Are you content with our current attacks on Content-Type?
Show original YouTube description
Show transcript [en]
hello everyone uh are you content with the current methods of content type attacks we' like to talk about a new attack Vector for browsers using content type if un unexpected path exist for danger to enter your protected areer uh what you you do perhaps like Attack on Titan we discovered an unexpected attack vector in uh in browsers this attack path can lead to several vulnerabilities uh big one and being xss oh now on to self introductions I'm a Mor please call me a I take care of uh web penetration testing and smartphone penetration testing at the Japanese cyber security company a FR security hi I'm noro but please call me Azara I take care of web pention testing and
croud peneration testing H and also R security Inc okay there here's today's table of contents yeah first we explain content type next we'll explain uh the old attack vectors and show how HTTP responses were difficult to change after that we will show how the new attack Vector we discovered makes it easier to change HTTP responses then we'll show some deficiencies with some uh with back Bounty problems and OSS using this attack pass finally we'll present the
mitigations okay now let's start uh start by explaining what content type is content type is one HTTP response head does that indicate uh the type type of data being transported this arows web browser to H correctly recognize the data type and process it appro appropriately for example content type image SL PNG is interpreted and uh image in pnz format and another another example content type Text slash HTML is interpreted as an HTML document but can the HTTP response content type RAR be rarely be trusted to illustrate it uh whether the HTTP response content type can be trusted Let's uh let as a first review the old attack pass until now it has been difficult to change the HD TP response
content type this is because in order to include malicious data in in the content type uh the malicious content type must be included uh with the files that in is uh being uploaded under the middleware and application validation uh validate the file for example file extension content type and Magic bite and the application returns a validate error okay however with the preparation of AWS and another cloud services H the pr upload mechanism itself has uh itself changed oh sorry the change in the mechanism include how the HTTP response content type is 100 recently object stage emerged and is incor increasing being used uh used to upload file upload files H object consist of binary data and
metadata and the object h can be made to store content type as metadata now now it easy to change the HTTP restance content type this is an unexpected attack pass for browsers this example is an approach to object Str this is because sdks are used to upload file to uh object stage however for some reason uh developers uh tend tend to forget uh about content type validation it's which they should have done before uh how have because they think the that the SDK H will do it for them and arbitary content type file is uploaded as a result arit content types uh can be stored in object stret as metadata okay okay um we believe that many
developers are aware that they could specify any content type as metadata in object stret and that they trusted the http responsee content type unconditionally we then searched for this vulnerability in back Bounty program and Os we investigated uh one ban program and uh found found one uh unverified S3 it caused xss though we couldn't escalate it into a more critical expl uh we had um uh we had verified over 100 products but other other than one all were uh either not using S3 or how to Accurate verification we suspect the reason for this is that companies that do bug bounties generally do not benefit uh from using microservices like F3 so we decide to investigate the
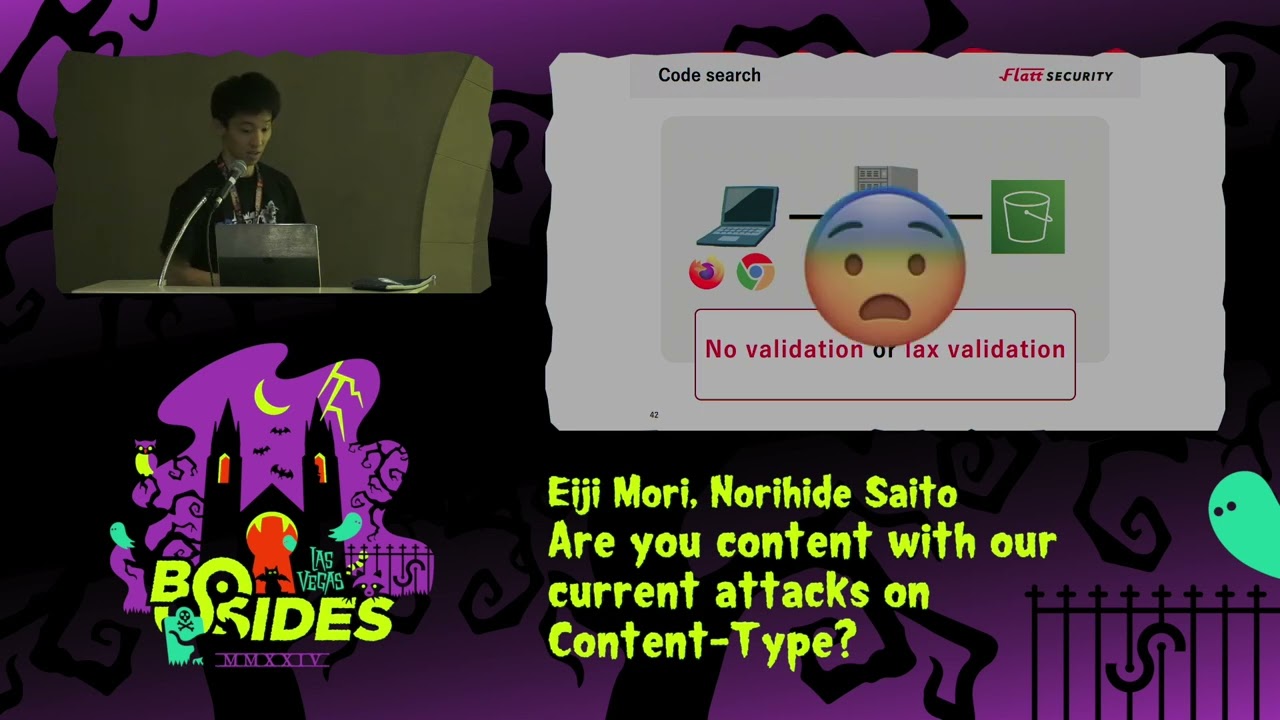
osss let's take a look at uh the result we did a simple code search we set the language to JavaScript or typ script and set the uh directory to be under s slash we got over 4,000 hits although we only looked at well-known products as expected most of them had no validation or La validation now um it's a pattern of uh validation Bypass or no validation pattern but uh it's a all calls are presented here after were dummy Cod okay it's uh uh in HTTP response the server has no validation in HTTP request okay um in one product the content type received from the browser on the server side was passed directly to to the object
stret as a result any content type could be specified in the HTTP response although this is a simple implementation in terms of code we had encountered many search patterns this enables xss for example the M type is uh a content type and uh put object uh like a diory M and another example it was just barely okay with web application firewall where uh there is a potential danger this is because the validation is frontend only so the validation can be easily be bypassed using proxies such as buob streets since the content type of the HTTP response is not Val validated there is a possibility of xss in the future if object s is specified as uh the fetching destination for
example you can upload text/html it calls accesss next um in HTTP response the server has no validation in HTTP response uh from especially S3 here is an example from uh vs extension which may allow uh rce from xss uh depending on the configuration uh why there are actually no problems in practice currently this product uses HTTP response content type as is so there does exist a lurking problem if object s could be specified in the future um xss to rce could be possible in this code content type of HTTP response is used unconditionally example um response. headers doget content type directory so um if get text/html it calls xss next um validation bypass pattern in HTTP
request even if there are validation using content type string where Manish file is uplo it they are often easily bypassed due to a lack validation such as starts with ends with and resists uh in Cru you can see the document uh presented at Biz Tokyo for more information on this bypass technique um let's look at bypass technique example carrier wave is most famous file approach library on Rubi on Rails carrier wave had a problem uh with a content type restol logic that could be uh bypassed so any content type could be specified in the HTTP response this vulnerability has been fixed at this time okay um uh this is a allow list for content type
for example you can see uh image/jpeg and image/png only and uh this is a logic to generate a regular expression based on that allow list car waves a Content connect the two CES in other words a content type regular expression is generated from the final allow list however this can be bypassed as we we have just shown for example you can bypass image/png comma t/ HTML next uh in http response even if there are validations using content type string where Malicia file is downloaded especially F3 from F3 they are they are often easily bypassed due to lack validations here is an example from electron electron may be access to rce capable um depending on the
configuration in this product xxs was at least possible due to the LA content type validation of the HTTP response for example the validation have a content type dot start with image so you can bypass image/png comma text slht ml this is an example from a Chrome extension xss in the Chrome extension has stronger permissions than normal xss it was just barely okay and has no problem but there is a potential danger it can bypass text/html semicolon PDF due to the lack uh determination of PDF in the HTTP response content type that is um you can have HTM render that uh looks like a PDF uh which may be a hit if you have a PDF sniffer turns on for example the
validation is content type dot ands with PDF so you can bypass text/html semicolon PDF so then a question of course is how can we mitigate this problem be sure to verify the content type value with an exact match to see if it is the intended value for example the content type string equal to um image slping or image/jpeg in addition do not unconditionally trust the content type of the HTTP response but verify it with an exact match thank you very much for listening to our talk thank you yeah uh here are differences for those who are interested yeah and the S3 and the content type research and the car wave cve and um if you would like to see the
slides on your phone please ask the QR code here and that's it uh thank
you question M any question all um if you have any questions um I we uh we remind in a few minutes please ask ask ask ask our okay
um thank you for a great presentation could you please go back to slide 75 I think where you had two content types uh 75 sorry 75 uh it's far 75 75 okay yeah oh sorry uh went back I went back okay so when the browser yeah when the browser sees uh text/html uh semicolon PDF are you saying that um the document is going to be treated as uh text HTML and the PDF part is going to be ignored did you test out uh um it's a yeah like you mean uh it's a like a like a weird content type mean uh yeah but uh yeah of course uh it's a weird uh content type value but uh uh
object strange can
OB stage can set set up this uh uh content type as uh uh metadata okay uh but uh do do you know what's going to happen when browser will see this will it render the document as text HTML yeah that's right okay yeah thank you thanks
all right thank you very much yeah thank you