The Proxy Warfare: Unmasking Russian and Chinese Externalized Cyber Capabilities
Show original YouTube description
Show transcript [en]
Good afternoon everyone. Uh thanks for having me. So uh yeah, in this talk we're going to see how um Russia and China outsource uh the cyber operation or cyber capabilities to private actors. Uh but first let me present myself. So I'm Alexia. I'm a geopolitical analyst actually and I've been working for Quintelligence for three years now. So we are um European cyber threat intelligence provider and uh we do um uh CTI and uh risk intelligence uh digital risk protection as well. So yeah if you want to know more about us don't hesitate to reach out. So uh first let's start with a bit of methodology so you have an idea how I conducted this research. Um in term of sources I used
uh leaks uh US indictments uh reports from uh cyber security or IT companies and academic research. And in terms of scope, so I focused on uh the outsourcing to private companies and um uh either hackers, independent hackers or e-rime groups. And in terms of structure, we're going to see the Russian model first, then Chinese, and then do a bit of comparative analysis between the two. Um so let's start with the Russian model. So if we want to understand uh Russia uh cyber threat landscape, we need to go back to the 90s with the collapse of the Soviet Union and uh which brought uh power vacuum and uh that left law enforcement uh underfunded and largely uneffective.
Um so in this context the digital sphere was unregulated. So that created uh the perfect fertile ground for uh cyber criminality to emerge. And on top of that we had a difficult situation in Russia at this time uh due to the end of um the centrally planned economy and really uh rapid and cowic um privatization process. Uh so um we had a lot of people that struggled during that time. A bit like what we saw uh with the Kilnet presentation this morning. Um uh lots of uh people struggled but also IT especially that really uh with high uh skill set and those people some of them decided to turn to cyber crime as an um lucrative alternative
and we had kind of the same thing with um intelligence officer that worked for the USSR. uh some of them uh were unemployed uh after the end of after the collapse of the SSR or some other were underpaid. So the some of them decided to uh leverage their skills and their contacts and offer their services to uh criminal networks. And after over the years uh Russian intelligence agencies they started to mobilize uh this connection that were tied during this uh specific period. Um so now let's see how um the intelligence uh agencies are um engaging cyber operation are organized in in uh Russia. So you have the FSB uh the domestic intelligence uh agency doing uh
counter intelligence and enforcement but also uh focus on uh Russia near abroad. So uh the ex USSR um environment. Uh then you have the SVR um the external uh intelligence agency and the GRU uh the military intelligence agency and known for um high-profile cyber attacks. So uh bit of doctrine uh Russia does not compartmentimentalize uh cyber operation uh psychological uh operation or information operation for them. all uh interrelated tools they used uh to uh achieve their uh their objectives and this institution they often have overlapping mandates and there are some bureaucratic rivalry between them. So they compete for resources for influence. Uh which mean that sometimes you have over um you have operation uh that are done uh in parallel or um that
are um redundant. Um now let's see the outsourcing model. Um so um how you could define it. So you could think of concentric circle cycle uh at the center you have the intelligence agency and then you have the different um non-state actor that uh or bite uh that are in orbite around uh intelligence agencies. So the first article uh you have um uh private uh companies um some of these private the companies engage with intelligence agencies in varying degrees. Um not all companies that collaborate with uh Russian uh intelligence agencies are directly engaged in malicious operations. Sometime they just provides uh defense tooling. Um and these uh companies uh they provide uh different services that we're going
to see later. Um you have also in beside uh IT companies and cyber security companies uh you have also uh private um public relation companies uh that engage in information operation. Uh then another cycle and you have the activist group the proa activist group. Um uh most of this group they emerge in the wake of uh the Russian invasion of Ukraine in 2022. And um Mandant has demonstrated that some of this group um and are collaborate with uh uh the GRU and uh more especially with ABT44 um uh in some in some operation. Um then another cycle you have um lone wolves individuals uh actors that are independent that may engage with the state from time to times. Um and then
you have uh erm groups that also do so. Um it is also plausible that um some FSB operative are embedded in some of these groups. So the leaks that uh involved uh Blackbuster content and trickbot kind of demonstrate that some members uh have link with the FSB. Either some have uh could be uh FSB operative or um are um have tied ties with the with the FSB. So uh probably the FSB uh tried to uh monitor this group and influence them on a more opportunistic um um opportunistic um outcome. And um some of uh this group or some of the non actors they either ideologically align with Russia but others they just cooperate with the Russian intelligence agencies
uh in in exchange for protection or tacid permission to continue to uh conduct uh financially motivated um operations. And another aspect of this escos system is that uh these group uh are sometimes enablers for uh state sponsor thread actors. uh they provide access infrastructures um and uh malicious code is also reused uh coming from uh um e-crime groups and then reused uh by uh state sponsor actors. Uh now let's see the services that uh companies actually provide to uh uh the Russian intelligence services. Um so the outsourcing activity in the case of rich Russia they um serve a more uh support oriented role. um they don't uh perform the all um uh spin uh lifespan of um cyber
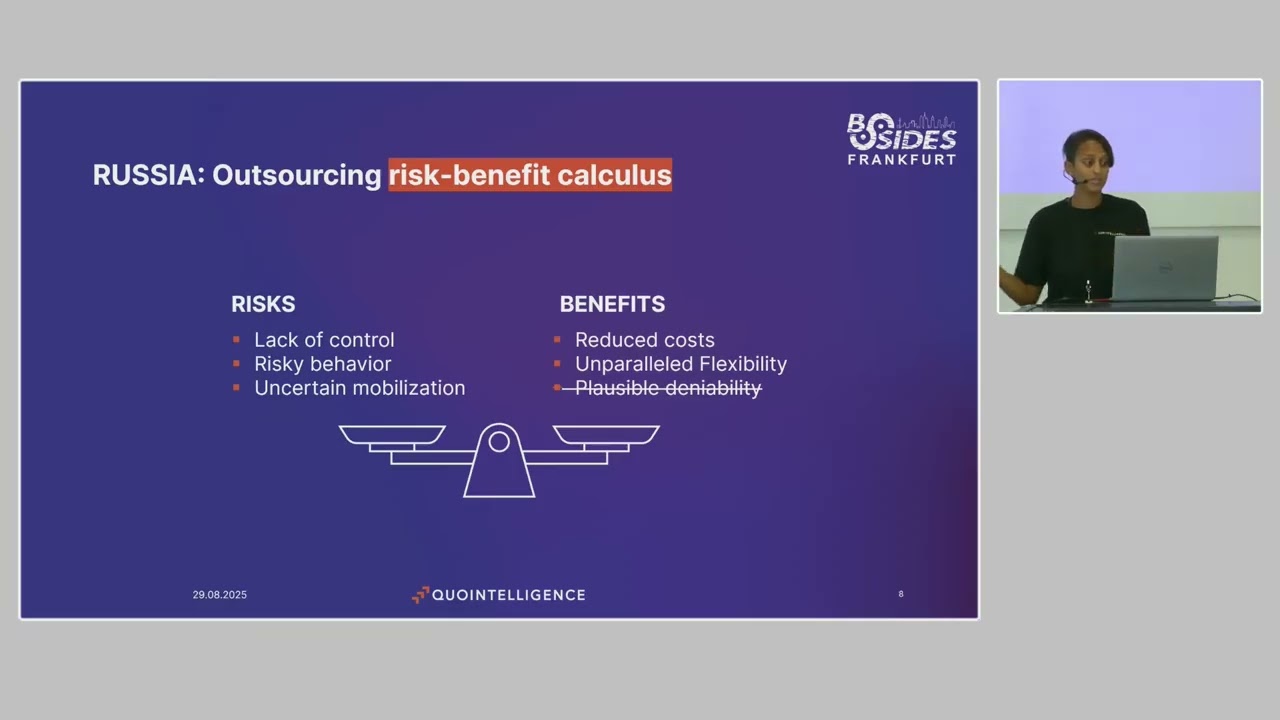
operation but they provide more tooling platforms uh for vulnerability identifications um data anal collection and analysis uh they also used for recruiting so um they uh will organize CTF competition uh where they could identify profile that are interesting for the states uh to later recruit and they provide also training platforms and uh as I mentioned before uh some public relation uh companies also engage uh in information operations. Um, now let's see. Uh, the risk benefit for for Russia. Um, on the risk side, obviously you have a huge lack of control. Um, if you outsource to private company, it's easier because uh you have a contract, you have terms and condition. But if you outsource to uh
informal actors like um independent hackers, ime groups or even activist group uh you don't have full control of them over them. they have their own uh motivation and they some most of the time only partially align uh with the state's motivation and their motivation or the engagements can also change in time. So um an example of this is like the case of cont. So uh in 2022 they announced the ransomware group announced support for Russia in its uh war against Ukraine. And only two day after they announced that um you had a Twitter account that pop up and um internal conversation from the group were uh leaked and this uh at the end resulted in the fragmentation and
dissolution of the group. Uh so when you engage with this type of actor um it's unpredictable and they are not really reliable. Uh they could also have risky behavior that don't align fully with um uh the uh state interests or uh escalating tension with adversaries for instance. Uh so yeah uncertain mobilization we've seen as well. So this is all behavior that uh could uh that are part of the risk uh from uh engaging with this kind of actors. In the benefit side, you have reduced costs because you don't have to maintain um pool of highly trained uh IT specialists and um and you have flexibility and innovation because uh intelligence agency they are bureaucratic institutions and we know
that this type of institution are not the best to be super innovative, super flexible. So, this is something they can mobilize from uh uh thread actors that are out there uh on the underground that are way more agile uh than than uh state actors. And maybe you wonder why I crossed the plausible denability because it's something that is uh cited a lot in security studies. But I think in this case it doesn't really make sense because uh this concept uh says that if you use a proxy you can say no I I I have no relation with this entity it's not me and therefore you can uh deny any involvement from the states but Russia
they don't care they deny even if it's their own uh operative that conduct operations uh even if it's super they you have a lot of evidence pointing to them pointing to even yeah operative uh from the FSB they would say it's not them. So uh actually I think the concept of implausible denability works better here which is uh the performative uh discourse of denying responsibility for any uh engagement and this is what uh Russia does and actually this strategy is quite good because it maintain ambiguity and it leave the adversary in a position where they don't know how to respond or if they should respond. Um so yeah, this has are the risk benefit calculus
that uh the Russian state does when uh outsourcing its cyber capabilities. Um and let's wrap up uh this section with a quick case study analyzing the network uh be behind Ganganger. So um since uh 2022 with the invasion of Ukraine uh obviously the uh British and influence operation have intensified a lot and Doer ganganger uh among others is one of those largecale information operation that impersonates uh news outleted uh news outlet and government website to disseminate uh Russian disinformation. information and this operation they are executed um also by a group of uh public relation companies or private companies. Uh first you have the presidential administration uh which act as a common hub. So they oversee the performance of uh these uh
uh companies. They also oversee the funding. They coordinate with the Ministry of Foreign Affairs so they can uh mobilize uh embassies, Russian embassies to relay the uh the disinformation narrative and uh then you have uh the social design agency uh which is at the core of the execution of um uh this campaign uh of of this operation the doer operation. So what they do is like they manage a bot farm and they uh those are they are the one uh behind the fabricated uh news new news site. Um and then you have structural which uh run more the logistic part uh maintaining the infrastructure behind uh this operation and ANO dialogue which is actually a
nonprofit organization that relay uh this narrative uh within uh Russia and they all coordinate uh between each other. They even have meeting with the presidential administration. So uh yeah really organized and you can see how uh for information operation uh Russia really um relay on uh um outsourcing and on private companies. So now let's see how the Chinese model works. So um we have to start with the Chinese entry into the digital age uh in 1994. Um and uh by the late 90s you had the creation of informal networks of uh hacker collective that emerged. So most of them were actually university students that were passionate about tech and wanted to share um their knowledge
and uh and also train and develop their capacities uh capabilities and uh so they created this this hacker collective. The first one was the uh green army in uh 197 and other group emerged uh during this time. So um this ecosystem was also influenced uh by um geopolitical incident during that time that were perceived as hostile against China. So we had um an anti-Chinese protests uh in Indonesia, the collusion of um recon US reconnaissance plane against Chinese fighter jet. So all these incidents um mobilized those groups and uh motivated uh their attacks. So during this period um there were those groups and the people behind it they were seen as hero. The Chinese state they really
tolerated uh the their activity as long as it was aligned with um uh national sentiment and also with um not targeting any Chinese entities but on uh focusing on foreign targets. But uh this started to change um in the 200 uh 10. So first the PLA started to recruit uh the people liberation army started to recruit some of the hackers and uh finally in 2010 around that time uh the Chinese state discourse started to change. They started to say, "Hey, those activities are actually illegal." And they started to um arrest some of these hackers that had uh the opportunity to work for the PLA in exchange of amnesty. And uh yeah, they also um started to uh
gradually impose more control uh get more control of uh the cyber sphere in in China and every anything that was happening online. Um and around this time so obviously since their action was not were not tolerated anymore. So some individuals the most the one with the most uh technical skills uh they join uh private companies either um leading uh IT companies or cyber security companies or they even some of them funded their own start startup. So we're going to see the case of uh some of them. So you have the first one who hibbo uh was a member of the green army and another hacker group um that uh was an active member and then
um he founded in uh 2010 and uh in February last year a leak uh uncover all the ties between and uh uh Chinese intelligence uh services. So uh then we have Sai Jing which was also who was also a member of the green army X focus and uh he was uh uh really important in that sphere. Um and it first joined Venice Tech uh so a uh state um um affiliated uh cyber security company and then also in 2010 he founded uh his own company uh integrity tech and uh yeah same thing in January this year uh the US sanctioned this company for uh providing ing infrastructure to the thread actor flax uh typhoon. And then
the last one uh the last example is Tan Daling who who actually uh went at university with funded his own hacker group and um he participated to a cyber security competition um and he was identified by the PLA recruited for a training program. Um then he was arrested by the ministry of public security and in 2009 and probably during that time worked for the ministry of uh state security in exchange for commuting in sentence. And then we see him reappear in the private sector where he funded uh um many cyber security IT companies uh between uh 2010 and 2020. And uh in 2019 uh US indictments uh linked some of his firms to strategic intelligence gathering uh activities
against uh dissident uh journalists and foreign government entities. So you can see all these individuals uh that were first part of uh this hacker collective then join uh uh companies that now work uh for the states um conducting uh cyber operations. So let's see a bit of the institution behind uh this ecosystem. Uh so um first you have the people liberation army which was historically the main actor. So they started to recruit hackers in 2003 and uh they were the one behind uh cyber operation at first information and psychological operation as well. But this changed um after the reorganization of the people liberation army which happened in 2015 2016. So this reorganization was due to
corruption cases and uh also uh the identification of um of some of uh its uh the PLA cyber units. So then around that time the state switch it switched uh preference uh for the ministry of uh state security. uh we which has um a more hybrid um uh working process mixing in-house capabilities and also a lot of outsour outsourcing. Um they are actually uh divided in a lot of provincial departments who outsource to uh companies uh with also a sort of um division of task in terms of province. So each province has its own specialty and uh they outsource two companies usually located in their own province who them those company themselves develop uh specialization
um aligned with the the state requirements. And then you have the Ministry of Public Security uh which is the main law enforcement uh uh security agency um in uh in China. So more uh overseeing uh domestic uh issues. Uh so let's see how the outsourcing system works. So um the outsourcing system in China it's the result of really a comprehensive national uh strategy promoting the fusion of uh state and civilian um function. So um article 7 of national of uh China national intelligence law that was passed in 2017 it obliged all individual and organization to support assist and cooperate with the national intelligence effort. So for China intelligence collection is not the domain of the
state it's the responsibility of the whole society. So in practice, this has created a dense uh and highly competitive environment where you have uh dozens of uh cyber security or IT companies um that range from uh uh industry leaders to small and midsize enterprise that complex for uh contracts uh with uh intelligence agencies and uh it's super common in this environment for some of the uh bigger uh companies to contract some smaller companies for some work. Uh so yeah the state contract a big company for uh cyber operation and then this company delegates to a smaller company that will uh do um a niche part of the of the contract. And uh so you have layered of
network of sub uh subcontracts uh and um therefore you have varying degree to uh of ties uh with the state and um this ecosystem is really competitive. Uh and uh this foster innovation because uh each company try to uh come out of uh these uh tenders and wind contract and therefore they're really competitive and they also uh win contract in based of relationships uh that have uh been uh personal and institutional rel uh relationship uh that are established and a specific uh aspect of this ecosystem compared to uh the Russian one is the high degree of uh of autonomy. So some of this company there launched their own uh cyber operation uh saying okay so maybe the
state could be interested in this aspect. So I will myself launch uh a cyber operation targeting um data of entities and then I will propose uh the information to the state. Sometime the state is not interested and sometime it does. Uh so they kind of trying to get the attention of the different um intelligence agency that way and they're highly autonomous and um yeah once in this system they can really conduct a full uh spectrum of uh operations. So what are they offering? So it's similar to Russia but uh the differentiator uh differentiator here is um not hugging for fire but hugging for hire. So and uh yeah they basically perform everything um vulnerability identification hugging for tools and
solution they offer the full package recruiting as well. um um organizing also um competitions where they can identify uh people uh with interesting profile for the state and information operation even though it's not really developed uh at least for the foreign aspect of it in China right now but this is something that uh is shifting so we see more and more um uh Chinese uh information operation, disinformation operation. Actually, I saw a report from Graphika published just this week about uh Chinese information operation um in I think it was in English, French, Spanish uh was targeting a lot of uh different uh countries and um uh basically anti-western narrative and pro-Russ pro-China um narrative. So yeah, this is something
maybe that could uh in the coming years uh develop in China with more and more uh private company offering this services for the state. So now let's see also the risk and benefit for China. So uh in the case of China um I identified a potential risk of resale of intelligence because you have um contractors that initiate their own operation but sometime the reso doesn't understand doesn't interest um um intelligence agency. So either they try to resell to another uh department another agency or maybe they sell it uh on their own. So this is a risk. Um and also uh you have the risk of corruption uh because in this model like I said uh
there is uh all these company are comp competing for uh state contracts and uh obviously they want to have um the best chance of winning this contract. So and in China in this case like uh institutional and personal relation are really important. So this is something that might uh happen uh that is some that there are some corruption in the uh conclusion of this type of contracts and then obviously you can have risky behavior because when you leave a large uh autonomy to this company to conduct their own operation against the targets of their choice obviously this is uh something you can have um consequences that are unexpected. in sometimes contradicting uh the state uh objective.
But uh once again on the benefit sides uh you have reduced costs uh large flexibility and also because this environment is super competitive you have a lot of innovation uh that you would not have uh um inhouse and same uh as uh Russia actually China always denied any involvement in cyber operation. So, uh yeah, once again, I don't think plausible deniability really matter to them. They don't care. It's just an efficient model uh for them. and okay uh for let's see a case study of how um is structured and regulated uh the Chinese model uh for uh the vulnerability discovery and exploitation. So you have a loop here that begins with private cyber security company and research entities that
organize um uh capture the flag competition uh and they discover vulnerabilities uh or they develop their their proof of concept. And since 2018 uh the participants to this uh competition they are legally required to submit any newly discovered vulnerability exploitation technique to the ministry of industry and information technology uh before public dissemination and since uh 2021 that any discovery uh of uh vulnerability must be reported to this ministry within 48 hours. Uh same for the proof of concept. So basically what we all suspecting they do is like they exploit this verbity uh do not uh make them public before uh laps of time so they can fully exploit them and uh then they uh notice the vendor or the vendor
uh itself found out. Um so once it's submitted to the ministry of industry and information technology then it's back to the intelligence agency. So either they exploit it inhouse or back to private companies. They uh delegate uh the exploitation to these companies. uh in the isudin leaks uh you can see that uh they are talking about um some proof of concept but it has they didn't have access to it yet so they're waiting for the Chinese government well the Chinese uh intelligence uh services to give them access and they hoping they will get access to them uh through u some contract. So this show how the Chinese model is highly um organized and uh incorporates
uh uh private company like outsourcing is really part of the model there. Okay. So now let's compare uh compare those two. So um in both countries um you have the use of private companies. Uh in the case of um Russia the degree of autonomy is medium low really they do not delegate fully uh uh cyber operation uh to um private companies. In the case of China, as we just saw, uh they do heavily um activist group uh in the case of Russia, they do we see that they do use it. Uh in China, it's pretty unclear. Uh so we have we kind of observe some uh activity that could be activist activism. Um like for instance when uh the US House
Speaker Nancy uh Nancy Pelosi went to Taiwan there were lots of DDS attacks um in reaction of uh uh these uh visit but it's something really uh short-lived and also uh those group if they exist they are not really vocal so we they're not like the pro-Russia one uh have they have their telegram channels with for each action they do they claim it and they make tons of it. It's not the case for China. So it's really hard to um know if there is any activist group and if they actually uh work with the state in terms of independent hackers. So we saw that uh Russia used it but for China uh it's the same. We have not knowledge
of um China uh intelligence agency resorting to um uh er groups or independent hackers. they are more more likely to neutralize this kind of group and uh recruit the interested uh the interesting profile out there rather than um collaborating with them and in terms of information operation. So uh Russia is really focused on foreign inter uh operation uh information operations. So targeting uh mostly European country and um as well as the the US but yeah mostly us and uh China um they right now they have more uh focused on uh domestic information operation in the province that are um more problematic for them. or in Tibet in um in uh Sang. So this is the kind of
uh province where they have just um information operation and also targeting Taiwans, not really fully domestic but yeah and but as I as I said before this is something that is uh likely um that will likely change as we see China more and more interested by information operation uh uh targeting uh western uh audiences. So uh where does that leave us? Um the externalization of cyber capabilities by China and Russia are a functional and effective model uh that allow both state to enhance their reach and control the costs. Um and this system is really effective in authoritarian uh context because these governments they have uh limited domestic uh scrutiny. They can operate uh with minimal transparency and
accountability. In our our democracies, that would be way more complex to uh fully outsource uh our capabilities to uh private companies or obviously there would be more scrutiny and way more uh problematic to resort to uh cyber criminals. uh um and in such environment attribution uh uh for uh cyber operation has limited uh deterrence value. So yeah, they don't care if uh they uh we identify that this company um engage uh in uh cyber operation against uh western um uh companies. So even like those companies especially in China they have been identified but they're still running like this is not an issue in China to have been identified as um a companies operating malicious uh cyber
operation against uh western targets. So this model works and it's probably continue to develop and we have now also other country that are developing this model. So recently uh in July uh there were a leak uh uh that uh highlighted the work of an Iranian companies uh that um provides services uh for the Ministry of Intelligence and and Security uh in particularly uh AP39. So yeah, Iran is probably going to replicate this model and uh uh that way um trying to enhance its uh cyber capabilities. So yeah, in the middle uh long term we'll see more and more companies providing this kind of uh of services and this is an issue because we have bird lines between states and non-state
actors and also it's difficult to um determine if um cyber operation uh is state related has been initiated by the state or has been endorsed first afterwards. So in terms of attribution, it's it's really um complicates our efforts and also in terms of anticipation um uh they it's harder if you don't know who's behind um and the motivation of who's behind the cyber uh attacks targeting likely to target you. So in terms of uh analyst and cyber security expert, we need to um rethink our framework and uh to or analytical models uh to explore uh new framework to keep pace with uh the outsourcing model. Um there have been um interesting initiative this year. Uh so
Talos intelligence they propose a relationship layer uh to the diamond model to keep track of um the growing prevalence as of as a service model which is in part kind of similar to the outsourcing model uh in the crime environment. So this is maybe something we can reuse um in the analysis of um state sponsored or uh state uh endorsed operation. And that's it. If you have any question
>> Yeah, I hear you. Okay. >> Hi. Thank you for your uh presentation. Very interesting. >> Um so those uh China private companies Yeah. >> mostly. Yes. >> Which are providing services to the government are the main like purpose revenue are coming from the private services or they are actually working mainly for the government? >> Mainly for the government. Yeah. >> Okay. So that's why they really compete for these uh government contracts and they need to differentiate themsel being super innovative and also it works because um like I said like large companies they sometimes um delegates uh or subcontract another company to do part of the work. Um and also China is huge they conduct lot of operation. So
for now this model works. You have about of a dozens of company that have been identified working in this ecosystem and fully like they do not provide really services for other private companies mostly they provide services for intelligence uh agencies. >> Yeah I'm asking because there should be a lot of intelligence already in this area right? Yeah, I mean it is uh I mean I think we're only uncovering the tip of the iceberg of what China is doing and uh the operation they're conducting and uh like right just this week we have s typhoon they um uh kind of like western uh intelligence agency identified they have been targeting uh uh telecom communication companies in
over 80 countries. So yeah, there is a lot of work for them those companies obviously. >> So they're busy. >> Yes. >> Um thank you for that. So we have um a lot of Chinese companies and to an extent some Russian companies, private companies that have customers from around the world. we're talking uh prior to 2022 Kasperski and Ki who Skylar or even stuff like Tik Tok. Um is there much evidence of them collaborating with the their governments um and misusing that trust that um people have put in them and what can we do to uh deal with this? So a lot I would not say there is a lot of evidence. Some companies uh yes they
have been identified uh having tool uh having ties with the states um which are not always um in um like like I said they not always engage in malicious directly engage in malicious activities. uh so um they can sell uh some tools to the states but then they're not fully responsible what the state do to uh with these tools um then the issue is more that they are required to collaborate with the state like in the case of China it's super clear that if at any point uh a Chinese intelligence uh service uh asked them to um collect information on their user or customers to the benefit of the state then they have they are required to do
it. So this is the issue. Um to be fully honest, it is also the issue with US companies because they also required uh somehow to uh pass on the data uh if requested. Uh and what can we do? Not sure we can do much. Uh I think it's important to know it. Uh it's important to um have uh for the best of our ability um if we can European providers. Um but yeah I mean we are in a globaliza globalized economy so it's really hard to uh limit ourselves but yeah uh we have to look our our supply chain uh and make sure uh we can we do the best with it and we limit uh the the risks but uh
yeah it's it's difficult. >> Thank you. >> You're welcome. Um, thanks for the talk. Are there any leaked government contracts from Russia or China? >> Um, full contract. Um, uh, yeah. In the is more uh conversations, some bits of contract. Yes. Uh, they exchange maybe more of a subcontract. Uh but uh um not sure I've seen full uh contracts uh out there. >> Thank you. >> Welcome.
Maybe a silly question, but um uh based on your report, would you say the most what would you say the most common initial access factor is for China and Russia? the the most >> uh most common initial access like would you say that uh I know that Russia likes to use fishing for the most part but sometimes they'll use u exploitation through let's say vulnerable services or uh for uh face and applications but it sounds like China based on your report likes to use um recently discovered vulnerabilities or um like CTF challenges to find new vulnerabilities and withhold that information. But if it was a public disclosed one um they would use that. So keep an eye out for that is
something you want to >> Yeah. Yeah. In the case of China they're like CVS like it's um >> it's what they aim for. They have this old framework that is designed to uh find them and exploit them as soon uh as uh they have been identified. So I think this is pretty something uh you need to look for uh CVS and yeah uh patch as soon as possible and at least be uh aware of it because this is something like really uh for at least for the one that are out there that are public knowledge uh it's really important to be uh very reactive but I think even ime actors are super attentive to what's
knowing uh what's uh going on with CVS and how they can exploit it. Um yeah, more and more groups even ransomware groups are using those uh right now.
Thank you. um for the for the creation of such profiles. Do you also do this for western based um entities >> or like all over the world or is it like limited to >> you? Uh by profile you mean predator profile? >> Yes. >> Yeah. This is actually an issue. Um I think like the O industry we have a lack of uh of yeah of sight on what western actors do and we like for sure they do but uh this is something also because we assume that we are more of a target for um actors such as China, Russia uh uh but yeah things can change and and I mean without even coming to thread actor I mean we know
like uh um with the Snowden leaks that uh the US for instance doesn't need uh thread actor or uh cy to uh conduct a cyber operation to collect our data. So but yeah this is something uh that the industry and yeah ourselves as well analysts should do more trying to find out. Um I think Spanish one was identified uh this year uh but yeah I have no knowledge of other uh lately. >> Thank you very much. >> Welcome. >> Okay. Thank you. >> Thank you very much.