Kyle Howson: How to build a Security Operations program

Show transcript [en]
so my name is kyle hudson uh so excuse my passion been here for about 15 plus years i've been a consultant penetration tester uh network security blue team bunch of different uh fields and different things um more recently i've been doing some talks and i got a few of them up here um so uh connecting the dots which is one of my first ever talks back in 2018 uh 2019 and then 2020. um we'll also have a little bit of overlap in some of these but this talks will be different than some of my other ones a little less technical a little bit more on getting over what i'm going to call the writer's block that we run into a
security operations all right so when we talk about security operations there is a number of things that we run into and i wish i had the image up here but the one about everything is on fire we have alert fatigue we have lack of context um our instant response has you know we're not seeing the full thing we're blocking the mains and not you know dealing with the malware on the box that wasn't detected and we're not able to connect these dogs very very well at all um and so these are sort of the challenges that security operations are uh dealing with day in and day out and you know as you start looking at this i
have some stats for you on the next slide you know some security operation centers um in 2018 we're reporting over 10 000 alerts per day that's insane um there's no way to keep up with that and so the more and more i gave these talks the more and more and stuff uh more and more times we had this conversation with different organizations um we ran into this conversation of all these things that we're doing is cool the thread actor profiling the connecting dots some of the intelligent stuff we'll talk to a little bit later but um you know we don't have time or we don't know where to start or how we're going to do this
and that comes from this over excessive alerts and are some in some ways legacy view of how we view security operations and security learning uh for example these are some of the traditional alerts that you'll see from the sim um you know ips high severity event what does that tell us right do we need to investigate those and if that's like fifty five thousand five thousand times in a day what does that really do for us from a security operations perspective or even at an investigation perspective so we start looking at all these types of defaults alerts alerts that we see out there we start seeing that they don't provide that context they're gonna fire
thousands and thousands of times and we're spending our hours sort of spinning our wheels and not really focusing on you know those alerts or the security the things that will actually help our security operations team um so as we go through this we're going to talk about those things that are more like the you know writer's block because we're always on fire we're always you know we have ten thousand dollars to deal with when i go and do these thread actor profiling connecting dots begin that same sort of cycle we can't do that we don't have the tools to do that so hopefully as we go through here that'll make this a little bit easier
then this great thing came out called friend together and it was supposed to help the problem right so friend john just came along said hey we're going to tell you what's bad in your network all these other attacks that people are seeing it's supposed to help us tell us who's attacked us and how but what ended up happening is we've got the more data that we're ingesting and what ends up happening is you start seeing screens like this so we look at this we have 15 million new indicators in the 90 day period we have 112 000 sources or 112 sorry different sources and over 102 million total matches so now we've got 10 000 today and now
102 million uh matches of threat intelligence what does that mean to our organization how are we supposed to handle this did we actually do anything better with friend intelligence are we just adding to the problem right so here's like uh you know the funnel of jackie chan like what you know we bought all this threat intelligence we bought all these tools but we didn't really solve any problems um so as we keep going through this and going through security operations hopefully by the end of this talk we'll start talking about you know how we use sort of pivots or the mindset or how we think about security operations just sort of answer these questions we're not looking at 10 000 words a day
and we're not looking at 102 million matches and going what are we supposed to do with this what does this mean to my organization how do we make this a little bit more um relatable all right so lovely things here and we'll sort of go into some modeling all right so with all this information overload now on top of that we get these things called like attack modeling or threat models or whatever else you want to call them we have a cyber kill chain on the right and the dominant model on the left these are really great tools both of them are excellent for different things that we can use them for but once again we've added more data and
we've added more things to do but you know how does this relate to what we're seeing in our sim how do we know that this domain match is part of this you know side of the kill chain or that this infrastructure is part of this actor when we don't have any of these things sort of tying together so now we have all this data and we're learning on everything but we're kind of sitting there going like huh so i get the c2 alert i see these dgas i steal these things but i really don't know if that means it's a real c2 um did i match the behavior to it now i'm going to investigate it they've
got to take all this data and somehow fit in these models to try to discover what actors are doing right and so we start going through this over and over again and you start getting this sort of that sort of hamster wheel where we're kind of chasing ourselves around we're never getting caught up we're getting burnt out and everybody's going like we can't do anything more you know threat intelligence you know sucks we don't have a way to do it all we have is another feed uh so one of my other talks that i did in partnership with one of our sponsors here ion and anomaly um talks about you know how we tag intelligence and we'll kind of go
through it's like a very brief moment of that but how we start trying to connect these dots and building these frameworks um so the next one here this is going to be a little bit interesting so we're going to take something uh my background is in networking uh my schooling was so we're gonna talk about a little bit more networking a little bit about the cyber kill chain and trying to merge the two together to sort of build an investigational alert framework um so you start mapping out these attacks so from another perspective if people aren't familiar the osi model here on the left talks to how a packet or how data goes back and forth between a computer
and the really key point is these arrows on the left-hand side and the right-hand side to go down and up and if we take a look at this model and we see how this sort of works and saying like hey you can't have a dating link layer without having a physical layer and you have a data network there without a daily data link there and we started mapping that out um and then you know i chose cyber kill chain um i called the attacker life cycle cyber kill chain but you can use whatever you want and sort of instead of taking let's say like lockheed or the diamond model to say this is what the cyber kill chain is we
took this model because it had seven layers instead of the usi model kind of worked out for me on that inside of that and started mapping out what this meant to our organization right so when you say like reconnaissance and on the top here i've noticed just as we're doing this talk at smb twice um but we look at this say like reconnaissance so who's scanning your network who's port scanning you who's doing smb scans what are we like what are we looking for the reconnaissance layer what would that mean from my network right from a weaponization there we look at vulnerability scanning right so we look at hey you know who's scanning because again
it's starting to build the build the exploits i can't watch somebody at their home right the cve to write the exploit code but i can sure see on my ips signatures and how many signatures they're hitting what they're looking for what they're trying to do on my network and you know as we go down it goes you know different ways again from an external perspective you're going to see things like reconnaissance weaponization and exploitation in sort of a realm you won't necessarily see delivery whoops sorry guys hit my mouse button there um so what you'll see is you see recon incense you'll see you know weaponizations vulnerability scans and then you'll go right into like
exploitation where people are getting cbes on your network your ips rules uh but you just have guys they're scanning your network for one cv or one vulnerability and then you have other guys they're scanning 20 of them which is more like the vulnerability scan more send as many packets in as i can hopefully i'll find one of their systems that are vulnerable to this and let's hope my ips hasn't bought that right um so if you look at it from that perspective now we start mapping this out right so saying like hey so if you see my somebody scan my web servers and then they go away and i have this in one of my other
presentations but then you know sure enough i was at last week web logic had a new remote remote code execution bug sure enough they have this here well what happens when they see somebody come back and that's all they start trying to target well i've already seen them do the reconnaissance and now i see them sort of escalate to that exploitation phase because they already know what they're looking for and they're just looking for that code execution that vulnerability my network and so you can see some of our rules all of my other presentations we have rules to say thread actor escalation rules we'll just say c guys went from recon to weapon weapon recon to exploitation or weaponization
to delivery or whatever you might see in those different payloads there but you sort of see them moving down that payload because i know that they're not going to necessarily just break into my network um especially not the advanced attackers nobody's just going to come in one day and say i know where your web logic is and i'm going to hit you here there had to be something there and whether it's the same ip the same asn the same type of activity usually you can start building up these infrastructures um that's a different talk that i give but um a little bit further um on the other side of the fence from an internal perspective we started
looking at things like delivery installation c2 and action objectives and the reason that we sort of skip over exploitation is because if we could actually detect exploitation stop it we wouldn't be here today because we wouldn't have an hour and salt or anything else right so what we usually do um and sort of in one of my other talks as well as we go from delivery installation um c2 and once we find that installation where that memory or that malware that was dropped then we can sandbox it and find the exploitation method but from a learning perspective you're not going to see it right um also an exploitation you'll see the cred stuffing where people get um you
know the passers phrase the cred something attacks against you um and in the same model if i have an alert at c2 i know that in order to have c2 on my network something whether in memory or on my computer had to be installed if something was installed on my keyboard it had to get there so now i have delivery so from a security operations perspective especially when you're trying to like go to like a level one or someone maybe with not as much experience and say this is how you investigate and remember we didn't like say to see the full breadth of the attack i'm going this a little bit later when we show some sample alerts
is that if you see an alert at c2 you now know that you have to look for an insulation and delivery same way that you've seen actual objectives you see somebody running the fan net group domain events well guess what that person might have c2 on your network that had to be installed and then had to be delivered right so all those different phases had to happen for action objectives to occur this is sort of the framework of starting to investigate it and not at an organization-wide level but even at a host by host level just like the osi model right so on each computer you can walk through each one of these phases all right now we get the fun part of how
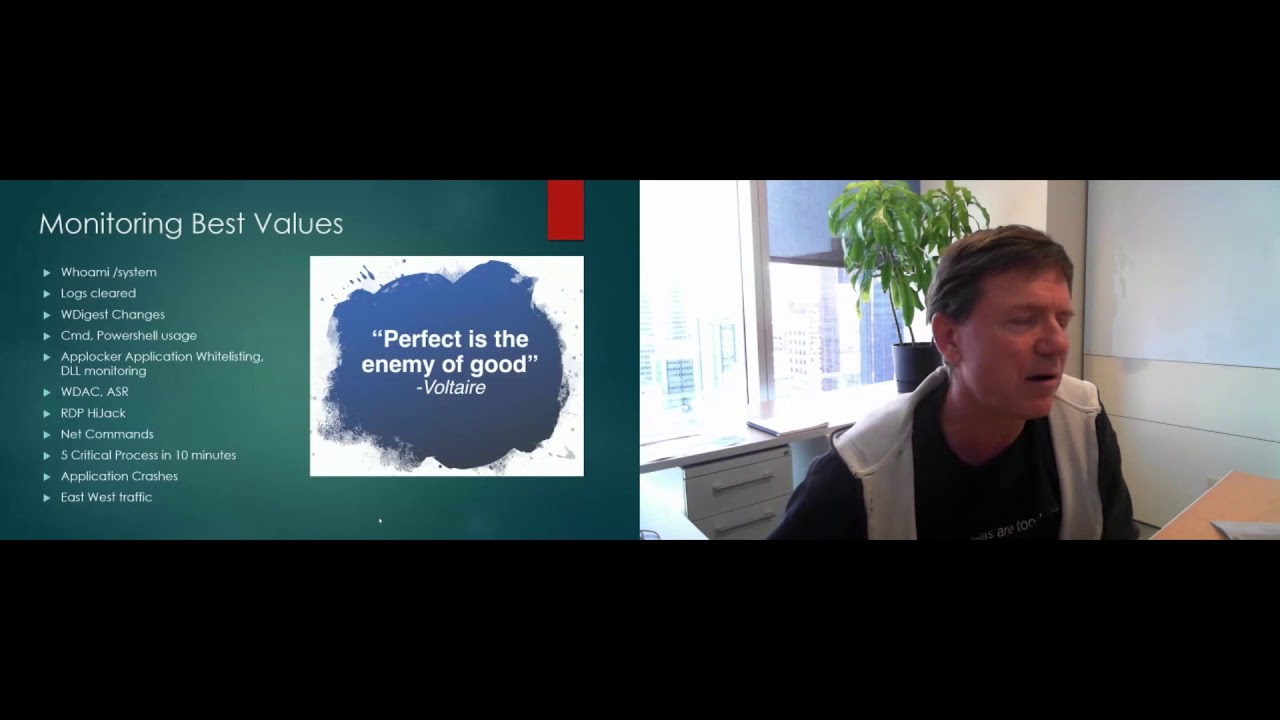
do we know if we're learning on the right things right so um talking back to that mindset we're trying to talk about today is um if we're trying to figure out as for this kill chain everything else where my alerts sit we need to first assess from the model what we're saying we're seeing and where do our alerts map out and so we can start going through alerts and they don't have to be named whatever else but you can start grabbing which logs which sources and which types of activity is really important to you for example if i'm at let's say where i'm at today enter canada we're not really concerned about ics or modbus or things like that
but in one of my previous roles modbus was a very important thing when people scanned it that was something that was very important to us so depending on your reconnaissance what is uh managed to organization you start walking through and mapping out all your rules one of the log sources in a very simple spreadsheet and you start seeing what you're tagging or what you're not tagging and actually write the rules identify those gaps whether it be that you're missing packet captures maybe you don't even have the logs well that's great but that's a huge chunk of visibility that you can start focusing on now because you've mapped it out um just more examples of this for
example we have this one here insulation logs and packets this one here is specific to let's say ransomware we have nothing here because we don't have those logs or we don't have anything here because maybe we don't have packet captures maybe you don't have this this is how you start mapping out where you're trying to find um in your network those alerts may or may not fire and sort the diagram so once you do this and once you go and start doing this a little bit more um we can start seeing from here we can actually start mapping and renaming our alerts to exactly that kill chain model um or attack your life cycle or whatever you
want to call it um we start looking at where our alerts are actually firing so that's great delivery great microsoft office powershell well if that happens we're probably going to look for installation after if we have virus from removable media and i know it's on there twice um we're going to start looking for who plugged in that usb what is the serial number etcetera etcetera for maybe assistment log and then the url we can sort of send box to go from there same sort of thing from the c2 level we have beaconing firewall detections whatever it may be there all right how does this start to look when you put it together so when you start taking this together
and start mapping this out you can actually start taking your alerts and uh i know it's hard to see and i see some common felt glasses and seeing on there some of that's on purpose some of that's not uh but you actually see that we have let's say a kill chain phase and we have a minor technique that are mapped to all these um so i didn't want to go into um too much about how i did the miter and cyber coaching mapping i do that in a different sort of talk that i give but you know when we start listing these alerts off and where we're seeing the stuff we can actually start seeing like on the
bottom here an actual phase of where all of our alerts are firing as you see we see exploitation credential attacks maybe uh logging in from iocs or we see like a lot of c2 and beaconing type activity what could be causing that and there's all different a bunch of different causes and things like that but you see well huh these are two major ones this is really smaller smallest one is actually objectives or edr alerts that's a good thing right you want to see less down here and more at the beginning stage of this attack cycle but again 193 and c2 is a little bit high what does that mean okay let's go take a
look at that maybe it's illegal streaming media maybe it's crypto mining what other factors can we book and depending on these alerts you'll actually see what they are but as i said but as you start mapping this out this gives you a very clear view of exactly where you're trying to go what you're trying to see and sort of you know um sort of that holistic view of okay where am i seeing all of my alerts if you're seeing a thousand alerts at installation but you're not doing anything about them why are you seeing so much malware right if you're seeing that much malware what email filter what web filter what other things are being bypassed you see
all that now on your computer are people just running around with usb drives these are the questions that you can start answering for your security operations for your management and even higher on why or where you're seeing most of your alerts everybody has a little comment so everybody installs malware great but at least i can now use this to write that story all right so that's what have been sort of the sort of the alert stuff and i'm removing some threat intelligence and go from there i'll answer some questions a little bit there i see your question there rod um i will focus on that in just a second here but uh let me go through a little bit
more of the talk and we should have some time at the end there all right so from front intelligence perspective um we do see that there's lots of platforms out there um there's anomaly which i know that uh i'm trying not to focus too many tools but there's some that are really good they can all mean others but there's recorded future true star threat connect uh but a lot of times you buy these feeds or these you know products that say i'm like fighting sort of said hey all these vendors promise the world just like that threat intelligence fee of 100 million matches of indicators is it really providing us what we need right if somebody keeps on telling you
what they're doing what does that mean anything to your organization or is that not and we're going to how we sort of provide feedback into the intelligence loop but this is how we start building sort of that framework for how we know what we're seeing and then what we're seeing and how we can alert on that um so again what are the requirements that you need if you start looking at this is it just our feeds can we call can we tag those same feeds and record a future with the email that said us malware what if it's a different malware that we saw then they saw from crowdstrike okay that's great but how do i provide
that feedback in so i know what they did to me last time not what i did to the rest of the world right and started building up this context and i said we do this another talk it's down here um it's on demand so you watch whenever and i'll post those links so we tag and i don't want to spend a huge time on this but we'll go over some examples of why and how we tag um so in this one here uh this top screen is all sort of the indicators that we start tagging in my network uh though this is recon because there's five of them is a little bit harder to do this than the others
as you see the other ones come up when we start looking at recon we started saying like rdp's three con sweeps huh well primarily you know other than the us and maybe some shared services russia seems to be know you know most interested in there whereas web is always going to be u.s uh but smb suites huh vietnam that's interesting and db scans well 62 are coming from china based ips maybe that doesn't tell me who an actor is but once they start mapping this out i can start worrying about let's say you know as you see our alerts well if china ever has a successful connection into a database there's something i can do why do i know
that well they're the ones that are heavily reconning it so that's where i'm gonna start to get concerned right we started answering that angel question what's hitting us or why and then we start building out sort of or that kill chain or the alerts or the friend tolerance around that and as we go down we're gonna show some of the different things we tag so from a vulnerability perspective you can see we have cves the name of the alert and the indicators that pop up we can start seeing delivery researching emails that have sent us malware the links the subject lines excuse me even hashes that have sent us stuff now when i think about the delivery
that's very interesting um just like um ken and a few other people talked about and even jason maynard some of his other talks were like hey you have all these malware alerts and it says oh well i've blocked it we're okay understanding what you're being hit with is just sometimes as important as what's you know getting past because how do i know if it gets passed if i haven't done that so for example i will take those emails and knowing that they sent me a phishing link or malware yesterday my alert will say now that i've tagged them if they send me an email that's successful alert me you know why yesterday i have proof and i have evidence
that these guys sent me malware or a fishing link so either they were compromised they're still compromised but that's how we start building out sort of that list um same with these hashes we can start seeing hashes installation some action objectives report numbers or the names of the files and then even behaviors that they're starting to do and in future talk we can actually map this out to miter on automatically but that's more of my sword talk that i'm building for later on this year but you sort of start seeing how we start tagging these over and over again and we start to build these patterns right from these same files we can now automatically tag all the c2 domains
and you see the confidence levels associated the documents and hashes associated and so as you start mapping that out we start getting into these um very pretty sort of graphical ways to represent these attacks and start seeing the overlapping indicators right and then again what i'm seeing so if i'm seeing a bunch of emotion in my borders when i start looking at what alerts are firing my network or what should i have in there guess what's important do i have rules that would detect that emo ebook landed on a computer yes or no do we know this i don't know but let's go see that let's go see what emote ran let's sandbox it let's go look at
our threat intelligence tools and let's go back to that whole thing uh where we mapped our cyber kill chain and our alerts and our intelligence and everything there see can i actually do or see this am i looking at this do i know that they're sending me this and if we don't have rules that are watching what's getting blocked in our mail filters what's getting caught in our antivirus um with being caught in our proxies going outbound for downloading network we're missing all that data how do we know what might actually make it through um so that's sort of how we're going with this and then we'll go into how do we do this all right so this is
sort of where we get a little bit technical a little bit more detailed and we'll actually show some examples of actually how to start doing this we already have most of data in our sim okay and the ones that we don't have we can add or at least we can identify as a gap let's say you don't have antivirus songs right or you don't have cis smaller on your computers yet that is a finding that you can do that mapping exercise we had previously but at least now we have this here so you don't need a store we don't need to say that hey how does all this cool stuff we know these cool things that this company does
over here we can actually start today with all the information you currently have in your system um any sim can do this they can write a csv file um and we can start today um look at your firewalls emails edr logs um so at the bottom we use this example of an rdp server suite so what we're going to do is we're going to look at all the different source ids that are not internal that are scanning for port 3389 and are greater than 800 unique systems unique destination ips so does that tell you somebody on your border has actually hit a firewall or an address range in your network and they try to get to 339 over 800
800 different ip addresses that's reconnaissance activity right for you might be 500 your company might be smaller it could be 100 but you can play that number for 800 1200 whatever it may be and gather that list right once you have sort of this list you start getting and this actually lies you can see the exact same rule right up here grabbing sort of those indicators and that list of different computers that they're scanning low and behold if you look at this here there's russia as one of the top ips if we go back to the recon tab we had a couple tabs back there a couple slides back who is more sister than rdp oh yes you
is the russian-based psyches we have two of them in the top three so then we start seeing all these ips and then we go okay well now what we do with them um i do apologize i'm going to use a commercial tool in the demo there are missed and uh oh uh some open source tools that are getting there but um having something like a normally or a thread connect or something type of a tip like that will really help you start mapping this out but we take that intelligence and we export that to a csv it's that simple of just grabbing that grabbing list of ips and then you can manually copy and paste
that into whatever platform you have miss whatever else and apply your tags so if you see at the bottom here reconnaissance rdp suite yes this is going to be manual if you don't have a sore you don't have some scripts um in our next iteration of this so this is the first iteration of threat intelligence saying in the next one we'll go into how we can semi-automate it and then fully automate it uh but as you start going through this that's how you start building out those rules of what hits there um as i said i'll answer some questions but yeah using proxies is very very interesting and we can actually start mapping that out as well um i don't if
we have time in the end i'll actually show how we've done that um all right so the second iteration all right so now we want to automate this a little bit more because getting emails from your sim or um you know let's say going into a tool or miss but doing that automatically can be time consuming i will admit but again the value is there so what we can do is you take your sim send an email or an ssdp of this csv font same exact thing but i've already got sort of the i type which is an anomaly thing the tags that i want to put on it and the values you uploaded to computers so for the
first little part of this when i first got here we didn't have a sword platform we didn't have this so what we did we just emailed an inbox every day and we had like 12 different emails you put the csv files in a specific folder run python on this script and it upload up to our tip platform and suddenly we were able to take all these different things um so you can do this you don't need a store um you do um one of my previous roles we even had this sftp off to a unix server unix server run that python script on a cron job after it was done and delete the files and this went on every single day
kind of like your performance or what you know source is doing right now but make it a little bit prettier to look like
all right and then the third iteration of the fully automated you can make pretty little playbooks like this one and make them very modular where you can start doing the ssh rdp web server database and smb and as you can see they just go in and run um so as you start doing this there's def definitely different iterations but you don't have to worry about not having this cool screen right here we can start doing it right here or even right here from a file in this or anomaly whatever else i start taking all this stuff today and we don't have to necessarily have too much there and i mean that first part of this is actually starting to
measure yourself and understanding where your gaps are and it's okay if you don't have the long stay it's okay if you don't have them tomorrow but at least if you know where your gaps are you can go and say you know what i don't give any logs in my swim so guess what i won't be able to see that great well if somebody did email you a virus would your antivirus logs get there yes perfect let's focus on those today and we'll get a little bit more of this stuff about connecting the dots all right so a little bit previous in this and i know i didn't uh point it out we had a malware domain
there was a c2 main that we had sandboxed as you can see we sandboxed it on november 2nd but on october 13th it was actually part of a already existing osm report and sure enough we have an actor associated with it so even though that domain wasn't used by there we saw it almost a month later from the friend intelligence we can see the hash that we had the name of the file we can see that hey it was used by ifc stands on here and now i have a ta551 actor associated this and even a malware document name like bach uh bachbot and iced ideas or ice id is the type of malware that was being
pushed by so without even having to analyze it without having a lot of data i've never started to connect these dots that start looking like those paragraphs i was telling them and we're doing this automatically today and like i said we'll do a sword talk a little while but here's the hash we saw on our network from this file name we have a bunch of tags but we also have 16 minor ttps take to this oh and by the way this domain is also seen by t855 t550 sorry t8551 uh we saw from ic sans and we see the command and control so now it's not just that we knew this domain was bad but now we have all the associated
content with it right so a lot of like as i said this got flagged and let's say our email security and or endpoint when we found this hash we sandboxed it we got all these gdps associated all their tags and by the way this was the domain it called once we went in there we saw this domain and saw that it was already in our sim so the good thing is we knew that c2 hadn't been active in our environment but we started going like well what is this did we identify it from our sandbox what are we gonna do well now we have all this other data to connect the dots go like huh
well now i have an actor associated with it so now we go okay well what other things does this actor do okay let's start looking at this let's start see what this other actor does because maybe there's a malware in c2 that i'm not aware of let's go take a look and that'll build into some of the threat hunting stuff a little bit later so as you can see um this is actually two attacks that happen on the same day we see two different hashes in here some overlapping ttps and we can actually start mapping out the overlap of those minor ttps from the various pieces of malware and i see um encrypted channels very red
that means it's overlapping on a lot of the different techniques um native api only one of the two hashes had that okay only one of the two hashes uses removable media but both of them had process injection okay well now you sort of see how we map this out and start using this in our sort of secure operations and going okay well would i have caught this do i have rules or my does my ebr c for process injection do i have um powershell scripting so as we click on these you can actually get more details but it's not interactive so i can't do that in my slideshow here but now we sort of draw sort of the
bigger picture of what's actually hitting our network and this type of alert we're looking for this gives you a hundred percent more context than my ips fire to high severity alert right because you kind of sit there like what would be your next step was it successful it was blocked okay great but did he do anything else well we don't know right but now we start building this up from the back so from the down on the lower ends of the kill chain and on the higher and then so the sort of meet in the middle all right so when we start doing this um the difference between thread hunting and alerting is very very different
right thread hunting is things that you don't necessarily know in your environment maybe low confidence indicators whatever else that have different behaviors some of them are um you know uh learning it's got to be your confidence stuff i don't want to see a confidence of 40 percent firing alert myself so we start grabbing three intelligence from there but we start making it very very tactical and very very close to what we're looking for so if you remember one of those first slides we had 50 million indicators in 90 days we only have 346 of those that make it to our cent okay why well we care if it's greater than 90 days old we don't want to see it
because greater than 90 days old isn't really an alertable threat intelligence indicator okay great well on ips we might want 90 but on domains you might want 50 percent okay great maybe you don't want urls or sim doesn't do that why do we have that intel so we start sort of tuning it down to what really matters from a word perspective to what we can see and as we start doing that now we can actually start matching on those to the behaviors that we see um so if we were to look at this okay we have intelligence that matches we have this well now we can see like a delivery a technique number and there's a phishing
email match great an email came in and we saw a match and it was delivered alert fires right we can come up here and say hey we have a fishing gear on and this is very interesting see how the matches up here and the matches down here same technique well one of them is a phishing email match one of them is they click the link this is my proxy log if they click the link they've exploited my user that matters to me authentication through iocs now we're detected emote downloaders so we have specific indicators for con um looking at emote and c2 and as you see depending on the rule we have many more rules and different
phases and these are not all of them i've kind of strategically picked different sections to show it for this we see two domains that are known c2 domains uh known uh threat detection etcetera etcetera and so as we start matching those up we can actually start seeing okay so if we see c2 domain if i see one hit from a c2 to me does that mean that i have c2 most you know most sims and most learners were like yes well what if that's not really c2 c2 beacons it calls them more than once and we see a lot more data around it okay great so how will we see a c2 domain then what
fires over 50 times in a 24-hour period that may be a much more i'm going to say context-based rule that it tells us that not only did we match the c2 domain but we measured more than this time um it was allowed or not allowed and you start looking at what called that domain whether it's the browser chrome or whether it's malware.exe but matching that intelligence to that alert and behaviors is really the key point takeaway when he starts looking at the threat intelligence and the alert matching is if you have the framework and you know where it says that now you have the intelligence and the tag and it matches all that you combine the two
excuse me you can start seeing how everything starts to fit together um and then you know as we get past that from security operations because everybody's sort of pivoting into uh threat hunting these days and i'm looking at my time so i'll keep on getting near the end here so when you answer some questions thread hunting is not the same thing thread hunting is looking for those different things in our network that may be high confidence maybe not high confidence but what do they find so yes this is a vendor tool called nominee match uh but allows us to use these indicators a much different way and as you can see there's obvious spikes in intelligence
and attacks and different types of attackers countries that are standing out and we actually certain matches over time and i can start matching on actors i can start matching on ttb's i can start matching vulnerabilities and even news stories of threat bulletins or you can start learning on them over time and so as we start going through this okay so remember how we said we didn't want like intelligence greater than 90 days that's great right because it's not a good indicator it's old everybody pivots emails ips etc etc right but as we start looking at this we start looking examples where hey we see an apt-ip with a confidence of 40 and 320 days old it may not be something
we care about however we see you try to send an email in from admin at support.vx.com and we also see that it says it's that a graceful spider just a cyber criminal interesting well on the same day we got this email but the first time passive dns had supportvx.com hosted on sip oh and look we also have onedrive.gm.eu.com and a few other one drives sort of domain so it's off that same ip around the same sort of time frames that we're seeing so a couple days later and more and more and more huh well it's an old indicator it's low confidence but now i see blocked emails coming in from this sort of same indicator
and i can see that they're blocked um unfortunately my current mail until i couldn't see the url or what they're sending but i can see that it dropped that it's associated with this actor and then we're seeing very targeted type of email so sword.vx.com or onedrive are very common fishing type stuff that we'd see maybe this indicator now i tagged with all these different things and now it becomes less than 90 days old now it comes up and says huh the confidence for me might be 80 because i can see a lot of fishing domains off of it and now i take this all together and now i have something i can work on and that comes from the
thread hunting spectacle uh so final wrap up um i know that we're 44 40 45 minutes here so um when you look at this it can be manual but it seems like when you do these sort of conversations or the ones that the feedback i've got from previous talks is this look right over here but we're over here how do we do this and i call this for the writer's block we constantly send this sort of that fire sort of image uh this one here where everybody's sort of seeing this image we're sitting in fire we don't have time to do this and we're trying to fight all these fires and we're sitting there like
we can't do this today we can't tell our intelligence we can't see what alerts we're currently firing we're going to look at these types of things and we're kind of losing that sort of the battle because we're seeing ten thousand words a day um if we went back to the alert one where i showed you how many words today let's say we see 20 alerts a day and maybe four of them actually make it past um you know the level of um automatically what level one triaging well that's four alerts a day that's pretty good to be able to manage right and even if you get up to 10 of them 10 20 30 alerts 30 alerts a day is
really easy to manage versus 10 000 and with the context that we're seeing it at the analysts already know what they're going to be able to do you don't have to sit there and go like huh so it says we had a ioc match for white we pro which is one of the other custom alerts that they showed up there okay what does that mean to me right and so we go back and we start looking at this and go okay well now i know it's at the c2 level that it was a c2 domain and he's what i've heard it says to it we talked about 50 times in this great so did anybody type commands on
that computer no do we have any malware alerts let's go see did we have any scheduled tasks but we did well now we have a way to hunt and use that okay well how did that schedule task or how did that you know registration get edited okay let's go look at our delivery and it's a structured way for them to look at you can do it today we don't have to we don't have to sit here and start by tools i know that code's there you don't need to buy brand new tools to start doing this work today and there's a lot of ground work to do when you start mapping this out and identifying where your gaps are
whether it be packets c2 logging um i've been talking like a lot of consulting friends they'll sit there and go hey you know half the time they don't even have the logs in their sim well what logs are they missing let's map it out against the lifecycle focus on those that are priority wise because of this and we're all going to start from here there's going to be challenges um focus on what you need to do focus on what's important look at what tools you currently have and use those the best of your abilities and then go from there and um that's sort of my final wrap up and i know there's a couple questions
um i'll jump into some questions the and then if you have time i'll show one another screenshot in advance or um people at cal state i might have to cover some things tonight as well uh for local meetings so sorry i'm just going back up uh rod had a question first do you think it's a big miss on vendors that promises the world and sells missing value this and that yes and no um i think that our vendors are trying but i think one of the biggest challenges that we have with a lot of this is that vendors um have to go to like the lowest common denominator so for example if you see vrs they'll say hey
we have the most minor matches in the world and we tag every single minor technique that's great but i don't want to know every time somebody takes that user or scheduled a task i want to schedule tasks fired when it goes from a normal user to an elevated user this and that right so i think that we have to take sort of what the vendors are doing and sort of start adding some intelligence around it from a behavior perspective and only we know what the behavior is in our network right if somebody types in that user five times from cmd.ec manually within an hour that there is probably a better indicator than the net user every time
but some companies might say 10 something might say five some might say three in an hour is enough to alert on so i think we have to start providing that back into our tools uh another one from rodney how do you dynamically imagine that for adjusting confidence the simulator this is related to this post anomaly uh yeah so normally there's private tags and internal tags and so what we usually do is um you can provide a confidence or source confidence level and then um they have the macular algorithm in the back of anomaly that does some calculations for us and we kind of go back and forth when we ingest them um and say hey this is what
we wanted to be this what it is however we also have on certain indicators with certain behaviors like credential stuffing based on the rules that we see from our sim 100 of the time we know that this is what they're doing so we don't rely on anybody doing any calculations and that's what it gets saved as uh nick what about corny word yes um so we caught so um this is actually good and thank you nick um one of my upcoming talks with diamond and only rationally providing a trusted circle but within anomaly and other tools we have a threat sharing circle or a trusted circle where we share this intelligence with others um whether it be an ir
rhi sac or an aviation eye sac or a health eye set you know there's these great sharing circles but i find that there's a sometimes it's hard to share they don't have mechanisms to do it in that in a very structured way and the other challenge is that they're sharing intelligence in a way that has no context um there's uh like for example my worst thing is when somebody uploads an ip says bad ip or ip block list if i see an indicator that says that um you know those get excluded from my sim and from my intelligence because that doesn't find me anything what do i know that it does now i have to go do my own research on an abused
ibdb and everything else and go through that um so yes we do share but i'm trying to get some structure on how we share whether it's private public tags to help us get a little bit more of that structure like the attack life cycle after the kill chain we can actually start seeing where that season alerts so that everybody provides some level of context around the alerts hey this email great was it malware or credit stuff or credential that's it right um uh so i'll go down to brett here uh what is the highest roi i can get this prediction that will happen next yeah so um with roi it's hard with for intelligence we've been able to map it out on some of
the attacks we saw so if you see um one of my slides back here where we had sort of the big spike because we tag and we know we tag a specific behavior this actor ip you can see it overlapped with the spam ip and bought ipml ip this huge spike because we take this can tell us exactly what that behavior was almost instantly we don't have to have almost like an investigation we know what's happening we know what's going on um the biggest roi is really hard because it's hard to measure but we've been able to a predicted tax so one of the other presentations going to bring up which if i have time
with five minutes at the end i'll bring it up is we're actually able to base on trending all this data actually predict threats when and how they're gonna hit us favorite ninja turtles leonardo um thank you tyler and rodney do you exclude them or do you have a main review a little bit of both so um for my indicators i auto import them depending on the um the slow rule that i have most of them auto import because we rule them out and there's like good examples where like the uh vulnerability tags that we have they'll go and have a whole bunch of cds and then what will end up happening is it'll take out quality and everything
else that's actually what we're using ah thanks rodney um so yeah so we include next with different things um it varies depending on the intelligence but we're able to start mapping this out like i said even with the um the mapping of reconnaissance and who's doing it in the cred stuffing we're able to do that a little bit easier and it looks like um i haven't got the message yet that i have to stop so i'll do one quick last thing here for this is a different presentation but um this is part of the one that we're doing with an omni and ion where we talk about sort of the cool things this is where you start getting
advanced and we start talking about sun tzu if you know the enemy and you know yourself you know you should not worry about any battle when we look at this and we start looking at the behaviors we can actually start mapping this out for example we have indicators that are under 90 days that were coming through here and they were actually hitting us and you can see they're all related to a specific actor on this or a malware family so this was a trick bought or with this fighter now our family when it's under 90 days and because of the behavior that we see over and over again we knew that this is going to happen so we're going to come
and say we're going to see a credential something attack from primarily russia-based ips uh within the next four to five days based on the fact that we can see whoops sorry second here there we go and this can be really hard to read so i'm going to go through in january we saw this do a credential stuff against us and around may or march timeframe we saw that the uh crowd striker another friend hellbender take this as trickbot and the behavior we see doing over here and i know it's really hard to read is they were doing things like missing headers firefox and chrome anomalies basically user agent things that we're not letting it pass or laugh
and when you combine these intel markers and these here and you see that behavior together we can make this prediction and it always happened like a monday tuesday night and we saw it go happen and then sure enough from the indicators that we saw on june 11th 15 failed logins from the country and indicator bonnet that we saw sure enough you know within four days so on the 15th 300 and started smiling from there went up for two days um so we're actually able to predict how these are happening now because of this framework and because of mapping it all out we can actually see when and how they're going to hit us so we need to say
i don't know even my boss hates this when you send them another thing in four to five days you're gonna get hit right and you're like what do you mean like don't worry we're ahead of it we're fine but when you can start telling them how and when you're going to be hit and what's going to happen if they got hit which means we have all these ttps mapped out we'd say yes we have all these rules yes we see this we're ahead of this we know what's going on and because of this we know this is going to happen we can go from there and they said there's taking profiles we're going to have a guidance for
tagging moderated that will be coming out by i think by the end of the month and so that's it thank you everybody for coming um like i said it's a different than more technical just trying to talk about the mindset and get past there thank you for all that if you have any questions please message me anytime