Oh, the Places Your Packets Will Go!

Show transcript [en]
We're starting right now. Oh, [laughter] the P places your packets will go. Congratulations. Today is your day. You're in packet. You're new and you're off and away. You have data inside. you have things to say, but you leak who you are all over the place. So, for those who don't know, uh network packets are the way that your computers communicate with other things and that carries across backbones. So whether that is at home and maybe it's your internet service provider, your ISP, maybe that's from your phone and that is your telco who you're sending that to. Maybe it's the uh MC fast food place that you're at on the Wi-Fi. Maybe that's your coffee shop. Maybe that's
your hotel. Uh whatever those things might be, those things in between your device and what it's talking to see your packets. And depending on what you do or don't do with those packets, they can see more or less things from them. So, my name is James Pope. Everybody calls me Pope because apparently that's just more unique. Uh it's not as uh impactful at family unions, but uh otherwise everybody's calls me pope. I don't care. You can call me James, whatever. I am the technical marketing engineering director at Corlite. That just means I have really smart people working for me like Elden here on this front row. Uh Jason, a bunch of threat hunters who do a bunch of cool stuff. Uh
I am the sock lead for the Black Hat Knock. And I help run some security conferences like Saint Con, Besides, and Cash. I got Mike Spicer here to uh come give you guys a keynote. I also uh helped kick off DC435. Uh we once a month meet here at this same place. It's free. It's by the community for the community. Every first Thursday at 7 o'clock. It's on dc435.org. I have not updated next month, but I'm actually presenting next month on using MCPS uh to query SIM data. So if you want to do that, uh these are just various logos and things. >> To be fair, you stole DC435 from us in the south. Uh, we got it first. So, it's
not stealing. >> We made a conscious decision. [laughter] It's all ours. We >> I own the RC channel like splitting the the codes. Weird. >> Uh, past stuff. I did threat hunting for multiple years. I did some pen testing. I was a VP of IT. I don't know. Been been in the IT space since 2000. So, the black hat knock um Mike spoke a bit about this, but uh this is the originating days before I started. I've been over a decade there now. And it's it's full of volunteers, knock leads, and partners. And the partners are we go choose a a technology, a solution that helps us solve a problem. We bring them in. So they're they can't buy their way
in. They can't uh hey, I'd like to be part of your knock. We we choose them and then they have to give us free tools, free things, and free people. So it's like great, right, for us. uh we get some a giant room of 60 70 people who are focused on finding the really bad things and the bad. Uh you can absolutely have legit bad things happening and they're totally cool at black hat because that's what they're paying money to learn. So we do a lot of uh evaluation on that to validate you know is is this a legitimate bad thing or as we call it a black hat positive a true positive but it's okay at black hat
attacking other people not okay attacking backbone not okay attacking registration not okay um I'll get to more detail on that here in a second so part of that it turns into we have to try to find people and in some situations it's they've come compromised and we want to let them know. In some situations, they have uh let's just call it bad hygiene. They have something in their traffic that is telling data about them that they didn't know it was telling about them. And sometimes it could be severe or other. And then uh in other situations it's um you know they're legitimately doing bad things. And there's different escalations for all those things. And uh
in this example uh every show without fail we see it's weirdly government agencies who have um connections to LDAP over the internet which is wild. It's different if you make a request to LDAP versus they actually um are connecting. So that's cool. Uh anyway, so that's a situation where we'd call that probably a bad hygiene. You know, you could put that in a different bucket of something more severe, but um that's where we would go find them, communicate with them, reach out. Sometimes we have to um make a request to the registration and say, "Hey, who at this or is here?" And then send them an email or go find them. It's easier when they're vendors, right?
Like you go down to their booth and you're like, "Hey, uh can I get a hold of your IT person?" type of thing. But uh LDAP government while but if even even without even without it binding this is a great way to fingerprint what organization somebody works for because even if it's not actually connecting um we're seeing that they're trying to reach out to or do something right we see that they most likely work there it's unlikely that they created a LDAP bind on their machine uh unless they work there. You're on your own and you know what you know, but your headers will tell everyone where you go. You'll broadcast your company. Plain as can be, your
patch level, your habits for all folks to see. Yeah. So, another way we fingerprint uh is DHCP and DNS. probably the top two in the year 25 is going to be your SSL TLS, your SNIS, and your um DNS records, right? And so in some of these situations, we're we're getting host names. Um I I I I try to get it was too hard to get a screenshot of 55,000 different iPhone and MacBook Pro names and and then I was like, well, how am I going to have to sanitize it? It's going to take forever. So I just made a a chart of it. But this is example. It'll be like Christopher's iPhone. And sometimes they'll be like iPhone and
org, right? And MacBook Pro or so something to think about. Um, sometimes your orgs don't give you a choice, right? They're dictated. Some of these Windows boxes are generic, whatever. And some are very explicit like company or name company or acronym of company a lot of times. So those are uh useful sometimes. You know, I left ANS up there because like and MVP is MacBook Pro. You'll see that a lot. Keraros like really shouldn't be at black hat with Keraros, but we do see it from time to time and they're very explicit typically to the org they work at. Um, I left a few pieces here, but yeah, education and corp and you'll see their domain forests and bunch of crap
like that inside of there. So, it's another interesting way to find out where they work for. And so in some of these situations like I'm just trying to notify them of a problem, right? We have some captive portals and things but it's uh I need sometimes to get in contact with that organization, that person to empower them with data to improve not only their own device posture but the rest of their org, right? We might see three or 20 people from that org there. But for those in some of these companies, there's 30,000 employees at that org who aren't at Black Hat. Maybe they're not all remote. Maybe only 10% are or whatever, but they're going
around the world likely with the same configuration. And so in a lot of situations, I'm trying to get it escalated to their security or IT team and give them my email address, give them raw data. And the best thing that I enjoy is when you see this, you don't see those same things happening at the next show. >> Yeah. >> What's the source of this data? >> This is Black Hat Security Conference. >> Oh, sorry. He asked for the recording. What's the source of the data? Um, we do point this out a lot. Illegal still legal at Black. We do have a luxury over like Defcon and that is when we tell people to knock it off, they typically
do because they or their org in most situations have paid money for them to be there and they probably don't want to go back and tell their boss, "Sorry, I got kicked out of Black Hat for trying to hack a space agency or payment processor or um those are just random things off the top of my head, not real scenarios, >> but um illegal still legal." So this is a situation where it's much easier. We we find a thing. We walk into the classroom and we say we interrupt trainings, right? I need the I need everybody's attention. Um depending on what it is, like you know, IP config all or whatever, right? Pull up your IP
addresses and your MAC addresses. This is the IP address. This is your MAC. I know more information about you. But you yell that in front of the entire class. Illegal, still legal, black hat. Knock it off. And most time it will drop, right? Um, one time there was a dude that you knew. I'm not naming names, but he he just left because [laughter] after we pinned it down to him, he just he left. He left. >> He he was bored in the training. He could have taught the training and so he was went to his own devices. Yeah, that but illegal still legal. Um, autodiscovers are great, right? Uh, your emails, the emails you're trying to uh
connect to your org. So um this is a pretty good indicator not by itself but this this is a high one. I have weights of this. This is one of the higher ones u that you are likely work at that organization. um because but you know there's community email addresses there's other situations where you could be part of something else but this is a good way to know that they work at setorg because they're you're saying I want to find out what the IP address is for my exchange server or Microsoft or whatever it is and it will point you to that direction but the DNS request autodiscocover or name Microsoft another variant there's like a
bunch of these So they they there's decades of Microsoft of people were self-hosting, moved some parts to the cloud, moved some parts to Microsoft but had their own hosting of Microsoft and now they're all 0636. Anyway, there's variations and this this is still all happening um out there. So on Microsoft.com is also another one that is uh very telling to the organization they work for. My highest weight of all of them is your VPN, right? So when people are doing things right, they are tunneling their traffic through VPN typically or they're validating that all their SSO is TLS and we're not seeing all that detail, but they're reaching out to their VPN. So that connection is
like these are my variants of it that I see. I try sanitize most is pretty good, I think. Um, but there'll be ones that'll be like MSDCS and it'll be AzureVPN and then um in there will be like the organization name and most of these are like something they will even give you like regions and a bunch of other information but yeah VPNs um portals Citrix portals uh lot of there's there's a lot of orgs that have uh special VPNs for phones and some have separate ones for iPhones versus Androids versus other. So, you'll see like one org will have like four uh and sometimes even more. I've seen like numbers like VPN 1, 2, 3, four, five,
six. I'm like, I don't know, they just didn't know how to do a load balancer or something, so they're just dropping them there. But this is a a very good indicator to see uh where somebody is working at. Uh the word remote is another um good one. And then yeah, regions. There's a lot of region based stuff that exists. So that leads to things like we we rarely call out big comp company names. Uh we we like to send disclosures to them like hey uh you guys should really like fix your product so that way um people who show up to conferences let alone security folks but the whole rest of the world use your
product uh isn't leaking all this stuff out. Big fix. We've been saying it pretty much every show. So much so that it's on the I'm tired of this grandpa slide in the black hat knock debrief. Um they in a postbody in the clear and I I don't know for sure if this is every big fix or if this is just somebody self-hosted but it's every show and it's more than one or it's enough where they should do something to ban steer their customers. So if you have big fix by chance, I highly uh recommend you go look at that traffic because it will tell you everything about it about that host and in some situations it'll even
tell you which patches are not applied and the severity of those patches. So again like here we are at black hat and you're like well why are you looking at my stuff? You're invading my privacy type of thing. But if you're at hotel Wi-Fi, somebody could be doing that same thing on your VLAN or that hotel or somebody over wireless grabbing your packets. Mike Spicer >> um grabbing your packets and they could be seeing these same things and this is like a glorious targeted list if that was somebody you were going after like here's every crowd strikes running on that box, right? Okay. Um well, I guess that's good, right? It's better than not if you're going to be releasing that.
But at the bottom of that is uh here's all the patches that haven't yet to be applied and their severity is like I don't even need to run a V scan. I already know what I need to go launch against that host. So this is one we call it every time. Um big fix. This is leaking your stuff out. Uh a program that shouldn't be doing that or it's misconfigured. A new one that's made our list is been um I think we started saying this public like a year or two ago. >> Year and a half. >> Year and a half. Zcaler. So Z tunnel is Zcaler and actually met with one of their guys and had a
conversation with him about it and apparently this is their um 1.0 product and he's like but it's but on 2.0 it doesn't do that and I was like cool as soon as your customers quit showing up to conferences using 1.0 then we'll quit saying it, right? Like we don't we don't want to see it in this situation. What this happens and literally the first time and every time that this it's it's so much now that we don't even go and talk to him anymore about it, but we used to go and sit down and and have that same find the person, go have a conversation about him and be like, "Hey, I don't know if you know,
but like we see every website you go to." And they're like, "No, you don't. I have a green check box in my corner." Right? And uh security folks are interesting. uh they're usually typ typically there's a lot of senior folks and they're very strong on their opinions and that's not a bad thing but um when they're challenged sometimes they get very defensive weirdly enough I always have to like come at it with like a hey well maybe you're right let's look even though I'm like I I see every site you're going to right uh so what happens you'll see this green checkbox for zcaler in the bottom right corner and uh proxying all of the URLs in the clear so
this just actual sites this person was going too. Um, and these are unique counts, by the way. So, for this in black hat USA, 5,600 sites that you could go to. And some are like, this is an internal chat application.org. And it's like, well, okay, cool. So, uh, yeah, if you have Zcaler, go check or move to version two. But I I argued with him. I said maybe you should like have your PS guys help ban steer everybody who's doing this and then we'll quit talking about it. Um then that leads to overall the SNI like all the sites you go to. Is this as strong as an indicator? It's not as is not as high as a VPN is because
you could have a org that sells a product, right? And a customer could be visiting that. Well, that doesn't necessarily say as much, but there's a lot of these vanity URLs the best way to put it. So, in this case, this is their 2.0 product, right? Zpath is different. Um, and these vanity orgs, so or do whatever string, these are all companies that are connecting to them. So I can say that these companies use this product but I can also say that it's unlikely that uh a non-employee is using zscaler.path for that company's subdomain. So it's a much higher likelihood that they work for that organization. And you're going to see a ton of examples of
this where there's a lot of applications that help me narrow really quick. I have two at the very end that are like my go-tos. Um, but this is uh useful. It's interesting too because a lot of times they're you know these orgs are like they they won't advertise that they like we won't tell people what our security stacks are. Uh even on LinkedIn we take away that information and and then like you could go on hotel Wi-Fi and look and you could you could see all the security not all you can see a lot of the security products. There are some that um I went and absolutely went and dug through and looked and couldn't find results in um
because they use load balancers or um other CDN type stuff that offuscated endpoints. Why aren't you encrypted? They ask with a fright. But you're just a small packet not sure what is right. You think that an AI should know what to do to answer the question and implement too. But wait, your packets are leaking. Oh, what can you do? You can hide them with tunnels. You can wrap them up tight. You can keep them from leaking and sleep well at night. >> Yeah. So, uh, starting in Black Hat Asia, I started calling it the rise of the vibes and also the rise of the self-hosting. We're seeing way more applications that have weird things in
clear text and chat applications where there's a lot of translation features that somebody put in and that translation features going to Google or something else and it's over HTTP. Well, that turns into you can view their entire conversation because it's being translated over HTTP, right? all these weather apps. I don't know how many weather apps that we've seen that that put out GPS exact locations of where they're at. And some of these are like, what is this thing? You go look and it's like 5 million downloads and you're like, oh my gosh, like I never even heard of this and who's getting five million of these. Uh and and so as you're just trusting AI and you're vibe
coding and I do a bunch of that, like let's go build a thing. If you're not really explicit, it just takes whatever path it's going to take. If you're not saying use brypt and this standard and make sure that your front end is talking to the back end over TLS, uh, it's not. And then you show up to your hotel or whatever and your backends at your house and you're VPNing and it's not done right. Uh, all that stuff just ends up in the clear and you see all these calls and we saw AI chat applications, people trying to compromise things. so much of that that uh cool go ahead and vibe AI but go validate don't just
trust that that's the case um same with your tunnels Mike they talked about it uh on his preso how um Avon how there's you know vulnerabilities in some tunnels and what they're leaking out and then one of the big ones at black hat is just split tunneling so at when you set up your VPN you can say I want to route everything to the endpoint or you can say I want to route everything but these things and most corporates will push VPN profiles and you can't control that split tunnel and a lot of the people who show up at Black Hat, they'll be there and I'll be talking to them and they can't change it. What happens is just sheer luck.
They get there and the subnet that they're split tunnel just matches the subnet of one of the classroom or gen Wi-Fi or whatever that we have. But that could be a true statement for again any place that you're at, any Wi-Fi that you're connected to, if the split tunnel aligns, that stuff goes over that channel. And a lot of times the stuff that you're in 2025 that you're VPNing to an organizations versus SSO to the internet, they're usually things that like are super sensitive or they never bothered to go set up the encryption and do all those things because it's sitting somewhere else. And so it turns into like, holy crap. And then self-hosted. I'm still trying
to figure this out. I'm debating if it's the uh you know piracies up or uh privacy's up or both. Um we're seeing a a big rise of self-hosted and maybe it's part of AI too. you can just slap things. But we're seeing way more self-hosted things where in one extreme situation, we had somebody who was best case a red teamer, a pentester for a government and bank syncing all their files back to their house but in the clear, right? So the company had maybe all their policies, everything set right. This employee had, well, I'm going to make sure I have my own backups. And that created a problem. And one of the one of the ones that you know
when a bunch of suit people walk into the knock, it's always going to be a longer day. Um especially when it's multi-country right? Uh we also do I do Black Hat USA, Black Hat Europe, and Black Hat Asia. So we go three around the year. Uh and then there's a bunch of other things, right? These are some of my higher fidelity ones. Uh there's a whole ton in here. There's not enough time to go through them. Some go really quick, but of these just they're that same vanity tag and they're a service that is unlikely to be used by somebody else, right? It's most likely for that work. Whether that's glean, this is some AI, listen to all my
conversations over Zoom, transcribe it, send it, they have a bunch of other stuff, but um all org names um pager duty. you know, the CIS adsman out in the world or, you know, previous life getting PTSD from that, but it's unlikely a customer's connecting to your pager duty, but I don't know, maybe you have an MSP and there's maybe a situation where it could have a little bit of overlap there. HR situations, my workday jobs is great. It's, you know, that's probably an employee or at least a exemp employee, right? Connecting directly to that. Out there, things can happen and frequently do to packets revealing and trusting as you. A sniffer may watch with a curious stare and log all the
secrets you accidentally share. Yeah. So the way you get a a the way that you get a feed into some network visibility tool on an enterprise level, you're typically looking at some sort of packet broker tap aggregate. Um maybe it's glass mirrors for uh fiber. Uh at home, maybe you got a span port, maybe you got a cheap little tap that's one in, two out. Uh span ports on switches. That seems to be a pretty common one to do. But you have the ability to do a lot of this. And these tools, some of these are absolutely free. Wire shark is free. Just download it. Go look at your stuff. TCP dump. >> Dump cap.
>> Dump. I don't even know dump. Dump cap. >> Dump cap will get you all the packets. I caught as much as everyone else at Black Hat with dump cap. >> Uh, Zeke is free. Serakata is free. Right. You can do these, run these. There's no situation where you shouldn't know this. It's weird to me. it not just for this but you know even on when I was doing pen testing stuff like how attackers know more about systems than the defenders do and they just do stuff like this they just look at the traffic that uh the typhoon ones reading those they were dumping pcaps xfilling entire pcaps leveraging those against the org I mean if you if you're not seeing gigs of
pcap leaving your network you're probably not looking anyway but what were they doing they're just looking at network traffic they're saying what was this. Oh, here's all these clear text creds to the VPN service account, right? Um, so go look, add a span port on your switch at your house. Go take a look. Um, there's some really cheap and ones on the Amazons that will get you what you need for a lot of those things. But yeah, definitely need to go look. And then there's a lot of security products in this bucket, too. Uh, this one I think I'm trying to remember what one trust was. It was like some um compliance reporting thing like that.
Microsoft has a lot of these like weird variations of sites that you could host. This one is a little bit less fidelity because there are situations where you could put up this host for a customer to use versus internal. But most people who do that right just get a proper DNS and do that right for customers. They don't want to redirect them to on microsoft.com.access.mmcas.ms type of thing. Um, same with I'll show you a few more other examples of other things like that too, but Service Now is another one of those. Most of these are internal, but it's a application that you can go spin up all sorts of websites and do all sorts of stuff with. And so
you have variations of that. Same with SharePoint. Uh, there's a lot of SharePoint 28 TW. These are unique numbers and these could be a little bit padded. Some of these are going to include like their own legit endpoints, right? But of that, it never makes it past like 10 12 unless they have regions and a bunch of other stuff. So 28, this is at black hat over 2,000 unique sharepoints. So that's a great fidelity to know where somebody works is probably what they're accessing on internal repos at their organization. >> [snorts] >> Then you'll face a real black hat surprise, a grifter with mischief and greeted their eyes. They'll see your VPN, a misconfigured state and use your
own data to open a gate. Yeah. So, back to that Volt Typhoon example. That's exactly this. Uh there was one black hat a few years back where people showed up on site and uh after some investigation we we realized that they had command and control on at that moment going to North Korea. So this these examples I'm showing you this is how I went and said well where do they work? How do we get in contact with them? Because it's one thing uh we have these captive portals at Black Hat. like, hey, uh, you know, your device uh might be compromised or you might have crypto mining on it or something's in clear text, but we have like continue,
right? Where at at your organization, you're like blocking stopping. At Black Hat, we're like, you know, maybe you meant to have crypto mining on your machine and you don't want me blocking you. Maybe it's part of your demo downstairs. Maybe you're literally on stage presenting some malware thing right now. And so, like, we don't stop that. So, I don't know, maybe it's maybe it's part of their demo that they have three people who all showed up with command and control to North Korea. So, we don't just want to block that, but we do want to let them know because if they don't know, then they might want to know, right? So, we went and looked at bunch of these
examples that I'm showing you and um we were able to go find them on they had a a booth on the floor. were like, "Hey, I understand you're just a salespeople, but like can you get me in contact with your IT or security and here's some high level and uh all of those three went off the network." So, um, success, right? Uh, at the end of the day, if we're not making things more secure, we're not doing our job right in the black a protecting our own stuff, protecting people who are there at the conference, but uh, hopefully making it better for future shows. Some of these organizations listen, some of these application listen and then some just
you see it show after show after show and we call them out. So um IT support stuff, Zenesk is great, but this one could be a little less because there's a lot of portals that customers get sent to that will redirect and clear on Zenesk, but when you add it with something else increases that weight. Um, this is a there's two versions of this for the same company. It's like a Zenesk. It's Fresh Service or myfreshworks.com. It's just another IT support ticketing system. Security tools. Cyberhaven is great. Um, WebEx is, you know, 400 of these. I'll show you one, the GOAT here in a minute. That's a competition of WebEx. Go ahead, Mike. You'll want to turn back. You'll
be filled with fright. They'll poke you and prod you with all their might. They'll copy your payload and send it along to a place where good packets should never belong. >> Yeah. So you can you can take a copy of your own traffic and do something good with it. Try to improve something, remediate or somebody else with a cactus device getting all the networks and all the channels could be taking that and doing whatever with that. Right? So it's not that we are at Black Hat trying to be overly monitoring. We're trying to protect things and then we're trying to let people know but people are absolutely doing this right you for wireless you can be I don't how how far away can you
be in to actually have reasonable capture mic >> depends on the antennas but 100 meters is a good rule of thumb >> so 100 meters is far when it comes to walls and not seeing somebody there like they don't need to be in your lobby they can be outside especially traveling employees right everybody here connecting Wi-Fi all your the stuff if it's leaking this stuff out. Well, they might be able to know what your name is, what company you work for pretty quickly just based on what I'm showing you. Security products, SSO things, there's a lot of that's another one you can go look for. O pages, um, portal pages, SSO pages, things like that are pretty good
indicators. Sassy products. They're usually all vanity. Go scope in this scenario. Octa. Kangji. This is an MDM. There's a bunch of MDMs out there. But on you will go through the network seems though. Through the network seems foul. On you will go through the grifter mayal. For a watcher is watching with tools of their own. a defender of data, not leaving you alone. >> So whether it's yourself, you're a student learning, whether you're an organization, if I'm if I'm one of you guys in an organization here, I am absolutely going to run this against a default profile. Whatever your golden image is of your reimag laptops, I am checking this. I'm checking that VPN connection. I'm checking that state. I'm
checking whatever I think I'm okay with being out versus not knowing. Then you want to think about traveling employees split tunneling where they land on the same subnet as the hotel Wi-Fi. What's the can they turn that off? Is it allowed? Because sometimes they can't and they don't have a choice. They're just routing that. So I'm absolutely validating that. If I'm an individual, I'm a student, I'm learning, just start with TCB dump or wire. Wire shark probably the easiest. If you get a guey on it, you can just hit start capture, end capture, and then just start looking at it. Uh, if you don't know, AI is pretty good at writing queries for Wireshark. Just say, tell me how I could
find one of those examples I just just told you and stick it in. There is a free form text search in Wireshark, too. So, you can just put that in. Um, go go look and see what is leaking out about you and your organization. Do you have something like Big Fix that's putting everything out? Or we see a lot of applications where they'll be like it's done right except for some weirdness with uh the first request is HTTP and you have your JWT your u web token is there and that could be used to log into that application. We had more than one occasion where it was like u like an avatar upload like everything was good
with this application. logging in was good. Everything is TLS. Everything is set. And then then suddenly we see like a post in clear text with like basic O, right? And so they built this app and at some point they added a module or something where it was like, yeah, but the they might the employee might want to change their avatar picture and that part was not configured right, wasn't tested. Maybe it was just MVPd up and they shipped it to prod too quick. there's no validation on it. And what we don't do at Black Hat is we see that we don't go try to log into that portal, right? Because that's that's illegal. Illegal things are still illegal. Uh but
you could make a pretty good guess that that credential is likely the same credential. And in one situation, one of our own tools, it was a signage tool, did that exact thing. Everything was great. you would upload only it was like it was like not PGs but JPEGs with an E. So if you uploaded a picture of JPEGs and E some some reason it's like oh that's that's basic O right. So we were updating an asset to one of the signage and it did a postbody with basic o and they like hey can we validate this this would log in and I was like yeah admin access to the entire thing right so in that situation we had permission because
it was our own tool and that was not a small signage company but edge case somebody didn't code for JPEG with an e just jpg pngs are fine but with an e yeah why I don't know I couldn't tell you the thought process some developer maybe could could it seems like that would be doesn't make any sense to me but anyway um go validate use your own tools and make sure that you're not like the part I always find fascinating is like we're at a security conference with a bunch of security folks and so in my head I'm trying not to get doom and gloom about it but it's like if this is what it's like at black hat
yeah like it's got to be pretty wild for the general pop especially like these some of these orgs that have very little or no say in their security team, let alone the ones that are giving them budget to go attend a training that they actually care enough to like try to like improve or maybe just sell their wares, right? I mean, that's also very valid reason to go to black hat. Uh Salesforce, there's lots of different variations. Force.com, Salesforce.com, and then they have this other Salesforce-scrt.com. All of these are theirs. They're all really good indicators. Um especially when there's multiple of them tying together. But Salesforce also lets you spin up a thing for a customer. Treat
this one as a little bit lower of a weight than some of the other ones. One password is pretty good. Um, and this one there's family accounts with names sometimes. So, you might want to think about how uh if you're paying for one of those and you're vanity tagging it, if it is your family's last name, which is a lot of these, that might be a good way to know who somebody is, right? So, I do think vaults are great. They're uh you just might want to think about that. They a know you're using one pass, right? Um by the way, a lot of orgs are 316, right? That's a lot of orgs. Um but in some of
these situations, I know the family's name, right? Because they come there probably with two vaults. They have one for their work, one for their home, then their whole family's on it. That's a great practice. I'm not knocking that, but might might want to make that a little more generic versus your actual last name. Another MDM JF. Um, see a bunch of this Atlassian is pretty high on here. Uh, this is the Jira suites of products and the confluence of things. Um, you'll see a lot of these, a lot of name vanity. Uh, going off of this one. That one's a pretty good indicator. Beyond trust. More vanity. The watcher sees you, your path, and your plight. They use your data to make
things secure and right. They'll see the weak spots that the grifter got through, and they'll patch it and fix it. All thanks to you. So, yeah, I mean, we absolutely leverage this to try to make things better. Uh I would love to say that the organizations the the organizations are pretty good at remediating not all some are same year after year the application the service layer what do you want to call that it's it's not been a high percent I mean I think anybody who does bug bounty can probably say the same thing you send them the information the details they say thanks I would like to think we have a little bit of higher percent than some of the
bug bounties only because like we're not asking for money. We're not asking for anything. We're just saying please please fix this. Like it's coming from Black Hat Gmail address. Hey, I'd like you to remediate this. Um let me give you two two examples that happened last US show. This one that just happened. We had um um somebody with Splunk. Splunk's a great SIM. It's probably the preferred SIM by everybody if they have unlimited budget, right? Um it's a great tool. It's very powerful, but you can self-host it. You can do whatever you want with it. And we had a a a bank, a large bank that we had multiple of their employees were there sending all of
their telemetry from their clients directly to or Splunk. I think it was Splunk.org something, but it was all over HTTP, right? So, is that Splunk's fault? Nah, probably not because they could spin up and host whatever they wanted, right? So, that one I we had to go in that room and that is much more challenging than you would think, right? When it's somebody doing something illegal, going in the room and saying, "Who is this IP? Knock it off." is way easier than saying, "Who's Carlos and works at this bank?" Because they think they're in trouble, right? And nobody wants to admit, "You're not in trouble. I swear that's what somebody would say." Like, if it was me on the
other end, I'd be like, "You're really not in trouble." And so, you have to like give out a little bit of information, but you don't want to like single people out and make them feel bad. But there's not a lot of other ways to do that. So you're just like, "Hey, I just want to have a conversation about some something we're seeing that's, you know, you might want to just look at over your network traffic, right?" So that was a situation I walked down there, made that announcement, got that guy to pull out, uh, have a conversation with him, and, uh, you know, in most of situations, they either, you know, arguing with me or they it's immediately
like, "That's not my job. I don't know what you're talking about." Um, which is fair, right? And I'm like, "Cool. Here's my email address. Have your IT team reach out to me." And then I send them the logs. And I I think I've only had like two responses to sending them all the logs that aren't just like thanks or nothing, right? Most of the time you send it to them, they're like, "Okay, we'll go we'll go do something about that." Um, every so often they'll be somebody wants to fight something, but that wasn't me. That wasn't this thing. But most time they just say, "Thanks." So that was one situation where the org had a thing. We told them, we got right
to their IT team. Hopefully that got solved pretty quick uh for that bank. And then there was another one that is Um, this one we haven't publicly said, so I'm trying to like mentally work around this, but um, they have an endpoint that sits on the device. They have name cloud name.cloud collecting that. And in that situation, I see no reason that should ever be over HTTP. They control both ends. There is no self-hosting. They are sending all the telemetry to themselves over HTTP. They probably have an HTTPS. some reason that one's not, but you shouldn't even freaking allow that, right? Um, Elden always talks about that initial first request over HTTP that could have your
JWT, which then could be used for whatever valid. So, a probably don't even have that um for that initial redirect. It should just be like a clear call or nothing. But um in this situation, send them disclosure and I'm hoping the next show we don't see it again cuz it's a new product and people are using it and all think uh OSQuery. Anybody know what OSQuery is? It's just like depending what you turn on all the logs from all your device. So it could be like this or it could be like this. Oh, that's another really good indicator when you're looking at uh traffic. Look for osquery.org. People put collectors just called the name of the thing. That's a pretty good
indicator what it is. This Okay, now we're to the uh the goats, right? There's two goats in the world. Um this is the fastest way that we found for that one for North Korea. Zoom is one of the goats. So, org.zoom us not 100% because you could join a sales call to somebody else's Zoom. There's situations where that's not the case. But when you tie that with the other goat, high high fidelity, right? Slack and Zoom buckle together, wonderful outcome. Slack again could not be the org. There's a lot of community slacks. There'll be trainers that will have their own Slack room that their students join and that they don't necessarily work for that org. But when you combine
usually Zoom and Slack by themselves and then start pulling in the other weights of those. So start with VPN. DNS is your friend. Go through the DNS bits if you need to know who the person is. Then move over to Slack and Zoom in like 2,25 unique. So take out all their service stuff like egregiously that's 50. So I mean there's you know 1,900 unique Zooms or Slacks in this situation. Uh Zoom was 800 at at Black Hat. And that's just, you know, black hat. That's only the people who are joined to the network. That's not counting all the other people who are there at the conference who are on hotel Wi-Fi or are on something else.
So, you'll get mixed up. As you already know, with decoys and honeypotss, wherever you go, the watchers are learning from the packets like you to stop all the grifters and see what they'll do. >> Yeah, honeypotss are big in the world. deception hosts, things where a vulnerability comes out and immediately it'll turn into um trying to replicate that in some system where people can compromise, validate what they do, create signatures, detections, behavioral heristics, anomalies. Uh we are doing this all the time at Black Hat. We have people there who are just working on straight signatures. We have people who are doing a bunch of ML things in the background. Um to uh the point of what Mike was saying,
we earlier we'll do things like these there this compromise is happening right now, but there's 20 people doing that same compromise and they're all going to the same three destinations. And then we took that further and said of all of that, what room is it in? We feed AI the curriculum of that room and we say here's here's the detection. Here's the place that they're going. Here's how many in that location are doing it. Does this align with the curriculum of that class? And if all those things are true, we autoc close those as black hat positive because there is a lot of alerts at a lot of alerts and we don't got time for that. I need to know what the real
alerts are. the ones I need human eyes on to escalate and do something about. Right? So, we're using that. We're validating that. We're creating signatures. We're using all the things. Right? It's if you're just trying to plug AI to solve all things, it's you're going to have a bad time. There's absolutely a place for a standard signature. Some of those are glorious and amazing. And then searchbased alerts are also amazing. If you got a SIM and you can narrow your query to something that's always impactful, that is a great thing to turn into an alert. do that. Then you get into the harder stuff and you need people like Nacho who know math to make
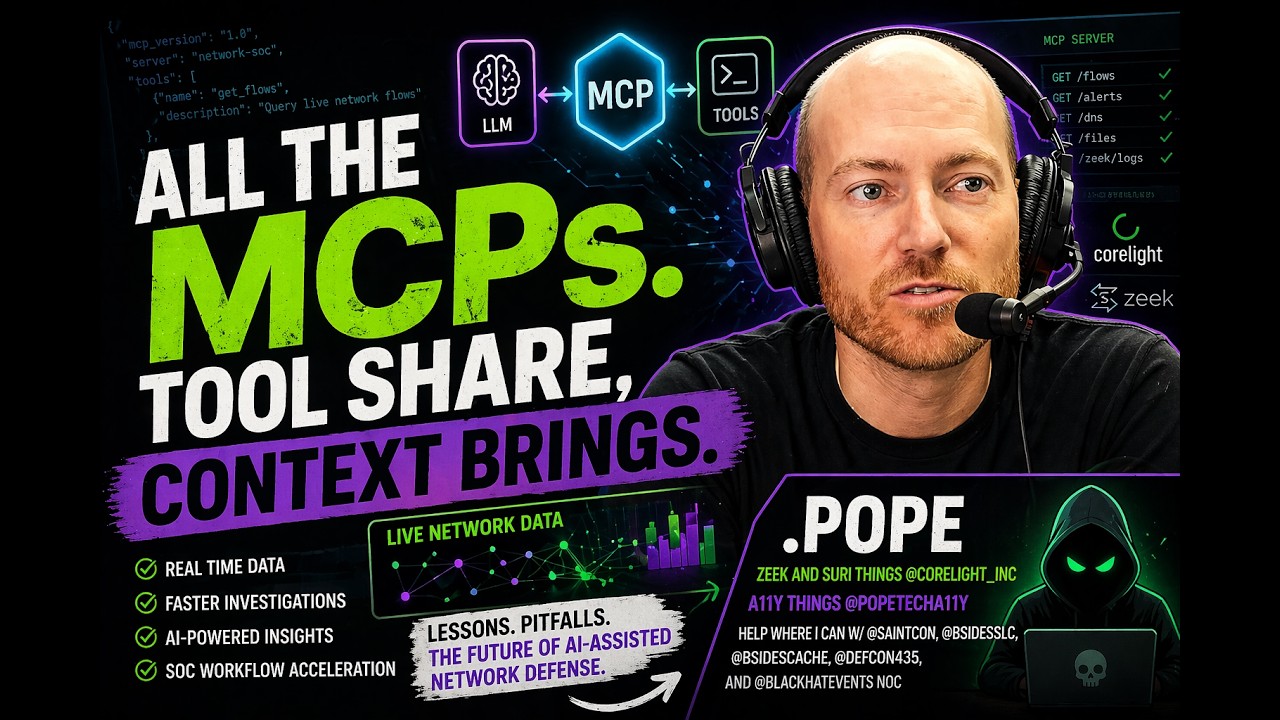
ML models and quadratic equations and you get over my head and then you apply AI to make your life easier and simpler. So this is where I so Black Hat USA um I did a MCP server that would let you go directly from Slack. Slack has a new AI app that instead of just doing hard-coded, you can just say like threat hunt an IP address or whatever and it would go from Slack to an MCP server to an LLM to the SIM and return data, right? And I started building out this phase because it's a question I immediately ask like we'll find something interesting and you know what do we do about this? And the first
question I ask every time is like well what do we know about this person? Right? That's literally this entire preso what do we know about this person? And so I started building the groundwork to answer that question. I didn't get far enough done. I actually ended up in the ER in Vegas. It was a whole another nonsense, but I I was behind on where I wanted to be, but this is where I'm trying to head. And essentially it is identify employers. Uh there's a whole section above this about identifying names if we can after this section. Um and then I I don't think I have a screenshot. I do. I have weights. So I have weights in here, but VPN is is the
go-to. Uh primary corporate services frequency. the more that you see the same thing going to here I'll show you an example this this would be this is an example of a or right this or has webex they have fresh service they have zpath they have sharepoint they have octa they have and that's it well the chance of them working at that or extremely high the chance that any one of us could get access to all of those vanity things for that or not likely als
who the exact person is or get their email address directly so I can let them know hey maybe you got C2 to Korea in North Korea and you don't know about it. So there's some gotchas on services. Uh there's a lot of these like you like I made a really good thing and it's like well sometimes they have io instead of com sometimes they have us zoom right sometimes they have cloud that endpoint telemetry thing right if you went and set search the org for that service it would have been sorry for the application would have been fine but if you did that application namecloud all their stuff righteu they have different regions so it's like oh well
this one's because they have some deal in the UK it has to be hosted there they'll UK.EU.APAC do whatever um dashameia right things like that different regions and then just just there's just a wild card of other. If your SIM lets you do wild card searches where you can just put in the name sometimes that's useful. You're going to get some collisions on other stuff. Right? If you put in the word force you're probably going to get like GeForce and a bunch of other things, but it will it'll help you to see if you're missing anything blatant. Sort that by top count. See what those are. Flip it by rare. I always like to see the very
bottom of each one of those. What's that one unique thing that's sticking out? Could be interesting. All right. So, what to do? You're like, "Cool." Uh, you have a super unique case here at Black Hat where you're trying to figure out an org. I work at an org. I already know what org they work for. That's not as useful. Um, but you might care about what your employees are doing going other places. You might care about the services you're leaking. You might care if things are in the clear. So, VPN, right? This is your friend. Um, but validate that VPN. check that VPN. You might have a misconfiguration. You might have split tunneling. You might have something
there that is making it not nearly as useful as you think it is. Maybe you're totally fine if somebody goes to Black Hat and they're going tovpn.org.com and that's all that we see. That could be totally acceptable, right? No problem. But if I see a vulnerability or some issue with that VPN, I now know who to go contact. But if you're using like tail scale is a great example. I don't see that. There's a lot of just endpoints of tail scale, but they're not it's not telling me the org they work for and there's different services and things like that. Split tunneling. This is one of the highest weights for what I'm starting to build that out. If
you're doing certificates, all those services, if you're using TLS 1.3 and there's a bunch of other caveats to that for the the nerd AP folks of uh Alice and Bob. Um, but there's websites out there, Cloud Cloudflare has one that you can go and check and see what you're leaking out of each step. Uh just know if you tune that up to the level 9,000 you will break stuff on sites. Uh I personally keep one uh Firefox on my phone which is really at the back end is you know that was you that's your conversation. Uh underneath on iOS is really just using Safari. But I have that one turned up to level 9,000. Then I have Safari sitting there
when I need to connect to Delta Wi-Fi because it won't work. It will not work if you have it turned up. It's just like no. it'll just spin. You think something's broke. It's not broke. Everybody else is on the internet. You're not on the internet. It's because you've turned up all your certificates, all your browser settings. So, there's a place for that if you want to stop tracking and a bunch of other stuff, but there are services that you're going to have a hard time with. Um DNS, um DO, there was a bunch of there was a DNS battle and DO seemed to won this battle. So, um go with DOH. But there are ways
that orgs can um ban steer that. You can like Apple's private relay, you can you can force that to not be used versus being used, but your phone will pop up with a thing. So, pay attention to things like that. Um, but yeah, I mean, all those DNS ones, that VPN, if they're using DO for that, probably wouldn't see that, right? But at the end of the day, go verify. If if you take nothing away from this other than go verify, uh, that's it. Just go check. Go if you never know you don't know what Wireshark is, go spin up Wireshark. just spin it up, start a capture. You're you're going to spend two hours just trying to figure
out what you're looking at, but um it's super interesting. Okay, so what's next? Um other things that I started looking into, UPN is super interesting. Um there's a lot of uh compelling things in there that leak out stuff about organizations. That's the also things like AirPlay and Bonjour and companion castings. There's a lot of stuff that started looking at that. Um, NTP has a lot of things that uh sometimes are very org specific. SMB [laughter] I don't know why that's in there. And then, yeah, I started seeing some bunch of WSUS stuff. I'm like, oh, I'm pretty sure I know what org they work for. Um, so I'm trying to take that, apply it to
the AIMCP, what company they work for, do the percent of math, and at the end of the day, I can just say like, here's the IP address, what percent chance they work at Corite. That was my MVP. Actually, I was looking at Elden stuff. He didn't know this. Um, and I got a n I got a 96% chance he works at corlite. [laughter] It's like he goes there, he goes there, he goes there, he goes there. 96%. Coralite is actually one of the really hard ones to do because uh all the logs have the word coralite in it for like sensor names and stuff. So like so much exclusions. It's so much easier to look at an org who's not part
of the knock. Okay. Um I don't think we have a ton of time for questions actually. Um questions I one or two if there are any and then um I'll have a final thought.
Perfect Mike. >> And you will succeed. Well, that's tricky to say. Your data has been copied and sent on its way. Your server is waiting a victory grand, but you've left your prints all over the land. If you think you're encrypted or tunnneled away, go and check to be sure before you're on your way. Thank you. [applause]