The Rise of Ransomware: A Look at CryptoWall, TeslaCrypt and Locky

Show transcript [en]
goodmornin hackers well today I'm going to be talking about the rise of ransomware a little bit about myself i am a malware researcher at fish me and one of my passions dealing with malware is taking a look those malware families that utilize PHP panels and finding you know vulnerabilities within that particular malware command and control some of my hobbies include playing the drums and listening to music and as you mentioned every now and then I'll tweet out things from at heck slacks so feel free to hit me up on there or my work email let's go over our agenda for today so we'll talk about what is ransomware some common practices regardless of the family and we'll also dive into three
particular families you may have heard about these in the news recently being crypto wall tesla crypt and locky will also talk about some mitigation steps and i'll not only that the end user or residential user can implement but also what you can do within your organization and finally also have a video demo of a live infection that i record it for you first a little disclaimer though anytime that you play with malware make sure you're doing it in a properly segmented lab don't be the one that you know infects your organization and this presentation may contain links so if you have your laptop your mobile phone and the audience please don't visit those that wouldn't be good for you all right
so what is ransomware rain somewhere is the type of malware that restricts access to the infected computer system in way in some way most notably usually through some type of file encryption process and the way that what the malware actors are monetizing that is that they will restrict that access back to a file usually with some type of digital currency that the victim has to pay usually in Bitcoin so show of hands who here has been ravaged by ransomware either their home computers or the organization I know Lance admitting that he got popped earlier yeah yeah hey you know somebody usually uh I gave this talk not so long ago in Birmingham and quite a few hands went up
over there and I was like okay well leave your hand in the air if you paid the ransom and everyone's like yeah kind of not really wanting to admit it but unfortunately I mean there's really no other way to get those files back I mean it's very strong cryptography and encryption that they're utilizing to hold those files to ransom you may have heard about these events recently in the news Hollywood Presbyterian Medical Center februari of 2016 paid a ransom of 40 bitcoins roughly at the time seventeen thousand dollars us so you can read about that incident they actually released a memo on the website it's pretty interesting and Methodist Hospital hint in Henderson Kentucky March of 2016 they declared an internal
state of emergency due to a locky infection screenshot of their website with that huge regiment red banner at the top saying that you know we've got popped by ransomware this was brought to light by Krebs Brian Krebs his website Krebs on security and like I mentioned earlier you know organizations they might have no choice but to pay that ransom especially if its credit business critical files that have been encrypted some common practices regardless of the ransomware family on encrypt files with very strong asymmetric crypto so even if you had all of the computing resources within the world it will still take you hundreds if not thousands of years to break this type of cryptography most of
these families that I'll go over they utilize on The Onion Router or tour for command and control relaying victim instructions and also the backend databases that handle payment verification deletes shadow copies and windows snapshots so as you can imagine you want to prohibit the user from rolling back from previous file snapshots so they usually just delete those out what we have also seen too is that some of the lesser known variants that are just now coming into the wall they might masquerade or pretend to be a more well-known crypto wolf are crypto ransomware family mainly to entice a user that you know in the event that they pay that they will get their files back most of these are
installed via exploit kits be it drive-by download attacks or massive spam campaigns and one other thing that we've seen is that most of these families they private are privatized network shares / local drives right so as you can imagine within an organization some of these malware families they're wanting to encrypt those files located on network shares prior to worrying about files on local drives main reason being you know that's obviously going to affect more people and that organization is probably more willing to pay that ransom to get those files back and as mentioned early to a digital currency usually Bitcoin so let's explore three of the notorious families in the news first one being crypto wall so the latest version of
this was version 4.0 first seen in November 2015 and although recently you know in the media they kind of portray this as being a very new threat but crypto wall obviously has been around for a while so it's definitely not a new issue when it comes to ransomware the way that this infects the system is processed by process Halloween or DLL injection usually into Explorer svchost.exe and also has a reboot persistence via registry run key encrypts the file names and files with a very strong RSA 2048 key deletes the shadow copies as most of them do and there was some actor attribution behind this particular family the author of a hymen exploit kit was doxxed and what
they noticed is that the the development of hymen dropped as soon as crypto wall came out so the idea being that this particular author stopped doing exploit kit development and then went on to ransomware first seen as cryptolocker clone in November 2013 and the actors actually abandoned the back end so right now although there might be some variants that are still being spread in the while of crypto wall the back end panel or the database that handles you know monetary transactions to verify ransom payments completely down so it's no longer really a threat but as we've seen with previous crime where families you know especially Sue's that the source code leak of that has spawned
several variants so we're definitely keeping our ear to the ground to see if that's the case as law enforcement is closing in on this guy because of the the daxing of the the particular author
here's a little snapshot here of the version history and this was taken from Krypto wall tracker org was very good website if you want to learn more about crypto wall has quite a few things about the family and attribution as well first started in November 20 2013 as i said as cryptolocker clone renamed itself crypto defense and then in March of 2014 we have crypto wolverton for I'm sorry crypto wall version one started one of the pretty funny things that you can take a look at as far as attributions concerned is to see which countries are excluded from execution for these particular families and as you can see here the map you know mostly the Russian
kind of gives way to the attribution of this particular family
here's a little snapshot of a typical campaign overview including the infrastructure hitting crypto wall so usually a je s downloader is included in a zip archive that's attached to an email and I'll go more into the JavaScript downloaders here in a minute that's massively spammed out and poor granny clicks on that and infects your computer that's then communicating with PHP proxy which is usually just one flat PHP file hosted on a compromised website which then again creates like a curl wrapper for any post information that's in fords that back to another proxy server usually provokes your engine X and then that gets forwarded back to the tor hidden web service here's an actual example of a email lure that dropped
crypto ball so information regarding your order and promotional offer can be found in the attachment below again with a zip archive attachment zip archive contains a dot jas file which when double clicked on windows execute just like a dot exe so this is actually obvious gated JavaScript that's executed by window scripting hosts and it's usually a heavily obvious skated this downloaded then reaches out usually to another compromise site or a engine X proxy that hosts the second stage payload and once that executes it does a series of check-ins over HTTP POST so pictured right set the actual PHP backend source code for this particular file and as you can see on line two they just statically hard code the IP address
of that third tier engine X proxy that would then communicate to the tor hidden web service back end on the cool thing though since this is over HTTP being a plaintext protocol there are some really good secure ekada hits or signatures that emerging threat even in there at the free version ET Trojan crypto while checking as you can see the screen shot down at the bottom there in a squeal GUI and this is what our poor grandma sees on her desktop so not only is it pop up a image file PNG within the windows photo viewer of the instructions on how she can you know get her files decrypted but also usually drops a HTML file which is rendered in
the background there in the default browser the same instructions so as I mentioned earlier yonathan here tweeted out March 28th that he noticed the back end monitoring yonathan being the actual curator of crypto well track org so you'd been monitoring this particular crew for a while and noticed that the the back end completely went down as you can see down at the bottom graph from ransomware abuse eh they track several crypto ransomware families it's a really cool website to get a little bit better idea of how far spread this particular threat is so definitely check them out and it's a you know in sharp decline there was probably one blimp there at april twenty seventh but if i had to
guess i was probably just some researcher that was messing around any uh any questions so far encrypt the wall yeah
yeah yeah that's the case but um as far as I understand this particular family it does do a check-in prior to encrypting so in the event that you know this is still being spread by some automated spam campaign that was set up way back yeah well yeah at least it won't be you know infecting your computer or encrypting the files at least good question yeah okay I like those yeah that's a good question yeah yeah I mean there the problem is is that they're utilizing encryption that you know is mathematically sound and what i'll i'll go over and one of the families there are some vaccinations or even some bugs with in the implementation of that so it's not
usually that the the encryptions flaw that you know someone can break the encryption because that's not the case it's that how that was implemented right so what we'll see with locking I'll talk about this here in a minute there was a trick to you could populate a particular registry key with a public key on that to which you already have the private key for so than the event that you were infected with walkie you already have that private key pair and could decrypt your files so there's usually bugs or vaccinations that's due to the implementation but not necessarily you know a flaw or zero day within the equip shin itself I'm moving on to Tesla crib so the
current version right now is actually 4.2 and this was released or seen in the wild just as recently as April twenty-eighth encrypt files with very strong RSA key of 4096 and yeah we kind of touched on this earlier so version 3 had a bug within its implementation that allowed you to decrypt the files that was published by Talos which Talos Intel I think they were bought out by Cisco recently and so you're able to get your files back but you know sure enough not even like a month after that these guys went ahead and patched it went with their release of version four point oh so that decoder to tool no longer works persistence again for reboots via
registry ronke and this has been seen dispersed in the wild via the angler exploit kit and of course your massive mouth spam campaigns but this family was also first seen in march of 2015 so this has been around for a while as well here's a snapshot of the the version history so again starting in march 2 2015 is when we fought first scene version 1 of tesla crypt and version 2 kicking off in november 2015 and then from there it looks like they're pivoting to almost like a bi-monthly release cycle like even scheduled on those so although you have minor versions that release the past couple weeks we'll probably see version 5 here in the next couple weeks so yeah yeah it
could be the case yeah yeah I could definitely be the case I'm not really sure why that sped the development up I guess yeah as more people or buying their their kit because this is like a ransomware as a service that they're able to spend more resources on development yeah yeah usually and I like to think of it as mimicking the actual software companies so you have your team's for development you have a team for distribution marketing sales and support so yes yeah well so the going theory is if you're a malware author and presiding in those countries that that you you know better than to attack your motherland that foreign you know attacks is a little bit not as watched as
closely I guess compared to you know if you're trying to attack the country that you reside in so that's a good question yeah
yeah they do utilize arm the question was was you know I guess from like a host detection standpoint in the event that you saw this encryption routine that's being performed why can't you block that but yeah most of these are utilizing you know the windows api type of keys from what I believe and that's how they encrypt the files as far as AV detecting it I mean there's from these fresh campaigns that I see every day there's usually zero detection at least running it through like segments a static signature on a virus total so very low detection as far as AV is concerned yeah yeah yeah yeah absolutely on they don't offer it right now but uh
I've heard of a couple researchers Tesla Krypton some of the earlier versions had a support number that you could call to get assistance with purchasing Bitcoin and there's some pretty phone calls that have been recorded for that trying to a social engineer a little bit more information out of these guys but they're probably just a call center that these guys hired I doubt they had you know any direct monetary ties with the actual actors yeah
yeah absolutely so an exploit kit is it's a custom piece of software ran by a malicious actor that in the event through normal user browsing exploit vulnerabilities within a browser session from there the idea is that you know once you have code execution they're dropping the malware and running that so it's just used as a as a means the distribution another question good so still very prevalent um even though the past couple weeks we've seen a little bit of a decline with Tessa crept and I think that might be attributed some of the same forms where this particular variant is being marketed has also been marketed for surber which is a fairly new ransomware just started playing with
it the past couple weeks so I think some of the actors that were playing with Tessa crypt if maybe have moved on to server right now and so definitely start paying more attention to that family as well it's still very prevalent taking a look at the typical campaign overview including the infrastructure so less intimate in mini airy notes for this family you know the the JavaScript attachment attached to an email on a massive mal spam campaign granny gets that email clicks on the attachment execute the second stage downloader and that then interns communicates with a PHP proxy again another compromised website usually a hacked WordPress or some other type of CMS that then Ford's that information to back-end again
another tor hidden web service here's another live example from our sample set this one attempting to lure the user to believe in that it was unsuccessful western union transfer so you you received a money transfer for the amount of you know however much US dollars via western union and a warning letter zip attachment so that zip archive of course again has a jay s and by the way i mean although j/s seems to be a popular choice for some of these campaigns at the moment we've also seen malicious office documents that have you know macros enabled so if that user clicks allow macro then it's going to fire off and grab that second stage executable as
well yeah question
yeah my guess is on since that sounds like it was more of a web-based infection that was probably coming from an exploit kit which that would be my guess but yeah the way that the exploit kits work and we kind of touched on this earlier is that in the event that a user is browsing the web site might be silently redirected to it to an exploit kit and if it has if the users operating system or 3rd party plugins like flash and one honor are not updated then it exploits a vulnerability that will then drop you know whatever type of malware that that exploit kit user has set up to be dropped ok so again yeah heavily
obvious gated JavaScript for the second stage downloader that then downloads it and you can see in the headers that for the return in the stream believe this one's actually engine X yes and Gen X proxy that was hosting second stage payloads as far as restrictions in place where oh yeah as far as like maybe geo restrictions or yeah some of the the PHP files that handle the the second stage download they might check user agent strings or I've seen geolocation as well they'll also place like it I've seen HT access files with long list of IP subnets that might block known security vendors or you know virustotal actually I just looked at a one of those the
other day and within the PHP code it was looking for the user agent of virustotal so apparently anytime that a virus total is attempting to grab a second stage that it has like it's google cloud user agent and i have seen that blocked in some of these so again it this family as well it checks in with HTTP POST to a compromise website that's hosting this PHP file source code pictured right the cool thing about this one though is that actually forged it back to the tour back end usually through some type of Tour de web gateway as you can see on line 15 in that source code is the tor hidden gateway addresses there and since we're
over HTTP again very strong suricata hits provided to us by emerging threat ET Trojan alpha crypt Tesla crypt ransomware CNC beacon and beacon response and this is what our poor granny sees on her desktop PNG file pops up foot and photo viewer with the instructions on how to decrypt and pay the ransom and of course the HTML file displaying a default browser any questions so far on Tesla [ __ ] yeah that seems to be the yeah the question was do they always use tor prior to encryption or the callbacks most of the families do but actually with surber even if you do not have a network connection it will go ahead and kurp your files so that's one difference
but yeah most of these families they'll attempt to do their check in first to get kind of instructions I guess from the OC two and then they'll start encrypting but what I've seen with server that's not the case yeah yeah
most of those arm so in Prior versions to some of these families that was an issue that the executable or the ransomware loader also had a private queue which may have existed in memory at some point so you could you know snapshot and hopefully get that key out of memory to decrypt in the event that your organization was pumped but what we're seeing now is that these miscreants / campaign are solely using private key and that's not being forwarded out to the clients at all so that the same public he might be in use for the entire campaign but that private key never touches the box that it's infecting it's it's only residing back end on you know their their back-end
services I see oh I see that huh that's a good form right yeah I mean there's definitely means of as long as you can do like a memory dump and extract keys from that method yeah mainly using volatility for that kind of stuff yeah yep yeah some of the the initial families they weren't utilizing the the tour to web gateways so you would have to there were instructions within the the ransomware decryption that you have to go out and download the you know tor browser to be able to actually get to the payment information or the payment portal but most of these families now they're they're going to just drop the instructions and the the victim user
would not have to utilize tour themselves that's just a method that they're utilizing to hide their back-end infrastructure yeah
yeah um someone else you know within the the AV sec could probably answer that better all I know is that a bee's dead at least from my viewpoint like even trip wire or any of those types of file system change detection utilities are going to tell you that it's happening but you're going to find it faster but you're still owes there is it unless you then you still have to recover whatever you didn't stop so what's Ailin well that is a problem some of them have to hibernate like some of the latest ones the mac ransomware yeah they're getting very tricky but yeah it wasn't in India back-end infrastructures across Greece yeah absolutely on so the question was
was the back-end infrastructure increasing as the amount of samples since most of these families are actually like a ransomware as a service we have um it's not necessarily that the malicious actor that's setting up these campaigns they're standing up their own infrastructure that's provided to them by the people that are selling the ransomware as a service but we have seen you know more middle notes or like burner nodes some of those like engine X proxy so instead of like hard coding three or four IP addresses they might do five or six just to have a little bit more of a nodes that they can burn yeah I think so yeah I haven't seen in an AWS
yet but I'm waiting for it yeah yeah
yeah as far as on the actual executable itself or where what would the scope of the are will be against yeah
yeah that's true um especially with the actual executable itself even from you know second stage payload that might be coming back if you're running you're against that those are heavily packed so and that's the reason why AV detections failing is due to packed executable code so yeah it's really hard to to see that so not only is that you know every two weeks they're they're patching bugs within the actual ransomware malware itself but the the Packers at they utilize I can see within the same campaign they might have 20 distinct hashes of an executable that they utilize and that would be a relatively small campaign yeah without executing it that's really tough mainly because of
the the issue with packing if so like a zit in user though um yeah right
yeah absolutely so that's actually one thing that my company works on not to do any type of plugging or anything but what so our analysts what they do is they take a look at you know what are some of the massive mouth spam campaigns per day and they'll they'll pull down the malware analyze that and we really set as threat indicators that you may have seen in some of the email slides it'll say you know threat ID number so idea being you know after a while we've detected enough signatures that we can pinpoint alright well this particular email has this indicator in it and we know that this has been a crypto wall dropper or a Tesla [ __ ] drop or campaign
in the past so we can you know create signatures around that that way you just solely looking at the email and some of the are signatures or signatures that are written for that particular campaign you already know that that's what the the first stage or the second stage payload could be does that make sense yeah absolutely on so virustotal of most um most reverse engineers to that at least the ones that I work with we're constantly commenting on virustotal so if if you have a secure means of checking the hash of that malware sample you might not be able to trap trust the initial j s droppers that are included in the attachments just because they
switch up so often there's so many per campaign but that second stage payload hash doesn't change up as as often / campaign so if you can get a hold of that get a hash and look that up on virustotal most researchers they've been pretty good about commenting on virustotal as far as what type of malware family that could be good question
moving on to LA key and lock is also spread via massive mouth spam campaigns with either doc mock macros office stock macros or JavaScript downloaders it's also being seen dropped as the final payload for neutrino and angler exploit kids again reboot persistence for your registry run key and some of the earlier versions that were pushed out with locky they actually placed some tracking information within the registry at HK current user software / locky so it was very easy to see that key in there and I'll talk about that here in a minute some of the mitigation steps that their team then you know pushed out as far as changes delete shadow file copies of course encrypts data with a very strong
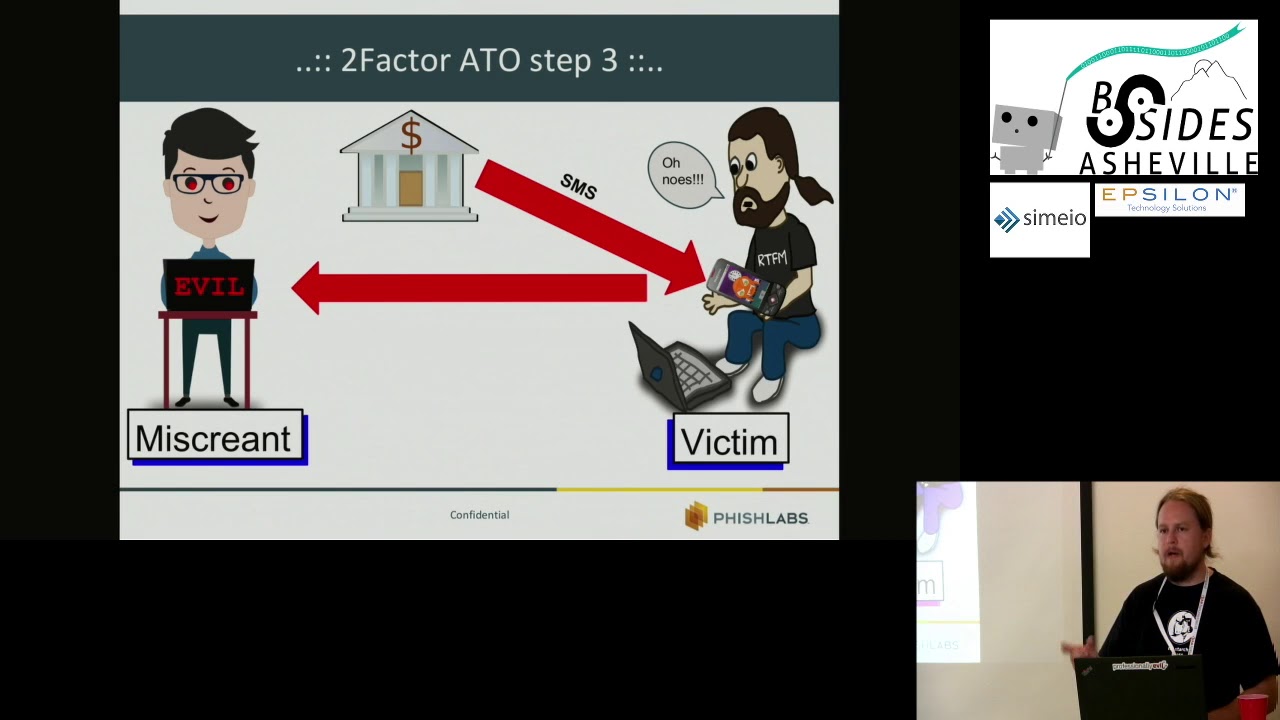
aes-128 and first appeared on the scene da mid-february of 2016 so show of hands not who's here who here is familiar with dried X banking Trojan quite a few people okay for those not in the know dried x is a man in the browser banking Trojan what that means is that as a user's computer is infected with dried x any sum that they're visiting a website that's included in the droid x configuration file javascript is going to be immediately injected into that browser session to you know usually to retrieve credentials one cool capability is that this actually started with Zeus banking trojan is a VNC connect back capability so as financial institutions they start to you know do more like
fraud detection and they notice that you know grandma Jo initiated an account transfer from Ohio but then you know not even an hour later a much larger transaction occurred from Ukraine so that's always going to set off fraud alerts so the way that the miscreants are combating that is to utilize a VNC connect back to that infected grandma joe's machine and initiating those account transfers directly from her computer it's a little bit harder to detect as far as you know fraud detection within the FI so pretty cool piece the reason why I mentioned dried X here is because there's been a very strong connection between dried x botnet 220 and lucky affiliate ID is one and three so we're
seeing some of the same distribution methods utilized for those families and there's also been some researchers that have monitored dried x baking charging for long term deployments and what they've noticed is that the running theory well is that you know since these research computers are not really being utilized for banking and they're not you know the miscreants aren't gaining any type of credentials from that so instead of just moving on from that infected endpoint one last-ditch effort to monetize that infection is to drop locky so people have been seeing that in long-term dried X infections here's a very small snapshot of about 3,000 unique source IP addresses so these are IP addresses that downloaded the second
stage payload second stage in this particular campaign being the after the victim clicks the the java script executable it then reaches out to a second stage payload which grabs the the locking loader so source IP addresses that were downloading this this particular campaign so taking a look at that map as you can see it's pretty geographically dispersed except for one country anyone take a guess Russia right yeah I mean there's like there's there's one red blip there and that if I had to take a guess i was probably some researcher that was downloaded in second stage through some type of like VPN solution so pretty much the same actor attribution as most of these coming out
of Russia here's a an example of a live email lure that we seen in the wild this one again being a you know some type of invoice lure please review the attached copy of your invoice in Eric Hauck air cargo copy within the zip attachment and of course has a javascript downloader heavily obvious gated and again is ran just like dot exe when a user double clicks on it the window scripting host reaches out and grabs the second stage payload for locking most of the distributions especially for affiliate ID 1 and 3 2nd stage payloads are being hosted on compromised websites for each campaign we usually see anywhere from about 10 to 20 compromised websites and these are burnt every day
so new compromised websites are being utilized for each campaign usually about 10 to 20 URLs for that so that's downloaded and executed and a little bit different a setup for locky so there's actually there's usually three or four hard coded IP addresses within this loader that I think it builds a URL around that some of the earlier versions it was posted in a URL to main PHP then that was changed up to submit and then most recently as of like a couple weeks ago they switched to user info PHP so again since we're over plain sex protocol very strong signatures from emerging threat that you can get for that trojan ransom we're at lucky CNC
beacon oh and also one other thing I failed to mention here in the slide deck is that although there's you know three or four hard coded IP addresses lock key also has a fallback domain generation algorithm or DGA and that seed value changes up weekly so unfortunately I mean as a researcher you might be able to predict a couple days out what the the DGA domains might be they then change that seed value the next week in a different campaign so very hard to predict those from you know longest long-term sinkhole een and poor granny Jo this is what she's getting on her desktop now so not only is it pop up the image instructions in photo viewer but
also sets the desktop background as those instructions as well just to make sure you don't miss him I guess all right so kind of touched on this earlier with a nice lady's question about prevention or you know vaccinations and just like any other type of software system you know the lack of proper programming and lack of quality assurance leads to bugs so there was a registry lock of again ACL that she could to implement so by setting a particular registry key I kind of I mentioned earlier it was that HKC you software locky so if you set like a read-only a tribute as an admin when locky initially execute it attempts to read that and due to improper exception
handling would just crap out and would not infect your system so one of one of my fellow co-workers initially found this bug and then like two weeks later a Lexi consulting firm publicly blogged about it and of course like within the matter of three days we saw that that was patched meeting along the wall wild so pretty interesting to see that you know these guys are performing Oh sent on their you know their their malware and in the event that you know there's some type of public information that's published they are obviously reading that in reacting very quickly in the development lifecycle of that malware so pretty interesting to see that in the world so one other method that you can
use to not get infected by lackey is just go ahead and setting your operating system language to russian i don't i don't know how usable it would be then but that is one method and there was also that same rich street key too although that has been patched around march 29th with the other registry lock crash and the setting a completed registry key that particular registry key is still based on the the computer name so it's still it can still be computed so that the same patch exists just not at the the easier statically coded registry key it's a unique per machine and as I mentioned earlier sue Lexie published how you might be able to populate that RSA
public key already on a machine so in the event that you are infected with locky the idea being that you you have a key pair for that public key that you can go ahead and decrypt your files so one other method of vaccinating yourself yeah that's a good question so the question was how would what dis applied to anything got saved in the cloud and yeah um so I'm not sure if depends how it's mapped I know one of my one of my fellow co-workers he was given a live infection demo and his the way that he transferred malware samples into his vm was through a network share so lucky was intuitive enough to scanned other
network shares and found that his dropbox was mapped to his local machine and then started encrypting our companies a drop box but but uh yeah it was pretty funny we give him [ __ ] for a while for about that but um he the cool thing about cloud storage is that they're you know they they have very good backups so it was very easily it was just like one phone call and they reverted everything back prior to encrypting those files that's a good question all right we talked a little bit about mitigation and we've already kind of touched a bit on this keep your environment patch first and foremost so not only you know keeping Internet
Explorer up to date your OS level win updates but also all of your 3rd party plugins to prevent you know third-party drive-by attacks with exploit kits so all of your Adobe Flash is java PDF pretty much anything that's web based on your machine one other thing that you can do is block executable scripts on gateways I have no idea why dot jas files within a zip archive are allowed through email gateways I cannot think of any business reason why that would be legit yeah why y dot zips at all yeah is that how you deploy code idea so even yeah even if your developers come back and say well that's how we you know patch things I don't
know I think there would be more secure ways to to transfer that type of stuff with an organization one other thing that you should definitely be doing not only for your home computer but also within your organization is back up in practice those two set disaster recovery drills first the forum oh so it's not only that you have you know three two one backups but also you know having your practice drills in the event that our HR guys are able to encrypt with ransomware all of our development source code you know how does that how does that impact our business and how do we quickly get back to operational status so you should be able to answer that you
know fairly quickly and know the timetable that that would take to occur train users to spot fish first the foremost you know is that the idea of especially the company dime at training your users to become an asset as opposed to a liability so definitely seeing that and only as they report things but you know how is that acted upon within your security operations center one pretty cool a tool that's published by a bit defender is anti ransomware so you might want to check out that I would not recommend that for the enterprise as I was playing with it even after the lackey patches it does prevent Loki from infecting but what I have noticed is
that it updates over HTTP plaintext so it reaches out you know and grabs an executable and updates so probably think of some type of in the middle scenario for that in the work we know sation but at least for a grand mal Joe's computer i'm probably going to install that on therefore also definitely want to implement least privileged access based on you know user business roles there's no reason why your HR your sales team has complete read write on your dev source trees right and starting to wrap up a little bit just want to go over some final thoughts of what I'm currently working on and what I'll be concentrating on in the future as a kind of mission earlier
the malware ecosystems starting to mimic legit software you know you have your support your sales marketing distribution and even your development team one thing with in some of these ransomware instruction sets you'll see that it prompts the user or instructs the user to reach out to particular Bitcoin exchanges where they might be able to utilize their PayPal account to exchange that for Bitcoin have those exchanges then looked at you know what it would with all the amount of money that's moving around with a big coin from ransomware you know that these exchanges are getting a nice cut of that action so I haven't seen too much research out on the exchanges themselves and of course there's a huge rise of
ransomware all these families that we talked about here they're marketing on underground forms so people can hire that they don't have to stand up the infrastructure to start these campaigns they're slowly just renting that service and then from there it's left up to them to hire maybe a spammer or a distributor to massively spam out those campaigns one other pretty cool facet that came across with ransomware while researching this stuff is it's being used to cover up corporate intrusions so some of your advanced persistent threat I know don't throw anything at me I mentioned apts some of these guys you know they've been in network for two or three years they've exfilled every bit that they
could have you know possibly get out of an organization that so one last-ditch effort maybe to monetize the foot hole that they have on an organization is to drop ransomware you know that probably maybe tips ahead as far as detection is concern these guys I think it was the secure wheres article is pretty neat that they distributed rent somewhere out to be like Active Directory somehow maybe wsus or whatever its successor is to all the the computers on a network but the they found out you know after you know coming in investigating that that these guys had been in the network for two or three years already so and some future work that i'll be taking a
look at personally identify more family vulnerabilities especially playing with the community control infrastructure backend server which is fairly new first thing in the wild around march 10th so starting to play with that now and of course any type of one project that kind of came up with and maybe wanted to run this by you all to see what thoughts were on this is taking a look at a long-term monitoring so after a user's infected they pay the ransom and that doesn't you know these guys aren't removing the malware from the computer so the invent are the reason why they paid the ransom in the first place the victims because they don't have solid backups and the data that they was
encrypted isn't important up for them to pay the ransom so they're probably not wiping the computers removing all traces in malware this malware still communicating you know back situ so that's one thing that i would like to play with you know perhaps maybe access you know to that infected node is sold to a third party could be the case or as later versions of particular malware family come out does it reinfect itself and the whole you know ransomware or the ransom process starts over again I think that'd be pretty interesting to take a look at and got a quick video demo here for you
so what I did here was um just create like a batch file of a whole bunch of different ransomware families and the only two that I actually got to pop up was a server and CTB locker so as you can see Sir bird didn't take any time at all as soon as i started the the video there that's when server infected popping up HTML instructions as you can see there the dot onion link early version of server actually requested that you download the tor browser which just as you think servers good pops up another text document it's pretty funny thing about I mean they definitely want to make the the victim user get those instructions but then CTB Locker takes
over minimizes all the windows and sets the desktop background to the instructions server comes back with HTML instructions again and they kind of battle it out a lot of Windows scripting errors going on mainly because the the infected file is there encrypting themselves at this point so it's a kind of a race condition which I thought was pretty fun yeah yeah yeah yeah true yeah that could definitely save you in some ways yeah this end user obviously having a really bad day probably call an IT right now I t's telling them well have you tried turning it off and on again yeah good one thing you good yeah catch a quick yeah I don't do much I are um
but that would be my approach to it I wouldn't try any other questions yeah it's very debated on there was like a FB i-- release i think it was a week or two ago and i don't know if it was lucky actors that they were talking about what they said it could have been as high as
yeah can be over inflated extra shirt the UM there has been a lot of tracking you since this is Bitcoin there has been some researchers out of it tracking watching transactions then some of the earlier crypto wall research that came out about blockchain tracking they suggested anywhere between 200 for out of dollars very high numbers
it's working so I change it please enough to get it like these guys but I mean the reason why there
yeah my fruit of these yeah cool any other questions good y'all bout hungry yeah I know I am um I think we had one announcement real quick