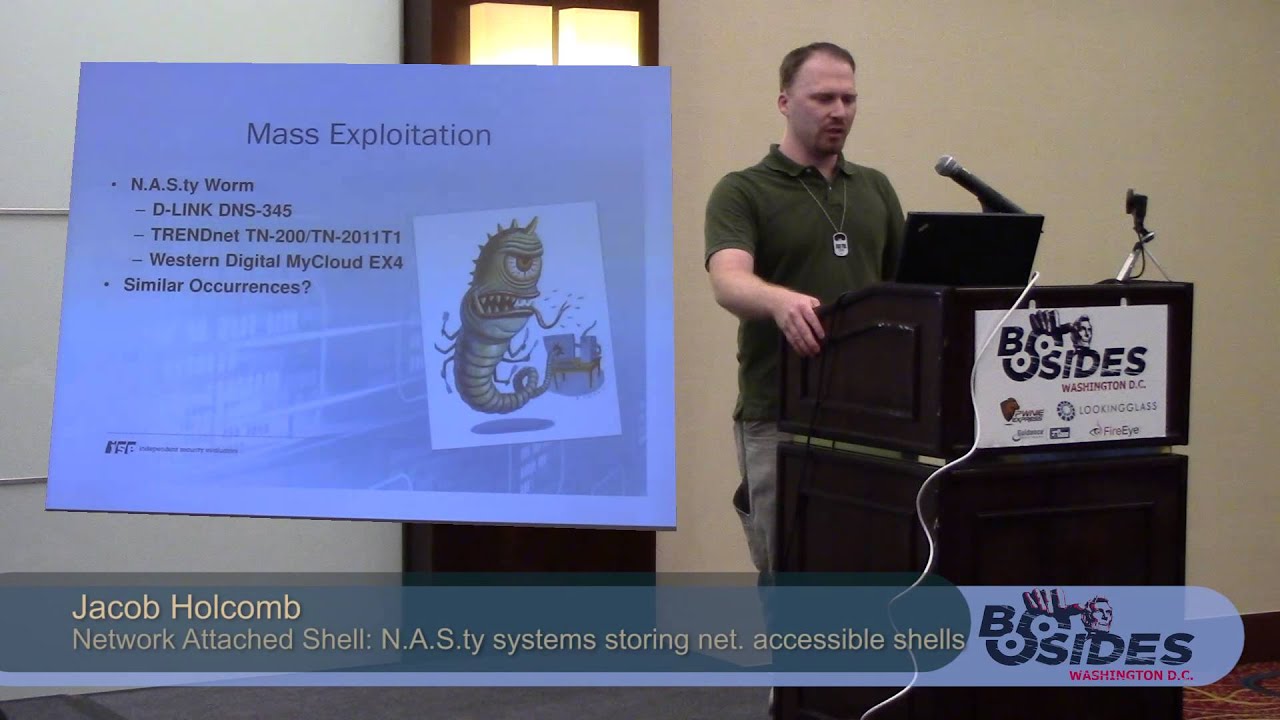
Network Attached Shell: N.A.S.ty systems that store network accessible shells
Show transcript [en]
all right everybody this is network attack shell nasty systems that store network accessible shells some of you may have looked at the program and seen Jacob Holcomb talk at other events I am not Jacob Holcomb we tossed the coin he went to Amsterdam I came here um I'm I'm presenting This research that was conducted by Jacob Holcomb at independent security evaluators I'm a software developer I'm a co-worker with him uh he this is his information if you want to go bug him on Twitter or LinkedIn or check out his blog feel free to do that he's having a good time right now so uh I encourage everybody to give him a hard time a little bit about ISE uh we're ethical
hackers and computer scientists we have we've got customers in Fortune 500 Enterprises and the entertainment industry Health Healthcare we like to look at systems white box if we can do it why make it hard for ourselves um so why are these sorts of um why is it important to check out network attached storage systems we bought we bought 10 network attached storage devices and we found that 100 of them were vulnerable to exploitation we have no reason to assume that anybody else's are any better storage systems are not the only embedded devices with software deficiencies some of you may be aware of ise's other research of these small office home office routers which are also fairly Swiss cheesy
um and as as we add more and more things to our lives this is just going to become more important now everybody now include everything up to your uh thermostat is now networked so we're going to go over some of the um some of the key players what our network attached storage devices uh what are some of the what some of the system functionality we're going to talk about exploit research development and the absence of security on these devices and then we're going to talk a little bit about how we can remediate it to the level that we can some of the key players Seagate Western Digital Netgear you know your usual uh your usual suspects for small office
home office equipment if they make a router these days they sort of make most of them also make some form of network attached storage and everybody buys these a homeowner might uh you know like a home user might buy one to store all their uh digital pictures or their music files small businesses uh it's a great way to have a bunch of network attached storage without a whole lot of administrative overhead and large Enterprises all these sorts of things also show up in large Enterprises as well everything from blessed installations where the IT department allows them to install this or a small Department decides they need some storage and they don't want to go through it so they buy it and just
connect it up most of the devices that we were evaluating tried to get a big cross-section of the of the market as it stands some of the some of the technology that's implemented on these network attached storage devices I mean obviously network attached storage you have to have the ability to store and retrieve files so you've got Samba and NFS got to configure it so you'll have telnet SSH HTTP and then there are some things that uh we find unnecessary um why why would you want to go to the cloud to manage the device that's sitting right next to your computer I haven't quite figured that out but apparently the cloud sells these days so we're going to go
we're gonna go through we've got a summary of uh summary of results we're going to talk a little bit about how we tested it and uh talk about exploitation and a couple of demos at the end of The Talk um as I said before every device that we tested had some form of root compromise half the devices could be exploited without Authentication uh we've got 22 CBE numbers assigned by miter and we've only just started these are these things are chock full of holes so scanning and enumeration we just did you know started off with the basic system scans we end mapped all the devices check what all what open what open ports there were we grabbed all the banners
and we used that to guide our future exploitation all the all the running Services we spent We examined we got a hold of the source code for web applications places where they use GPL software this soft this is available online we analyze the web applications for common vulnerabilities and we did some Network closing we discovered cross-site request forgeries buffer overflows I mean back doors poor session management basically the laundry list of all the things that you find that could be problems somebody has has a problem so when we when we managed to get into the Seagate uh we poked around a little bit and we did not use the back door but we discovered uh as you can see there's
user w4l980 CK blah blah blah with a password so Seagate has hopefully left us an account with the password on our devices thanks CD moving on to the Asus store we analyze there in this case we're showing that we're analyzing the session cookies to the left of the screen you can see the cookies in a list from sequence from several connections note the 53df C90 the cookies had showed a very low amount of entropy meaning they're easily guessable the entropy basically all exists in the last two bits so poking around a little bit more we decided to just print out the time of day in in seconds and note the 5 3DF prefix again sure looks like instead of generating a
random session cookie they just grabbed the time and use that so then we then we move on to exploiting the vulnerabilities that we discovered exploiting things like command injection there are missing function level access controls that we found and the whole the whole gamut command injection is where the the user input gets eventually used by something that runs the system command many of the management interfaces are borrowed so they so the web application behind the scenes is calling a Unix system command to execute something like turn on Samba and unfortunately they don't do a good job of scrubbing user input so if you add to the end of that we can run other more nefarious
Developers please please try and Implement counter managers we do not want I mean wherever possible avoid calling shell that's just asking for trouble if an API doesn't exist gotta sanitize the book gotta sanitize the user input the user is going to put in something that you don't like or if not the user than somebody like us these are you need to just make sure that we do a good job of wiping the input so that things like reverse shells will make through
cross-site request forgeries I think we were all familiar with them it's an attack where we ask and where we convince and unsuspecting uh you victim to execute a or a web command visit a website and that website uses their credentials on their browser to go do something at a third site there are ways that we can avoid the problems associated with cross-site request forgery log out of all your web applications there's no reason to leave yourself logged into your router or your network attached storage don't save credentials in your browsers manufacturers we need to implement any csrf tokens and check to make sure that you're coming from a location that you expect not uh we don't want to be
running administrative commands when our referrer is not administrative interface if we're coming from some place in Czechoslovakia and we're in the United States that's probably probably a bad probably a bad thing uh other things anytime you change a state change a password turn on or off a service it would be a good thing to force the user to re-authenticate to the system our missing function level access controls their doesn't do it doesn't do much good to put up a big security door when somebody can just walk around your gate when you're when you're actually performing the important task changing a password turning on external web access make sure that the user that is performing that action
is both authentic and authorized to perform that action
buffer overflows we've been working on these since 1993. they're still here you have a 128 bytes and the user gives you 512 and now you're now you've overwritten everything else on your stack and bad things happen we know we know the problem quit quit using unsafe functions don't use Stir copy don't use S printf perform balance checking make sure that the input that you expect to be 128 bytes actually is no larger than 128 bytes um let the compiler help you out we've got stack protectors we've got um we've got data execution prevention please turn these on these are not on by default in the devices that we evaluated we're going to uh there is a
worm that Jacob Holcomb has been working on he is going to be giving a demo at I'm sorry a he's going he's got a webinars that is scheduled for October 23rd I believe if you visit his uh his website at the beginning of this he has the when and where pre-registration is required his worm currently operates on following devices there are excuse me there are there are other worms that have happened in the wild that are similar uh the moonworm and the there was a worm that q a p uh shell shock that was recent the worm scans for an open network attached storage device of the brands listed fingerprints to make sure that device is what it expects
exploits it downloads the worm keeps going so your typical typical worm operation these things this uh this will be demonstrated in the webinar there's there's the webinars address like I said October 23rd so we're going to look at the Terra station 5600 we've got a it's got command injections and we've got missing authorization checks in this in this demo
here we're logging in as the administrative user on the interface note the session ID
you log out and then we come back as the guest user which is a which is a non-disableable account on this device it always exists
note we are now logged in as guest not as admin
here we're showing we're trying to connect to the device nothing is running on it got a new session ID no this session ID is not the session ID of the previous admin here we're showing a request that does a edit of the password we're replaying the request from a from the admin Note invalid session ID so the old set the old session ID for admin does not work you grab the session ID for the guest user and replace that and we get a response uh the password change on this particular device is a two-step process so the first the first step is it's expected for that to be no here we go through and we're operating
the second step changing the session ID again to the guest users session ID and we see that the the device has changed the password here we're going to log in now as the administrator using the newly changed credentials
it's the password we're using up there copy and paste again so guest has successfully changed admin's password
now we're going to now we see we've got a new session ID and we're going to up uh we're going to create a we're going to use command injection to start up and telling that telnet server telling that in and root congratulations
the next thing that we're going to look at is a network Netgear Readiness 104 uh this device sitting at my feet this one we're going to use a command injection and a cross-site request forgery this is this does require tricking an unsuspecting user to visit a to visit a page for the cross-site request forgery to work
over here I am logged into the Netgear Netgear Readiness I'm logged in as admin some form of phishing attempt would be needed to or you'd have to convince them to log in but then we're going to
right here we're starting up a netcat session it's listening on a port we're going to start up a reverse shell up here
we have the we have an example web page that you would have to trick an unsuspecting user to there is so
right up there the busy box NC is where we've got a reverse shell that we're going to have uh we that we're going to inject into the system and that will connect down and we'll be able to see in the lower terminal connection so over here
we're going to visit a website which unfortunately is cut off a little bit let me see if I can rearrange this
so this is the file that we catted over here so we're going to convince our user to visit this website that has the cross site request forgery in it sitting here now we come down here and we've got a root shell we can do things browse around on this on the system
you can see we've got the we've got the shadow password file we can we can even do fun things like add user
and now we happen to have now if we check shadow
you can see we now have added an additional user and he has a home directory and everything that's fine
these systems these systems really don't have much in the way of security as they come out of the box this is this is not just network attached storage systems layer 3 routers the ISE Soho office small office home office router project has already has already shown routers we've got IP cameras that are beginning to show up thermostats are you know the nest various other companies our manufacturing devices that that are intended to bring about the internet of things but these things really don't have a whole lot of security and nobody is really focused on making these devices survive the hostile environment they're going to be um the router project has over 56 CBE numbers we have more than 20 cve numbers issued
for problems in network attached storage continue to keep exploiting these things and submitting to manufacturers so that they can Harden their devices but right now they're don't trust them out of the box so what can we do better vendors a lot a lot of this for the average user is going to rely on vendors patch management needs to be at large a larger part of their system we need to be able to fix these holes as we find them we need to we need to work on developing these devices secure out of the box Implement things like defense in depth there if we don't want a we don't want a file sir we don't want a
router that can then lead to a compromise of our file server least privilege don't let don't let a user that is starting or that is just sorting files on the device don't let them change IP addresses consumers when you buy one of these there are a few there there are a few things that we can do to help reduce the attack surface change the default credentials when they when they come from the store and the you and the admin account is admin and the password is admin that that lets anybody who drives by load up and get into your device so trying to try to disable services that you don't need you know if you don't want to manage
your network attached storage through the cloud make sure to turn that off just in general try to try to avoid leaving these things in the state as they come out of the box upstairs we've upstairs we have been running the so hopelessly broken so hopeless we'll be broken the hacker contest ants we've we've been running this at Defcon and derbycon we'll see you again at work on you can talk to us about our previous research with the small office and home office routers and the
I sort of so I guess I'll open the floor to questions there are some I apologize I'm not Jacob
um
yes they are the some of the vendors have been more responsive if I was if I was Jake I could probably tell you which vendors have had have been more responsive we have been following responsible disclosure we've been telling these manufacturers about the problems so hopefully they have or will have firmware updates in the near future it's not quite as good as home routers at this point where you can just download something like DDWRT but hopefully we'll get something like that for the network attached storage
so the question was have any of these vulnerabilities been found in DDWRT and open wrt I actually don't know I would I would I would suggest pinging Jacob Pokemon one of his methods on one of his uh forms of contacts he will be able to he would be able to answer that
so the question is what can we as the security Community do to help help this situation name and chain uh create competing products at the at the risk of putting my foot in it I'd say probably a little of all of the above I I personally favor responsible disclosure first let the let the manufacturers have the opportunity to fix their problems before we go about pointing fingers I think pointing fingers should be reserved for only very egregious cases creating and creating secure products I mean the the market will tell I suppose I mean DDWRT and open wrt came about because small office and home office router firmware was not sufficiently powerful and not sufficiently secure so I see no
reason why a product why a project such as that could not be started I think I think it would be good for the market as a whole but that's something that something that can be done
anyone else
the question was have we looked at Network enabled printers and scanners and whatnot not yet I think I think it's on our I think it's on our plan of things to do but we don't want to talk for other people in my organization these seemed interesting so we started looking at them first
anyone else
don't see any more hands so I guess thank you for your time