attempting to provoke some sort of discussion um so I'm Rick I'm going to be giving you some hot takes throughout this so I'm going to prove some credentials about me um I like motorbiking uh I like traveling
on motorbikes unfortunately uh it's very expensive and time-consuming hobby so I don't get to do it much so my other hobby is hoarding pants um these are our three on the slide uh I'll show you mostly say my favorite is the top one because of a great safe in literature but it's a bit unfair the other two can't read more seriously um uh kind of like said I'm I've unfortunately been in cyber security for a long time predominantly as a consultant and a creation pastor and that kind of thing but I recently completed a PhD which essentially means I wrote a really specific and boring book um mine was on quantifying Cyber risk um the picture on the left hand side of
the slide is Lancaster's industrial control system or operational technology lab which is where I cut my teeth where I learn everything and although my PhD wasn't about operational technology um the collaborative environment there is fantastic and um yeah I managed to get involved in lots of fun research including the re-implementation and design of the lab and also some really cool stuff about offensive techniques improving reconnaissance and enumeration and attacking within these kind of environments which kind of led me to do a black hat talk which is super exciting especially for a PhD student doing very academic kind of stuff more recently than that I spent the best part of the year as an OT cyber security
consultant working mainly in power generation transmission and distributions I've seen this kind of thing for quite some time um but recently um I couldn't stay away from research so I've moved over to Orange as a senior security researcher and I'm focusing again on operational technology and I'm having a great time doing it because this is literally my job so we have to talk about operational technology I'm going to go on a limb and assume everyone knows about it here at least in some sort of capacity so I'm not going to have a primer on it but for OT devices um there are three main ones I'm going to be talking about throughout this talk on the left hand side we have a
programmable logic controller which is essentially the heart of an operational technology environment so this is the thing that we'll be listening and sensing from the physical world and then according to its programming actuating pumps sensors that kind of thing moving over we've got the human machine interface which is kind of like the first interface that an engineer will be seeing it's basically taking the data directly from the PLC and uh basically you can kind of actuate prompts and stuff manually there and these are usually quite localized on site and then we finally have the remote Telemetry or remote terminal units um either one seems to be applicable I literally don't know which one is worth
anymore but these uh they've kind of crossed over with programmable logic controllers where plc's now do a little bit of the kind of networking but these used to be the ones that different networking so as you can tell from the state of what they look like and we just had a really good talk on the future of things from Holly I'm talking about things from 30 years ago [Music] so when we talk about this kind of environment this OT environment we tend to think of critical National infrastructure power plants uh water treatment facilities that kind of thing however there is another sector that um that uses operational technology quite prolifically and that's Manufacturing and orange our data says that the
manufacturing sector ranks highest for both incidents and cyber extortion cases so things like ransomware double extortion and that kind of thing which is interesting because if manufacturing prolifically uses operational technology and it's the highest hit sector why we're not seeing that many uh deliberately targeted OT cyber attacks so on the left hand side we've got a timeline from 1988 to 2020 um which is when the paper that I took this from was published so there's nothing after that there were a few of operational technology attacks the the researchers could actually find and what you'll notice is there's only a handful there aren't really that many um which when you compare it to I.T cyber security attacks we're
experiencing like tens if not hundreds of thousands a year so there is a stark difference between those two and the the reason I'm saying this um that we aren't seeing that many is when these OT attacks do happen they are very typically newsworthy so even um as as late as last year we saw a predatory Sparrow attack Iranian steel mills we saw the Cyber extortion group Club um gets uh get access to the OT environment of South's Capital water not too far from here and even if you look at attacks like stuxnet I have to say it's an OT part um that happened 13 years ago and we're still obsessed with it because there are
so these attacks are so infrequent that 13 years ago we're still relevant somehow I mean then again 13 years ago on the scale of these OT vulnerabilities that still exist um from 30 years ago is all right so we're also experiencing the OT but not OT attack dilemma and all these quotes that you see on the slide right now are from the same report which is kaspersky's 2022 Roundup of industrial control systems or OT cyber security incidents and I'm I'm going to kind of summarize this so you don't have to read them all um what what you will notice is that a lot of these quotes or all of these quotes at least for a lot of the actual
attacks the OT wasn't targeted and it was barely effective um in in a number of cases it wasn't affected at all and in most cases where it was affected it was as collateral damage or the OT was disconnected or shut down as precaution during an I.T incident so these kind of things are labeled as OT attacks but they are and if you look on the bottom left of the slide what we have is a screenshot from ghostset who purportedly managed to do some sort of ransomware style encryption on a an rtu remember I said remote terminal Telemetry unit before um uh so it's supposedly an OT device but when people actually log into this remotely at all
everyone realized straight away that this isn't an O2 device this is an I.T router that can speak a few protocols so even these hacksavers groups although scary that they are trying to show some power and show some capability in this area they they're not really doing it right so I want to just quickly go over the approximate anatomy of an OT organization uh before we go any further um just so I can describe a few things a little bit better what we have on the left hand side of the slide is the Purdue Enterprise reference architecture or Purdue model and it kind of just very Loosely describes um how an organization that utilizes operational technology would lay
everything out in terms of what technology they use in it and O2 it does say the manufacturing Zone but this does apply to any kind of organization that uses operational technology now of the at the top we have the Enterprise there and the IT Zone this is essentially the kind of the I.T like infrastructure that everyone here should probably be familiar with and these are kind of devices that you can go in you can slam your own matching necesses around and they are typically very resilient to that kind of thing you don't really have to worry you can use all your typical tools and techniques and everything like that it's fine well when we get down to the
manufacturing zone or OT area we start to get assets that are very bespoke and they fall over on the the smallest of circumstances for example if you send an nmap a generic end map to a Siemens PLC it will think that Port 102 which is their F7 poms protocol is RDP so it'll go oh I'll test that for RDP instantly breaks it so you have to be much more careful you can't just start slamming around your I.T security techniques in this kind of area um this is this is uh this is built into levels so we've got level zero through the three in this area so level zero the process is where the sensors the pumps
the actuators and that kind of thing um and that then feeds up to level one which is where we have our plcs which is basic control so this will sense everything that's going on and it will actuate the pumps according to the programming whatever up level two we'll have those hmis those human machine interfaces um typically just basically kind of like taking the the information and presenting it in a nice way so that you can maybe uh do something manually and that kind of thing and then finally we get up to level three which is the manufacturing and operations control which it might be on site in a organization that is quite geographically dispersed like power
transmission water treatments for example um you might find that these are um in a kind of centralized location like you may see like a suck or a knock or something like that and this is where you've heard of supervisory control and data acquisition scada this is kind of the amalgamation of that data and one Central Point and then between those two things I've just spoken about we have the demilitarized zone or the oh level 3.5 between levels three and four the artist formerly known as air gap and the whole point here is it kind of very typical of the entire OT security Paradigm which is just separate everything pop firewalls in place and just don't let anything get
anywhere because we want to not only keep bad guys out but even just like random bits of traffic that could go and then just knock a PLC up because just one thing could have a cascading cascading issue and then we have one we have one PLC that goes offline in uh in one uh Power transmission site and then the entire UK is then knocked up from a Cascade and then we have lots of problems so that kind of gets on to the point that OT really does just focus on on that perimeter and it's just keeping people out there is obviously the idea of keeping defense in depth but these are these are these environments they can't
just be shut down and patched you can't just like go oh we'll just patch an engineering workstation they'll be used to configure a PLC because they need to keep running at all times especially in critical National infrastructure and some of these environments they will only have a specific shutdown period maybe once every five or even 10 or more years so when you hear this Trope that oh operational technology is out of days it needs patching it's got vulnerabilities like people know that like they're very acutely aware of that it's it's not the case that this is a choice or this is ignorance this is this is straight up you just can't do it so this is why we focus on on on keeping
bad guys or general generally anyone that you don't want out of your operational technology and going a little bit further if we start looking at the more prominent kind of uh standards and guidelines like IEC 62443 we then go in a little bit more detail into things like zones and conduits and really separating things out and really putting things into categories so that's kind of how we'll we're laid out but why aren't we seeing these these uh these attacks targeting OT if we're basically focused on a perimeter which demonstrably in iot over the past 30 years hasn't worked that well so going back to when I said that um maybe it's a case um that we're not seeing uh over the
attacks because they're not reported maybe it is just a case that they're not interesting and there is a lack of reporting I kind of doubt that when we see things like uh steel mills just going nuts maybe because of the OT but not OT attack dilemma uh it's kind of creating a journalistic boy who cried World culture whereby uh we've had journalists that have reported things to be OT attacks that have days or hours later been found out to actually be um uh basically an I.T attack that has had collateral damage or just simply an engineering issue it might be the case that adversaries just aren't interested um I referenced before the self-staffage of water attack by the ransomware or
cyber extortion group Club they had access to the human machine interface which means they were where they were deep into the physical environment they could have done what they wanted they had the option to play around with things there um but they deliberately didn't and they even released a statement saying they don't attack critical infrastructure or health organizations so it could be a case that they have some sort of conscience I doubt that it could be a case that they don't want the attention they don't want to potentially impact human lives because of that's a bit different in terms of authorities coming after you than stealing some money it could also be a case that no one's
really figured out how to monetize this kind of environment yeah and the predominant attacks we see are financially motivated so maybe it's just the case that no one has really worked out how to actually get money from attacking operational technology in the same way that you can get money from doing cyber extortion it could be the case that they don't have the capability now this is a niche area and getting into it is there are barriers to entry there's the cost of actually being able to get access to the the actual technology itself to play around with it um so maybe it's just that there's no capability however if they even do have the capability there are then still barriers
for the for the uh adversaries that actually know what they're doing in an unfamiliar environment getting from the top left of the slide where you've got a foothold in an OT environment to the bottom left of the slide where we have access to hmis we can exfiltrate piping and instrumentation diagrams so the right hand side of the slide where we're actually starting to write exploit code but very bespoke environment it's it requires an additional tactic called process comprehension because we can't just look at the actual Network and we can't just like scan for ports and find out what's going on it's much deeper than that the plcs have underlying code the the actually work in
the the uh in the physical environment that affect that kind of thing and you have to really understand that and this can even involve physical infiltration of the the environment that you want to attack to actually really understand what's going on because you don't know what the PLC is doing you don't know whether it's attached to what sensors what kind of pumps maybe a robot of some sort and then what are those pumps and what are those valves connected to is it a big water tank is it something that's holding gas you don't know so kind of getting that information to be able to cause some sort of deliberate physical impact is extremely difficult and that's
why we really only see it from state level actors to do these really highly complex emphasis and finally going on to why we might not be seeing these attacks and I think this uh might be the least likely of all of them but I'll let you decide for yourself it might be the case that this perimeter that this notion of the militarized zone or level 3.5 is actually working and it's keeping bad guys out I I don't really quite believe that because we aren't seeing people doing attacks deliberately on operational technology but we are certainly seeing them get to the operational technology and even at that point we're starting to see the emergence of the industrial internet of
things and Industry 4.0 and whatever buzzwords that you may hear that basically connect things like plcs hmis rtus directly to the internet and completely forgo this whole idea of a perimeter and I think we can all kind of have an idea of what happens at that point so why and how my operational technology actually become a Target the first thing is these environments have very mature metrics so they know almost down to the minute how much money they're losing by not being operational and they'll also be very acutely aware of if they actually have to hold the process while it's actually going what kind of things will be spoiled and what kind of things that other how much money
that will cost so there is definitely a way of of the adversary uh being able to monetize this because the victims will know exactly how much it's going to cost and they'll know how exactly how much they're willing to pay for a certain amount of downtime it's way more tangible than say for example encrypting some data or leaking some data which is kind of a little bit more nebulous you don't always know the exact value of that of this you can literally quantify directly what's more is the barrier to entry for getting into this uh a a lowering like OT cyber security knowledge is becoming more pervasive just the fact that I'm doing this talk for example
Research into this area I mentioned that I got involved with some research before um while I was at the the University full time and what we did was we essentially uh were able to extract uh the the binary that is running directly in a plc's memory take that pause it and understand exactly what it's doing which vastly uh made easier process comprehension the tactic that it was telling you about before which then in turn makes OT attacks far more accessible we then don't have to necessarily physically infiltrate the environment we can know what's going on uh from basically a distance other research involves digital twins so one of the other things I mentioned was that there is a financial cost not only
to uh getting into this area but to doing the attack it's widely speculated that the more precise and complex attacks such as structnet the adversaries will have re-implemented the physical environment to develop and test their attacks and with the emergence of digital Twins and more capable simulation we can basically rely on these things rather than having to buy costly devices to to basically do this and we don't have to rely on Engineers are wiring everything together to kind of make sure that we have a good re-implementation yeah the dissemination of knowledge as an example like I said before is me doing this talk but there are literal conferences dedicated to this so there's S4 which happens over in the US which is
a massive conference entirely dedicated to this part of them Defcon and a number of other conferences have had the ICS Village running for for years now so people people are ever exposed to this in conferences all the time there are academic courses about this kind of thing there are online courses like on YouTube and things like that they're about operational technology and also you can just see a plethora of videos on YouTube um like you can literally just go and check out oh how do I break into an earthy environment on YouTube nowadays unfortunately it's becoming more more prevalent and the kind of the last thing why I think this is going to be uh be more
prevalent in in the coming years is that more recently when we've seen these attacks happening from the high level kind of state-sponsored actors we're seeing malware and attack Frameworks are specifically dedicated to operational technology now and it's not just like one kind of like one fire and forget like bespoke exploit it's the case that these these these adversaries are prepared they have a whole Suite of things that they can do with with one software package capability things like Triton pipe dream and destroyers one and two a good fairly recent examples and it's if the bad guys are making these Frameworks how long is it until we start seeing commercial organizations commoditize Frameworks dedicated to OT
attacks we've already seen it with things like idea types like metasplay Cobalt strike and that kind of thing I want to leave you with one thought it attacks were once restricted to Advanced adversaries with Leaf skills too so if we really think about it how long is it until we start seeing these kind of attacks be accessible to less Advanced adversaries and that's me thank you very much and I think I've got tons of questions
absolute Legend has anyone got any questions we have got a couple of minutes of oh go for it
yes um so most of the attacks we're seeing at the moment are kind of like nuisance attacks you can just stop a PLC and it just takes an engineer to go put the switch um there are two cases under only research theoretical cases of ransomware in operational technology and are not very effective because while theoretically they work you can you can encrypt the PLC they didn't explain how said that was a bit weird but um you can encrypt the PLC but it's it's kind of pointless if you encrypt an individual PLC in one of these environments um the engineers are going to go through exactly the same process as if the PLC broke it's very similar to um to Modern
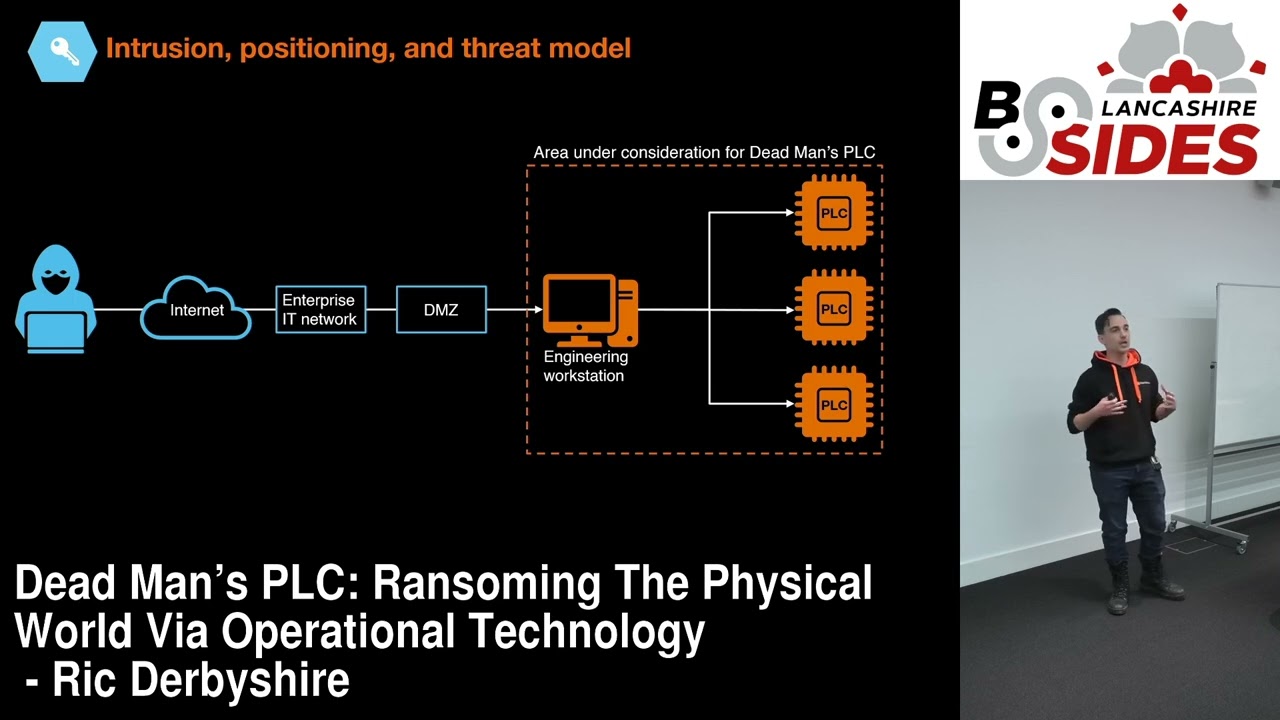
I.T backups where there's a resilience built in they just take the PLC out put a new one in and reprogram it and then the encryption is it doesn't matter anymore however I've actually been working on a piece of research at the moment um that is called Dead Man's PLC that is um a completely pragmatic and realistic way of um basically extorting an entire OT environment it's completely vendor agnostic and it affects every OT environment in the world so we're not releasing the code um well so that's that's just been submitted to an academic conference and it will be submitted to more wider industry companies so I will be doing the rounds and speaking about that and
but it's really interesting we you know exploits it's purely using uh things that are available to the to the actual obviously environment itself so we only use native functionality no exploits so it's undetectable as well as as well as as well as being quite brutal but at the moment now as but I'm living proof that there is research in the area from I'm going to ask any more questions if you could grab Rick he's probably going to be in the well you're around all day foreign