Car hacking – a real security threat or a media hype?
Show transcript [en]
I am a Secure Car Specialist with headquarters in UK and offices in Japan. In the last two years we have seen many security results in car hacking. They demonstrate how to optimize the vehicle system functions and the vehicle data. In this presentation I am going to talk about car hacking and give an idea of the real security issue, just a little bit. I'm going to demonstrate the current situation in the automotive industry and for the automotive industry, ensuring that my highly autonomous cars are secure for... I can say that cars are computers on heels and this is not an extreme metaphor. A motorhome is highly connected with additional functions that didn't exist 15 years ago.
The first kind of hacking research was in 2010. Many more security researchers are demonstrating their results and their findings. I'm not going to get into details of those hacking stories. You might have heard of the latest G-Hack which got the mass media cover. It was, how to be recalled, they sent USBs out to the affected, they updated themselves or even visited the fellowship to help them. This is when you use a smartphone or laptop that the user is used to install and update a card that they had to read on the vehicle in order to hack it. We have increased public card hacks that have been the last few years. You may see them below,
but two or more conferences are expected to take place in the next few months. Blanca and ESCA are not going to be are going to take place and we know already that these are going to demonstrate new findings. We want to show you a video to give you a research that was at TechBase in 2015. I will explain. Oh my gosh! Here we go, here we go! Oh my gosh! He's trying to stop a car but because there is someone with a laptop she can't do anything. Chrome is activating some control from the laptop. This is, this was the US TV. People saw that and they were scared or not and that's how the car hacking is real or is
a media hype. The truth is this is from data that defends advanced research in the US which is working with other security researchers. If you know Miller and Balancer, which were the two security... They know advanced research in car hacking In Europe we have NISA, which is money security. They have guidelines on how to ensure security on cars. But all these are in a very high level because everybody is violent. At the same time, where the US research agencies, European research agencies are working on security, Hackers are working as well. If you don't have time, there are already more than 10 hacking tools available where anybody can take, connect to their vehicle and start doing the wrong tools of how
to successfully compromise a car. You may know that there are spoils, waitraces in the leaderships. An additional tool where you can solve on the car software.
reverse engineer the system in the vehicle. You can monitor the communication between the vehicle and even a smartphone application associated. You can inject messages and also you can do the actual testing which can be used by researchers to increase the security. But because it's an open source, we can't edit the audio script by the good guys or the bad guys.
So 2017 was one of the years of ransomware. We have seen so many examples of real attacks, especially with the Rizobona crime attack. The hospital was out of service in certain cities. There were many attackers and they couldn't perform
health checks until they pay the ransom. So something similar may be applicable for cars. For decades we have seen that theft is in two forms. There may be theft of vehicle or theft of the vehicle items inside the vehicle. But we may see in the future theft of the service vehicle as a service for example you may be reusing your car and suddenly you may see an notification you can't use your car anymore until you pay a ransom you may consider who we want to hack us to cause a real-time incident something that may harm because we are talking about lives when we consider car hacking So a lot of times we underestimate the people
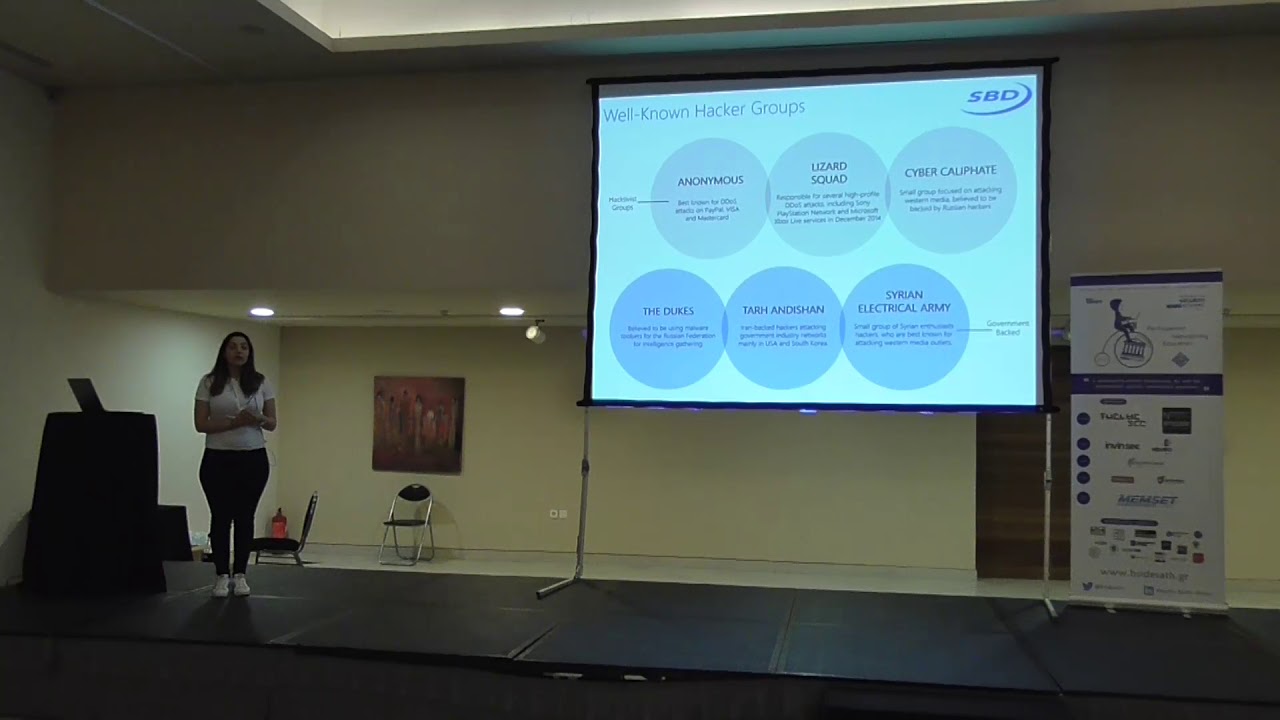
that are able to hack. For example, there are government-backed hackers, that fight employees that want to take advantage of the access that they have in the systems to damage their own work with because they are not satisfied. And the motivation behind an attack may be very or even formal.
Not surprisingly, many of those groups remain anonymous. That's why we don't have enough information to be able to know who is working on cat-packing or who is focusing on other systems. But here are just examples of activist groups and government-backed groups
Two years ago, a report was published by FBI claiming that there are clear indications that criminals may use autonomous cars as vehicle vehicles and at the same time, Security Bureau of the F-Secure said that they have clear evidence that ISIS is working on autonomous cars. We have seen recently a few examples of terrorist attacks where cars were imagining to perform an attack without losing people from their room. They organized this in advance, sent the vehicle to a certain location, autonomous vehicle where nobody would be in sight, where nobody would endanger their own lives and then they would trigger something. When it comes to modern cars, we are talking about more than 50 attack points that they can be taken into the
hands of a hacker to perform an attack. It's not just the vehicle itself, it's the telematics providers that they see and the service provides. We are talking about the backend services, the servers of the automotive manufacturer. They control the operations. We are talking about Wi-Fi, we are talking about the DSRC, the advanced data systems for safety. So there are more than 50 autonomous cars. So this is an example of the autonomous car architecture. This is a simplified version. We have the road, we have a gateway, there are external interfaces and car services. So it's really complex.
with autonomous car. We have additional sensor fusion where all the processing from the sensors are taking place and we have artificial intelligence. So with sensor fusion, the first at the sensors itself. Real time examples, people trying to not function properly, we check the data received from the cameras. All the additional interfaces that are working sensor vision, we have data updates, we have the V2X communication, the cloud computing, and we have connected a highly autonomous infrastructure, which is far more complex, and at the same time, the threat landscape is increasing. So when we're talking about highly autonomous cars, we are talking about an advanced system that is processing data, So we have the case that the
vehicle is learning from experience and is processing and is getting better over time but at the same time is communicating with other vehicles in order to increase the efficiency of the vehicles. So what are autonomous cars? We have here examples of the potential attacks as categorized by strides. a threat modeling framework for rising threats and we have a score of these are just six examples of the 100 additional attacks that will take place in a highly autonomous car. So now we can see that the differences in attack surface are really technology dependent so we will the vehicle, the accident rate is increasing as well. With the highly autonomous cars, ultimately the full autonomous vehicle is much higher. The reason
is that there is no driver fallback. When we are talking about autonomous cars, the driver does not have control anymore, the will to control the vehicle in case of a hacking. That's when the real problem begins.
we can consider that they are trying to control the situation. So in order to control this whole change, we have to create into the auto-winding industry, we have to consider security the design phase of the vehicle or an additional system. We have to perform threat modelling, risk assessment and actually perform penetration testing in every single vehicle. Car packing is not a real problem now but when thinking about cars you have to keep in mind the very long life expectancy. When a car is built it is available in the most or even 20 years. So it's not like a phone or a laptop where identity replaces them. For example, for a smartphone, it's usually normal to replace it every three
years, but with the cars it's a completely different story. So for threat monitoring, we have to consider both the attacker's and the attacker's point of view. We have to consider both the attacker wants to for example to take advantage of primary functions, get access to the vehicle data, the history of the locations of the car, the facilities, parts of the vehicle, the facilities and threats that may exist in the architecture of the system. So that gives us an idea of the system, able to have the essential security requirements that will cover I can't complete, minimize the risk of traffic. For measures that are starting to modernize the industry, we need to have secure gateways, we have hardware security modules,
we need to have a campus and a management system, something like similar to a laptop or to a system that will be able to detect So the key takeaways from this presentation are basically that cyber attacks are increasing in general and highly autonomous, we have as a consequence that the attack surface is increasing as well and cyber security is becoming a real issue for the automotive industry. A lot of most of the action stories we've seen so far are very mental or practical into a safe environment but we need to follow the countermeasures, the standards and the methodology in order to prevent a real hacking incident happening in the next few years. Everything is taking part in order
to be part of the actual mutation phase. That's why we have to start from now in order to have secure... There was a talk about mobile home interception, SSL interception. In your slides you showed network interception The current protocol for boosting cars is developed by India. security in place that's why there is no direct verification of the message but the every product manufacturer has specific card messages and that's why anomaly detection will be able to block any message that is injected that is not part of the given protocol But the efficiency of this is currently not satisfactory because the detection has to be developed specifically for its awareness of the age of development. Is there
any other questions?





