BSides Scotland 2019: The Top 10 Devices Found In UK Homes - Callum Wilson
Show transcript [en]
good afternoon everyone hey Dean my name is Karen Wilson a life lesson when Rory Alsop says hey we're going to talk about make sure that your commas actually leave a separate line between the name of your talk because actually the name of the talk is just the first line and the second and third line of the talk heading were actually things I put into the email afterwards but we thought let us stick number six is actually quite dull so my name is Karen Wilson I work in security for longer than I care to remember there are people in this audience who I work with three decades ago not quite three thirty years but almost there
and I'm gonna talk to you about the top ten devices found in UK homes but I want to know a bit about you so this is going to be a show of hands everyone has to take part hands up who works or studies in academia right I'm counting yeah quite a lot who works in government that's the spooks sorted out thank you and who works into a corporate big enterprise that type of stuff yeah okay quite a lot okay that's interesting that's going to become relevant in a minute so so we start with this number is that the average day rate for a consultant in Edinburgh is that the number of Internet of Things devices
and you were listening no it's not actually that is a volume in dollars and that's the total amount that garner predict will be spent in security in 2019 seems quite quite a lot and they've actually done their sums on this they've been working for every year counting up using accounting records to say that basically you know application security 2.4 billion dollars cloud half a billion data security and they're measuring how these things change through the years as well and then the consultants get 64 billion dollars I've probably paid some consultants 64 billion dollars and even what I love about Ghana even though they're doing estimates they still have other what enough that's for thirty two point two billion dollars
down the back of the sofa but it's the last figure that want to draw your attention to and that's consumer security six point six billion dollars and it sounds like a lot of money but it isn't basically consumers are screwed if you work that out it's about ninety cents per consumer for 2019 and at the end of the day who are we actually protecting all the rest of this is protecting the corporation or the governmental entity or academic institution there's not a lot actually protecting the consumer another number five hundred and this is the last of the research numbers don't worry we're going to come on some real data in a minute by 2022 Garner predicted it would have five
hundred smart devices in the home that seems like quite a lot because I can tell you today that actually the real numbers are rough that on average for each of those different geographical areas and you're gonna say Tom how'd you know this stuff how'd you actually know this so garner went out with a clipboard they worked out the number of five hundred devices in the home they've done research to work how much we're spending in IT security these are real numbers this is what I'm presenting you today so everything than the rest of this pack is real data that's come from a system that we put together so basically we few years ago we thought how are we gonna
work out what are people actually running in their home so we thought of different ways about doing this and really it came down to a nap so put together this up it's called secure smart I'm not going to be talking too much about the app but I want to show you where all the data came from so I can tell you what the top ten things Mac found in smart homes is number six is to dial to mention essentially we very quickly we provided app customer's download that they use it on their telephone identifies devices and know it doesn't use any map and we had to build something a bit more unique to actually find things and map actually is
not very good at finding devices on the network would you believe and it provides results as you can see this is actually my home here net gear GS 74 is absolutely terrible bit of equipment with loads of Stevie's probably best not to have in the home and the idea being is that consumer to run this and you get an idea about what's good and bad actually in your home and you get some advice and guidance about what actually you're going to do next and it's written in such a way that the normal consumer can use none of you are normal by the way in that category so do i junk it do I update it where's the manual all that
sort of stuff so data the byproduct of this system is that to get free app we ask consumers to consent us just knowing what what actual devices they have in their home network we don't ask who you are we're not interested in that we simply say if you've got Netgear gs-7 240 and your home would just like to know that you have so oh my god data and you've heard all those date as the new oil and all that sort of thing data it's not really the new oil data's data is a new petrol with some flammable liquid around so in our data model and this will become important at moma we start going through the top 10 things
number 6 and remember each device has what we call a personality the personalities built up from its network fingerprint and also that's behavior so if you have a samsung smart cooker then it's probably going to be switched on during meal times if you have a set-top box it's probably switched on all the time if it's a child's toy it's probably switched on when the child is actually using it but basically behaviors about the way we use devices fingerprint is about what does it look like and from that we can start working out what the top 10 things in a smart home are so starting off number 10 it's like those things you see on channel 4 later now
you just can't stop watching number 10 is music devices in the lead is sawn offs they have a great set of hardwired music devices the play play one I think is rocky would come in at number two with their streaming stick and if you're a UVU watcher you probably got one which I just rebranded Roku devices and then things like Yamaha and provide musical equipment so if you're jamming you can plug it into a network and do all the things that you need to do what's properly interesting about this is some of these products do things that you wouldn't expect and we picked this up in our data with one of these now I've very
badly tried to pixelate the name of this device but it's a high-end audio receiver it's designed to have really good sound quality from a tee at 4k TV with all the proper sound system it's a blu-ray player and does a lot of things but the actual model is not important the manufacturer of this device probably use the same software across all of them but something interesting your phone and about this and it does some really unusual things so the first thing we did was look at the manual like you should of course we all read the manual don't we now it's a 290 page money and I read the whole thing I can tell you you plug
it into your network and it can get your Spotify list it can do all the sort of things you'd expect it to do is all very good we know why there's a laptop in that picture but there is and it's when you start to look at things like that that are out there in the manual I think these guys have built a network connected device but don't really understand it and it all came about because our scanning product showed that this was actually running a web server port 80 with no authentication and you may say well who cares I would care if you turn it up to 11 in the middle of night and start playing howling noises
or whatever through someone's home and you got to remember that we're talking about consumers here rather than the corporate marketplace this is where people live is where we all live you own your home you don't want to feel targeted inside your home interestingly this particular one had 5 stars what - I'll give somebody a pound that they can find anyone any what - report that has less than the four stars but the interesting of all those pages never thought to say this had an open web server and it wasn't even clear what it was used for it was just a part of the software package but it was new in 2014 when I buy things at home like my fridge
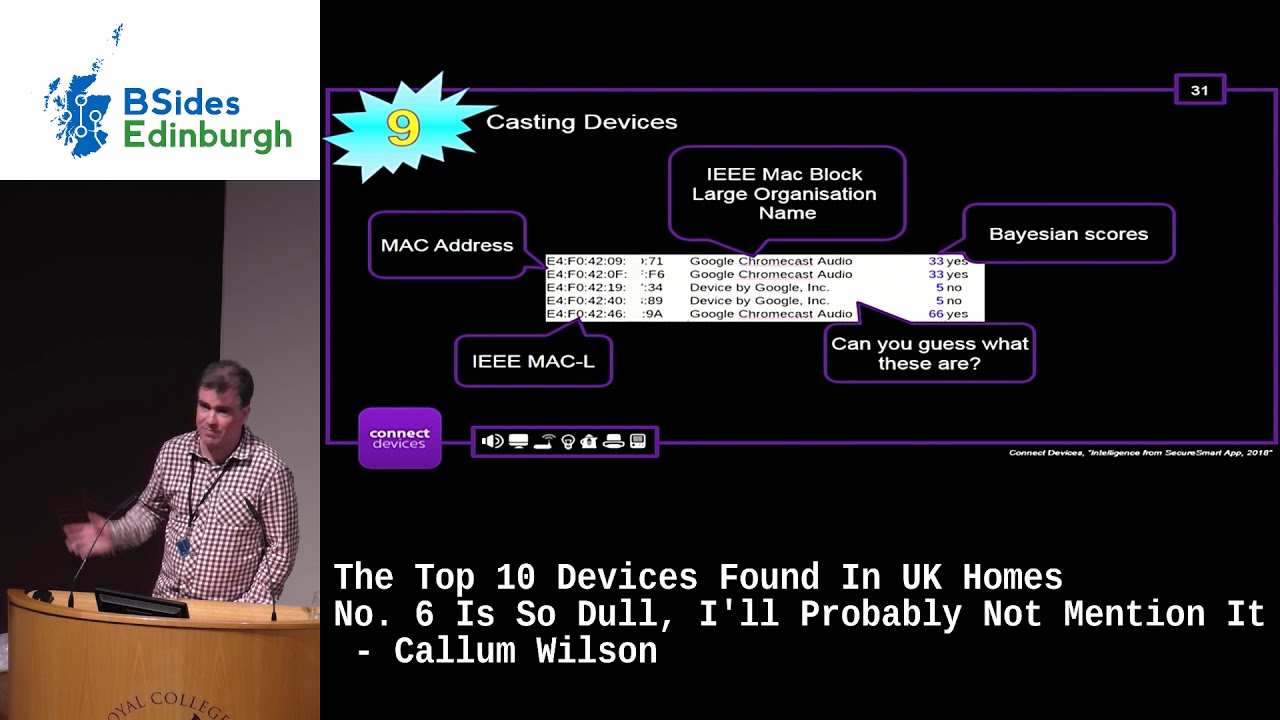
and my cooker they last for years and years and years and what our data shows and this will come will reflect this in the talk is that when people buy things at home and they work really well we just keep them and from a security point of view things get a bit old will the as battabox say the name of the manufacturer will the manufacturer build this will they keep that out today actually answers no for this one that firmware hasn't been available for years [Music] number nine casting devices we've all got them that is the original chrome class audio they sold about 50% more chrome crust version - but what's quite interesting is the chrome cast of one
has 69% of the install base now what do I mean by that I'm pretty sure that if you go to Google and say how many chromecast did you sell they're going to say we actually sold more and chromecast audios than we did chromecast version once but because our scanning app is scanning what's actually running in people's hands and not in the top drawer everyone's got stuff in the top drawer bottom drawer filing cabinet of all that old stuff you don't use anymore this is what's actually running this is what becomes important because when you talk about the attack surface of a smart home it's what's running today not what's running what was running yesterday or
was switched off and not being used funny enough actually we provide advice and guidance on the chromecast v1 because even though it's actually a really well-built tool great updates and it's a fabulous custom device it does allow users to cast without any authentication and anyone with a child below the age of nine you probably had chromecast Wars in your home where it's versus you know use versus Peppa Pig or something you know and it keeps being taken over certainly in my home anyway but when you're searching through networks you start to see all sorts of data and so I thought I'd just open the lid a little bit and what we see so trying to identify devices on a network
to really hard anyone who's done that in the corporate environment even with the greatest CMDB it's really really difficult to work out what everything is and for us because we could see we're scanning consumer homes we have to do a reasonable amount of I call it guesswork that there's any investors in the audience we call it machine learning and so here you go here's an example when you're trying to detect you know what Google's back catalogue is obviously you can see there's a gap there and that's this scoring is the blue numbers down the right-hand side we use a sort of Bayesian scoring probabilistic matching mechanism to work out what things actually are in this example you can see
the MAC addresses MAC address is just a unique number that's assigned to every networking device and least you hope that's neat and the I Triple E the institution electrical electronic engineers something like that they actually register the Mac block large or so the first three are tests of the MAC address and as a manufacturer you're then permitted to use that MAC address and you can work out how you're number everything in your manufacturing process so always the easy as that sometimes you get things like this so in one network we spotted three consecutive MAC addresses that's like winning the lottery three times over oh I see actually they're fake they're fake MAC addresses VMware as virtual computers
and thus basically just a silent its own MAC addresses and VMware will have some sort of knowledge of the network it's in to make sure it doesn't assign to MAC addresses to the same device because if anything happened like that you're in all sorts of trouble in fact I've got a Nintendo Wii old school with the an Ethernet adapter and it has the MAC address a a BBC seaworld 123 3 so if I had two of them in my network all sorts of chaos would ensue my art table beam our kids and the things would stop working and weird in wonderful ways it was get some other unusual things private most private that's not a
company I know actually it is if a certain members the audience the private is where a company has registered with the I Triple E that they don't want to be known who they are it's a very strange situation you have to pay a little bit extra to get this one of those is an Argos tablet 50 pounds Argos tablet tablet God knows why they bothered spending the extra money to register as a private company with their with it with the I Triple E and that means that actually these things are very hard to detect you can clearly see some from similar manufacturers ten to a 60 it's a manufacturer that we haven't identified yet I could well be this is
test equipment so if you've got a test lab and you're making the brand new version of a TV or a Playstation five or whatever you might register it's private to begin with and then go on to you know Sony Entertainment Limited or whatever sometimes just get things like this and that's just not helpful guys get total fake MAC address isn't anyone use anyone who's haptens an 80 to 1 X network with network address control in your corporation when though how easy it is to spoof MAC addresses we actually seen this and we think someone was mucking around with our head so network attached storage it's actually really difficult to detect what is network attached storage in the home so this pie chart
wakey-wakey it's after lunch shows the 50% of all a scam networks have either FTP SFTP or SMB running or I should release a SCP running that's what we say is network attached storage it's quite high and I think that's because a lot of people don't actually realize they're running it so we where there is network attached storage running a network 40% FTP 53% SMB that's probably your Windows laptops within switched on potentially a network attached storage device and 33% SSH running SCP and so on what gets quite interesting is we start merging it together and you start seeing devices that are running all three so two percent of of all network attached storage what we're
classifying as nas is actually run all three and that's a bit strange because why would you run FTP and SSH together or why'd you run SSH and SMB it's not always absolutely clear we think most consumers don't realize and just got ticked all the boxes and let this thing this these things are all completely open and of course two of those protocols are in clear text and certainly old SMB which is Windows File Sharing for those don't know she will transmit passwords or the hashes of passwords in the clear broadcasting now of those there's different types of ways of detecting things in a home network so obviously finding FTPS cessation SMB you can look at what ports are open on a
device start to learn about that device but also some devices you do the equivalent of hey who's got SMB on the network and then 6% of them will come back and say hey I've got something by the way here's all the information in order to connect and this is using protocols like mdns mdns is like a it's like a handy helper in the network it's trying to help you configure things so you have a mobile app that needs to connect to something then the device itself will say hey this is how you connect to me again great for hacking networks if you're into that sort of thing because you no longer if you did the port scan
typically you'll be picked up as a port scan and blocked by any sensible networking equipment but if you use broadcast addressing everything just tells you what it is you don't even need to do any work and we like that we're lazy oh yeah security conference you can't put a black arm on a black background rather this black arm on ours we seek few of these it's not massively we don't see huge numbers of these running across the world but there are a number and they have turn there's a really bad CV so a CV is a common vulnerability exposure we've talked a little bit about that this morning some the other talks they have a score
associated them called the CBS s common vulnerability scoring system essentially if you've got a 10.0 it means that device is going to get totally owned it means it can be owned as an administrative access from a network without any physical access to the device that's during all your files a lot of the older this is this particular black arm on ours is from about 2012 2013 but people are still running them today because they still work it's in the home it's not like a corporate Sam policy or storage policy where you you recycle and devices of a period of time but I've got perimeter security now this starting to think my way my notice is interesting so what we're
saying here is homes that almost like our workplaces where a few years ago quite a technically thick outer shell soft machine interior it's going to be no excuse we'll talk a bit all about that later so number seven home automation my favorite for any of you who have not seen mr. robot this is at the beginning of series two where the hacker group F society I've got the t-shirt are trying to hack into this fancy flyer that has full automation blinds the garage door the lights the media center and cooker hot water everything and they are taking over this lady's house and basically she's on the phone to clearly whoever had provided those equipment she says what am I
supposed to do um plug what but everything's inside the walls that's how it was when I install I bought the home pocket and we've seen a bit of this with home automation the first version of the Honeywell Honeywell controllers or central heating had a pretty serious bug with and I've seen no way of updating anything well it's not that expensive just replace it and anything well I've got to call out a heating engineer have no heating no hot water whilst they do that and then I've got to make a decision whilst the thing is broken about whether my can heat my family I'll move out the house so these things have quite big ramifications in the world of
of home automation the marketplace in terms of what we see running today is roughly that with a bigger the circle the more we see of them these are the big guys must have had some problems and in fact they've all had problems in the past pretty much now fixed there but they've got big companies behind them most of them have good disclosure processes and they have pen tests being operated but interestingly they've all had problems the nest one was because people were guessing passwords but also they had some problems of the nest cameras where there's the crack kr ACK hack on them and there's a few other bits and pieces we don't see so many
light wave systems because all you really see is the hub and lightwei it means a radiofrequency light wave RF to them to connect out to all your light switches and so on an interesting new entrant into the arena's IKEA IKEA has a 25-pound home so a hub thing and it's really interesting how what the play is going to be there are they going to start moving into the home automation so you just pick up your home automation stuff when you go to buy wooden furniture I don't know it looks like it's going to be that way but Philips our nests are really you know we see a lot of these actually running today in in networks not I'm good like that I'm
not this fellow this we saw this in Berlin at the ephah show which is like CES for Europe it's an enormous conference where they show off all the latest devices and this is Mikey and this is a consortium that's been led by Siemens who showed off this new device that basically would interpret your fridge cooker and you kitchenware type devices and the sort of questions you could ask is based on what I have in my fridge what can I cook for myself tonight and this but the scariest thing about Mikey is that the head arrangement had a sort of because obviously it's winking at us in that right-hand picture but had a whole set of facial expressions and as
you walk past Mikey the head would turn around and face you pretty scary stuff so scary that when I tried to buy one it never made it to market thank the Lord number six to remember it's just too tough now we're going to cover number six number six they are the ancients of home networking they old-school the very first things that were connected to home networks and these are the printers their printers printers are great I love printers print is just you just connect them they print whatever you tell em to print you don't ask you for anything it just print it also a really easy to spot using network scanning techniques because they tell you everything taking
all sorts of information there is some MD and s scans here where there Rick or which is a color that's Africa is quite a big sort of multifunction printer that someone's got but interestingly that's the red oblong on the right hand side actually has a serial number which it presents to you for free when you ask for it to a broadcast tell me everything about a PDL data stream you can have my serial number and the serial numbers all you need to register that Rick at records website and then you can start doing all sorts of things you can take control of the printer because it has a clouds function to it you can start
ordering lots of new toner and you can reject print jobs you can make it do things other little things like the bottom one that HP Envy which is a sort of a home class printer re displays its MAC address in mdns where at the moment isn't such a big deal because you've got the MAC address anyway if you're on the network but if you're using sort of modern Apple iOS devices that prevent you over have been able to scan Network Sookie she didn't know Apple change the rules on iOS about two years ago and said that we're no longer to allow any application to scan networks except for their own which you have to pay for so
tools like ours and like faying and like some of the other networks gaming products simply don't work on Apple iOS anymore but you can still get the information because things like printers are giving you that information you also get some interesting things so the middle to there it says HP Envy 5530 act simons iMac and that's because they've connected in a USB printer into a I mark in this case and it's Murray and the computers acting as their server for the for the for the printer that got me thinking so did a quick search just the other evening across our database and we found hundreds and hundreds of these so broadcast network scanning your devices start telling the world about
who they are and in this case quite a lot of people like to for some reason when the Apple device like to put their name on it so here it belongs to and Apple are quite happy to tell everyone who that name is so in your home it's not such a big deal but outside if you're in the airport lounge or if you're browsing from public Wi-Fi then people can start building up this picture about you and I'm hoping that you start to see that the information that we use for home scanning Keys be equally applied to public networks to your corporate networks your academic network at university and by the way people put their full names and they say
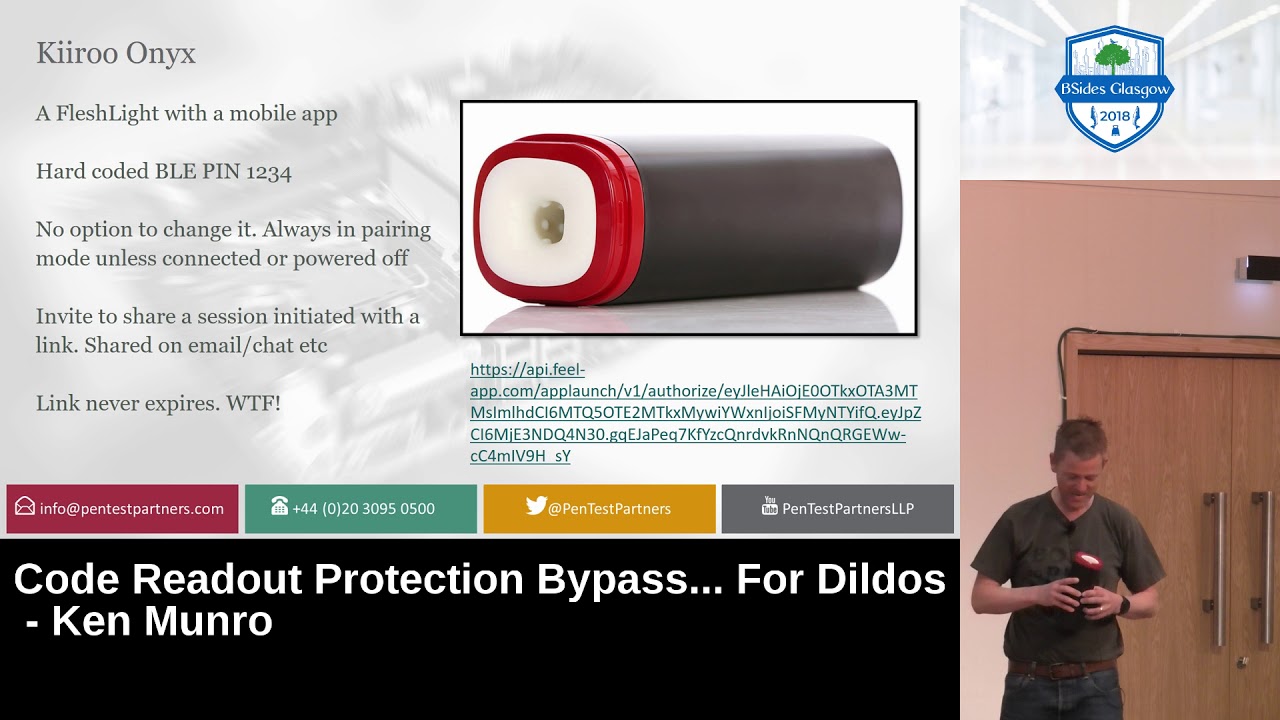
Joe I just redacted that just in case is very small likelihood Joe's in this audience and my luck sometimes works like that but yeah toys and games you remember Ken Monroe at previous conferences was talking about my friend Kayla and a view robot and that sort of thing I think actually what happened was that this started to change the way the industry works and we've actually we worked with a company called whale stuff and I've never heard of well stuff I buy toys for my kids while stuff the third biggest designer manufacturer of toys and they did Toys Science Museum sorts of really cool stuff and we've been talking to them about sort of compliance
package for for toys making sure that they're safe and they meet the same criteria we would have on corporate assets in the company Network and really where it works is like this and I think that some of the the findings for the my friend Kayla Fiasco a couple years ago is start to change this model and it's really important to say in any security problem you have either where there's home scaling like us or when you're scaling corporate networks say who is responsible it's actually not clear-cut of the toy industry you got retailers the person who sold you I don't care they sold it to you the distributors do have it insurance bar in the case things
is set on fire or choking hazards for toys but not really responsible for firmware updates or for keeping things fresh or from being able to handle disclosure events she go back to the toy designers and toy designs really interesting because basically right today they are not designing toys for this Christmas all the Christmas after right now they're designing the toys that we will see in our stockings in 2021 so they're looking very far ahead so by the time that you buy that toy or Santa delivers it do we know there would be nobody there to be able to answer the question to be to deal with a disclosure to be able to update the firmware
they're long gone and really when you start to say well okay I don't really know who's responsible who's going to have the biggest loss you look at the licenses and the license or so who really rule the industry in the toy in the toy industry they are the you know Barbie from Mattel and the Pixar and Disney with a few exceptions like Lego and matchbox and some of the other brands as well but the licenses hold all the way and they will massively lose imagine if the my friend Kayla door was a well known and well his Brown like action man or Barbie or whatever it would have crucified them the accountant over the name of the
company that the of my friend Kate I think was called that Mediacom or something like that I can't remember but they had a thousand people working for them there's a hundred million dollar enterprise that no longer exists but the license wars are a fact of a hundred bigger than that so there's been a bit of an ease and and what you'll see today is a lot of the toys and games that are smart typically a Bluetooth connected and connected through another device as a proxy device so we don't see very many in our scanning database we don't see so many directly connected devices but we're working with the next generation of toys which are absolutely brilliant
I can't tell anything about that I've sworn to secrecy we do see Playstations Xboxes and the odd Nintendo that's connected it what's quite interesting is we see a lot more PlayStation 4s than anything else that's largely because they're switched on all the time even when you switch them off they keep the network card running that's quite common amongst other devices such as set-top boxes and so on and Rob as your home router stays on all the time but some devices were going to sleep mode Xbox sleeps from time to time so we see Xbox is when they're switched on mostly Xbox one rather than some of the older versions PlayStation 3s have got Seavey's against them there's not a lot
of people knew which I don't think have been fixed number for TVs and set-top boxes I hope you like my Amazon bar graph amazon reached the UK europe after they after a while it took a few years before they launched here so our database shows things are actually running today the first product the TV cube and the tvs fire TV were mostly launched and mostly used by customers in the USA I'm sure there's a few early adopters here that might have bought one so the fire TV sticks 1 & 2 Maithili massively outnumber those but again it's kind of like the chromecast you've got the older version of the device has way more actually out there so if you start
looking about the attack surface of Amazon TV sticks so I fire TV sticks it's more the old version than the new version even if someone says put mine my device tidy up today is past what about the old versions they're still running today so what's the responsibility for the for the whoever's maintaining these devices to be able to stay with them because at the end of the day there's not much in terms of regulation for maintaining things once we've bought them just for interests sake that's about I said this is a bar graph of things were actually running all types of chromecast are vastly we have vastly more running instances of fire Amazon fire stuff then
Google chromecast I know that they're not quite both casting devices they do slightly different things but just for interest sig but that's not the only thing that can run media streams set-top boxes and TVs right so we could wake your hands up who connects their TV directly to the internet through Wi-Fi or Ethernet okay you will spread out and I can sort of see is about quarter who connects a set-top box whether it's a skybox a human or a year view right it's kind of 50/50 that's kind of ruined my whole slide so thanks for that she didn't pay more attention we actually see three times the amount of running set-top boxes than we do
televisions although there's a Wii we accept that we've gotta do some work on there and that's probably cuz the TVs weren't all switched on at the time whereas a set-top box has to be switched on for its PVR capabilities to write a view program EastEnders at 7:30 it has to be switched on and ready to beam to record across the world we see B BSkyB or skyboxes but they come in various flavors the Australian ones show up exactly the same when we look at them in and I using our scanning techniques to the UK ones I guess it's the same company behind the scenes pace and eros and a few others manufacture the devices on behalf of sky
so we see the same sort of things you see Hume axes which is replacement satellite boxes ISP TV is sort of like this seems to be a whole bunch of new ISPs particularly in Europe that are packaging TV deals with your so if you're a sky customer virgin to me that you've probably got this you probably get some sort of media packet or an extra box that gets plugged in I'm Cody seven runs cozy but doesn't tell anyone but Cody we actually begin to take Cody running on raspberry PI's or whatever people are running on that's obviously part of our our poster say to consumers give them advice and divers if something's not quite good doesn't mean
there's just a vulnerability you could say actually this particular device can go on fire and there was a there's a database that there's that's curated I think by the DCMS department culture me the sport that says anything that has a hazard and that particular Cody box had some sort of fire has another I would warn that the Sun isn't a great thing to sight that's the first way I could find on Google and also this was actually written by the anti-piracy Alliance so they might have had some skin in the game about this particular article but that's the cool thing about identifying devices on the network suddenly you can start to work out things like hey how
much power has been consumed how much is it worth you know what could you replace it with what vulnerabilities that are either going to go on fire that's okay because I don't run a set-top boxes I plugged my TV directly into the Internet so I'm safe actually I'm not my TV listens to me it's the only thing that listens to me I think this was actually mentioned in one of the earlier things I won't go too much into it but Samsung on page 129 of their license terms and conditions said don't have private conversations in front of your TV all I can say is that in my house some poor bloke in Samsung must be thinking what on earth is going
on in there but how does a consumer know this what's who's telling them this you can get some exciting rapport and BBC news or in the Sun or whatever but really you know it's there's no one really looking out for the consumer they ask good three SmartPlug so we're getting into the top three here this is where it gets exciting I bet you're guessing wonder what number one is okay I did a bit of research on smart folks this is the smart plug in my house apologies the pictures a bit day I didn't clean up before take the picture I could never really work out how these things work because I can't use my phone
which is not connected to my Wi-Fi push the battery and the light would immediately come on how can it go that fast I've built big and price systems before unusually there's some sort of latency and in such an on-off on-off I could do it from here it's not how enough does this work so rewiring my home a little and using some wires art this is how it works what they do is when they power up they send a DNS query outside of your network to a specific DNS server on the in the cloud that then responds with the details of an AWS winter server now I actually bought this plug it came free with a an
Amazon I paused there because I can't say the word Alexa in my home because suddenly she wakes up and see I just called it as she we have big arguments and the favorite thing in our houses Alexa stop and bet it came free with an Amazon echo device voice assistant voice assistant speaker and I've always since ever watching Star Trek is a youngster always what a debate to make my lights to come on for a voice command it's a thing a wired it and this plug came basically free I think you could buy them for less than a fiver so the cloud responds that so the dinner service bonds with the details on AWS rent a server and this is not Amazon
that the branded I think this one was called long back subject it then makes our long live TCP connection out to that server it just stays on and if you power off the switch the actual plug itself at the end just reconnect afterwards it just stays on all the time and that's how it works because when you are then using the app there's a picture of the app basically what it's doing is it's connecting to the cloud system which has a long live permanent or semi-permanent connection to the cloud and that's how it does it that stuff you sell to ask a few questions how on earth does the business how does that work in
terms of I got that plug from pretty much free or I could buy it for five pounds and I've had it for four years already who's paying for that Amazon rent a server is it Amazon maybe because they're selling more Alexa devices who is it and also why is it that when they put that little image on the right was just a screenshot from my phone did a Google search images on it I found about 50 exactly the same from all different companies there's something going on here they don't fully understand and I think that basically there's a b2b play in these these plugs for what I can work out is and this is still to be figured
out I think that basically there is some sort kickback scheme happening or potentially that plug is telling its lords and masters more about my network than perhaps I know about or I've consented to but we see quite a few of these we see different ones and obviously this is a generic brand with a brand you never heard of and there are some bad ones and this and worse ones I imagine - but here's the thing I'm a security perspective right hack that AWS realtor which I now know the name of and let's face it I've never heard of any Amazon servers ever been hacked I could have control of all this power across the energy grid I could switch
things on and off I can I could burn down a nuclear power plant where I couldn't but you know you can have a sort of critical national infrastructure problem if you kid across the world as well so really interesting and I think there's a long way to go I'm fully expecting that smart plug just to stop working one day when those Amazon bills stop getting paid it doesn't tell you that when you buy it never mentioned anything about protecting out to a another server in order to for it to work of course it wouldn't number two CCTV all-seeing eye seems to be they're great devices in the home network we did some research last year and presented cyber
UK last year and IITs F last year where we did a correlation of people with CCTV cameras and firm that will try to work out average value of their products in their home network and found that people with Apple Mac equipment and more likely to have CCTV equipment but also more likely to have really bad quality CCTV equipment so your classic security theater so how do you how do you work out what some of these new is well firstly you look at some protocols like real time streaming protocol it's a protocol boy of the 1980s it has functions such as play fast-forward rewind record so anyone who's under the age of 35 has got no idea what I'm
talking about and it's a protocol that has essentially optional security which when I mean optional in most of the retail products that we see in our in the homes goes no one's got passwords on this stuff it's just completely open and we all we've all heard about showdown we might even hello we peek at showdown dot are you which is a website that shows people's cameras and you can see people's backyards and or worse but this they're just that people have done something nutty enough to export or do port forwarding through their home router but inside the home all this data is available so if you drop another device in there that's a bad device or
it's been hacked to suddenly get access to all this stuff I've been talking about so RTSP it's really easy to detect and to be able to see the video feeds and for you it depends what that cameras pointing at your risk appetite would be different to mine yours may be facing the garden mine might be a baby monitor which I do care but consumers don't know this stuff some of the better ones in his custom broadcast broadcast techniques some use UPN pH and only gonna cover too much in this presentation but operates in a very simple way where you say hey you PNP device determine what you are come back with a massive configuration including everything you need to connect
to them coming similar to mdns and axis which are mainly of a major manufacturer of CCTV cameras mostly for the corporate marketplace do this properly obviously and they use mdns oh damn oh there we go some run HTTP service I like the one called Nets of Bay loans they start to work out these HTTP servers tend to be HTTP and not HTTP allows you change the Umrah point tilt zoom and do all sorts of things with people's cameras there should you wish but there's always one isn't there's always somebody it was ooofff top 10 never build your own security where we find we found one actually a CCTV camera that somebody created and put together properly and is
still running the basic is through fantastic these are just not reading there to look for the red dots this is just some CVS from there very handy website CVE details comm we looked up to three manufacturers and these are reasonably big manufacturers we see call out from across the across various smart homes just count the red blobs the three at the bottom and one of the ones in the middle is a 10.0 and I was totally earned these ones were mostly code execution and vulnerabilities if you remember mirror mirror I took advantage of this and was able to install its own firmware and then be part of a bot and of course CCTV cameras are great they've
got some attributes they've got big CPUs because they're running 4k video they've got amazing network interfaces and very handy if you want to denial-of-service crabs on security as it turned out so these worms go back just a couple of years for three magnified remember imagine what it's like for all the CC devices that are not even in they missed national vulnerability database with all the other CVS and another finally from this and take takers away is that the CVE databases don't really include much in the way of home IOT or home devices number one the worst device in the home is also the one we rely on for security home Reuters so whenever you're thinking
about a device think about attack surfaces it's just scary to think that 62% of home users don't have just don't even run HTTPS it's scarier to think that 10% of them run teller I love the ones on 23:23 hey we've run out in 23 23 no one will thinkers tell me but it actually is some of the open Mountain protocols like CW MP and a few have held up for some weird reason which I can only imagine is some sort of someone scans their workplace I can tell you have to drink about what people have actually scanned but we can also tell how old things are and this is a graph that shows the last firmware date for
devices that we see do you think I just thought t5 camera you know the quite a lot of them were patched in 2018 less than a year away but this is a this is about the actual manufacturers if we look about what's actually running in people's homes we get a very different picture we get that and what's happening there is there was a bump in the curb when a lot of UK cities and towns went into ADSL - were given route and so oh if you look at the area under the graph around 2014 to 2016 there's a huge number of home routers that were probably supplied by the ISP that are just old and not being passed and this
is the sole security device we have in the home typically and then if you take part the other known categories of things have just been talking about and all the problems with them you start to say well wait a minute we've got a problem here so people's homes are operating it too much risk security 15 years ago in companies and most of you put your hands up see you worked in companies had these four major problems there's reliant and by the way I apologize if you're actually facing these today you've got bigger problems in your company if your reliance on perimeter security lack of encrypted protocols inside the network unmaintainable outbound connections and patching compliance is pretty much
non-existent the problem we see today is actually is also in homes today and there's no one there to look out for the consumer so thank you hope you enjoyed the insight into UK homes they've got any questions
what someone's gonna say what's running in my home [Music] be aware just be aware of what you're actually running information is them just knowing what you actually have in your home is really important and that's what our app actually tries to do is give the consumer some advice because what you want to do with a particular bad device in your home will be different to what I have because we have different risk appetites you may have young children in the home and they might have children who've already left to go to university or whatever or they might just a different profile might be living in the flat students so the most important thing is just knowing and
being aware of what actually where the vulnerabilities are what the risks are in your home it's yeah there's a QR code it's actually all changed he sprays he's gone so there's a zoo it's all happening here because if you put back slide three please top there all right here we go click click keep them in order ok we go that is the QR code for apt is there it's called secure smart to search for purple they've a lot of purple in our branding yes yeah that's right so CBA they're scoring as a score of one to ten obviously a score one to hundred because we felt that consumers would work a little bit better than that we also use
some configuration scoring so that if we see for example a Rooter with toner on it that would get points deducted from over and above any CVS so for example the Netgear GS 74 had two CVS rated at 7.8 but also had open toner and just basically everything wrong with it and so it's called a really barb zero and when you click on the button it gives you advice and guidance about what to do next anyone for any more so thank you oops sorry what I I trust all my devices absolutely no I don't I totally don't I run a zero trust network at home the problem is is what humans live there apart from me humans
also live in my home and they like this sort of stuff and so you make a decision in life or whether you trust the devil but at least I know you know I can make decisions about things if I got some particularly sensitive work information I can segregate my network and run in a different way for example we actually had a case where somebody had a musical receiver used for plugging musical instruments in and it was had two network ports and it was B it was actually implicitly bridging two parts of a network together this was somebody who worked in a sensitive environment was trying to keep a family life away from work life so it'll be really really
careful about what you actually run but turns out Amazon and other does Google have a Google home and how many and so on there's all sorts of voice assistant devices you make choices in life about when you want to trust or not it does do some freaky things then one for another talk I think that's it thank you very much have a great day