Whack A Phish
Show transcript [en]
[Music] Good afternoon everyone. If you thought you'd walk through the door for a talk about how to hack web applications, cheat at online games, or feeding a cat with a Roomba, you've come to the wrong room. It just turns out you've fallen for a fishing scam, and the door was the bait. Lucky for you, I'm only here to steal your time so my cat can knock it off at 3:00 a.m. in the morning. Now, I hope I have your attention, unlike my cat who walked out when I rehearsed the first slide. Thank you all for coming to my Wackerfish talk. It is my very first public talk, so I'm very nervous and and and unlike my cat, I hope you don't walk
out. So, please excuse me if I come across nervous, flustered, or lose my voice. It's it those that know me know that it's way out of my comfort zone and I'm challenging myself. I'm looking forward to sharing this talk with you all and hope it sparks some conversations after the conference or during. Right, time to put on your detective hats. I'm about to show you two pictures and I want you to tell me which is not the fake. Don't worry, no PhD in forensics is required. I'll give you a moment to have a look at the first one. Now, look at the second one. I'll give you another moment for the first one and then number two.
Raise your hands if you think number two was the fake. If you chose number one, congratulations. You've just earned yourself some quality time to know before while the scammers are going to be spending your money like it's Monopoly cash. And you you're going to be on hold to your bank explaining to them why you ordered 75 cans of tuna addressed to Dingleberry Jones. Raise your hand if you've ever been if you've ever had to cancel your credit card because of fraud. It's not a fun way to spend a day or a week. I've always loved solving puzzles and challenges, so hunting fishing emails and tracking them back to the source to take them down has always been my kind
of fun. We'll look at some real fishing campaigns I've come across and see how they operate and see if we can figure out any patterns. I'll dive into some tools and services and figure out if we can flip the switch moving from being reactive to a more to get ahead of the of the the curve all while facing the challenges that comes with it because why would it be so easy? And finally, we'll talk about how we as a community and industry can take can tackle this threat together, even when it feels like you're chasing a laser pointer. A little bit about myself. I'm Jeffrey Chisnel, aka Moon Cake. I love to torture myself on the on the ultra trail
marathons. If anyone asks, I'm not interested in the Commerce Marathon. I'm an avid gamer. I don't play FPS shooters because I suck at them, but I love to play indie and mobile games. I'm a security analyst at Orange Cyber Defense, and I love to break things. I'm a staff member at Hack South, one of the largest South African ethical hacking discord communities and one of the organizers that kept down bides. Right, let's get into it. What is fishing? Fishing is basically when a scammer throws digital bait and hoping you'll bite and cough up your passwords and credit cards. The classic hook, line, and sinker. Except you're the fish and your wallet's the prize. I'm pretty sure I'm talking
to a technical audience, so fishing should be familiar for you all unless you failed the challenge that I showed earlier. And I'll just give you a brief summary of what fishing is. There are many flavors to the sneaky scam. Mass email fishing such as um emailing your bank emailing you, SARS, Netflix, Netflix and even Uber. Spear fishing. This is more targeted at um individuals or organizations. Smishing. This is when you get a uh fishing from into your uh mobile phone. Fishing is when the scammer actually picks up the the phone and pretends to be your bank. Another one is your cure cure fishing. Here they just make you scan QR code like besides Joberg.
Domain spoofing. What is domain spoofing? It is when an attacker registers a domain that looks almost exactly identical to the real deal. The goal so that when you glance at an email or click the link, it looks perfectly legitimate unless you really squint really hard and notice that typo or swap letters. So, let's go over some of the different types of domain spoofing. You have your typo squatting, your subdomain spoofing, your combo squatting, your cousin domains, and your homograph attacks. All right, come with me on a little adventure. We'll trolls through some real fishing cam scams I've come across. As we poke around, let's see if we can spot some of the indicators that these
scammers use and see if we can spot use them to try and be more proactive later on because honestly, no cat deserves to be in the hands of a scammer. So, last year I sent a message on my socials to ask for some fishing links so I could investigate and so and solve the the the puzzles that I like. Hippen aka Ross dropped me a message and said, "Hey, here's a link." So, this is where my fund started. So, here is so here's an email that claims that you have 24,000 un unredeemed ebooks with an HTML file attached. So, one thing I like to do is I like to use online tools, one such being as
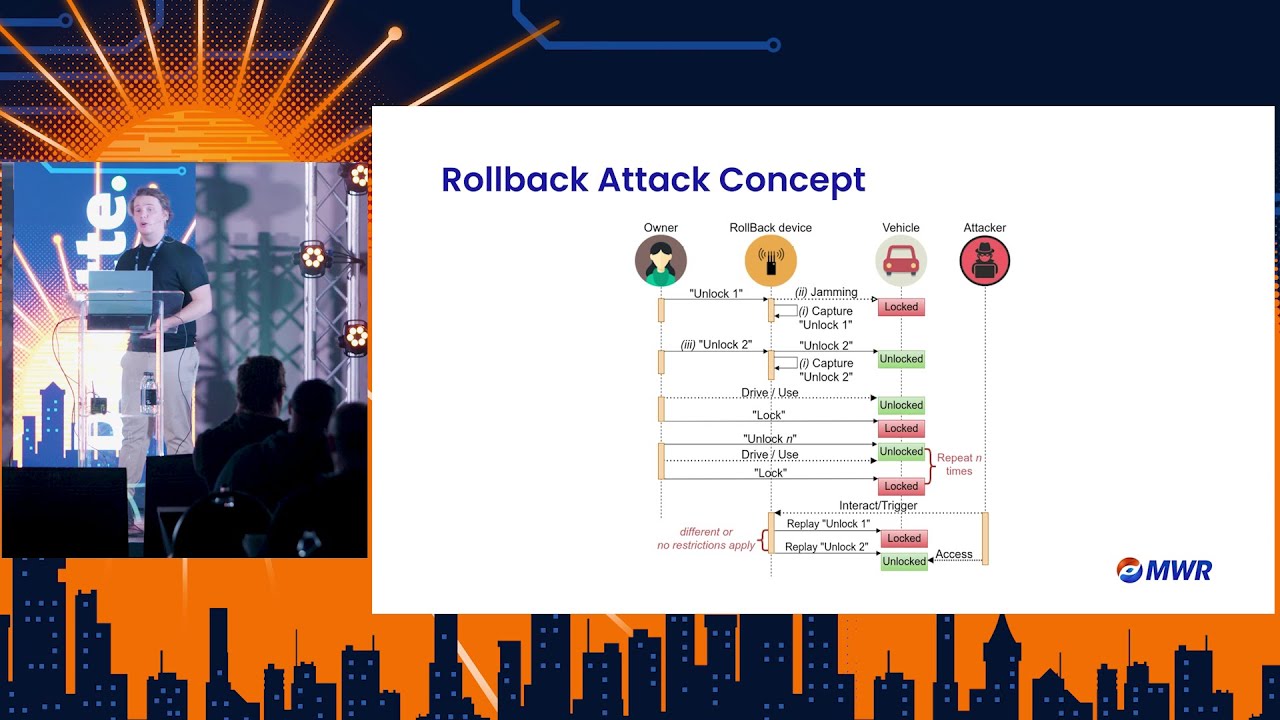
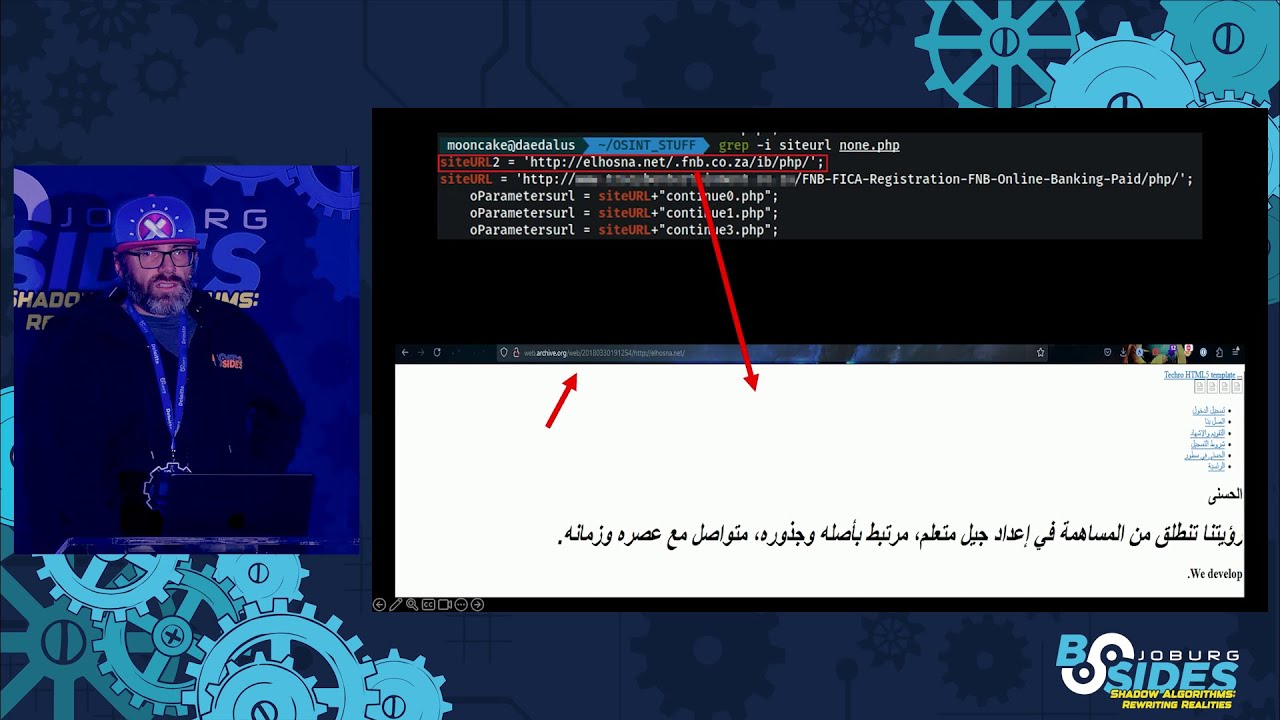
virus total, where you can throw suspicious links or files in there and it'll give you any signs of any indicators of maliciousness. So, here you can see uploading the HTML file, it gave two indicators that you can see. One other thing I like to do is to look at the source code. sometimes virus total and the likes don't um don't have new uh campaigns that that are on at the moment. So you can if you look at the source code you can see any indicators of of maliciousness there. So as we can see there there's a none.php. A further look in that PHP file we can see two variables in there site URL 2 and site URL.
The site 2 had a reference to alhosna.net which at the time was not available. So I threw it in the internet wayback machine. For those that don't know what that is, it is a digital internet archive where you can view a website at any point given time. So throwing that into the wayback machine, we can see that it was from 2018 and some Arabic education a site which I assumed was compromised. So looking at the continue 0 1 and three, we can see some references to a AZN internet banking which was from New Zealand and Australia. Further down we see that there was reference to FNB and as well as standard bank. So clearly this fishing kit has been used in
multiple campaigns. So now we look at the actual fishing page. Here we they get the user to enter their credentials coaxing them to to cough up their money. Here we have the to validate their card number, ATM PIN and so forth. Another thing that the we uh that you can look at is directory listing. Sometimes the the usually a compromised site they don't have their directly list they got the direct listing enabled. You can then see what type of files are there and see how they to further investigate. Here we can see there is one is the homepage, two is the verification page, three is the OTP, couple of CSS and image folders and then an interesting
PHP folder. In the PHP folder, we see the three files that we saw, 0, 1, and three. Don't ask me where the second one is. Doesn't seem that it can count. Uh, there's a PHP light folder and a SQL light PHP. So, we look at the PHP admin PHP. It's got some authentication on there. I tried to do some default passwords, but yeah, none none none worked. There was a results DB file um but sadly it was not accessible that made me sad. I assumed this file would have contained the credentials of suspecting victims but notice that the date was 4 years prior. So either this was part of some other fishing kit or that no credits
were actually being sent there but yeah I have no idea why that file was there. So nothing further to look at on the site. I decided to look through GitHub for references to the FNB FIA. I found a few um repositories there. Having looked at the repositories, uh one was forked from the original, but this was from four to five years ago. Cloning it so I could so one could see what fishing kits they were loading. Um, sadly this error came up that the GitHub LFS was over quotota. So I did a quick Google search for this and found out that the person maintaining it um didn't have time for to maintain it anymore. So it was time to do a takedown notice.
I sent the email and was hope you know sometimes you send them and you have not not much luck but the next day yeah smash got one.
So the next one was just a credit card monthly e statement also with an HTML file. the reference to amatsulum.com. This was also clearly compromised site um being hosted at namecheep. This is just the front page. Um this one had directory listing. Then there was a interesting admin folder. Within the admin folder was a debug folder along with some various uh PHP files. But one interesting file was a MP3 file that was a 3second clip of a Morse code. Truly bizarre. In the debug folder, we saw I saw numerous debugging logs which I assumed would give us indication of what was behind the scenes. I was right. We can actually see the post requests being made which seemed to
be to another server on the 27th of July. more logs for a few days late from a few days later. We can see that the site they were posting to on the 31st of July started giving a 403 which says that the site that they're trying to post to is is being was taken down. We can see there that it was taken down because of their terms of services. A few days later, we can see that they actually used another site as their previous one was taken down and this time they were using a local2.net domain. But in this one, I actually noticed that there were actual legitimate credentials of a victim that was sent was entering their username and
password. So with that, I did a takedown notice, sent an email to NameCheep detailing the what I saw. They replied back to say not sufficient evidence, which I was really confused. So I'd sent them come at me, bro. I'm going to just even be more hard on you. And every day since then, I was looking at my email to make to see if they sent me uh to say that it was taken down. But on the se seventh day, I got the account suspended. And that's another one. [Applause] So you all should know this one. You receive an SMS of an outstanding career payment that is required. So user would be a URL shortener um to
the URL scam. And in this case, a horribly spelled the courier guy.buzz. Two Rs. Well, two double Rs. Yeah, but remember back to domain spoofing Trixies. They are. So, this page consists of you entering your um credit card details and a C uh VC. Shouldn't that be CVV? they can't even spell um and then your bank name. So another thing once you complete the whole process it to go back home it actually redirects you to the career guy legitimate site. So if someone goes through the page they won't be they won't really notice what's just happened. So, so intercepting the request through burp suite. We can see three distinct uh post requests, a product store, a
product card and a product code. The last two just being a OTP. So, we'll focus on the product store. In the request, we can see the requests being done and that was being done with a post request. What happens if we do a get request? I did this and it gave a nice verbose error message which allowed me to look at the directory structure below and in this case it it was under the home folder take elot maybe it's a reference to take a lot um so now because this did not look like a compromised site and this was actually a site that was registered by a scammer I would usually use subdomain enumeration so I used a tool called
Sublister and I created my own little script which uses sublister and various other things and it it uses some providers such as virus total and netcraft to search for other subdomains on those. Um here I found the domain to be behind Cloudflare but I noticed an additional domain there. So doing the same thing as the previous we look for further subdomains on the take elot.live and we see that there's references to ram courier SARS and take a lot which yeah it's been used for multiple campaigns but we'll notice that it's also being used um on the same IP and um hosting provider. So just to confirm the RAM curb buzz was in the same folder structure as the race
and once we do a NS lookup on the IP address we can see that it's been hosted at the onion host. So I sent a takedown notice listing all the domains that I found. 6 hours later the account is suspended and the websites are taken down. I just confirmed and we got one. Does that classify as one? [Applause] So, this is becoming kind of fun like whack-a-ole Mario style. This time we have another career payment for import duty tax for 16 rand 13. Here we have a URL shortener goes to an R2.dev domain. long string. Before that, we get the following page. Confirm. And while I was editing this slide, well, my slides two days ago, I only
noticed this now. Even after a while being for this, seeing this for a while, the grand total did not match up. They they can't count and they can't spell. So we go through the whole the whole process again. Uh credit card OTP OTP and yeah scammers got monopoly money. At this stage I switched to a project discovery to this project project discovery sub subfinder tool as this now s this actually surpassed the tool I did which was using the sublister and this this tool the subfinder tool uses many more providers such as virus total who is xml api search spotter but all but use using this you need to have an API key And there is
rate limiting and you can only use queries for uh certain amount of queries depending on your subscription but it gives many more more um subdomains. So when I ran it it came back with 725 subdomains. At this stage I didn't understand what it was looking at. Further, I added another tool called HTTPX also by project discovery, not to be confused with the other HTTPX to find the status code and the technologies what they were behind. They all came back as Cloudflare. So, I'm pretty sure some of you are laughing hard right now because this guy, are you living under a rock? Apparently, I have. Now, for those that don't know, Cloudflare has a service called R2,
which is their cloud storage, the same as Amazon S3. This allows you to run public buckets. So, you can host sites on their R2.dev domain. So, coming back to so because this was in CL in front of Cloudflare, let's have a look at the source code. We can see two suspicious URLs there. If you don't if you don't look carefully, you'll just think that it's a normal jQuery CDN, but we throw we throw the URL into virus total and we can see that it's Christmas lights. Looking at the JavaScript, we can see that it's a little bit obuscated. So me trying to make sense of it is like me trying to solve a Rubik's cube. Not
going to happen in a week. But thank goodness for tools out there that can decode it in seconds. So we look at the requests being made. There's a CC.PHP OTP and another OTP. Putting this through Burpuite, we can see the request being made. And during the request, I noticed this the following a reference to some bot of some sort. More on this later. Another thing I noticed in that was created by Megalord. What is this? A quick Google search and it is apparently a hacker for hire. So let's go back to jQuery link. We saw that it was using cloudns.nz. What is cloud DN cloud NS? It is a managed DNS hosting platform where you
can create your own subdomain on top of their their domains which is similar to thin DNS and you can point it to any other web hosting uh platform you wish. So one thing I did was run run subfinder against the cloud ns.nz and search for the jQuery string across them all. And as you can see there was multiple uh domain subdomains that came back all on the same IP. So just to confirm doing a reverse lookup on the IP it was being hosted at hostinger. So we go off and we send a takedown not notice at cloudns and they confirmed that it was um that it was marked. I sent through two email address emails to clouds and hostinger
and again unfortunately I could not find any evidence of it. I was like come on guys. So I sent another uh email detailing it and finally both of them replied. So, I just double checked to see if the dom uh the domains were taken down and we can see that it was not um they could not get to it. A year later, I tried to access it again. Um the R2.dev dev domain this time didn't that gave a 403 and not a not accessible but Cloudflare actually took it down permanently which is which was good so a quick one to a high level view of this you access the r2dev you you returns the jQuery DNS at
cloudns and then gets the files from the hosting app So, we took the that one down and that one down. Two more down. Yay. This was fun. [Applause] Now, you conspiracy theorists out there. You've all ordered something from Take a Lot loot. I've even heard of people opening bank accounts where a few days later you receive an SMS to either make a payment for the courier or to ficker your account. So, I ordered something from Loot. I got my tracking number on the 23rd. 3 days later. Whoa. What is this coincidence? Both being ram at there. This there has to be something to be investigated here for sure, but I'm not going to go into that here.
So, as I always do, I go through the whole structure. Same structure. Could be the same template because again, they can't do math. Enter your payment OTP and done. More Monopoly money behind Cloudflare. Look at the source code. That didn't help. So I look at the request and this time it's actually look doing a call to Telegram API. So once you enter your details, it will send a request to their to a bot and as we can see there there's a bot telegram bot ID I chat ID and a whatever you put in the front end it would send a send it through there. There was a tool um that someone wrote with Netifi but this tool has been
since taken down. All you do is just enter the Telegram bot ID and it'll give you the bot information and you can send a message there. Once you send a message there, it'll give you a JSON response as you can see there below. But in this instance, when I sent my test details there, I didn't receive my one. I saw some other legitimate details there. Could it have just been a race condition I that I actually saw? I'm not sure. So after investigating some of these R2 dev domains, there was some pattern I noticed with some they were either using RAM.html, CC or home. So I wrote some code snippets just to go find them on the
R2.dev and and it came back with two. So I thought I'd broaden it a little bit. I created another script which should actually uh do screenshots using go witness and it came back with 223 screenshots. All of them most of them being my couer guy but in there I could see DHL, Absa, Netflix and more. I'd got all the source code of those pages to search for the Telegram bots. And as you can see there, there were quite a different um bot ids in there. Um out of the 223, if I remember correctly, there was over a 100 unique Telegram bots. Shout out to Sing and Shifty who at the time decided, hey, it would be fun to
try and dodo them. So I got into the fun, too. created a script to overload their chat chat uh channel and after a while it would hit a rate limit but then after a while it would that rate limit would be lifted. It was fun for a while to play with. Um one thing is to take down Telegram bots is a pain. So if anyone has an easy way to take them down let me know. So, the following I call the litter box of my life just due to the fact that it's hard to find sites with these domains, but they're all actively host um hosting uh fishing sites. Shout out to things Canary. They have a Canary you can use for
credit cards. So, I like to enter those details in there and just see where the scammer is actually trying to use them. I've seen them to try use it at Netherlands, Uber, Google Wallet from Hong Kong, Britain. Um, it is something I definitely want to try look into more. So, this got me thinking. It is pretty much an ocean out there with thousands and thousands of fishing sites. I'm interested to see if I can do this from another approach. Can I somehow try and find a way to be proactive and not wait for the links or SMSs? Although in most cases would be impossible especially if a site is a compromised site and or being um cloudflare or AWS just
maybe I can find some other method. So let's first talk about reactive and proactive. Reactive is something that has already happened. So you are only solving the problems after the fact be it quarantining emails, deleting emails, reporting them or reporting them to Google um safe browsing. Proactive is trying to be ahead of them. So things like domain registration, monitoring certificate transparency logs or preemptive domain registration and monitoring for known patterns. So what do they need? They need a domain, a registar or a hosting provider. So this is where I started. I I I used a service I looked for a service which is search stream. Search stream is a real time stream of to monitor SSL and TLS certificates. It
monitors the updates and deletion and modifications. Uh various um certificate transparency log providers have to sorry certificate transparency um requires them to log log them to a publicly um place. These logs help to detect misuse or rogue certificates and also gives the domain owners uh visibility in their issued searchs. Another one is zone stream. This one is similar to search stream but this monitors for uh DNS zone um updates and creations. So I first had a look at search stream. Uh, Cali Dog wrote a tool called Search Stream, which allows you to interact with their service in real time. When I tried to use it at at the time, um, I just used a websocket. I don't
know if I was doing this correctly, but I left I left it for a few hours and there were no CT logs. I so I wasn't sure if it was me but I followed some some documentation but so I didn't have any luck so I just moved on. So I use so I used zoneream. Zoneream is a tool that was is developed by open intel project um which is an initiative of the univers. it uh they use a Apache CFKA which acts as a message broker so you can interact with it in real time too. This will just monitor for DNS zone uh updates on open uh TLDDS and CT logs as well. Um the
only issue is that some registars and the centralized zone data services um don't all post to these as some of them are gated. So with that successfully uh connecting to zone stream um it was time to get to what I wanted to do with it. I've got to log the data on it, get a dashboard, get some sort of alerts, get the who is data, screenshots and then all the things after that. Now the question was how do I where do I log it ingest the data? I had many database options. Um it was also like um unstructured or structured. This is typically what it would look like just a bunch of unstructured JSON. So I so I opted for MongoDB.
Now the next step was to also get a front end. With me not being a front-end developer, I did not know kind of what front end I wanted. I could basically just do anything. But I eventually decided that because I didn't want to spend hours and hours and this was just a a research um something quick that I wanted to do. I was not a coder. So I decided what the end thing was and I did vibe coding. Yeah, I remember this is just research at the moment and I didn't want to figure out spending months and weeks on those. So this is what I came up with just a little dashboard. No guesses if you can
spot the vibe coding in there. So the next step was to get the who is data. Um what you need is the IP, the ASN, the registar, the registing provider. So you can get that information to get takedowns easier. So to get that who is data I decided to go with the RDAP and who is and IP info. Um RDAP and who is um gets is used to query domain registration and ownership data but both of them offer different formats access and capabilities. Um RDAP is supposed to be the replacement for the outdated who is protocol. Um, the only issue is that the RDAP does not have all the TLDDs in there. So, you still need to rely on who
is. Um, so in my code, I had to do some logic. Um, if RDAP can't find it, fell over to who is and even if who is can't find it, I had to fail to IP info. In its current slate, it is not 100% working. There's still some logic issues in there. So yeah, the next one is screenshots. What I want to do is I want to take screenshot of the first first one that I find and then as time goes on see if the page updates because sometimes when a domain is registered it'll just be the default of the hosting provider and then say 2 days later it will be the fishing campaign. I also want to get a the page source
code so that when you look at the source code you can see the different comprom uh indicators such as the um say for example the jQuery or even I've seen with the save as so this is kind of like what it looked like um you have the domain when it was registered and then all the information of the the who is and the screenshots I've been monitoring since about April up until now and I've logged close to 9 million domains, but remember this is not all the TLDDS. Um the red that you see there is the I've decided to put in weekends there just to see if there was any um change in there. As you can see, people
actually do have lives. Zone Stream does have unreliability issues. So, it's been down about four times for me. Um, the latest being last month, which was down for a day or two. So, when it's down, you don't get those domains. So, let's move on to the my first case. So, one of my first examples of successful was I don't screen looks all right. A bit small. Sorry about that. Um, this one was a fishing site which was um to verify your Capitech virtual card. Definitely not sus. Once I saw it, I confirmed it with with Capek and they and then I sent takeown. Yeah, that was that was that was a nice feeling. So with me wanting to focus my research
on specific things and not try to fix the whole world, what if we just focused on what we have here in South Africa. I I first started out on our banks and couer companies and there are many industries out there. So within zone stream I Zone stream I set up some alerts with certain keywords to look out for certain domains that get registered and a notification would be sent to my discord server. So as you can see there I got a notification for discovery fickerup.com the again not sus right. So you can see there's a screenshot gets the who is I check the page I go through the whole motion of the logging in and investigating.
I send a take down notice. It got taken down quickly. Another one. So it was time to relook at search stream two months later because I was having too much fun. So I searched for other alternatives. I found one search ser search stream search stream server go um and some other other ones in there search spotter and seale but I focused only on search the go and the cale some of the drawbacks of this that of this is you have to host it locally so it requires bandwidth and disk space as you can see below there. So unfortunately I had to run it on my home network and yes it was maxing my line almost
even the database running search stream and seale this was just a week or two weeks of data 180 gigs and n and about 79 gigs respectively. Now, me just having enough for a $5 droplet, this was not going to work as I did try and it would crash the server. But fortunately, zone stream was running 100% on it. So, the amount of CT logs being spewed back to me, I found it very overwhelming even when you're just looking at certain keywords, especially with the CT logs. When you run things like search stream, you have you have an inane amount of data coming in. I still need to find a way to make it less overwhelming.
Let's move on to one last one. So I received this is actually in the last 3 weeks which is you'll be surprised standard. go to ZA. That doesn't sound sus either. So, we get the screenshot. I'll tell you why was sus. They got a signing page here. You can add you can you can enter any username and password and it will go straight to the account verification. Send down takedown notice with and within I think it was an hour or two it got taken down. Then these started popping up also standard a cup one two three four five and I received another one two days ago. So sent a take down notice to the ISP
and I'm going to name drop the ISP. They all come from namecheep. Okay. So 2 3 4 5 Thank goodness for namecheep being so vulnerable. [Applause] So this for me is still a work in progress. In this short space of two months it's been a maze trying to work navigate my way through the challenges and trying to figure this out a way forward. One thing I want to want want to do is be more be collaborative with the community and see who else this inspires. I came into this um research blind. Did not know what other others are doing out there. So this was me trying to figure it out on my own. Um, it would be nice to collaborate to
confirm if a domain is truly spoop spoofed. Well, spooped. Um, cuz you don't want to take take down a domain and it's actually legitimate because there will be consequences for for the clients. So, I just want to break that barrier and find the channels to be to to find it easier. So to recap, we've looked at some of the examples of fishing attacks both from a compromised domains and from domains set up by scammers. We tried to identify the patterns and see if we could somehow either find them before they are registered or go and hunt for them. With some of the tooling, we're able to find these domains being registered by the scammers and take them down before they
even got into play. there are certain challenges that comes with it such as reporting sometimes or confirming if they are legit or not. And finally, some of the projects that that I've seen that has started has died due to the the person maintaining it doesn't have the time or the funds or costs for it.
So the takeaway I want you to to that I hope you take from this is that we can start a conversation and maybe us as a community fight this in a way and maybe it's maybe it's already been done and I'm just oblivious of it. Thank you for for for coming to my talk.
And I'm under my cutoff. Oh my word. That's That's amazing. For those that don't know, my dry run was like an hour. So yeah, the dreaded question. No questions from that guy. >> One question. >> Yes. Firstly, well done. We're all very proud of you. Sorry, Charles Roth. Yeah. Firstly, I just want to say well done. Proud of you. Second question I think that's on my mind and a lot of Hack South people's mind is why were we not added to your fishing uh Discord? That's it. >> Cuz otherwise I can't take credits for the takedowns. I'm kidding. Oh my word. I hate questions. >> Sorry. So, this one should be quick. Um, I noticed you had timestamps for the
initial registration and then the updates as well. Are the what fishing sites being updated faster than a usual site? Would that be a possible way of detecting it? Because it seems like it was very quick from registration to being live. compared to most companies I know >> that is just the data I get from the certificates uh transparency log and the zone stream. >> Yeah. And then the screenshot you had. >> Oh the screenshots the first one the first one is when I initially is is it are you talking about the screenshot? >> Yeah. So the screenshot times they were uploading very very quickly in terms of registration to going live a lot faster than a normal company would in my
experience. Yeah. >> Would that possibly be a way of detecting them? >> Maybe. Yes. I'm not 100% sure. I haven't. Yeah.
>> I don't know who put their hands up first. I'm blind. Hi. >> Sorry. On the Telegram, how did you manage to find the usernames and passwords or was just in the code? Uh, from the one screenshot, I think it was a race condition. >> Okay. >> Yeah. >> Was that actually getting it was accident? I don't know if it it was accidental. >> Okay. >> It was like a coincidence that I've saw it. >> Cool. Thanks. >> Unless unless the channel the actual chat ID the actual chat channel is public, then you can see what the everyone posts, but usually they are private. >> Okay. So for sites which were taken down, have you ever considered building
a script that would monitor reactivations? >> Sorry, >> for sites that were taken down, have you ever considered building building a script that would monitor for reactivations? >> Uh, no I haven't. Thank you.
I don't think they saw you.
Thanks. Um, while you were doing your research, did you hit any fast flux sites? And I've I've seen a lot of fishing pages now also using Cloudflare again with bot detection, which should probably nuke all your screenshotting and stuff. Did you hit any of that? And you got any thoughts of sort of a Rev two for those? >> I've come across that, but I haven't really figured out how to Yeah, this is still early days in my research. So, but I did come across, you know, Cloudflare just giving like a front end so you can't see what is behind it. But I did play around with some tooling like um where you can actually bypass that at
certain at it bypass that front page. You could actually bypass with like um the Chrome headless. There was some tools out there that you could do that. It worked now and then but yeah. >> Yeah. Thank you. Great talk. And um I also had a question around the fast flux side. If you are able um to also track TTLS where those um domains are being hosted, that's also something that could help identify potential fast flux operators. >> Oh, cool. Thanks. >> Yeah, I haven't looked at fast flux, so that's a good one. Awesome. Thank you very much.