BSidesCharm 2024 - Top Ways I Still Hack Your Company (and How to Defend Against Them)
Show transcript [en]
[Music] so today I'm going to be talking about the top ways to hack your companies still and how to defend against them uh in in case you haven't guessed by the title I'm a penetration tester uh I uh lead pent testing over at RIS Point I've been doing pentesting for a while along with network engineering and uh uh software development um so today I wanted to talk about a couple areas I picked out where I'm commonly getting wins against your environments both application and network along with um why these areas are still prant nothing I'm going to talk about to day is zero day it's I'm sure stuff all of you have already heard of uh but why are these low hanging food
really persisting and what tweaks have kind of happened to them that allow them to do so so I'm going to start with application security and when I was trying to figure out what uh kind of vulnerability to talk about first I took a look back at uh a couple years worth of reports uh put together and looked at the high and critical vulnerabilities and just broke it down and what's the most uh prevalent we see out there and uh above anything else it's improper authorization um which I'm sure might not be a surprise to anyone um and this aligns with what we see from oosp so oosp in 2021 upgraded uh what they call uh broken Access Control same thing up
to number one so it's still a very prevent and a very serious uh kind of issue so just to give a quick uh kind of background authentication is hey am I who I say am authorization which is uh more prevalently the issue is am I allowed to access what I'm trying to access so why is it so hard to get authorization uh right so I think there's a couple components that go into this uh first applications without a doubt have gotten more and more complex over the uh past couple years this me more roles more tenants more routes and kind of meshing and testing the uh Matrix of all of those to make sure we
have proper authorization checks in and logic in each of those is really getting harder to do we're needing more complex test to do it also I think that uh SAS and Das scanners are really struggling to pick up on these authorization issues over the past uh several years they've gotten really really good a lot better at picking up on things like cross- a scripting and SQL injection but authorization is a lot harder and more nuanced because it's for one application say I can list all the users from a standard user role maybe that's okay for the application for another type of application that uh action could be catastrophic so but the scanner has no way of knowing what the uh truth of the
matter is so what are some of the defensive measures we can take a look at and really it comes down to for a lot of these good cyber hygiene this is uh where consistency is key auditing and testing every route every role every time so making sure that we're consistently testing that whole Matrix of authorization also building the authorization as part of our Dev culture making sure that we're reviewing for it looking at it in every kind of commit we make to the code making sure that we have authorization um focused on I'm going to move on to exposed secrets I'm kind of worrying through these I know uh we only have 20 minutes and I'm keeping you from happy hours so
wanted to make sure we uh cover a lot of ground in a short amount of time so Expos secrets we see a ton of I'm sure you've all seen stories like this uh Microsoft Mercedes uh an employee inadvertently commits to a public code base some uh proprietor code some uh Secrets Cloud credentials API Keys what have you very common occurrence who's the enemy here well of course it's GitHub or whatever Version Control System you're using uh joking side here's a case found a couple months ago this is a fortune uh 500 company this is in a public repo on their organization and it's API key and secret and um uh URL info for a API
endpoint that allows you to reload payment cards so like think like gift card reloads and stuff uh so as you can imagine a prime target for a threat actor um so how are we defending against this well secret scanning tools have gotten a lot better and there are some really good options out there there's githubsign and on the open source side we have truffle hog uh which is really great Tool uh should definitely be implementing some kind of secret scanning if uh you aren't already but there's a kind of a attack service that's being missed and where we're getting some wins on where we're able to uh get in on some of our clients and I
call it the shadow it of uh secret exposure and that's on personal GitHub accounts so in this case this was a client from a little bit ago we had um the employee uh of the client uh their personal GitHub account and they have a repository there called dot files for those of you that aren't familiar with do files it's a way of kind of managing configs uh developer configs desktop configs and moving them from one machine to another and in this case um to make it nice and easy for everyone uh he added uh the organization AWS keys to easily move to another machine and uh that allowed us to escalate into their AWS account and of
course you can imagine where from there so this is something that our secret scanners aren't going to pick up on because it's not within our organization repos so really this is something that should be worked into your organization's threat models saying hey we have employes they have personal GitHub accounts we need to consider that and considered to be part of a uh a tax surface and a potential room for exposure um so how can we defend against this the personal GitHub accounts some organizations out there believe it or not allow employees to commit off their personal accounts that definitely recommend against uh but even if you don't understanding what your employees personal accounts are and just scanning
them Audi having that in your threat model um for the organizational GitHub accounts another really common exposure we see is where the organization is scanned for Secrets but the individual accounts for that uh organizations's employees aren't and the uh employee inadvertently creates a uh public repo so think ben- Acme Corp and I expose um Secrets through a repo on that account rather than in my organization account the other thing I'd mention here is don't neglect uh scanning and looking at GitHub gists as a source of exposure uh for those of you who aren't familiar it's a uh way to quickly share text documents alipin but it's searchable and they're out there forever and we've definitely seen a lot of exposure there
and it's uh kind of slept on in terms of um considering where things can be comp rised I'm going to Pivot now to what we're seeing on the network security side as common wins and I would be remiss if I didn't start off with network poisoning and relaying think responder and uh llm andr um so real quick for um a high level Network poisoning is where I have a client on the network a user on the network they say hey I'm looking for or x file server which doesn't exist or was an old thing decommissioned or typo and I as the attacker stand up and say hey I'm x file server I'd love to give you all the
files I just need you to authenticate with me first and out of that in a high Lev from Windows Network I will get um the authentication in the form of a net ntlmv1 V2 hash uh that hash can't really do too much with I can try to crack it priority crack maybe I get a win there maybe not so the next thing I'm going to turn to is relaying going back to that example with the file server when the user says hey I'd like to authenticate with you I take that authentication session and I turn to a resource on the network I'd like to get access to so let's say the mail server I say hey I'm
going to take this authentication session and relay it over and say I'm ready to authenticate and just pass along the authentication that's relaying and uh for more there's a great blog post on it by bip leader and as you can see on the date it's uh 2017 so 7 years later and still very effective now how effective you're wondering in 85% of Enterprise Network penetration tests We performed over the past two years we gained access to privileged accounts using these poisoning and um uh relaying techniques so even still we've known about it for decades the idea of poisoning and still just as effective it ever as ever on Enterprise networks so what are some of
the initial mechanisms of Defense we might put in place to kind of help this out let's say we go in and disable uh net bios name service we disable llmnr which are two of the common protocols we poison and then let's say we take relaying off the table so we disable S smbv1 we uh enable be signing and then also take ldap reing off the table with ldap signing and channel binding as an attacker the first thing I'm going to do is I'm going to switch protocols that I'm poisoning so instead of going after uh net bios and LMR I'm going to go over to mdns ARP DHCP now with reing off the table we
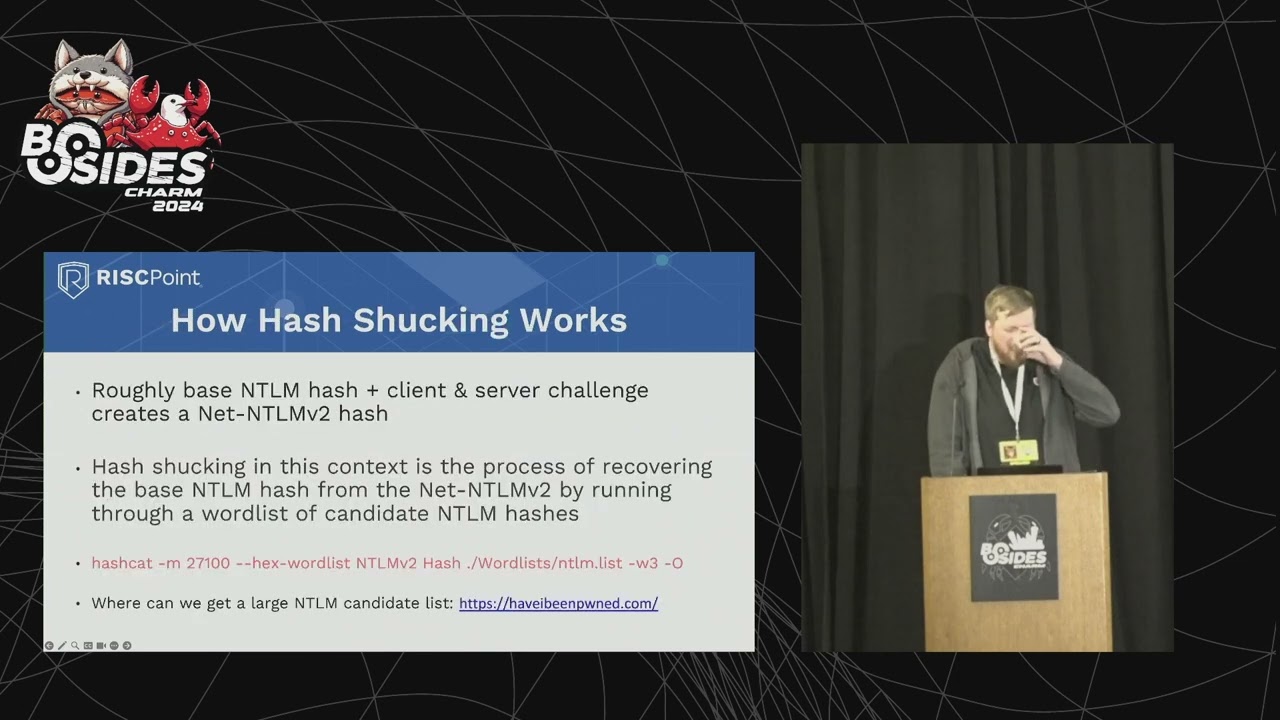
said that we don't get to go over to a new service we get that net antium hash that we can't authenticate with what we really want out of that is the entm hash that's something we can go and authenticate with services with through pass the has as good as the password so the next kind of attack I'm turning to is one that is slept on a little bit it's called a hash shucking or password shucking to describe this one we need to First understand what goes into a net ntlmv2 hash that's the type of hash I'm capturing from Poison at a very simplified level there's a little bit more that goes into it but roughly it's the base ntlm hash plus a
client and server Challenge and then that's hashed again to uh create the N Net nlm V2 hash the idea of hash shucking is I'm trying to recover that base nlm hash so I'm taking the net enm V2 hash I captured along with the client and server challenges and I'm trying to hold list of candidate and hashes slotting them in there seeing which one fits to create the net andm V2 hash if I do that successfully I've recovered the Anum hash that I can then go and use to authenticate with Services uh for a reference there's the kind of hash cat command to do this kind of attack um we've found great success with doing this recovering those entum hashes on
networks that have put in some of the safeguards and that's a way we're still getting wins even when we're starting to see some defenses go into uh poisoning and relaying one quick note um where do we get that giant list of candidate hashes uh and hashes it just happens that have I been poned uh the site that collects all the breach data puts out a huge list of all of their passwords in entm format so uh definitely a good resource there so what can we do in terms of Defense what defense mechanisms can we put out there well well like we mentioned we can disable L M&R net bias SMB signing um we can enable and disable S&B
V1 the L app signning as well uh we can block uh DHCP V6 and a router advertisement and Windows Firewall that is another kind of protocol we look to poison for wpad which is a common attack path uh disable it or if you're using it manually specify the path no Auto Discovery there and then kind of the gold standard is to take the nlm problem away entirely migrate away from ntlm to something like ceros so the next thing for Network I wanted to touch on another area we're getting um into your company through is through LSA Secrets now what are LSA Secrets um it's a place in Windows registry where Windows stores domain credentials service credentials Keys
website logins um to use and it's not uncommon on our test we found domain administ credentials stored in these uh Secrets why am I talking about LSA secrets I'm sure a lot of you probably heard MIM cats and Elsas memory tacking which is where I'm dumping the memory of the Elsas process and recovering um credentials in memory and really that comes down to with how prevalent uh MIM cats and and the LSS member taxs have been both through um pentesters and through threat actors themselves uh it's been an area that's really been monitored and started to be uh hardened by EDR EDR if you touch any kind of memory or try to dump the LCS process at
all in any way ered flags on it tries to block it immediately of course there's ways to bypass that there's Ed unhooking EDR bypasses but Els uh in our experience and we've seen a lot of big name Big Brand edrs It rarely if ever flags on this and uh blocks that attack path so I think there's certainly room for improvement in terms of the monitoring um for accessing these secrets so to that point what are some defensive measures we can look at so this is back to that good cyber hygiene stuff the regular password changes and complexity by rotating those passwords we're reducing the life span of those Secrets stored in the LSS so or in the
LSA memory so if uh teer gets them hopefully they've been expired by that point there's also um applying the least privileged principle so making sure that domain administrators are using regular accounts for their day-to-day and only using those um privileged accounts for specific Administration functions just reducing the spread and exposure of those accounts in general and then and then uh finally of course increased loging invisibility specifically relating to the LSA um Secret store so I know I went through just a whirlwind of and I'm sure there's a hundred kind of findings we could add to this but this was just in the past couple years the findings that we feel uh have been really prevalent despite
being known for years and years and years and we haven't seen much improvement in defending against them or slight tweaks make them still relevant so I know I'm uh keeping everyone from the uh happy hour so I'll end there but happy to take any questions either now or afterwards thank you so much for your [Applause] time yes
so I will be very candid I think in the hundreds of network engagement I've seen maybe one of them have had MFA enabled Network side on their Windows ad environment I think it certainly can be a very effective tool I have almost never seen it actually implemented great question any other questions awesome well thank you very much [Applause] [Music]





