Illuminating Malware Adversaries with MalBeacon
Show transcript [en]
so yeah my name is Paul Bridge today I'll be giving you a talk on illuminating malware adversaries with Mal beacon really excited to show and share with you today a passion project that I've been working on for over three years so let's go and dive in a little bit about myself on me malware researcher and as nice lady that introduced me mentioned currently work at cross track but this particular project is not affiliated with them this is a personal project that I've been working on myself you know for over three years so my passion in the field is looking at those Maur kits that have some type of lamp stack and finding vulnerabilities within them on my
drummer like music course and I was active duty marine 2004 to 2008 any devil dogs in here by chance yeah simplified brother yep good to go feel free to reach out to me on at hex slacks on the Twittersphere so we'll go over our agenda for today I'll discuss what uh what I foresee is a problem within the the Mauer ecosystem it's far too easy for people to go out and acquire malware kids and utilize that to breach organizations to understand how we're able to beacon Maur command and control I need to touch upon stored cross-site scripting just to kind of lay that foundation of how we're able to do it then I'll dive into the system itself so
how we're able to inject those beacon payloads into malware situ and then what that receiver looks like all the information that we're recording from the adversary as they log into that malware control panel touch upon the legality concerns utilizing this type of intelligence collection and then have some case studies to present to you finally wrap that up with some conclusion and QA so what is the problem it's far too easy for anyone to go out to the Internet and whether or not they're there purchasing these within you know cybercrime forms or finding them for free malware kits that leaked and they can utilize these to breach organizations and these in my opinion the current attribution for people that are
utilizing these to attack companies it's one-sided it's typically grouped by shared infrastructure you know shared domain registration details or shared IP addresses or similar tools techniques and procedures as well as malware code however with most commodity markets you know it's one author that's selling to you know several different individuals so to trace that back to an author is one piece of attribution but who's actually utilizing these kits to attack these companies so there needs to be better attribution you know in order to protect ourselves we need to understand the attacker and where they're coming from is it a target attack or are these attacks occurring you know across multiple industries and they're just trying to do like drive-by drive-by
download attacks or drive-by attacks to reach as many people as they can so one way that we can do this to get better attribution is to beacon the adversaries as they utilize their malware see - so I want to touch upon the sort cross-site scripting so story cross-site scripting in general is just whenever a web Apple web app vulnerability allows an attacker in this case us the researcher to execute script it's the most common vulnerability in web apps today I was talking to the the very code guys out there actually about some of the different abilities and they confirmed that you know cross-site scripting is still very prevalent and even more so in Mauer command-and-control right so these
these families these web applications they're not going to go hopefully through the rigorous testing that you know customers of ver code would be utilizing their stack for so this persistent or stored cross-site scripting occurs whenever that payload is persistent across this session so it's not reflective this is typically a payload that's stored inside the database but can also be stored on the the web server file within session information and so on then it's printed out or echo to the web application user in this case a malware actor who's logging in so you look at all the you know infected machines under their control so it's printed out and it's rendered and although it's possible within stored
cross-site scripting vulnerabilities to insert JavaScript with this particular system we're slowly doing benign image callbacks and I'll show you why that is when we touch upon the legality concerns I wanted to briefly cover what is am our command and control so most of these systems the ones that we're you know able to insert beacons in it's essentially just a web application most of the underground actors refer to these as panel most of them running on a lamp stack so your Linux Apache my sequel and PHP so all of the infected nodes communicate you can think of it as an API with the malware situ this is commonly referred to as the gate so all the infected nodes
they might check in or exfiltrate data from those infected machines and send that to the sea to the other interface allows the adversary to log in it's usually a nice GUI you know web front-end where they're able to log in see all of the infected machines under their control and issue commands or you know download exfiltrated information from those infected nodes one other so to give you kind of a higher level overview of what the system is doing here we're actually pretending to be an infected node so some of those artifacts that are submitted to a situ might be like the workstation name so we write it's code to mimic that infected node check-in protocol and we're able to
insert beacons inside of that protocol and then hopefully if the the Marcy 2 is vulnerable to that the actor then logs into the situ and it triggers an image callback whenever an adversary logs in they might be created with a screen like this so this is a an administrative interface for a form book malware form book one of the families that we are collecting fairly heavy on and I'll dive a little bit more into the case studies here in a little bit but as you can see further down towards the bottom there's a couple rows and these indicate two infected machines and again some of these fields like the OS version there or the bots I D to the left I might be
one of the fields that are susceptible to store cross-site scripting so we can insert our beacon payload into that and then as that actor logs in again it triggers that image callback and we get all of the information about them so I want to dive into this system itself how are we able to first insert the beacons into Marcy two and then the receiver so the the beacon injection method there's also there's also two methods how we're actually able to inject this particular beacon I kind of touched upon it earlier so we do a manual insertion where we pretend to be a bot to check into the situ and then we also have an automated
hooking function as well within our sandbox so if an some is anyone familiar with KooKoo sandbox yeah quite a few cool so yeah it's just heavily modified cuckoo for those not familiar cuckoos an open-source project you can download it for free on github allows you to execute malware samples within a virtualized environment it's pretty cool if you want to play with it and then finally there's the receiver part so this essentially is just an image request that's coming back and hitting our systems we're able to log all the information about the actual attacker you know utilizing these these and our families and wanted to go over the injector method or the manual injection so this actually
requires human researchers to analyze the c2 source code so we have to have a copy of that right we have to you know some of these leak or these kits are leaked out on the Internet we can grab a copy of the kit and take a look at that pH people have application find these vulnerabilities and then bright you know reverse engineer that check-in protocol and then create a fake bot to check in and leverage those particular vulnerabilities so the pros of using the manual injection it's very high precision right you get a nice callback rate as far as people if the c2 is still up you know by the time that you are able to inject that beacon nine
times out of ten you'll get a very nice beacon response from the actual person behind that particular on our campaign cons of this is that it's time consuming right so some our families we might find a family but if it's still under active development that author might change the check-in protocol then we kinda have to go back to the drawing board reverse engineer the the newer version of that and rewrite our fake bot to check in just to see if it's you know still vulnerable for collections so let's talk about the Automator I kind of touched on this earlier so it's just heavily modified KooKoo sandbox and the way that it works is that we're able to rewrite
the the monitor for the executable and the DLLs that get injected so monitor the behavior of malware samples as they're being ran within this virtualized environment so what we do is hook these windows API functions you know the malware sample is as soon as it fires it might say give me the machine name give me the user name of the Windows computer that I just infected so that would be like a Windows API call that username X so we hooked that function and on the return we taint the their response tit out with our beacon payload again that might be one of the artifacts that are submitted up to the situ and if it's vulnerable it would you
know pop and give us if telemetry on who's used in the actual situ there so the pros of this is that is highly scalable right we can scale out cuckoo to you know run not hundreds but thousands of samples discover new families in the wild that we might not have the source code to analyze for vulnerabilities and then from there you know we can take a look at the the ones that we're getting callbacks for and then fine tune and reverse-engineer that particular malware family to develop a little bit you know a better check-in protocol for the manual injection so kind of feeds itself right um the cons of this so that is quite noisy and the
reason why is noisy is that it's a best-case scenario that AM our family is not susceptible it's not vulnerable is that you know that initial gate or the the Maui check-in protocol it just drops that connection it says this is a bad input I'm not even gonna try to process it drop it goodbye worst-case scenario though is that information is still stored into the database but the particular field is not vulnerable to cross-site scripting attacks so now we have a you know a URL are benign image callback that's not properly rendered as HTML so they can they can see those domains our infrastructure that were utilizing for call back so obviously a bit of an
offset concerned there then again so as that malware situ you know person who's conducting these campaigns as they log in to look at all the infected machines they are going to trigger these image requests back to our systems and what we stood up is just a you know an image another web application to record those image requests when I first started looking at this I was amazed at how much information you can get just from an image request I really opened my eyes up to the amount of information that advertisers have on each and every one of us so what the receiver is is just an Apache with some HD access hacks so image request comes
in redirect that gift to a PHP script and now I'm able to you know do some stuff programmatically as far as all that information is concerned pulling out the source IP address which of course can be geo locate located in the event that it's you know a true IP address questions that I receive in the past our actors are utilizing VPNs the answer is yes but just knowing you know what VPN provider your attacker is utilizing I think that's a pretty unique intelligence aspect in a know it selves what are some of the other fields the HTTP referer field is probably one of the most interesting so the refer field this is going to be the actual c2
address of the malware campaign or where the the malware actor is currently logged into so that's this always pretty cool to see and we get the the complete like get parameter that they're utilizing as they're browsing around on the malware c2 for some of the manual injection methods I'm able to submit a unique ID parameter so this is really interesting especially malware families where you might have multiple proxies in between the infected nodes and the c2 so receiving a UID response and that initial gate URL is different than the UID response HTTP referer that indicates that this is a completely different back-end infrastructure that the bad guys are utilizing stuff that you wouldn't see from typical you know
running malware samples just in a sandbox to retrieve those indicators are compromised and some of the crappy there's like browser add-ons that some people you know place that or they utilize like free HTTP or HTTPS proxy list some of those proxies actually leak the true IP address of the individual so they might think that they're utilizing these free proxy's to OB skate their their true origin but within that proxy requests they include headers of that true IP address so if we see that we obviously log that particular IP and then the user agent of course the all of these client headers can be forged but if the user agent is true that tells us quite a bit
of information about our adversary everything from the architecture that they're utilizing you know x86 64 whether or not they're coming from a mobile device the operating system in use and their preference and web browser so the script just you know records all this saves it to a database for later review and then we send back a 1x1 pixel image why do we do this because the as long as that cross-site scripting field is rendered properly we just want to send back a 1x1 pixel image hopefully to not mess up any of the HTML formatting as that actors you know looking through their their c2 web application so hopefully the actors none that there's a know a tiny 1x1 pixel being rendered
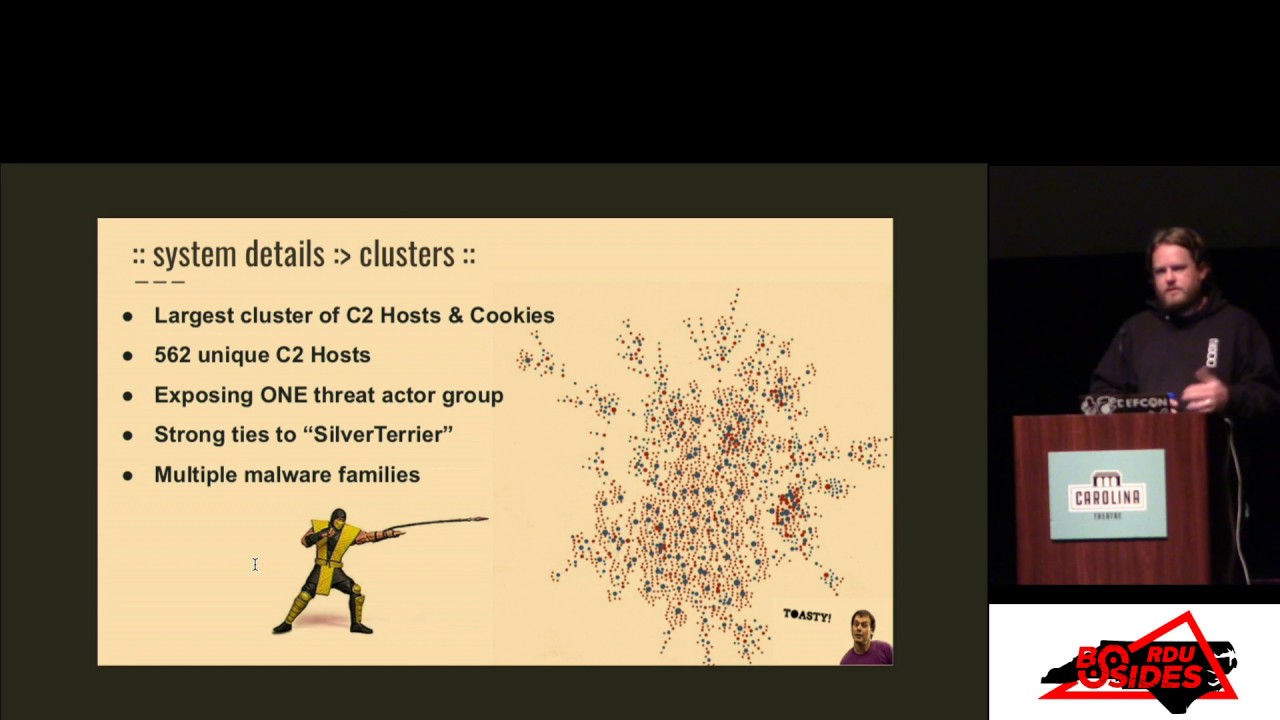
they're on their c2 and then probably one of the coolest art effects that implemented earlier this year I was discussing with some some researchers in the field and they're like Paul why aren't you placing a persistent cookie in the reply to that image requests and that's exactly what I implemented and I'm seeing some really nice clustering from this data so again going back to you know how we're starting to the the old ways of attributing had this malware sample it communicates with this domain and I found this other domain that was registered with the same email yeah that might be an indication of the same threat actor group but now we're able to track these browser sessions as they log
in to new C twos so they can change the domain we can track that the movement of that we can start clustering you know C twos together to form like this this picture here this this data was actually just generated last week so what I did was map the c2 host and the persistent cookies and what this indicates is that 562 unique domains or IP addresses can be attributed to one threat actor hearth and you know previously looking at this you wouldn't be able to draw those conclusions it would just look like a bunch of commodity malware that's hitting you know organizations networks and we've actually been able to tribute to a lot of this activity to silver
Terrier say unifor T to publish publishes a report usually about once a year most of these guys doing business email compromise but also dabbling and Loki bot malware form book malware but yeah it was pretty cool to draw that to that one threat actor group mainly operating out of Western African nations like Nigeria and Cameroon so let's discuss the legality of utilizing this type of collections apparatus so I actually went several rounds with the EF f the Electronic Frontier Foundation and I wanted to get their opinion know what's how far can I get away with you know doing this and they said as far as as long as they're not doing code execution which in this case would be
JavaScript you're good to go which is kind of it was kind of a letdown because in the event that we were doing JavaScript we could do some pretty cool things like I don't know request access to the the adversaries web cam take a picture of it there's a company just off the top my head called session can that records video of what's occurring inside the web app so we could take like you know an mp4 of everything that they're doing inside the the Mauer c2 but again that unfortunately utilizes JavaScript and it's a little bit out of balance for staying legal so I wanted to keep this system you know legal that way I could talk to you all
about it here today so it's no no worse than advertisements I bet each and every one of us if we pulled up our phone and take a look at know the raw source of the you know emails on the phone you'll find these you know benign image callbacks does tell the advertisement companies whether or not or tracking companies that you opened that email no worse than that there's no authentication bypass again an event that we were doing JavaScript we would be able to grab those authenticated cookies and then you know utilize that to of the Nicator against the other c2 but since we're not doing javascript we're not able to grab those cookies that wouldn't recommend that so and it
is privacy respectful so again these are beacons that are solely submitted through a bot check-in protocol and the only way for them to be tripped is if you're the adversary that's logging into these malware c2s you wouldn't be you know tripping these beacons just by ordering blowup dolls on amazon good to go so let's dive into some case studies here I believe blue live called this group air nine and maybe Talos or maybe even at 42 actually calls them ta five four five again I've been collecting this data for over three years back in January of 2018 some groups of knuckleheads were utilizing an online or spam bot to send email attached with Canada Post dot zip the zip cars VBS
loader which is actually a commodity malware family that was sold and Russian underground forums pedro dried is that uh the c to login for that so it's just a VBS that when that victim clicked on it it reached out to this c2 and asked you know what additional now or would you like me to download and execute and the the underground vernacular actors call this a loader right so this particular campaign it was loading Canadian banking Trojans did you know Canadian financial institutions users as well as deploying zero evil stealer the same author actually zero evil the same author behind hearts VBS loader um so receive some pretty interesting callbacks on this one from a dedicated
server and hosted in the UK by by friendly nation right so I reached out to see the Canadian search folks they were pretty interested in getting that piece of intelligence taking a look at the IP address at the time across shodhan indicated that it was a Windows 10 box and the same thing with the user agent there as far as the callback so that was pretty good attribution for this particular case so they were actually utilizing this dedicated host in UK as a bounced box to conduct their Maori campaigns second case study back in September of 2018 this is actually ongoing threat I see it probably at least two or three times a month where guys will go out they'll
though bad guys will go out they'll take a look at popular crypto coin wallet software they'll copy that website stand up a fake one and by tricking users via yeah like SEO or advertising that link in like crypto forms they'll trick people to visiting these web sites to grab the new you know addition of this software in this particular case it was downloading k-pot info stealer k-pot is actually info sealer sold in Russian underground forms k-pot actually pronounced Krotz in Russian means mole this particular campaign tracing back to a VPS provider in Russia so this not only works with commodity Maur the system has also recorded advanced persistent threat groups a PC activity back in January of this year
a piece of mole-rats Bauer came across my desk and these this was one of the families that you know we obviously didn't have the c2 source code for but I tossed them our sample into the hooked sandbox the modified sandbox and received some pretty nice attribution callbacks from this particular campaign IP address tracing back to Gaza cyber gang I'm sorry Geo traced back to you the Gaza Strip and of course well mole-rats has been attributed to the Gaza cyber gang one pretty cool artifact in in this particular campaigns that in order to render the back end situ panel there down at the bottom you had to set that particular user agent of twos so I
thought that was a pretty unique screen and sure enough searching that string across social media profiles may or may not have found a couple people attributed to this particular cyber game just wanted to briefly touch upon the current statistics over three years unique IP addresses that I've collected over 28,000 beacons received so this is each like page refresh that's sending an image request over 355,000 yes that's were pulled up yesterday morning and I've identified over 32,000 c2s wanted to give a shout out here to this the slick front-end graphics that you see is one of my good friends Chris quark who programmed that so he'll probably watch this later can everyone say thanks Cort awesome thanks he'll get a kick out of
that appreciate it so in conclusion some of the my future work that I want to take a look at is you know really scaling out that automated sandbox a cuckoo itself supports like a distributed mode so I'm looking to you know get past the you know just doing like hundreds of samples today and take that up to thousands run several samples through see what kind of callbacks we get and then we can go back and reverse engineer those particular check-in protocols and fine-tune the other beacon responses for that the clustering of beacons so if anyone in here has a like a data science background I really like to understand how we could you know applying some
machine learning models start clustering these thread actor groups into you know ash of all intelligence to hand off not only to Ellie but also you know cyber threat Intel teams so on so that being said I'm currently working on an API as well as like a Miss fee so if you're into threat intelligence the the front-end the website snippet that I showed you earlier you can request access to it right now is just you can log in and search for the data but eventually we'll have a like a malware submission where you can upload samples and we'll attempt to run it in our malware sandbox so you can hopefully try to get beacons back on
that so the short URL there it doesn't go to a rick roll or anything you can hit up that short URL to a Google Form just request some information to verify who you are or where you might work just to know verify I'm not giving access to any bad guys so so that's about it thanks for having [Applause] got through that pretty quick did anyone have any questions or concerns
yeah I would like to so the question was have I considered any other type of beacons beyond image callbacks yeah that was one thing that I was hoping to do with JavaScript so with with JavaScript especially utilizing like web RTC so web RTC is notoriously known to sometimes circumvent VPNs so by issuing a web RTC request from the victim's machine if they have a pretty crappy VPN provider they don't filter those properly and you can get a true IP address back from that but unfortunately again that's that's utilizing JavaScript so it's kind of how to bounce yes sir
I'm sorry could you repeat that
oh that's interesting yeah so the question was has I have I considered utilizing long domain names to see if there is any dns leakage yeah that's a really cool idea the only use well that could work for some of the manual injection methods with the automated version you have to have a very small payload right because the Windows kernel will crop out like if you do a payload longer than the Windows user name field which is like 20 to 25 characters or something like that it's a very small payload but I do see how that could be very beneficial for manual insertion two techniques that's cool one other thing that I'm kind of playing with is no show of hands anyone
familiar with jaw 3 buddy so Joffrey it's it's an open source project I think published by Salesforce what ja3 does is it attempts to fingerprint the web client and the way that it does this each web client is built with you know an SSL library and the way the the connection occurs the particular order in which these crypto libraries are compiled can be fingerprinted so Joffrey is able to fingerprint like the difference between chrome SSL connection compared to you know other browsers so I'm looking to implement that but that's more on like the network layer side but there's also like other oh s or TCP fingerprinting that I could implement I'm so taking a look at that
Network stack as well I think it'd be pretty pretty beneficial any other questions good to go all right thanks for your time [Applause]